| File name: | 41ce8dc9fe52cbb66ddf436ec0d9160bf9ce9194c423fbc0397705793f8ddc2c |
| Full analysis: | https://app.any.run/tasks/73b9390a-7368-485f-be25-fa35cdde381b |
| Verdict: | Malicious activity |
| Threats: | CryptBot is an advanced Windows-targeting infostealer delivered via pirate sites with "cracked" software. It has been first observed in the wild in 2019. |
| Analysis date: | January 18, 2020, 13:13:52 |
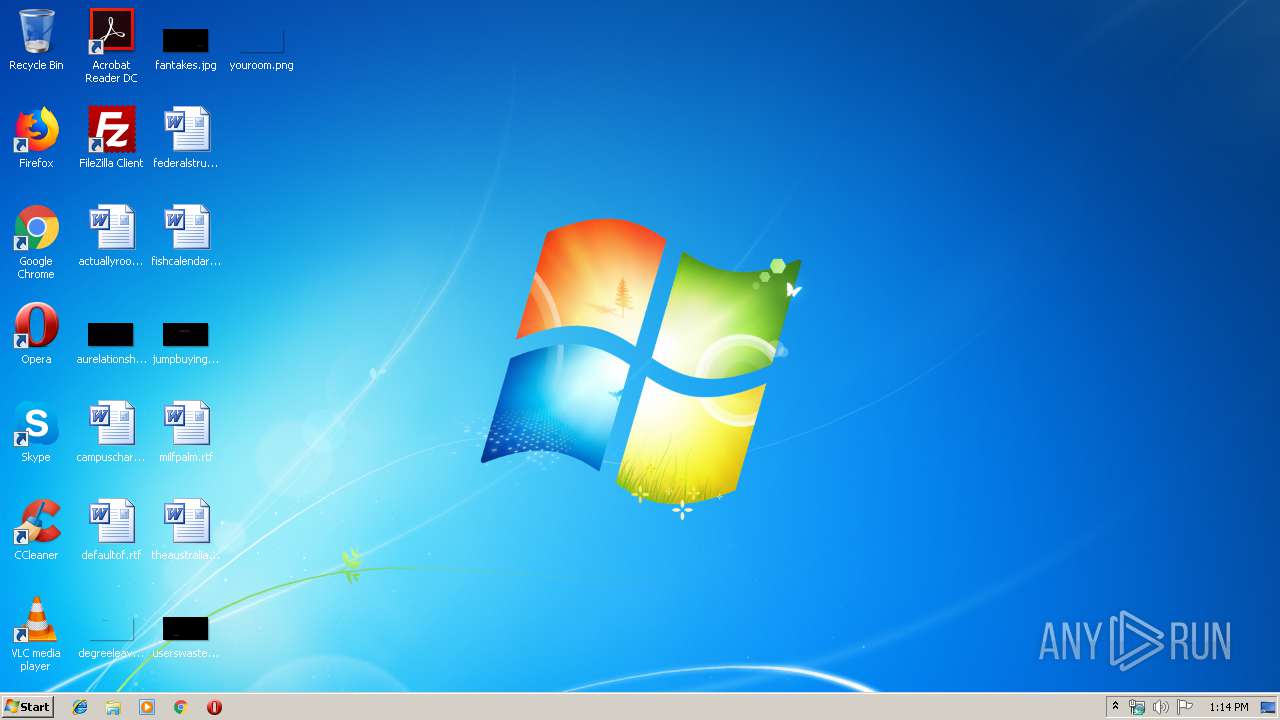
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 88F8F695E6AF7D58DA5F5B7EF60D0BDE |
| SHA1: | 16B06BD05058ABF520703AB656826099F93A094B |
| SHA256: | 41CE8DC9FE52CBB66DDF436EC0D9160BF9CE9194C423FBC0397705793F8DDC2C |
| SSDEEP: | 98304:HQCkuQvwiizV8qUOMbKQ4G2ZQFyEVBo9OAFKlAmdxGQyx7AAkvvj:HQCfJV8qUOMqZHEfnl1xGQ4AAkvb |
MALICIOUS
Loads dropped or rewritten executable
- 41ce8dc9fe52cbb66ddf436ec0d9160bf9ce9194c423fbc0397705793f8ddc2c.exe (PID: 2364)
Application was dropped or rewritten from another process
- Download.exe (PID: 2892)
- nsB439.tmp (PID: 328)
- DowloadX.exe (PID: 2776)
Changes settings of System certificates
- CScript.exe (PID: 3900)
Actions looks like stealing of personal data
- Download.exe (PID: 2892)
Stealing of credential data
- Download.exe (PID: 2892)
CRYPTBOT was detected
- Download.exe (PID: 2892)
SUSPICIOUS
Executable content was dropped or overwritten
- 41ce8dc9fe52cbb66ddf436ec0d9160bf9ce9194c423fbc0397705793f8ddc2c.exe (PID: 2364)
Creates files in the program directory
- 41ce8dc9fe52cbb66ddf436ec0d9160bf9ce9194c423fbc0397705793f8ddc2c.exe (PID: 2364)
- Download.exe (PID: 2892)
Adds / modifies Windows certificates
- CScript.exe (PID: 3900)
Executes scripts
- nsB439.tmp (PID: 328)
Starts application with an unusual extension
- 41ce8dc9fe52cbb66ddf436ec0d9160bf9ce9194c423fbc0397705793f8ddc2c.exe (PID: 2364)
Loads DLL from Mozilla Firefox
- Download.exe (PID: 2892)
Reads the cookies of Google Chrome
- Download.exe (PID: 2892)
Starts CMD.EXE for commands execution
- Download.exe (PID: 2892)
Reads the cookies of Mozilla Firefox
- Download.exe (PID: 2892)
Starts CMD.EXE for self-deleting
- Download.exe (PID: 2892)
Checks for external IP
- Download.exe (PID: 2892)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:20:04+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 29696 |
| InitializedDataSize: | 489984 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x38af |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.25.0.0 |
| ProductVersionNumber: | 1.25.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | - |
| FileVersion: | 1.25.0.0 |
| LegalCopyright: | Mev ltd. |
| ProductVersion: | 1.25.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:20:04 |
| Detected languages: |
|
| FileDescription: | - |
| FileVersion: | 1.25.0.0 |
| LegalCopyright: | Mev ltd. |
| ProductVersion: | 1.25.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:20:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000728C | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49971 |
.rdata | 0x00009000 | 0x00002B6E | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.49793 |
.data | 0x0000C000 | 0x00072B9C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.80494 |
.ndata | 0x0007F000 | 0x000E1000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00160000 | 0x000040F8 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.29319 |
.reloc | 0x00165000 | 0x00000FD6 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 1.57704 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11084 | 543 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.68983 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 1.72047 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 0.982333 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 3.06304 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
46
Monitored processes
8
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | "C:\Users\admin\AppData\Local\Temp\nsdB3FA.tmp\nsB439.tmp" "C:\Windows\system32\CScript.exe" "C:\Program Files\Doper\ipras.vbs" //e:vbscript //B //NOLOGO | C:\Users\admin\AppData\Local\Temp\nsdB3FA.tmp\nsB439.tmp | — | 41ce8dc9fe52cbb66ddf436ec0d9160bf9ce9194c423fbc0397705793f8ddc2c.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 600 | timeout 2 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | "C:\Windows\system32\cmd.exe" /c rd /s /q C:\ProgramData\85fuRT2EeqyQwIKY & timeout 2 & del /f /q "C:\Program Files\Doper\Download.exe" | C:\Windows\system32\cmd.exe | — | Download.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2364 | "C:\Users\admin\AppData\Local\Temp\41ce8dc9fe52cbb66ddf436ec0d9160bf9ce9194c423fbc0397705793f8ddc2c.exe" | C:\Users\admin\AppData\Local\Temp\41ce8dc9fe52cbb66ddf436ec0d9160bf9ce9194c423fbc0397705793f8ddc2c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.25.0.0 Modules
| |||||||||||||||
| 2776 | "C:\Program Files\Doper\DowloadX.exe" | C:\Program Files\Doper\DowloadX.exe | 41ce8dc9fe52cbb66ddf436ec0d9160bf9ce9194c423fbc0397705793f8ddc2c.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.1.29.01 Modules
| |||||||||||||||
| 2892 | "C:\Program Files\Doper\Download.exe" | C:\Program Files\Doper\Download.exe | 41ce8dc9fe52cbb66ddf436ec0d9160bf9ce9194c423fbc0397705793f8ddc2c.exe | ||||||||||||
User: admin Company: Aw Company Integrity Level: HIGH Description: SA Exit code: 0 Version: 1.3.0.0 Modules
| |||||||||||||||
| 3080 | "C:\Users\admin\AppData\Local\Temp\41ce8dc9fe52cbb66ddf436ec0d9160bf9ce9194c423fbc0397705793f8ddc2c.exe" | C:\Users\admin\AppData\Local\Temp\41ce8dc9fe52cbb66ddf436ec0d9160bf9ce9194c423fbc0397705793f8ddc2c.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.25.0.0 Modules
| |||||||||||||||
| 3900 | "C:\Windows\system32\CScript.exe" "C:\Program Files\Doper\ipras.vbs" //e:vbscript //B //NOLOGO | C:\Windows\system32\CScript.exe | nsB439.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
574
Read events
507
Write events
67
Delete events
0
Modification events
| (PID) Process: | (3900) CScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CScript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3900) CScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CScript_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3900) CScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CScript_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3900) CScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CScript_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3900) CScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CScript_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3900) CScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CScript_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3900) CScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CScript_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3900) CScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CScript_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3900) CScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CScript_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3900) CScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CScript_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
5
Suspicious files
1
Text files
75
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | Download.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LoginDataCopy | — | |
MD5:— | SHA256:— | |||
| 2892 | Download.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\WebDataCopy | — | |
MD5:— | SHA256:— | |||
| 2892 | Download.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\CookiesCopy | — | |
MD5:— | SHA256:— | |||
| 2892 | Download.exe | C:\ProgramData\85fuRT2EeqyQwIKY\moz_cookies.db-shm | — | |
MD5:— | SHA256:— | |||
| 2364 | 41ce8dc9fe52cbb66ddf436ec0d9160bf9ce9194c423fbc0397705793f8ddc2c.exe | C:\Program Files\Doper\Download.exe | executable | |
MD5:— | SHA256:— | |||
| 2364 | 41ce8dc9fe52cbb66ddf436ec0d9160bf9ce9194c423fbc0397705793f8ddc2c.exe | C:\Program Files\Doper\DowloadX.exe | executable | |
MD5:— | SHA256:— | |||
| 2892 | Download.exe | C:\ProgramData\85fuRT2EeqyQwIKY\moz_cookies.db | sqlite | |
MD5:— | SHA256:— | |||
| 2892 | Download.exe | C:\ProgramData\85fuRT2EeqyQwIKY\Files\Browsers\Cookies\Mozilla_Firefox_Cookies_QYJRubT.txt | text | |
MD5:— | SHA256:— | |||
| 2892 | Download.exe | C:\ProgramData\85fuRT2EeqyQwIKY\moz_forms.db | sqlite | |
MD5:— | SHA256:— | |||
| 2892 | Download.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\line[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
7
DNS requests
4
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2892 | Download.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line | unknown | text | 150 b | malicious |
2892 | Download.exe | POST | 200 | 8.208.19.185:80 | http://cede01.info/index.php | US | text | 3 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3900 | CScript.exe | 88.99.66.31:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
2892 | Download.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
2892 | Download.exe | 8.208.19.185:80 | cede01.info | Level 3 Communications, Inc. | US | malicious |
2776 | DowloadX.exe | 18.205.93.0:443 | bitbucket.org | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iplogger.org |
| shared |
ip-api.com |
| malicious |
cede01.info |
| malicious |
bitbucket.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2892 | Download.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2892 | Download.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2892 | Download.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
2892 | Download.exe | A Network Trojan was detected | STEALER [PTsecurity] CryptBot |
2892 | Download.exe | A Network Trojan was detected | ET TROJAN Suspicious Zipped Filename in Outbound POST Request (Mozilla_Firefox_Cookies) M2 |
2892 | Download.exe | A Network Trojan was detected | STEALER [PTsecurity] Stealer.BrowserPassview |
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
Download.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
DowloadX.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|