| File name: | 42a4aabdd58575f684b3bcf47947b9420931b5a90744e07080f39792ae2dca22 |
| Full analysis: | https://app.any.run/tasks/6c7f4719-49a3-4352-bbf3-858fd267093b |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | March 24, 2025, 15:23:20 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
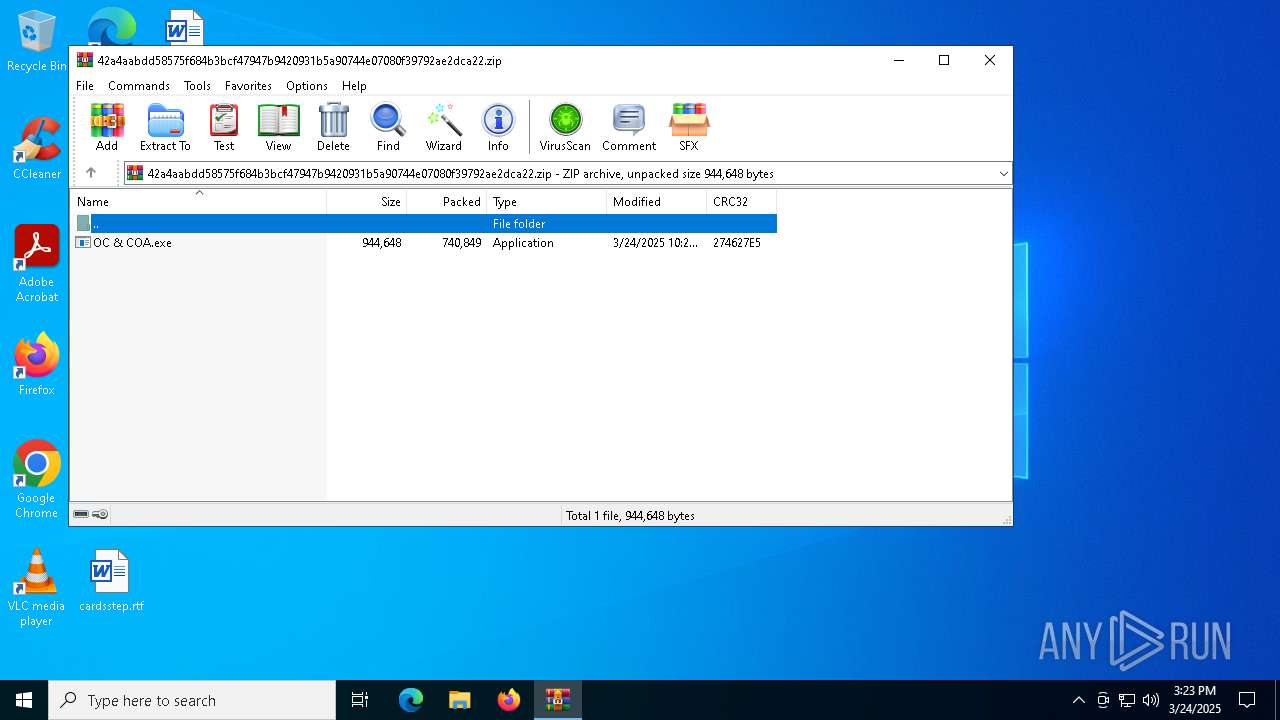
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 551242303F5C08A7488CBE2D6BCBA257 |
| SHA1: | EE7C705C3F27F7314DD2CF7517BB5F9B196899E5 |
| SHA256: | 42A4AABDD58575F684B3BCF47947B9420931B5A90744E07080F39792AE2DCA22 |
| SSDEEP: | 24576:bJ1fFtU1eTVbfTXDE4FeqiJkWWXtQ3m59q7qejFx74KM9WX4PCKlSaPSKbPDXFKt:bJ19tU1eTNfTXDE4FeqiJkWWdQ+9q7qq |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 5988)
Executing a file with an untrusted certificate
- OC & COA.exe (PID: 6644)
Steals credentials from Web Browsers
- RegSvcs.exe (PID: 5048)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 5048)
AGENTTESLA has been detected (YARA)
- RegSvcs.exe (PID: 5048)
SUSPICIOUS
Starts a Microsoft application from unusual location
- OC & COA.exe (PID: 6644)
Connects to SMTP port
- RegSvcs.exe (PID: 5048)
The process connected to a server suspected of theft
- RegSvcs.exe (PID: 5048)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5988)
Process drops legitimate windows executable
- WinRAR.exe (PID: 5988)
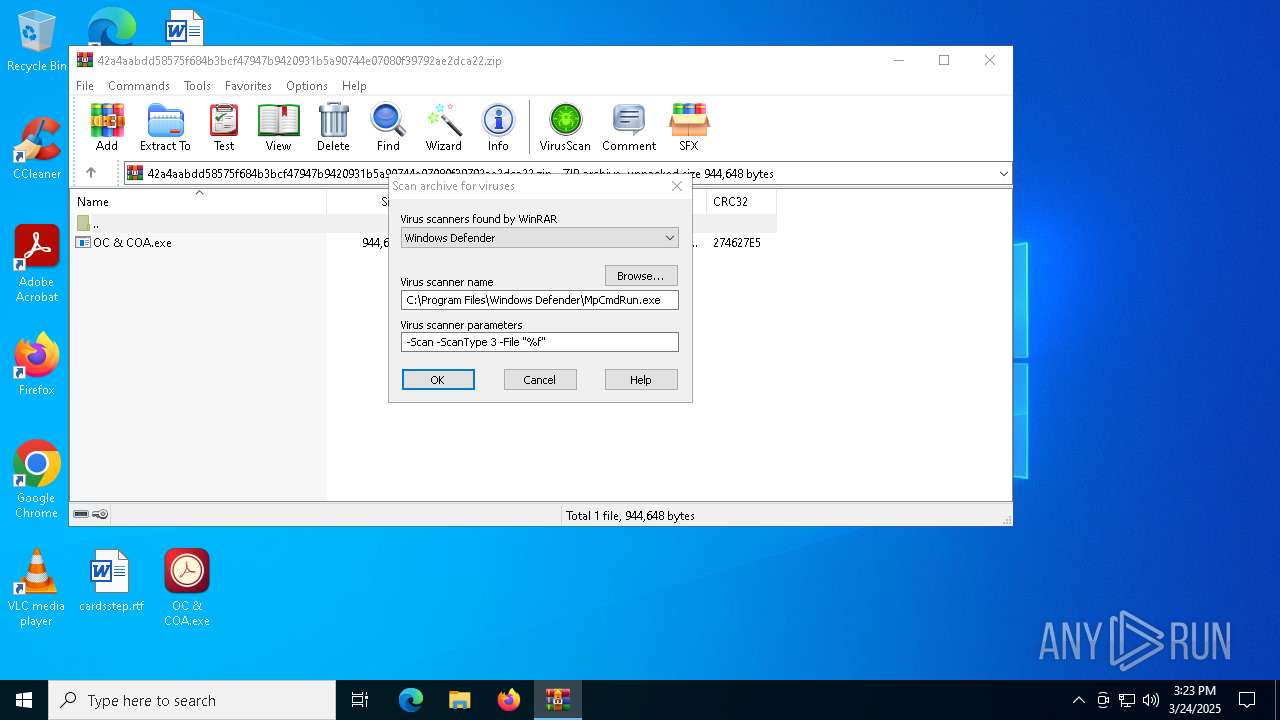
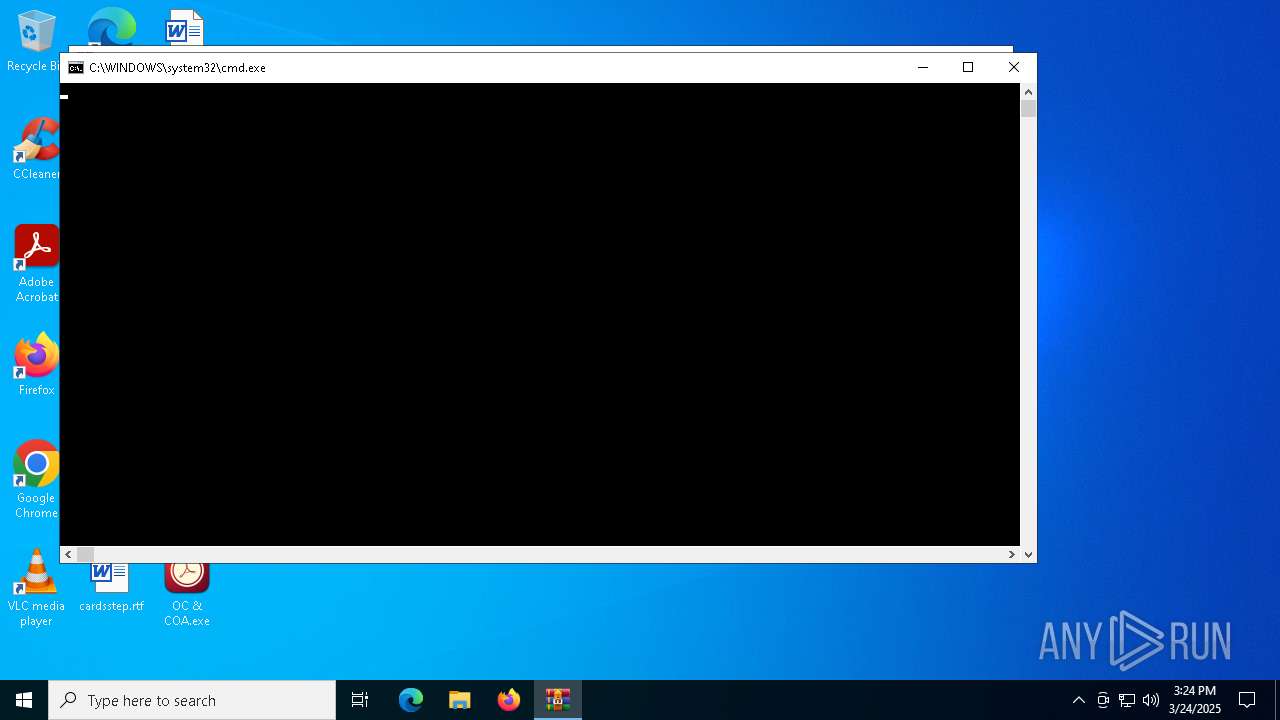
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 5988)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 5988)
INFO
Manual execution by a user
- OC & COA.exe (PID: 6644)
Checks supported languages
- OC & COA.exe (PID: 6644)
- RegSvcs.exe (PID: 5048)
- MpCmdRun.exe (PID: 6656)
Reads the machine GUID from the registry
- OC & COA.exe (PID: 6644)
- RegSvcs.exe (PID: 5048)
Reads the computer name
- OC & COA.exe (PID: 6644)
- RegSvcs.exe (PID: 5048)
- MpCmdRun.exe (PID: 6656)
Reads the software policy settings
- RegSvcs.exe (PID: 5048)
- slui.exe (PID: 6676)
ULTRAVNC has been detected
- RegSvcs.exe (PID: 5048)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5988)
Checks proxy server information
- slui.exe (PID: 6676)
Create files in a temporary directory
- MpCmdRun.exe (PID: 6656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:03:24 11:24:00 |
| ZipCRC: | 0x274627e5 |
| ZipCompressedSize: | 740849 |
| ZipUncompressedSize: | 944648 |
| ZipFileName: | OC & COA.exe |
Total processes
126
Monitored processes
8
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4200 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR5988.16059\Rar$Scan40106.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5048 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | OC & COA.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 5428 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5988 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\42a4aabdd58575f684b3bcf47947b9420931b5a90744e07080f39792ae2dca22.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6644 | "C:\Users\admin\Desktop\OC & COA.exe" | C:\Users\admin\Desktop\OC & COA.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Compatibility Database Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6656 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR5988.16059" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6676 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 029
Read events
6 020
Write events
9
Delete events
0
Modification events
| (PID) Process: | (5988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\42a4aabdd58575f684b3bcf47947b9420931b5a90744e07080f39792ae2dca22.zip | |||
| (PID) Process: | (5988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6656 | MpCmdRun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | text | |
MD5:037BF08D64842D36CAC964DF4DE9B02B | SHA256:86A39367CF072CEDABAD47752D92D2A1D4DADFF09DB91F9DE3591E63146AA708 | |||
| 5988 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR5988.16059\42a4aabdd58575f684b3bcf47947b9420931b5a90744e07080f39792ae2dca22.zip\OC & COA.exe | executable | |
MD5:1FA4A5C689DE43891A6FC6749C8B8A03 | SHA256:D4AE7E790E777630F32CACB8B2975A478A7058F1E19010BB5F2D7E389ED64B40 | |||
| 5988 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR5988.16059\Rar$Scan40106.bat | text | |
MD5:9B7952715C58024C4E153A6CC0F3AD9B | SHA256:CB20CEE3305C3C9AE984F6627F0D2FD2E1BE4E1C21404DE340E19D9D4F2B18CB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
21
DNS requests
4
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5048 | RegSvcs.exe | 194.36.191.196:587 | mail.agaliofu.top | Host Sailor Ltd | NL | malicious |
2284 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6676 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
mail.agaliofu.top |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
5048 | RegSvcs.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via SMTP |