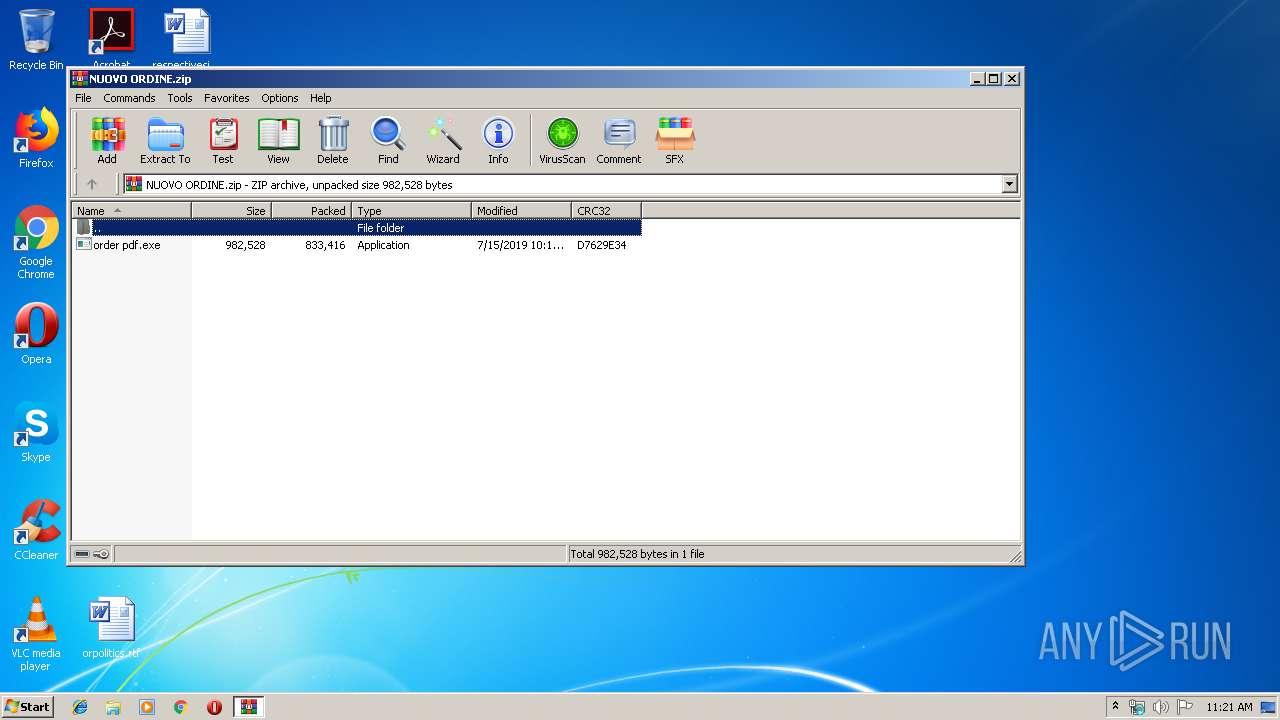
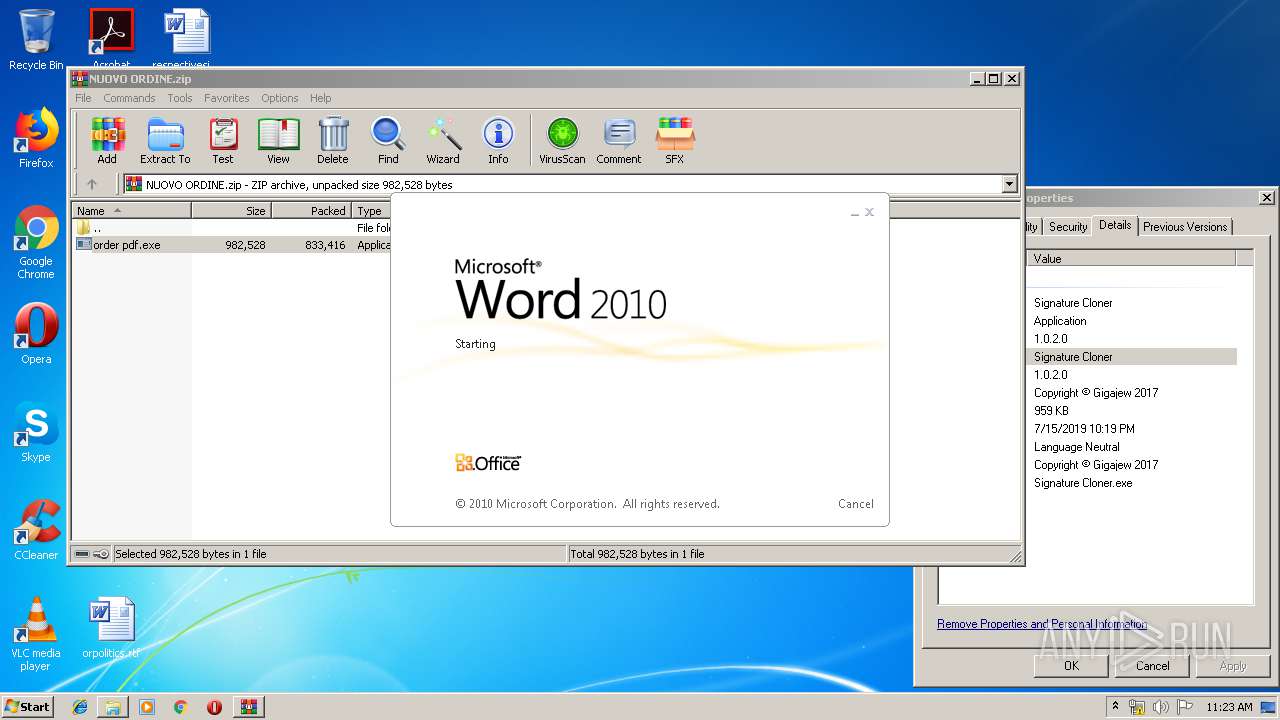
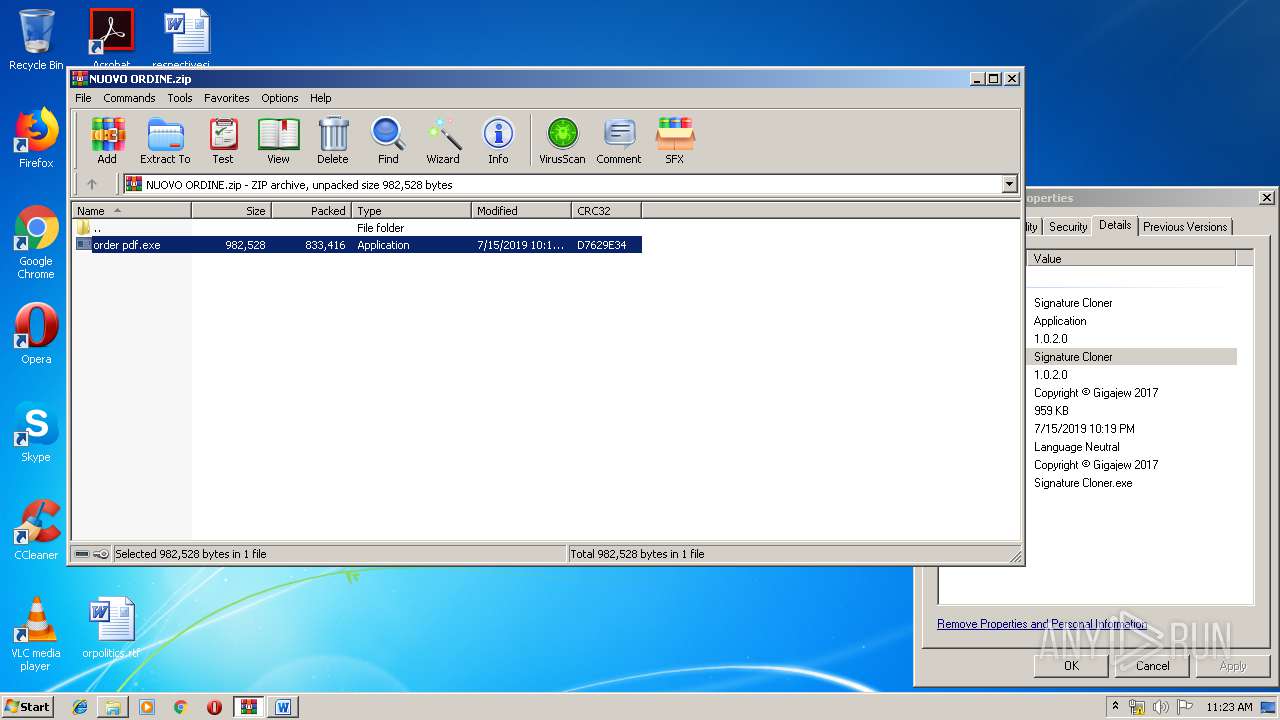
| File name: | NUOVO ORDINE.zip |
| Full analysis: | https://app.any.run/tasks/a6d4ed2a-569c-4860-a6cd-5edbaee2f2e8 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | July 17, 2019, 10:21:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 61BEF721E6697DC79423734B3A61D4AD |
| SHA1: | A032E82D20C49E44D23BA73C4C1FCA50D4C2F0DC |
| SHA256: | 438E25C79F4AD75C4942174CBC7255C74FE521920999646CE855100D9923216C |
| SSDEEP: | 24576:c9BAjTQ+oIfUS2XHQ6aahQJ7xgKhaTCuW6P/cEJ5Arld:cQXQo2g6ahgeICr6Pbk |
MALICIOUS
Application was dropped or rewritten from another process
- TVwrd.exe (PID: 3384)
- order pdf.exe (PID: 2652)
- TVwrd.exe (PID: 3592)
Changes the autorun value in the registry
- TVwrd.exe (PID: 3384)
Detected artifacts of LokiBot
- TVwrd.exe (PID: 3592)
LOKIBOT was detected
- TVwrd.exe (PID: 3592)
Connects to CnC server
- TVwrd.exe (PID: 3592)
Actions looks like stealing of personal data
- TVwrd.exe (PID: 3592)
SUSPICIOUS
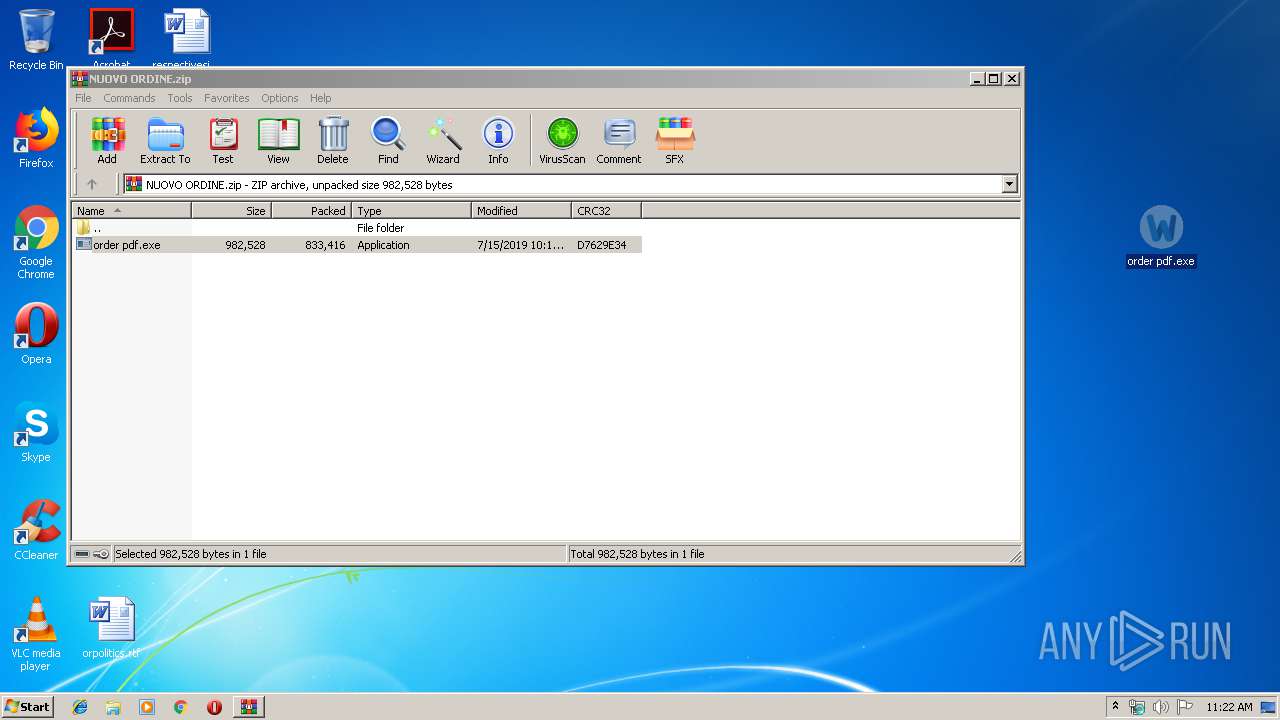
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3528)
- order pdf.exe (PID: 2652)
- TVwrd.exe (PID: 3384)
Application launched itself
- TVwrd.exe (PID: 3384)
Loads DLL from Mozilla Firefox
- TVwrd.exe (PID: 3592)
Creates files in the user directory
- TVwrd.exe (PID: 3592)
INFO
Manual execution by user
- WINWORD.EXE (PID: 3332)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3332)
Creates files in the user directory
- WINWORD.EXE (PID: 3332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:07:15 22:19:21 |
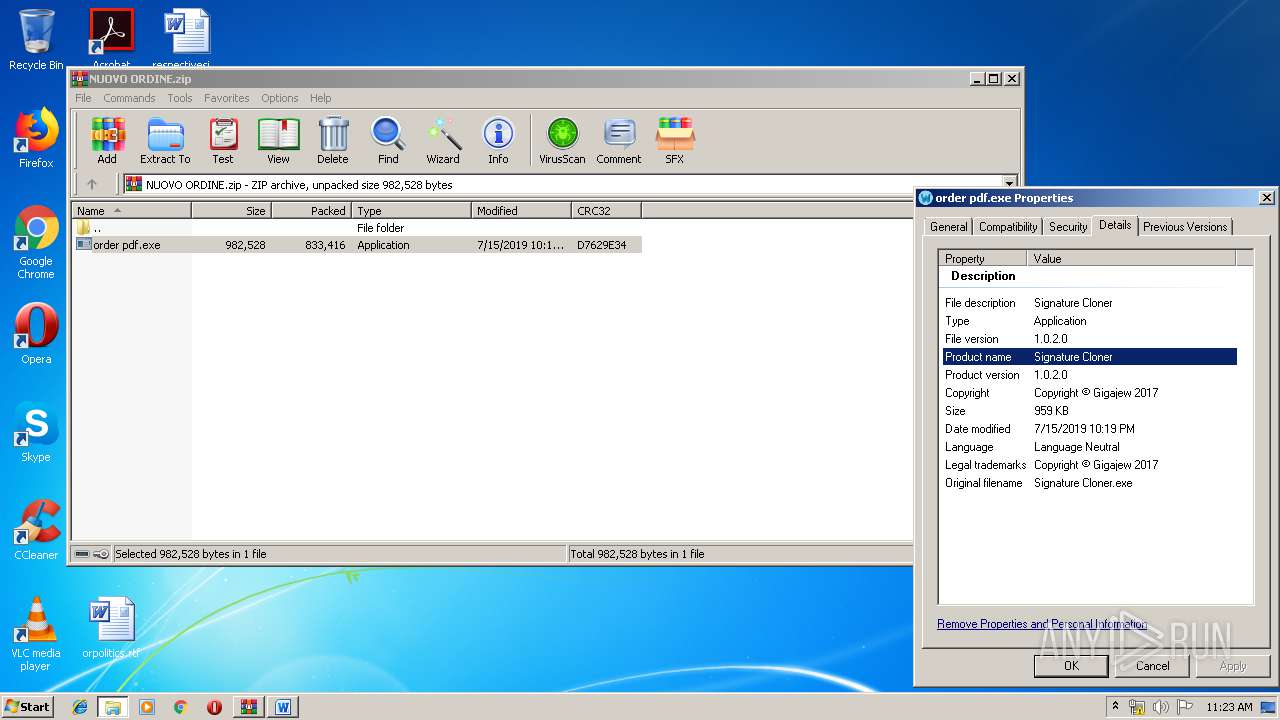
| ZipCRC: | 0xd7629e34 |
| ZipCompressedSize: | 833416 |
| ZipUncompressedSize: | 982528 |
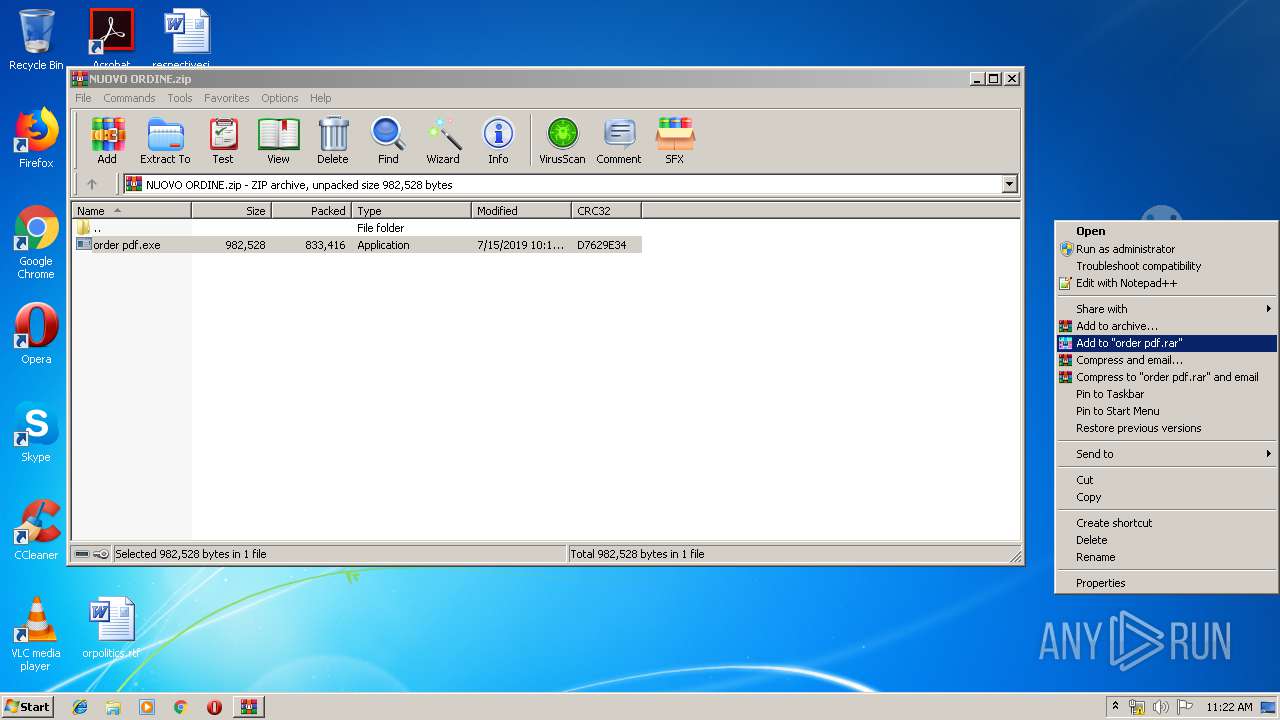
| ZipFileName: | order pdf.exe |
Total processes
43
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2652 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3528.1558\order pdf.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3528.1558\order pdf.exe | WinRAR.exe | ||||||||||||
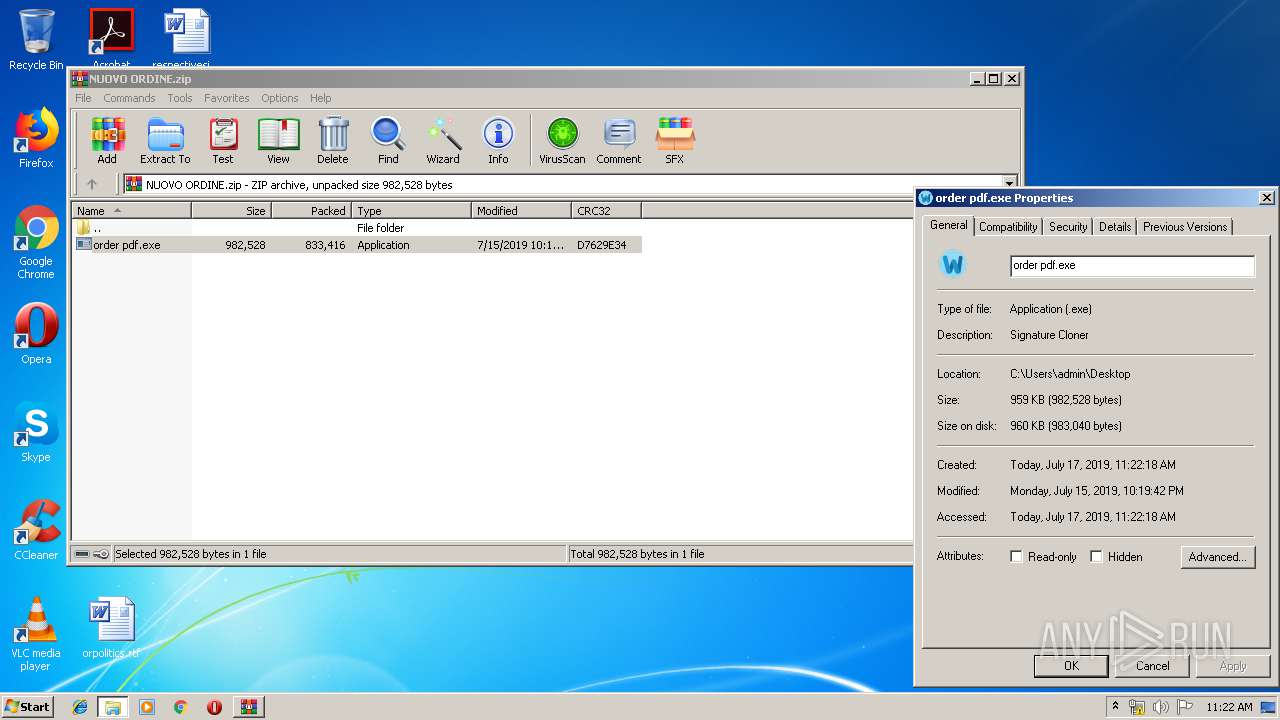
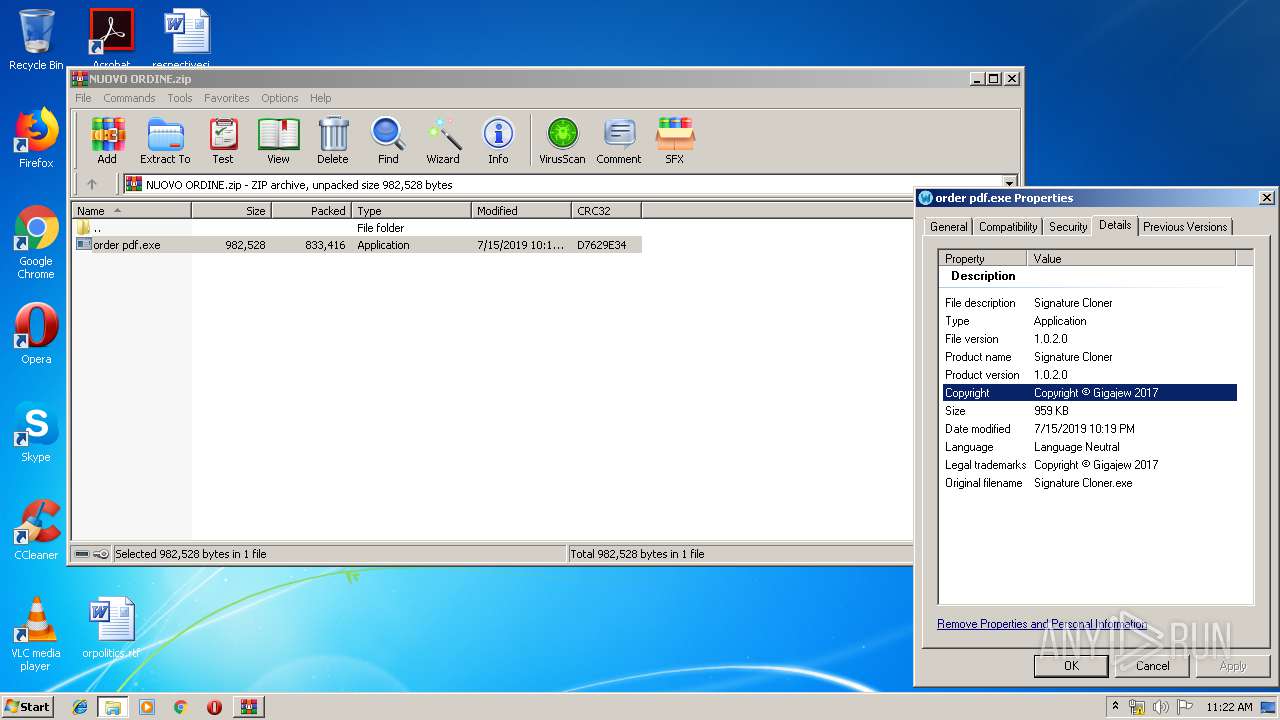
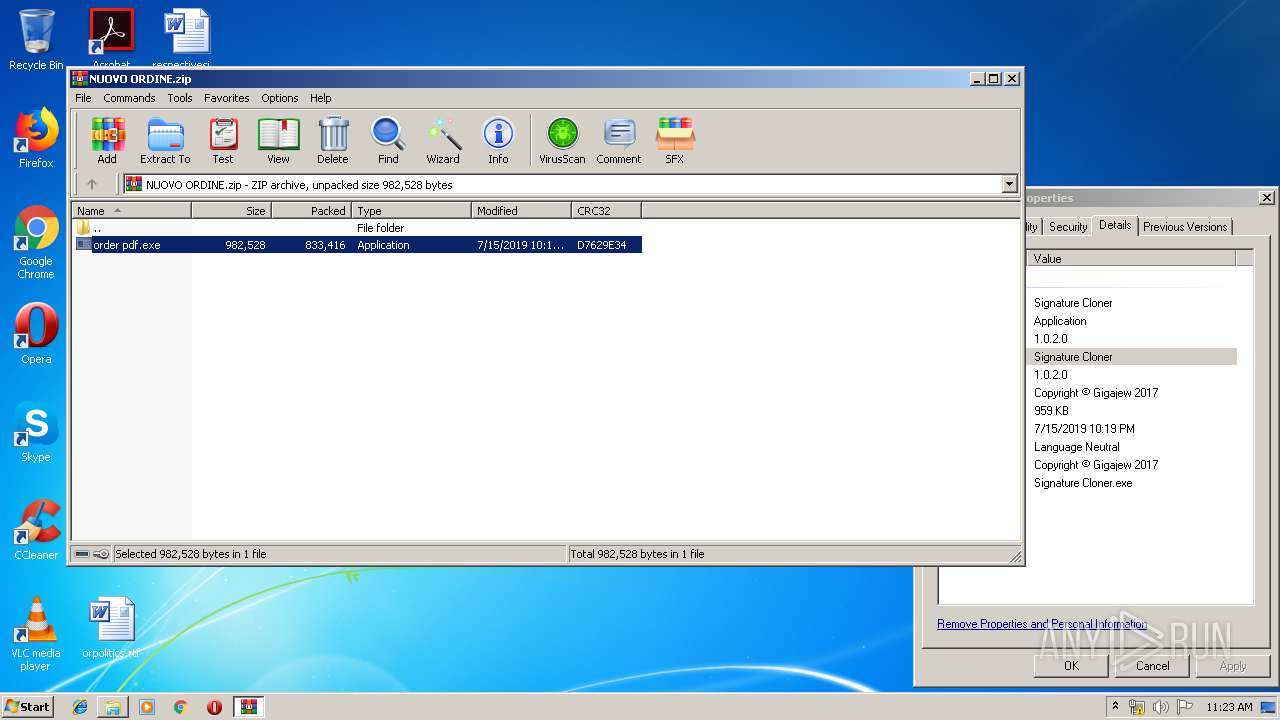
User: admin Company: HackForums Integrity Level: MEDIUM Description: Signature Cloner Exit code: 0 Version: 1.0.2.0 Modules
| |||||||||||||||
| 3332 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\orpolitics.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3384 | C:\Users\admin\AppData\Local\TVwrd.exe | C:\Users\admin\AppData\Local\TVwrd.exe | order pdf.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3528 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\NUOVO ORDINE.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3592 | C:\Users\admin\AppData\Local\TVwrd.exe | C:\Users\admin\AppData\Local\TVwrd.exe | TVwrd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 335
Read events
988
Write events
340
Delete events
7
Modification events
| (PID) Process: | (3528) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3528) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3528) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3528) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\NUOVO ORDINE.zip | |||
| (PID) Process: | (3528) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3528) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3528) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3528) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3528) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3528) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
0
Text files
5
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3528 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3528.44009\order pdf.exe | — | |
MD5:— | SHA256:— | |||
| 3332 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE768.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3592 | TVwrd.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 2652 | order pdf.exe | C:\Users\admin\AppData\Local\Tm.bmp | image | |
MD5:— | SHA256:— | |||
| 2652 | order pdf.exe | C:\Users\admin\AppData\Local\TVwrd.exe | executable | |
MD5:— | SHA256:— | |||
| 3332 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\orpolitics.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3332 | WINWORD.EXE | C:\Users\admin\Desktop\~$politics.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3332 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3592 | TVwrd.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.hdb | text | |
MD5:— | SHA256:— | |||
| 3528 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3528.1558\order pdf.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3592 | TVwrd.exe | POST | — | 47.74.38.64:80 | http://bioconscolors.com/nweke/fre.php | JP | — | — | malicious |
3592 | TVwrd.exe | POST | — | 47.74.38.64:80 | http://bioconscolors.com/nweke/fre.php | JP | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3592 | TVwrd.exe | 47.74.38.64:80 | bioconscolors.com | Alibaba (China) Technology Co., Ltd. | JP | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bioconscolors.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3592 | TVwrd.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3592 | TVwrd.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3592 | TVwrd.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3592 | TVwrd.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3592 | TVwrd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
3592 | TVwrd.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3592 | TVwrd.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3592 | TVwrd.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3592 | TVwrd.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3592 | TVwrd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
2 ETPRO signatures available at the full report