| File name: | file |
| Full analysis: | https://app.any.run/tasks/7d46f177-063d-4b15-bd41-2a0d3f7d2dfb |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | December 14, 2024, 03:52:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | C34A786DE9705B019FFA55C575B12412 |
| SHA1: | 105A41ABBA38C4420D3B6ED6F7F464374257559B |
| SHA256: | 423D31C445F4F1B659E88A21E588D5C96910E86C6F40EA271201FBB55D40F39D |
| SSDEEP: | 98304:KiOIMGTJOyM6NNJZnjApX64g0mh3rtRqLIxRyroGbAydBw1GnEu9qJFWQv3Bl2By:x+Cw |
MALICIOUS
AMADEY has been detected (SURICATA)
- skotes.exe (PID: 6792)
Connects to the CnC server
- skotes.exe (PID: 6792)
- 8ec376bf72.exe (PID: 1064)
- svchost.exe (PID: 2192)
Uses Task Scheduler to run other applications
- in.exe (PID: 4764)
- in.exe (PID: 8576)
LUMMA mutex has been found
- c327a990f6.exe (PID: 6712)
- faa8372f9e.exe (PID: 9140)
Actions looks like stealing of personal data
- c327a990f6.exe (PID: 6712)
- 8ec376bf72.exe (PID: 1064)
- b2f500d49a.exe (PID: 8364)
- faa8372f9e.exe (PID: 9140)
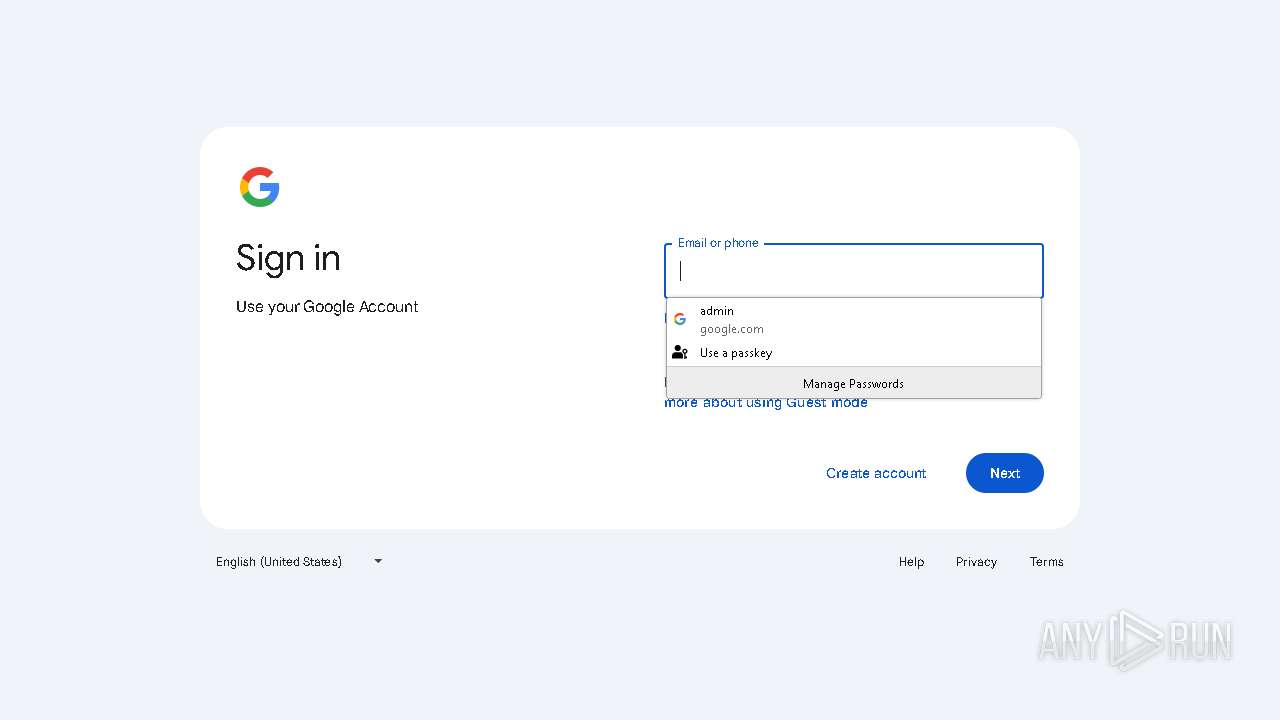
Steals credentials from Web Browsers
- c327a990f6.exe (PID: 6712)
- 8ec376bf72.exe (PID: 1064)
- b2f500d49a.exe (PID: 8364)
- faa8372f9e.exe (PID: 9140)
Changes the autorun value in the registry
- skotes.exe (PID: 6792)
StealC has been detected
- 8ec376bf72.exe (PID: 1064)
Possible tool for stealing has been detected
- c839c72355.exe (PID: 2164)
- firefox.exe (PID: 5300)
STEALC has been detected (SURICATA)
- 8ec376bf72.exe (PID: 1064)
VIDAR mutex has been found
- b2f500d49a.exe (PID: 8364)
LUMMA has been found (auto)
- skotes.exe (PID: 6792)
AMADEY has been detected (YARA)
- skotes.exe (PID: 6792)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
- faa8372f9e.exe (PID: 9140)
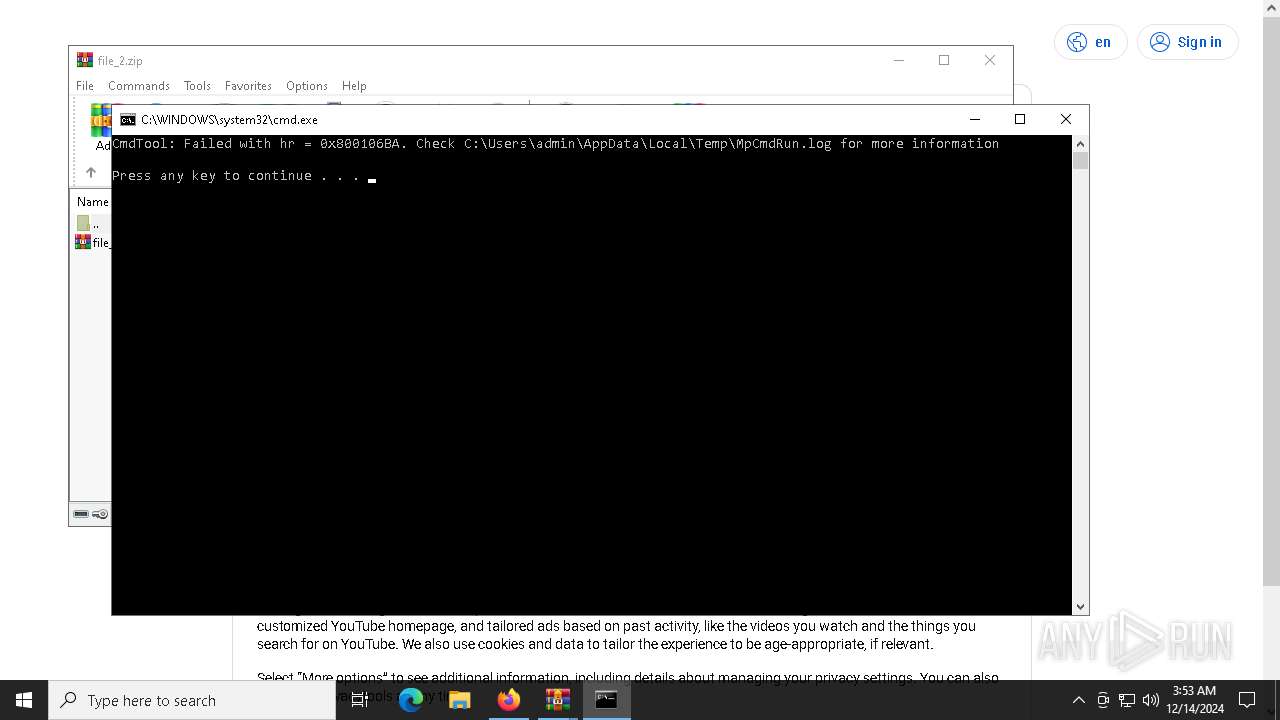
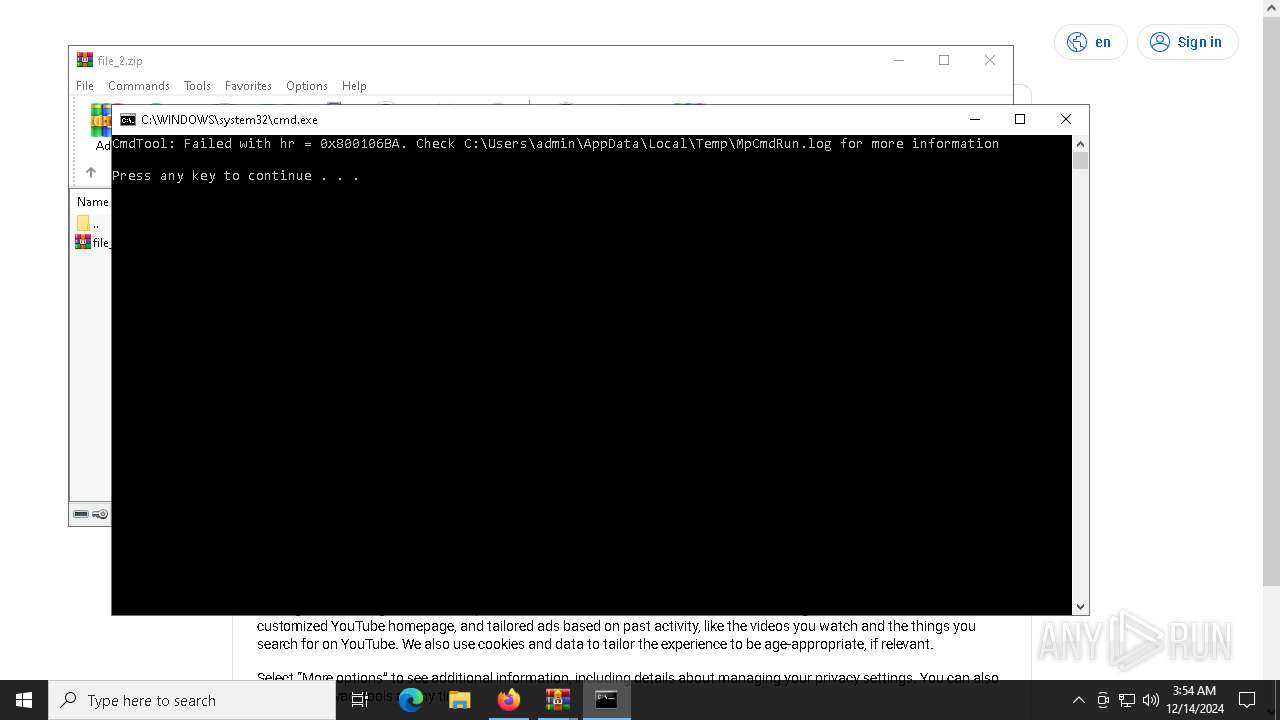
Antivirus name has been found in the command line (generic signature)
- MpCmdRun.exe (PID: 4392)
SUSPICIOUS
Reads the BIOS version
- file.exe (PID: 6444)
- skotes.exe (PID: 6792)
- skotes.exe (PID: 5776)
- 8ec376bf72.exe (PID: 1064)
- 2650b1e700.exe (PID: 8168)
- JJDBAEHIJK.exe (PID: 8472)
- skotes.exe (PID: 8328)
Starts itself from another location
- file.exe (PID: 6444)
Executable content was dropped or overwritten
- file.exe (PID: 6444)
- skotes.exe (PID: 6792)
- b2b72eb325.exe (PID: 6240)
- cmd.exe (PID: 628)
- 7z.exe (PID: 4388)
- in.exe (PID: 4764)
- 8ec376bf72.exe (PID: 1064)
Reads security settings of Internet Explorer
- file.exe (PID: 6444)
- skotes.exe (PID: 6792)
- b2b72eb325.exe (PID: 6240)
- 8ec376bf72.exe (PID: 1064)
- b2f500d49a.exe (PID: 8364)
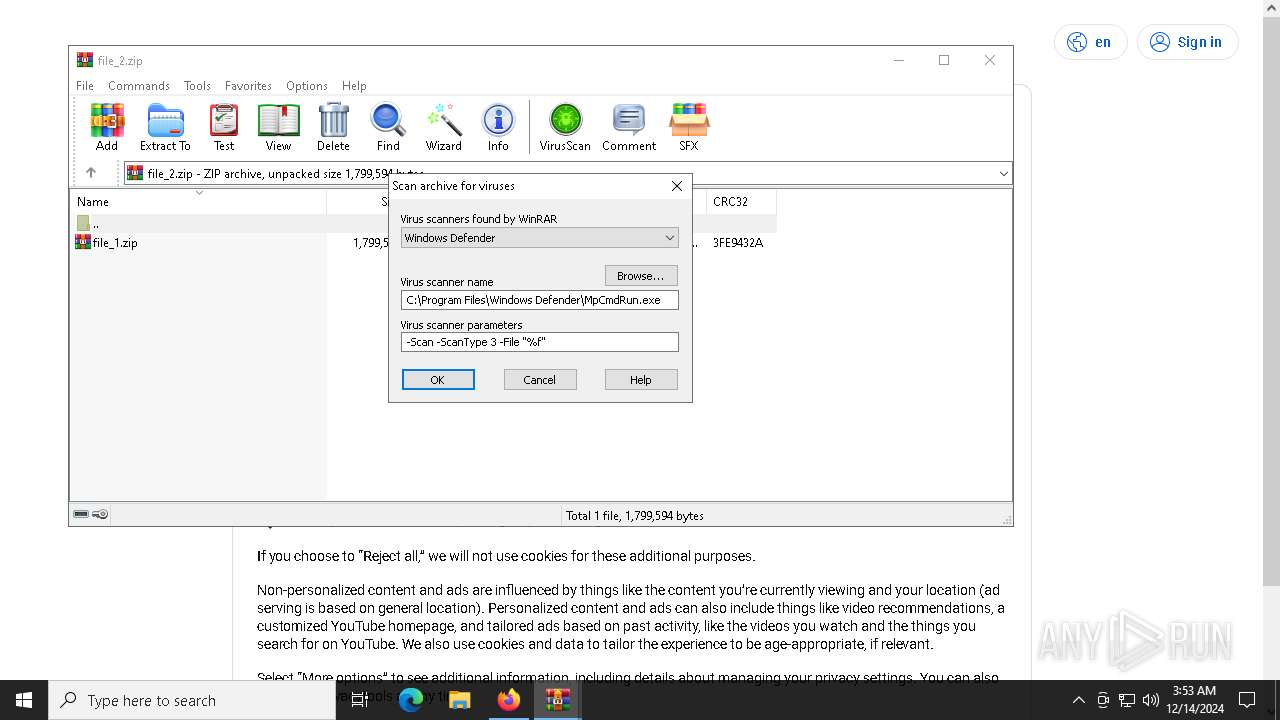
- WinRAR.exe (PID: 8084)
Contacting a server suspected of hosting an CnC
- skotes.exe (PID: 6792)
- 8ec376bf72.exe (PID: 1064)
- faa8372f9e.exe (PID: 9140)
- svchost.exe (PID: 2192)
Potential Corporate Privacy Violation
- skotes.exe (PID: 6792)
- 8ec376bf72.exe (PID: 1064)
Starts CMD.EXE for commands execution
- b2b72eb325.exe (PID: 6240)
- 8ec376bf72.exe (PID: 1064)
- WinRAR.exe (PID: 8084)
- b2f500d49a.exe (PID: 8364)
Drops 7-zip archiver for unpacking
- b2b72eb325.exe (PID: 6240)
Executing commands from a ".bat" file
- b2b72eb325.exe (PID: 6240)
- WinRAR.exe (PID: 8084)
The executable file from the user directory is run by the CMD process
- 7z.exe (PID: 1616)
- 7z.exe (PID: 5472)
- 7z.exe (PID: 1580)
- 7z.exe (PID: 5028)
- 7z.exe (PID: 5748)
- 7z.exe (PID: 4388)
- in.exe (PID: 4764)
- 7z.exe (PID: 4548)
- 7z.exe (PID: 4224)
- JJDBAEHIJK.exe (PID: 8472)
Connects to the server without a host name
- skotes.exe (PID: 6792)
- 8ec376bf72.exe (PID: 1064)
Process requests binary or script from the Internet
- skotes.exe (PID: 6792)
- 8ec376bf72.exe (PID: 1064)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 628)
- in.exe (PID: 4764)
- in.exe (PID: 8576)
Found IP address in command line
- powershell.exe (PID: 3080)
- powershell.exe (PID: 4872)
- powershell.exe (PID: 8636)
- powershell.exe (PID: 1864)
Starts POWERSHELL.EXE for commands execution
- in.exe (PID: 4764)
- Intel_PTT_EK_Recertification.exe (PID: 6300)
- in.exe (PID: 8576)
- Intel_PTT_EK_Recertification.exe (PID: 2164)
Application launched itself
- c327a990f6.exe (PID: 4328)
Uses TASKKILL.EXE to kill Browsers
- c839c72355.exe (PID: 2164)
Uses TASKKILL.EXE to kill process
- c839c72355.exe (PID: 2164)
The process executes via Task Scheduler
- skotes.exe (PID: 5776)
- Intel_PTT_EK_Recertification.exe (PID: 6300)
- skotes.exe (PID: 8328)
- Intel_PTT_EK_Recertification.exe (PID: 2164)
Windows Defender mutex has been found
- 8ec376bf72.exe (PID: 1064)
Searches for installed software
- 8ec376bf72.exe (PID: 1064)
- b2f500d49a.exe (PID: 8364)
Checks Windows Trust Settings
- b2f500d49a.exe (PID: 8364)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- b2f500d49a.exe (PID: 8364)
The process drops C-runtime libraries
- 8ec376bf72.exe (PID: 1064)
The process drops Mozilla's DLL files
- 8ec376bf72.exe (PID: 1064)
Process drops legitimate windows executable
- 8ec376bf72.exe (PID: 1064)
Executes application which crashes
- b2f500d49a.exe (PID: 8364)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6436)
INFO
Reads the computer name
- file.exe (PID: 6444)
- skotes.exe (PID: 6792)
- b2b72eb325.exe (PID: 6240)
- 7z.exe (PID: 1616)
- 7z.exe (PID: 1580)
- 7z.exe (PID: 5472)
- 7z.exe (PID: 5028)
- 7z.exe (PID: 4548)
- 7z.exe (PID: 4224)
- 7z.exe (PID: 5748)
- 7z.exe (PID: 4388)
- c327a990f6.exe (PID: 6712)
- c839c72355.exe (PID: 2164)
- 8ec376bf72.exe (PID: 1064)
- 2650b1e700.exe (PID: 8168)
- b2f500d49a.exe (PID: 8364)
- faa8372f9e.exe (PID: 9140)
- MpCmdRun.exe (PID: 4392)
Sends debugging messages
- file.exe (PID: 6444)
- skotes.exe (PID: 6792)
- 8ec376bf72.exe (PID: 1064)
- skotes.exe (PID: 5776)
- 2650b1e700.exe (PID: 8168)
- JJDBAEHIJK.exe (PID: 8472)
- skotes.exe (PID: 8328)
The process uses the downloaded file
- file.exe (PID: 6444)
- skotes.exe (PID: 6792)
- b2b72eb325.exe (PID: 6240)
- 8ec376bf72.exe (PID: 1064)
- WinRAR.exe (PID: 8084)
- b2f500d49a.exe (PID: 8364)
Checks supported languages
- file.exe (PID: 6444)
- skotes.exe (PID: 6792)
- c327a990f6.exe (PID: 4328)
- b2b72eb325.exe (PID: 6240)
- mode.com (PID: 3224)
- 7z.exe (PID: 1616)
- 7z.exe (PID: 5472)
- 7z.exe (PID: 1580)
- 7z.exe (PID: 5028)
- 7z.exe (PID: 4548)
- 7z.exe (PID: 5748)
- 7z.exe (PID: 4388)
- in.exe (PID: 4764)
- 7z.exe (PID: 4224)
- c839c72355.exe (PID: 2164)
- c327a990f6.exe (PID: 6712)
- 8ec376bf72.exe (PID: 1064)
- skotes.exe (PID: 5776)
- Intel_PTT_EK_Recertification.exe (PID: 6300)
- 2650b1e700.exe (PID: 8168)
- in.exe (PID: 8576)
- faa8372f9e.exe (PID: 9140)
- b2f500d49a.exe (PID: 8364)
- JJDBAEHIJK.exe (PID: 8472)
- skotes.exe (PID: 8328)
- Intel_PTT_EK_Recertification.exe (PID: 2164)
- MpCmdRun.exe (PID: 4392)
Process checks computer location settings
- file.exe (PID: 6444)
- skotes.exe (PID: 6792)
- b2b72eb325.exe (PID: 6240)
- 8ec376bf72.exe (PID: 1064)
- b2f500d49a.exe (PID: 8364)
Create files in a temporary directory
- file.exe (PID: 6444)
- skotes.exe (PID: 6792)
- b2b72eb325.exe (PID: 6240)
- 7z.exe (PID: 1616)
- 7z.exe (PID: 1580)
- 7z.exe (PID: 5472)
- 7z.exe (PID: 5028)
- 7z.exe (PID: 4224)
- 7z.exe (PID: 4548)
- 7z.exe (PID: 5748)
- 7z.exe (PID: 4388)
- MpCmdRun.exe (PID: 4392)
Checks proxy server information
- skotes.exe (PID: 6792)
- 8ec376bf72.exe (PID: 1064)
- b2f500d49a.exe (PID: 8364)
- WerFault.exe (PID: 8896)
Creates files or folders in the user directory
- skotes.exe (PID: 6792)
- in.exe (PID: 4764)
- 8ec376bf72.exe (PID: 1064)
- b2f500d49a.exe (PID: 8364)
- WerFault.exe (PID: 8896)
The sample compiled with english language support
- b2b72eb325.exe (PID: 6240)
- skotes.exe (PID: 6792)
- 8ec376bf72.exe (PID: 1064)
Starts MODE.COM to configure console settings
- mode.com (PID: 3224)
Reads the software policy settings
- c327a990f6.exe (PID: 6712)
- b2f500d49a.exe (PID: 8364)
- faa8372f9e.exe (PID: 9140)
- WerFault.exe (PID: 8896)
Reads mouse settings
- c839c72355.exe (PID: 2164)
Manual execution by a user
- WinRAR.exe (PID: 6628)
- WinRAR.exe (PID: 6648)
- WinRAR.exe (PID: 6696)
- WinRAR.exe (PID: 7724)
- WinRAR.exe (PID: 8084)
- in.exe (PID: 8576)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3080)
- powershell.exe (PID: 8636)
- powershell.exe (PID: 4872)
- powershell.exe (PID: 1864)
Application launched itself
- firefox.exe (PID: 5300)
- firefox.exe (PID: 1520)
- chrome.exe (PID: 7828)
- msedge.exe (PID: 8676)
- chrome.exe (PID: 8672)
- msedge.exe (PID: 9104)
Reads Environment values
- 8ec376bf72.exe (PID: 1064)
- b2f500d49a.exe (PID: 8364)
Reads CPU info
- 8ec376bf72.exe (PID: 1064)
- b2f500d49a.exe (PID: 8364)
Reads product name
- 8ec376bf72.exe (PID: 1064)
- b2f500d49a.exe (PID: 8364)
Creates files in the program directory
- b2f500d49a.exe (PID: 8364)
- 8ec376bf72.exe (PID: 1064)
Reads the machine GUID from the registry
- b2f500d49a.exe (PID: 8364)
Themida protector has been detected
- skotes.exe (PID: 6792)
Executable content was dropped or overwritten
- firefox.exe (PID: 1520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:09:22 17:40:44+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.24 |
| CodeSize: | 322048 |
| InitializedDataSize: | 104448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31b000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
256
Monitored processes
126
Malicious processes
12
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1860 -parentBuildID 20240213221259 -prefsHandle 1788 -prefMapHandle 1416 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {626320f4-9dfd-4690-bb88-bde1c0b2ed45} 1520 "\\.\pipe\gecko-crash-server-pipe.1520" 21cb4fee810 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 440 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | c327a990f6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\main\main.bat" /S" | C:\Windows\System32\cmd.exe | b2b72eb325.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x220,0x224,0x228,0x48,0x22c,0x7ff81c8cdc40,0x7ff81c8cdc4c,0x7ff81c8cdc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=1668 --field-trial-handle=2004,i,5224202274265671212,9320447260293636780,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1064 | "C:\Users\admin\AppData\Local\Temp\1015045001\8ec376bf72.exe" | C:\Users\admin\AppData\Local\Temp\1015045001\8ec376bf72.exe | skotes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1400 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1476 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2860 --field-trial-handle=2824,i,16375157422972005361,5571938583012685340,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Mozilla Firefox\firefox.exe" --kiosk https://youtube.com/account?=https://accounts.google.com/v3/signin/challenge/pwd --no-default-browser-check --disable-popup-blocking | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1580 | 7z.exe e extracted/file_7.zip -oextracted | C:\Users\admin\AppData\Local\Temp\main\7z.exe | — | cmd.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
Total events
62 313
Read events
62 231
Write events
82
Delete events
0
Modification events
| (PID) Process: | (6792) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6792) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6792) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6792) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | c839c72355.exe |
Value: C:\Users\admin\AppData\Local\Temp\1015044001\c839c72355.exe | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\file_4.zip | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
62
Suspicious files
485
Text files
181
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6792 | skotes.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\random[1].exe | executable | |
MD5:3A425626CBD40345F5B8DDDD6B2B9EFA | SHA256:BA9212D2D5CD6DF5EB7933FB37C1B72A648974C1730BF5C32439987558F8E8B1 | |||
| 6792 | skotes.exe | C:\Users\admin\AppData\Local\Temp\1015042001\b2b72eb325.exe | executable | |
MD5:3A425626CBD40345F5B8DDDD6B2B9EFA | SHA256:BA9212D2D5CD6DF5EB7933FB37C1B72A648974C1730BF5C32439987558F8E8B1 | |||
| 6444 | file.exe | C:\Windows\Tasks\skotes.job | binary | |
MD5:761D8E14732F3FF985450BDC0C92546B | SHA256:8E678574816C855C6ECFA047E387263A9BE891D5BD75F203E8F565A1BB35FEB8 | |||
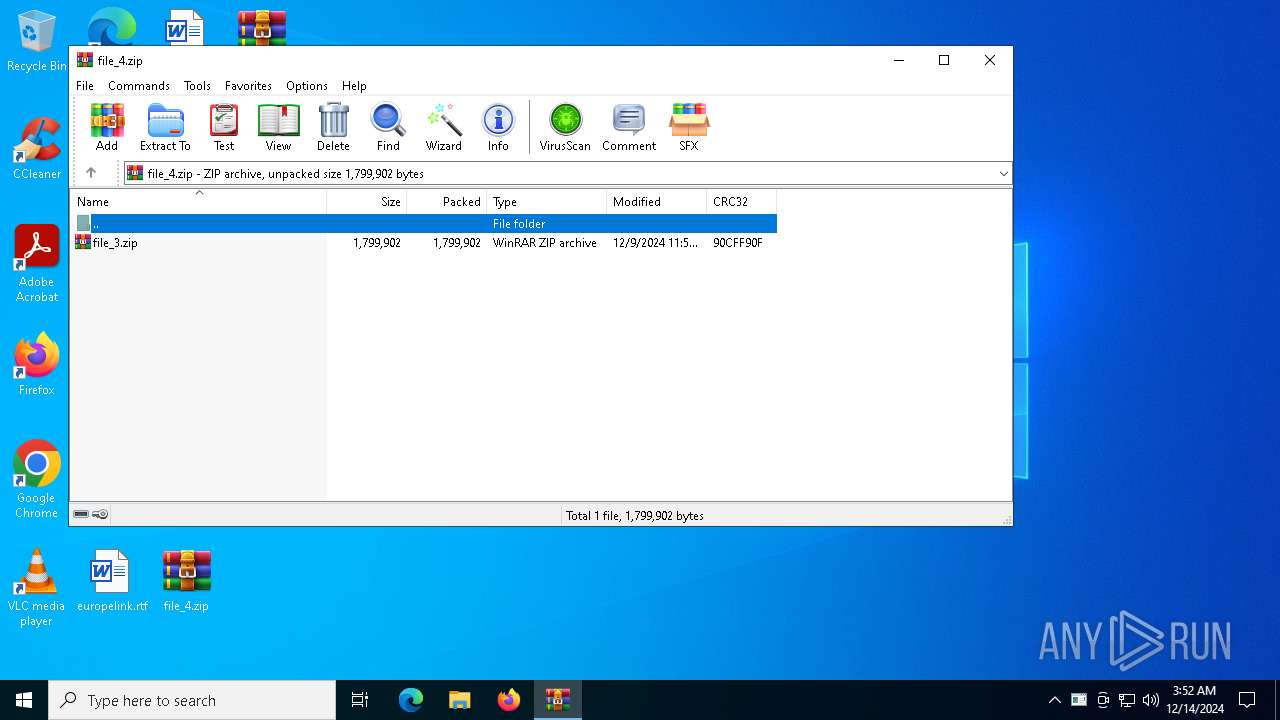
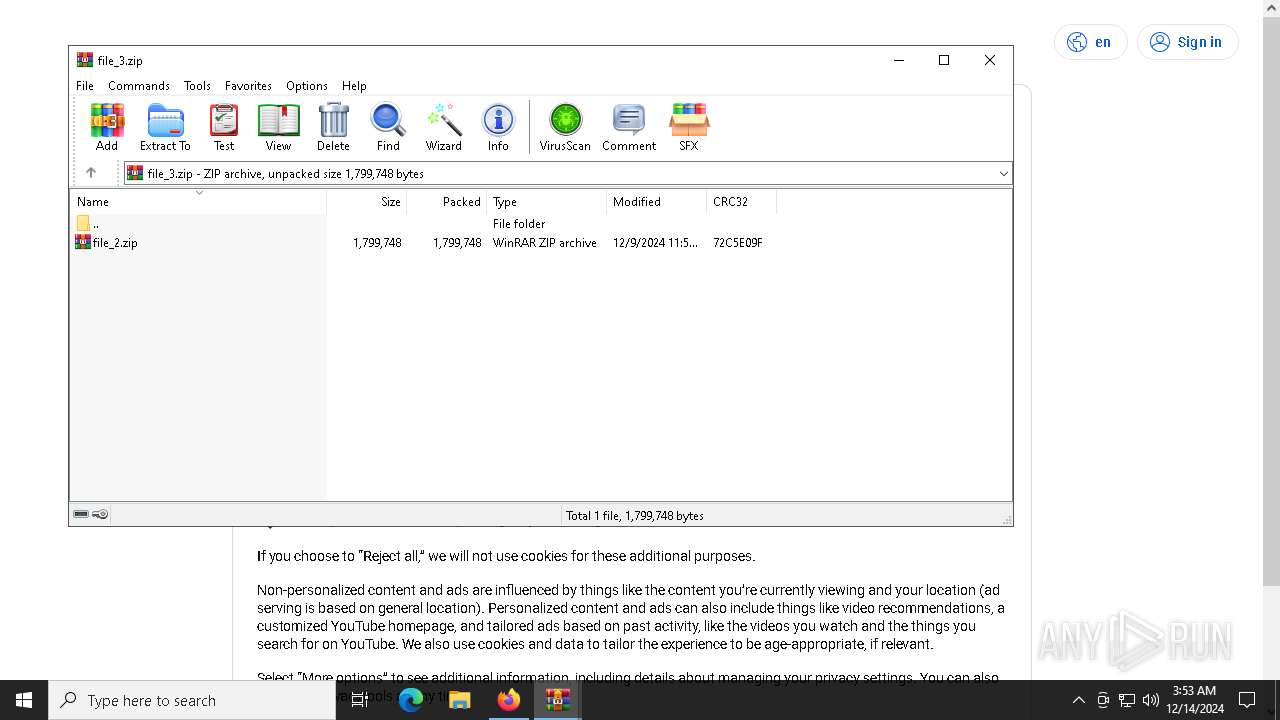
| 4548 | 7z.exe | C:\Users\admin\AppData\Local\Temp\main\extracted\file_3.zip | compressed | |
MD5:5EB39BA3698C99891A6B6EB036CFB653 | SHA256:E77F5E03AE140DDA27D73E1FFE43F7911E006A108CF51CBD0E05D73AA92DA7C2 | |||
| 1580 | 7z.exe | C:\Users\admin\AppData\Local\Temp\main\extracted\AntiAV.data | text | |
MD5:579A63BEBCCBACAB8F14132F9FC31B89 | SHA256:0AC3504D5FA0460CAE3C0FD9C4B628E1A65547A60563E6D1F006D17D5A6354B0 | |||
| 6444 | file.exe | C:\Users\admin\AppData\Local\Temp\abc3bc1985\skotes.exe | executable | |
MD5:C34A786DE9705B019FFA55C575B12412 | SHA256:423D31C445F4F1B659E88A21E588D5C96910E86C6F40EA271201FBB55D40F39D | |||
| 5472 | 7z.exe | C:\Users\admin\AppData\Local\Temp\main\extracted\file_5.zip | compressed | |
MD5:B7D1E04629BEC112923446FDA5391731 | SHA256:4DA77D4EE30AD0CD56CD620F4E9DC4016244ACE015C5B4B43F8F37DD8E3A8789 | |||
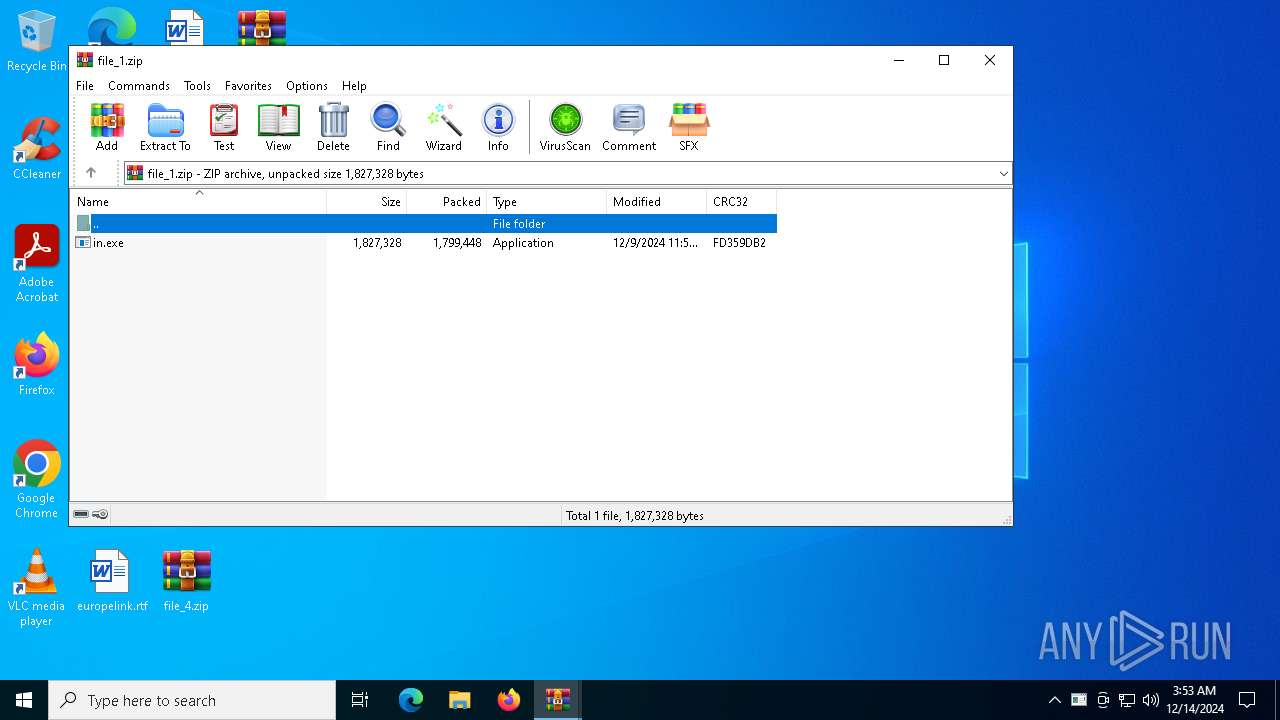
| 5748 | 7z.exe | C:\Users\admin\AppData\Local\Temp\main\extracted\file_1.zip | compressed | |
MD5:5659EBA6A774F9D5322F249AD989114A | SHA256:E04346FEE15C3F98387A3641E0BBA2E555A5A9B0200E4B9256B1B77094069AE4 | |||
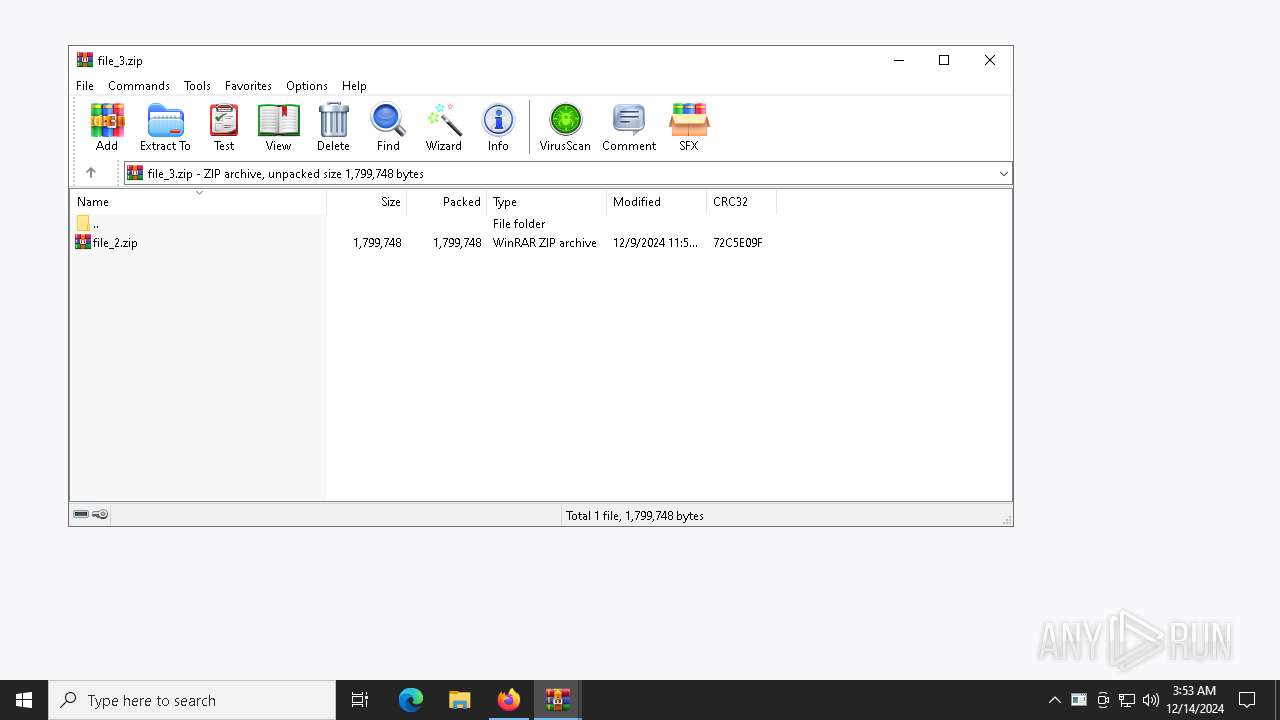
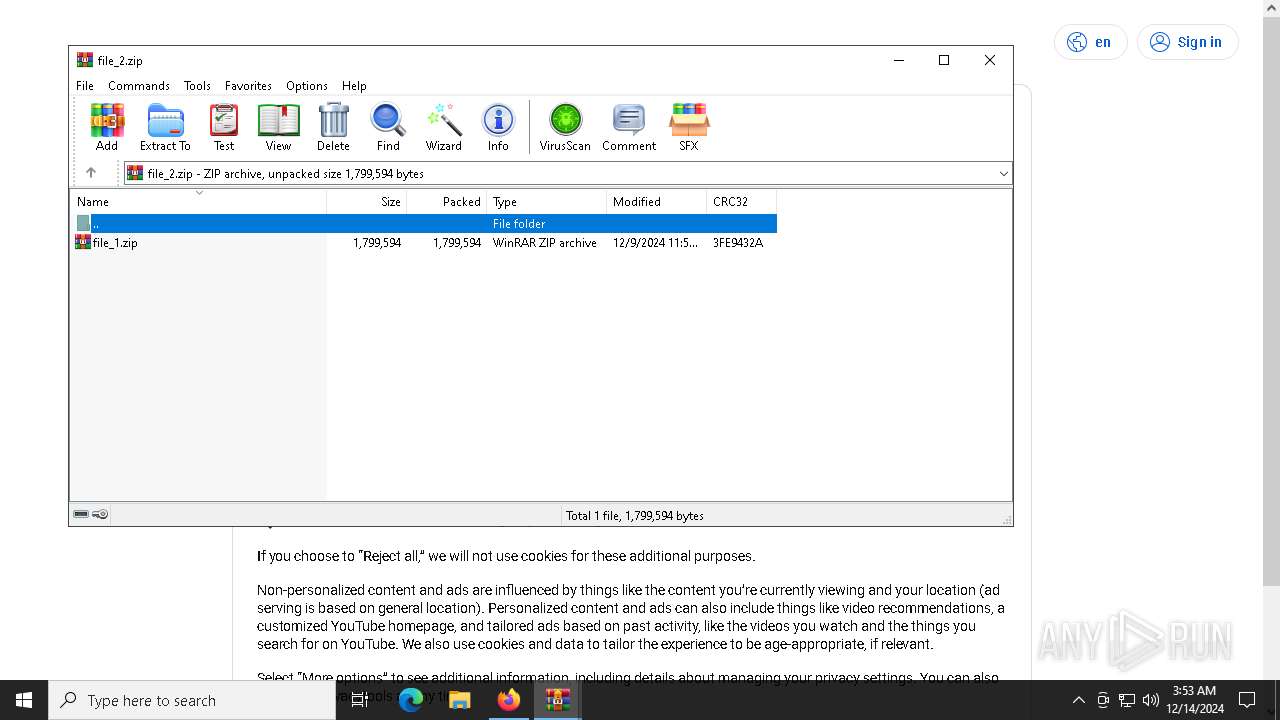
| 4224 | 7z.exe | C:\Users\admin\AppData\Local\Temp\main\extracted\file_2.zip | compressed | |
MD5:5404286EC7853897B3BA00ADF824D6C1 | SHA256:EC94A6666A3103BA6BE60B92E843075A2D7FE7D30FA41099C3F3B1E2A5EBA266 | |||
| 6792 | skotes.exe | C:\Users\admin\AppData\Local\Temp\1015043001\c327a990f6.exe | executable | |
MD5:28E568616A7B792CAC1726DEB77D9039 | SHA256:9597798F7789ADC29FBE97707B1BD8CA913C4D5861B0AD4FDD6B913AF7C7A8E2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
90
TCP/UDP connections
245
DNS requests
243
Threats
71
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
436 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
436 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6792 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
6792 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
6792 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6792 | skotes.exe | GET | 200 | 31.41.244.11:80 | http://31.41.244.11/files/burpin1/random.exe | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
436 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
436 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.182:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
1176 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
drive-connect.cyou |
| malicious |
youtube.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6792 | skotes.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
6792 | skotes.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
6792 | skotes.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6792 | skotes.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 2 |
6792 | skotes.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6792 | skotes.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6792 | skotes.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
6792 | skotes.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6792 | skotes.exe | A Network Trojan was detected | ET MALWARE Win32/Amadey Host Fingerprint Exfil (POST) M2 |
6792 | skotes.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
file.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
8ec376bf72.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
2650b1e700.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
JJDBAEHIJK.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|