| File name: | 客æ·é款ç³è¯·è¡¨-SUPERLEON NOVIEMBR.exe |
| Full analysis: | https://app.any.run/tasks/b3816505-afe0-49fe-b24d-33bfd0567bef |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | November 20, 2024, 09:09:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 39550A5532AF152DF27A096508A0D4E2 |
| SHA1: | 45317173C2771B28460DC4A473C2532983977DE1 |
| SHA256: | 41B359E55E25D9F92E6F4EA1B88B3CFE7C6CA962075A60AC9417548AD190C41E |
| SSDEEP: | 24576:QKMGHfgPpKL4a/l8yPMrBu8RLhK3lpNO5fm2ZHxe31wkxo4wwVTnQPK:QKMGHYPpKL4a/l8SMrBuoLhK3lpg5fF4 |
MALICIOUS
GULOADER has been detected
- 客æ·é款ç³è¯·è¡¨-SUPERLEON NOVIEMBR.exe (PID: 2160)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 4516)
Starts POWERSHELL.EXE for commands execution
- 客æ·é款ç³è¯·è¡¨-SUPERLEON NOVIEMBR.exe (PID: 2160)
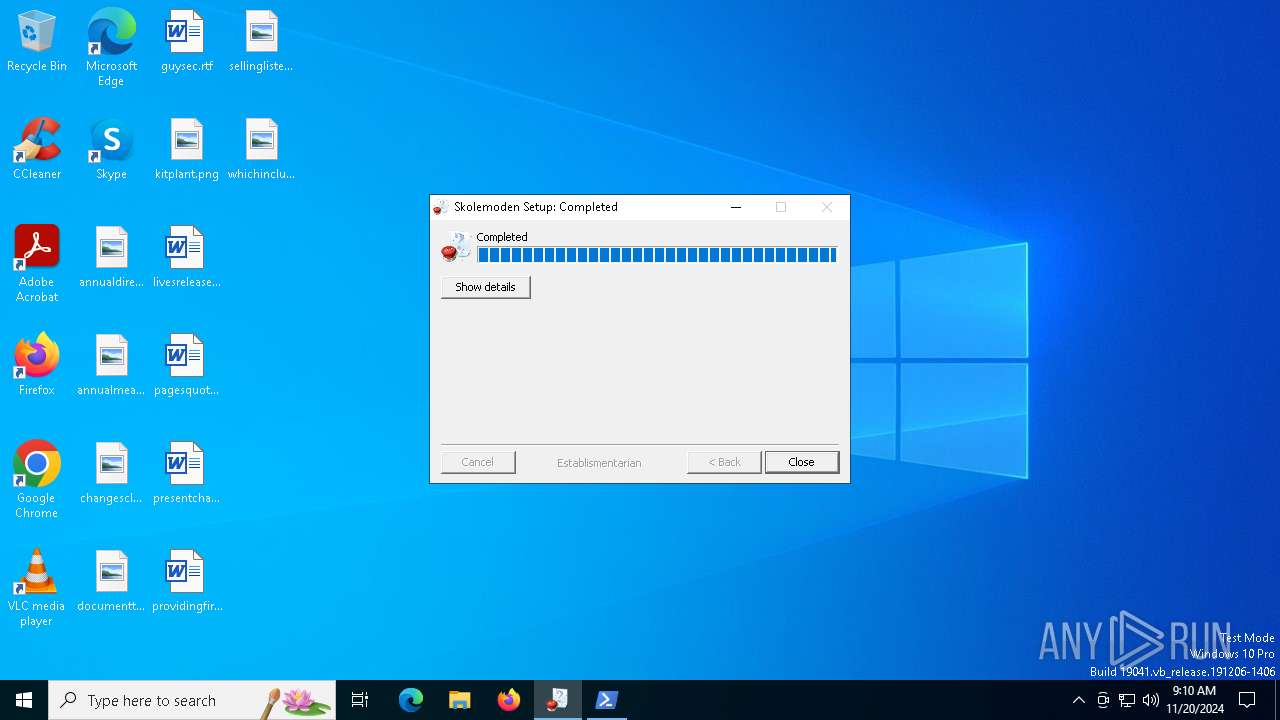
Executes application which crashes
- msiexec.exe (PID: 6460)
INFO
Checks supported languages
- 客æ·é款ç³è¯·è¡¨-SUPERLEON NOVIEMBR.exe (PID: 2160)
Reads the computer name
- 客æ·é款ç³è¯·è¡¨-SUPERLEON NOVIEMBR.exe (PID: 2160)
Creates files or folders in the user directory
- 客æ·é款ç³è¯·è¡¨-SUPERLEON NOVIEMBR.exe (PID: 2160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 03:57:48+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.0.0 |
| ProductVersionNumber: | 3.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | falskmntnerens trkrudes microblepharia |
| CompanyName: | gefulltefish prickiest convenientness |
| FileDescription: | checkende |
| FileVersion: | 3.0.0.0 |
| InternalName: | ridestis.exe |
| ProductVersion: | 3.0.0.0 |
Total processes
131
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2160 | "C:\Users\admin\AppData\Local\Temp\客æ·é款ç³è¯·è¡¨-SUPERLEON NOVIEMBR.exe" | C:\Users\admin\AppData\Local\Temp\客æ·é款ç³è¯·è¡¨-SUPERLEON NOVIEMBR.exe | explorer.exe | ||||||||||||
User: admin Company: gefulltefish prickiest convenientness Integrity Level: MEDIUM Description: checkende Exit code: 4294967295 Version: 3.0.0.0 Modules
| |||||||||||||||
| 4516 | "powershell.exe" -windowstyle minimized "$Havegrund=Get-Content -Raw 'C:\Users\admin\AppData\Roaming\argoters\Necrotizing\Ukristeligheden\Gtevielsen.Pro';$Enmotoret=$Havegrund.SubString(14070,3);.$Enmotoret($Havegrund)" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | 客æ·é款ç³è¯·è¡¨-SUPERLEON NOVIEMBR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6460 | "C:\WINDOWS\SysWOW64\msiexec.exe" | C:\Windows\SysWOW64\msiexec.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 3762504530 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6836 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6460 -s 2076 | C:\Windows\SysWOW64\WerFault.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 099
Read events
8 962
Write events
137
Delete events
0
Modification events
| (PID) Process: | (2160) 客æ·é款ç³è¯·è¡¨-SUPERLEON NOVIEMBR.exe | Key: | HKEY_CURRENT_USER\skoddenes\Uninstall\polypodiaceous\Excretive140 |
| Operation: | write | Name: | Deputeretkamret |
Value: 0 | |||
Executable files
1
Suspicious files
16
Text files
8
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2160 | 客æ·é款ç³è¯·è¡¨-SUPERLEON NOVIEMBR.exe | C:\Users\admin\AppData\Roaming\argoters\Necrotizing\Programbibliotekets\termineret.for | binary | |
MD5:6A58E51F862B68E1512139BA57FC966D | SHA256:62B9CA6B988C819D7FD11C2D73D6A7634B80989CC129A184F0177BB1DB391DF3 | |||
| 2160 | 客æ·é款ç³è¯·è¡¨-SUPERLEON NOVIEMBR.exe | C:\Users\admin\AppData\Roaming\argoters\Necrotizing\Ukristeligheden\nskvrdigste.had | binary | |
MD5:0938BE94531932AB7BE23268164C4B8D | SHA256:B3580AD5E5ACD9167E64EDDB2133A817B253BE860F0C80788900540002C5577E | |||
| 4516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wbygd5o5.hso.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2160 | 客æ·é款ç³è¯·è¡¨-SUPERLEON NOVIEMBR.exe | C:\Users\admin\AppData\Roaming\argoters\Necrotizing\Ukristeligheden\Gtevielsen.Pro | text | |
MD5:433B637E00993C25FF9C0E99137A4FE9 | SHA256:F7297C998E655734E779D3A4B699E8E0B58D263104850A18536628EF4BCFB344 | |||
| 2160 | 客æ·é款ç³è¯·è¡¨-SUPERLEON NOVIEMBR.exe | C:\Users\admin\AppData\Roaming\argoters\Necrotizing\Melodiseres\Banakite.Tor | binary | |
MD5:82FEC85CA061EB5F2F6F249EFA179539 | SHA256:8BFB0B50216B8E379ADBE03D7DBBD36EF83686899F0E372314558B6AEB25D648 | |||
| 4516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_f1ot3xn4.luu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6460 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:B2968515F3BFB788F5B1D036A2F87795 | SHA256:40FEC07C72BFB56FE91BC86D30AFA69A572D80C48EDC5178ED75248661BDE5A9 | |||
| 6460 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\05DDC6AA91765AACACDB0A5F96DF8199 | binary | |
MD5:E935BC5762068CAF3E24A2683B1B8A88 | SHA256:A8ACCFCFEB51BD73DF23B91F4D89FF1A9EB7438EF5B12E8AFDA1A6FF1769E89D | |||
| 6836 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_msiexec.exe_3ea2e75e41137a81dbe87ebb74dfc6fde299f1a_f3dcd582_79180a0d-37c7-429d-9a3e-bca2d9407315\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6836 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\msiexec.exe.6460.dmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
39
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4932 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6548 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6548 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4800 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6836 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6460 | msiexec.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
6836 | WerFault.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4036 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4932 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4932 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.169:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4932 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |