| File name: | filelegend.exe |
| Full analysis: | https://app.any.run/tasks/eaa7463c-e46d-4709-836f-1e85c946a476 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | October 25, 2020, 14:59:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | F93EE232EBFB7CF5293927A295A3149A |
| SHA1: | 2BA11DEB25247EFC4A7232CC40B80750B35DF39B |
| SHA256: | 42FDF8EA94129772B3A3A9CB027AE40613D5ABA9DE2B6F32F801D00F1C5CCF44 |
| SSDEEP: | 6144:YglzdTZ4rjNxG/i/OfFGr6O2lNu6HCIYNLKjCAKSjB:5V/4rjvGiO9C6OuNuzHVKO2jB |
MALICIOUS
Application was dropped or rewritten from another process
- AddInProcess32.exe (PID: 2928)
- 9rfx9hdxcjwtq.exe (PID: 1908)
Connects to CnC server
- explorer.exe (PID: 392)
Loads dropped or rewritten executable
- filelegend.exe (PID: 2428)
Changes the autorun value in the registry
- wininit.exe (PID: 3968)
FORMBOOK was detected
- wininit.exe (PID: 3968)
- Firefox.exe (PID: 3744)
- explorer.exe (PID: 392)
Actions looks like stealing of personal data
- wininit.exe (PID: 3968)
Stealing of credential data
- wininit.exe (PID: 3968)
SUSPICIOUS
Executable content was dropped or overwritten
- filelegend.exe (PID: 2428)
- explorer.exe (PID: 392)
- DllHost.exe (PID: 716)
Starts CMD.EXE for commands execution
- wininit.exe (PID: 3968)
Creates files in the user directory
- wininit.exe (PID: 3968)
Executed via COM
- DllHost.exe (PID: 716)
Loads DLL from Mozilla Firefox
- wininit.exe (PID: 3968)
Creates files in the program directory
- DllHost.exe (PID: 716)
INFO
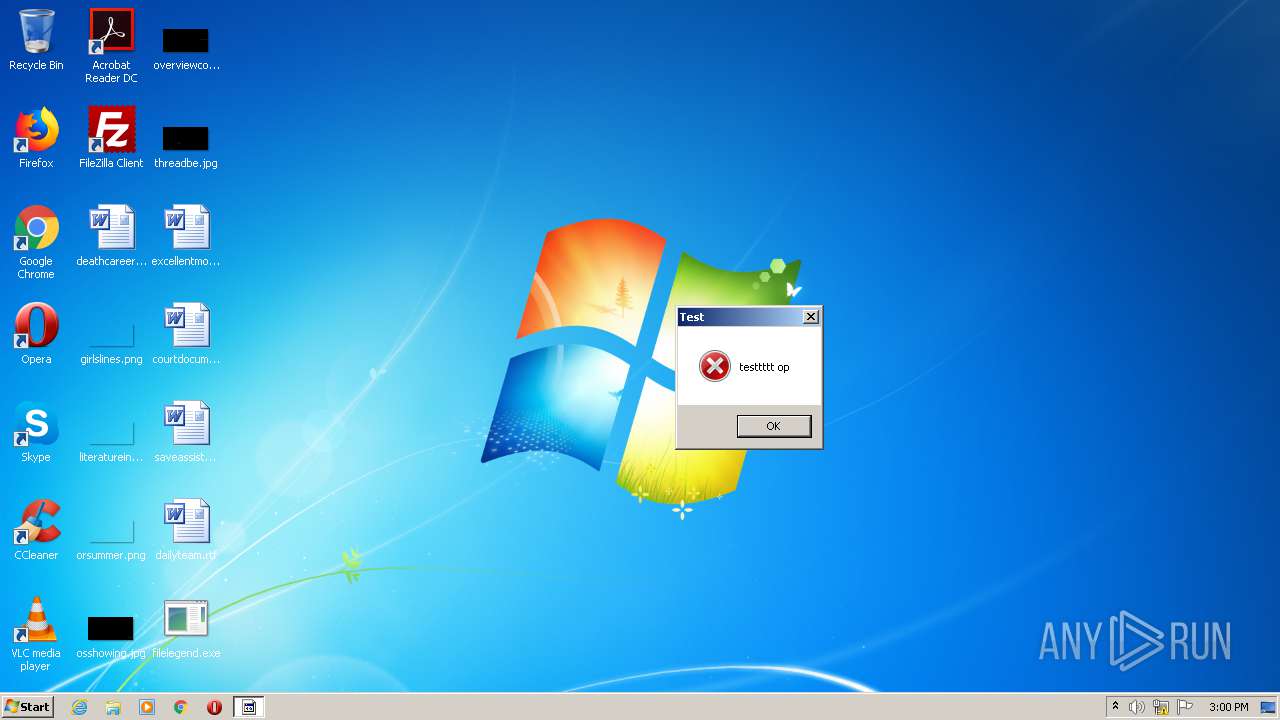
Manual execution by user
- wininit.exe (PID: 3968)
Creates files in the user directory
- Firefox.exe (PID: 3744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:10:24 16:04:55+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 468480 |
| InitializedDataSize: | 2560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7457e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.1.1 |
| ProductVersionNumber: | 1.1.1.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Wefaebakegexoqaelokunaesyje |
| CompanyName: | n$8>6ta;43e(j/15f]-2us@09 |
| FileDescription: | Tamiqaehacivaeredaevyjumy |
| FileVersion: | 1.1.1.1 |
| InternalName: | filelegend.exe |
| LegalCopyright: | Copyright © 2008 - 2020 |
| OriginalFileName: | filelegend.exe |
| ProductName: | Tamiqaehacivaeredaevyjumy |
| ProductVersion: | 1.1.1.1 |
| AssemblyVersion: | 0.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Oct-2020 14:04:55 |
| Comments: | Wefaebakegexoqaelokunaesyje |
| CompanyName: | n$8>6ta;43e(j/15f]-2us@09 |
| FileDescription: | Tamiqaehacivaeredaevyjumy |
| FileVersion: | 1.1.1.1 |
| InternalName: | filelegend.exe |
| LegalCopyright: | Copyright © 2008 - 2020 |
| OriginalFilename: | filelegend.exe |
| ProductName: | Tamiqaehacivaeredaevyjumy |
| ProductVersion: | 1.1.1.1 |
| Assembly Version: | 0.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 24-Oct-2020 14:04:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00072584 | 0x00072600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.8026 |
.rsrc | 0x00076000 | 0x00000632 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.58811 |
.reloc | 0x00078000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
46
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 716 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1908 | "C:\Program Files\Vy4g49dw8\9rfx9hdxcjwtq.exe" | C:\Program Files\Vy4g49dw8\9rfx9hdxcjwtq.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 1 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 2428 | "C:\Users\admin\Desktop\filelegend.exe" | C:\Users\admin\Desktop\filelegend.exe | explorer.exe | ||||||||||||
User: admin Company: n$8>6ta;43e(j/15f]-2us@09 Integrity Level: MEDIUM Description: Tamiqaehacivaeredaevyjumy Exit code: 0 Version: 1.1.1.1 Modules
| |||||||||||||||
| 2928 | "C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe" | C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe | — | filelegend.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 3384 | /c del "C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe" | C:\Windows\System32\cmd.exe | — | wininit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3744 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | wininit.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3968 | "C:\Windows\System32\wininit.exe" | C:\Windows\System32\wininit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Start-Up Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 012
Read events
967
Write events
45
Delete events
0
Modification events
| (PID) Process: | (2428) filelegend.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2428) filelegend.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\Qrfxgbc\svyryrtraq.rkr |
Value: 000000000000000000000000242E0000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000680000009C000000764446001000000033000000218616007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFF70599D7500000000000000003CE57600857599750004000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFFD0333B00D4343B0068DB3A006CE576002FB14E7680B08176ACF27600381E4F7614634F76A0173800A0E57600B87A390070000000BD0EB51780E57600BE6A4F76A0173800A0E5760000000000ACE776006F624F76A0173800A0E5760000000400000000807C624F76A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E00670011000000483D3800403D380073006F00660074005C00690064E600002D0EB51768E60000D50DB5171CE6760082914F7668E67600E4080000C90DB51730E67600B69C4F76E80823024C06000048E6760011000000483D3800403D38000000000040B0817648E6760078042302B8E60000810DB51768E6760082914F76B8E676006CE6760027954F7600000000E408230294E67600CD944F76E408230240E7760058042302E1944F76000000005804230240E776009CE676001000000033000000218616007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFF70599D7500000000000000003CE57600857599750004000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFFD0333B00D4343B0068DB3A006CE576002FB14E7680B08176ACF27600381E4F7614634F76A0173800A0E57600B87A390070000000BD0EB51780E57600BE6A4F76A0173800A0E5760000000000ACE776006F624F76A0173800A0E5760000000400000000807C624F76A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E00670011000000483D3800403D380073006F00660074005C00690064E600002D0EB51768E60000D50DB5171CE6760082914F7668E67600E4080000C90DB51730E67600B69C4F76E80823024C06000048E6760011000000483D3800403D38000000000040B0817648E6760078042302B8E60000810DB51768E6760082914F76B8E676006CE6760027954F7600000000E408230294E67600CD944F76E408230240E7760058042302E1944F76000000005804230240E776009CE676001000000033000000218616007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFF70599D7500000000000000003CE57600857599750004000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFFD0333B00D4343B0068DB3A006CE576002FB14E7680B08176ACF27600381E4F7614634F76A0173800A0E57600B87A390070000000BD0EB51780E57600BE6A4F76A0173800A0E5760000000000ACE776006F624F76A0173800A0E5760000000400000000807C624F76A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E00670011000000483D3800403D380073006F00660074005C00690064E600002D0EB51768E60000D50DB5171CE6760082914F7668E67600E4080000C90DB51730E67600B69C4F76E80823024C06000048E6760011000000483D3800403D38000000000040B0817648E6760078042302B8E60000810DB51768E6760082914F76B8E676006CE6760027954F7600000000E408230294E67600CD944F76E408230240E7760058042302E1944F76000000005804230240E776009CE67600 | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\display.dll,-4 |
Value: S&creen resolution | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Windows Sidebar\sidebar.exe,-11100 |
Value: &Gadgets | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\themecpl.dll,-10 |
Value: Pe&rsonalize | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02 | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
Executable files
5
Suspicious files
73
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | wininit.exe | C:\Users\admin\AppData\Roaming\326NTTBE\326logim.jpeg | image | |
MD5:— | SHA256:— | |||
| 716 | DllHost.exe | C:\Program Files\Vy4g49dw8\9rfx9hdxcjwtq.exe | executable | |
MD5:6A673BFC3B67AE9782CB31AF2F234C68 | SHA256:978A4093058AA2EBF05DC353897D90D950324389879B57741B64160825B5EC0E | |||
| 392 | explorer.exe | C:\Users\admin\AppData\Local\Temp\Vy4g49dw8\9rfx9hdxcjwtq.exe | executable | |
MD5:6A673BFC3B67AE9782CB31AF2F234C68 | SHA256:978A4093058AA2EBF05DC353897D90D950324389879B57741B64160825B5EC0E | |||
| 3968 | wininit.exe | C:\Users\admin\AppData\Roaming\326NTTBE\326logrc.ini | binary | |
MD5:— | SHA256:— | |||
| 2428 | filelegend.exe | C:\Users\admin\AppData\Local\Temp\e34dd831-6d57-4d92-81ec-c008864dca6e\AgileDotNetRT.dll | executable | |
MD5:14FF402962AD21B78AE0B4C43CD1F194 | SHA256:FB9646CB956945BDC503E69645F6B5316D3826B780D3C36738D6B944E884D15B | |||
| 3744 | Firefox.exe | C:\Users\admin\AppData\Roaming\326NTTBE\326logrf.ini | binary | |
MD5:2F245469795B865BDD1B956C23D7893D | SHA256:1662D01A2D47B875A34FC7A8CD92E78CB2BA7F34023C7FD2639CBB10B8D94361 | |||
| 3968 | wininit.exe | C:\Users\admin\AppData\Roaming\326NTTBE\326logri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
| 2428 | filelegend.exe | C:\Users\admin\AppData\Local\Temp\b35bc50e-fc56-4239-a7d0-bb79118b31c9\AgileDotNetRT.dll | executable | |
MD5:14FF402962AD21B78AE0B4C43CD1F194 | SHA256:FB9646CB956945BDC503E69645F6B5316D3826B780D3C36738D6B944E884D15B | |||
| 3968 | wininit.exe | C:\Users\admin\AppData\Roaming\326NTTBE\326logrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
| 2428 | filelegend.exe | C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe | executable | |
MD5:6A673BFC3B67AE9782CB31AF2F234C68 | SHA256:978A4093058AA2EBF05DC353897D90D950324389879B57741B64160825B5EC0E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
29
DNS requests
10
Threats
50
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
392 | explorer.exe | GET | — | 172.252.51.169:80 | http://www.fightr4hir.com/qh86/?UTyLh4=uOriLnq8IGV3IwE3UYuuFzk2fDZcmTW1BjNbmv02RwWbkYxEg8s9ojToO8L+mEe5kzetXw==&PpQ=HbMhL8lhJj8luN | CN | — | — | malicious |
392 | explorer.exe | GET | — | 163.44.185.226:80 | http://www.matsukusa.com/qh86/?UTyLh4=1lvqfIHpzps+Ejs6Zr/53FvuILNi0Odqw5+mbiRTMqho1uIqHLxvHG0utPwOWH6dLt43QQ==&PpQ=HbMhL8lhJj8luN&sql=1 | JP | — | — | malicious |
392 | explorer.exe | GET | — | 81.169.145.159:80 | http://www.equaliby.com/qh86/?UTyLh4=0tVkhtX1ZgUCN1BLtvAuUm7yDy95TIT1joPS2Ex/2FvhNXjWcRasSeMhlgEDfsjr7Y+VDg==&PpQ=HbMhL8lhJj8luN&sql=1 | DE | — | — | malicious |
392 | explorer.exe | POST | — | 81.169.145.159:80 | http://www.equaliby.com/qh86/ | DE | — | — | malicious |
392 | explorer.exe | GET | — | 154.220.181.19:80 | http://www.lifeunredacted.com/qh86/?UTyLh4=/4vVsX8e/QJyaWpBYhuPaCdB0K8l4/E9h7nHuuPx+OC+HF8Ph7SoiNKDtH9I4WO4Z7aNGg==&PpQ=HbMhL8lhJj8luN&sql=1 | US | — | — | malicious |
392 | explorer.exe | POST | — | 81.169.145.159:80 | http://www.equaliby.com/qh86/ | DE | — | — | malicious |
392 | explorer.exe | POST | — | 81.169.145.159:80 | http://www.equaliby.com/qh86/ | DE | — | — | malicious |
392 | explorer.exe | POST | — | 163.44.185.226:80 | http://www.matsukusa.com/qh86/ | JP | — | — | malicious |
392 | explorer.exe | POST | — | 163.44.185.226:80 | http://www.matsukusa.com/qh86/ | JP | — | — | malicious |
392 | explorer.exe | POST | — | 163.44.185.226:80 | http://www.matsukusa.com/qh86/ | JP | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
392 | explorer.exe | 163.44.185.226:80 | www.matsukusa.com | GMO Internet,Inc | JP | malicious |
392 | explorer.exe | 121.254.178.252:80 | www.waymaker-kr.com | LG DACOM Corporation | KR | malicious |
392 | explorer.exe | 160.153.136.3:80 | www.sekaccountingllc.com | GoDaddy.com, LLC | US | malicious |
392 | explorer.exe | 172.252.51.169:80 | www.fightr4hir.com | EGIHosting | CN | malicious |
392 | explorer.exe | 162.213.250.239:80 | www.top-dex.com | Namecheap, Inc. | US | malicious |
392 | explorer.exe | 175.29.155.81:80 | www.handbagshe.com | Access Telecom (BD) Ltd. | BD | malicious |
392 | explorer.exe | 154.220.181.19:80 | www.lifeunredacted.com | MULTACOM CORPORATION | US | malicious |
392 | explorer.exe | 81.169.145.159:80 | www.equaliby.com | Strato AG | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.fightr4hir.com |
| malicious |
www.equaliby.com |
| malicious |
www.matsukusa.com |
| malicious |
www.waymaker-kr.com |
| malicious |
www.sekaccountingllc.com |
| malicious |
www.thevichola.date |
| unknown |
www.lifeunredacted.com |
| malicious |
www.top-dex.com |
| malicious |
www.handbagshe.com |
| malicious |
www.riverrockla.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
21 ETPRO signatures available at the full report