| File name: | TEST Sample.exe |
| Full analysis: | https://app.any.run/tasks/0be54fb9-a4a0-4827-b699-1ab577c55094 |
| Verdict: | Malicious activity |
| Threats: | Phorpiex is a malicious software that has been a significant threat in the cybersecurity landscape since 2016. It is a modular malware known for its ability to maintain an extensive botnet. Unlike other botnets, Phorpiex does not concentrate on DDoS attacks. Instead, it has been involved in numerous large-scale spam email campaigns and the distribution of other malicious payloads, such as LockBit. |
| Analysis date: | October 19, 2020, 07:54:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
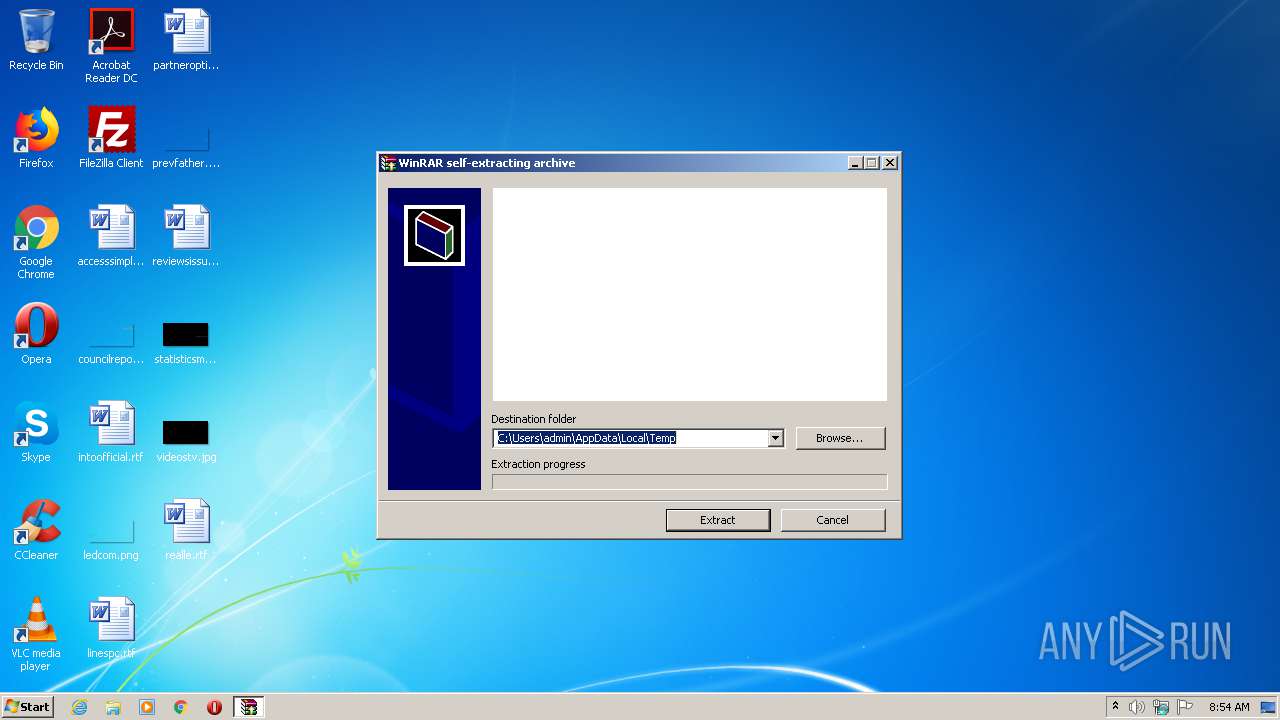
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 28AAECE0E087D818F6F005CF7BB72E2E |
| SHA1: | 8DFBDBA3FE3947DD122B4B228FA2255B2B33A0CA |
| SHA256: | 42C5C179AEEB86544E1A61A0908C55182E02A92E6F9F129FA0B8210544B1D845 |
| SSDEEP: | 24576:o20gPgFKWHWO0sWO03WO0FWO0FWO0lWO0R9EFvBQcNFlevJGtOfPz2PdYjvBQcND:5KM1aUU0OvBQimvwtekqjvBQiTX |
MALICIOUS
Application was dropped or rewritten from another process
- syscwbg.exe (PID: 3604)
- syslqph.exe (PID: 3448)
- sysfmcs.exe (PID: 2076)
- syseomj.exe (PID: 2028)
Disables Windows System Restore
- syscwbg.exe (PID: 3604)
- syslqph.exe (PID: 3448)
- sysfmcs.exe (PID: 2076)
Connects to CnC server
- syscwbg.exe (PID: 3604)
Disables Windows Defender
- syscwbg.exe (PID: 3604)
- syslqph.exe (PID: 3448)
- sysfmcs.exe (PID: 2076)
Changes Security Center notification settings
- syscwbg.exe (PID: 3604)
- syslqph.exe (PID: 3448)
- sysfmcs.exe (PID: 2076)
PHORPIEX was detected
- syscwbg.exe (PID: 3604)
SUSPICIOUS
Reads internet explorer settings
- TEST Sample.exe (PID: 2504)
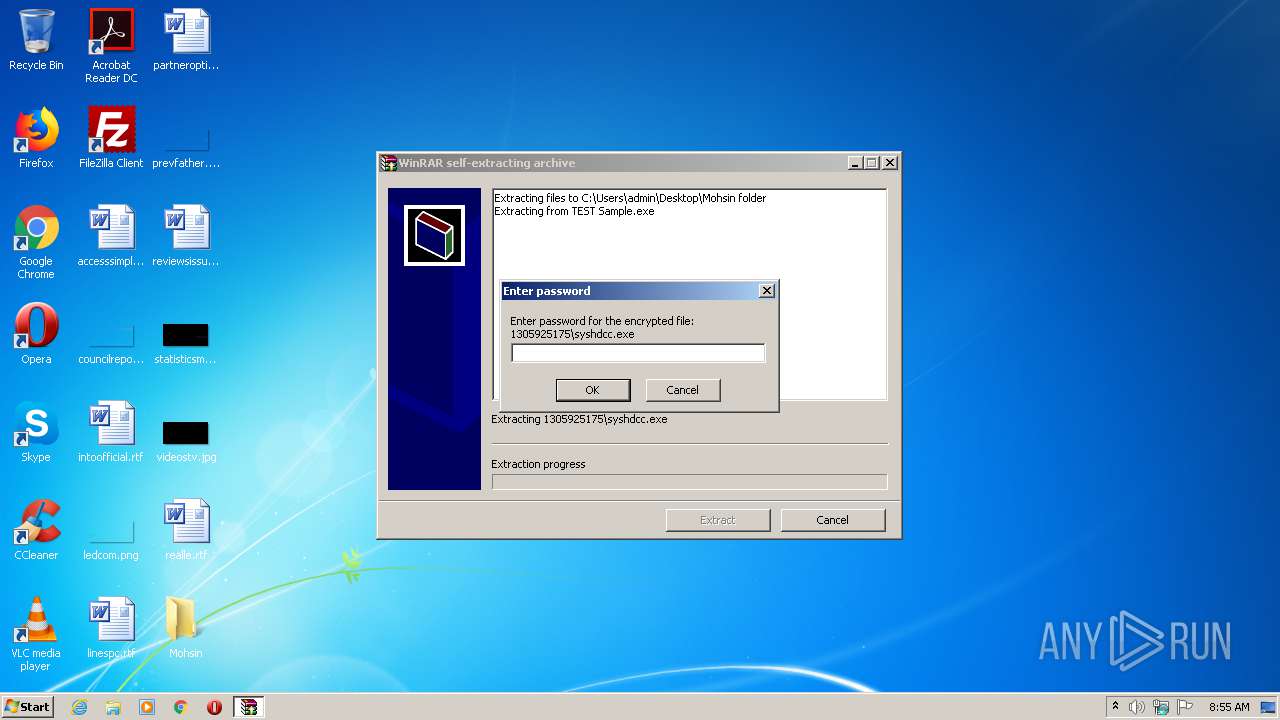
Executable content was dropped or overwritten
- TEST Sample.exe (PID: 2504)
Reads Internet Cache Settings
- TEST Sample.exe (PID: 2504)
- syscwbg.exe (PID: 3604)
- syslqph.exe (PID: 3448)
- sysfmcs.exe (PID: 2076)
Creates files in the user directory
- syscwbg.exe (PID: 3604)
INFO
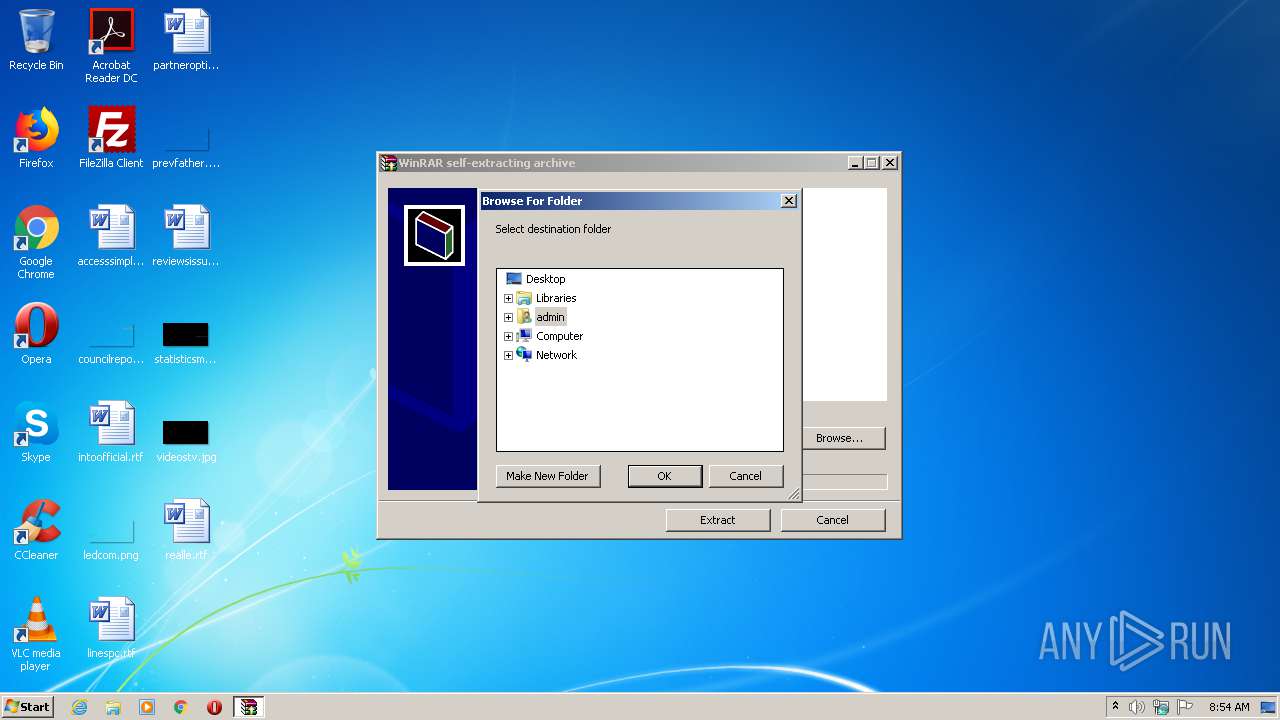
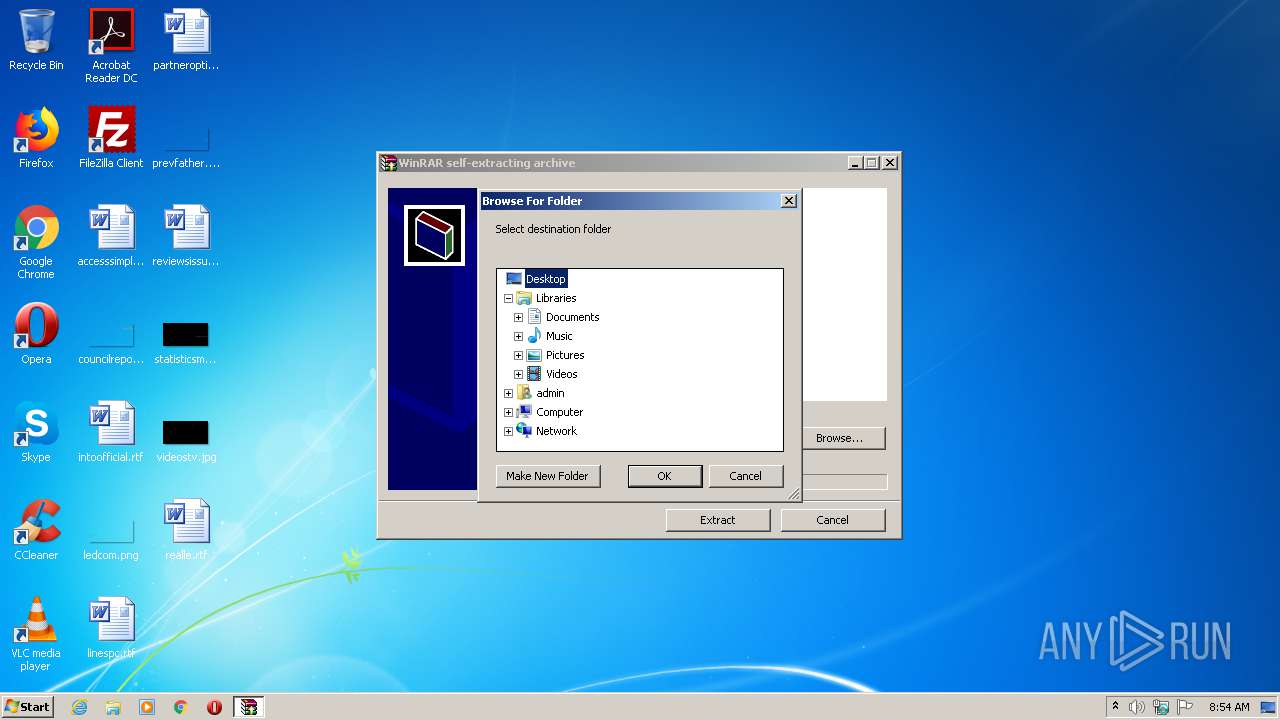
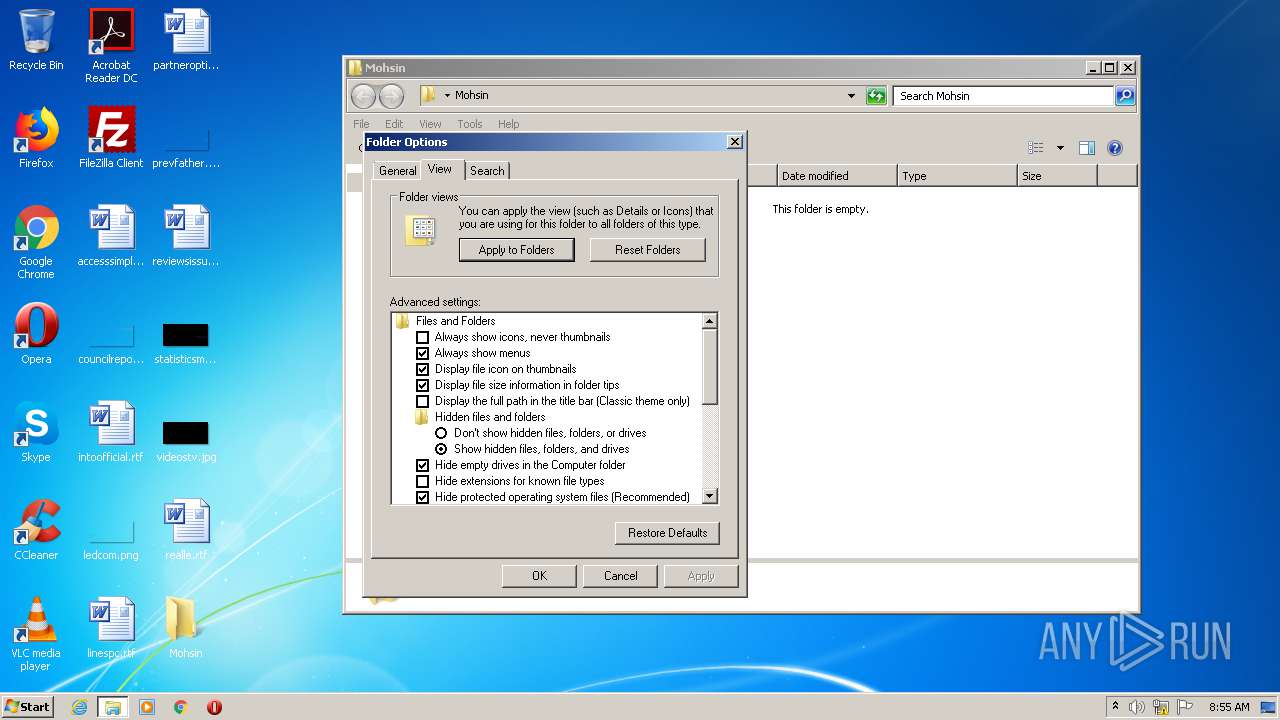
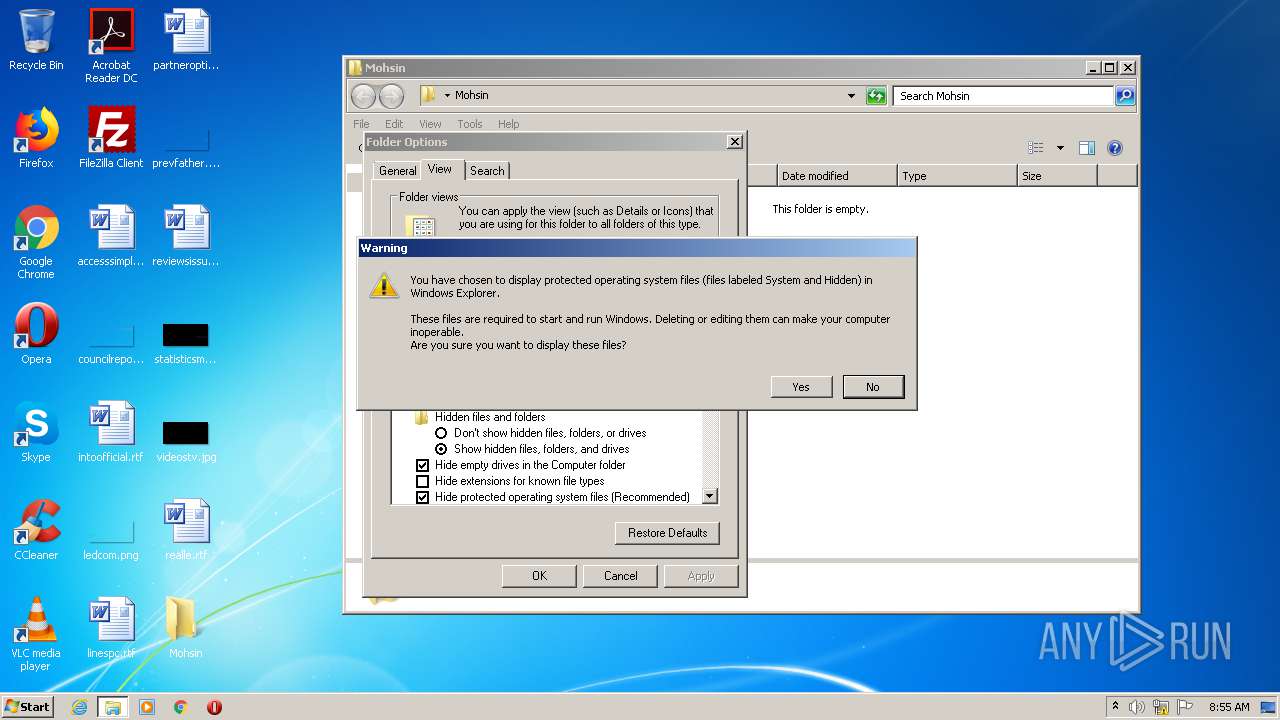
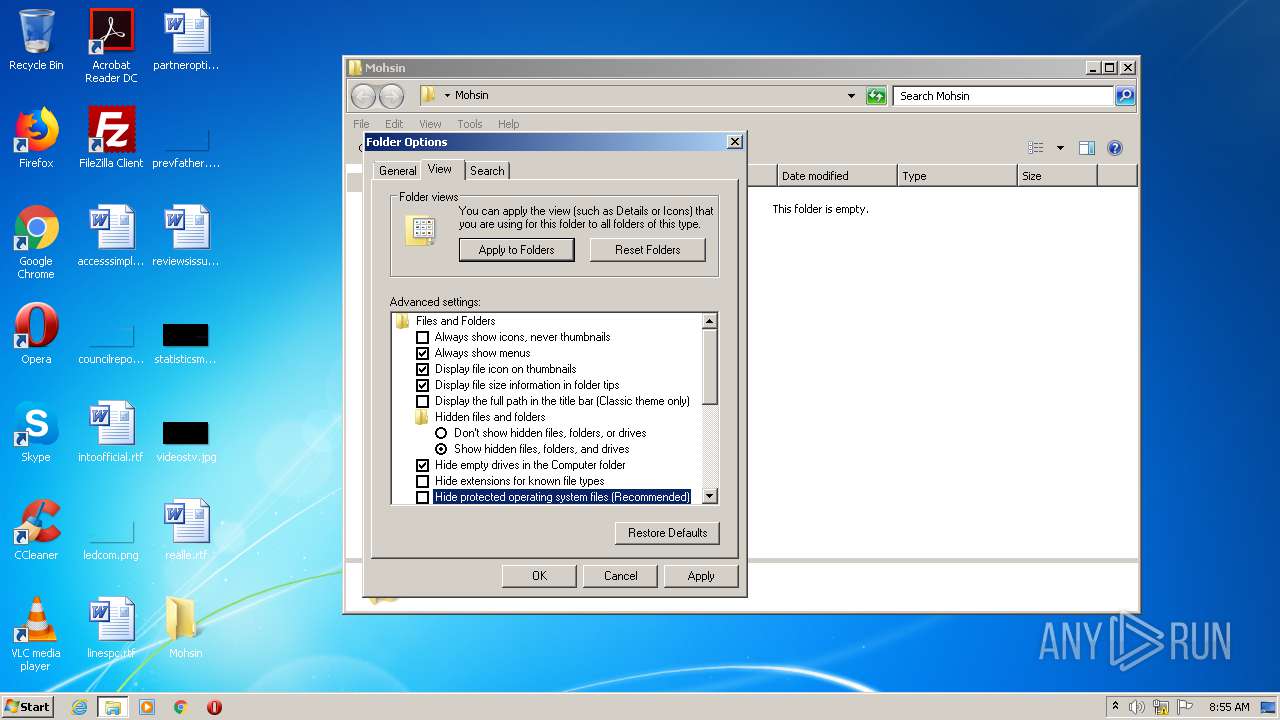
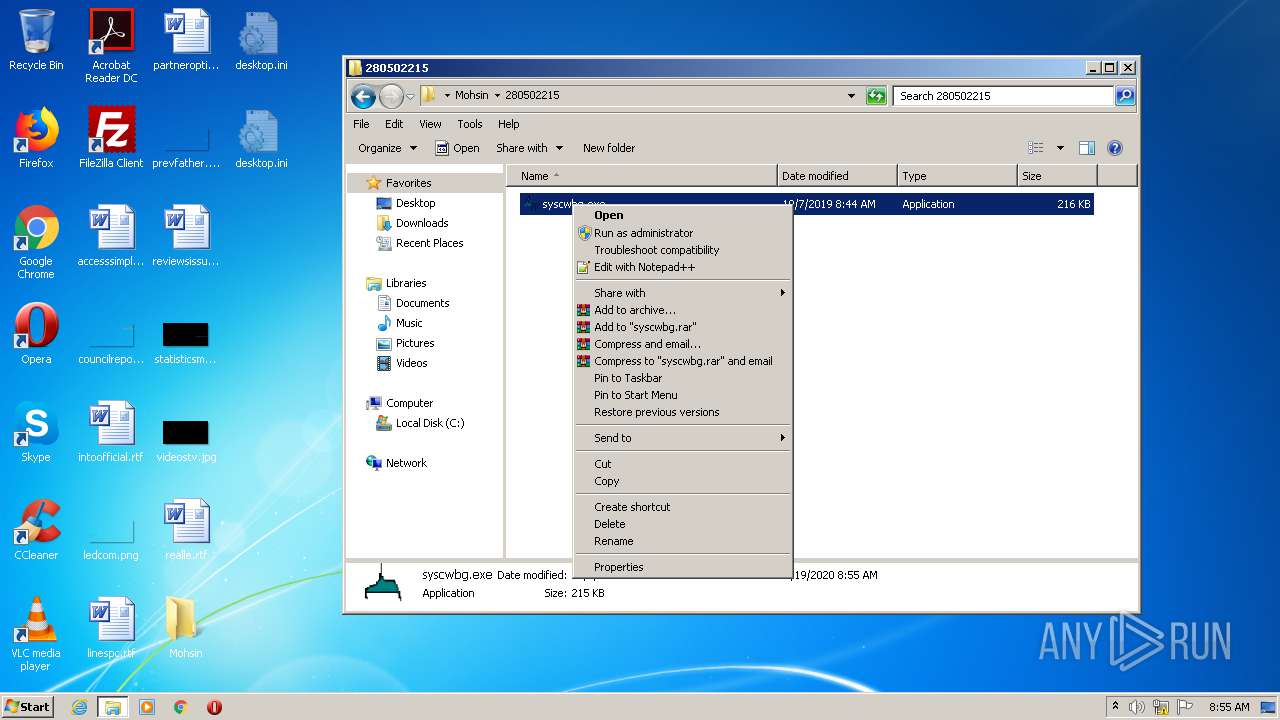
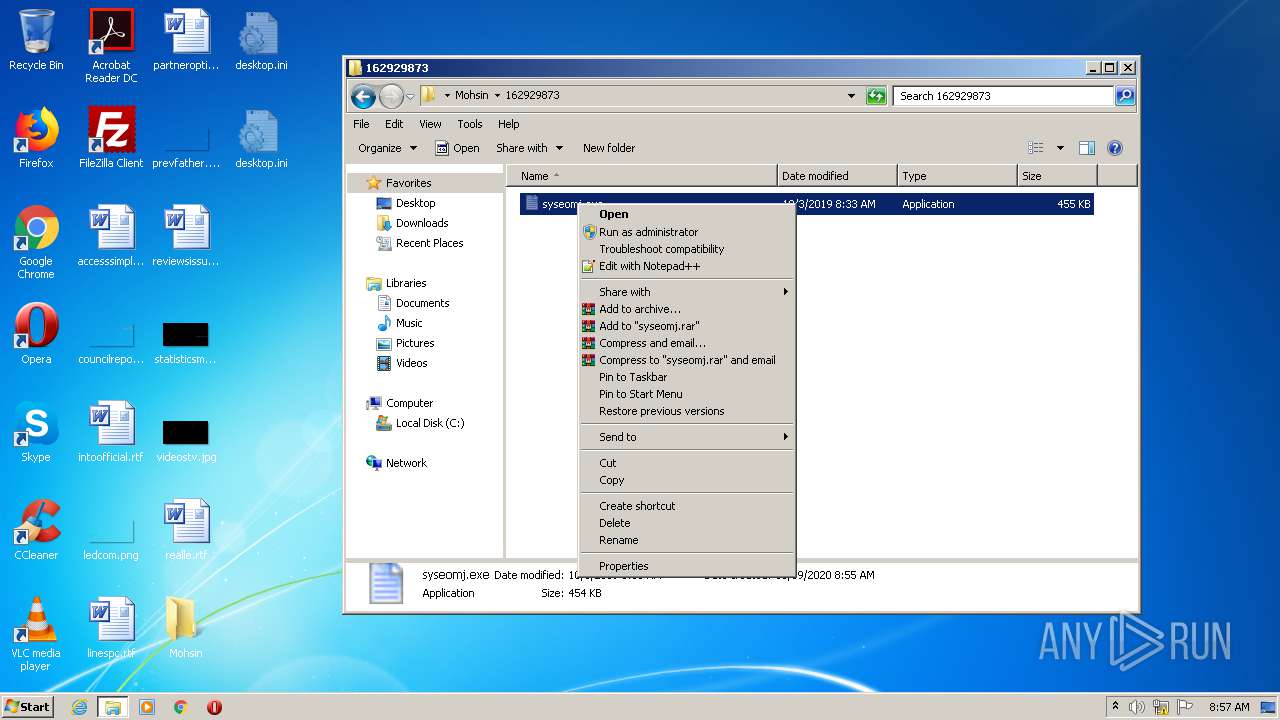
Manual execution by user
- syscwbg.exe (PID: 3604)
- syslqph.exe (PID: 3448)
- sysfmcs.exe (PID: 2076)
- syseomj.exe (PID: 2028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:12:02 11:07:30+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 165376 |
| InitializedDataSize: | 175104 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d5db |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Dec-2014 10:07:30 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 02-Dec-2014 10:07:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002859A | 0x00028600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.72265 |
.rdata | 0x0002A000 | 0x00004FD3 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.38632 |
.data | 0x0002F000 | 0x00021428 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.46654 |
.rsrc | 0x00051000 | 0x000044D8 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.65066 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.24822 | 1738 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.88998 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 4.12176 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 4.68705 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.15447 | 494 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
11 | 3.2036 | 1094 | UNKNOWN | English - United States | RT_STRING |
12 | 3.12889 | 358 | UNKNOWN | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
60
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
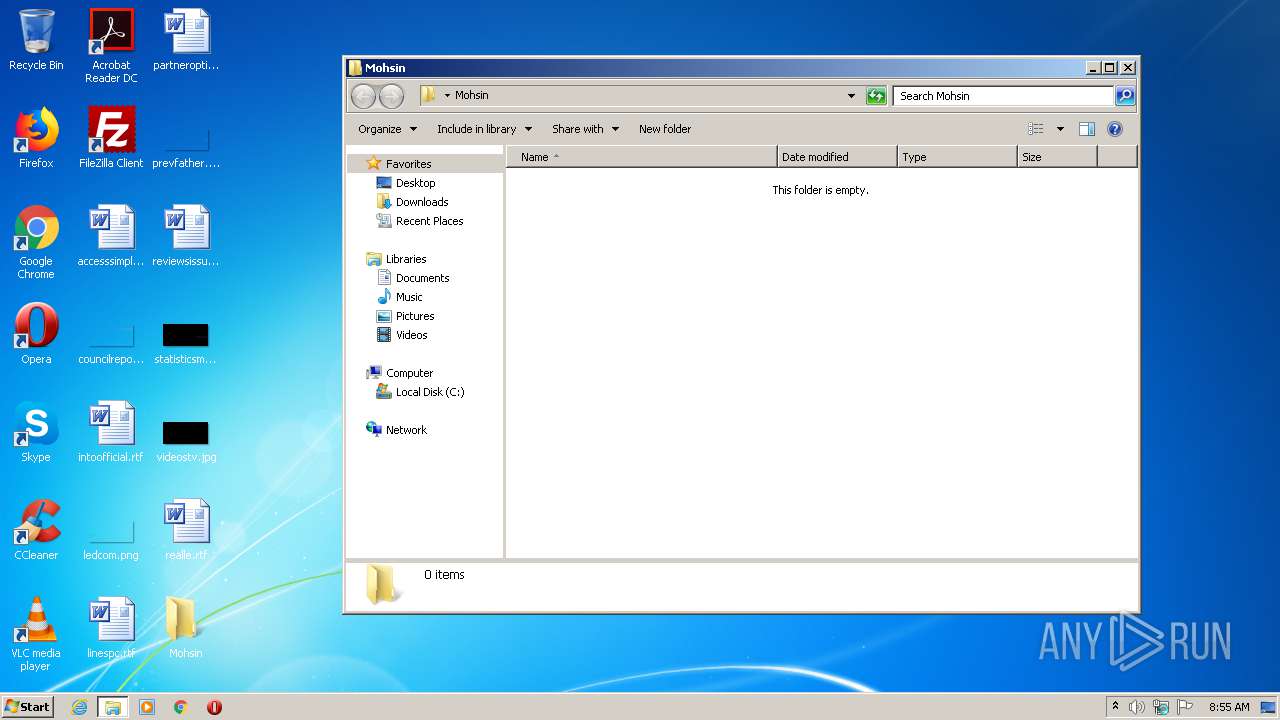
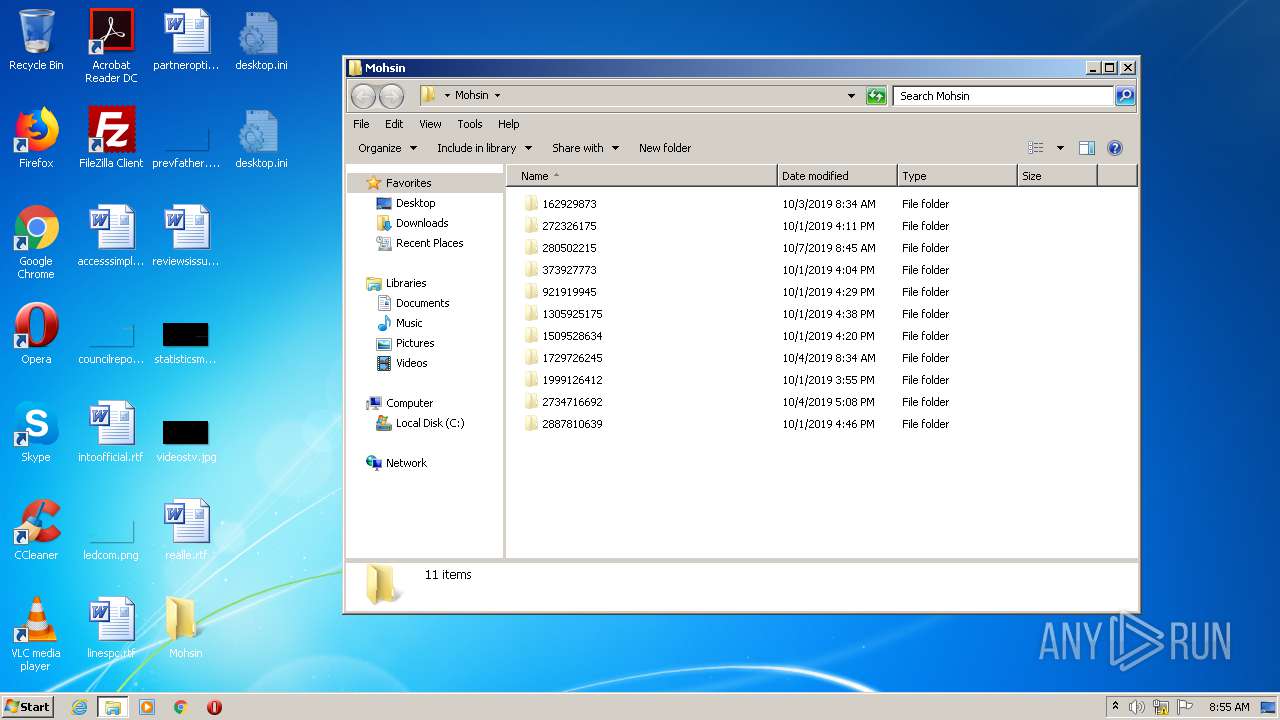
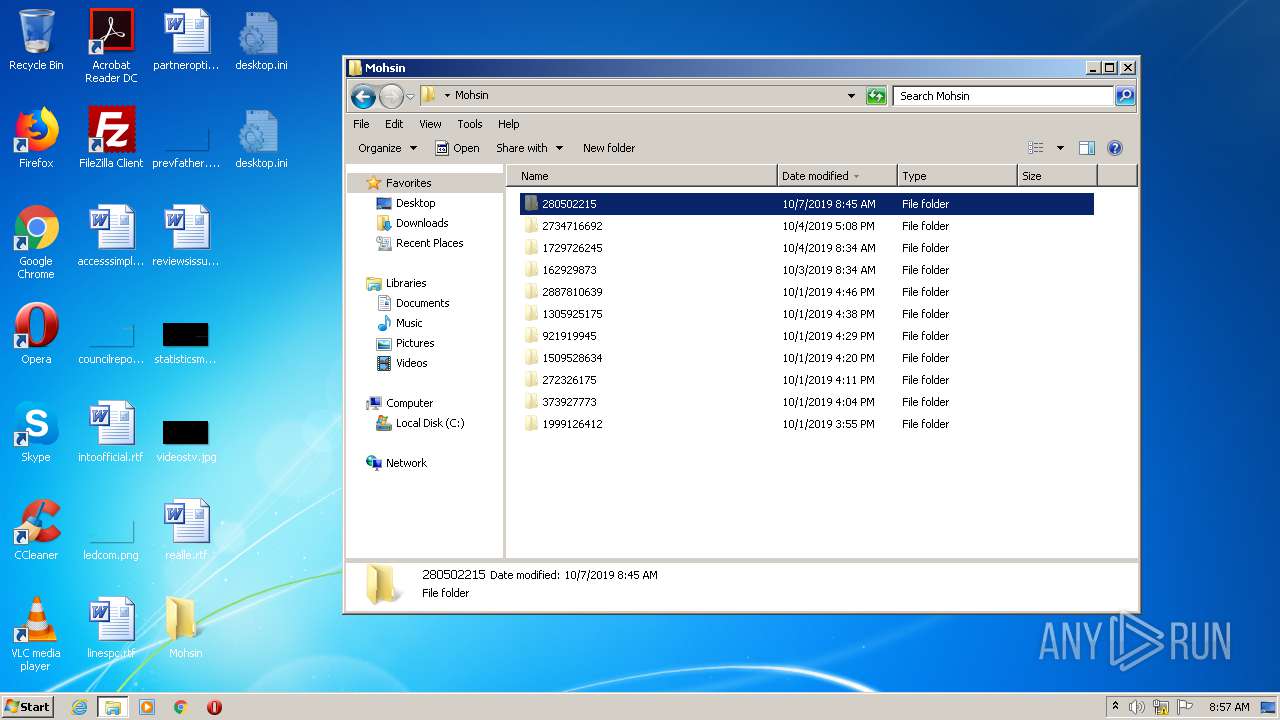
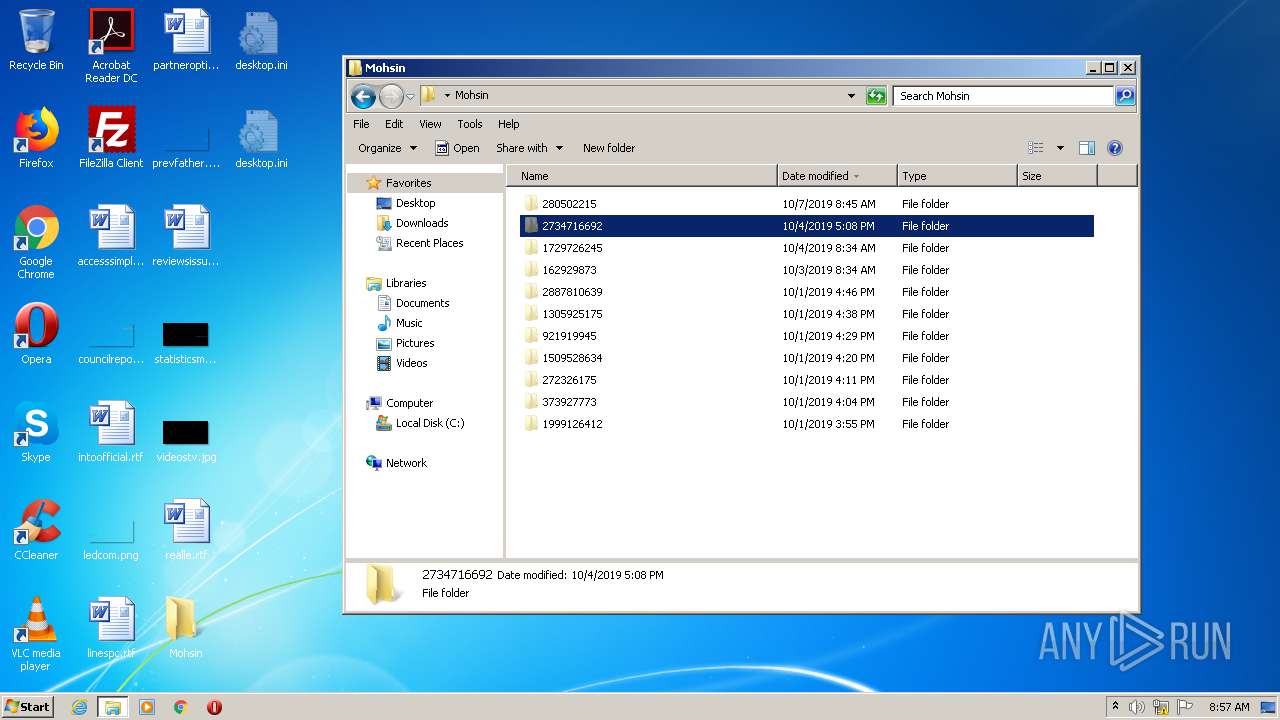
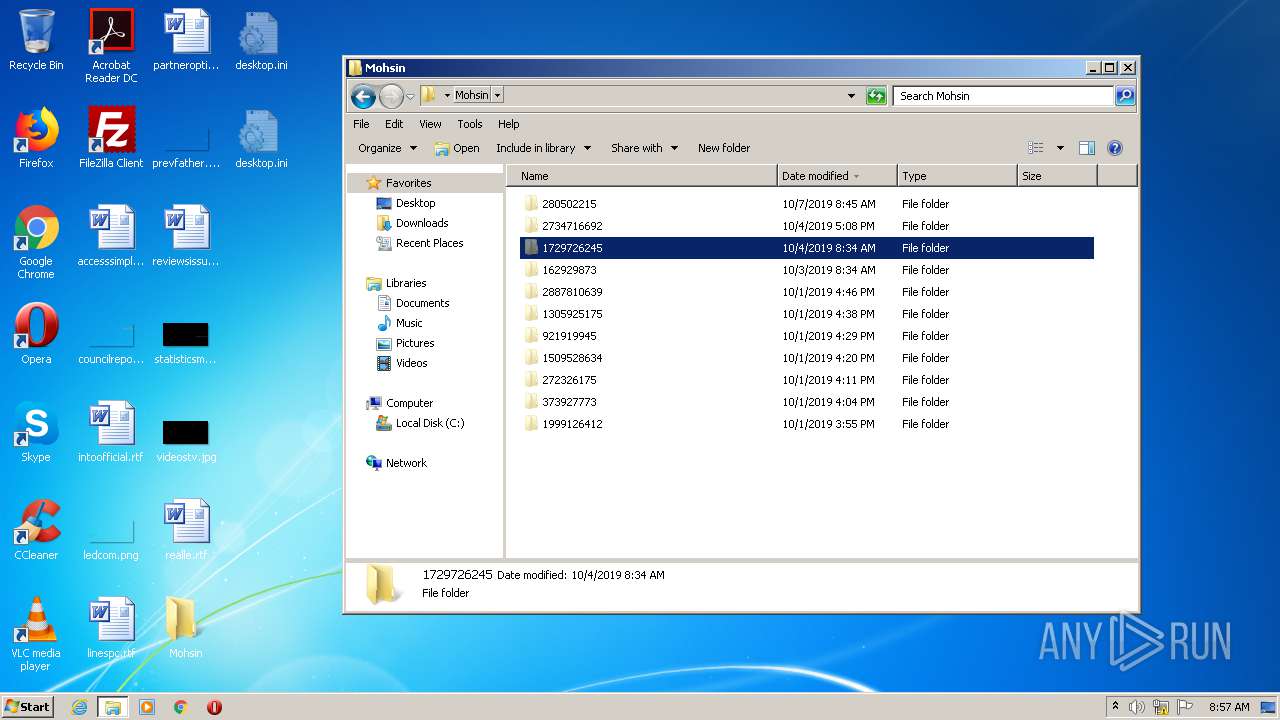
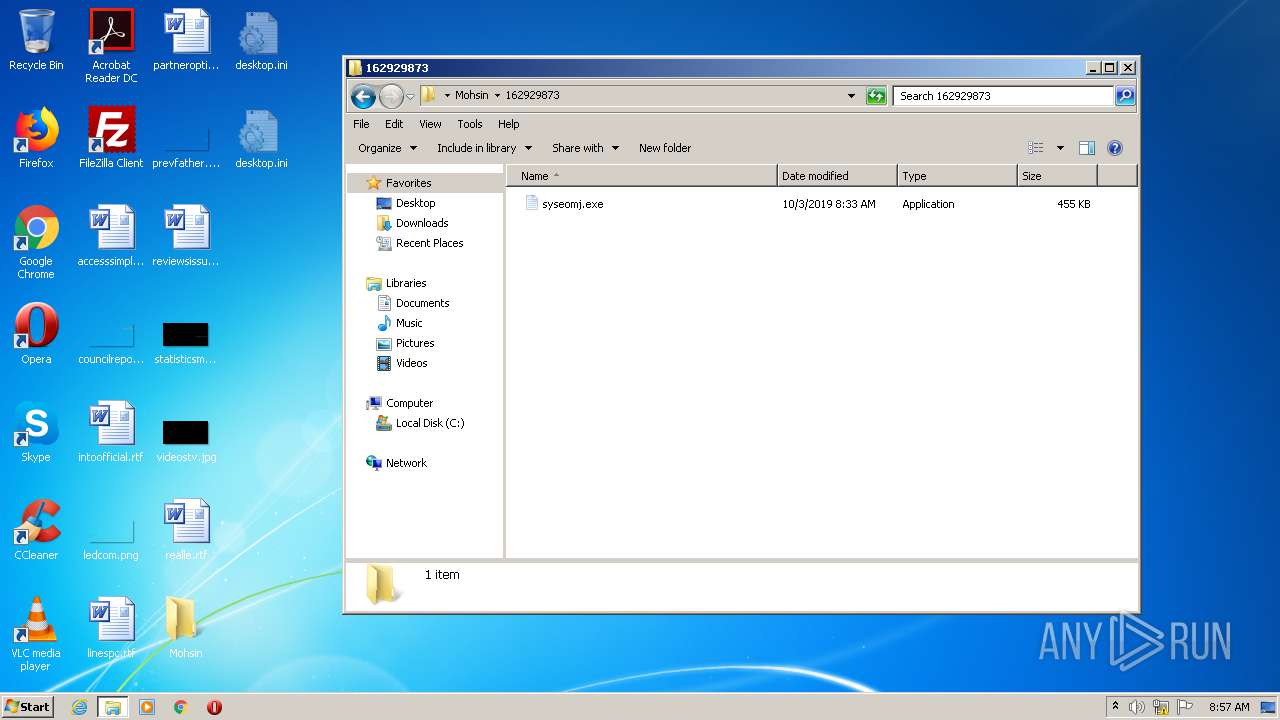
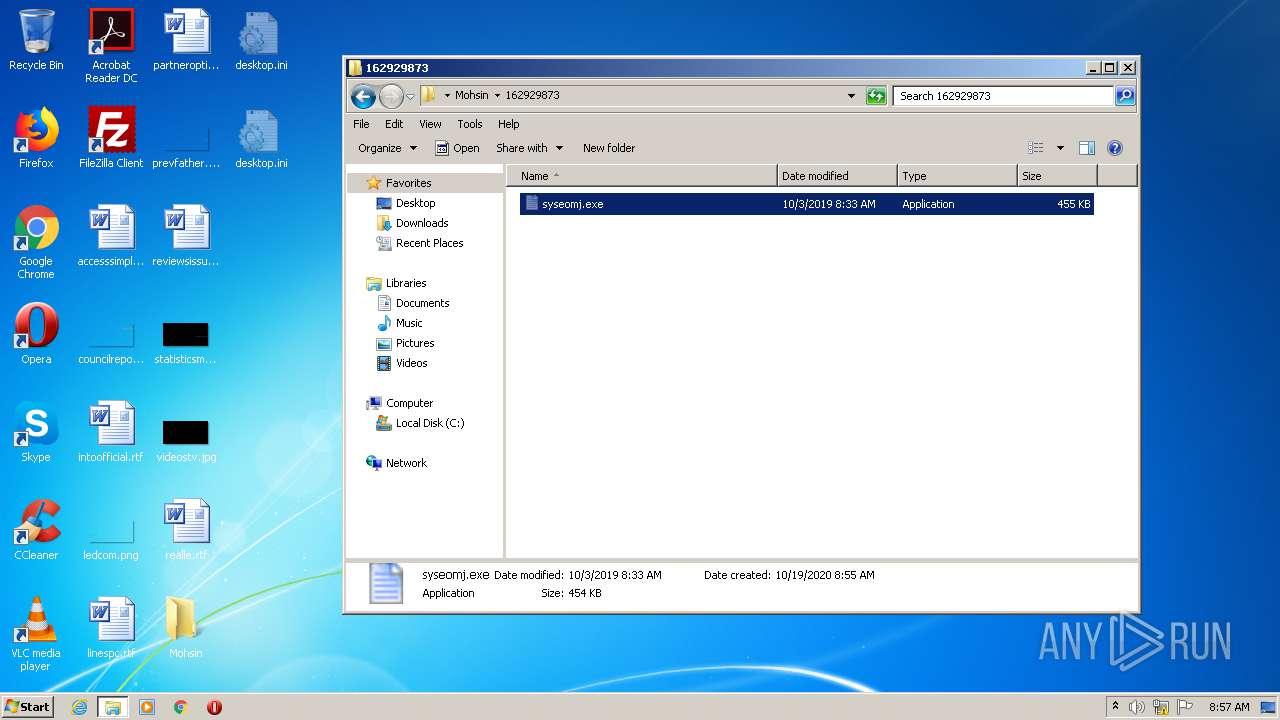
| 2028 | "C:\Users\admin\Desktop\Mohsin\162929873\syseomj.exe" | C:\Users\admin\Desktop\Mohsin\162929873\syseomj.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Ocydina Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
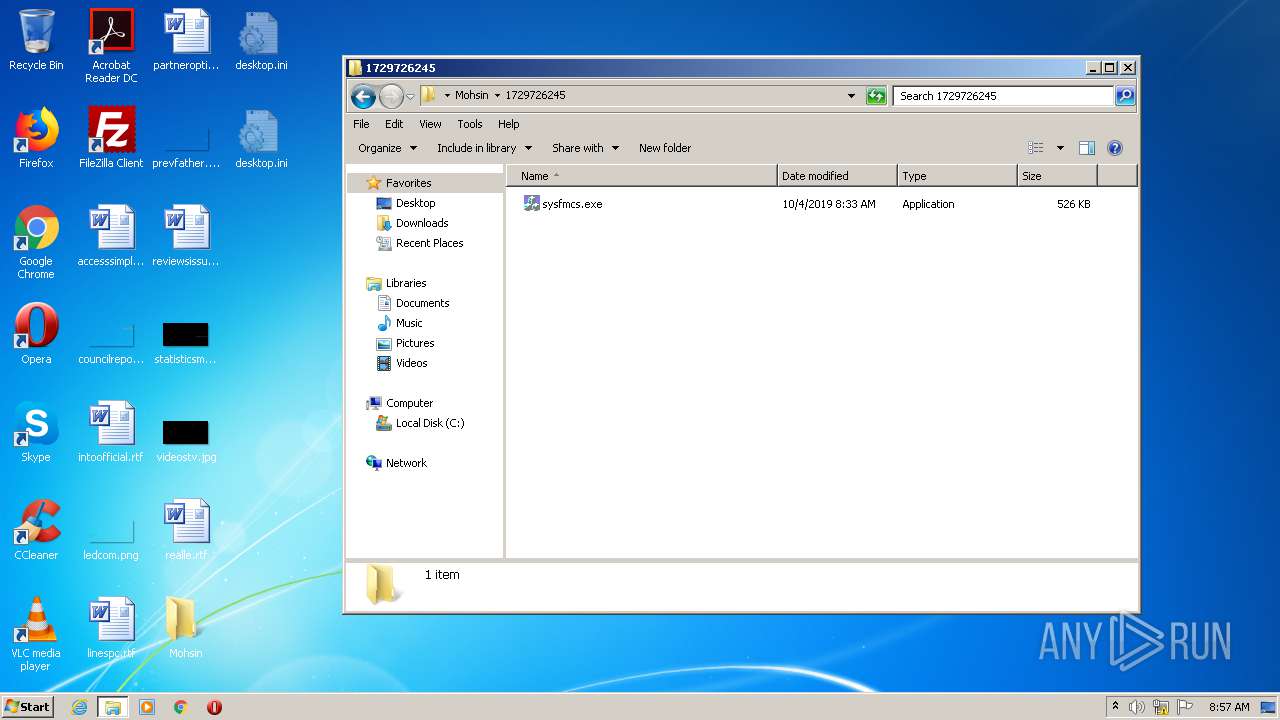
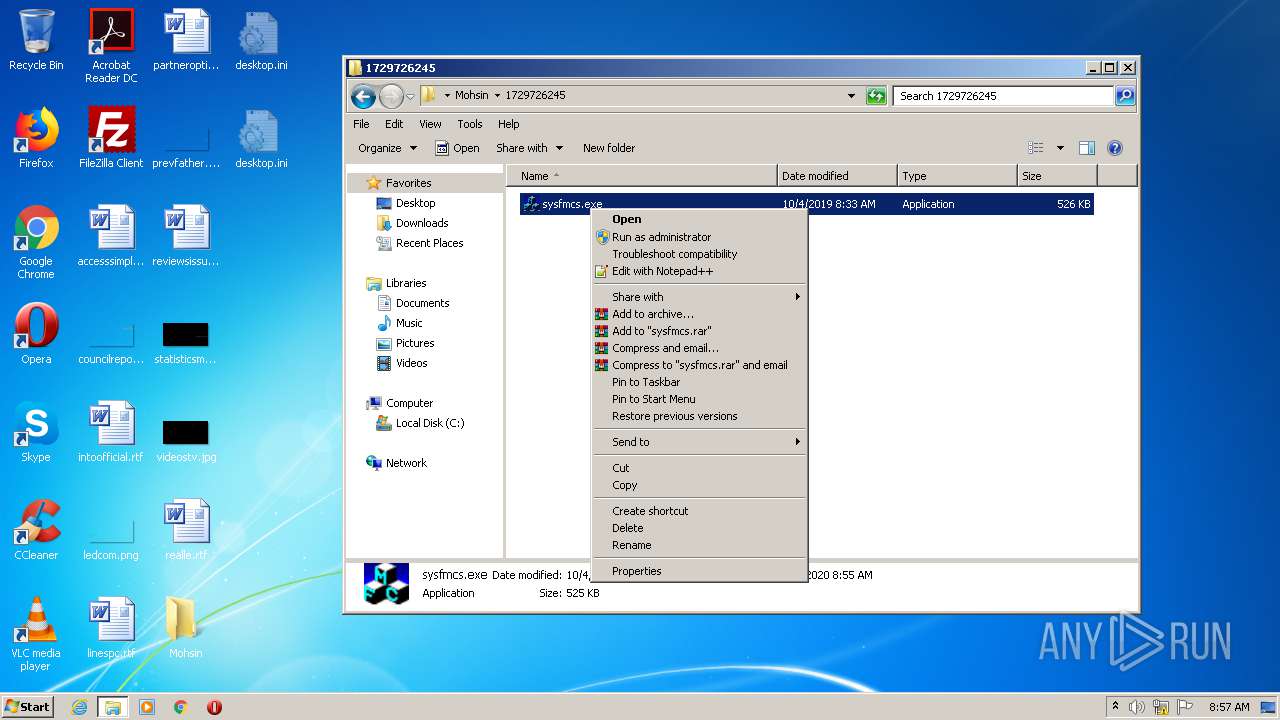
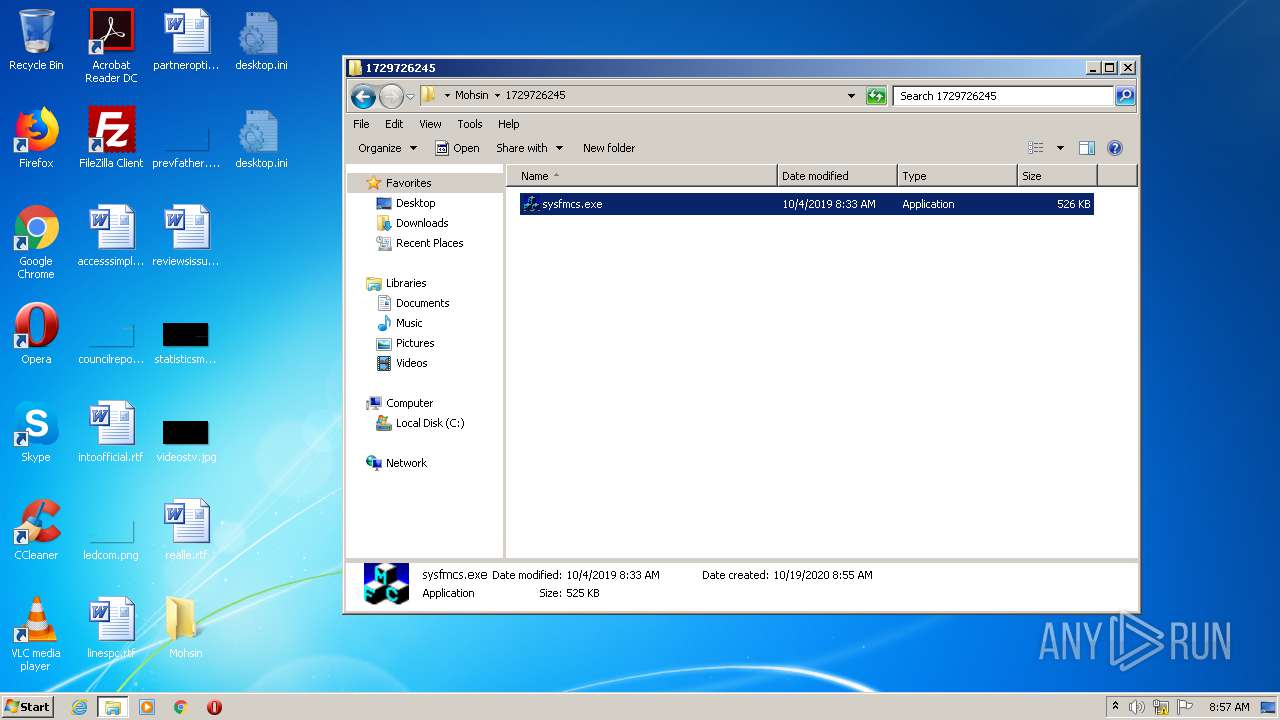
| 2076 | "C:\Users\admin\Desktop\Mohsin\1729726245\sysfmcs.exe" | C:\Users\admin\Desktop\Mohsin\1729726245\sysfmcs.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: GlowEffect MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
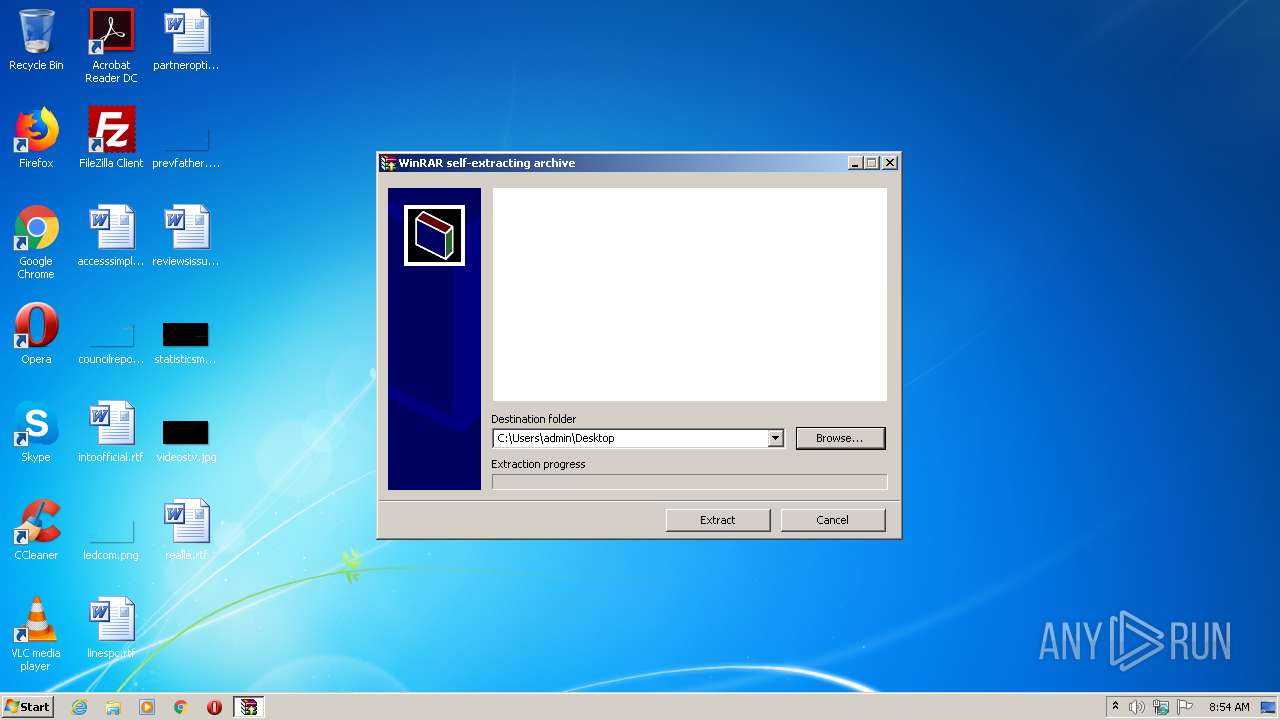
| 2504 | "C:\Users\admin\AppData\Local\Temp\TEST Sample.exe" | C:\Users\admin\AppData\Local\Temp\TEST Sample.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
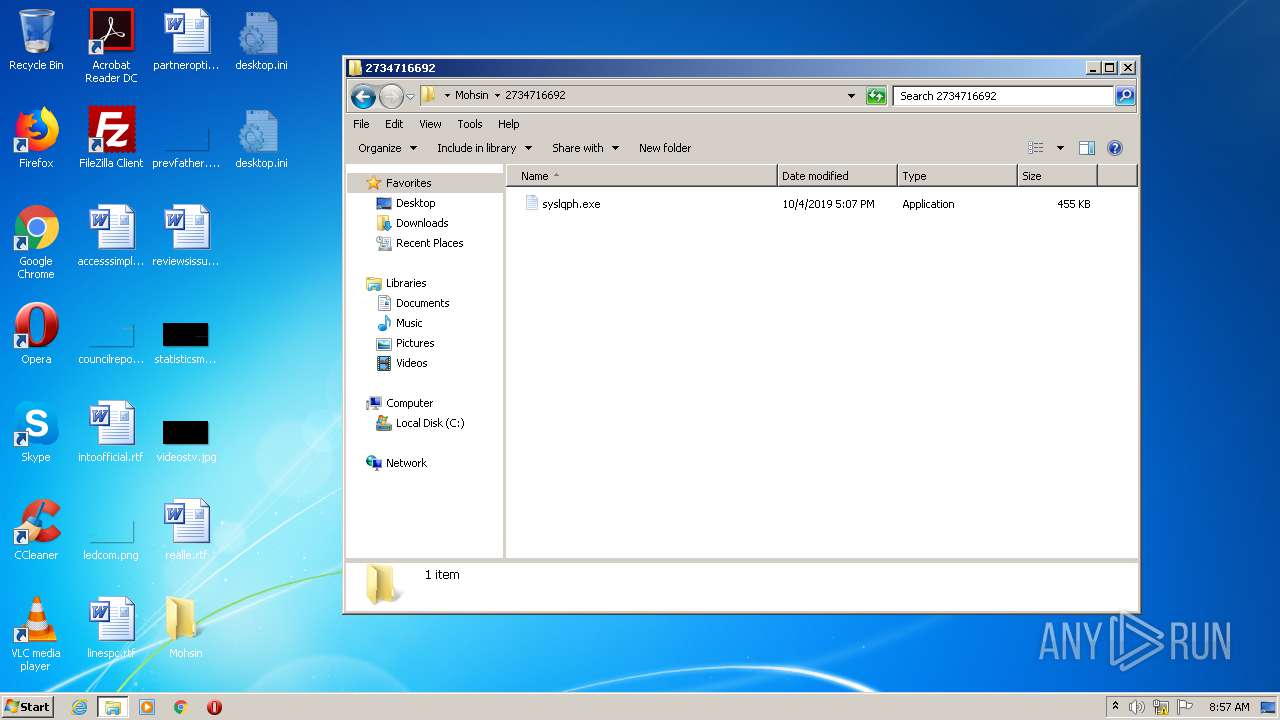
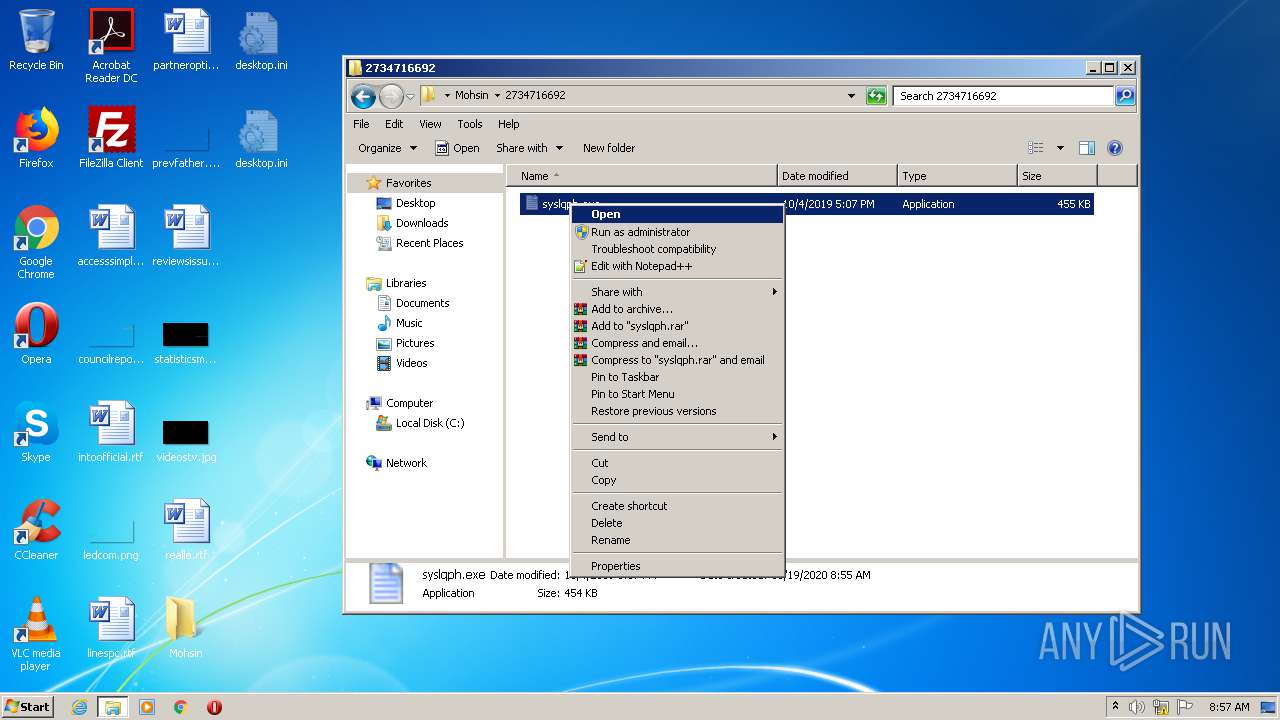
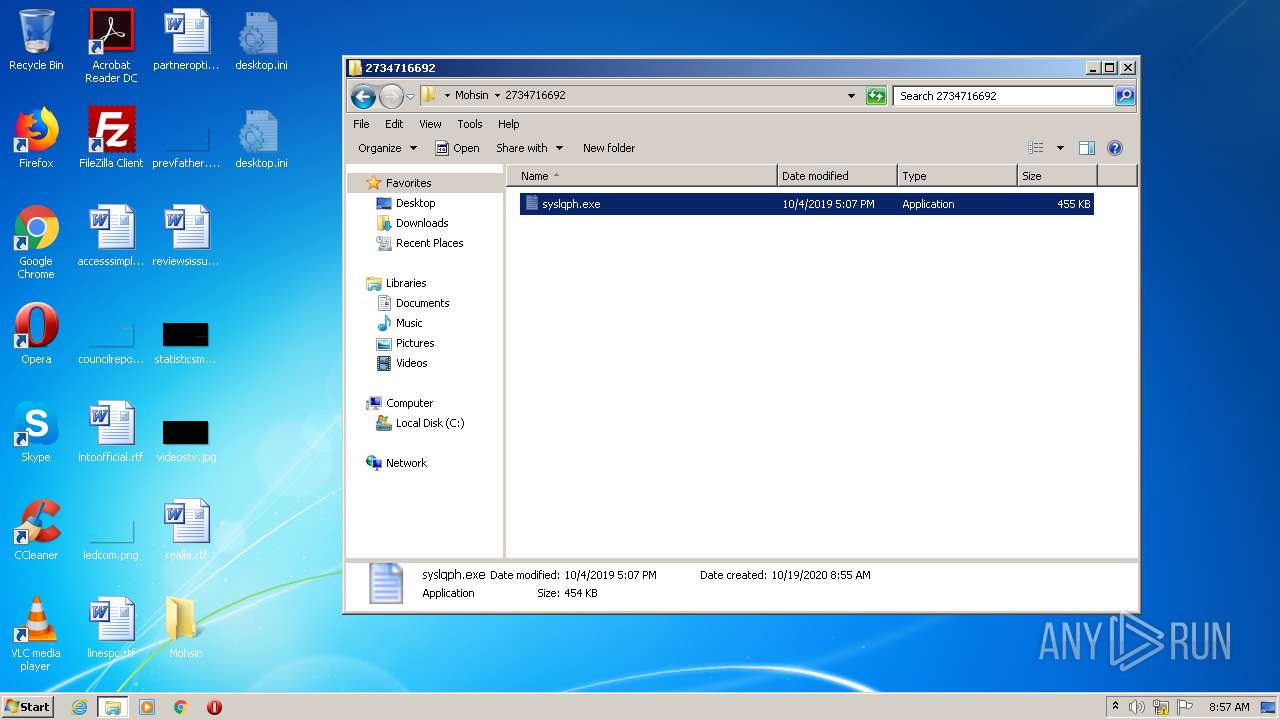
| 3448 | "C:\Users\admin\Desktop\Mohsin\2734716692\syslqph.exe" | C:\Users\admin\Desktop\Mohsin\2734716692\syslqph.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Ocydina Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
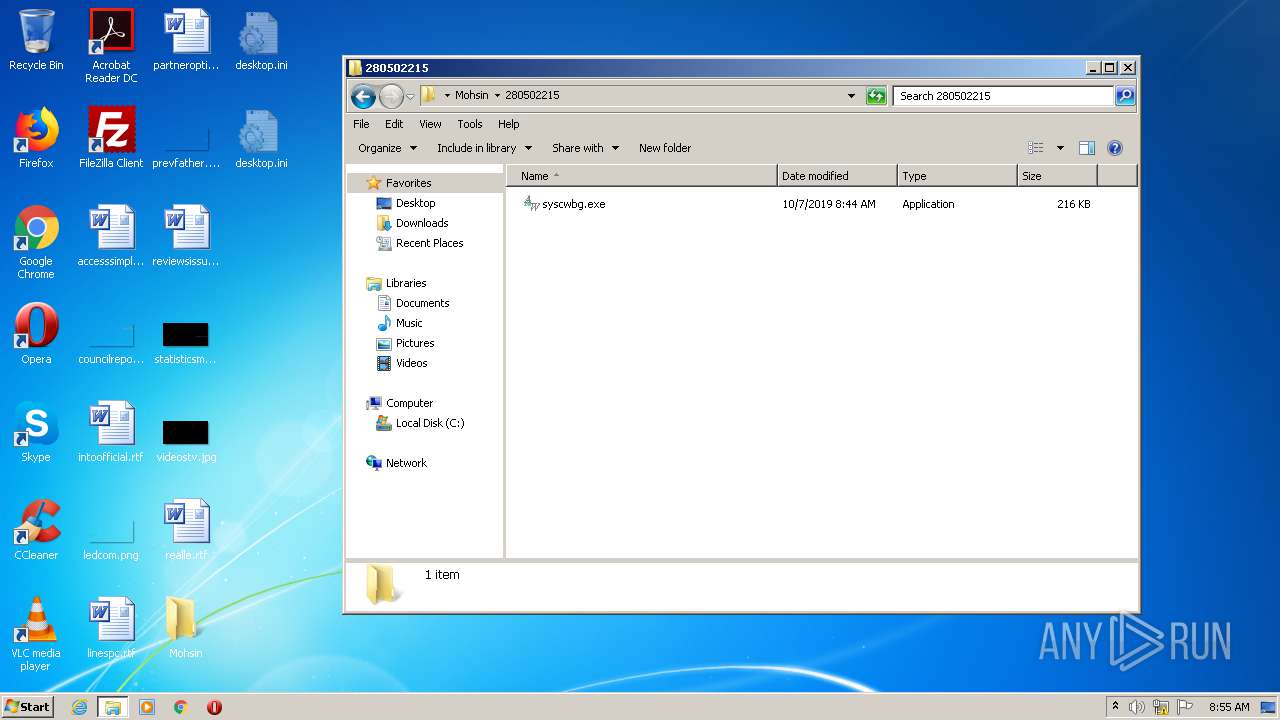
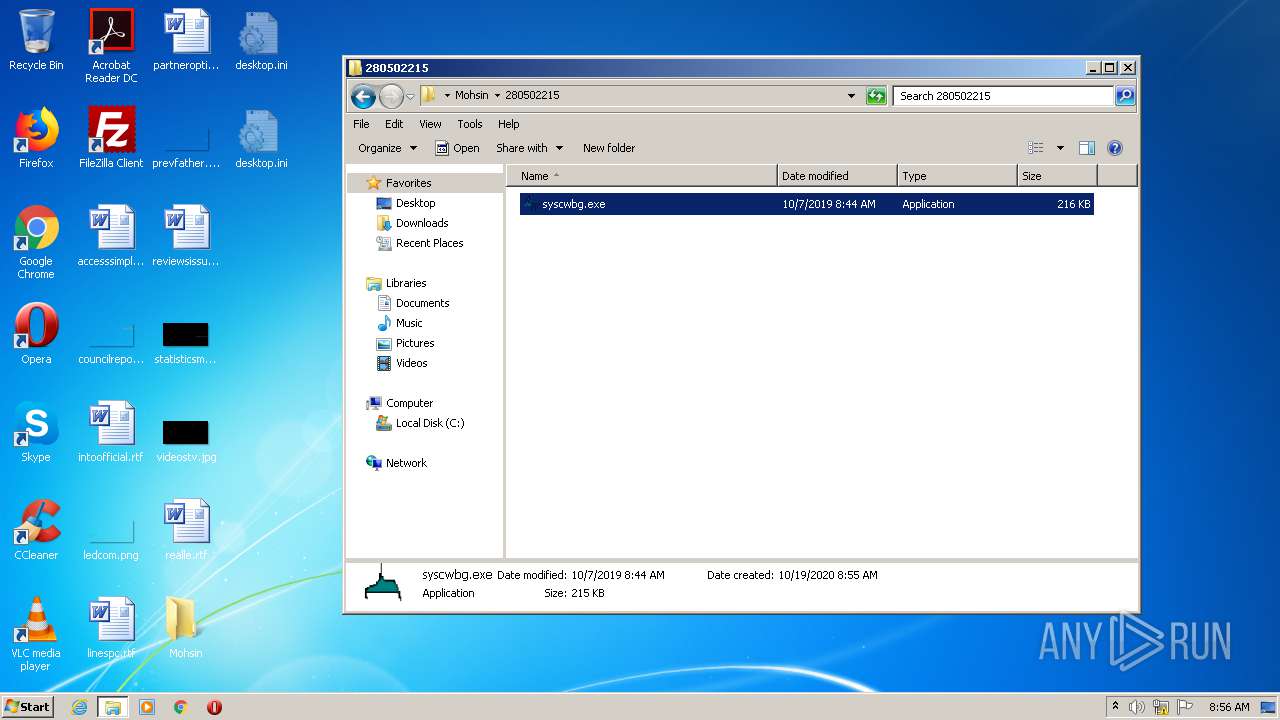
| 3604 | "C:\Users\admin\Desktop\Mohsin\280502215\syscwbg.exe" | C:\Users\admin\Desktop\Mohsin\280502215\syscwbg.exe | explorer.exe | ||||||||||||
User: admin Company: Ruksun Software Technologies Integrity Level: HIGH Description: AutoWallPaper Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
630
Read events
552
Write events
78
Delete events
0
Modification events
| (PID) Process: | (2504) TEST Sample.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2504) TEST Sample.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2504) TEST Sample.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2504) TEST Sample.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2504) TEST Sample.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2504) TEST Sample.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
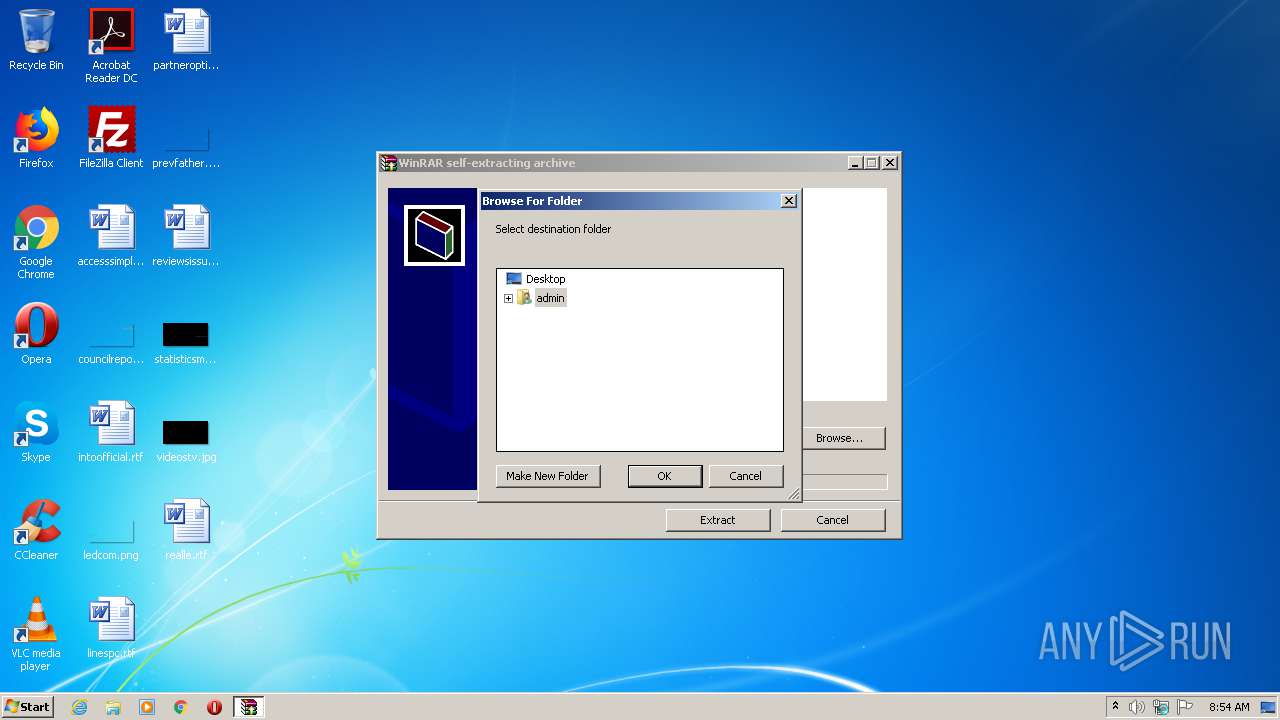
| (PID) Process: | (2504) TEST Sample.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (2504) TEST Sample.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
| (PID) Process: | (2504) TEST Sample.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-2 |
Value: Access the computers and devices that are on your network. | |||
| (PID) Process: | (3604) syscwbg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
Executable files
11
Suspicious files
0
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
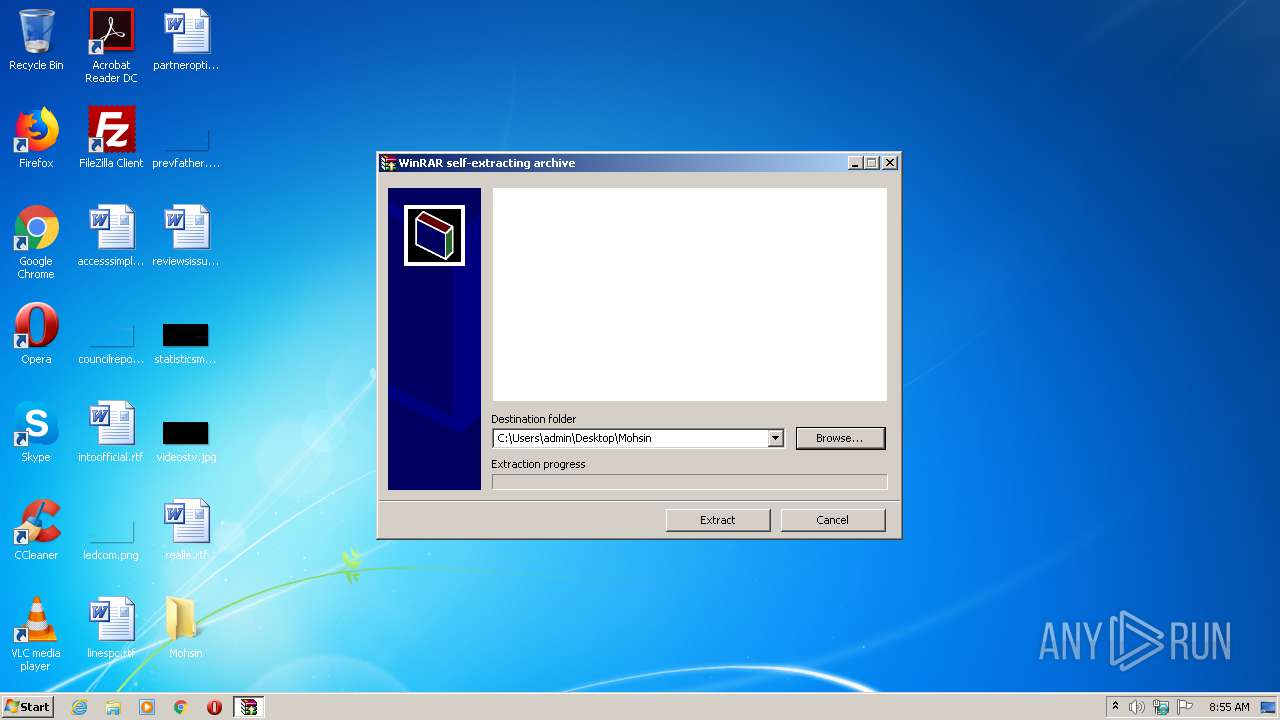
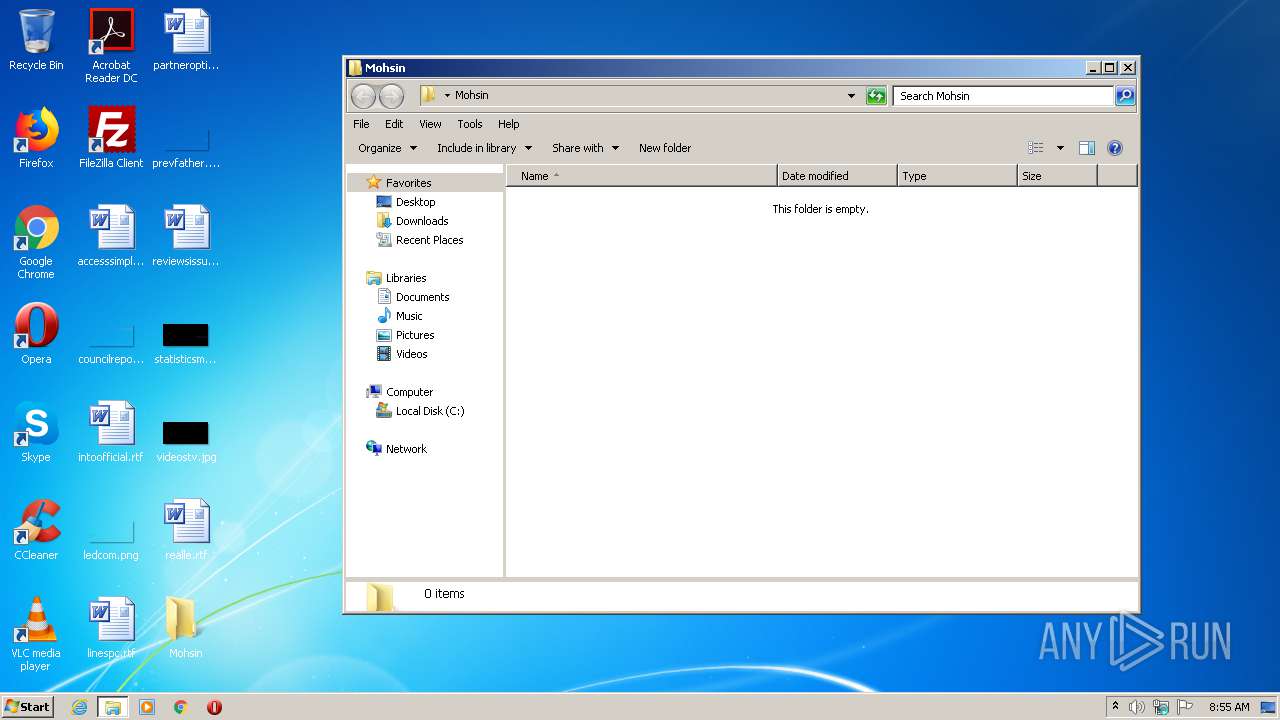
| 2504 | TEST Sample.exe | C:\Users\admin\Desktop\Mohsin | — | |
MD5:— | SHA256:— | |||
| 3604 | syscwbg.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\8ABX89FZ.txt | — | |
MD5:— | SHA256:— | |||
| 2504 | TEST Sample.exe | C:\Users\admin\Desktop\Mohsin\162929873\syseomj.exe | executable | |
MD5:— | SHA256:— | |||
| 2504 | TEST Sample.exe | C:\Users\admin\Desktop\Mohsin\2734716692\syslqph.exe | executable | |
MD5:— | SHA256:— | |||
| 2504 | TEST Sample.exe | C:\Users\admin\Desktop\Mohsin\280502215\syscwbg.exe | executable | |
MD5:AB97F71125A89D4D3D0855B8A419D3E1 | SHA256:F4909C420E208E4728116E8B0F4254C9F741D864F9618CDDBE3F51B71F602066 | |||
| 3604 | syscwbg.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\G84S2KPN.txt | text | |
MD5:— | SHA256:— | |||
| 3604 | syscwbg.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\8F0GUHOQ.txt | text | |
MD5:— | SHA256:— | |||
| 2504 | TEST Sample.exe | C:\Users\admin\Desktop\Mohsin\1729726245\sysfmcs.exe | executable | |
MD5:— | SHA256:— | |||
| 3604 | syscwbg.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\QGGUSKBL.txt | text | |
MD5:— | SHA256:— | |||
| 3604 | syscwbg.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\RMDHEZ6R.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
32
DNS requests
120
Threats
82
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3604 | syscwbg.exe | GET | — | 195.22.26.248:80 | http://befaheaiudeuhughgh.co/t.php?new=1 | PT | — | — | whitelisted |
3604 | syscwbg.exe | GET | — | 195.22.26.248:80 | http://daedagheauehfuuhfd.io/t.php?new=1 | PT | — | — | whitelisted |
3604 | syscwbg.exe | GET | — | 195.22.26.248:80 | http://gaoheeuofhefefhutd.io/t.php?new=1 | PT | — | — | whitelisted |
3604 | syscwbg.exe | GET | 200 | 107.6.74.76:80 | http://afaeigaifgsgrhhafd.io/t.php?new=1 | US | — | — | malicious |
3604 | syscwbg.exe | GET | — | 195.22.26.248:80 | http://bfagzzezgaegzgfaih.co/t.php?new=1 | PT | — | — | whitelisted |
3604 | syscwbg.exe | GET | — | 195.22.26.248:80 | http://eaeuafhuaegfugeudh.co/t.php?new=1 | PT | — | — | whitelisted |
3604 | syscwbg.exe | GET | — | 185.176.27.132:80 | http://185.176.27.132/2 | GB | — | — | malicious |
3604 | syscwbg.exe | GET | — | 185.176.27.132:80 | http://185.176.27.132/3 | GB | — | — | malicious |
3604 | syscwbg.exe | GET | — | 185.176.27.132:80 | http://185.176.27.132/1 | GB | — | — | malicious |
3604 | syscwbg.exe | GET | — | 195.22.26.248:80 | http://aeoughaoheguaoehdd.io/t.php?new=1 | PT | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3604 | syscwbg.exe | 195.22.26.248:80 | daedagheauehfuuhfd.io | Claranet Ltd | PT | malicious |
3604 | syscwbg.exe | 185.176.27.132:80 | — | — | GB | malicious |
3604 | syscwbg.exe | 208.100.26.245:80 | rzhsudhugugfugugsh.co | Steadfast | US | malicious |
3604 | syscwbg.exe | 52.4.209.250:80 | geauhouefheuutiiiw.top | Amazon.com, Inc. | US | malicious |
3448 | syslqph.exe | 185.176.27.132:80 | — | — | GB | malicious |
2076 | sysfmcs.exe | 185.176.27.132:80 | — | — | GB | malicious |
— | — | 185.176.27.132:80 | — | — | GB | malicious |
3604 | syscwbg.exe | 107.6.74.76:80 | afaeigaifgsgrhhafd.io | Voxel Dot Net, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
urusurofhsorhfuuhp.su |
| malicious |
aeifaeifhutuhuhusp.su |
| malicious |
rzhsudhugugfugugsp.su |
| malicious |
bfagzzezgaegzgfaip.su |
| malicious |
eaeuafhuaegfugeudp.su |
| malicious |
aeufuaehfiuehfuhfp.su |
| malicious |
daedagheauehfuuhfp.su |
| malicious |
aeoughaoheguaoehdp.su |
| malicious |
eguaheoghouughahsp.su |
| malicious |
huaeokaefoaeguaehp.su |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
3604 | syscwbg.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 24 |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
16 ETPRO signatures available at the full report