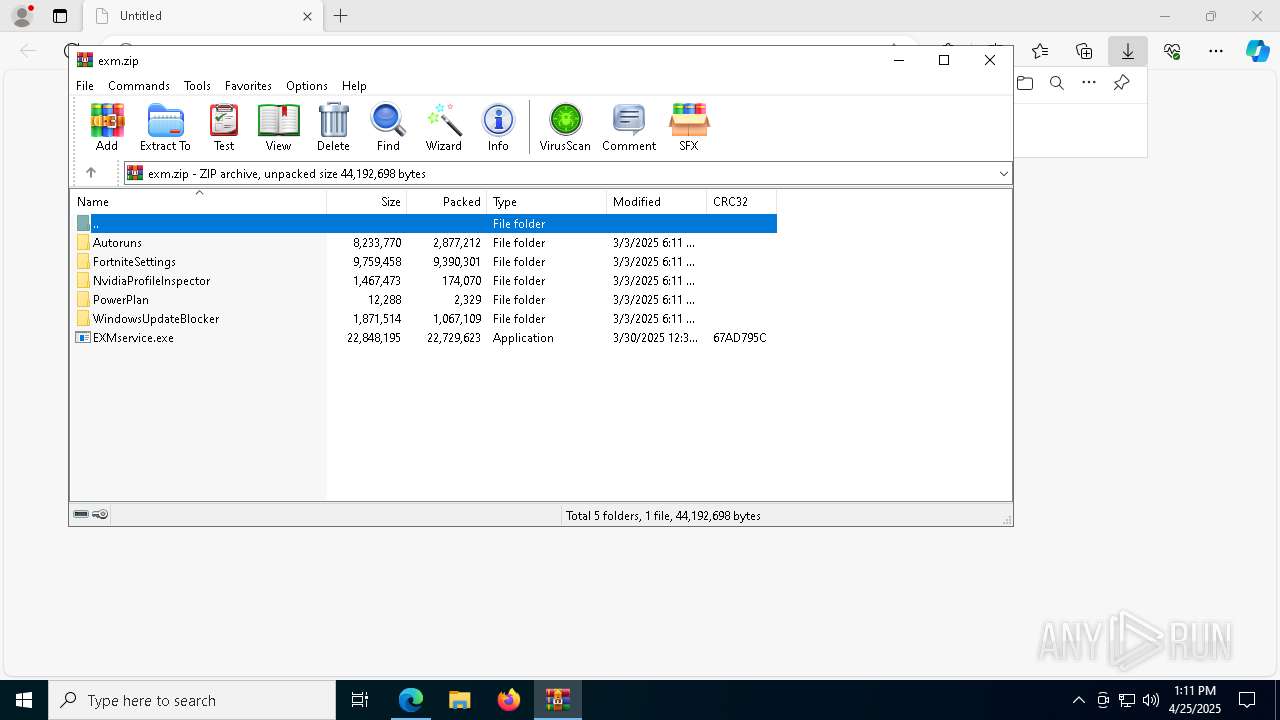
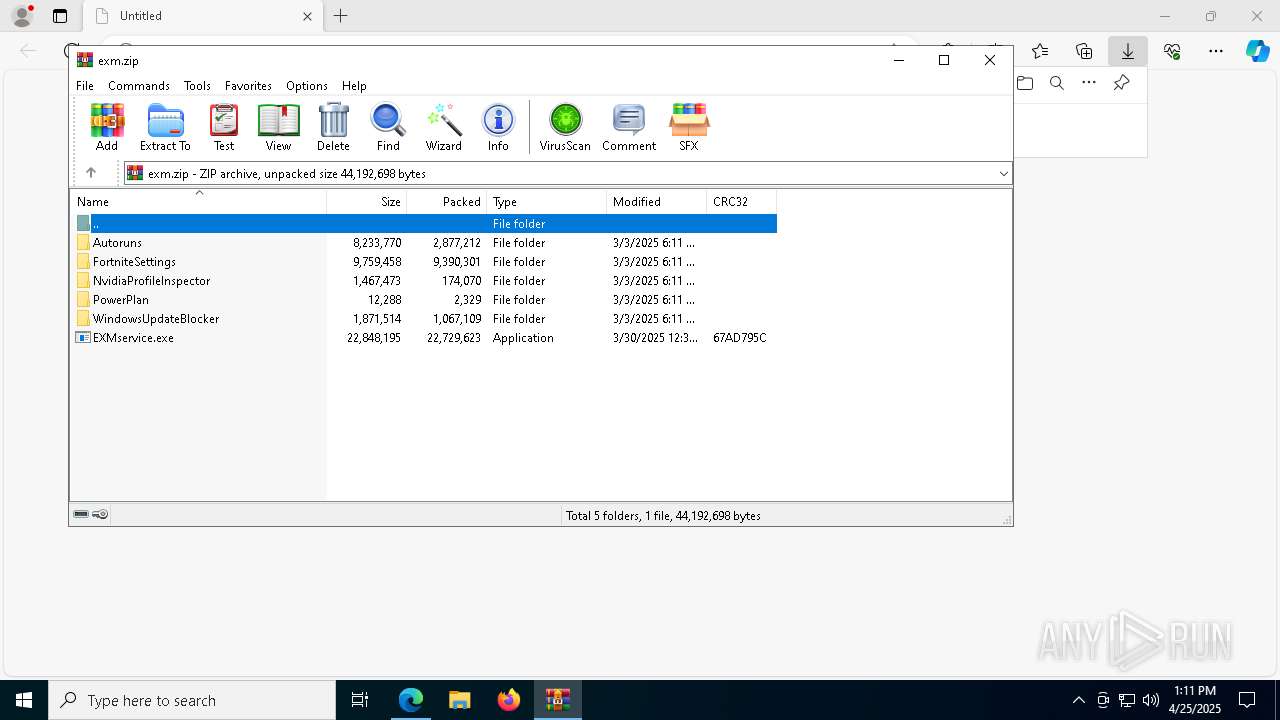
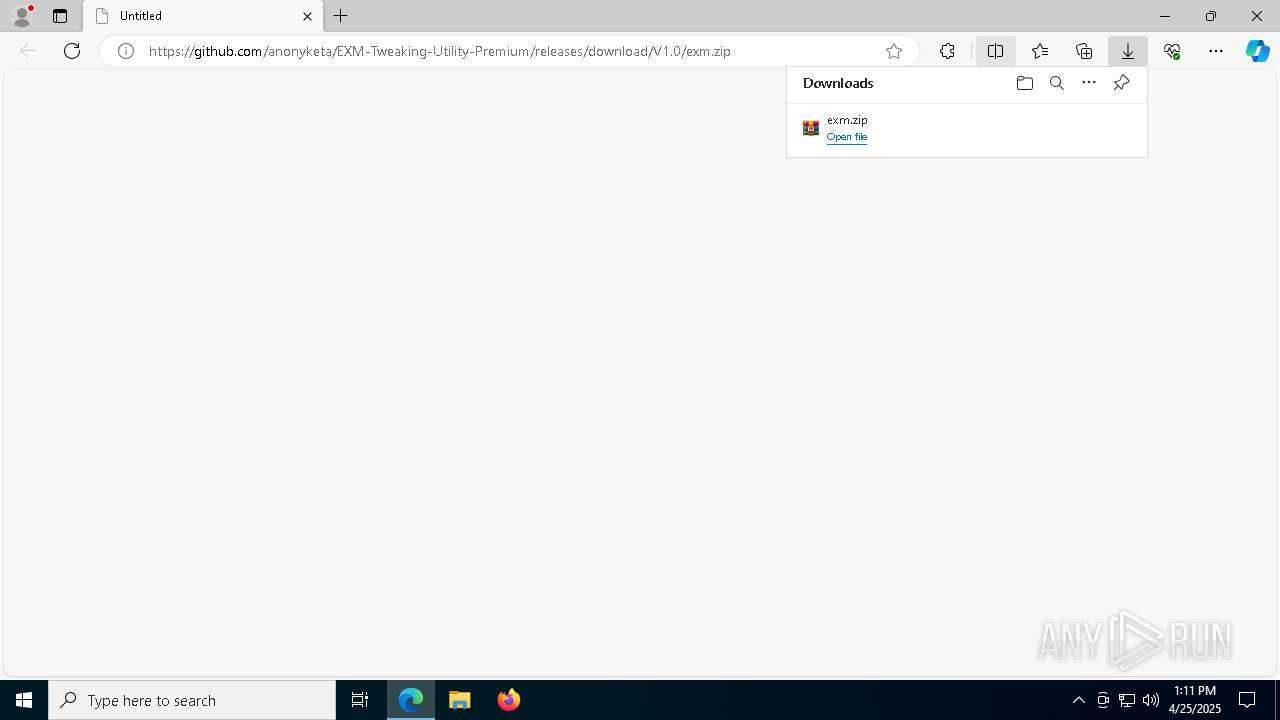
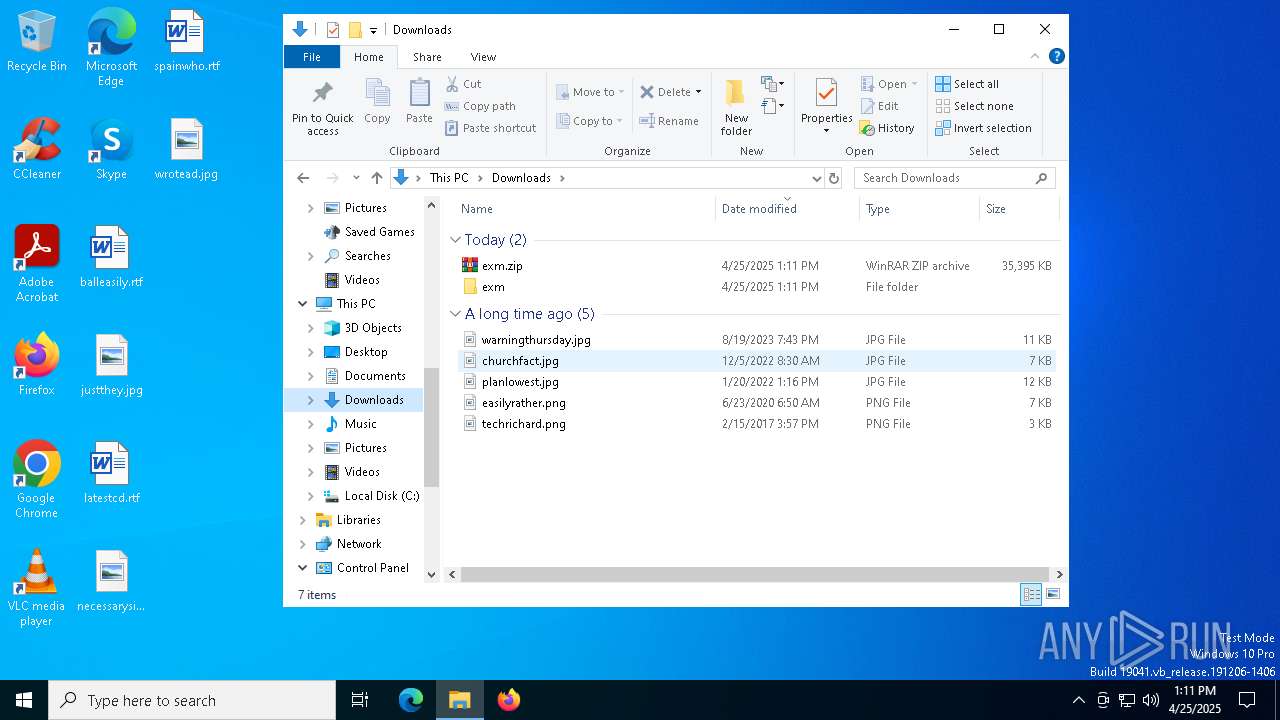
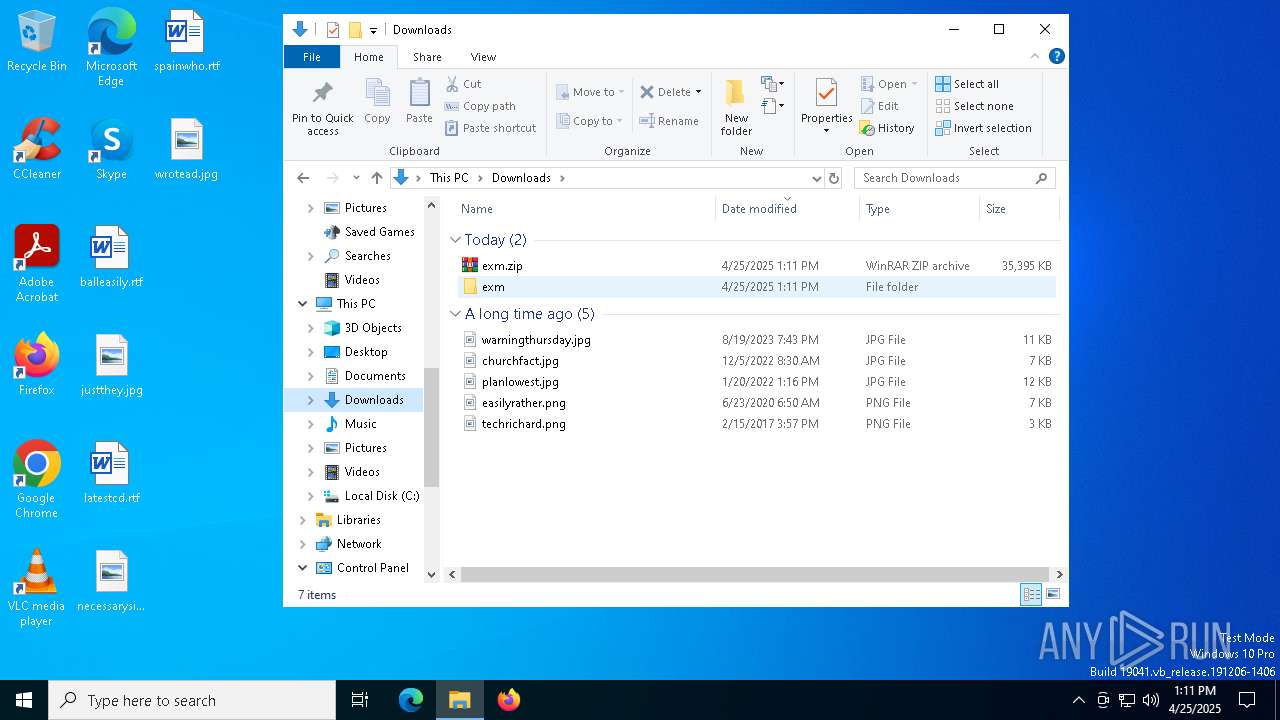
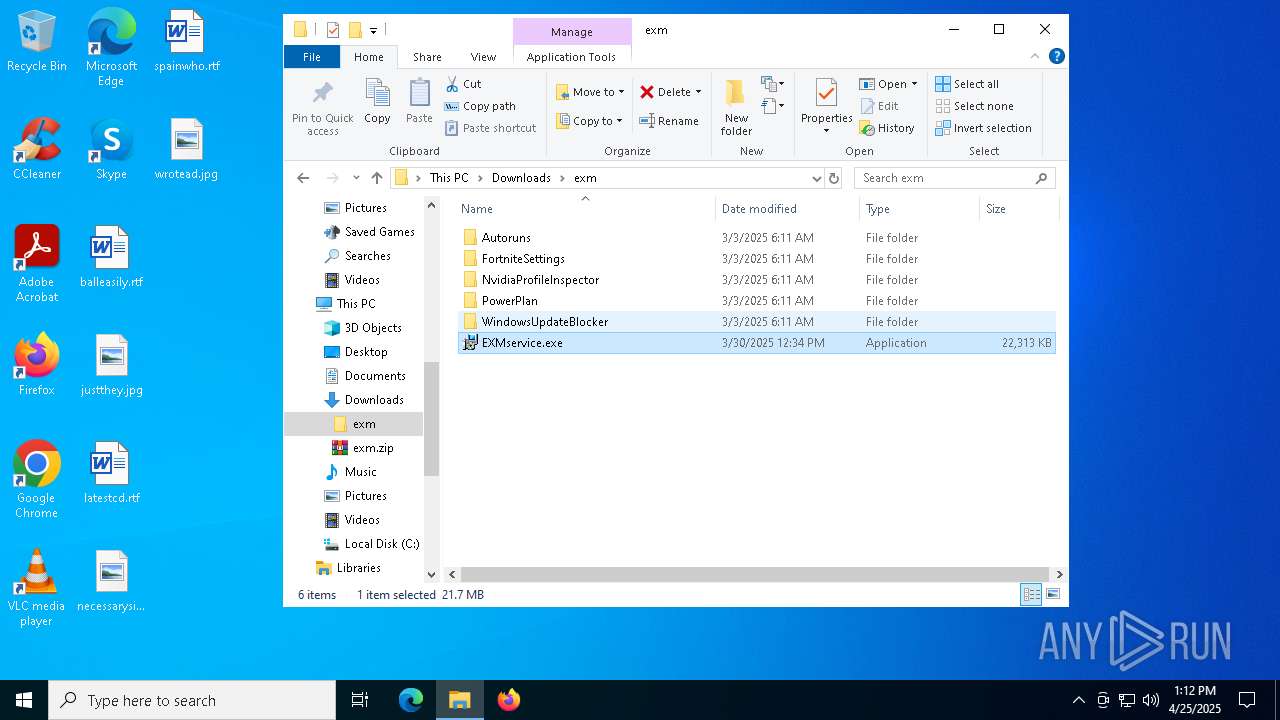
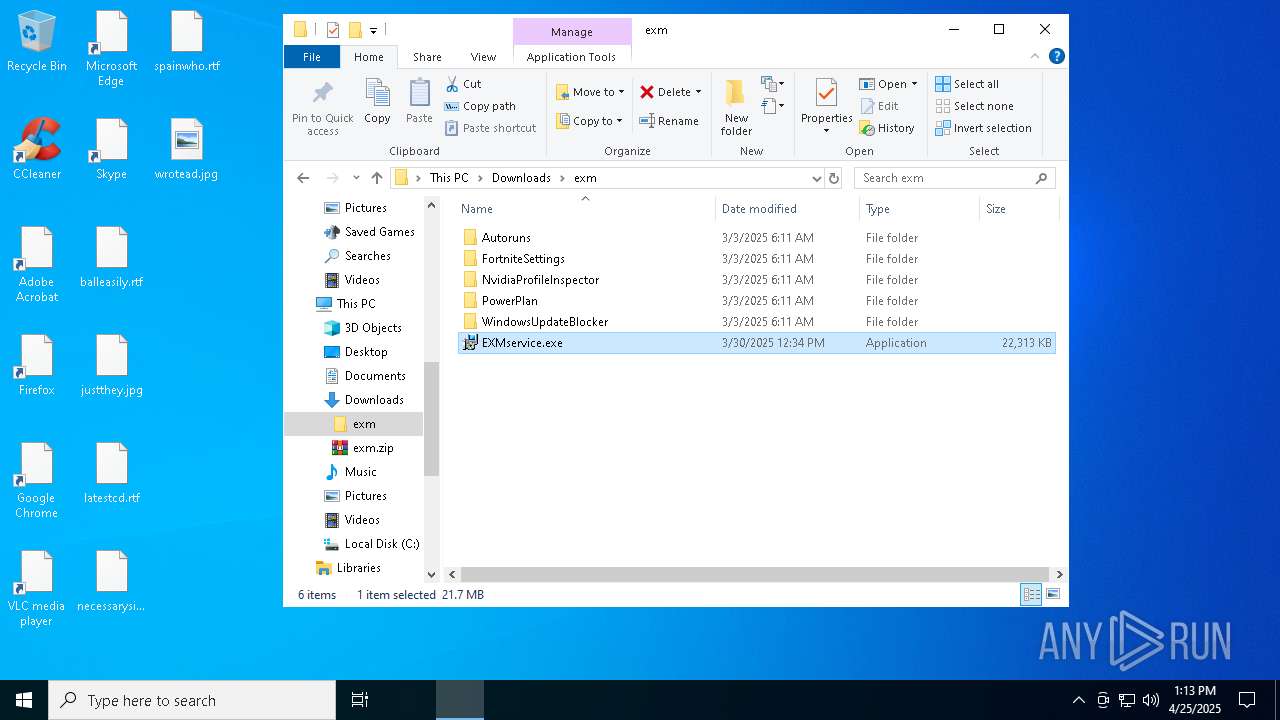
| URL: | https://github.com/anonyketa/EXM-Tweaking-Utility-Premium/releases/download/V1.0/exm.zip |
| Full analysis: | https://app.any.run/tasks/7bd4e4d7-d878-476a-8d73-1391b12c225b |
| Verdict: | Malicious activity |
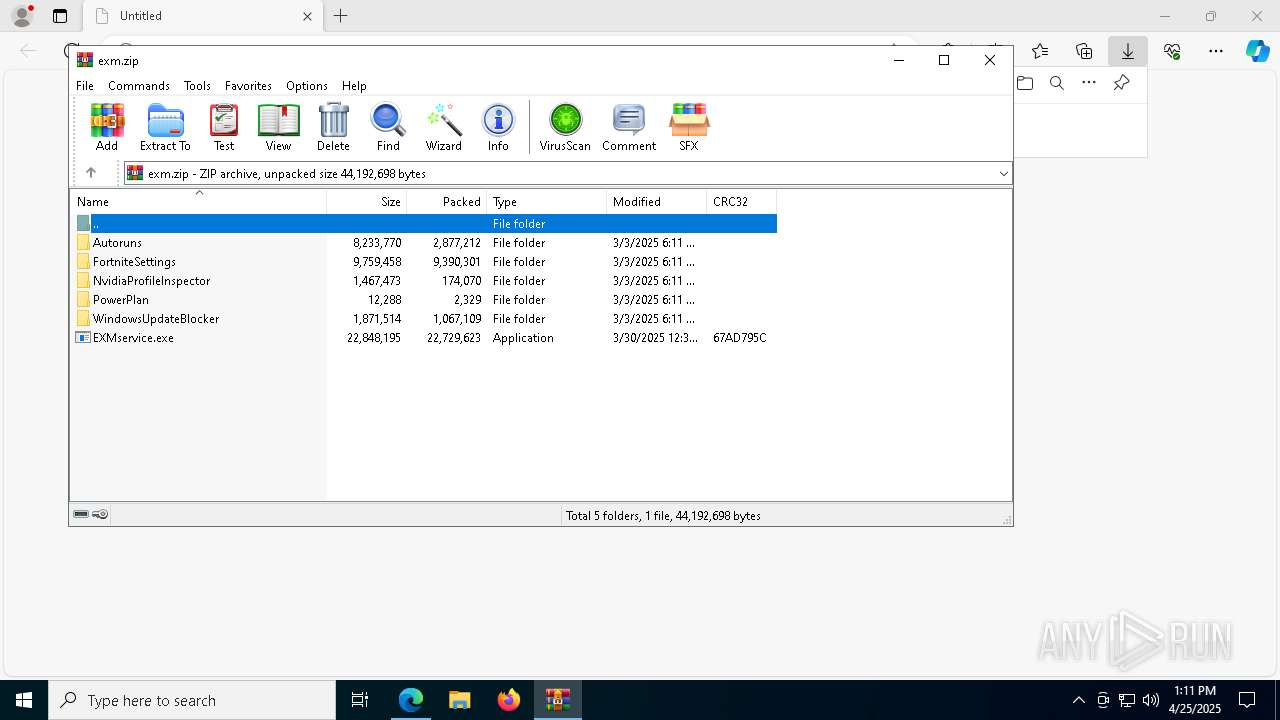
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | April 25, 2025, 13:11:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | ADE6D5866B2D5BB34EE4090E1A3E63D6 |
| SHA1: | 61F8E77D38570F9E287CF44FFDC2FFF9224D9167 |
| SHA256: | 424516C710F24CABA353065ABA890A21E2DEFD20F003F2E5577E6936F29E81CA |
| SSDEEP: | 3:N8tEd0+TAsZM2NRJMSrkC4xKLkVn:2ui+bM2NRJMmGVn |
MALICIOUS
GENERIC has been found (auto)
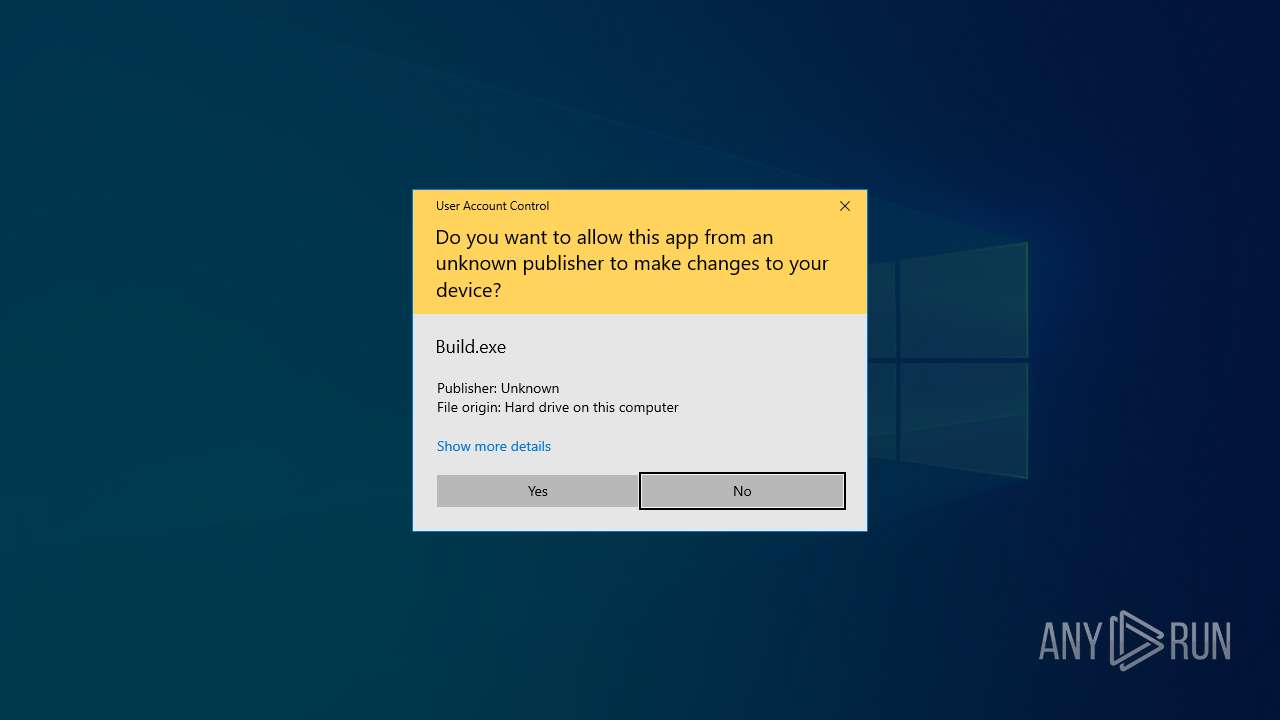
- Build.exe (PID: 7376)
Executing a file with an untrusted certificate
- hacn.exe (PID: 6620)
- based.exe (PID: 1244)
- based.exe (PID: 7204)
- hacn.exe (PID: 7244)
- crss.exe (PID: 8500)
- CompPkgSrv.exe (PID: 8564)
- setup.exe (PID: 8276)
- crss.exe (PID: 456)
- setup.exe (PID: 2136)
- CompPkgSrv.exe (PID: 8552)
SFX dropper has been detected
- Build.exe (PID: 7992)
Adds path to the Windows Defender exclusion list
- based.exe (PID: 7204)
- cmd.exe (PID: 7240)
- cmd.exe (PID: 4608)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 7356)
Changes Windows Defender settings
- cmd.exe (PID: 7356)
- cmd.exe (PID: 7240)
- cmd.exe (PID: 4608)
- setup.exe (PID: 2136)
Changes settings for real-time protection
- powershell.exe (PID: 6828)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 6828)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 6828)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 6828)
Changes Controlled Folder Access settings
- powershell.exe (PID: 6828)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 6828)
Bypass execution policy to execute commands
- powershell.exe (PID: 7676)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7144)
STORMKITTY has been detected (YARA)
- csrss.exe (PID: 1760)
Uses Task Scheduler to run other applications
- svchost.exe (PID: 7580)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 8524)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 6828)
Stealers network behavior
- csrss.exe (PID: 1760)
BLANKGRABBER has been detected (SURICATA)
- based.exe (PID: 7204)
DISCORDGRABBER has been detected (YARA)
- based.exe (PID: 7204)
GROWTOPIA has been detected (YARA)
- based.exe (PID: 7204)
COINMINER has been found (auto)
- s.exe (PID: 7036)
- setup1.exe (PID: 7464)
Attempting to use instant messaging service
- csrss.exe (PID: 1760)
Adds process to the Windows Defender exclusion list
- setup.exe (PID: 2136)
Starts REAGENTC.EXE to disable the Windows Recovery Environment
- ReAgentc.exe (PID: 7884)
Vulnerable driver has been detected
- updater.exe (PID: 8640)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2196)
SUSPICIOUS
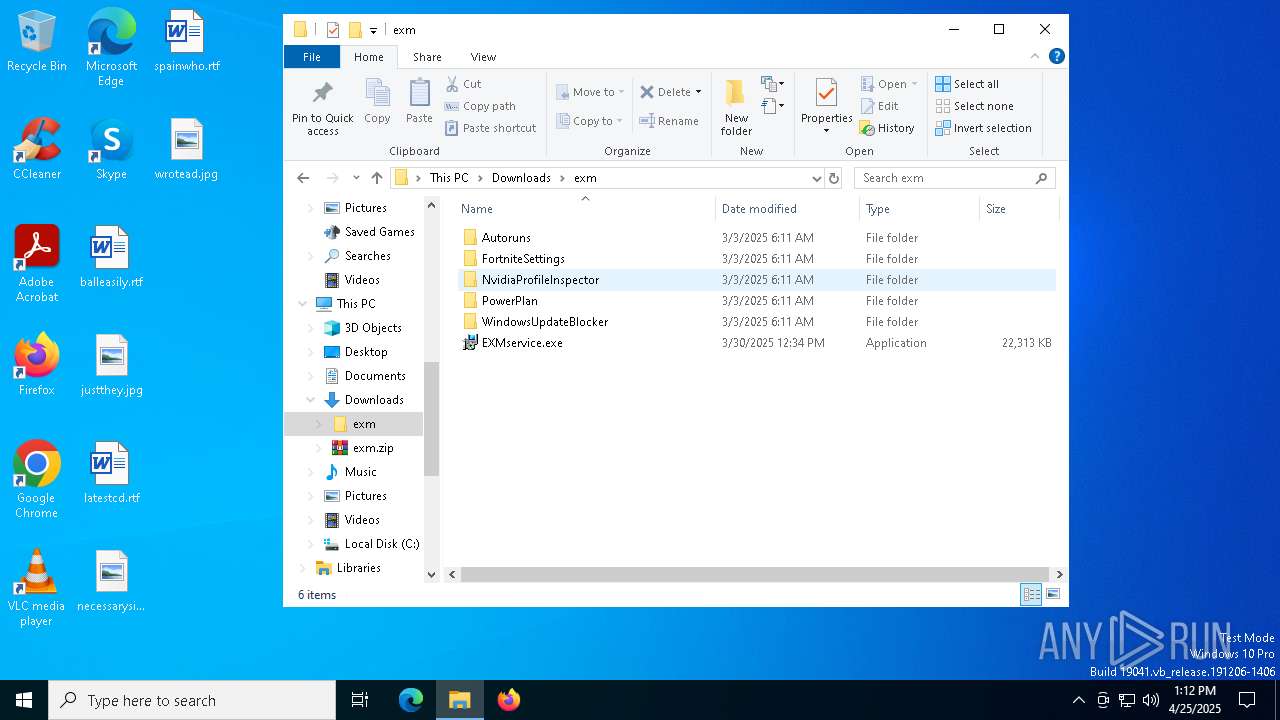
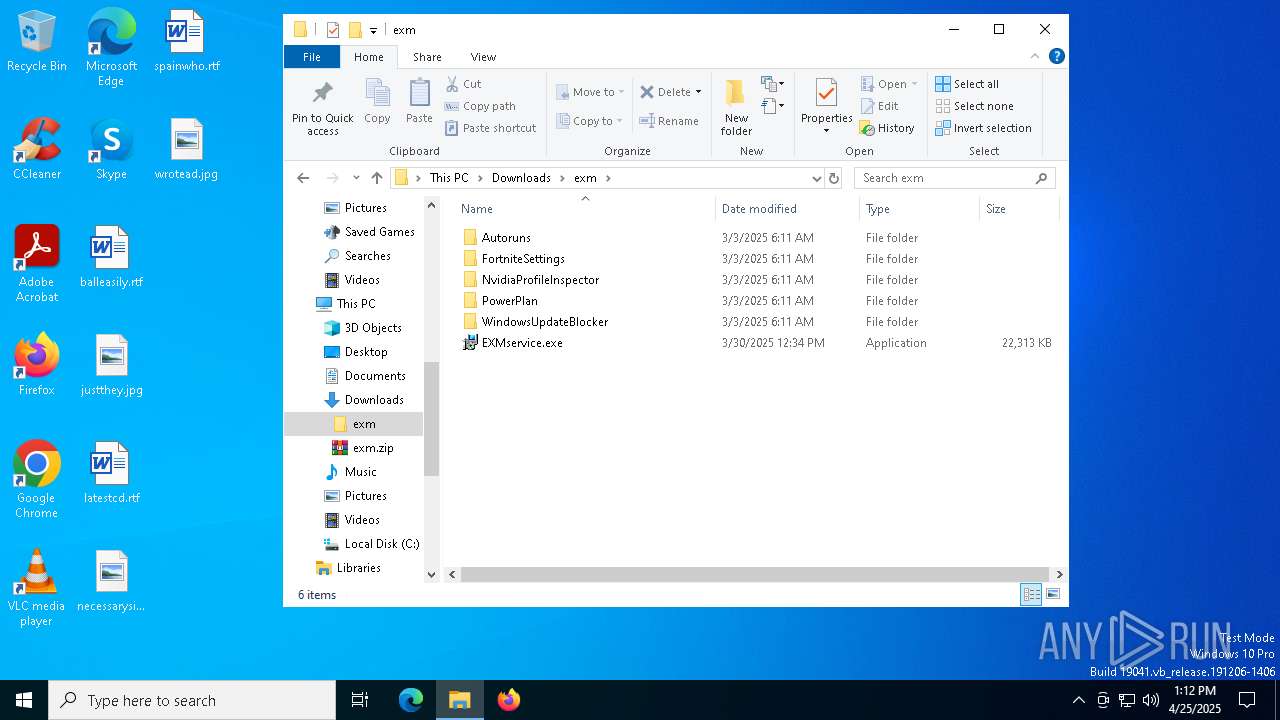
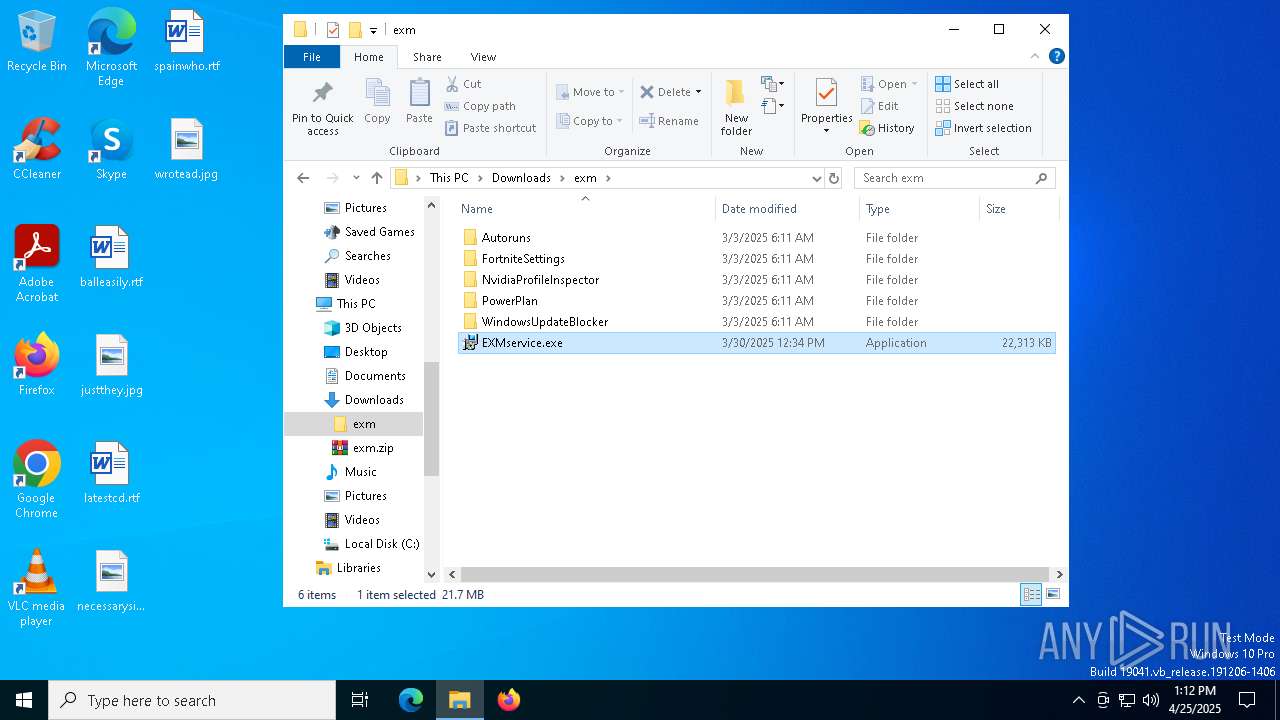
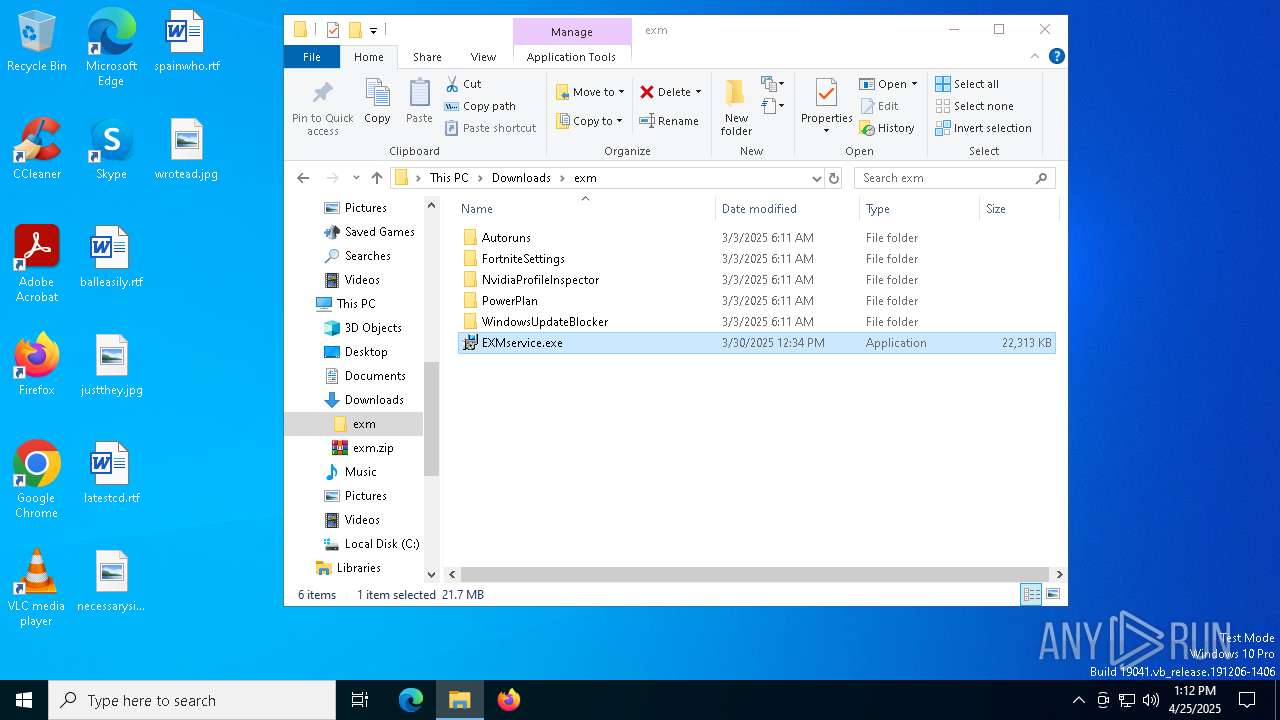
Process drops python dynamic module
- EXMservice.exe (PID: 7548)
- based.exe (PID: 1244)
- hacn.exe (PID: 6620)
- u1CFBzp7.exe (PID: 8076)
- CompPkgSrv.exe (PID: 8564)
- crss.exe (PID: 8500)
- setup.exe (PID: 8276)
Executable content was dropped or overwritten
- EXMservice.exe (PID: 7548)
- Build.exe (PID: 7376)
- hacn.exe (PID: 6620)
- based.exe (PID: 1244)
- based.exe (PID: 7204)
- bound.exe (PID: 8120)
- svchost.exe (PID: 7580)
- csc.exe (PID: 8988)
- u1CFBzp7.exe (PID: 8076)
- s.exe (PID: 7036)
- CompPkgSrv.exe (PID: 8564)
- crss.exe (PID: 8500)
- setup.exe (PID: 8276)
- powershell.exe (PID: 7344)
- setup0.exe (PID: 8208)
- Dism.exe (PID: 8628)
- setup1.exe (PID: 7464)
- Dism.exe (PID: 7816)
- Dism.exe (PID: 5172)
- update.exe (PID: 9040)
- updater.exe (PID: 8640)
Process drops legitimate windows executable
- EXMservice.exe (PID: 7548)
- Build.exe (PID: 7376)
- based.exe (PID: 1244)
- hacn.exe (PID: 6620)
- CompPkgSrv.exe (PID: 8564)
- crss.exe (PID: 8500)
- setup.exe (PID: 8276)
- u1CFBzp7.exe (PID: 8076)
The process drops C-runtime libraries
- EXMservice.exe (PID: 7548)
- hacn.exe (PID: 6620)
- based.exe (PID: 1244)
- CompPkgSrv.exe (PID: 8564)
- u1CFBzp7.exe (PID: 8076)
- setup.exe (PID: 8276)
- crss.exe (PID: 8500)
Application launched itself
- EXMservice.exe (PID: 7548)
- Build.exe (PID: 7992)
- based.exe (PID: 1244)
- hacn.exe (PID: 6620)
- u1CFBzp7.exe (PID: 8076)
- cmd.exe (PID: 7512)
- setup.exe (PID: 8276)
- crss.exe (PID: 8500)
- CompPkgSrv.exe (PID: 8564)
Reads security settings of Internet Explorer
- Build.exe (PID: 7992)
Start notepad (likely ransomware note)
- Build.exe (PID: 7376)
- based.exe (PID: 1244)
Found strings related to reading or modifying Windows Defender settings
- based.exe (PID: 7204)
Starts CMD.EXE for commands execution
- based.exe (PID: 7204)
- hacn.exe (PID: 7244)
- csrss.exe (PID: 1760)
- cmd.exe (PID: 7512)
- CompPkgSrv.exe (PID: 8552)
Script disables Windows Defender's IPS
- cmd.exe (PID: 7356)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7240)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 4608)
- cmd.exe (PID: 7448)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 8456)
- cmd.exe (PID: 9044)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 4920)
- setup.exe (PID: 2136)
The executable file from the user directory is run by the CMD process
- bound.exe (PID: 8120)
- rar.exe (PID: 6708)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 4608)
- cmd.exe (PID: 7240)
- setup.exe (PID: 2136)
Get information on the list of running processes
- based.exe (PID: 7204)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 5008)
- cmd.exe (PID: 7504)
Starts application with an unusual extension
- cmd.exe (PID: 7480)
- cmd.exe (PID: 7256)
- cmd.exe (PID: 8360)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 8616)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 1852)
- cmd.exe (PID: 8324)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5624)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 7912)
Potential Corporate Privacy Violation
- hacn.exe (PID: 7244)
- csrss.exe (PID: 1760)
- crss.exe (PID: 456)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 7476)
- cmd.exe (PID: 1852)
- cmd.exe (PID: 8324)
Base64-obfuscated command line is found
- cmd.exe (PID: 7144)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 7144)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7144)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 2284)
Possible usage of Discord/Telegram API has been detected (YARA)
- csrss.exe (PID: 1760)
- based.exe (PID: 7204)
CSC.EXE is used to compile C# code
- csc.exe (PID: 8988)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 8580)
- cmd.exe (PID: 8660)
- cmd.exe (PID: 5020)
- cmd.exe (PID: 9184)
- cmd.exe (PID: 8404)
- cmd.exe (PID: 7376)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 7708)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 4572)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 7356)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- svchost.exe (PID: 7580)
- csrss.exe (PID: 1760)
- based.exe (PID: 7204)
- CompPkgSrv.exe (PID: 8552)
There is functionality for taking screenshot (YARA)
- hacn.exe (PID: 6620)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 6512)
- CompPkgSrv.exe (PID: 8552)
Connects to unusual port
- svchost.exe (PID: 7580)
Checks for external IP
- svchost.exe (PID: 2196)
- csrss.exe (PID: 1760)
- based.exe (PID: 7204)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8324)
The process connected to a server suspected of theft
- csrss.exe (PID: 1760)
Script adds exclusion process to Windows Defender
- setup.exe (PID: 2136)
Uses REG/REGEDIT.EXE to modify registry
- powershell.exe (PID: 1672)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 8044)
The process checks if current user has admin rights
- setup.exe (PID: 2136)
Connects to the server without a host name
- crss.exe (PID: 456)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 7344)
Manipulates environment variables
- powershell.exe (PID: 3020)
- powershell.exe (PID: 4188)
- powershell.exe (PID: 8056)
- powershell.exe (PID: 4692)
Stops a currently running service
- sc.exe (PID: 8072)
- sc.exe (PID: 7352)
- sc.exe (PID: 9040)
- sc.exe (PID: 232)
- sc.exe (PID: 9032)
- sc.exe (PID: 8952)
- sc.exe (PID: 8768)
- sc.exe (PID: 8412)
- sc.exe (PID: 8104)
- sc.exe (PID: 7448)
- sc.exe (PID: 6044)
- sc.exe (PID: 6048)
- sc.exe (PID: 5868)
- sc.exe (PID: 5332)
- sc.exe (PID: 8688)
- sc.exe (PID: 8432)
- sc.exe (PID: 8712)
- sc.exe (PID: 8428)
- sc.exe (PID: 8948)
- sc.exe (PID: 9092)
Starts SC.EXE for service management
- cmd.exe (PID: 8528)
- cmd.exe (PID: 8212)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 8836)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 3620)
- DismHost.exe (PID: 6584)
- DismHost.exe (PID: 7228)
- DismHost.exe (PID: 7808)
The process executes via Task Scheduler
- svchost.exe (PID: 6268)
- updater.exe (PID: 8640)
- update.exe (PID: 9040)
- svchost.exe (PID: 9032)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 812)
- schtasks.exe (PID: 8428)
Removes files via Powershell
- powershell.exe (PID: 8464)
Drops a system driver (possible attempt to evade defenses)
- updater.exe (PID: 8640)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2196)
INFO
Reads Environment values
- identity_helper.exe (PID: 1660)
- identity_helper.exe (PID: 7796)
The sample compiled with english language support
- WinRAR.exe (PID: 5352)
- EXMservice.exe (PID: 7548)
- Build.exe (PID: 7376)
- hacn.exe (PID: 6620)
- based.exe (PID: 1244)
- CompPkgSrv.exe (PID: 8564)
- u1CFBzp7.exe (PID: 8076)
- crss.exe (PID: 8500)
- setup.exe (PID: 8276)
- powershell.exe (PID: 7344)
- Dism.exe (PID: 8628)
- Dism.exe (PID: 7816)
- Dism.exe (PID: 5172)
Application launched itself
- msedge.exe (PID: 6816)
- msedge.exe (PID: 7968)
Checks supported languages
- identity_helper.exe (PID: 1660)
- identity_helper.exe (PID: 7796)
- EXMservice.exe (PID: 7548)
- EXMservice.exe (PID: 1760)
- Build.exe (PID: 7992)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6816)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5352)
Reads the computer name
- identity_helper.exe (PID: 7796)
- identity_helper.exe (PID: 1660)
- EXMservice.exe (PID: 7548)
- Build.exe (PID: 7992)
Create files in a temporary directory
- EXMservice.exe (PID: 7548)
Manual execution by a user
- EXMservice.exe (PID: 7548)
- powershell.exe (PID: 3020)
- powershell.exe (PID: 4188)
- cmd.exe (PID: 8528)
- dialer.exe (PID: 7456)
- cmd.exe (PID: 8212)
- schtasks.exe (PID: 9068)
- dialer.exe (PID: 5084)
- schtasks.exe (PID: 8112)
- schtasks.exe (PID: 812)
- schtasks.exe (PID: 8652)
- schtasks.exe (PID: 5548)
- schtasks.exe (PID: 8428)
- powershell.exe (PID: 8056)
- powershell.exe (PID: 4692)
- cmd.exe (PID: 8836)
- cmd.exe (PID: 7376)
- dialer.exe (PID: 7804)
- schtasks.exe (PID: 9120)
- schtasks.exe (PID: 7648)
- dialer.exe (PID: 7512)
- dialer.exe (PID: 7172)
- dialer.exe (PID: 616)
Reads the machine GUID from the registry
- EXMservice.exe (PID: 1760)
Process checks computer location settings
- Build.exe (PID: 7992)
Checks operating system version
- hacn.exe (PID: 7244)
- CompPkgSrv.exe (PID: 8552)
Checks the directory tree
- tree.com (PID: 2140)
- tree.com (PID: 8476)
- tree.com (PID: 8304)
- tree.com (PID: 8708)
- tree.com (PID: 8568)
- tree.com (PID: 8808)
The Powershell gets current clipboard
- powershell.exe (PID: 1088)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 9096)
Attempting to use instant messaging service
- svchost.exe (PID: 7580)
- svchost.exe (PID: 2196)
- csrss.exe (PID: 1760)
- based.exe (PID: 7204)
PyInstaller has been detected (YARA)
- hacn.exe (PID: 6620)
- based.exe (PID: 1244)
Changes the display of characters in the console
- cmd.exe (PID: 1852)
- cmd.exe (PID: 8324)
Found Base64 encoded reflection usage via PowerShell (YARA)
- based.exe (PID: 7204)
Changes the registry key values via Powershell
- setup.exe (PID: 2136)
Returns hidden items found within a container (POWERSHELL)
- powershell.exe (PID: 3020)
- conhost.exe (PID: 1096)
- powershell.exe (PID: 4188)
- powershell.exe (PID: 7344)
- conhost.exe (PID: 4220)
- conhost.exe (PID: 7840)
- conhost.exe (PID: 8260)
- conhost.exe (PID: 1600)
- conhost.exe (PID: 9028)
- conhost.exe (PID: 1912)
- conhost.exe (PID: 7872)
- conhost.exe (PID: 7876)
- conhost.exe (PID: 6656)
- conhost.exe (PID: 7020)
- powershell.exe (PID: 4692)
- conhost.exe (PID: 8856)
- powershell.exe (PID: 8056)
- conhost.exe (PID: 8800)
- conhost.exe (PID: 7844)
- powershell.exe (PID: 8464)
- conhost.exe (PID: 5544)
- conhost.exe (PID: 6424)
- conhost.exe (PID: 8292)
Returns all items recursively from all subfolders (POWERSHELL)
- powershell.exe (PID: 8464)
The sample compiled with japanese language support
- updater.exe (PID: 8640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(1760) csrss.exe
Telegram-Tokens (1)1119746739:AAGMhvpUjXI4CzIfizRC--VXilxnkJlhaf8
Telegram-Info-Links
1119746739:AAGMhvpUjXI4CzIfizRC--VXilxnkJlhaf8
Get info about bothttps://api.telegram.org/bot1119746739:AAGMhvpUjXI4CzIfizRC--VXilxnkJlhaf8/getMe
Get incoming updateshttps://api.telegram.org/bot1119746739:AAGMhvpUjXI4CzIfizRC--VXilxnkJlhaf8/getUpdates
Get webhookhttps://api.telegram.org/bot1119746739:AAGMhvpUjXI4CzIfizRC--VXilxnkJlhaf8/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot1119746739:AAGMhvpUjXI4CzIfizRC--VXilxnkJlhaf8/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot1119746739:AAGMhvpUjXI4CzIfizRC--VXilxnkJlhaf8/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token1119746739:AAGMhvpUjXI4CzIfizRC--VXilxnkJlhaf8
End-Pointsend
Args
(PID) Process(7204) based.exe
Telegram-Tokens (1)7564421410:AAHgBw2xu-96C8rVIiibt59lzDnMAPliOm4
Telegram-Info-Links
7564421410:AAHgBw2xu-96C8rVIiibt59lzDnMAPliOm4
Get info about bothttps://api.telegram.org/bot7564421410:AAHgBw2xu-96C8rVIiibt59lzDnMAPliOm4/getMe
Get incoming updateshttps://api.telegram.org/bot7564421410:AAHgBw2xu-96C8rVIiibt59lzDnMAPliOm4/getUpdates
Get webhookhttps://api.telegram.org/bot7564421410:AAHgBw2xu-96C8rVIiibt59lzDnMAPliOm4/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7564421410:AAHgBw2xu-96C8rVIiibt59lzDnMAPliOm4/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7564421410:AAHgBw2xu-96C8rVIiibt59lzDnMAPliOm4/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token7564421410:AAHgBw2xu-96C8rVIiibt59lzDnMAPliOm4
End-PointsendDocument
Args
StormKitty
(PID) Process(1760) csrss.exe
C2 (1)127.0.0.1
Ports (3)6606
7707
8808
Credentials
Protocoltelegram
URLhttps://api.telegram.org/bot1119746739:AAGMhvpUjXI4CzIfizRC--VXilxnkJlhaf8/send
Token7564421410:AAHgBw2xu-96C8rVIiibt59lzDnMAPliOm4
ChatId7741783264
Version
BotnetDefault
Options
AutoRunfalse
MutexAsyncMutex_6SI8OkPnk
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE9jCCAt6gAwIBAgIQAKQXqY8ZdB/modqi69mWGTANBgkqhkiG9w0BAQ0FADAcMRowGAYDVQQDDBFXb3JsZFdpbmQgU3RlYWxlcjAgFw0yMTA3MTMwNDUxMDZaGA85OTk5MTIzMTIzNTk1OVowHDEaMBgGA1UEAwwRV29ybGRXaW5kIFN0ZWFsZXIwggIiMA0GCSqGSIb3DQEBAQUAA4ICDwAwggIKAoICAQCnRXYoxuLqqgXdcvIAYWb9DuVRl5ZpdpPfoIgmb7Y9A9AuiddKNm4is8EvIlEh98bQD4OB...
Server_SignaturedQGfIfAUJro61UaCd4+i2Qqnsf/zEDN+fZ4h8gDjVSkmu7ESembGXl891tNVgGKe9Qz+nk/xzADktB8zxLXU2iriwDHifRUL7Fh82KjcCcM32ei88S6axgv5BIUcwWH2xJCLBrhpkYvzyqKIt4VTLD++OlvgMPdTlmu544zGSXqjLEJgP4d/IQFtqn/zZCwzuKRQcdytr1/uFpwPX62saaig9C8QDbo9l/roL9FkdIg5wo+ceVF+sehs5x4XQeFhfwlemzotvWXtOjYrj5F1vy9dmoqjJTju4vW6c8QN+6+F...
Keys
AES302432bc6853d384b08da87e078b98990df7cab1ee0f8aecf4ddc4bc0d4df22e
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
Total processes
425
Monitored processes
287
Malicious processes
33
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | sc stop bits | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | "C:\ProgramData\crss.exe" | C:\ProgramData\crss.exe | crss.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 616 | C:\WINDOWS\System32\dialer.exe | C:\Windows\System32\dialer.exe | explorer.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Phone Dialer Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2644 --field-trial-handle=2376,i,10781175962996264412,16153328604896623862,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6800 --field-trial-handle=2368,i,12203809235190289513,15129809174979119248,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | C:\WINDOWS\System32\schtasks.exe /delete /f /tn "GoogleUpdateTaskMachineQC" | C:\Windows\System32\schtasks.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7476 --field-trial-handle=2368,i,12203809235190289513,15129809174979119248,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5696 --field-trial-handle=2368,i,12203809235190289513,15129809174979119248,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1088 | powershell Get-Clipboard | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
137 955
Read events
137 791
Write events
86
Delete events
78
Modification events
| (PID) Process: | (6816) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6816) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6816) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6816) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (7148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (7148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
Executable files
561
Suspicious files
287
Text files
285
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b77a.TMP | — | |
MD5:— | SHA256:— | |||
| 6816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b77a.TMP | — | |
MD5:— | SHA256:— | |||
| 6816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b77a.TMP | — | |
MD5:— | SHA256:— | |||
| 6816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b78a.TMP | — | |
MD5:— | SHA256:— | |||
| 6816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b7b9.TMP | — | |
MD5:— | SHA256:— | |||
| 6816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
1 194
DNS requests
58
Threats
44
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 92.122.244.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.61.29.203:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.61.29.203:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7848 | SIHClient.exe | GET | 200 | 23.61.29.203:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7848 | SIHClient.exe | GET | 200 | 23.61.29.203:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7244 | hacn.exe | GET | 200 | 142.250.186.36:80 | http://www.google.com/ | unknown | — | — | whitelisted |
1760 | csrss.exe | GET | 200 | 104.16.184.241:80 | http://icanhazip.com/ | unknown | — | — | whitelisted |
7204 | based.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=225545 | unknown | — | — | whitelisted |
456 | crss.exe | GET | 200 | 142.250.186.36:80 | http://www.google.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 92.122.244.32:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.61.29.203:80 | www.microsoft.com | NTT DOCOMO, INC. | JP | whitelisted |
— | — | 23.61.29.203:80 | www.microsoft.com | NTT DOCOMO, INC. | JP | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6816 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7244 | hacn.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2196 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7580 | svchost.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
7580 | svchost.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |