| File name: | Gilded.exe |
| Full analysis: | https://app.any.run/tasks/87084895-928b-4f93-a1dd-af33e2a8df02 |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | January 04, 2024, 23:08:41 |
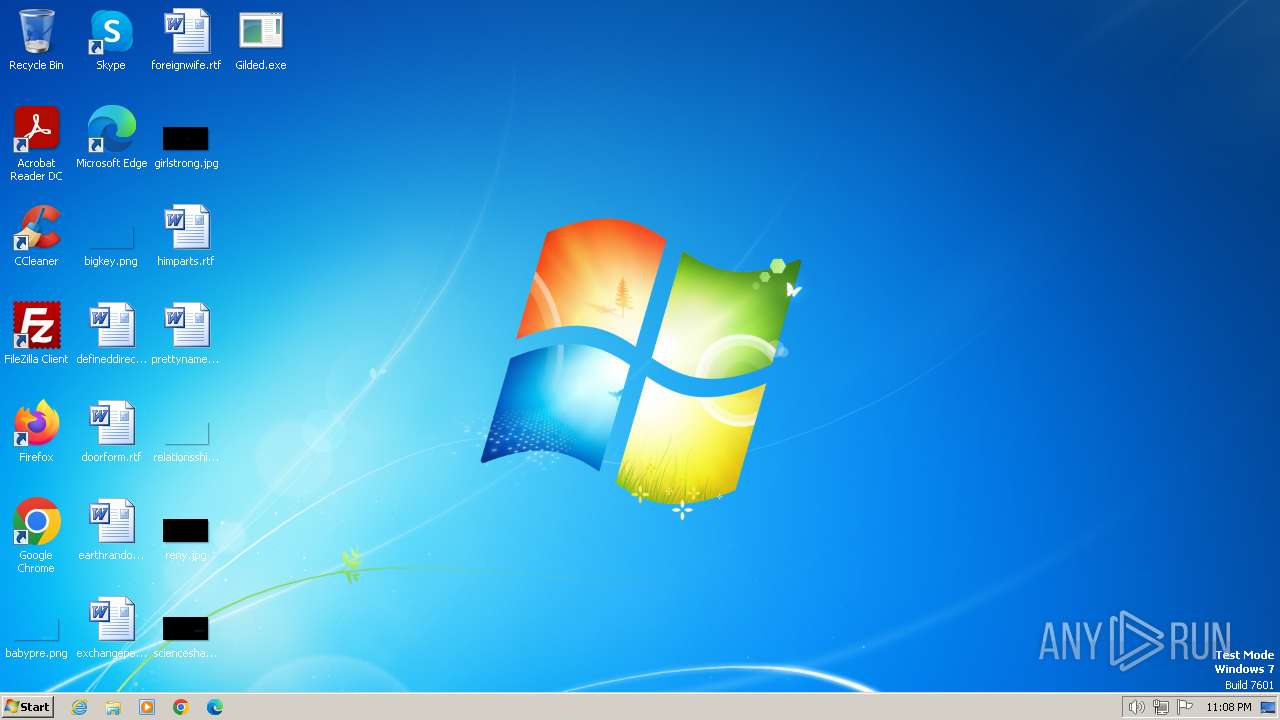
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | BE0783DB2E1FF4D7BAB3B180D33DAABF |
| SHA1: | CFBBAD9088BDF2E800F9F3734C81FB63C05DAA49 |
| SHA256: | 42DE7A49058E8D6F5D75496D3D162E3A50AA6A6F5B153CDF5E22C39F125C363C |
| SSDEEP: | 6144:KfLHrYr55yatoNy52Re7GB73wFj6f5WF3m6B2ZaHCwd+QD:KjrY7Yk5eosWF3C |
MALICIOUS
REDLINE has been detected (YARA)
- AppLaunch.exe (PID: 2036)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- Gilded.exe (PID: 2120)
- AppLaunch.exe (PID: 2036)
Reads the computer name
- AppLaunch.exe (PID: 2036)
Drops the executable file immediately after the start
- Gilded.exe (PID: 2120)
Reads the machine GUID from the registry
- AppLaunch.exe (PID: 2036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(2036) AppLaunch.exe
C2 (1)45.138.74.121:80
BotnetTOP441462863|1680865900|Krnllo
Options
ErrorMessage
Keys
XorCurassow
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31.7) |
| .scr | | | Windows screen saver (15) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:04:07 13:11:43+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 74240 |
| InitializedDataSize: | 168448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9200 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 5.250.269.2 |
| ProductVersionNumber: | 5.250.269.2 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | Shoots mangler bimonthly polyethylene |
| CompanyName: | Regressive |
| FileDescription: | Maternal allowances addressability |
| FileVersion: | 5.250.269.2 |
| InternalName: | Facetiousness |
| LegalCopyright: | Copyright © Smacked overeating signor catalysing chinese waterfront |
| LegalTrademarks: | Peafowl rant |
| OriginalFileName: | Gilded |
| ProductName: | Commissariat pluralists |
| ProductVersion: | 5.250.269.2 |
Total processes
36
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2036 | "C:\\Windows\\Microsoft.NET\\Framework\\v4.0.30319\\AppLaunch.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AppLaunch.exe | Gilded.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET ClickOnce Launch Utility Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
RedLine(PID) Process(2036) AppLaunch.exe C2 (1)45.138.74.121:80 BotnetTOP441462863|1680865900|Krnllo Options ErrorMessage Keys XorCurassow | |||||||||||||||
| 2120 | "C:\Users\admin\Desktop\Gilded.exe" | C:\Users\admin\Desktop\Gilded.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
389
Read events
389
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
0
Threats
6
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2036 | AppLaunch.exe | 45.138.74.121:80 | — | AEZA GROUP Ltd | AT | malicious |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2036 | AppLaunch.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
2036 | AppLaunch.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
2036 | AppLaunch.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
2036 | AppLaunch.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
2036 | AppLaunch.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
2036 | AppLaunch.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |