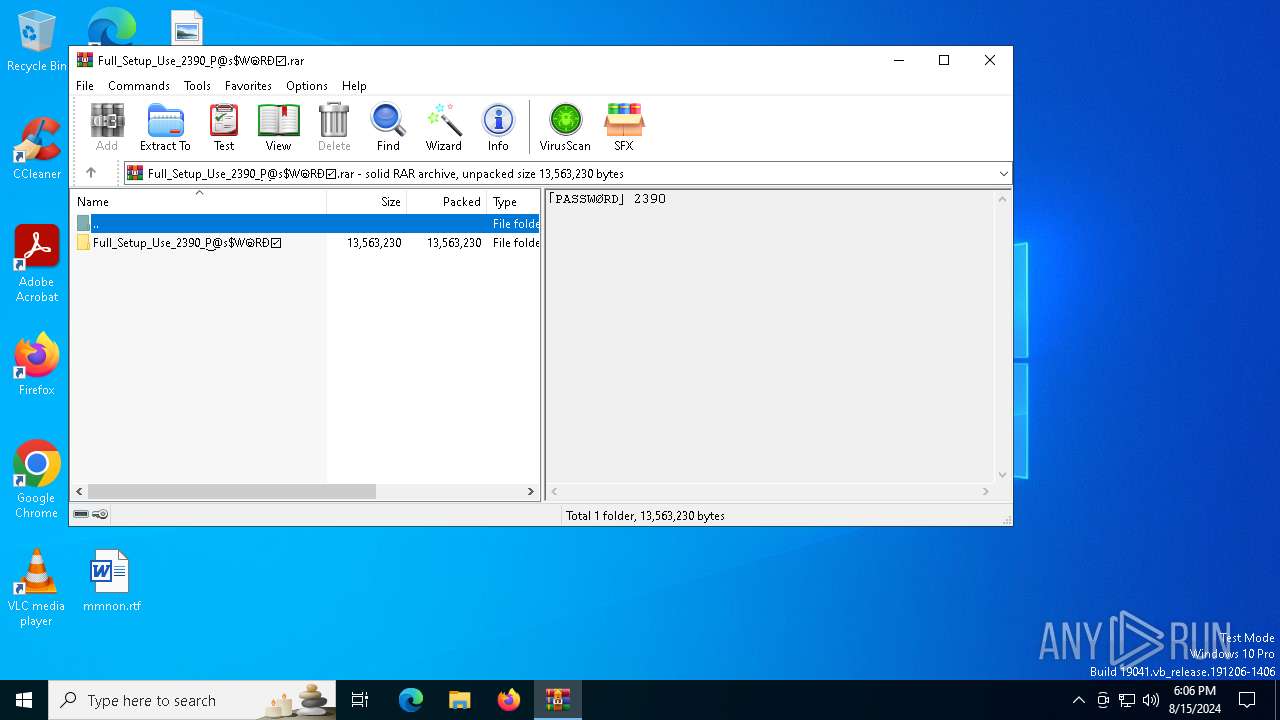
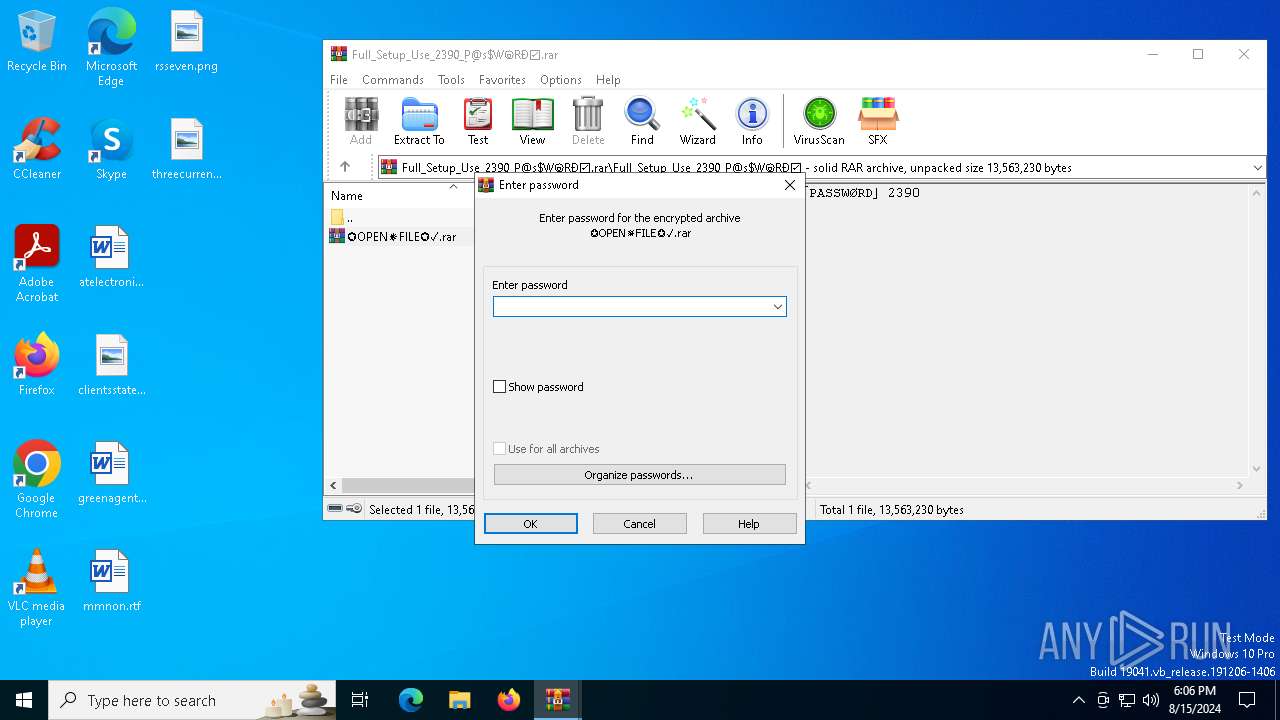
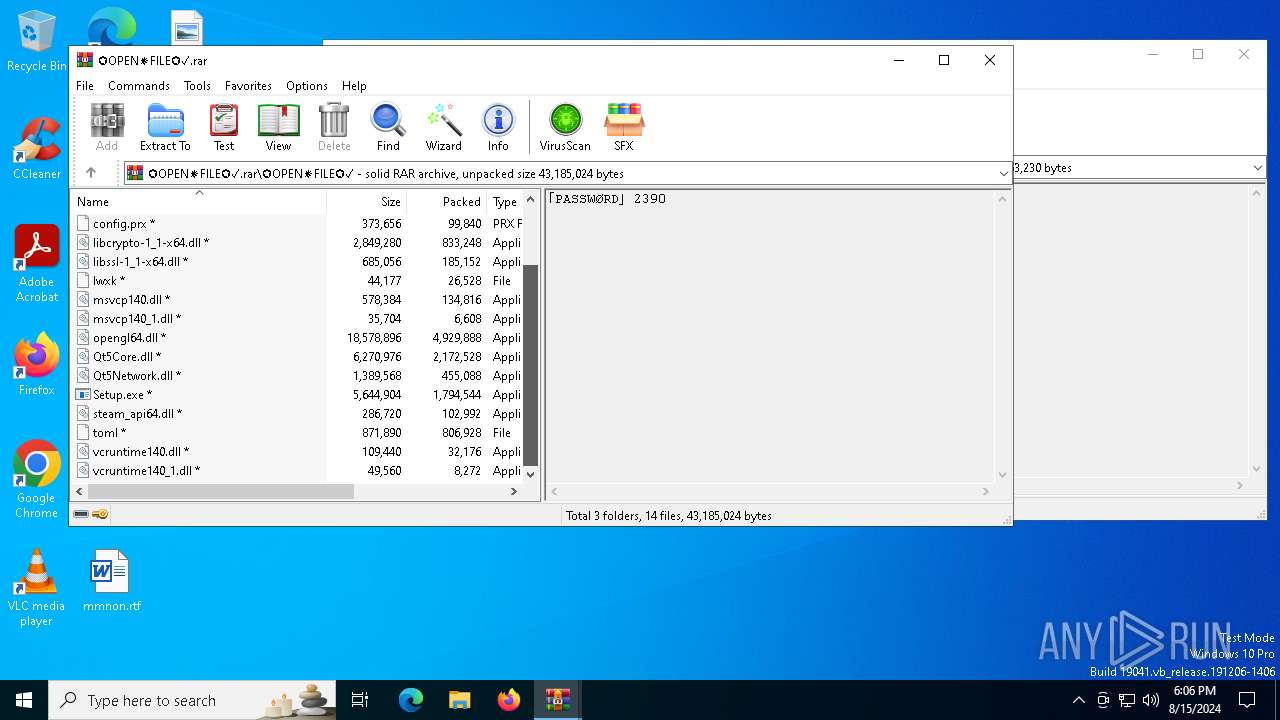
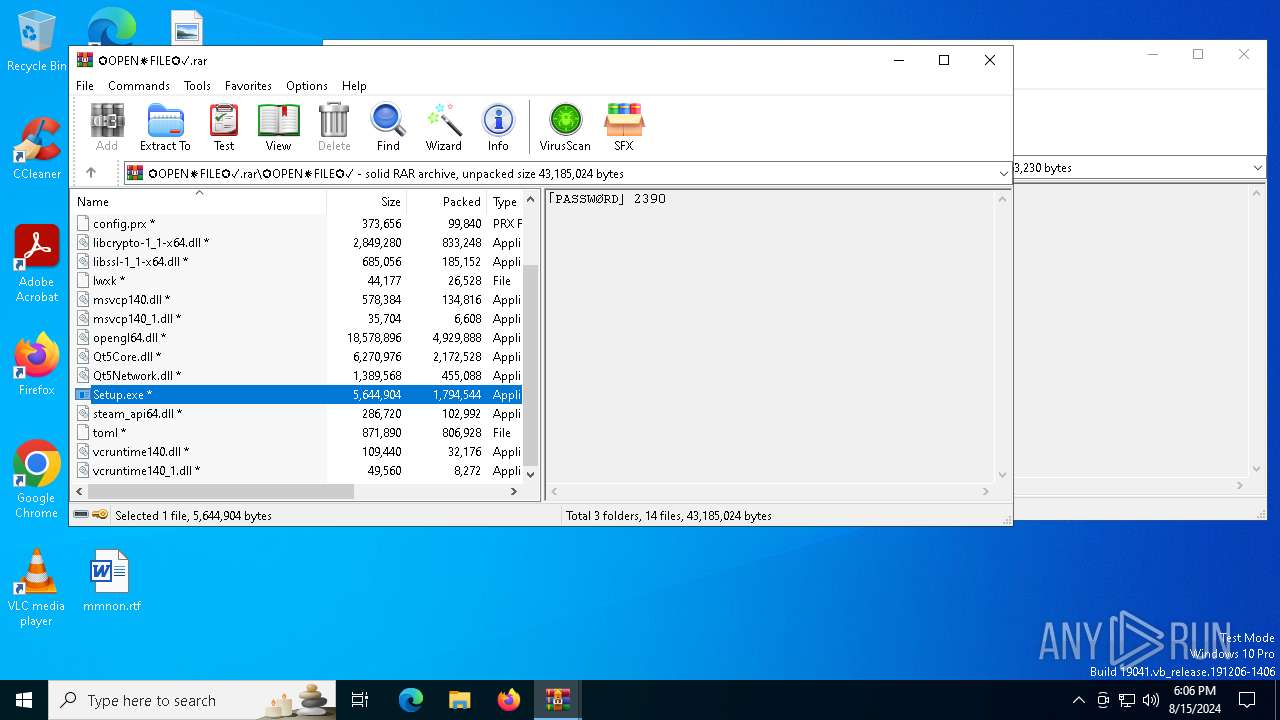
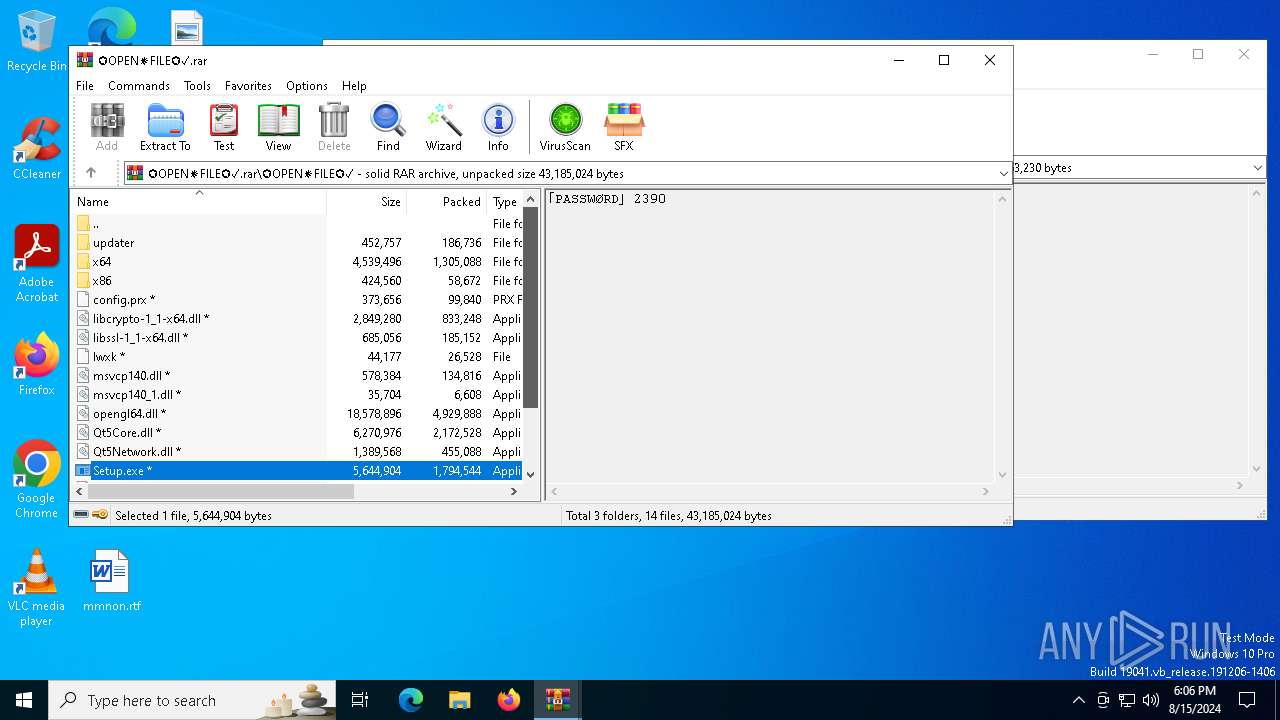
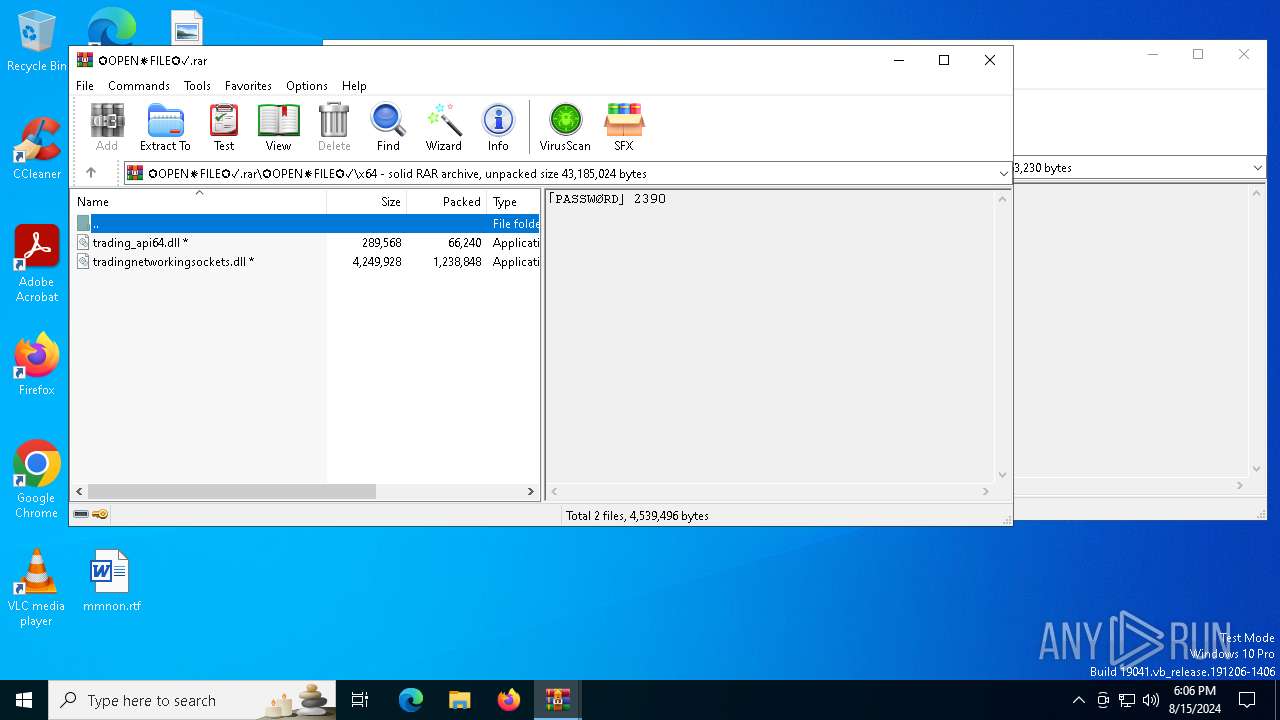
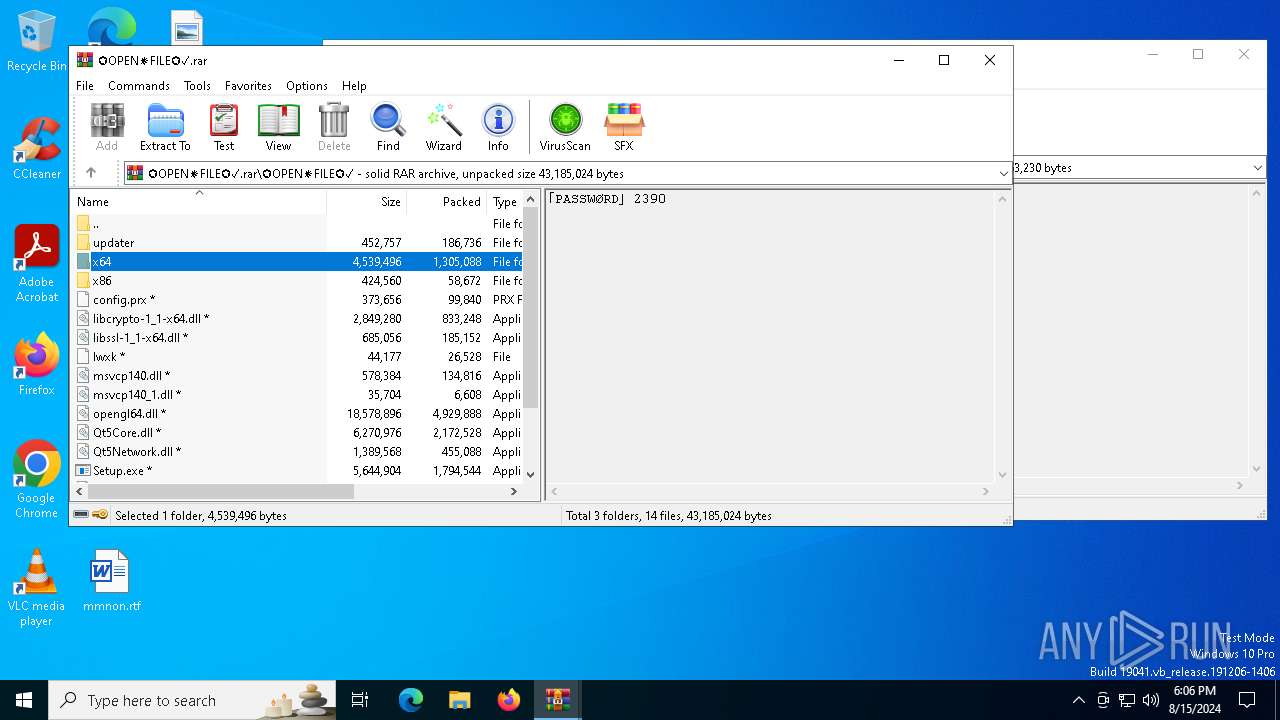
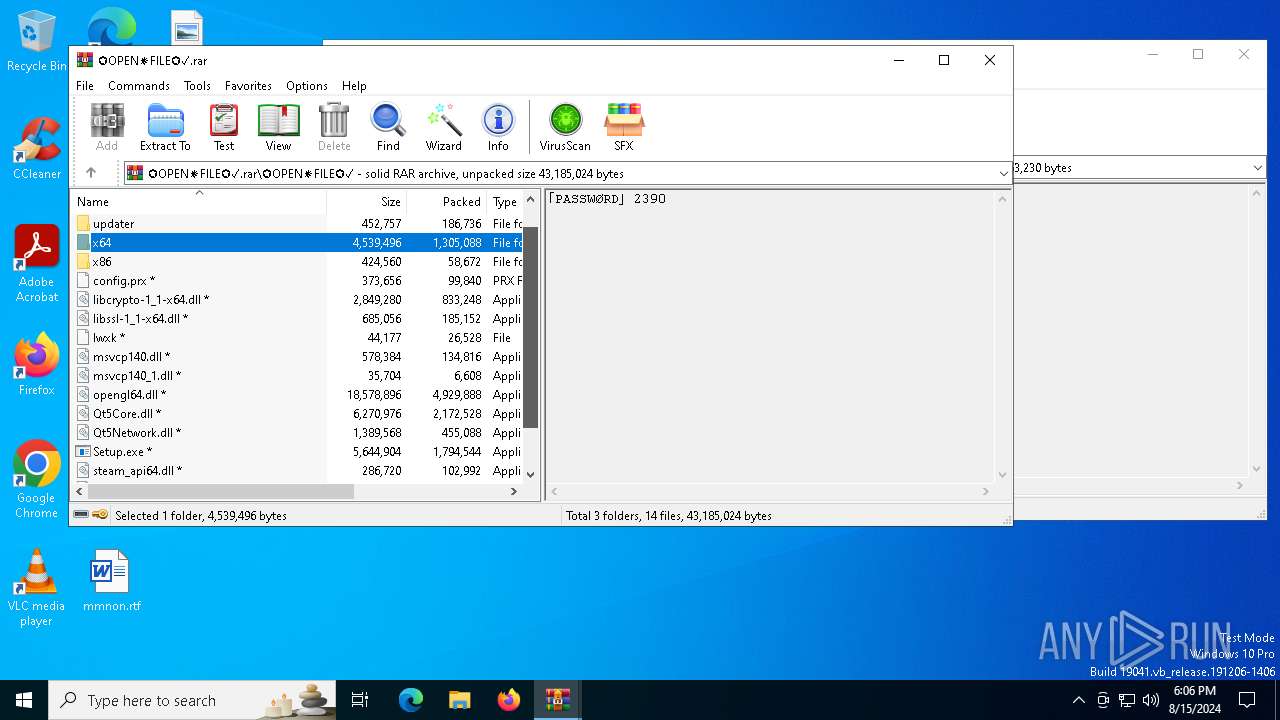
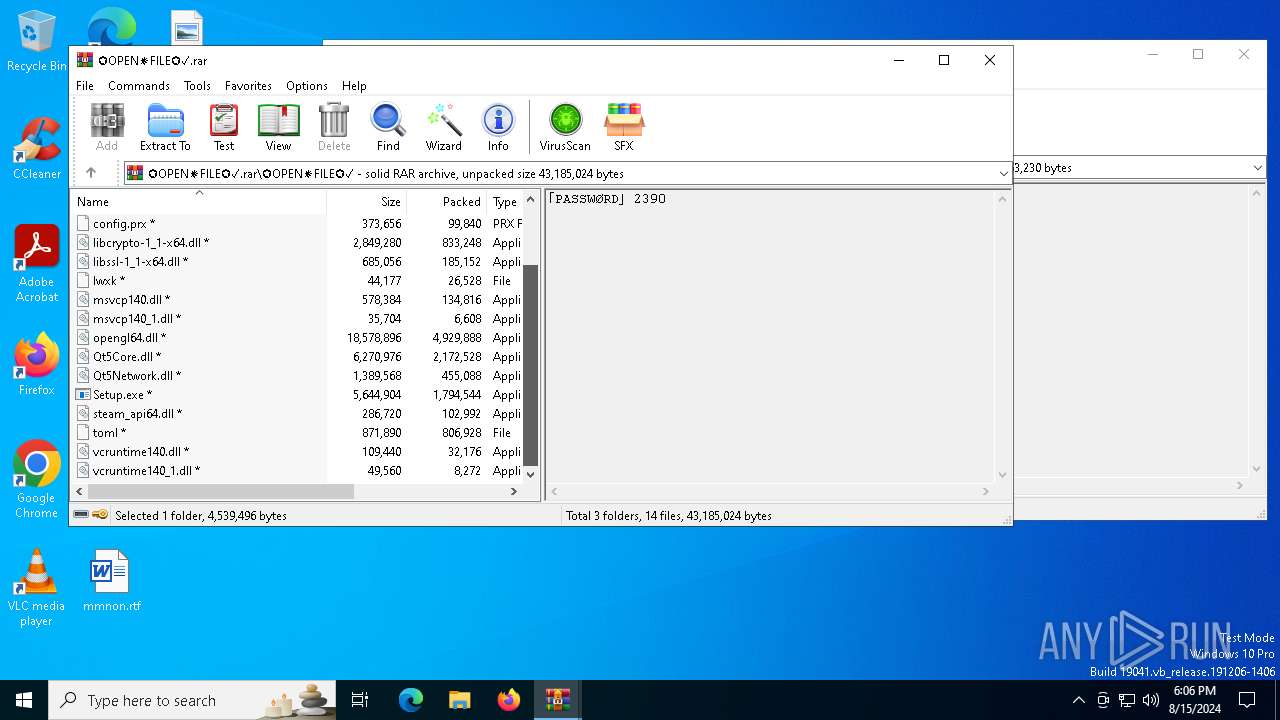
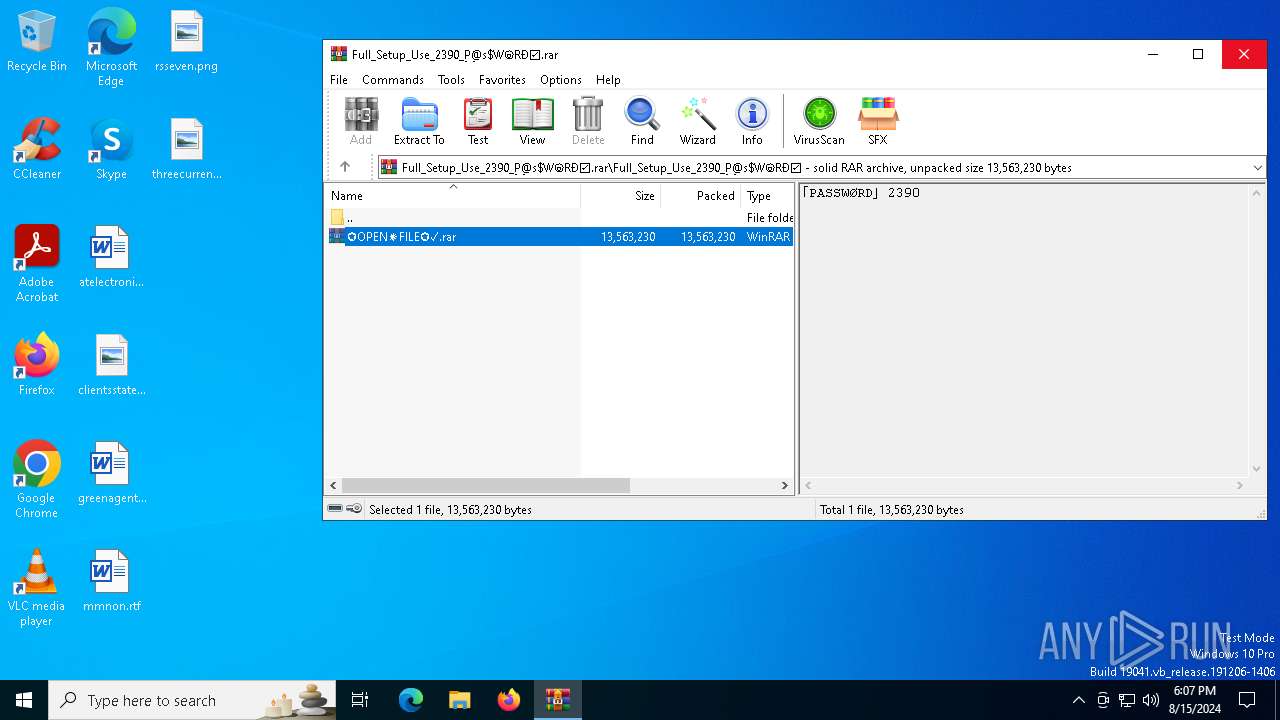
| File name: | Full_Setup_Use_2390_P͜@s$WⓞRÐ☑.rar |
| Full analysis: | https://app.any.run/tasks/cf8f29e3-e61b-4335-bc62-8ce1450c6263 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | August 15, 2024, 18:05:51 |
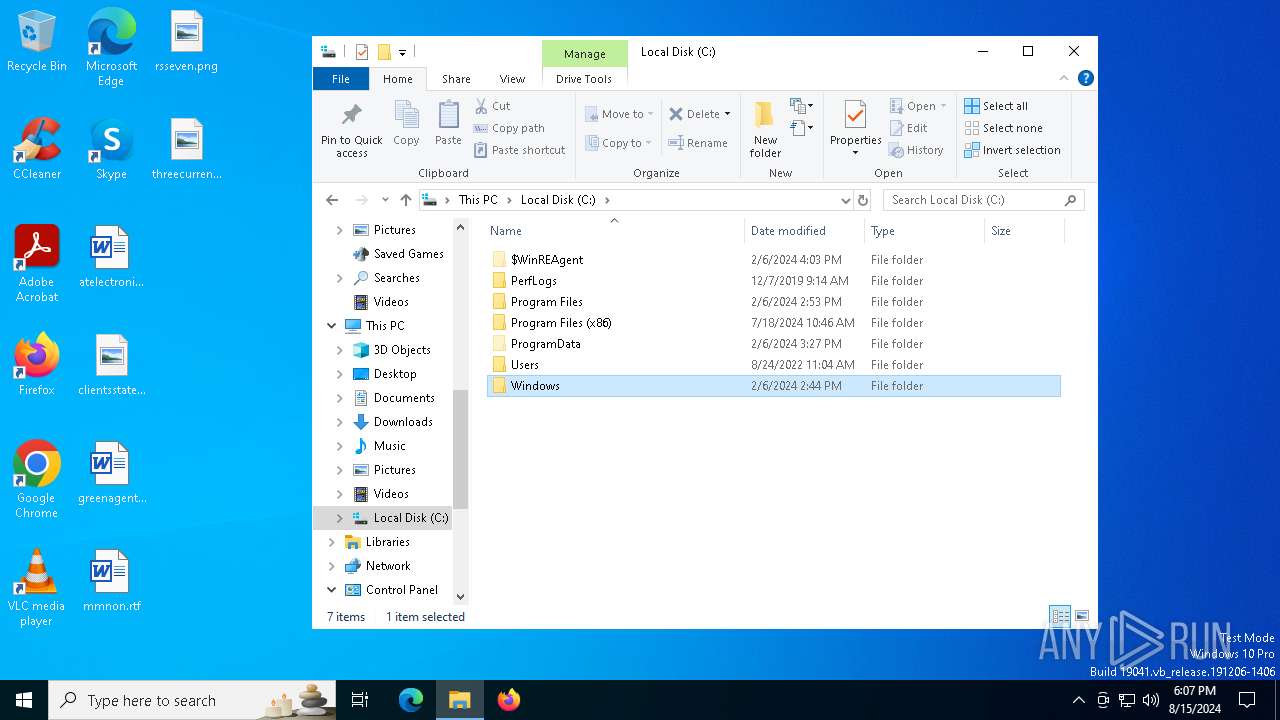
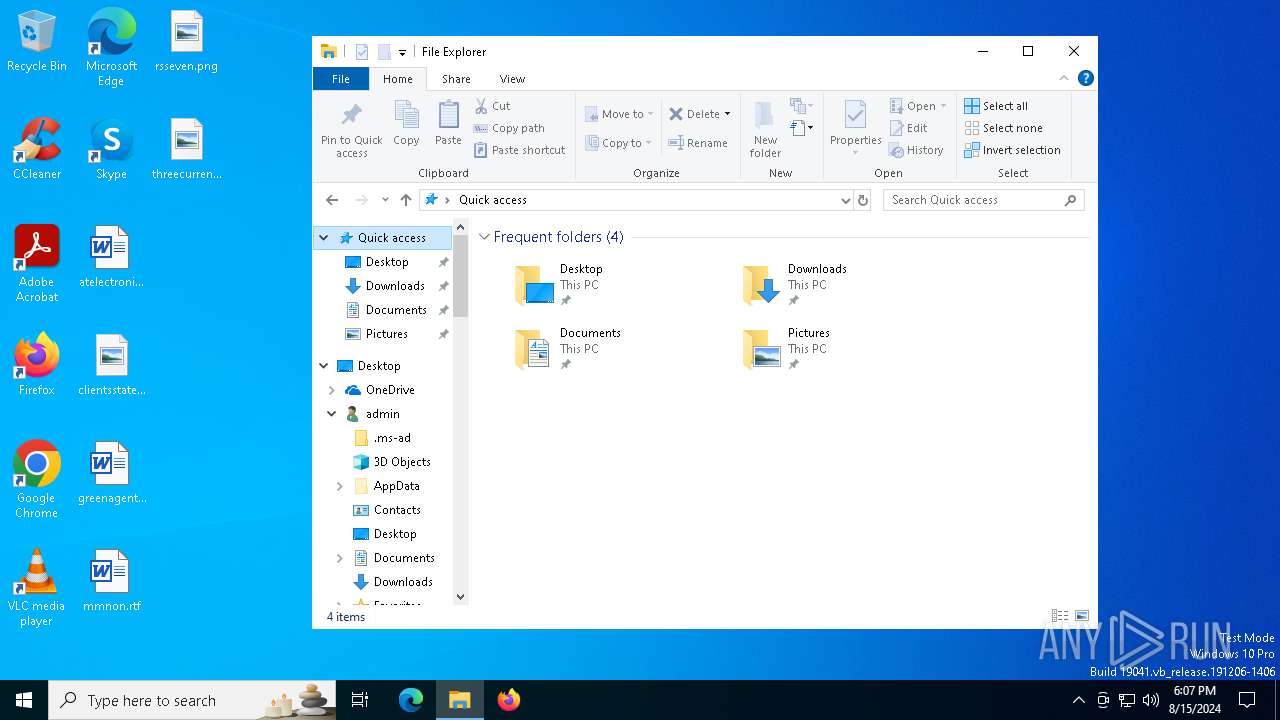
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | DBB5E5B3259132440236505D78B23B3C |
| SHA1: | 4A5A2D7FDB0519468BB123D96F3244D3C1EA90A4 |
| SHA256: | 426E304509D31F073BE374F3F33BB27E8B31981EC83275EFB5B069415EA22E6D |
| SSDEEP: | 98304:OJRP/1MNupgVQ0m+PjIXzkURFQ/G/AwFPCzSTiGbs4sFu50q40d8RStxAg3z/gOb:I0DKvEebSXigwq7KPKlFeVnRqxLOwS |
MALICIOUS
LUMMA has been detected (SURICATA)
- SearchIndexer.exe (PID: 876)
- SearchIndexer.exe (PID: 6520)
LUMMA has been detected (YARA)
- SearchIndexer.exe (PID: 6452)
- SearchIndexer.exe (PID: 6520)
- SearchIndexer.exe (PID: 876)
Stealers network behavior
- SearchIndexer.exe (PID: 876)
- SearchIndexer.exe (PID: 6520)
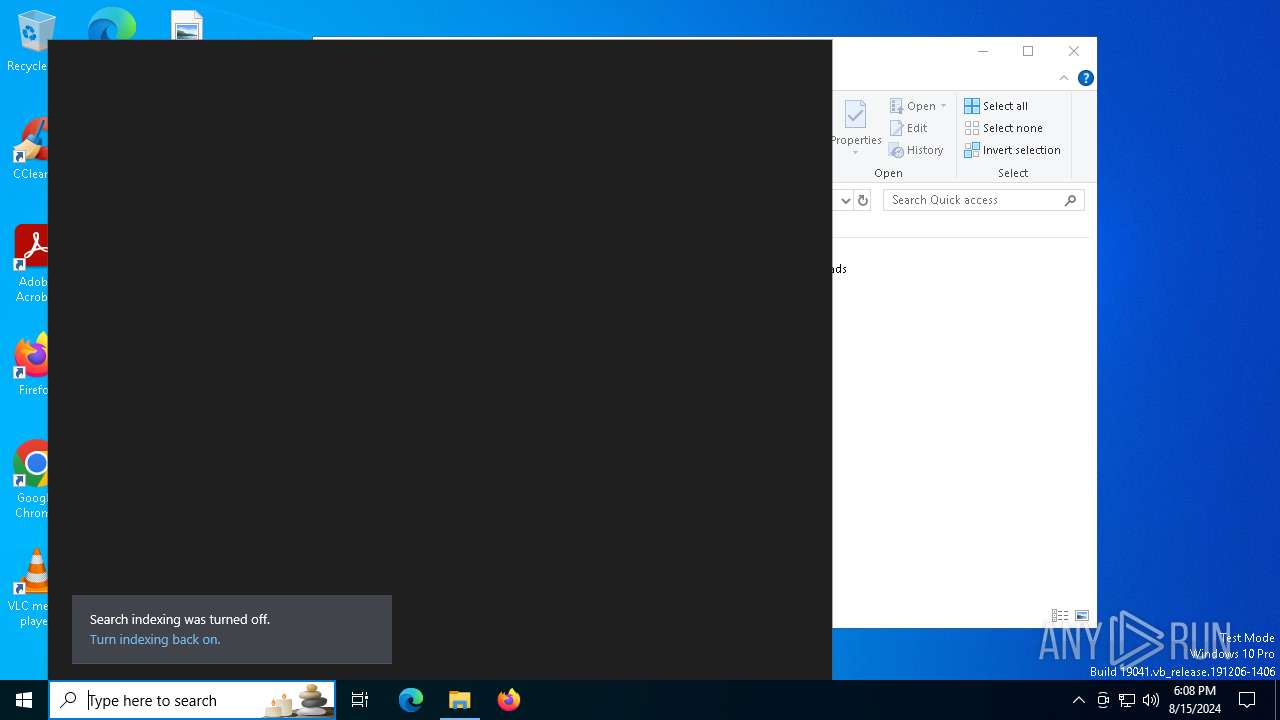
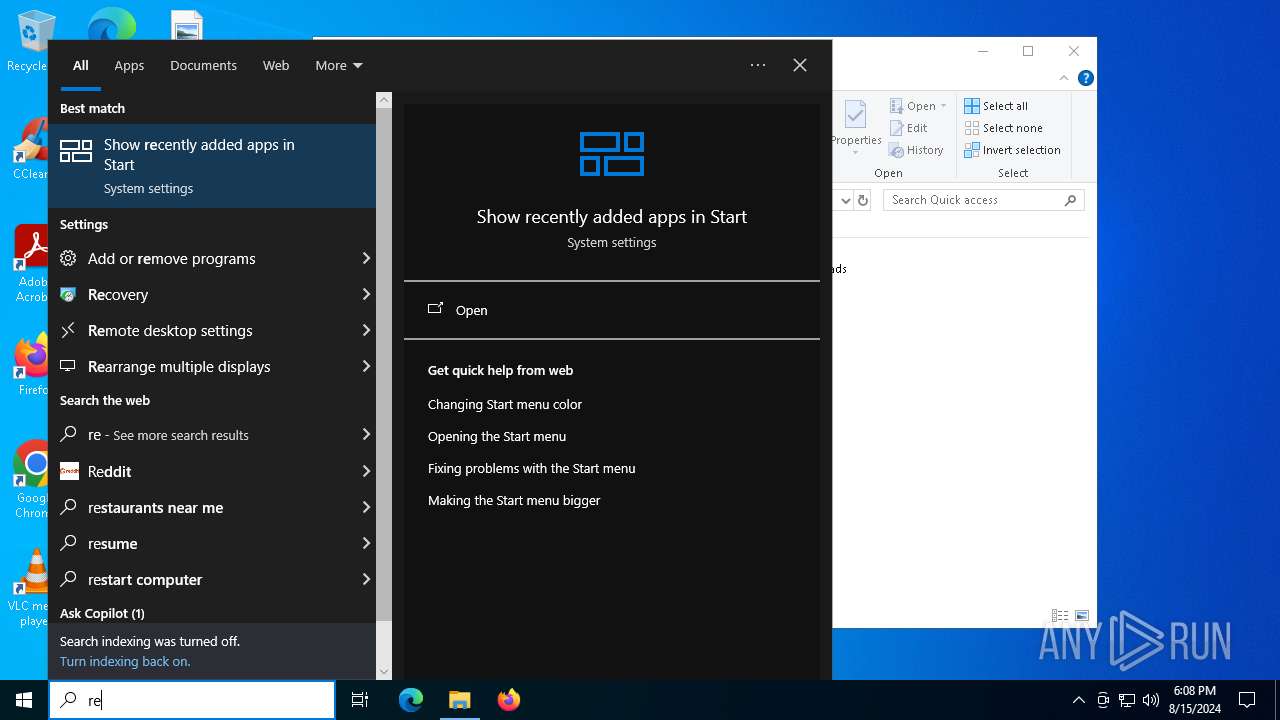
Bypass execution policy to execute commands
- powershell.exe (PID: 2608)
- powershell.exe (PID: 3292)
Probably downloads file via BitsAdmin (POWERSHELL)
- powershell.exe (PID: 2608)
- powershell.exe (PID: 3292)
Modifies registry (POWERSHELL)
- powershell.exe (PID: 3292)
Changes powershell execution policy (Bypass)
- SearchIndexer.exe (PID: 876)
- SearchIndexer.exe (PID: 6520)
SUSPICIOUS
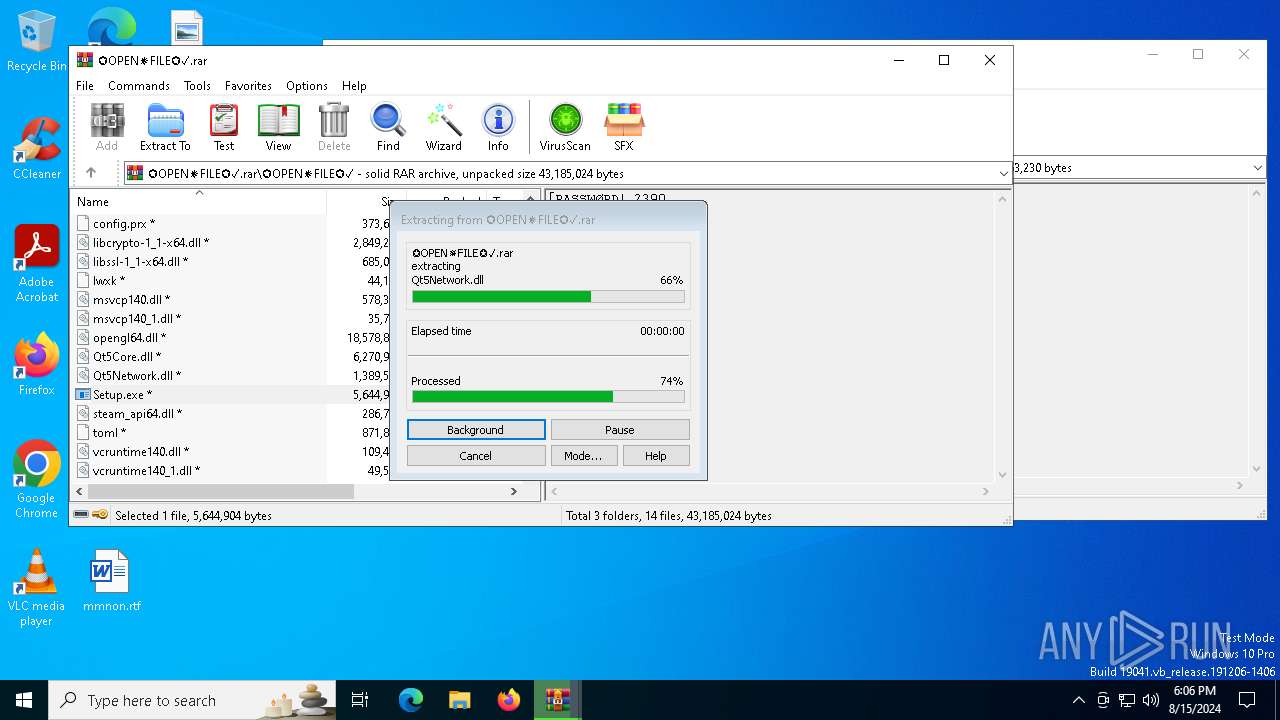
Application launched itself
- WinRAR.exe (PID: 1420)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1420)
- WinRAR.exe (PID: 3068)
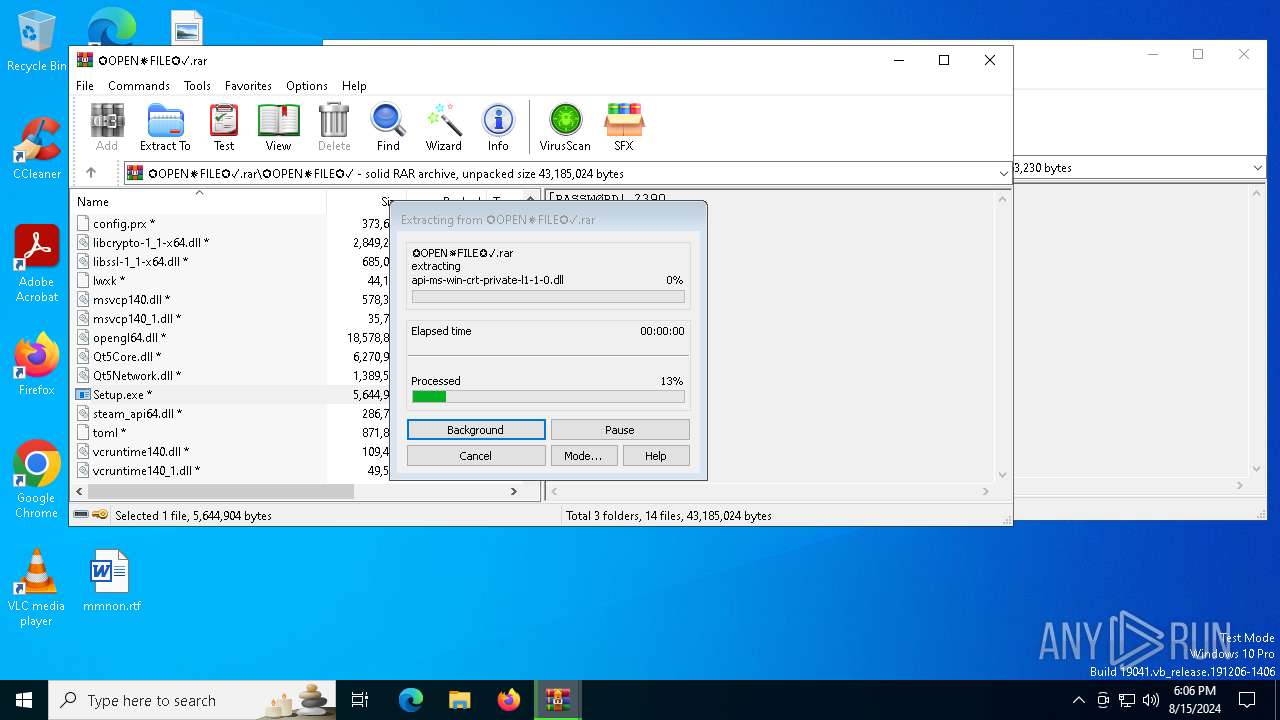
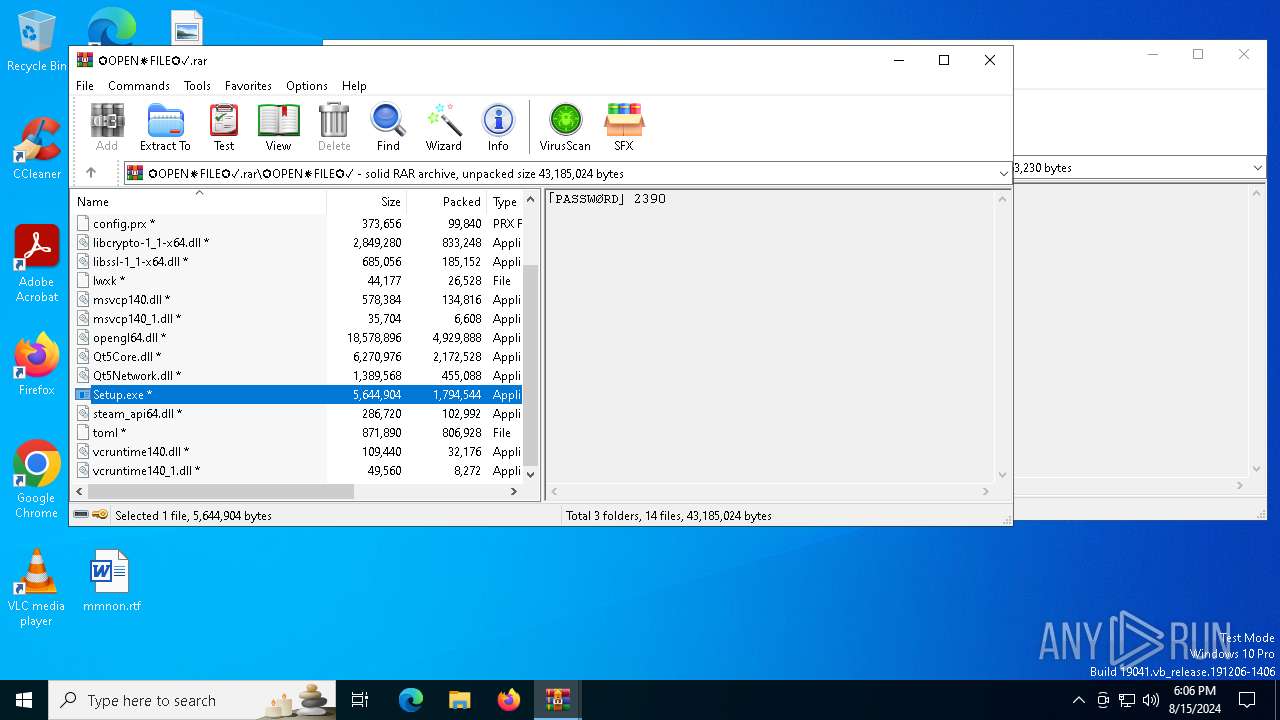
Process drops legitimate windows executable
- WinRAR.exe (PID: 3068)
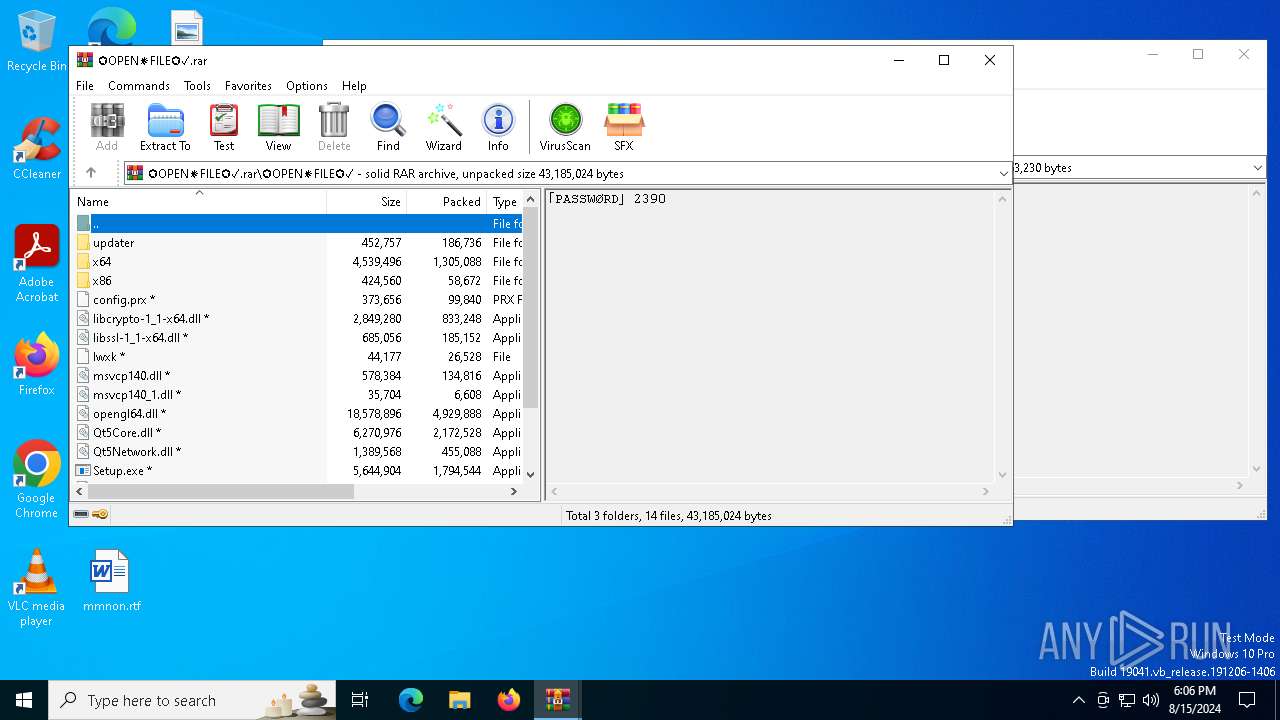
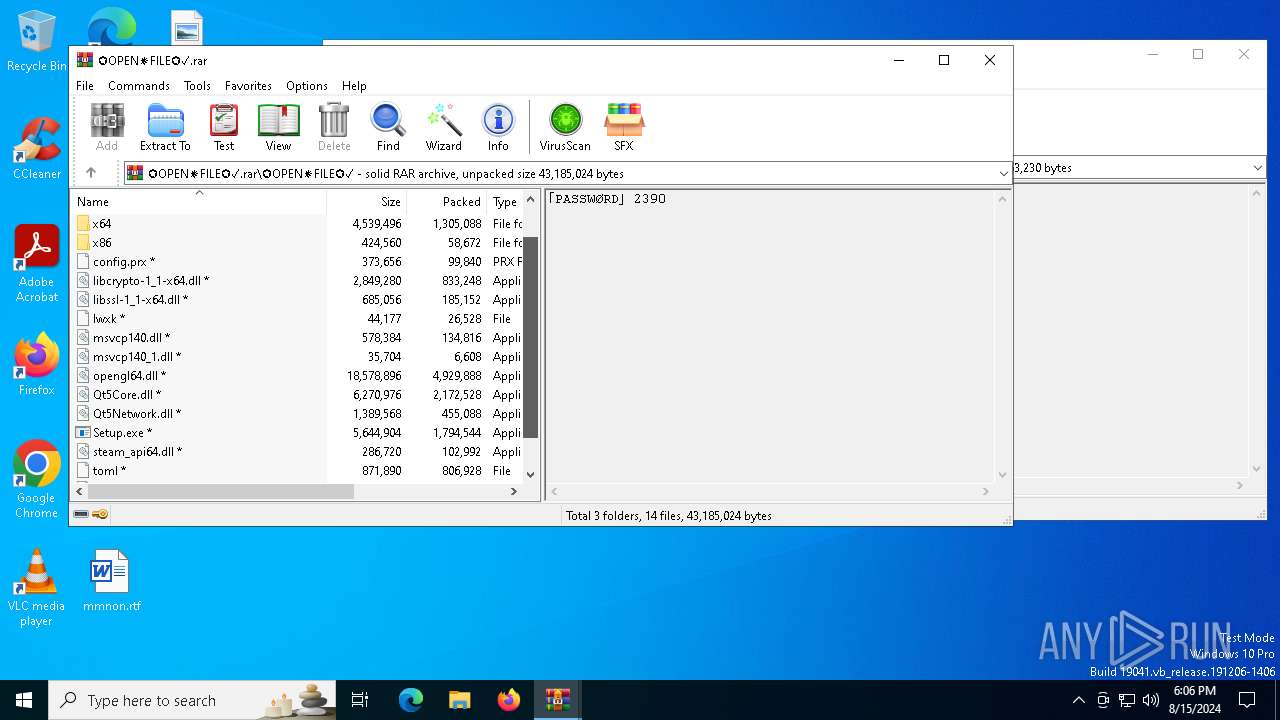
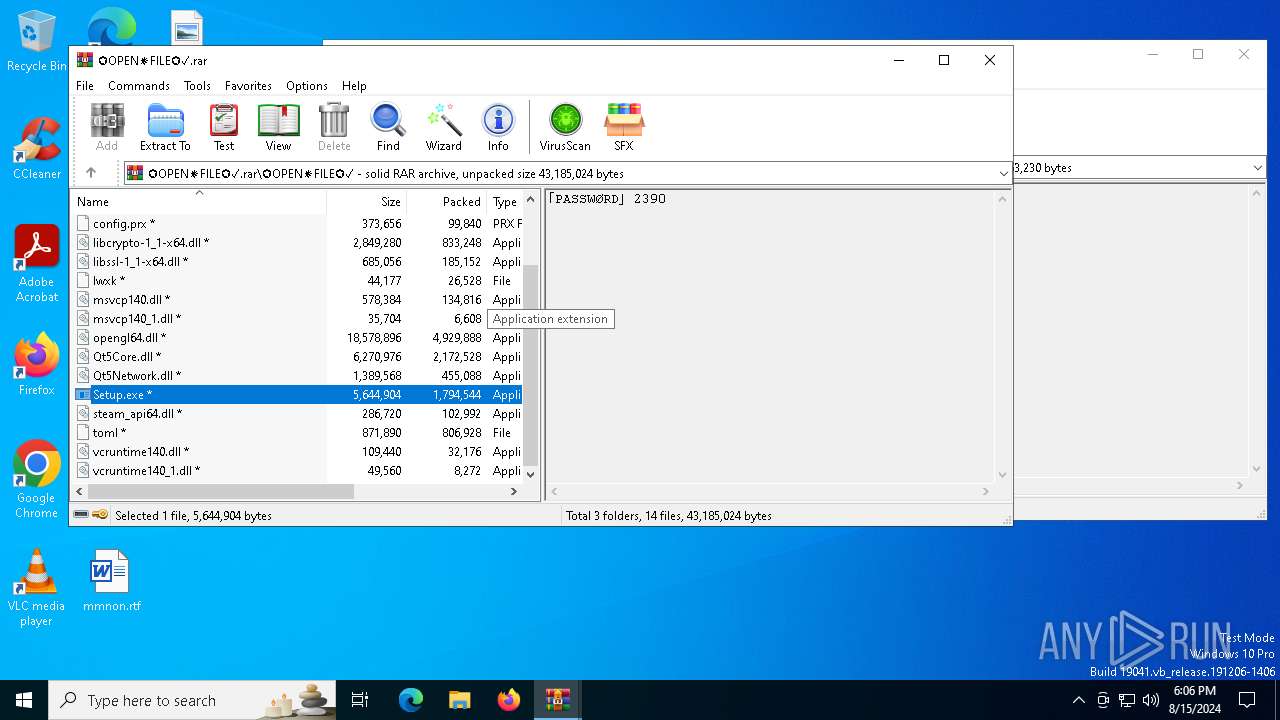
- Setup.exe (PID: 6732)
Drops the executable file immediately after the start
- Setup.exe (PID: 6732)
- WY0R1KZJLMAMR5W8C16.exe (PID: 7116)
The process drops C-runtime libraries
- Setup.exe (PID: 6732)
Executable content was dropped or overwritten
- Setup.exe (PID: 6732)
- SearchIndexer.exe (PID: 876)
- WY0R1KZJLMAMR5W8C16.exe (PID: 7116)
- SearchIndexer.exe (PID: 6520)
Starts application with an unusual extension
- Setup.exe (PID: 6992)
- Setup.exe (PID: 4280)
- Setup.exe (PID: 6732)
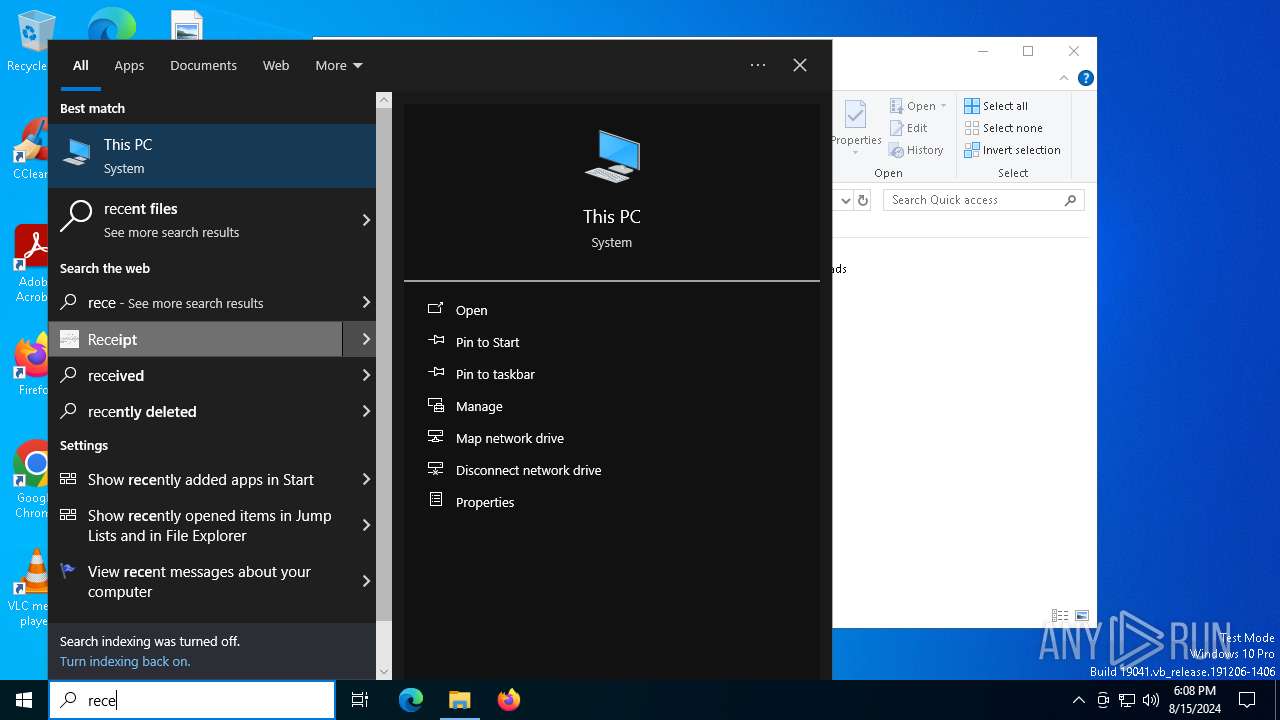
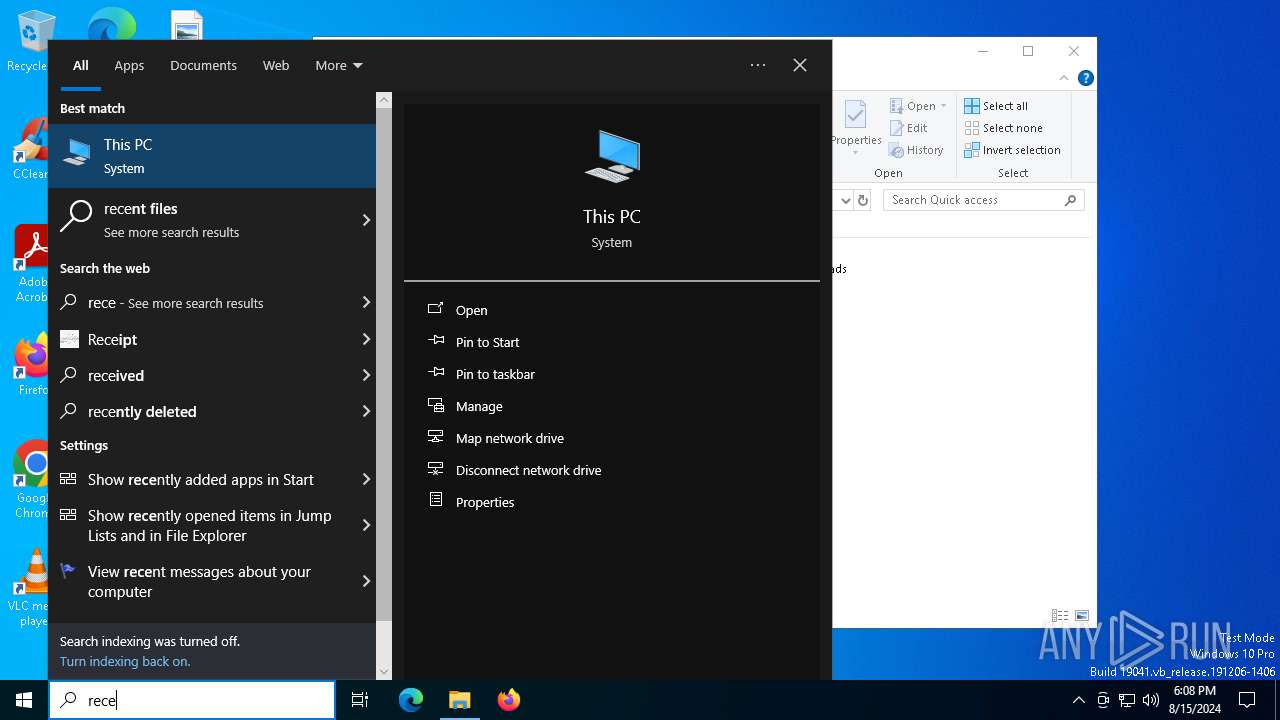
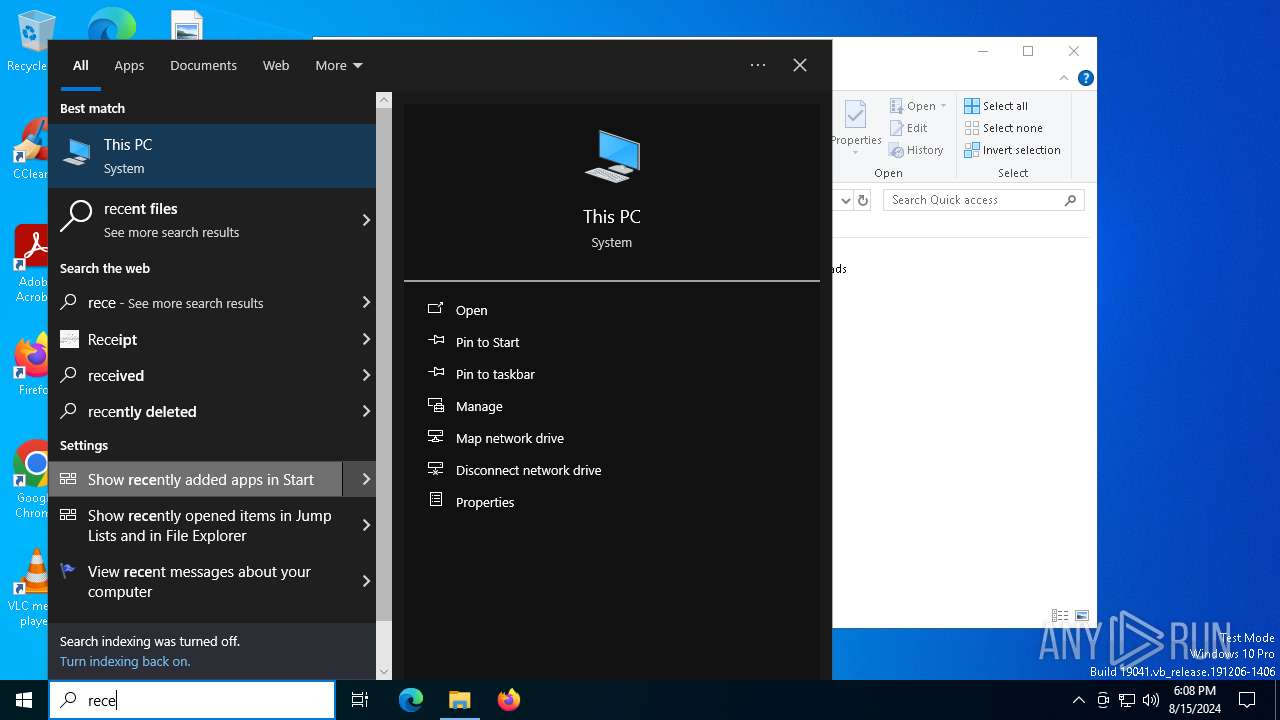
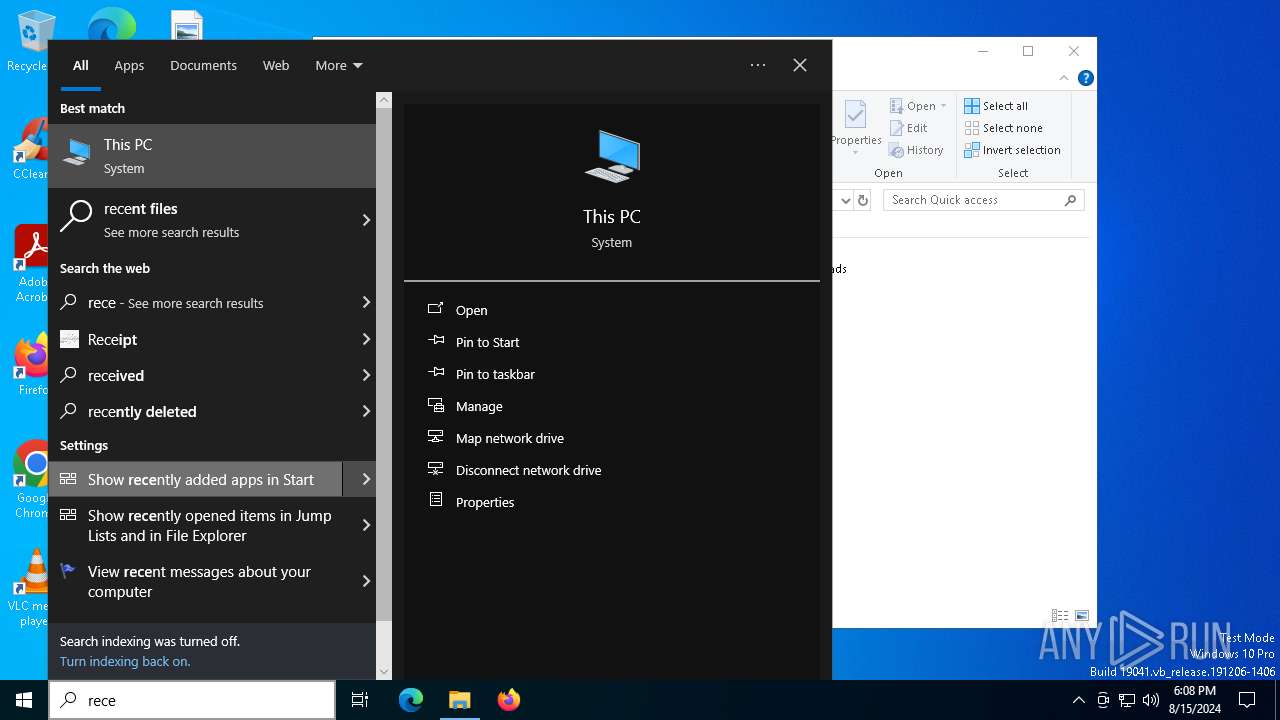
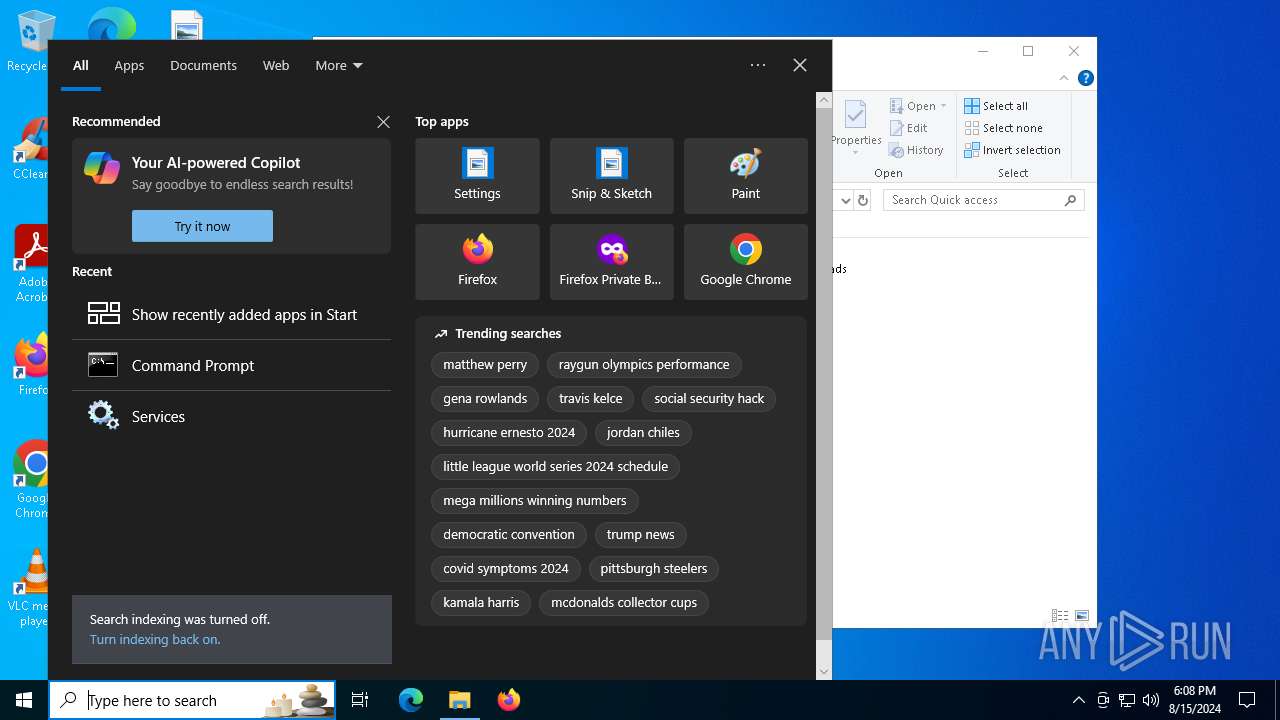
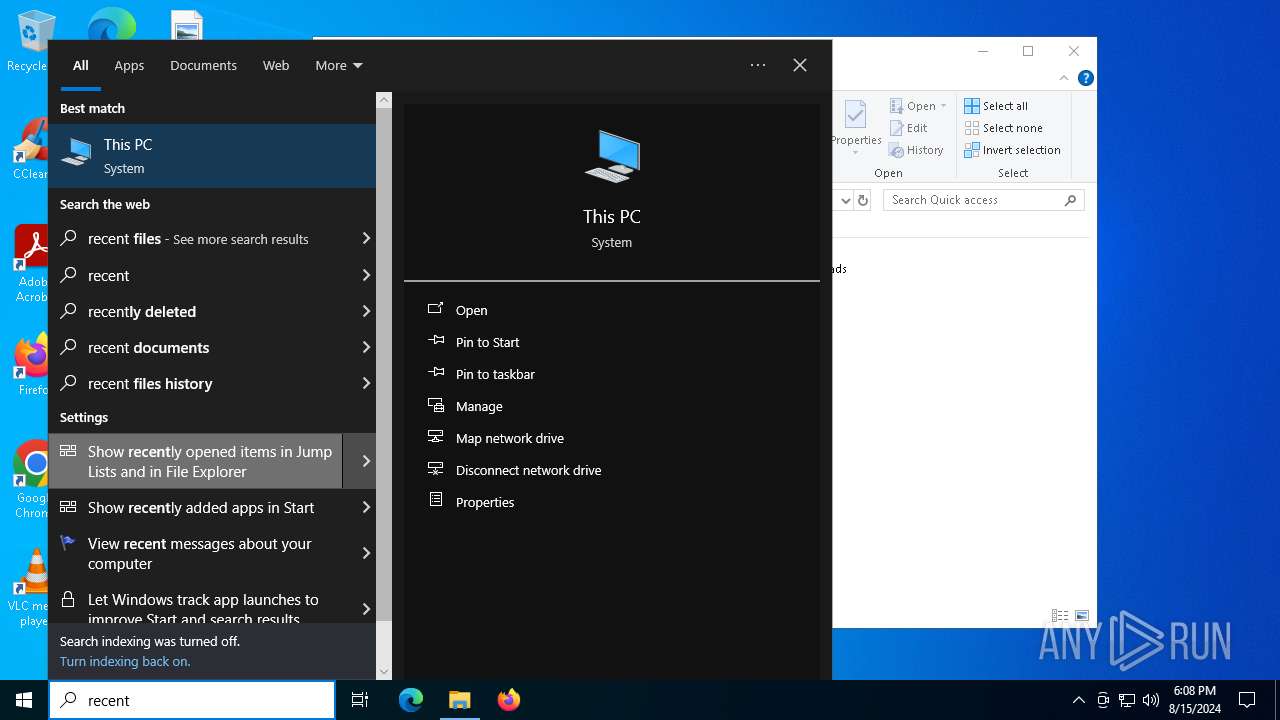
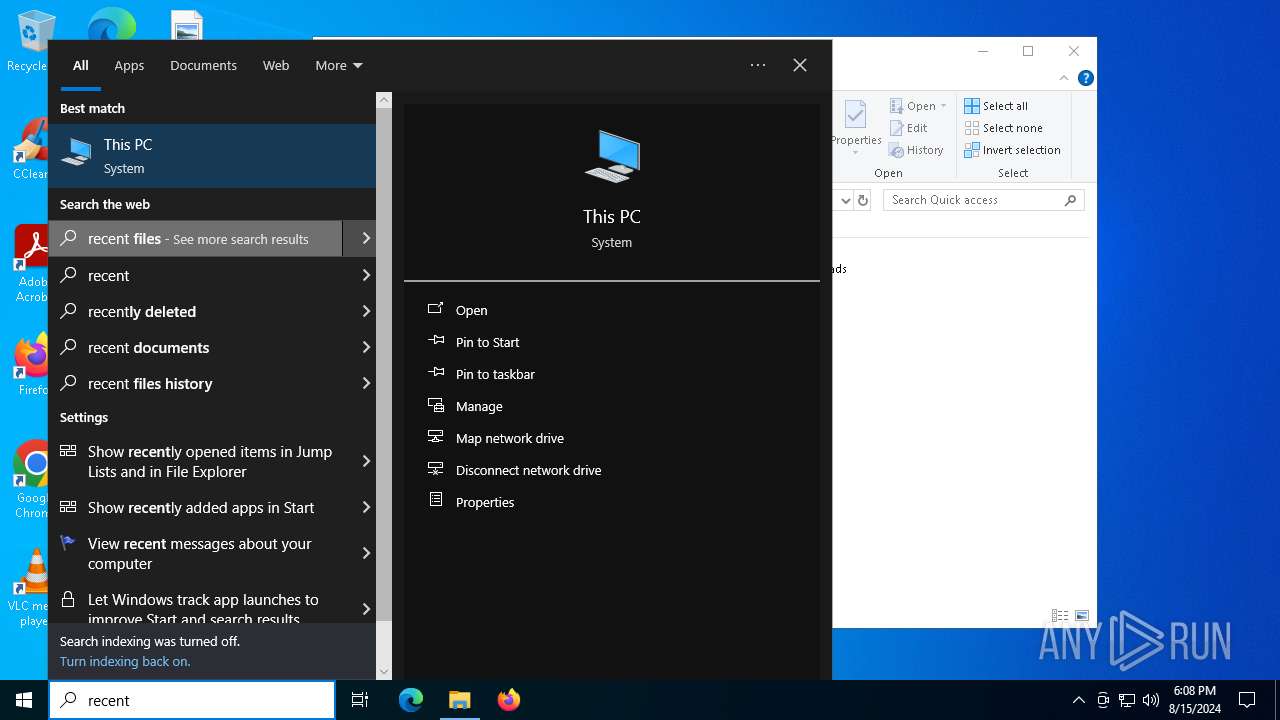
Searches for installed software
- SearchIndexer.exe (PID: 876)
- SearchIndexer.exe (PID: 6520)
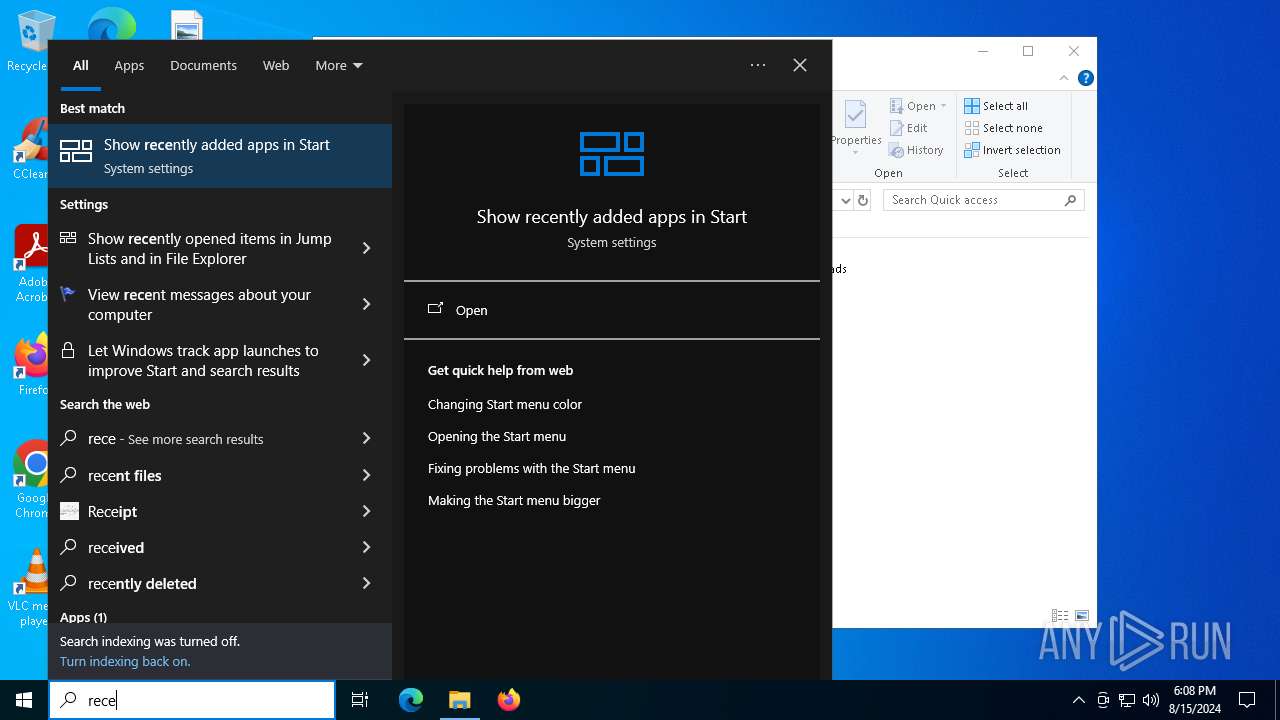
The process executes Powershell scripts
- SearchIndexer.exe (PID: 876)
- SearchIndexer.exe (PID: 6520)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 2608)
- powershell.exe (PID: 3292)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 2608)
- powershell.exe (PID: 3292)
Connects to unusual port
- MSBuild.exe (PID: 840)
Found regular expressions for crypto-addresses (YARA)
- MSBuild.exe (PID: 840)
Starts POWERSHELL.EXE for commands execution
- SearchIndexer.exe (PID: 6520)
- SearchIndexer.exe (PID: 876)
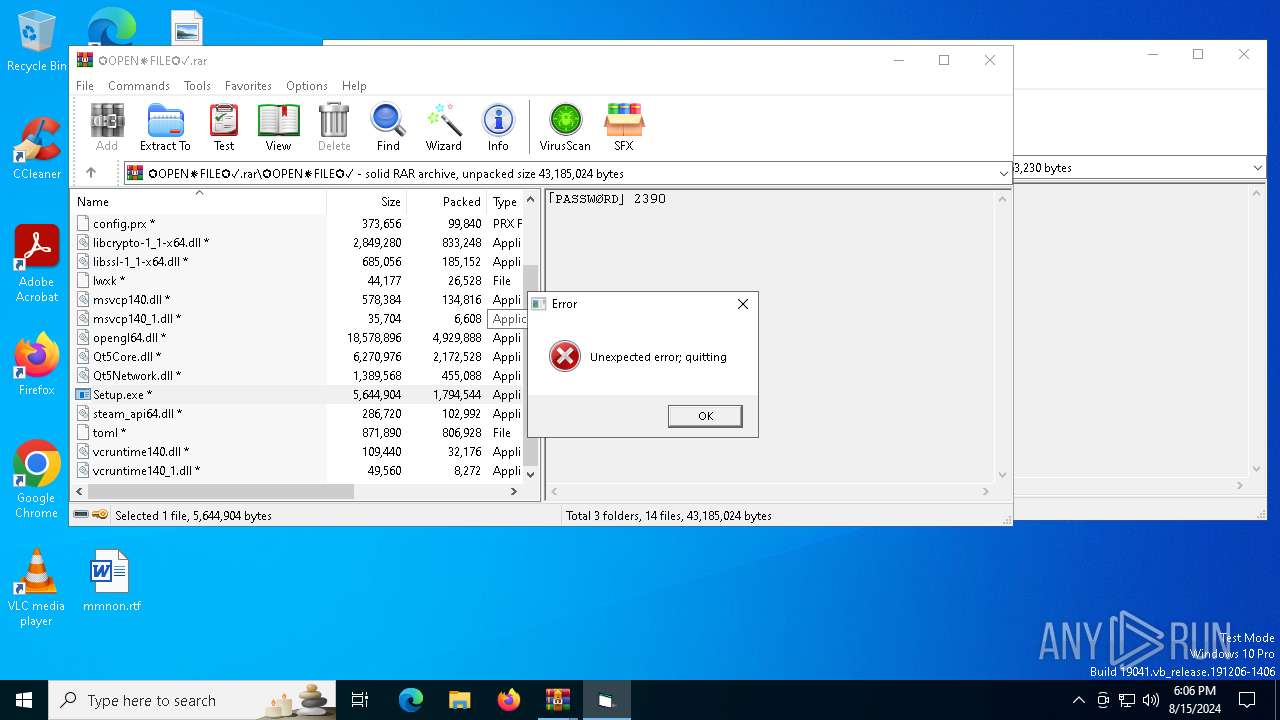
Executes application which crashes
- MSBuild.exe (PID: 1544)
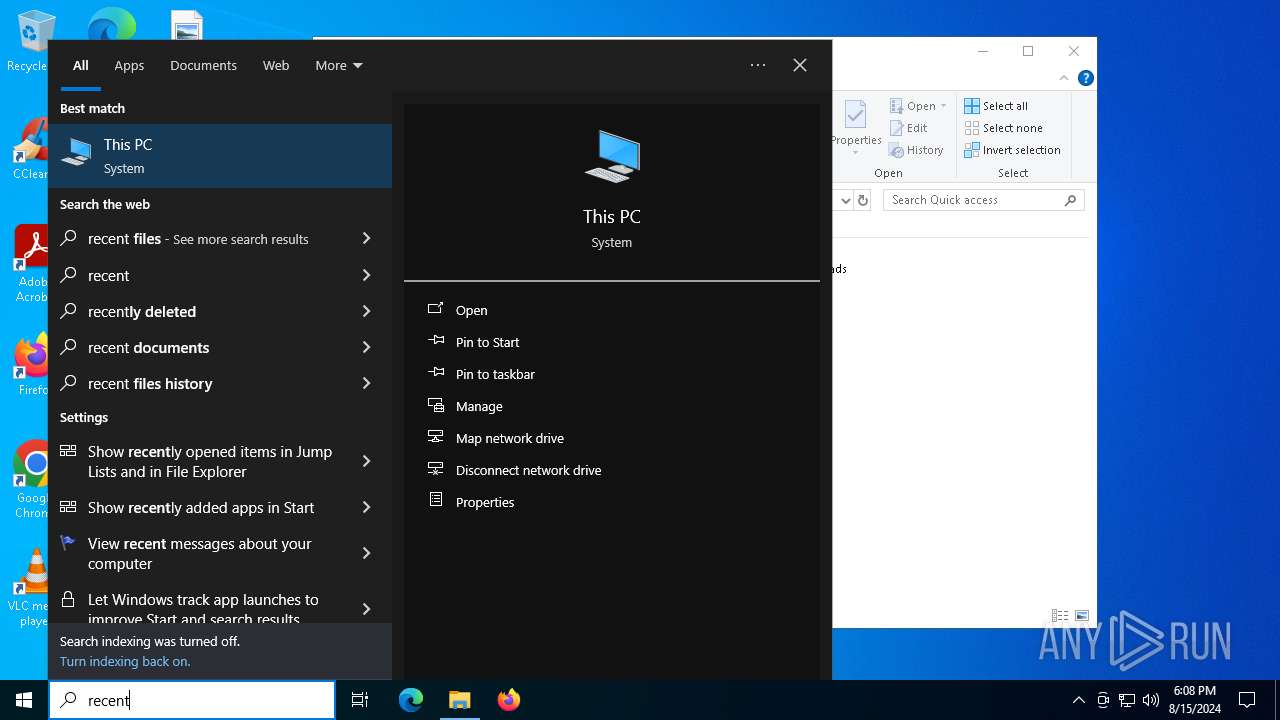
The process executes via Task Scheduler
- oakley.exe (PID: 532)
INFO
Checks supported languages
- Setup.exe (PID: 6732)
- more.com (PID: 4060)
- Setup.exe (PID: 6992)
- StrCmp.exe (PID: 6956)
- Setup.exe (PID: 4280)
- more.com (PID: 5980)
- more.com (PID: 6924)
- WY0R1KZJLMAMR5W8C16.exe (PID: 7116)
- PE7BDERD3WE1VEAVUNKK9T.exe (PID: 2080)
- MSBuild.exe (PID: 840)
- K7RMS1UAOI9PAYDPVZKTBYNFHYNSUX.exe (PID: 2992)
- CU92URRP6ZQE1KR4Q01V7D.exe (PID: 6884)
- TextInputHost.exe (PID: 6632)
- oakley.exe (PID: 532)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3068)
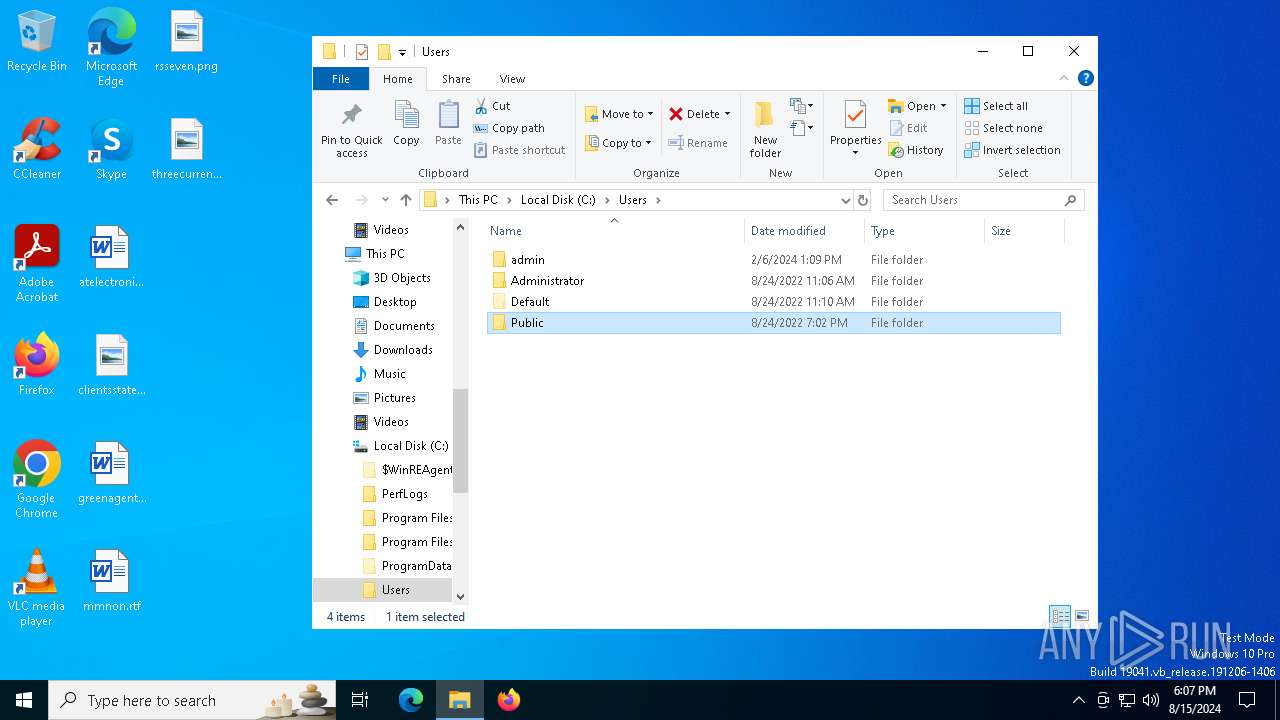
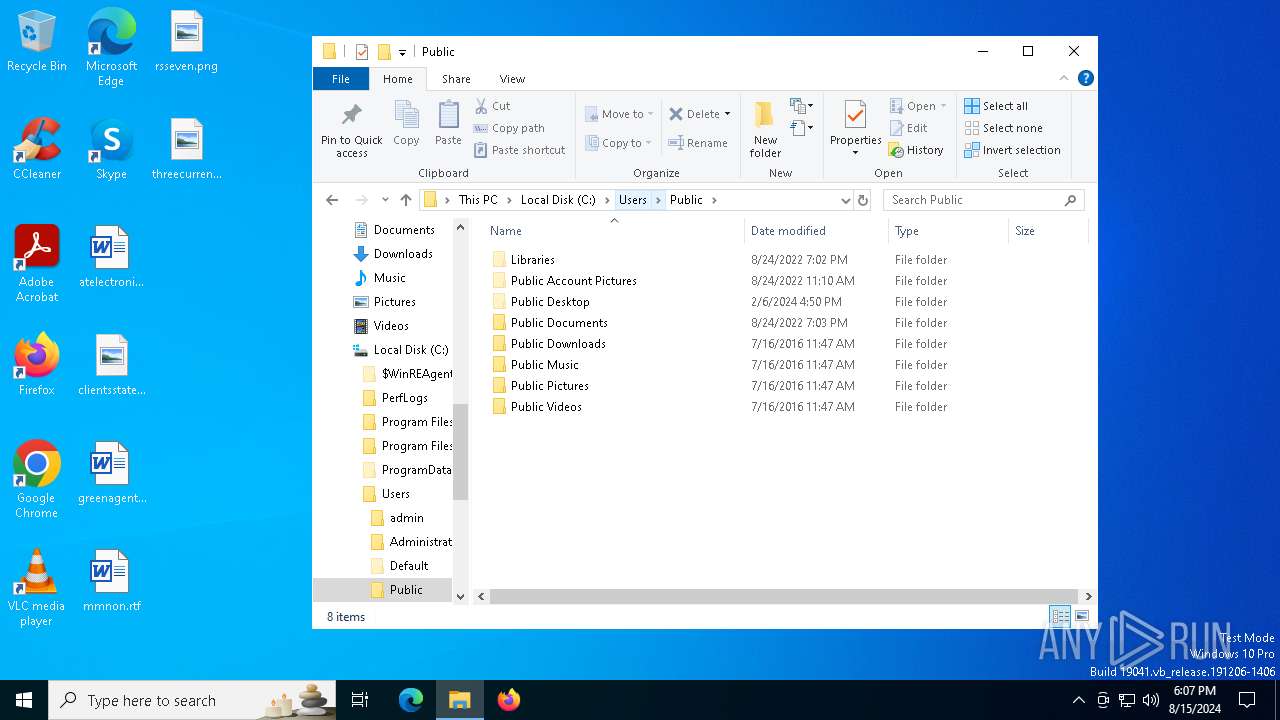
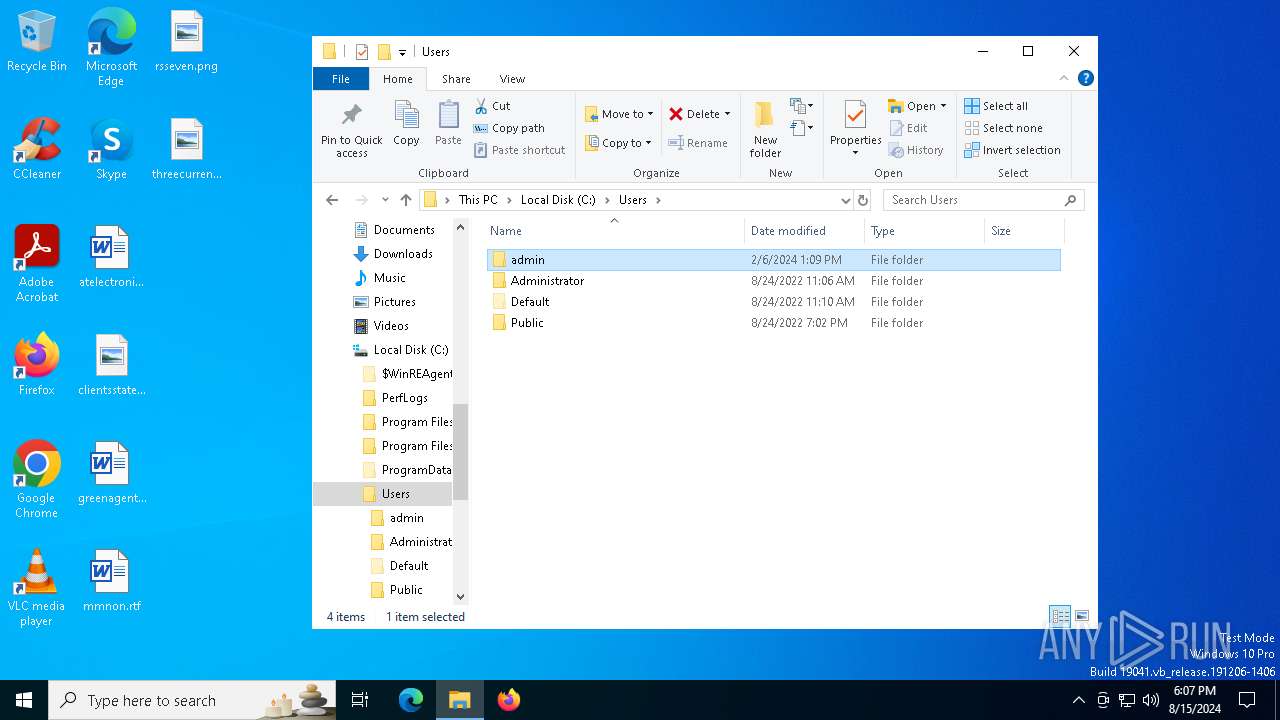
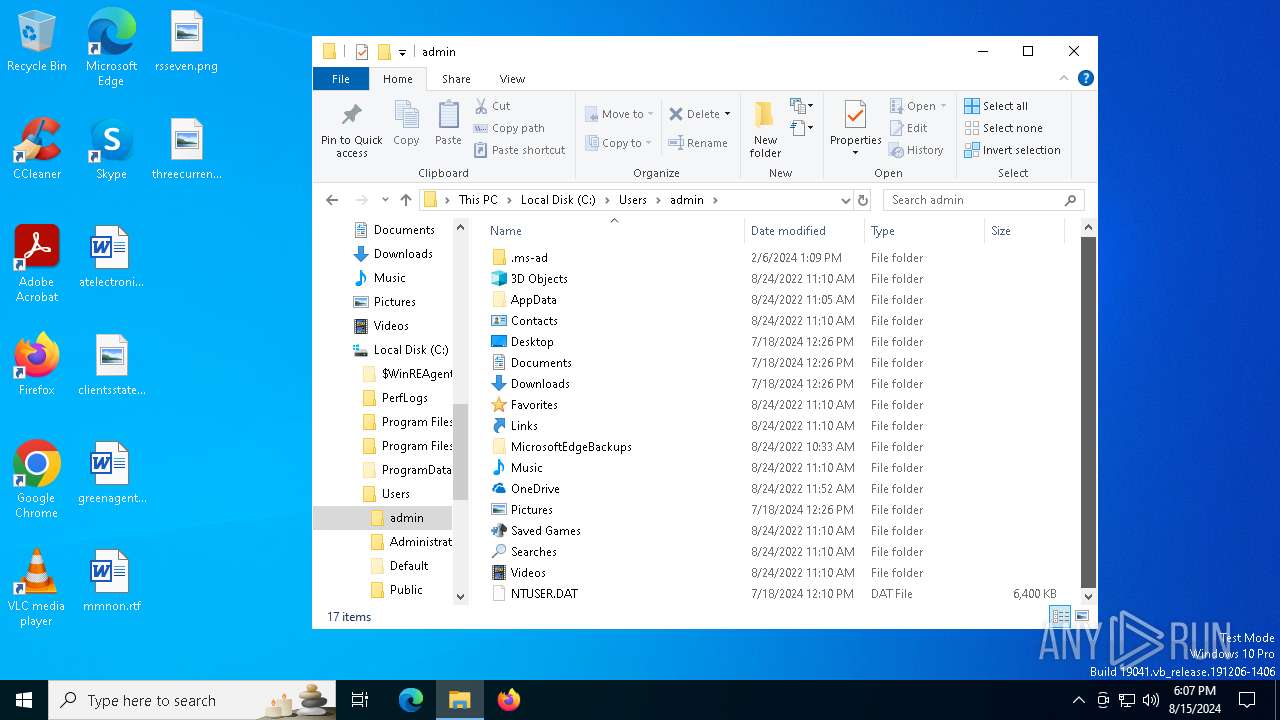
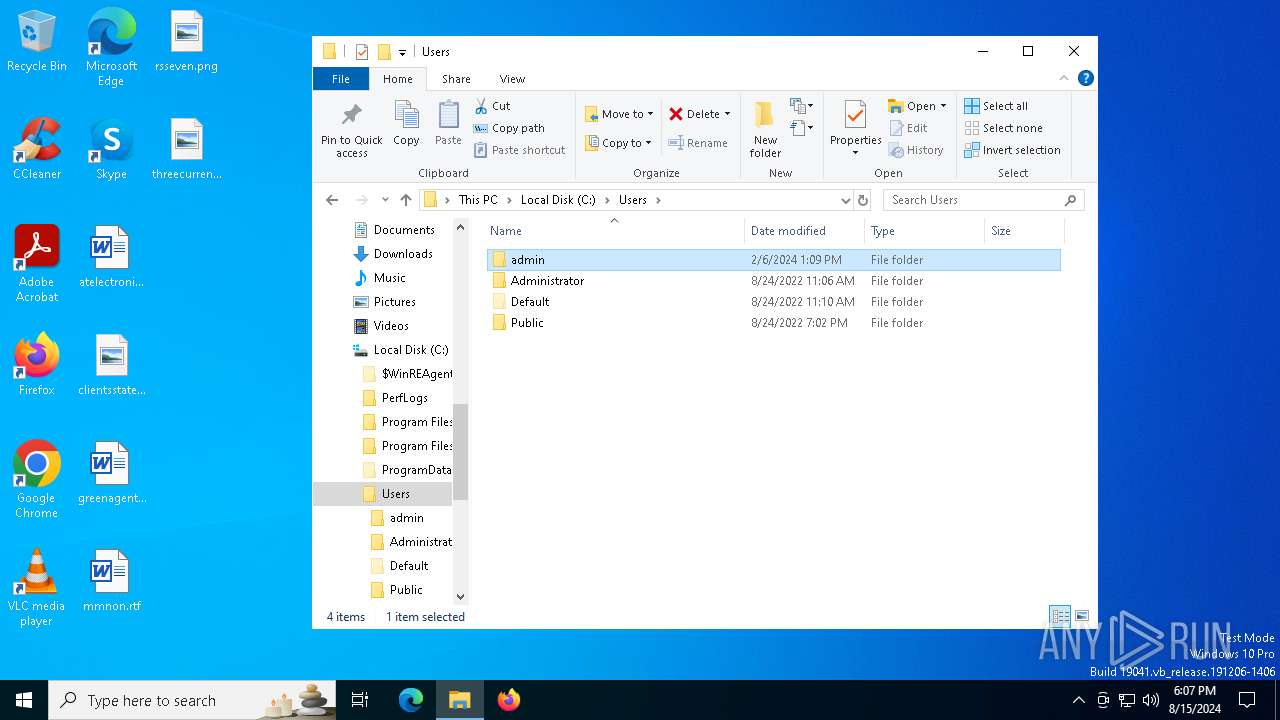
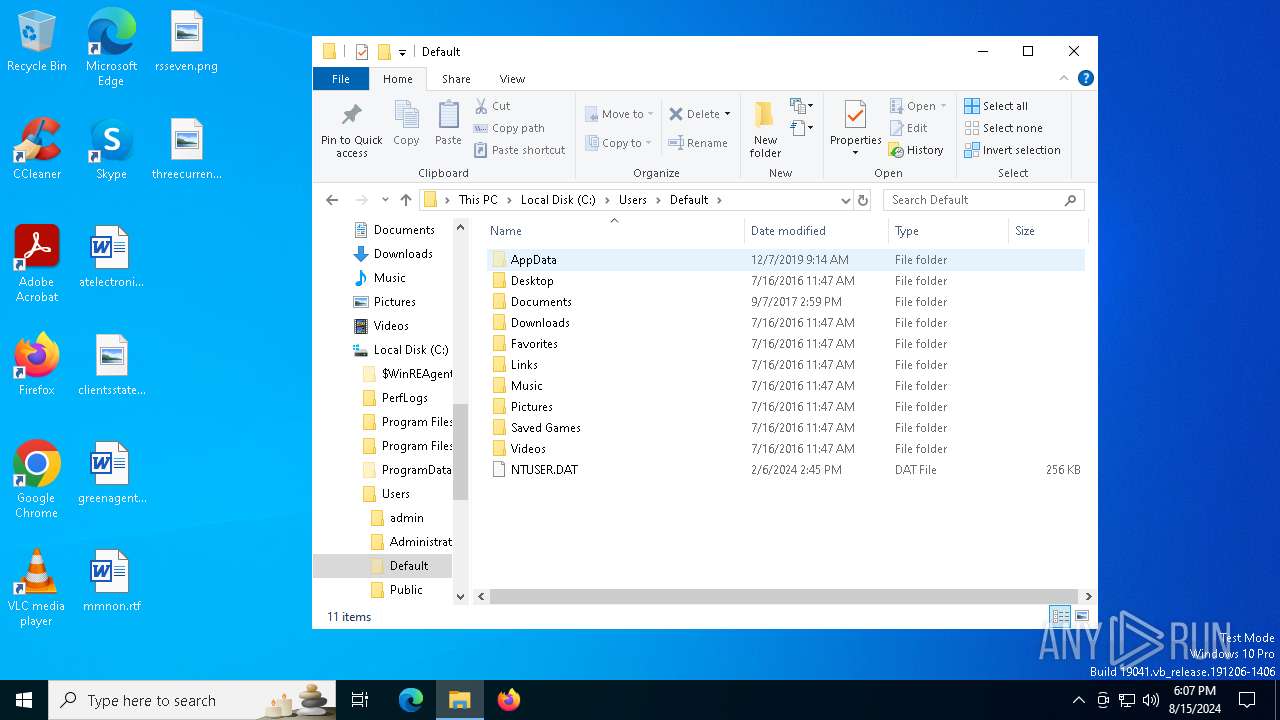
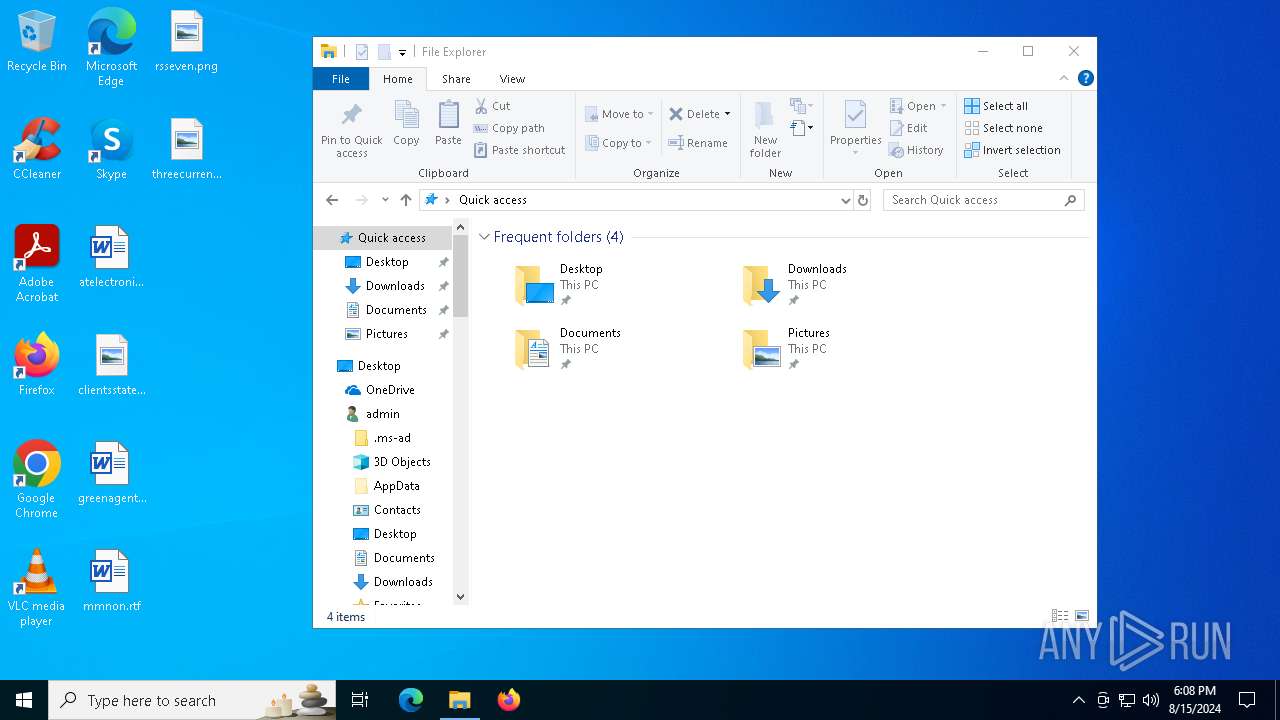
Creates files or folders in the user directory
- Setup.exe (PID: 6732)
- WY0R1KZJLMAMR5W8C16.exe (PID: 7116)
- WerFault.exe (PID: 7272)
Reads the computer name
- more.com (PID: 4060)
- StrCmp.exe (PID: 6956)
- Setup.exe (PID: 6732)
- Setup.exe (PID: 6992)
- more.com (PID: 6924)
- Setup.exe (PID: 4280)
- more.com (PID: 5980)
- PE7BDERD3WE1VEAVUNKK9T.exe (PID: 2080)
- WY0R1KZJLMAMR5W8C16.exe (PID: 7116)
- TextInputHost.exe (PID: 6632)
- CU92URRP6ZQE1KR4Q01V7D.exe (PID: 6884)
- K7RMS1UAOI9PAYDPVZKTBYNFHYNSUX.exe (PID: 2992)
Create files in a temporary directory
- more.com (PID: 4060)
- Setup.exe (PID: 6992)
- more.com (PID: 6924)
- more.com (PID: 5980)
- SearchIndexer.exe (PID: 876)
- PE7BDERD3WE1VEAVUNKK9T.exe (PID: 2080)
- Setup.exe (PID: 6732)
- SearchIndexer.exe (PID: 6520)
- MSBuild.exe (PID: 840)
- Setup.exe (PID: 4280)
- CU92URRP6ZQE1KR4Q01V7D.exe (PID: 6884)
- WerFault.exe (PID: 7272)
Reads the software policy settings
- SearchIndexer.exe (PID: 876)
- SearchIndexer.exe (PID: 6520)
- WerFault.exe (PID: 7272)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2608)
- powershell.exe (PID: 3292)
Reads the machine GUID from the registry
- WY0R1KZJLMAMR5W8C16.exe (PID: 7116)
- K7RMS1UAOI9PAYDPVZKTBYNFHYNSUX.exe (PID: 2992)
.NET Reactor protector has been detected
- WY0R1KZJLMAMR5W8C16.exe (PID: 7116)
- K7RMS1UAOI9PAYDPVZKTBYNFHYNSUX.exe (PID: 2992)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2608)
- powershell.exe (PID: 3292)
Manual execution by a user
- MSBuild.exe (PID: 840)
- MSBuild.exe (PID: 1544)
Checks proxy server information
- WerFault.exe (PID: 7272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(876) SearchIndexer.exe
C2 (9)consciousourwi.shop
southedhiscuso.shop
interactiedovspm.shop
weiggheticulop.shop
cagedwifedsozm.shop
charecteristicdxp.shop
deicedosmzj.shop
refrigaterpsm.shop
potentioallykeos.shop
(PID) Process(6452) SearchIndexer.exe
C2 (9)consciousourwi.shop
southedhiscuso.shop
interactiedovspm.shop
weiggheticulop.shop
cagedwifedsozm.shop
charecteristicdxp.shop
deicedosmzj.shop
refrigaterpsm.shop
potentioallykeos.shop
(PID) Process(6520) SearchIndexer.exe
C2 (9)consciousourwi.shop
southedhiscuso.shop
interactiedovspm.shop
weiggheticulop.shop
cagedwifedsozm.shop
charecteristicdxp.shop
deicedosmzj.shop
refrigaterpsm.shop
potentioallykeos.shop
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
210
Monitored processes
29
Malicious processes
14
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
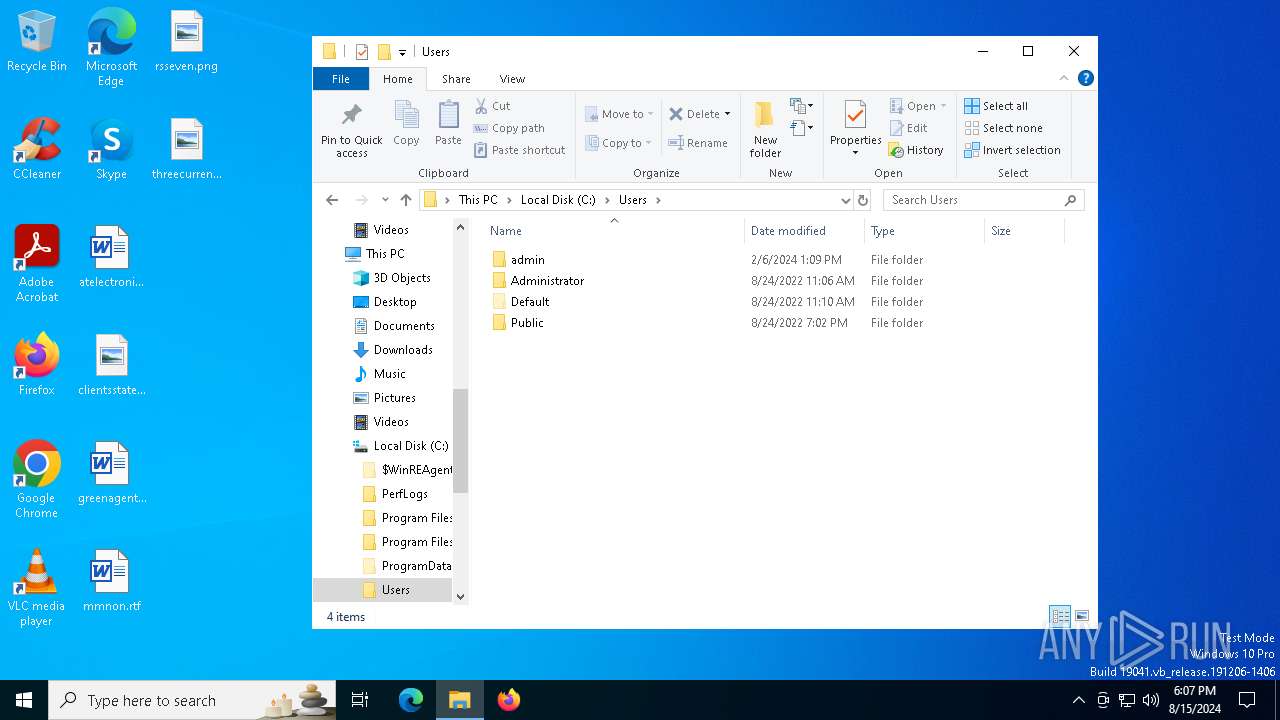
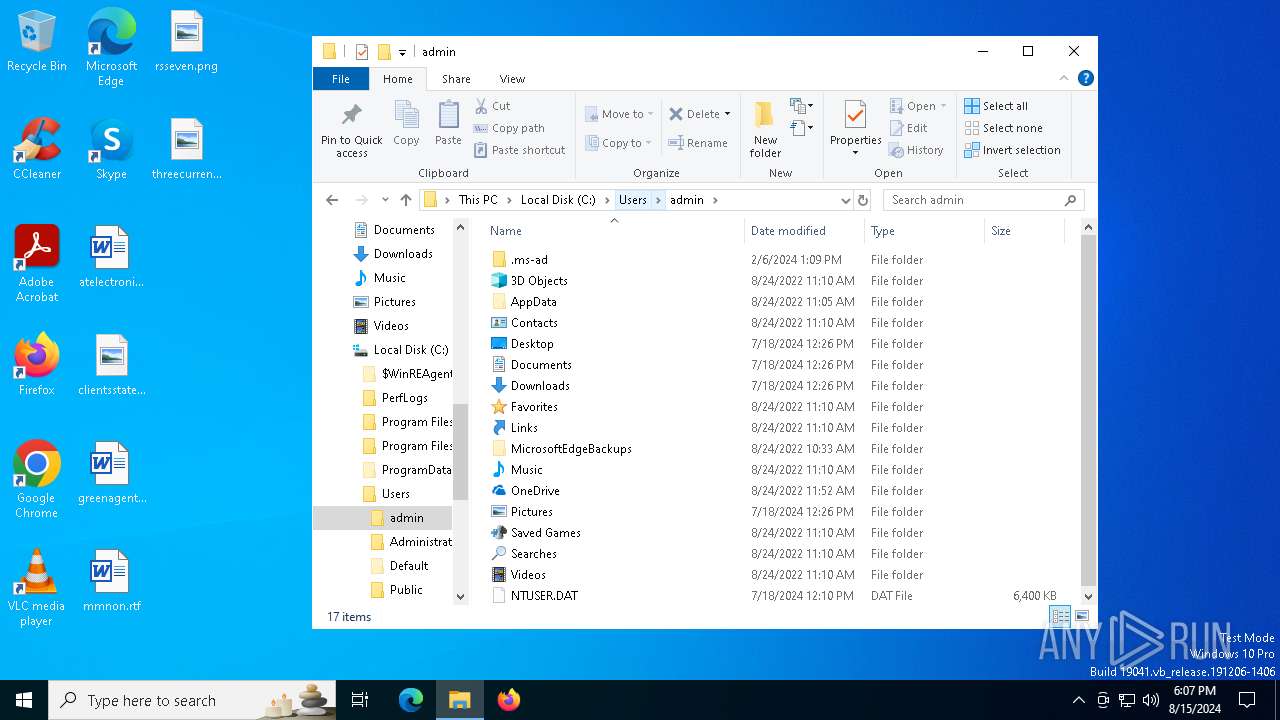
| 532 | "C:\Users\admin\AppData\Local\oakley.exe" | C:\Users\admin\AppData\Local\oakley.exe | — | svchost.exe | |||||||||||
User: admin Company: Argotronic GmbH Integrity Level: MEDIUM Description: ArgusMonitor Setup Version: 7.0.4.2720 Modules
| |||||||||||||||
| 840 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 876 | C:\WINDOWS\SysWOW64\SearchIndexer.exe | C:\Windows\SysWOW64\SearchIndexer.exe | more.com | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Indexer Exit code: 0 Version: 7.0.19041.3758 (WinBuild.160101.0800) Modules
Lumma(PID) Process(876) SearchIndexer.exe C2 (9)consciousourwi.shop southedhiscuso.shop interactiedovspm.shop weiggheticulop.shop cagedwifedsozm.shop charecteristicdxp.shop deicedosmzj.shop refrigaterpsm.shop potentioallykeos.shop | |||||||||||||||
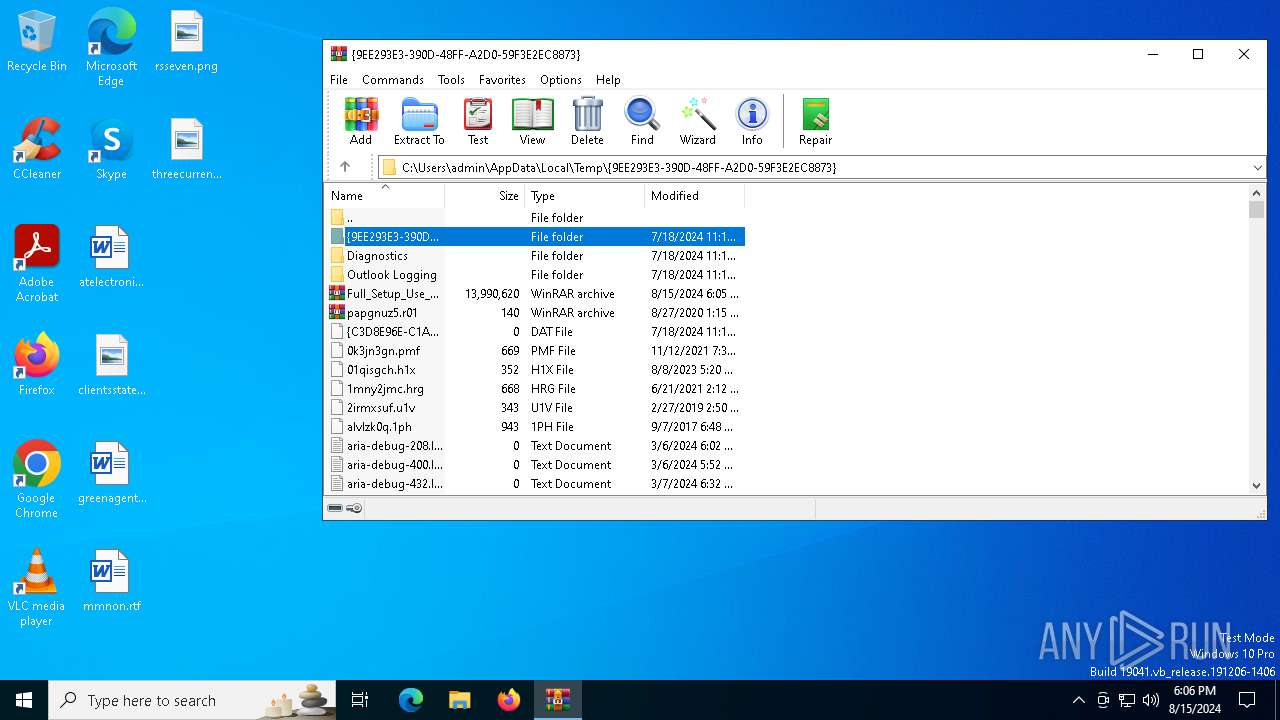
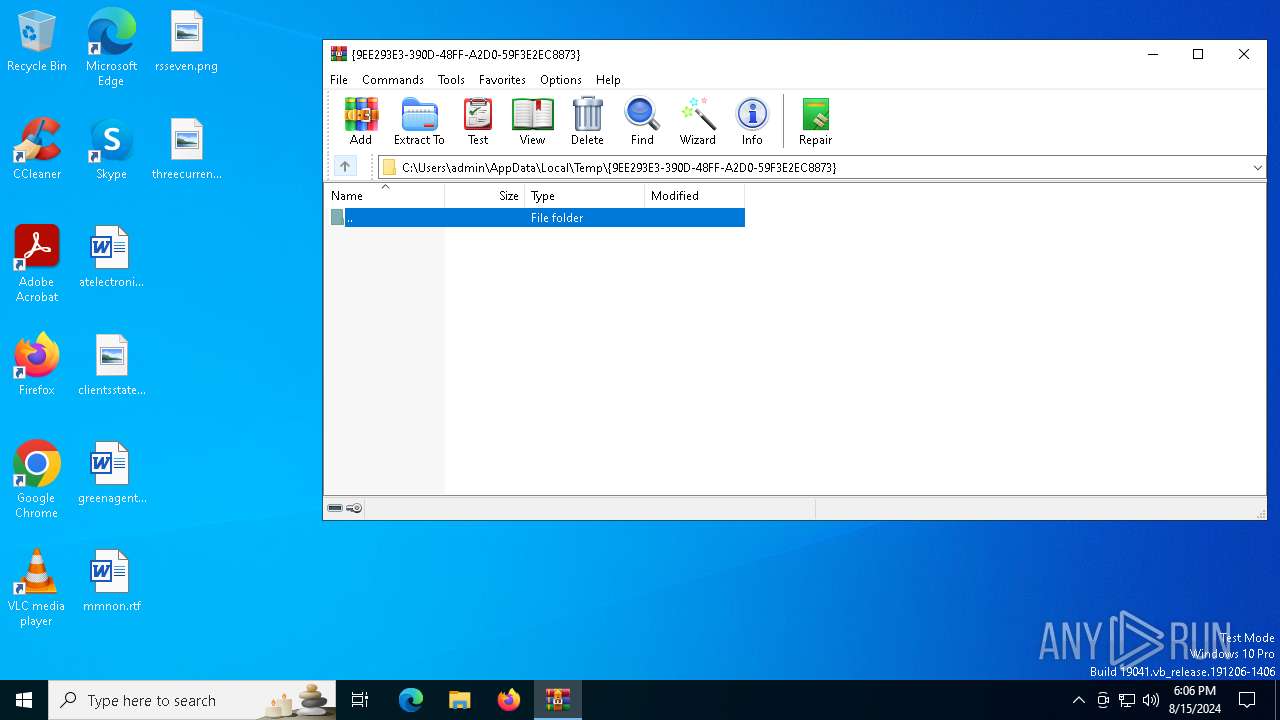
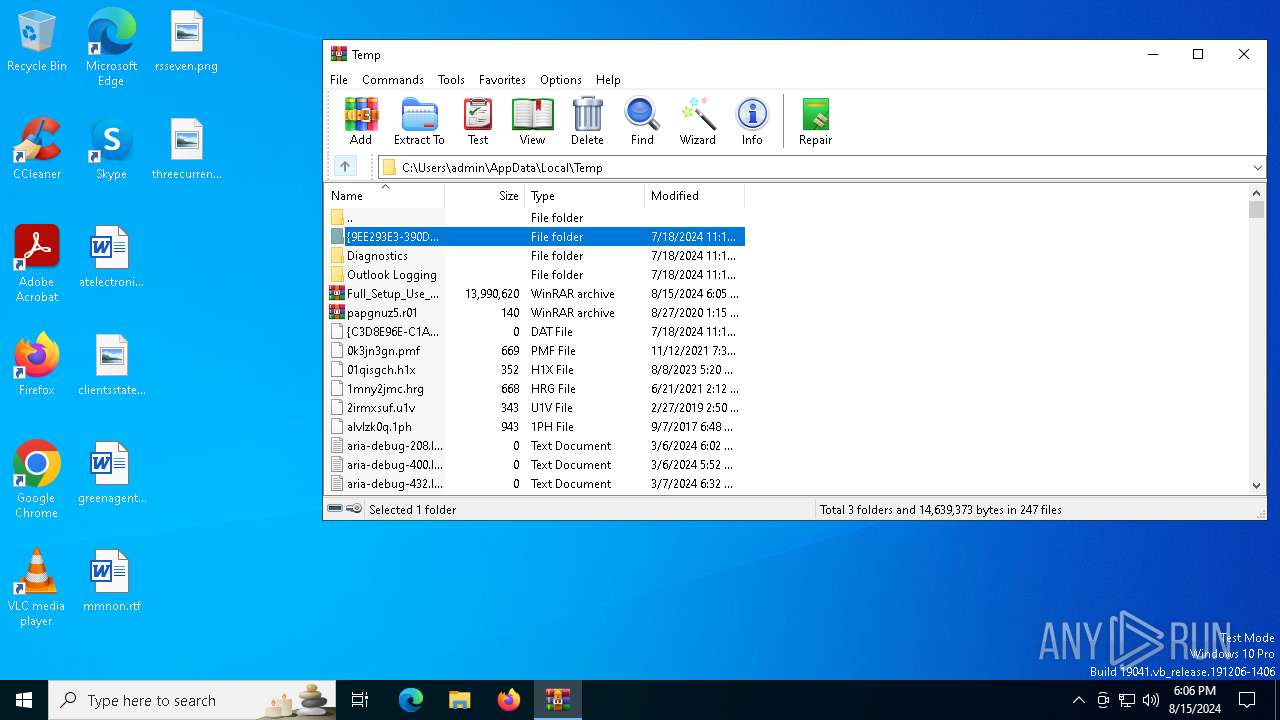
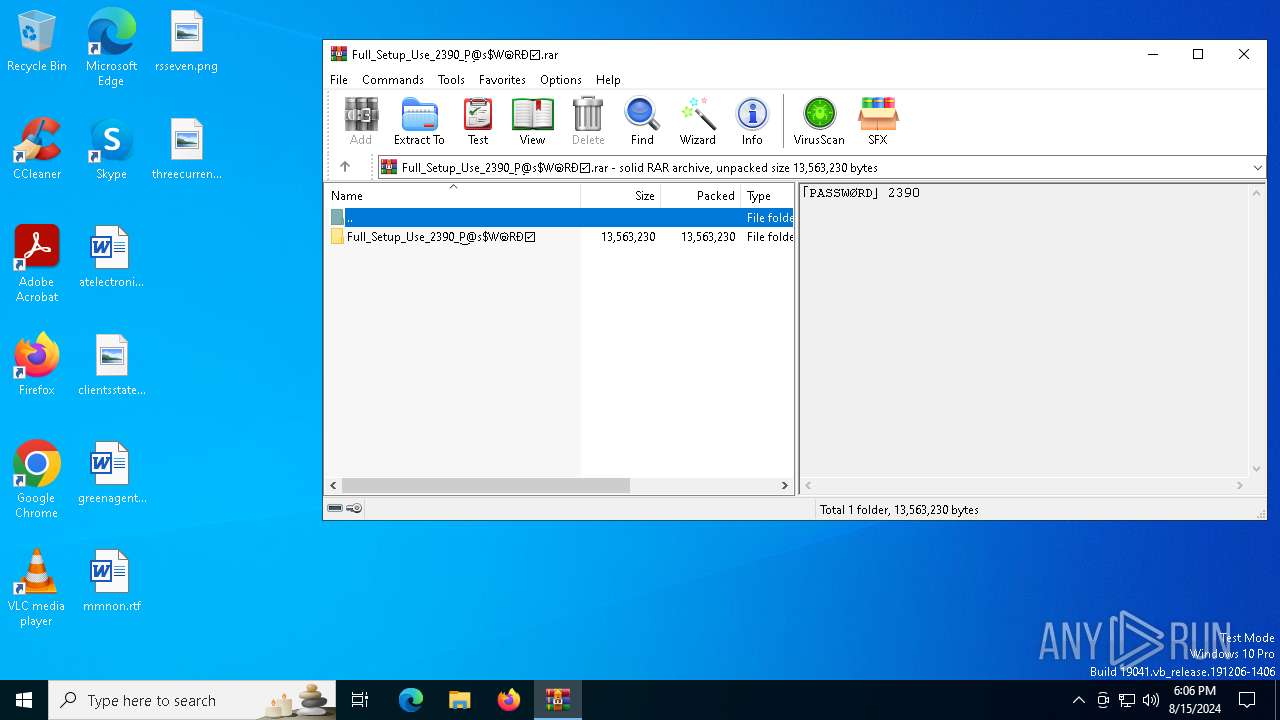
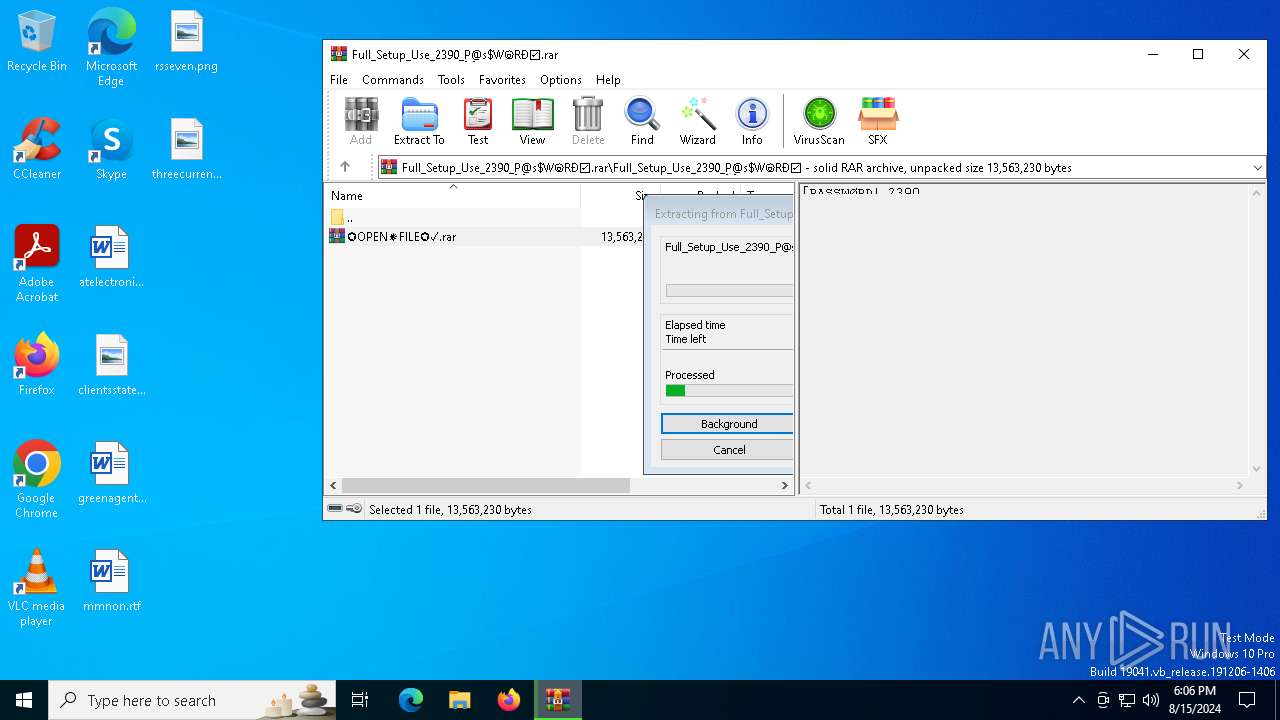
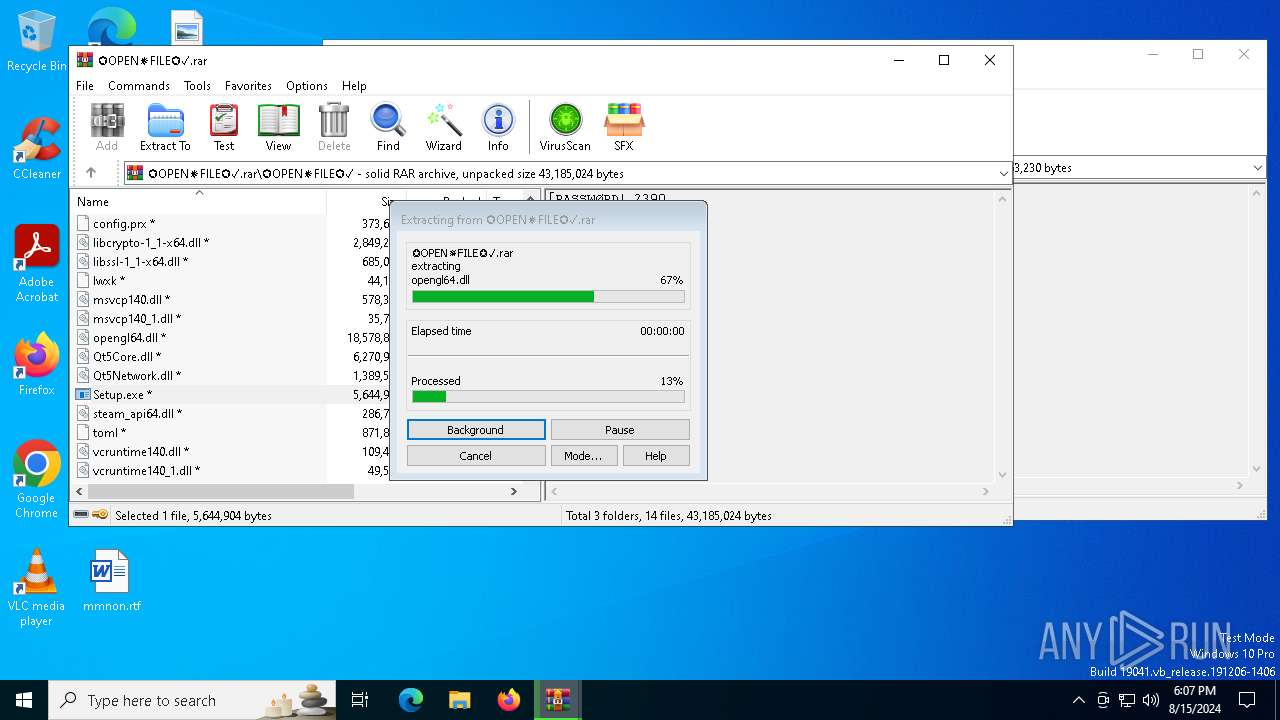
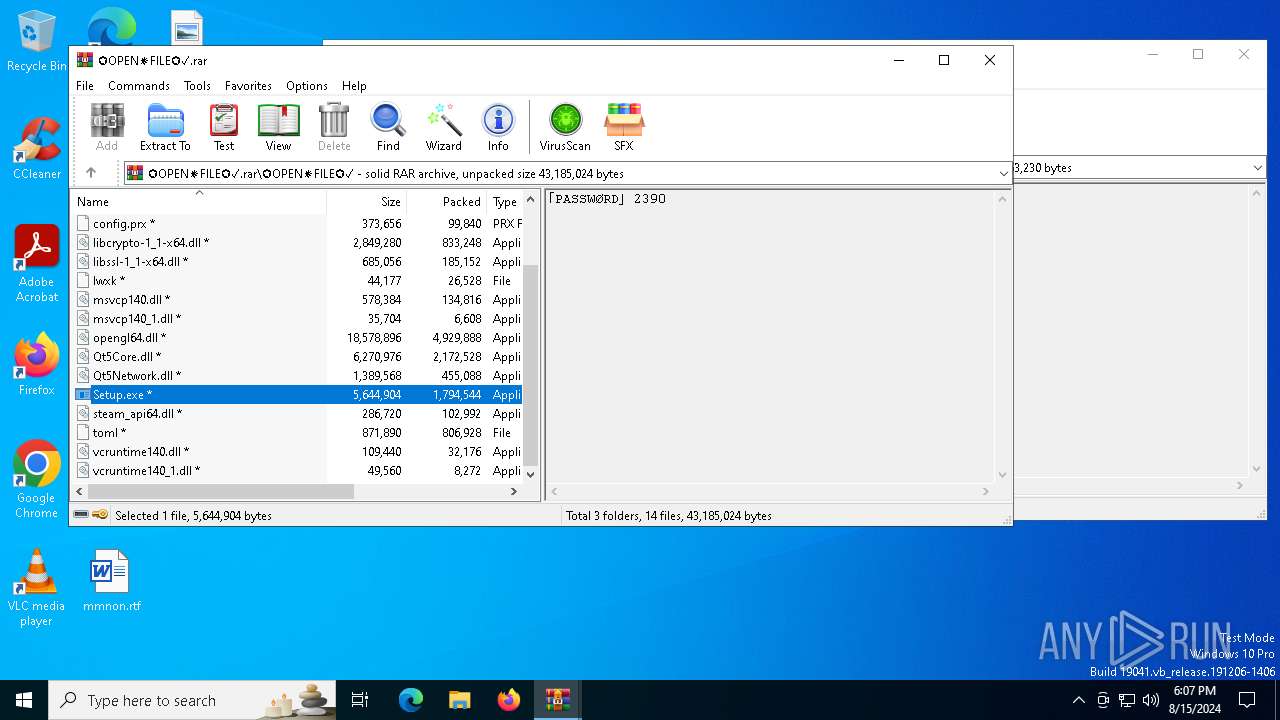
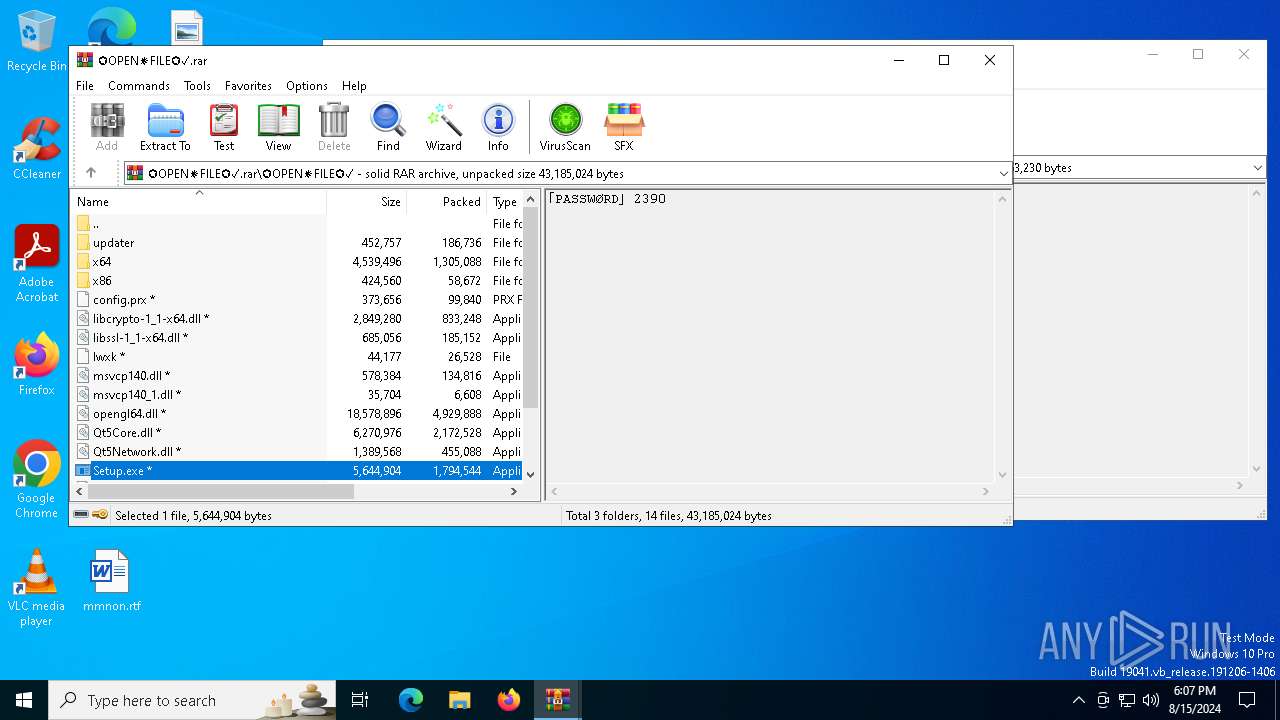
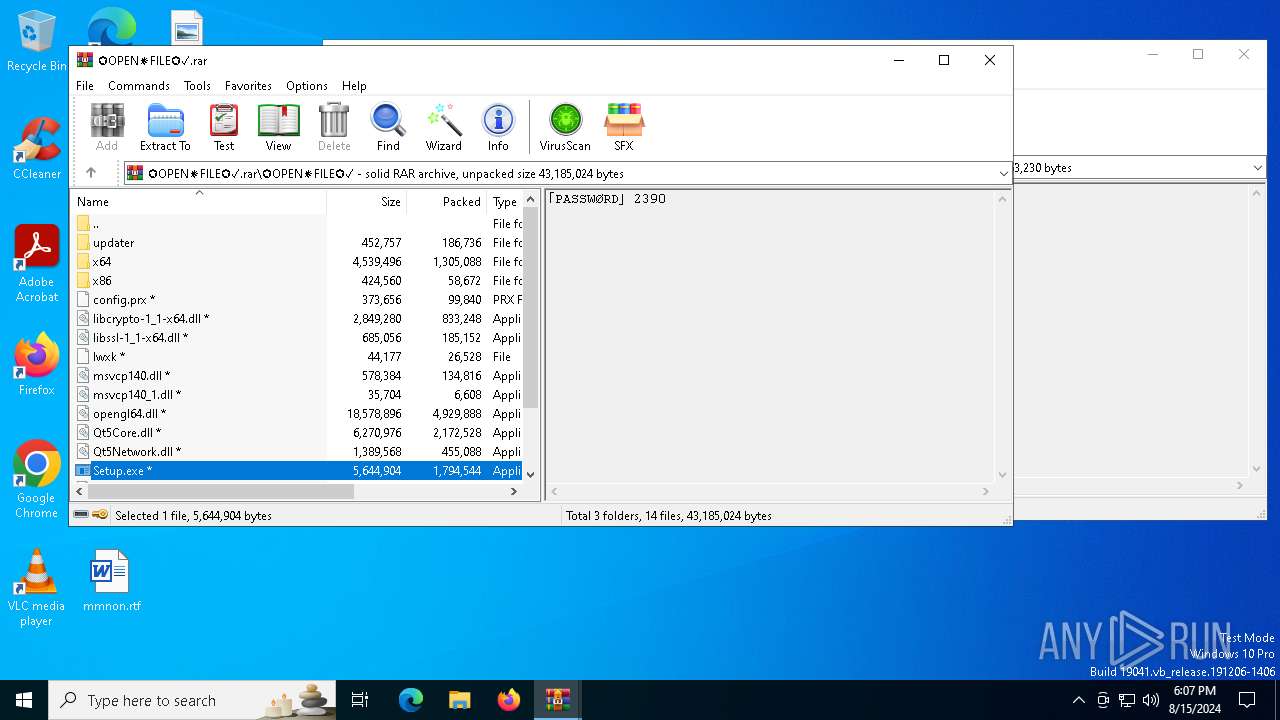
| 1420 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Full_Setup_Use_2390_P͜@s$WⓞRÐ☑.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1544 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 3221225477 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2080 | "C:\Users\admin\AppData\Local\Temp\PE7BDERD3WE1VEAVUNKK9T.exe" | C:\Users\admin\AppData\Local\Temp\PE7BDERD3WE1VEAVUNKK9T.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR Exit code: 0 Version: 7.1.0 Modules
| |||||||||||||||
| 2608 | powershell -exec bypass -f "C:\Users\admin\AppData\Local\Temp\APAKTV8FLY4KIKQA.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2992 | "C:\Users\admin\AppData\Local\Temp\K7RMS1UAOI9PAYDPVZKTBYNFHYNSUX.exe" | C:\Users\admin\AppData\Local\Temp\K7RMS1UAOI9PAYDPVZKTBYNFHYNSUX.exe | SearchIndexer.exe | ||||||||||||
User: admin Company: Argotronic GmbH Integrity Level: MEDIUM Description: ArgusMonitor Setup Exit code: 4294967295 Version: 7.0.4.2720 Modules
| |||||||||||||||
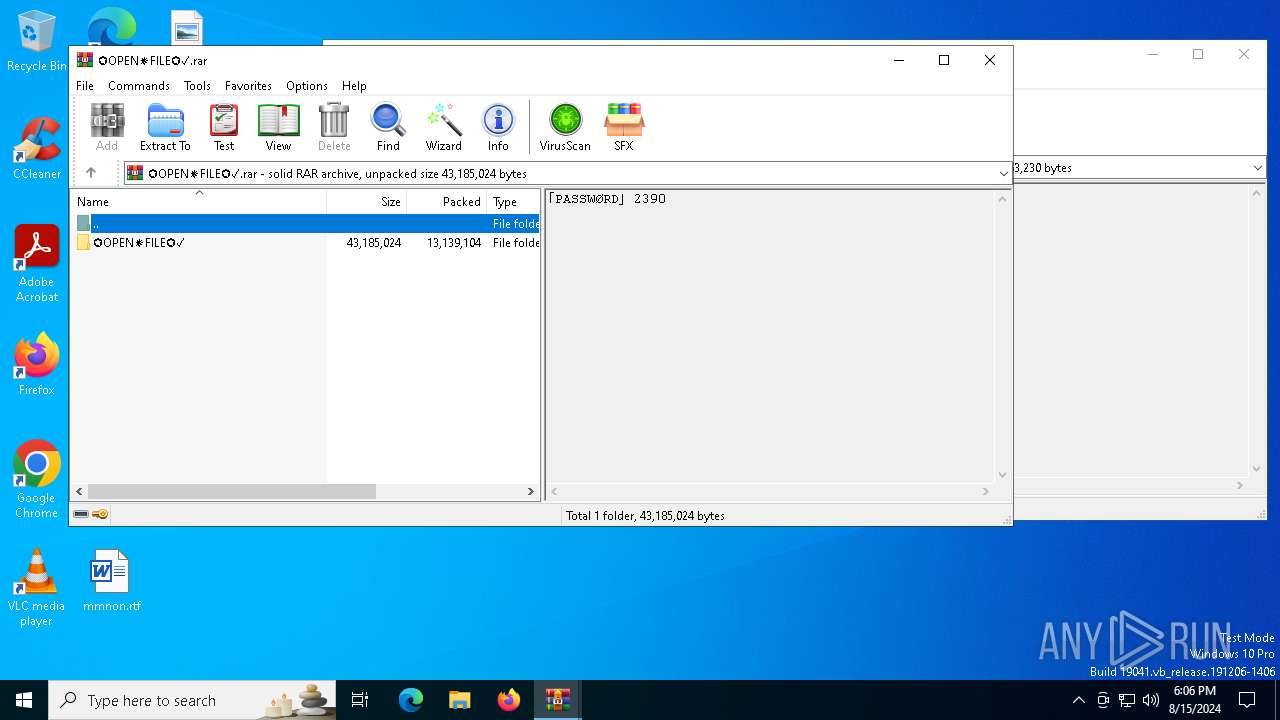
| 3068 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa1420.49047\✪OPEN✵FILE✪✓.rar | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3292 | powershell -exec bypass -f "C:\Users\admin\AppData\Local\Temp\LXY4W4PKBOP3X38HL3JGB.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
55 009
Read events
54 917
Write events
92
Delete events
0
Modification events
| (PID) Process: | (1420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (1420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Full_Setup_Use_2390_P͜@s$WⓞRÐ☑.rar | |||
| (PID) Process: | (1420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Comment |
| Operation: | write | Name: | LeftBorder |
Value: 472 | |||
| (PID) Process: | (1420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
117
Suspicious files
13
Text files
23
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1420 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa1420.49047\✪OPEN✵FILE✪✓.rar | — | |
MD5:— | SHA256:— | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3068.078\✪OPEN✵FILE✪✓\x86\api-ms-win-core-string-l1-1-0.dll | executable | |
MD5:2E5C29FC652F432B89A1AFE187736C4D | SHA256:3807DB7ACF1B40C797E4D4C14A12C3806346AE56B25E205E600BE3E635C18D4F | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3068.078\✪OPEN✵FILE✪✓\x86\api-ms-win-core-profile-l1-1-0.dll | executable | |
MD5:6EE66DCA31C5CCE57740D677C85B4CE7 | SHA256:D00A0EDACE14715BF79DBD17B715D8A74A2300F0ADB1F3FC137EDFB7074C9B0A | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3068.078\✪OPEN✵FILE✪✓\x86\api-ms-win-crt-environment-l1-1-0.dll | executable | |
MD5:AD0CBB9978FCF60D9E9CA45DE6A28D30 | SHA256:6C9C0DC7B36AFE07DFB07DD373FC757FF25DF4793E6384D7A6021471A474F0B9 | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3068.078\✪OPEN✵FILE✪✓\x86\api-ms-win-crt-convert-l1-1-0.dll | executable | |
MD5:3E415147CCD7C712618868BDD7A200CD | SHA256:77B69E829BDC26C7B2474BE6B8A2382345B2957E23046897E40992A8157A7BA1 | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3068.078\✪OPEN✵FILE✪✓\x86\api-ms-win-crt-filesystem-l1-1-0.dll | executable | |
MD5:14F407D94C77B1B0039AE2C89B07A2FF | SHA256:85B1B189CE9E3C6F4D2EFDD4CD82B0807F681BEA2D28851CAAF545990DE99000 | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3068.078\✪OPEN✵FILE✪✓\x86\api-ms-win-crt-locale-l1-1-0.dll | executable | |
MD5:C5D747F96237B6E9AA85C58745D30C80 | SHA256:F16447B5FC7FE6FB8A6699A3CEF1B2B8BA92D408579BCC272D3DD76ACD801E2A | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3068.078\✪OPEN✵FILE✪✓\x86\api-ms-win-core-synch-l1-1-0.dll | executable | |
MD5:979C67BA244E5328A1A2E588FF748E86 | SHA256:8BB38A7A59FBAA792B3D5F34F94580429588C8C592929CBD307AFD5579762ABC | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3068.078\✪OPEN✵FILE✪✓\x86\api-ms-win-core-rtlsupport-l1-1-0.dll | executable | |
MD5:0069FD29263C0DD90314C48BBCE852EF | SHA256:D11093FDC1D5C9213B9B2886CE91DB3DED17EF8DAE1615A8C7FFBC55B8E3F79B | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3068.078\✪OPEN✵FILE✪✓\x86\api-ms-win-core-timezone-l1-1-0.dll | executable | |
MD5:69DF2CCE4528C9E38D04A461BA1F992B | SHA256:A108A8F20DED00E742A1F818EF00EB425990B6B24A2BCD060DEA4D7F06D3F165 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
114
DNS requests
73
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2272 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6720 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6340 | svchost.exe | GET | 206 | 217.20.57.24:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/062b65bc-b6a4-4f5a-8413-7218292237fe?P1=1724201909&P2=404&P3=2&P4=ZRCtZ91n4Pogxt44jI4Hr7DBiicFSth70nq8iSau03OzJuiCUfdFuYuuE80HnhMm3%2b13BKsuEZkCndqbaI5MmQ%3d%3d | unknown | — | — | whitelisted |
6340 | svchost.exe | GET | 206 | 217.20.57.24:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/062b65bc-b6a4-4f5a-8413-7218292237fe?P1=1724201909&P2=404&P3=2&P4=ZRCtZ91n4Pogxt44jI4Hr7DBiicFSth70nq8iSau03OzJuiCUfdFuYuuE80HnhMm3%2b13BKsuEZkCndqbaI5MmQ%3d%3d | unknown | — | — | whitelisted |
6340 | svchost.exe | GET | 206 | 217.20.57.24:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/062b65bc-b6a4-4f5a-8413-7218292237fe?P1=1724201909&P2=404&P3=2&P4=ZRCtZ91n4Pogxt44jI4Hr7DBiicFSth70nq8iSau03OzJuiCUfdFuYuuE80HnhMm3%2b13BKsuEZkCndqbaI5MmQ%3d%3d | unknown | — | — | whitelisted |
2272 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1028 | SystemSettings.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4208 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6012 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
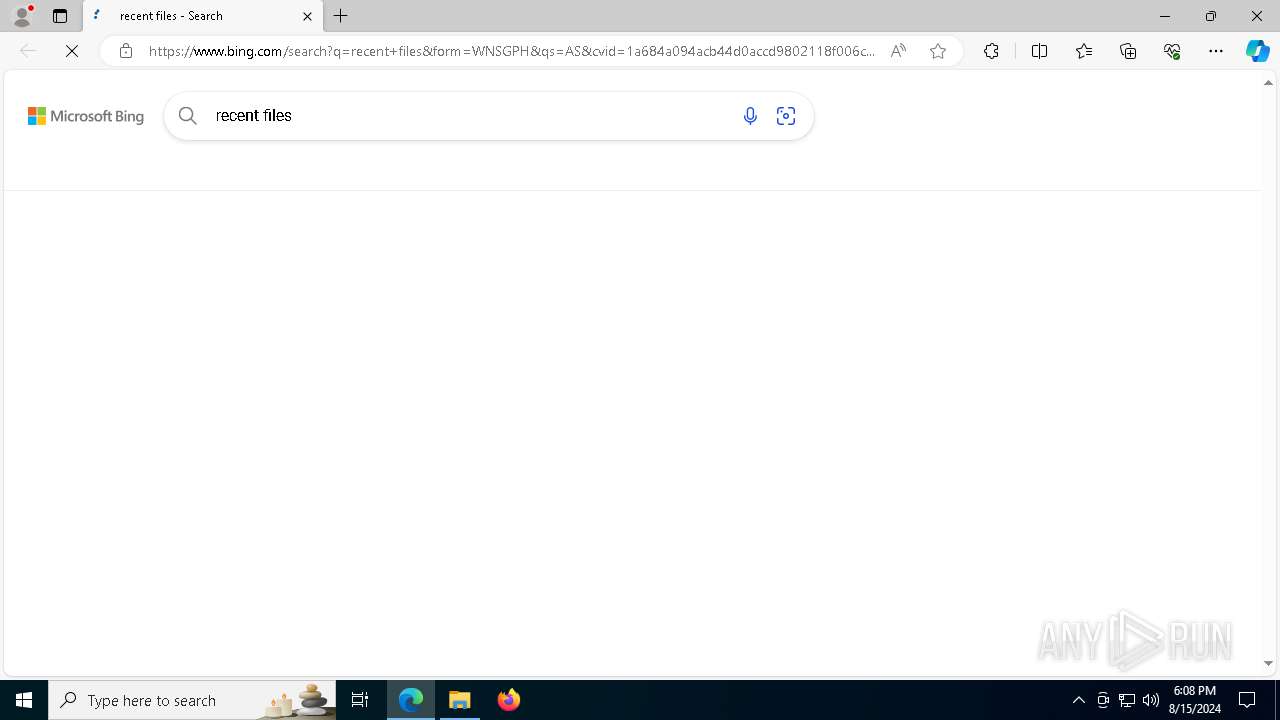
5336 | SearchApp.exe | 92.123.104.25:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2272 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
876 | SearchIndexer.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
2256 | svchost.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
876 | SearchIndexer.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
6520 | SearchIndexer.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
6520 | SearchIndexer.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |