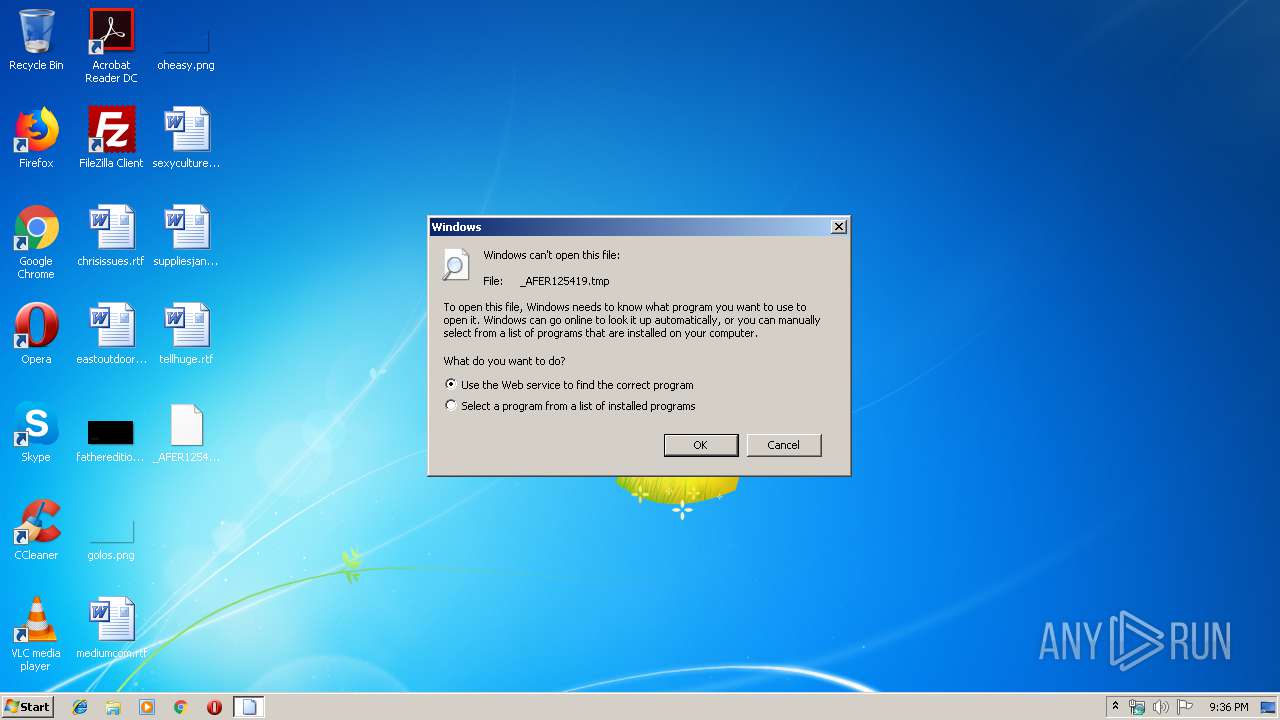
| File name: | _AFER125419.tmp |
| Full analysis: | https://app.any.run/tasks/da8363a9-fb91-412f-aa0f-432065a5a515 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | March 21, 2019, 21:36:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 0059549BED7D7A3426B31620267D7644 |
| SHA1: | BDE82DE71FDEE9A47E3AB74250DA2E6A3C9EAB8E |
| SHA256: | 41CE0B73781A31E9A23C8D5CC3171352DD21D5DBE4BAE1662B82A3D5B97BFE0A |
| SSDEEP: | 12288:hwltpc6P6jeiwltpc6P6jefcqnSA64bRSQs:Clrc6P6jAlrc6P6j4cxedSQs |
MALICIOUS
FORMBOOK was detected
- explorer.exe (PID: 1696)
Connects to CnC server
- explorer.exe (PID: 1696)
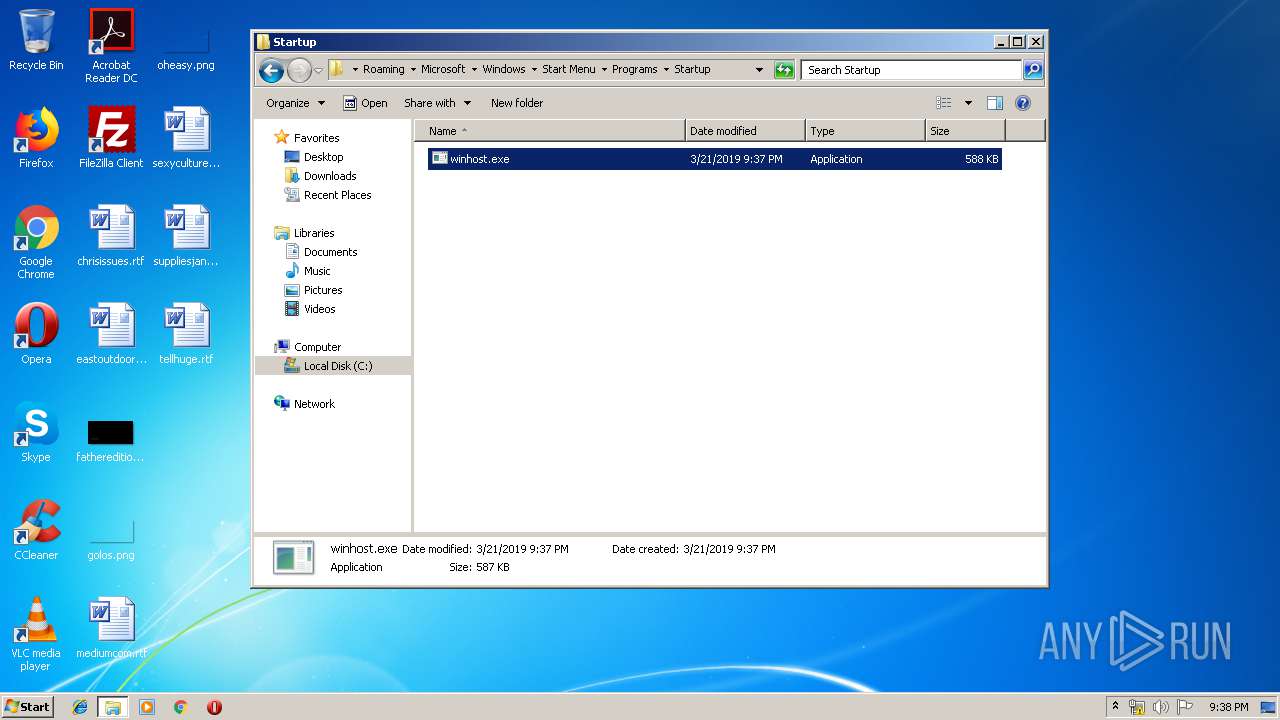
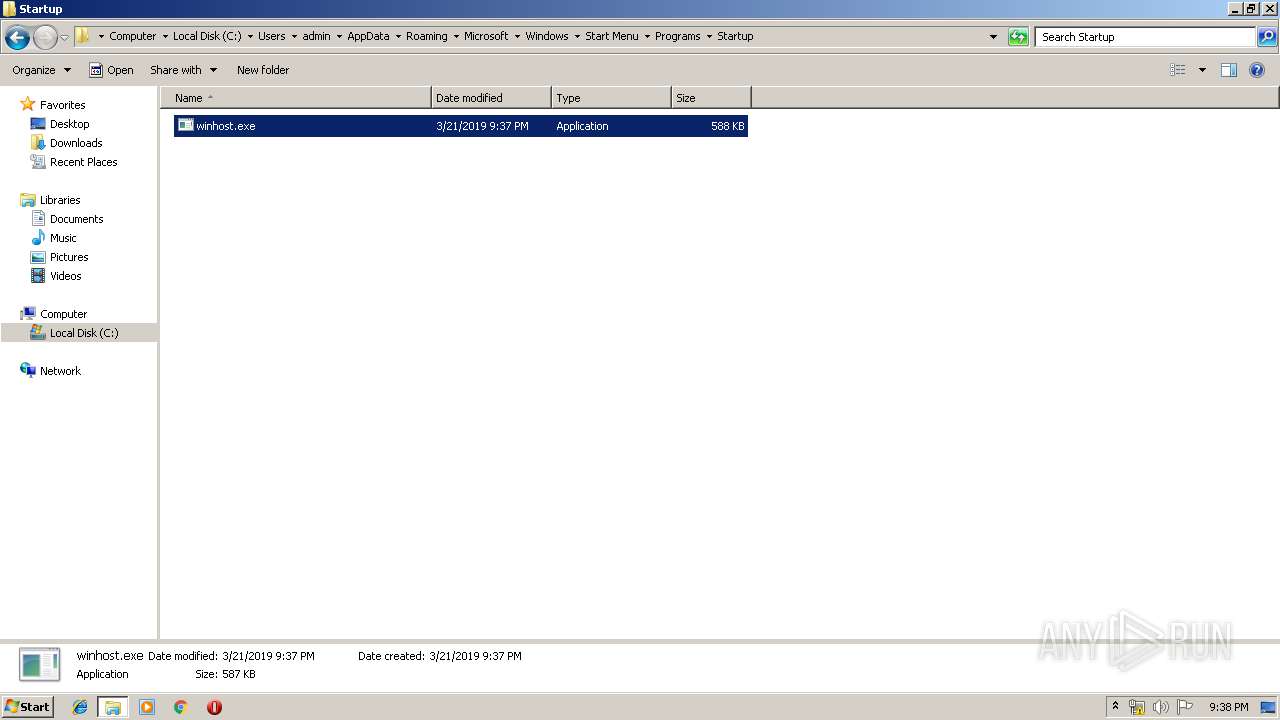
Changes the autorun value in the registry
- rundll32.exe (PID: 2868)
Formbook was detected
- rundll32.exe (PID: 2868)
- Firefox.exe (PID: 1556)
Actions looks like stealing of personal data
- rundll32.exe (PID: 2868)
Stealing of credential data
- rundll32.exe (PID: 2868)
SUSPICIOUS
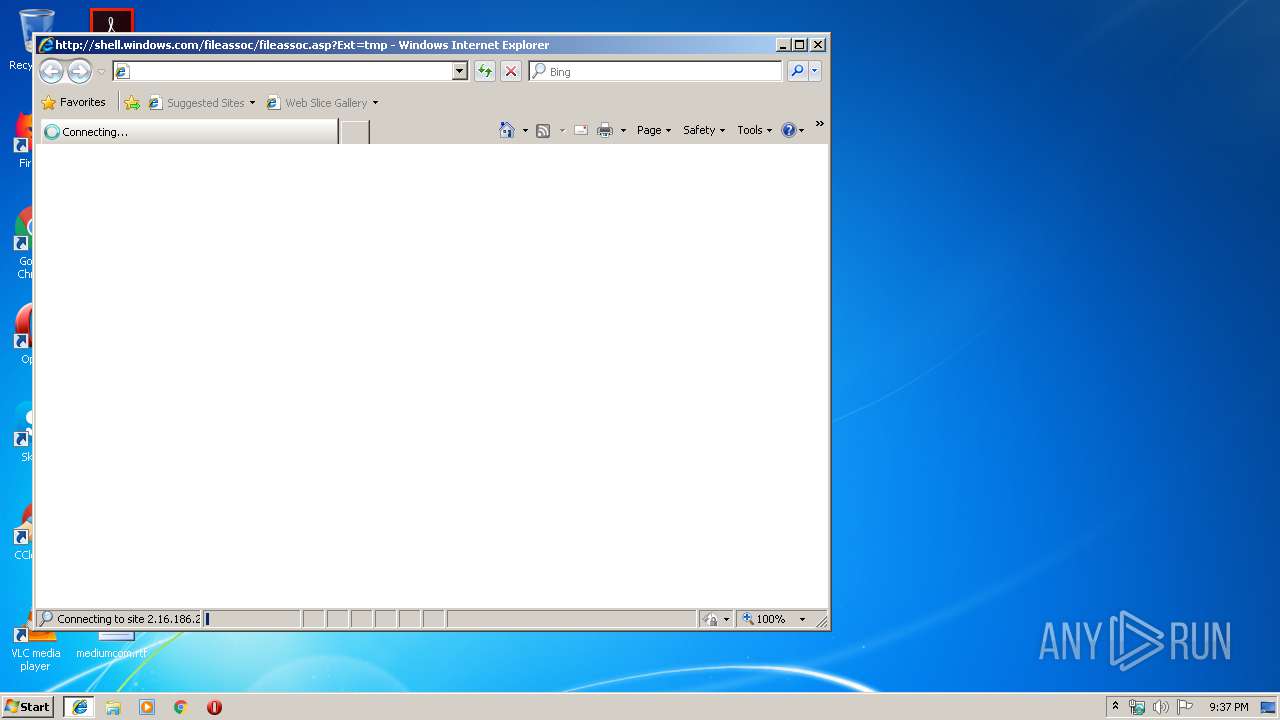
Starts Internet Explorer
- rundll32.exe (PID: 2272)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 1696)
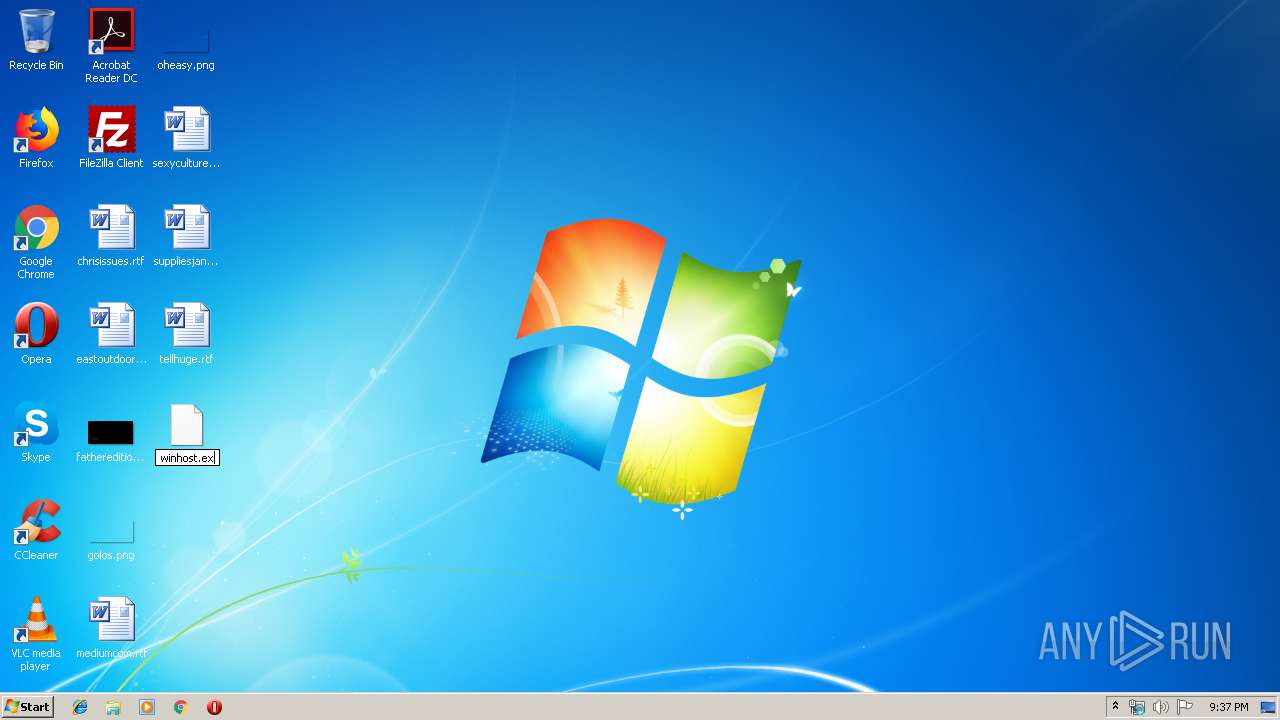
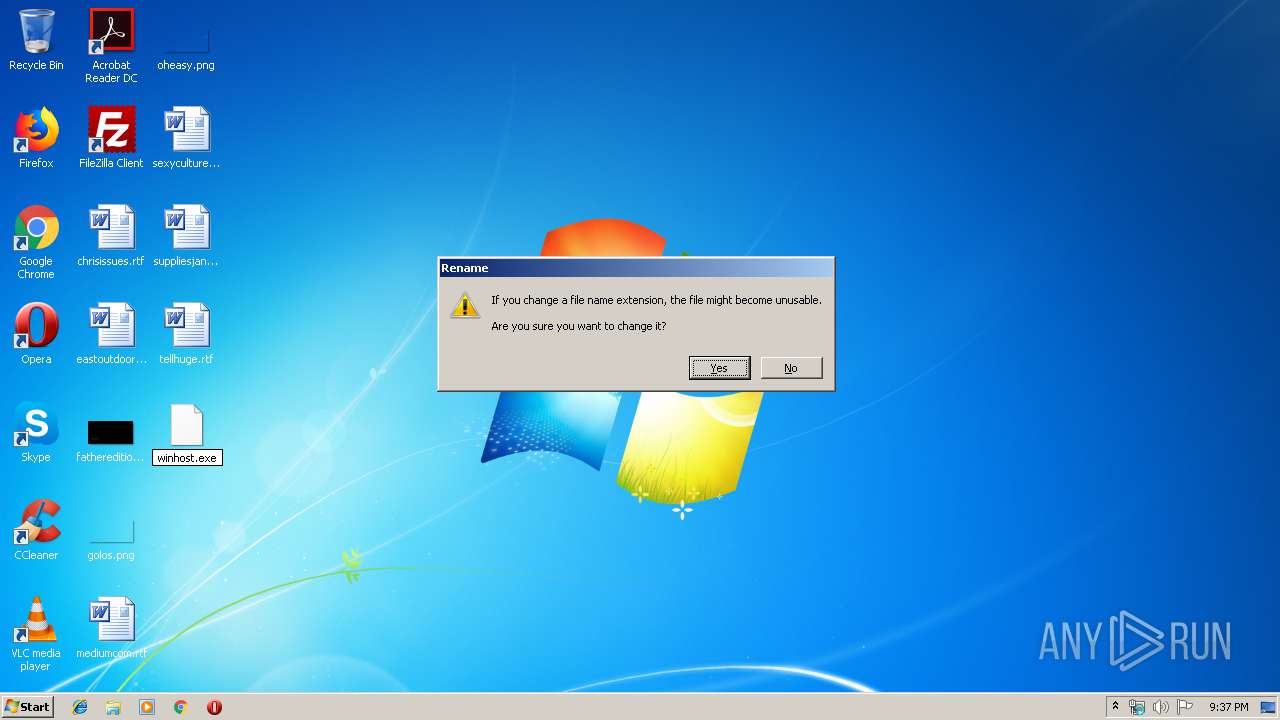
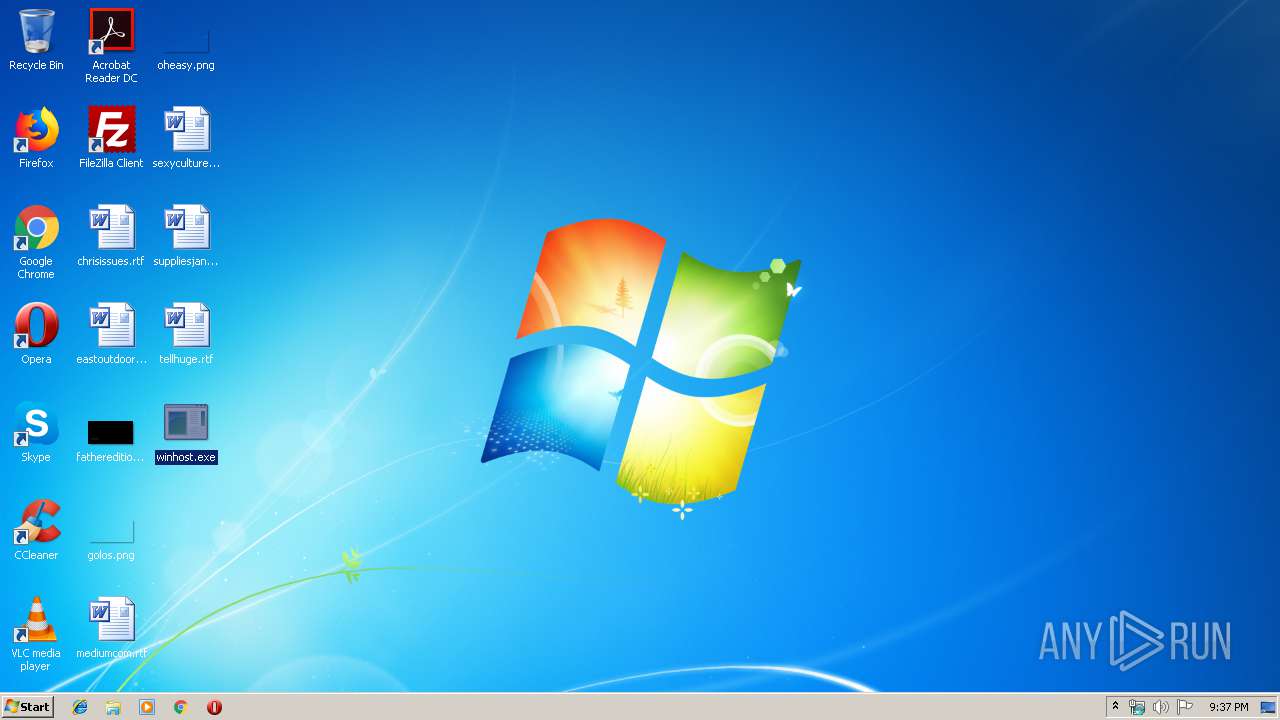
Application launched itself
- winhost.exe (PID: 2688)
- update_df4an.exe (PID: 236)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 2868)
Executable content was dropped or overwritten
- explorer.exe (PID: 1696)
- DllHost.exe (PID: 3916)
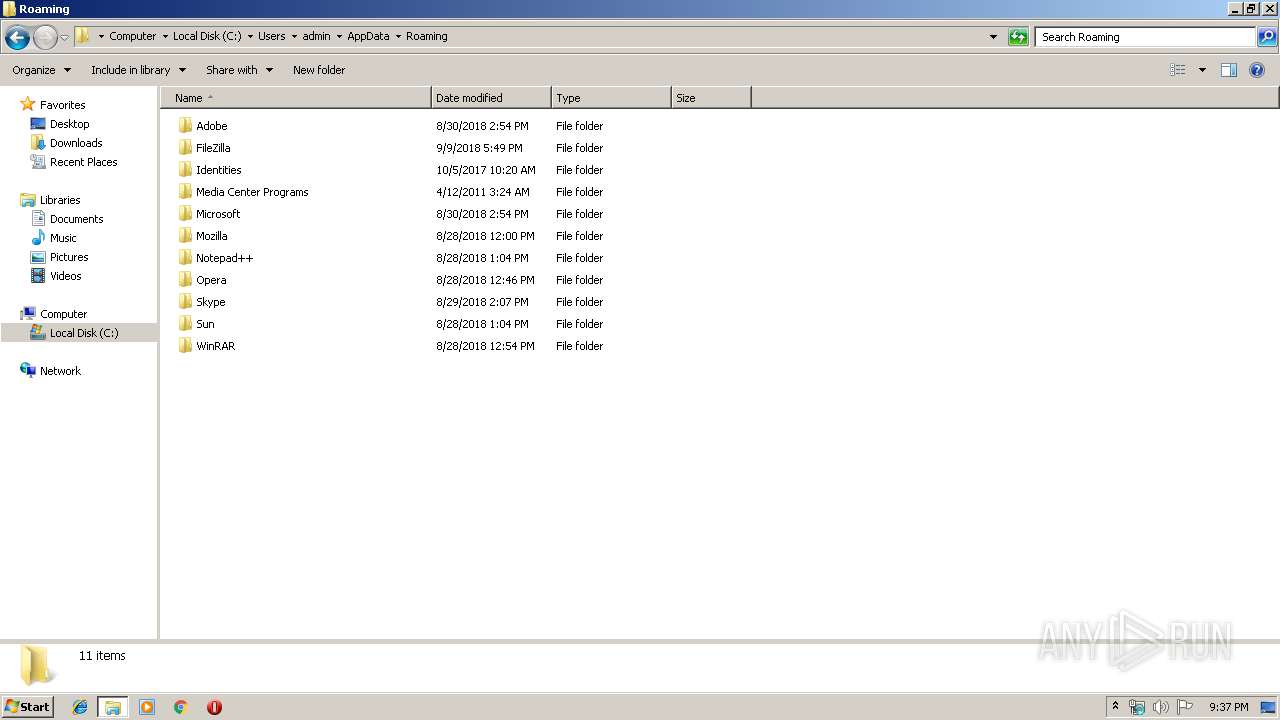
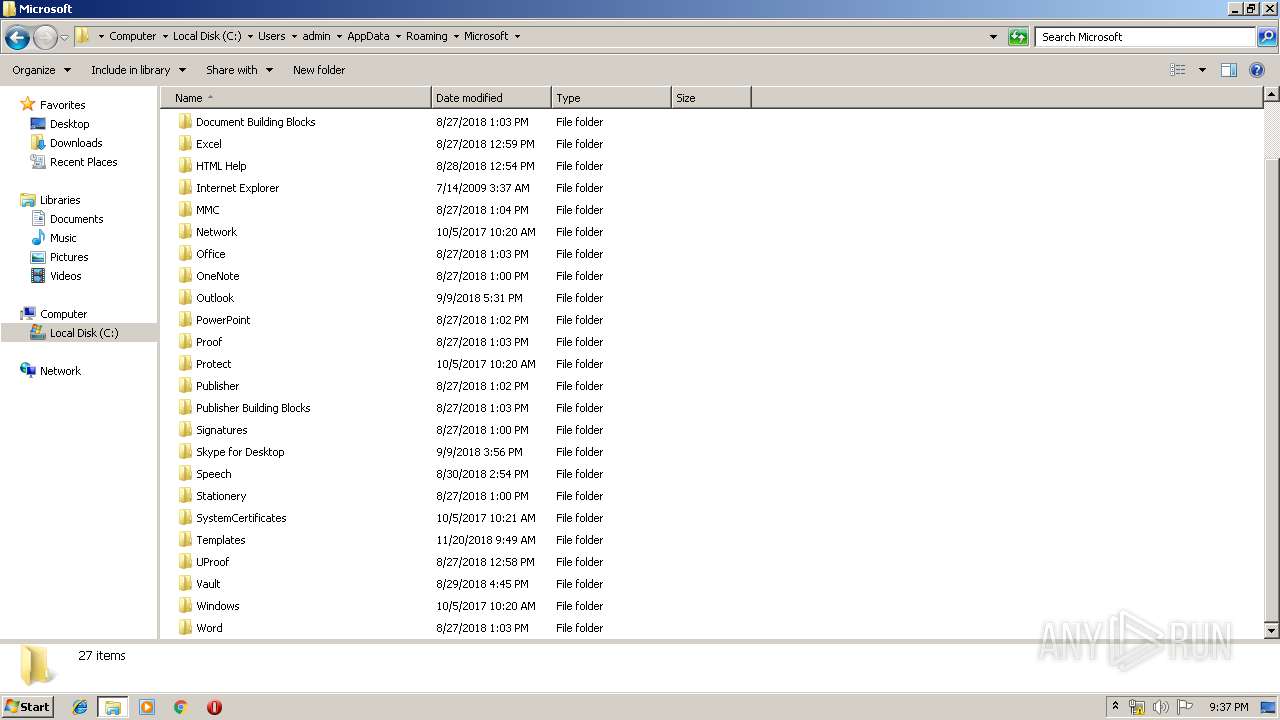
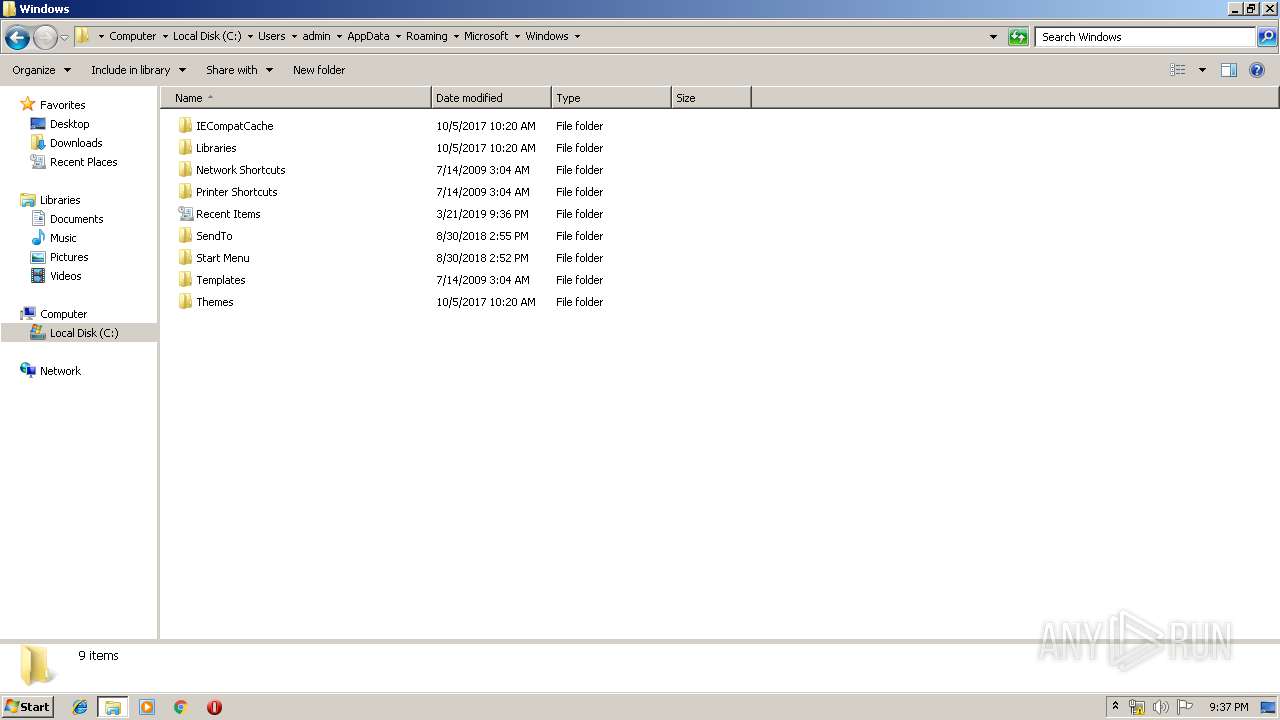
Creates files in the user directory
- rundll32.exe (PID: 2868)
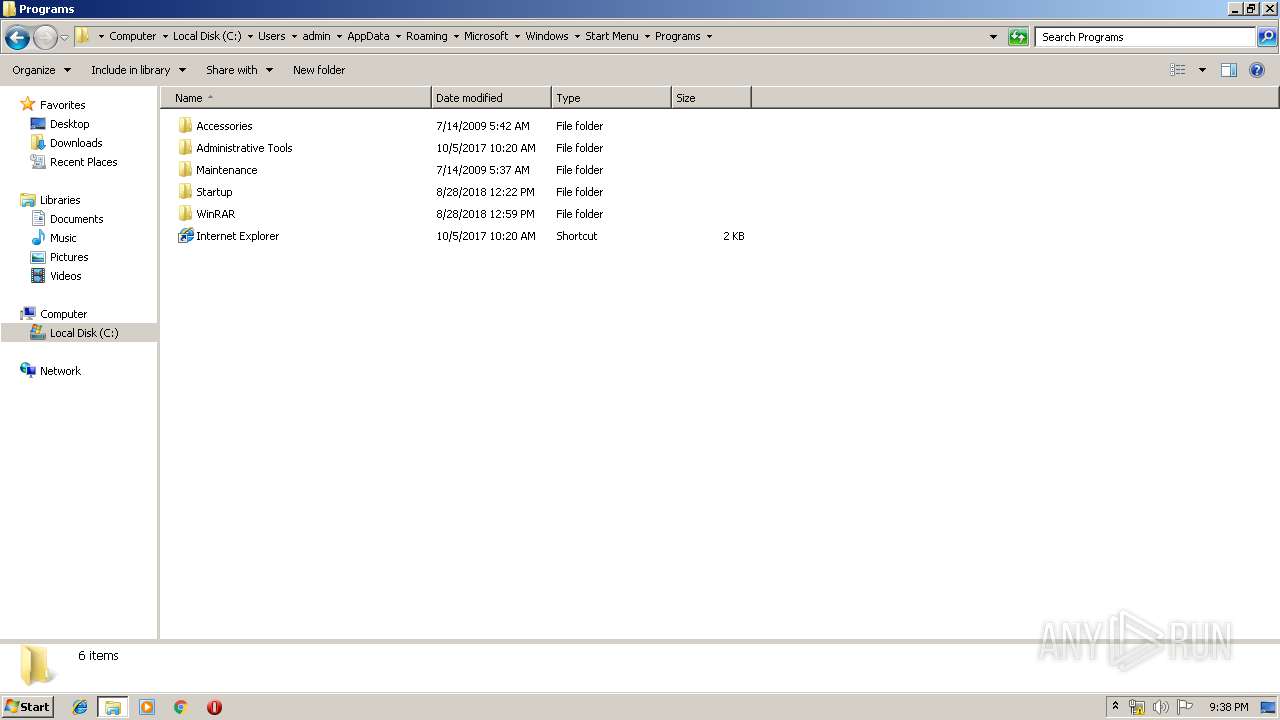
Creates files in the program directory
- DllHost.exe (PID: 3916)
Loads DLL from Mozilla Firefox
- rundll32.exe (PID: 2868)
Executes scripts
- explorer.exe (PID: 1696)
INFO
Changes internet zones settings
- iexplore.exe (PID: 572)
Creates files in the user directory
- iexplore.exe (PID: 2608)
- Firefox.exe (PID: 1556)
Application launched itself
- iexplore.exe (PID: 572)
Reads Internet Cache Settings
- iexplore.exe (PID: 2608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (81) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.2) |
| .exe | | | Win32 Executable (generic) (4.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.2) |
| .exe | | | Generic Win/DOS Executable (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1999:12:20 05:01:24+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 448512 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6f6ae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | retries |
| FileVersion: | 1.0.0.0 |
| InternalName: | retries.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | retries.exe |
| ProductName: | retries |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Dec-1999 04:01:24 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | retries |
| FileVersion: | 1.0.0.0 |
| InternalName: | retries.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFilename: | retries.exe |
| ProductName: | retries |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 20-Dec-1999 04:01:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0006D6B4 | 0x0006D800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.66212 |
.rsrc | 0x00070000 | 0x00000600 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.02439 |
.reloc | 0x00072000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
52
Monitored processes
16
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 236 | "C:\Program Files\Qx4wx6tt8\update_df4an.exe" | C:\Program Files\Qx4wx6tt8\update_df4an.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: retries Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | "C:\Windows\System32\autochk.exe" | C:\Windows\System32\autochk.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto Check Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
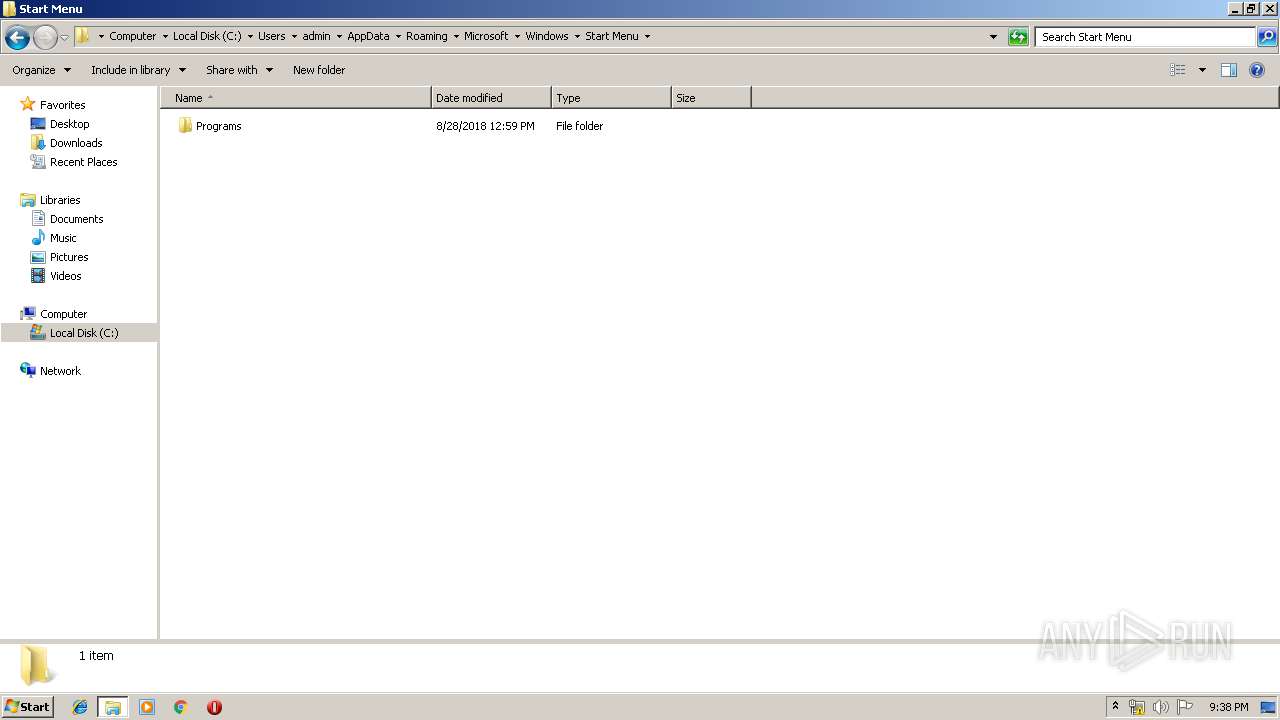
| 1472 | /c del "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\winhost.exe" | C:\Windows\System32\cmd.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | rundll32.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 1696 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2204 | "C:\Windows\System32\wscript.exe" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2272 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\_AFER125419.tmp | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:572 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 061
Read events
4 702
Write events
358
Delete events
1
Modification events
| (PID) Process: | (572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {7767BDB3-4C21-11E9-A302-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307030004001500150025000400ED01 | |||
Executable files
4
Suspicious files
73
Text files
10
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF891CF8D8151147AE.TMP | — | |
MD5:— | SHA256:— | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{7767BDB5-4C21-11E9-A302-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF0EC49C80471E315B.TMP | — | |
MD5:— | SHA256:— | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{7767BDB4-4C21-11E9-A302-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF01448C94BDA696D8.TMP | — | |
MD5:— | SHA256:— | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{7767BDB3-4C21-11E9-A302-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 1696 | explorer.exe | C:\Users\admin\AppData\Local\Temp\Qx4wx6tt8\update_df4an.exe | executable | |
MD5:— | SHA256:— | |||
| 2608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
12
DNS requests
12
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2608 | iexplore.exe | GET | 302 | 104.109.80.115:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=tmp | NL | — | — | whitelisted |
1696 | explorer.exe | GET | — | 69.195.124.189:80 | http://www.samarassociates.com/ap/?9r=5fxGkrR/2/H5heH/XzwJKcXdZihMsEpdLbBd8GWuTo+ViGuxavEuHccHBJD1UjrShdIbtQ==&Otcl=vZ14dx4XcnyhUDd | US | — | — | malicious |
1696 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.batdongsanmb.com/ap/ | US | — | — | shared |
1696 | explorer.exe | GET | 404 | 176.28.103.205:80 | http://www.carlossalmeron.com/ap/?9r=L3hKdfiLY5Ax6vp0piztrF2U+7KLJo/5poVQ8F+dqivauxgGv4SS5FbODDGEnhAo8ACGMg==&Otcl=vZ14dx4XcnyhUDd&sql=1 | ES | html | 320 b | malicious |
1696 | explorer.exe | POST | — | 176.28.103.205:80 | http://www.carlossalmeron.com/ap/ | ES | — | — | malicious |
1696 | explorer.exe | POST | — | 176.28.103.205:80 | http://www.carlossalmeron.com/ap/ | ES | — | — | malicious |
1696 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.batdongsanmb.com/ap/ | US | — | — | shared |
1696 | explorer.exe | GET | 302 | 23.20.239.12:80 | http://www.batdongsanmb.com/ap/?9r=7sNsHt+u0ir4W+unInP1cxFLila42ixSMsHMM1aBPDuN/Ix9v8Tj9CtAB1sOVBCaIrD/Dw==&Otcl=vZ14dx4XcnyhUDd&sql=1 | US | html | 188 b | shared |
572 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1696 | explorer.exe | POST | — | 176.28.103.205:80 | http://www.carlossalmeron.com/ap/ | ES | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
572 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2608 | iexplore.exe | 104.109.80.115:80 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
2608 | iexplore.exe | 2.16.186.24:80 | shell.windows.com | Akamai International B.V. | — | whitelisted |
1696 | explorer.exe | 69.195.124.189:80 | www.samarassociates.com | Unified Layer | US | malicious |
1696 | explorer.exe | 23.20.239.12:80 | www.batdongsanmb.com | Amazon.com, Inc. | US | shared |
1696 | explorer.exe | 176.28.103.205:80 | www.carlossalmeron.com | acens Technologies, S.L. | ES | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
dns.msftncsi.com |
| shared |
www.sibmsharpcopiers.com |
| unknown |
www.samarassociates.com |
| malicious |
www.batdongsanmb.com |
| shared |
www.xinduocheng.com |
| unknown |
www.carlossalmeron.com |
| malicious |
www.chrisandkrystal.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1696 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1696 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1696 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
1696 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
1696 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
1696 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
1696 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1696 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
1696 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
1696 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
7 ETPRO signatures available at the full report