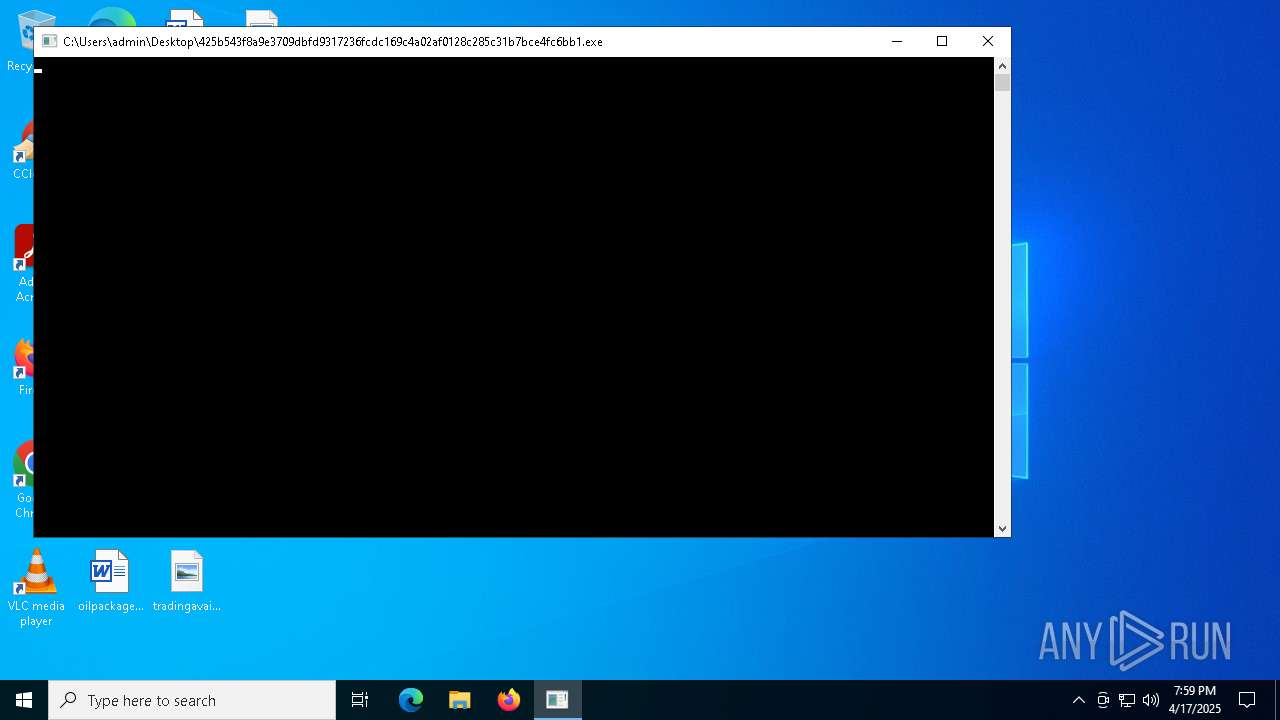
| File name: | 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1 |
| Full analysis: | https://app.any.run/tasks/132cf204-2faf-49bc-b06a-67f1843685e5 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 17, 2025, 19:59:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | F2D5F9466D92077F4C6F03C89C28D504 |
| SHA1: | F25EBE46D064D711B4D66E4322EAD0459F8F3BC9 |
| SHA256: | 425B543F8A9E3709DBFD9317236FCDC169C4A02AF0128C285C31B7BCE4FC6BB1 |
| SSDEEP: | 1536:X1iJFublNaNGllw/Avg0GUx90+oGkKZfhg:XMFublNaNr0GUx90Lf |
MALICIOUS
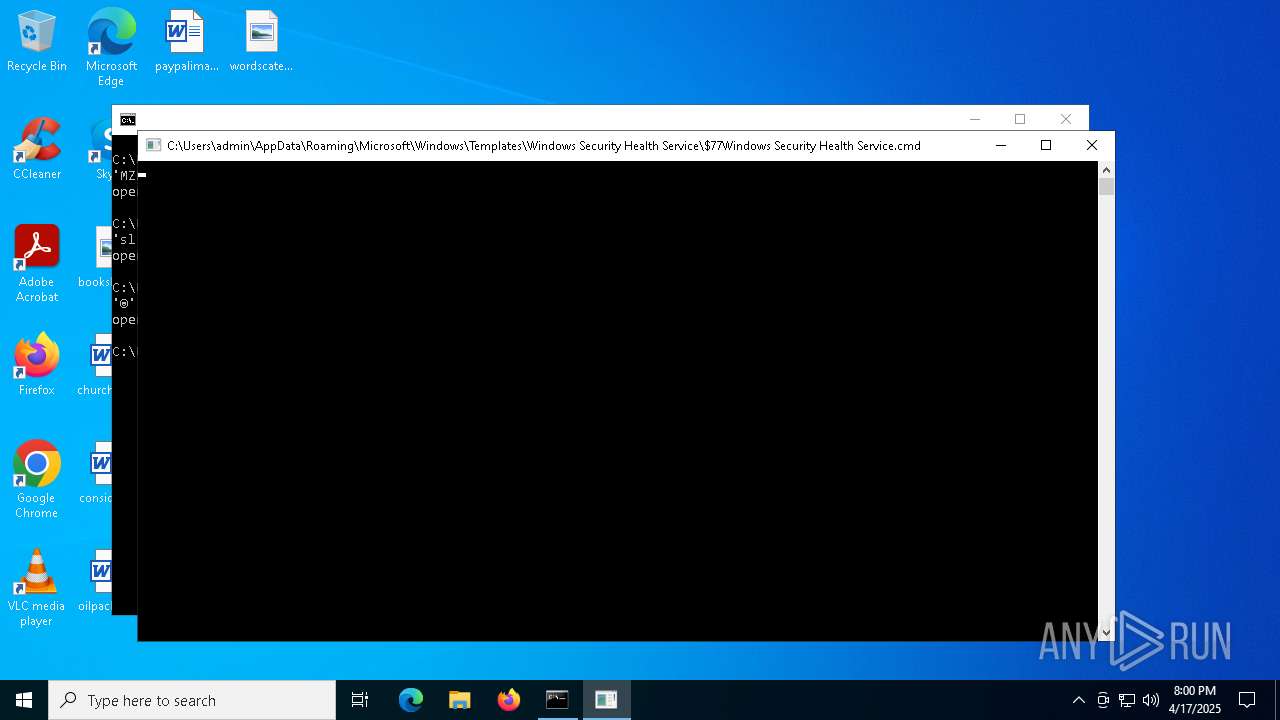
ASYNCRAT has been detected (YARA)
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
- $77Windows Security Health Service.cmd (PID: 2088)
Changes the autorun value in the registry
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
Uses Task Scheduler to run other applications
- $77Windows Security Health Service.cmd (PID: 2088)
Attempting to use instant messaging service
- $77Windows Security Health Service.cmd (PID: 2088)
Stealers network behavior
- $77Windows Security Health Service.cmd (PID: 2088)
SUSPICIOUS
Reads security settings of Internet Explorer
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
- $77Windows Security Health Service.cmd (PID: 2088)
Reads the date of Windows installation
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
- $77Windows Security Health Service.cmd (PID: 2088)
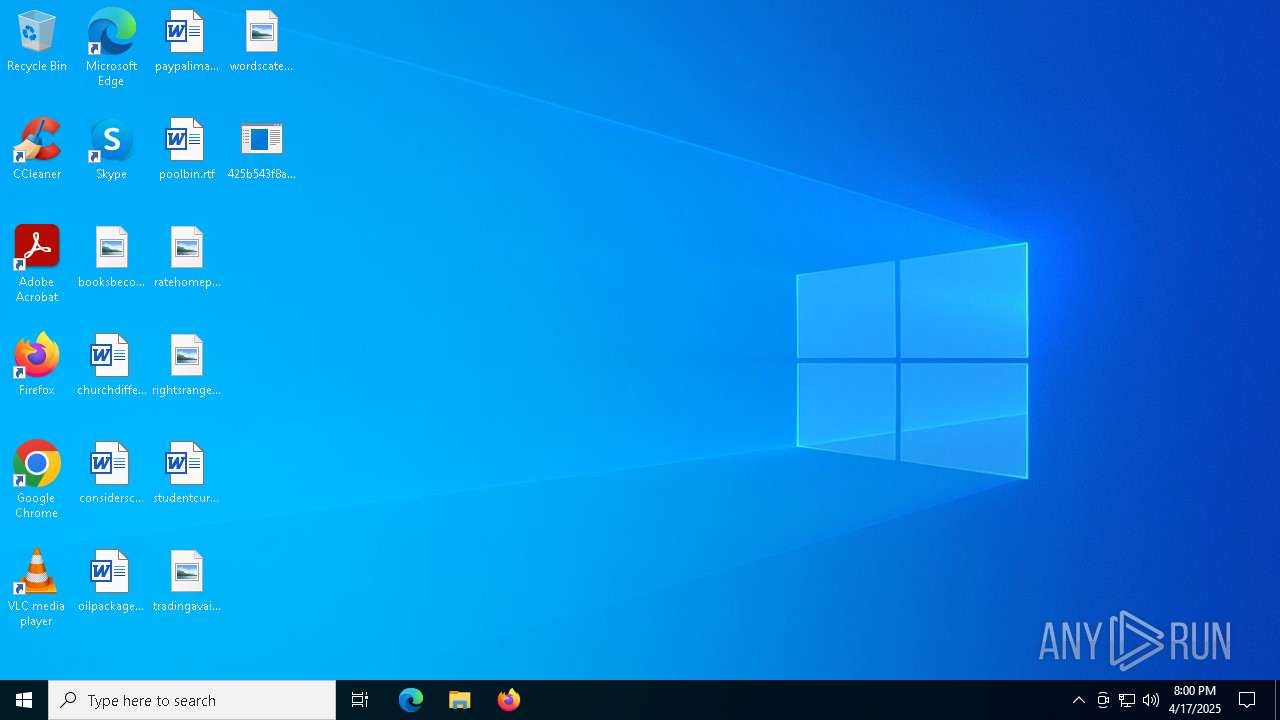
Executable content was dropped or overwritten
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
Suspicious files were dropped or overwritten
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
Uses ATTRIB.EXE to modify file attributes
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
Possible usage of Discord/Telegram API has been detected (YARA)
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
- $77Windows Security Health Service.cmd (PID: 2088)
Executing commands from a ".bat" file
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
Starts CMD.EXE for commands execution
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
- cmd.exe (PID: 6028)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6028)
Executing commands from ".cmd" file
- cmd.exe (PID: 6028)
The process connected to a server suspected of theft
- $77Windows Security Health Service.cmd (PID: 2088)
Application launched itself
- cmd.exe (PID: 6028)
Connects to unusual port
- $77Windows Security Health Service.cmd (PID: 2088)
INFO
Checks supported languages
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
- $77Windows Security Health Service.cmd (PID: 2088)
Reads the computer name
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
- $77Windows Security Health Service.cmd (PID: 2088)
Reads the machine GUID from the registry
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
- $77Windows Security Health Service.cmd (PID: 2088)
Checks proxy server information
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
- $77Windows Security Health Service.cmd (PID: 2088)
- slui.exe (PID: 4688)
Creates files or folders in the user directory
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
Process checks computer location settings
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
- $77Windows Security Health Service.cmd (PID: 2088)
Create files in a temporary directory
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
Auto-launch of the file from Registry key
- 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe (PID: 5416)
Manual execution by a user
- $77Windows Security Health Service.cmd (PID: 2088)
Auto-launch of the file from Task Scheduler
- $77Windows Security Health Service.cmd (PID: 2088)
Reads the software policy settings
- $77Windows Security Health Service.cmd (PID: 2088)
- slui.exe (PID: 4688)
Reads Environment values
- $77Windows Security Health Service.cmd (PID: 2088)
Disables trace logs
- $77Windows Security Health Service.cmd (PID: 2088)
Attempting to use instant messaging service
- $77Windows Security Health Service.cmd (PID: 2088)
- svchost.exe (PID: 2196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(5416) 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe
Discord-Webhook-Tokens (1)1362208671114723479/LvdkCF57ZASLhyMey8E8SalpGbpRjudiP5GtndFuJHj6Qkuha-CXPrshzVau_JY7H3k6
Discord-Info-Links
1362208671114723479/LvdkCF57ZASLhyMey8E8SalpGbpRjudiP5GtndFuJHj6Qkuha-CXPrshzVau_JY7H3k6
Get Webhook Infohttps://discord.com/api/webhooks/1362208671114723479/LvdkCF57ZASLhyMey8E8SalpGbpRjudiP5GtndFuJHj6Qkuha-CXPrshzVau_JY7H3k6
(PID) Process(2088) $77Windows Security Health Service.cmd
Discord-Webhook-Tokens (1)1362208671114723479/LvdkCF57ZASLhyMey8E8SalpGbpRjudiP5GtndFuJHj6Qkuha-CXPrshzVau_JY7H3k6
Discord-Info-Links
1362208671114723479/LvdkCF57ZASLhyMey8E8SalpGbpRjudiP5GtndFuJHj6Qkuha-CXPrshzVau_JY7H3k6
Get Webhook Infohttps://discord.com/api/webhooks/1362208671114723479/LvdkCF57ZASLhyMey8E8SalpGbpRjudiP5GtndFuJHj6Qkuha-CXPrshzVau_JY7H3k6
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:17 01:32:57+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 44032 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xca1e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.1.1.2 |
| ProductVersionNumber: | 1.1.1.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | Windows Security Health Service |
| FileVersion: | 1.1.1.2 |
| InternalName: | Windows Security Health Service.cmd |
| LegalCopyright: | |
| OriginalFileName: | Windows Security Health Service.cmd |
| ProductVersion: | 1.1.1.2 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
137
Monitored processes
17
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | $77Windows Security Health Service.cmd | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1276 | "C:\Windows\System32\attrib.exe" +s +h "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Windows Security Health Service\$77Windows Security Health Service.cmd" | C:\Windows\System32\attrib.exe | — | 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Windows Security Health Service\$77Windows Security Health Service.cmd" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Windows Security Health Service\$77Windows Security Health Service.cmd | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Windows Security Health Service Version: 1.1.1.2 Modules
ims-api(PID) Process(2088) $77Windows Security Health Service.cmd Discord-Webhook-Tokens (1)1362208671114723479/LvdkCF57ZASLhyMey8E8SalpGbpRjudiP5GtndFuJHj6Qkuha-CXPrshzVau_JY7H3k6 Discord-Info-Links 1362208671114723479/LvdkCF57ZASLhyMey8E8SalpGbpRjudiP5GtndFuJHj6Qkuha-CXPrshzVau_JY7H3k6 Get Webhook Infohttps://discord.com/api/webhooks/1362208671114723479/LvdkCF57ZASLhyMey8E8SalpGbpRjudiP5GtndFuJHj6Qkuha-CXPrshzVau_JY7H3k6 | |||||||||||||||
| 2140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | attrib.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | "C:\Windows\System32\schtasks.exe" /create /sc daily /tn "Windows Security Health Service_Task-DAILY-21PM" /TR "%MyFile%" /ST 21:00 | C:\Windows\System32\schtasks.exe | — | $77Windows Security Health Service.cmd | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4452 | "C:\Windows\System32\attrib.exe" +s +h "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Windows Security Health Service" | C:\Windows\System32\attrib.exe | — | 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4688 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4812 | C:\WINDOWS\system32\cmd.exe /K "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Windows Security Health Service\$77Windows Security Health Service.cmd" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5376 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 191
Read events
9 176
Write events
15
Delete events
0
Modification events
| (PID) Process: | (5416) 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | (default) |
Value: "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Windows Security Health Service\$77Windows Security Health Service.cmd" | |||
| (PID) Process: | (2088) $77Windows Security Health Service.cmd | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\$77Windows Security Health Service_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2088) $77Windows Security Health Service.cmd | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\$77Windows Security Health Service_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2088) $77Windows Security Health Service.cmd | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\$77Windows Security Health Service_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2088) $77Windows Security Health Service.cmd | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\$77Windows Security Health Service_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2088) $77Windows Security Health Service.cmd | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\$77Windows Security Health Service_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2088) $77Windows Security Health Service.cmd | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\$77Windows Security Health Service_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2088) $77Windows Security Health Service.cmd | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\$77Windows Security Health Service_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2088) $77Windows Security Health Service.cmd | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\$77Windows Security Health Service_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2088) $77Windows Security Health Service.cmd | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\$77Windows Security Health Service_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5416 | 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Windows Security Health Service\$77Windows Security Health Service.cmd | executable | |
MD5:F2D5F9466D92077F4C6F03C89C28D504 | SHA256:425B543F8A9E3709DBFD9317236FCDC169C4A02AF0128C285C31B7BCE4FC6BB1 | |||
| 5416 | 425b543f8a9e3709dbfd9317236fcdc169c4a02af0128c285c31b7bce4fc6bb1.exe | C:\Users\admin\AppData\Local\Temp\tmp1049.tmp.bat | text | |
MD5:1E399A53444A4E103FBACAEA90AE6335 | SHA256:F1E9E0FC389F7D82CAC3C9E4512A85F61359ACA5E1CECEF917B81CF981C9DF97 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
42
DNS requests
17
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 4.175.87.197:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
5936 | SIHClient.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5936 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 40.69.42.241:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
5936 | SIHClient.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
5936 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5936 | SIHClient.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5936 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
5936 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 4.175.87.197:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5936 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2088 | $77Windows Security Health Service.cmd | 162.159.138.232:443 | discord.com | CLOUDFLARENET | — | whitelisted |
2088 | $77Windows Security Health Service.cmd | 147.185.221.27:37035 | traffic-equipment.gl.at.ply.gg | PLAYIT-GG | US | malicious |
5936 | SIHClient.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5936 | SIHClient.exe | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
discord.com |
| whitelisted |
traffic-equipment.gl.at.ply.gg |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
2088 | $77Windows Security Health Service.cmd | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
2088 | $77Windows Security Health Service.cmd | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Discord |
2196 | svchost.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
2088 | $77Windows Security Health Service.cmd | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
— | — | Misc activity | SUSPICIOUS [ANY.RUN] Sent Host Name in HTTP POST Body |