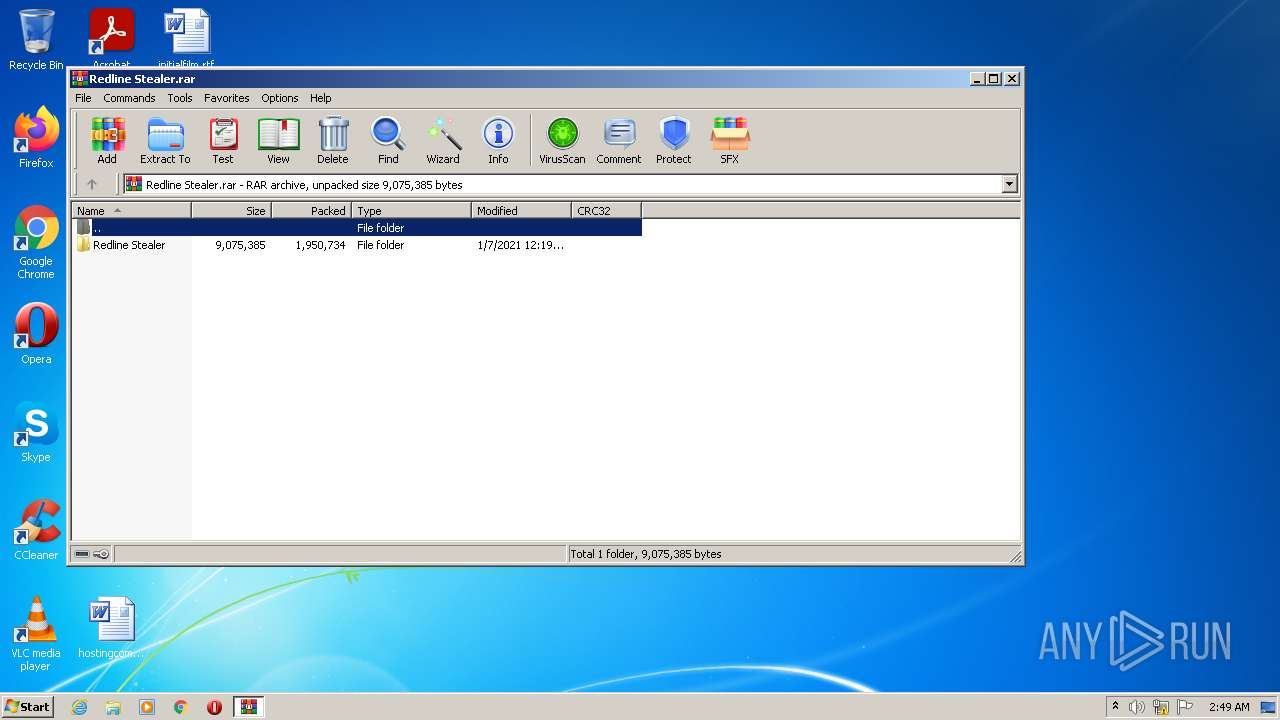
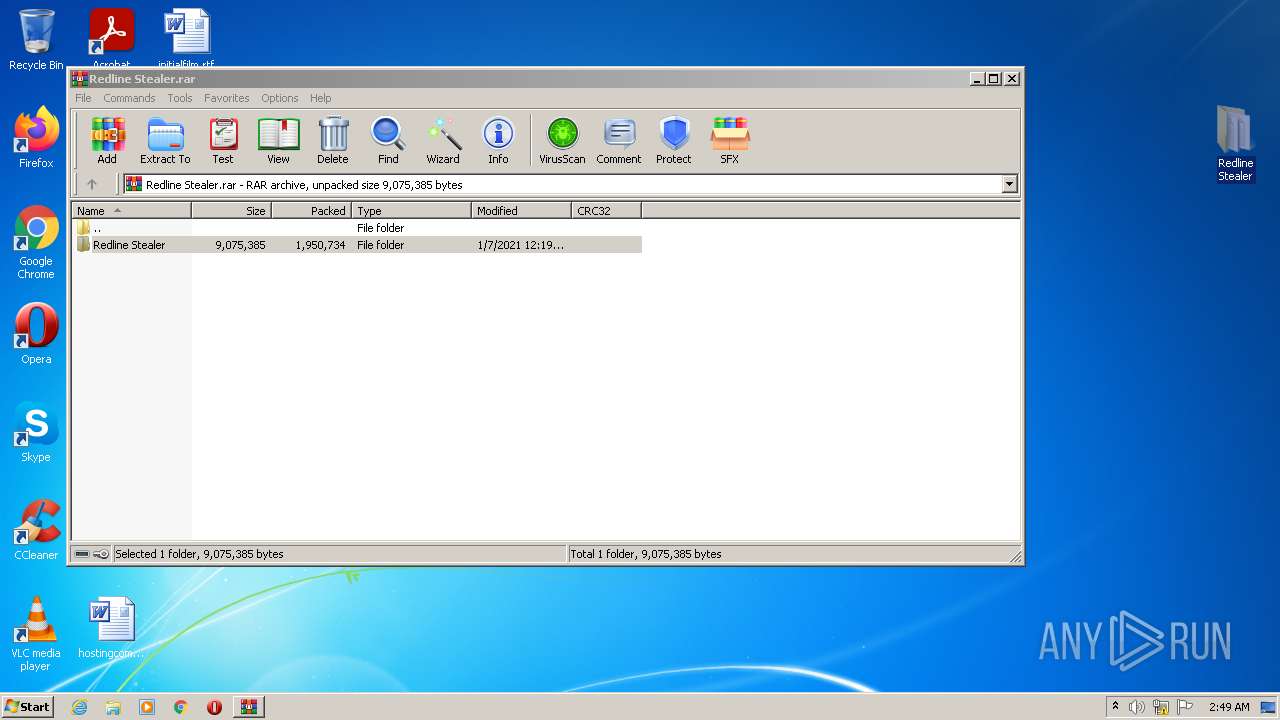
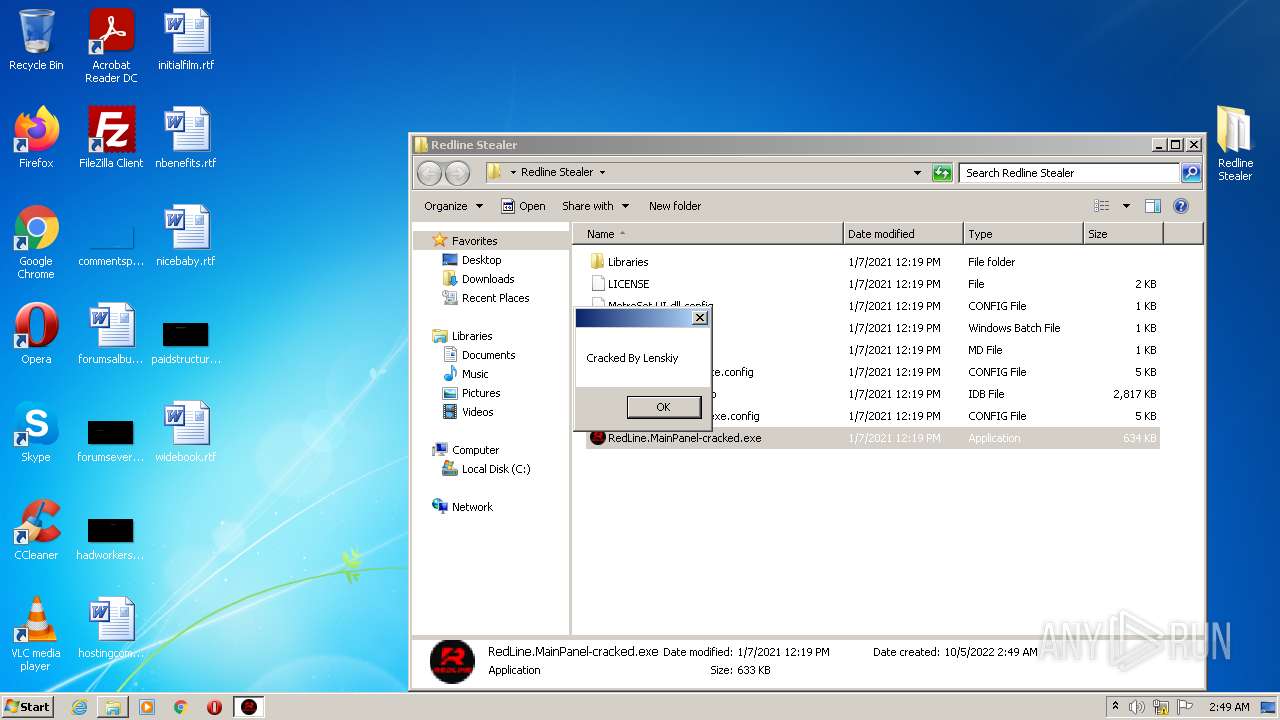
| File name: | Redline Stealer.rar |
| Full analysis: | https://app.any.run/tasks/1d734673-d515-4a97-8ff8-423079e4da9d |
| Verdict: | Malicious activity |
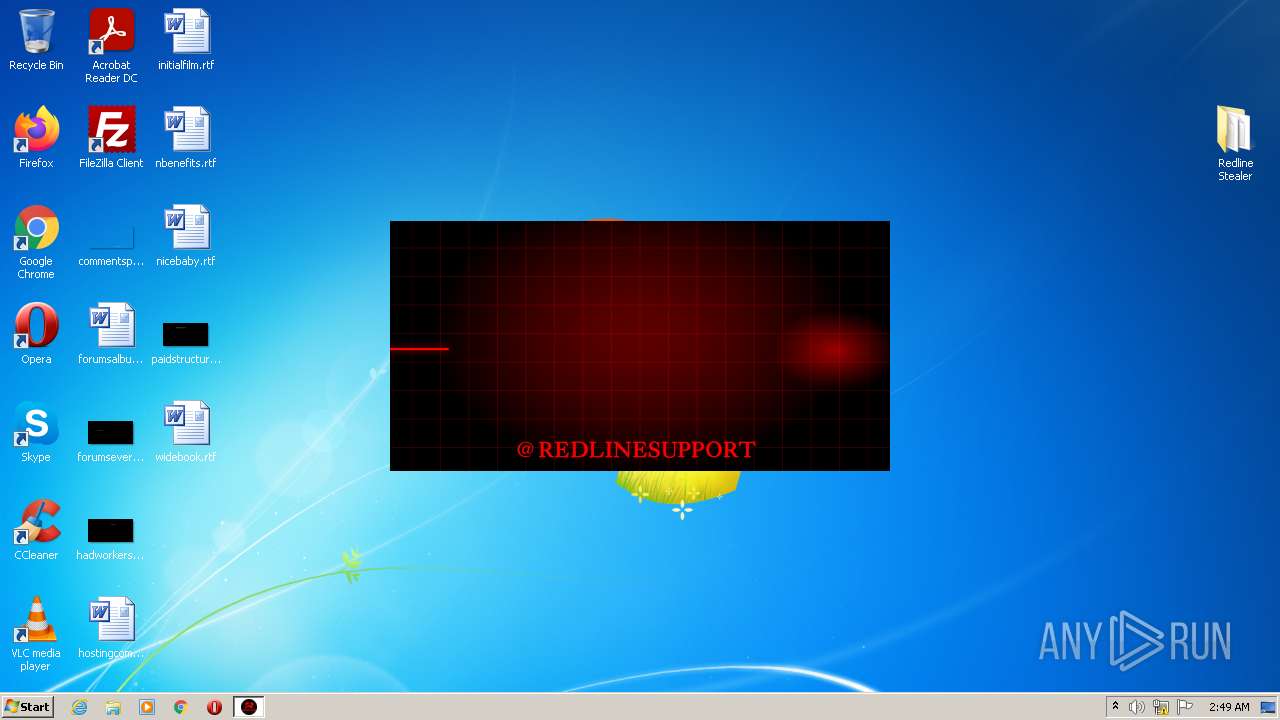
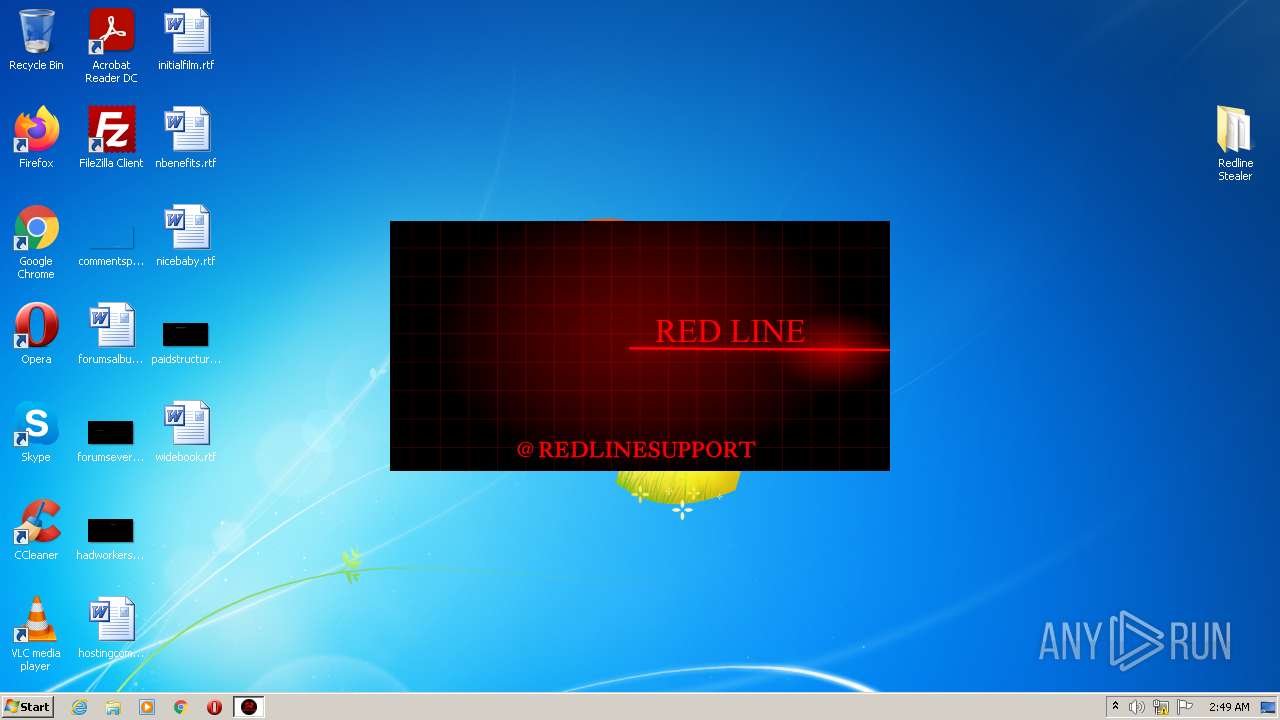
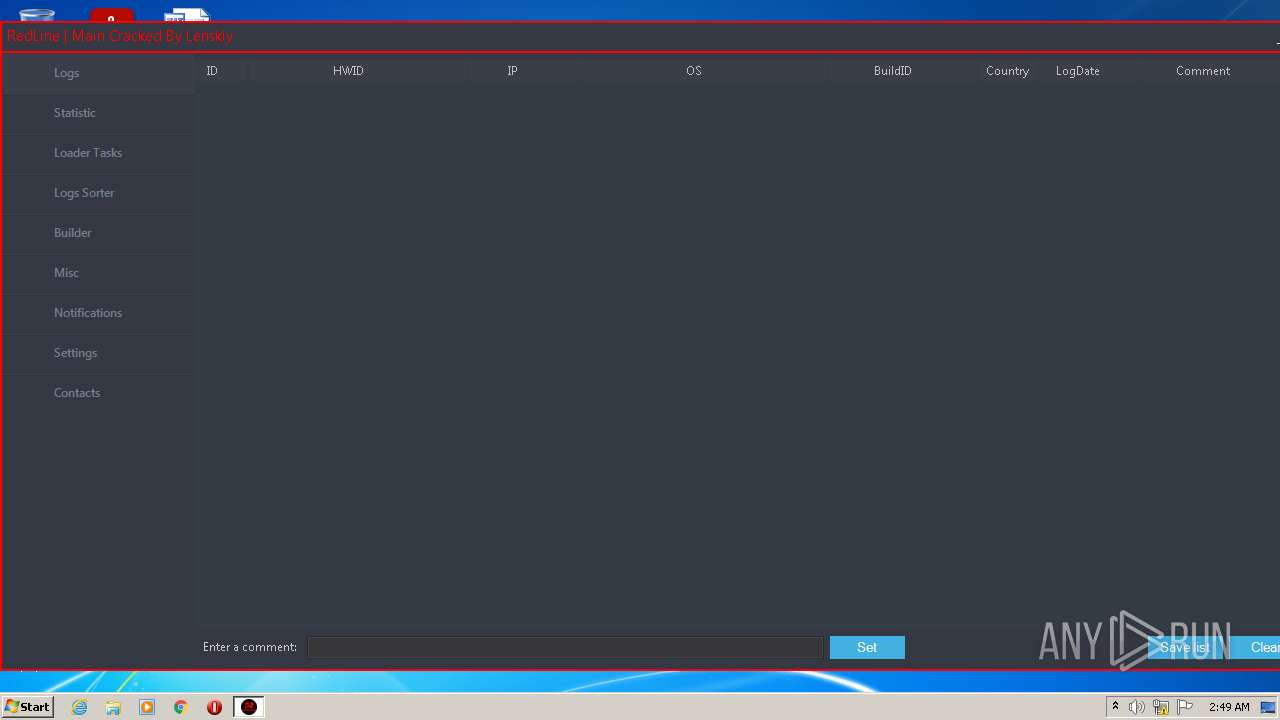
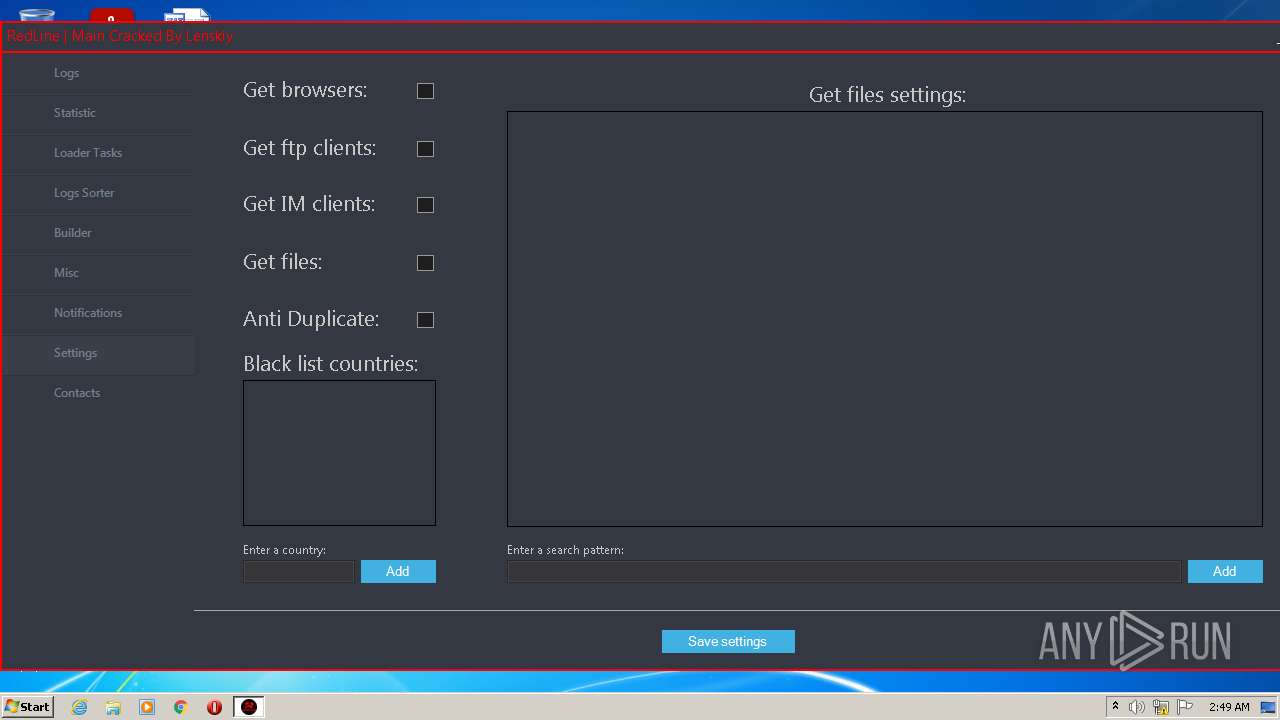
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | October 05, 2022, 01:49:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | D7415F1D29E97D582C278CF3DF04ADE4 |
| SHA1: | E4AB5E38EDC6A106CF6ED5A97DED120DF49650EE |
| SHA256: | 4191CD799AD6D4F6D7ABDF79C91172FF042CA4C6ECC53F1F01BE5F673CAA9656 |
| SSDEEP: | 49152:03PZM4v/kvGmEr61v/onGCRh3un7ehyl3tR2:036o/uGTr6B/oGCLC33tQ |
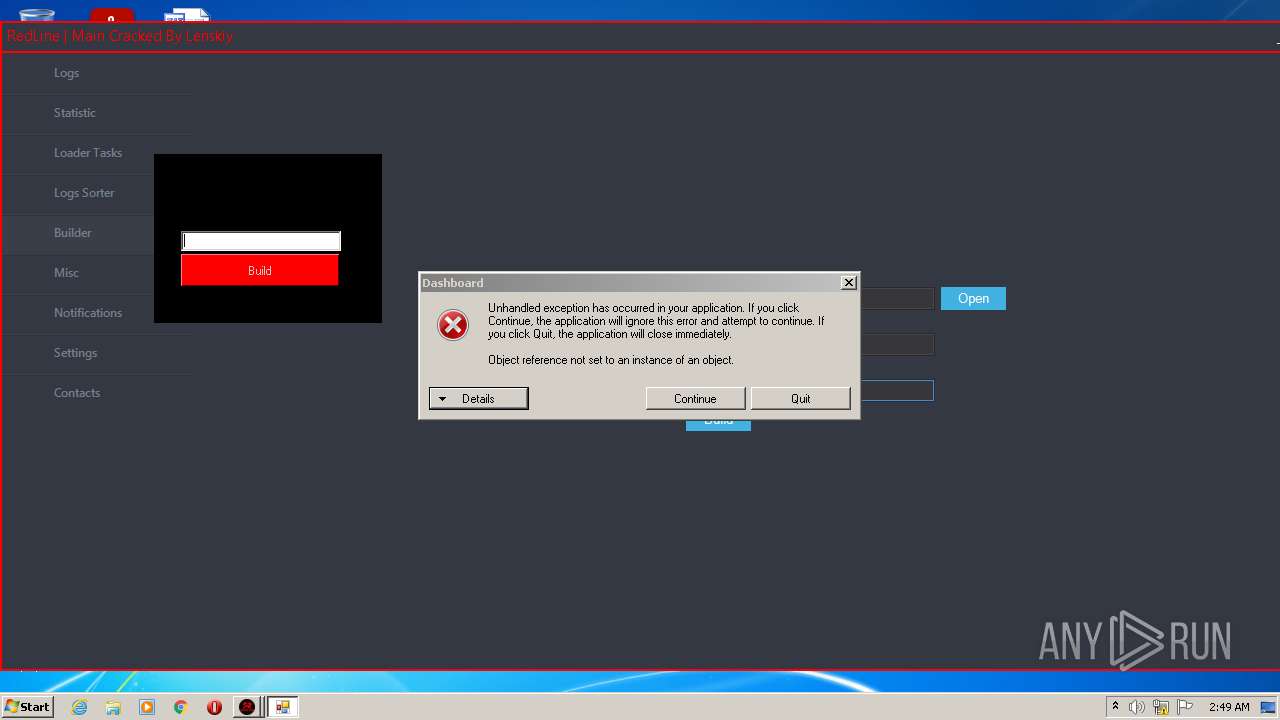
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 464)
- RedLine.MainPanel-cracked.exe (PID: 128)
Application was dropped or rewritten from another process
- RedLine.MainPanel-cracked.exe (PID: 128)
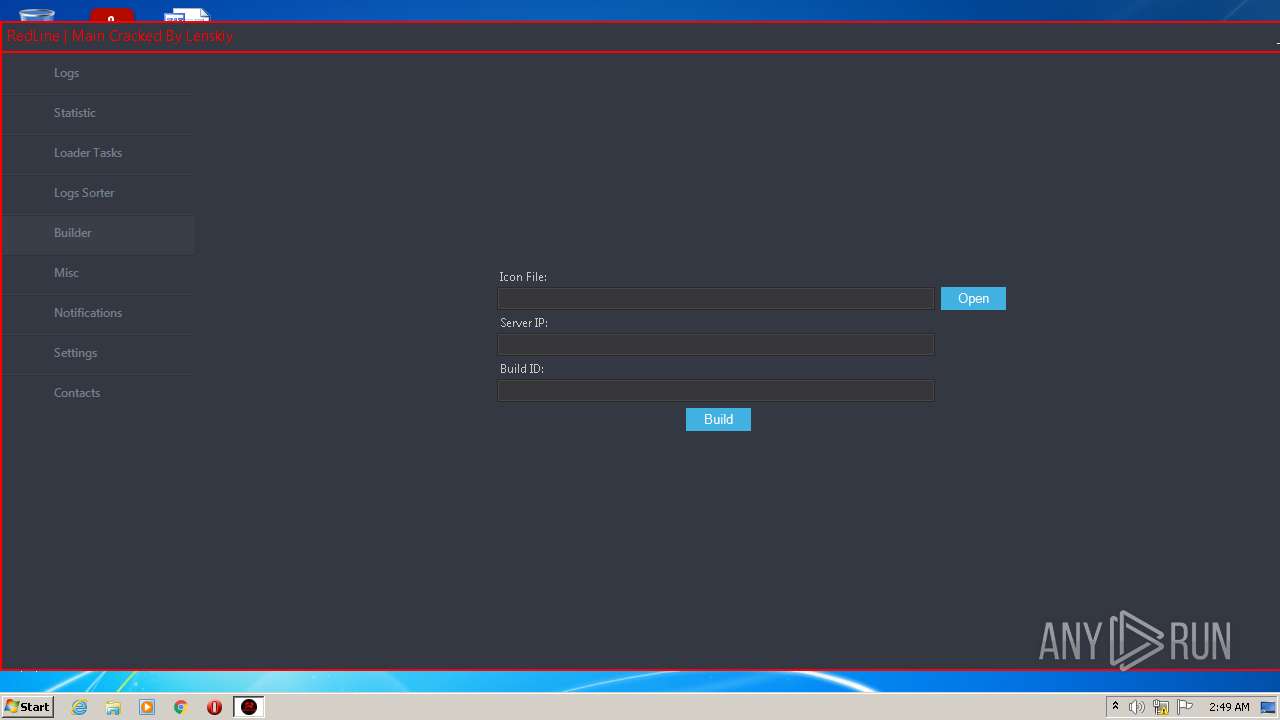
- builder.exe (PID: 3724)
Drops executable file immediately after starts
- WinRAR.exe (PID: 3588)
REDLINE detected by memory dumps
- RedLine.MainPanel-cracked.exe (PID: 128)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3588)
- RedLine.MainPanel-cracked.exe (PID: 128)
- builder.exe (PID: 3724)
Reads the computer name
- WinRAR.exe (PID: 3588)
- RedLine.MainPanel-cracked.exe (PID: 128)
- builder.exe (PID: 3724)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3588)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3588)
Reads Environment values
- RedLine.MainPanel-cracked.exe (PID: 128)
INFO
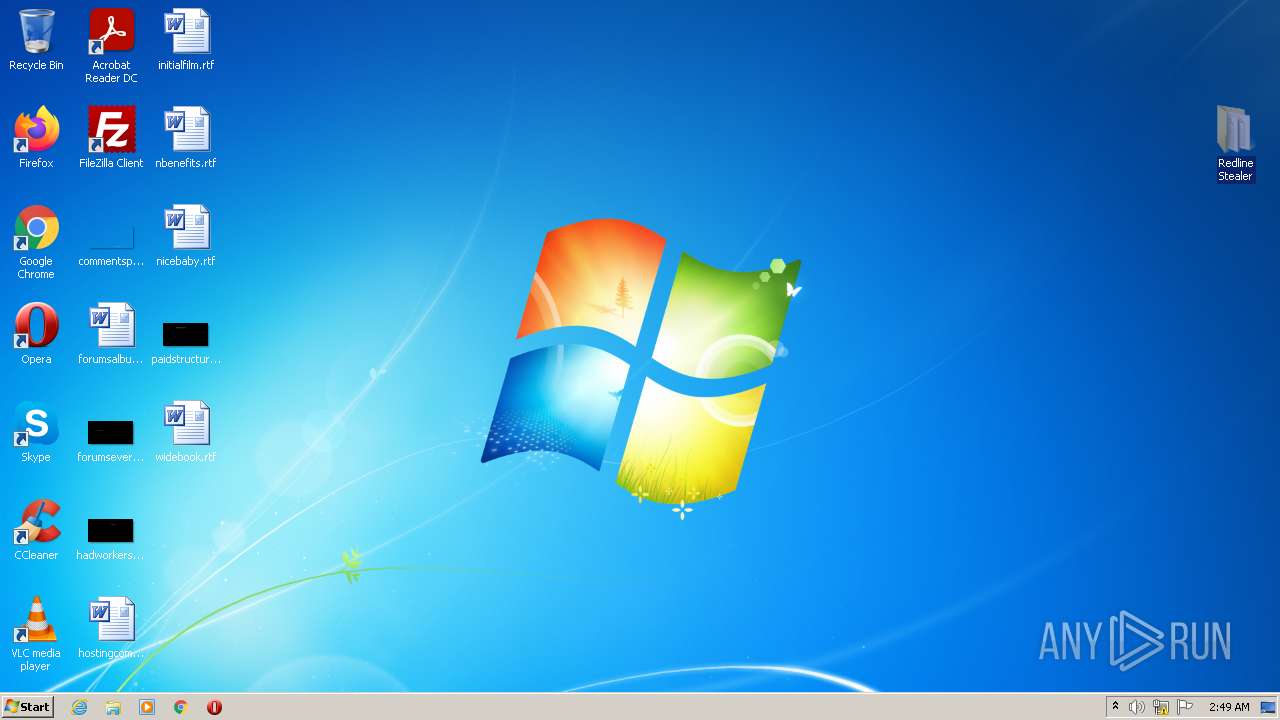
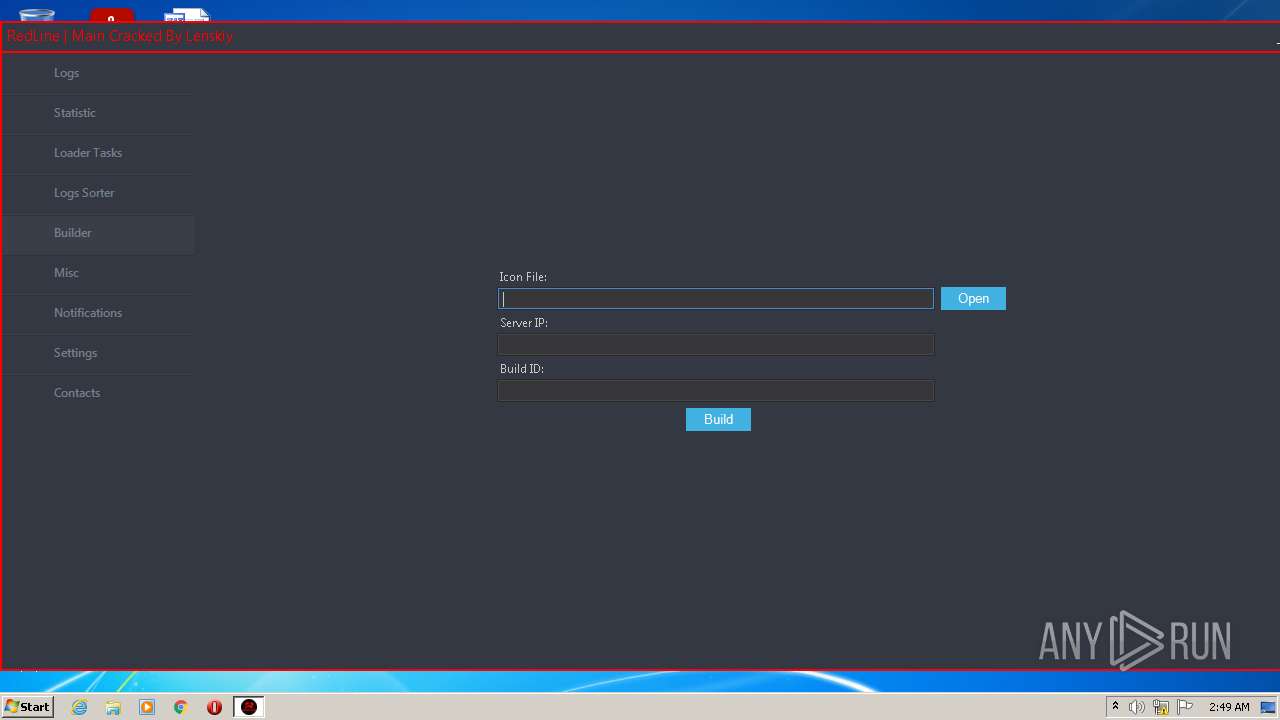
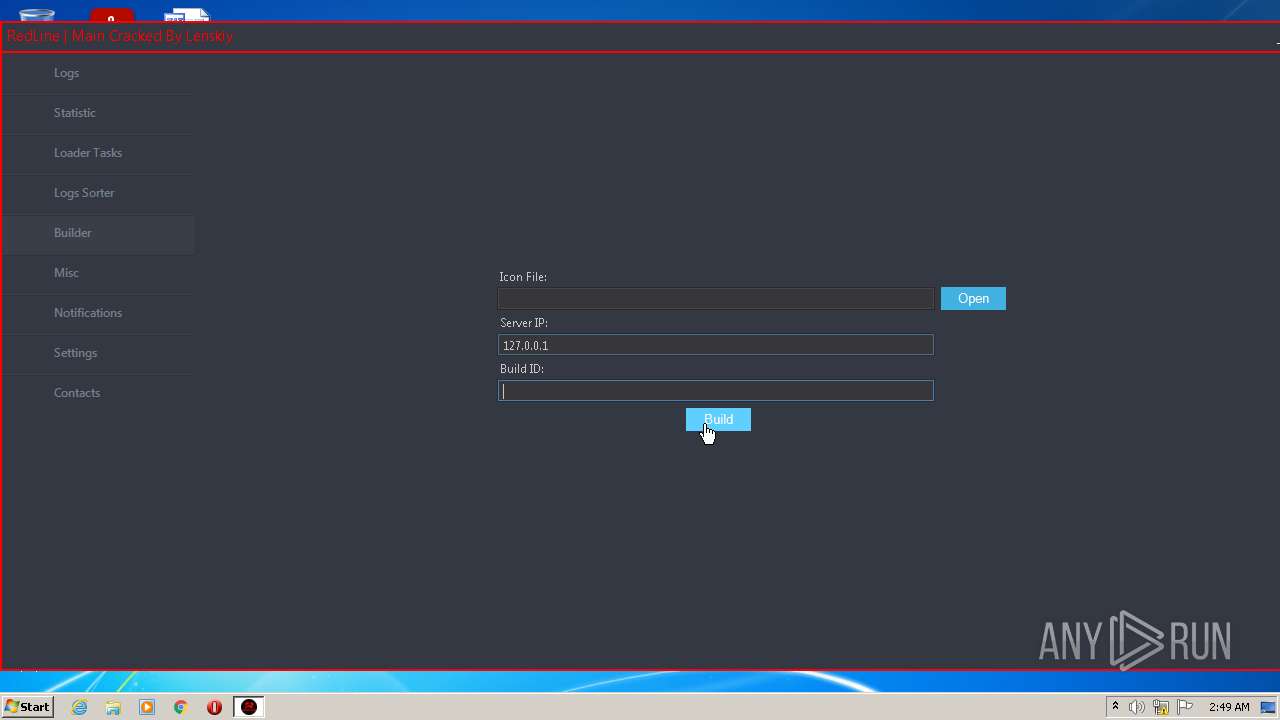
Manual execution by user
- RedLine.MainPanel-cracked.exe (PID: 128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
36
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
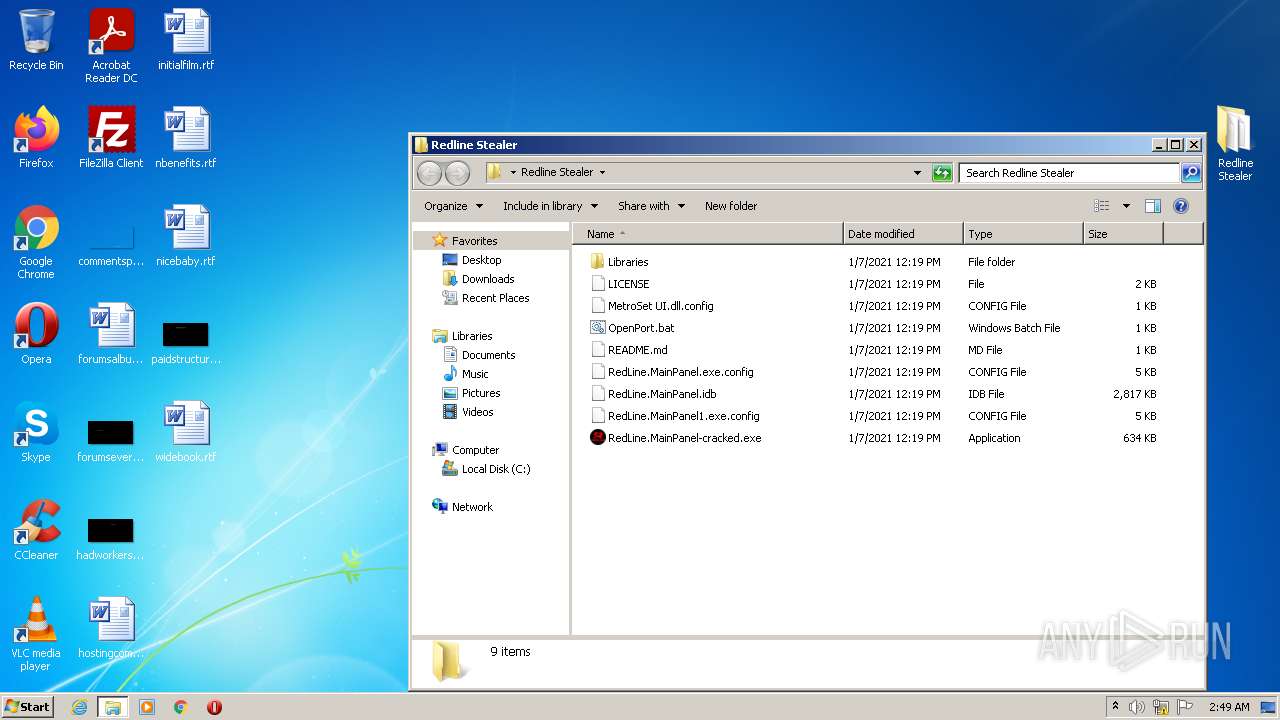
| 128 | "C:\Users\admin\Desktop\Redline Stealer\RedLine.MainPanel-cracked.exe" | C:\Users\admin\Desktop\Redline Stealer\RedLine.MainPanel-cracked.exe | Explorer.EXE | ||||||||||||
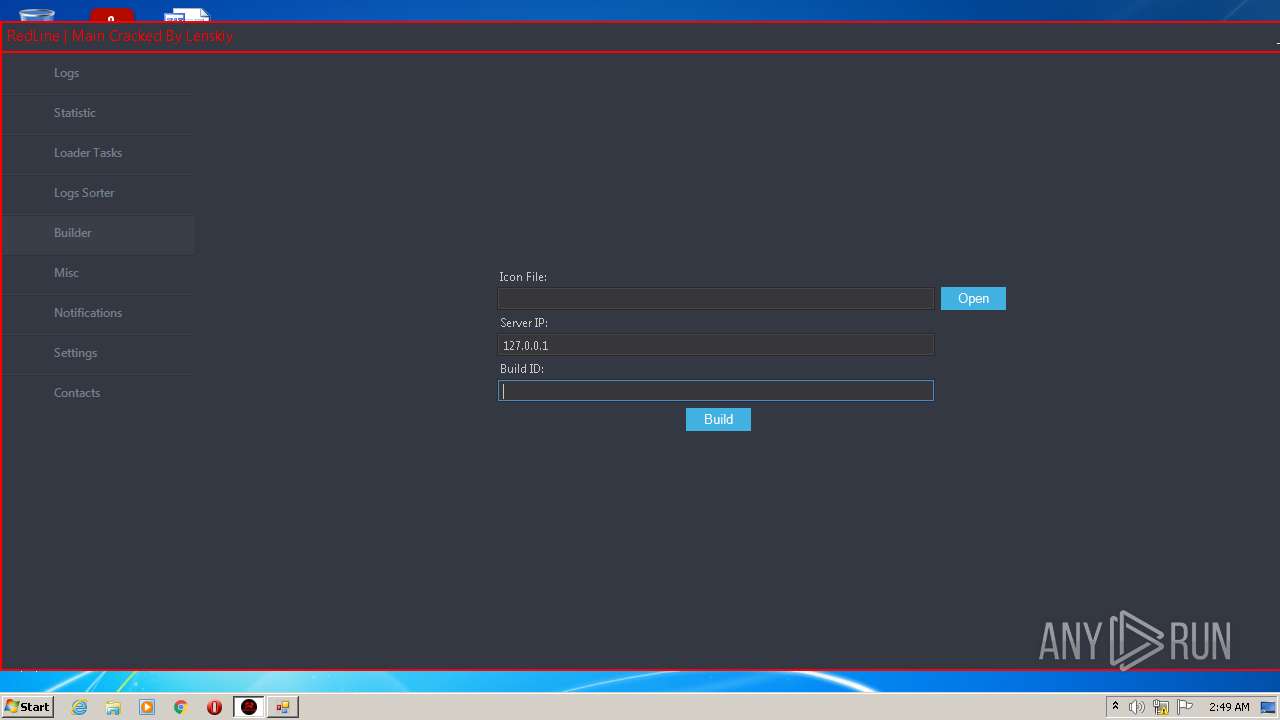
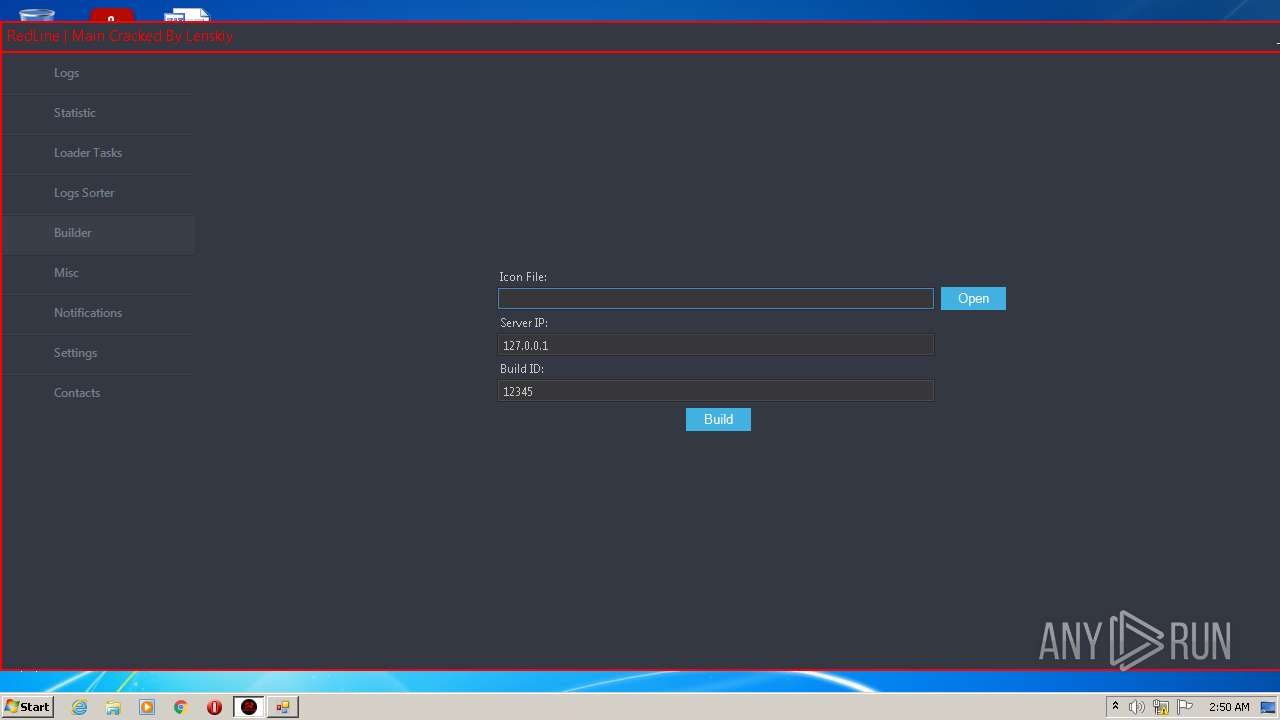
User: admin Integrity Level: MEDIUM Description: RedLinePanel Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 464 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 3588 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Redline Stealer.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
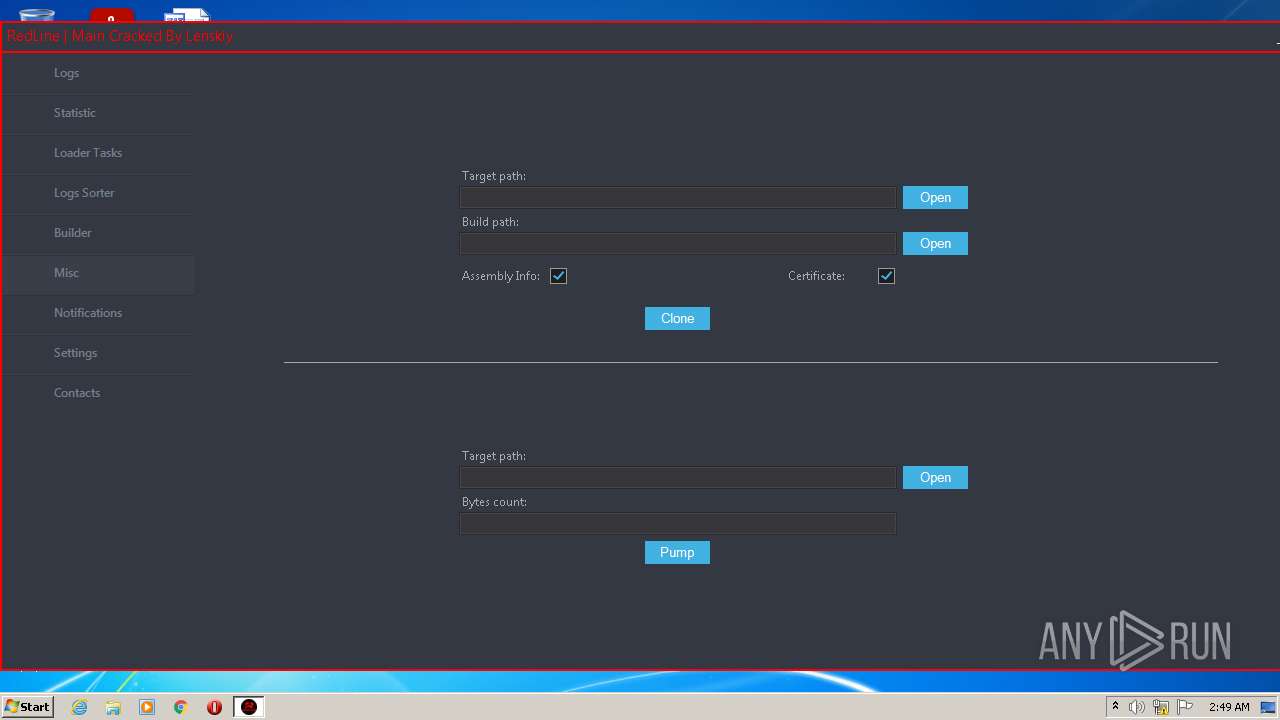
| 3724 | "C:\Users\admin\Desktop\Redline Stealer\Libraries\builder.exe" | C:\Users\admin\Desktop\Redline Stealer\Libraries\builder.exe | — | RedLine.MainPanel-cracked.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: builder Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
2 228
Read events
2 197
Write events
31
Delete events
0
Modification events
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Redline Stealer.rar | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
14
Suspicious files
5
Text files
7
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3588.21353\Redline Stealer\Libraries\builder.exe | executable | |
MD5:DE6F68CDF350FCE9BE13803D84BE98C4 | SHA256:51BBC69942823B84C2A1F0EFDB9D63FB04612B223E86AF8A83B4B307DD15CD24 | |||
| 3588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3588.21353\Redline Stealer\Libraries\Mono.Cecil.dll | executable | |
MD5:7546ACEBC5A5213DEE2A5ED18D7EBC6C | SHA256:7744C9C84C28033BC3606F4DFCE2ADCD6F632E2BE7827893C3E2257100F1CF9E | |||
| 3588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3588.21353\Redline Stealer\Libraries\GuiLib.dll | executable | |
MD5:EAF9C55793CD26F133708714ED3A5397 | SHA256:87CFC70BEC2D2A37BCD5D46F9E6F0051F82E015FF96E8F2BC2D81B85F2632F15 | |||
| 3588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3588.21353\Redline Stealer\Libraries\Bunifu_UI_v1.52.dll | executable | |
MD5:5ECA94D909F1BA4C5F3E35AC65A49076 | SHA256:DE0E530D46C803D85B8AEB6D18816F1B09CB3DAFEFB5E19FDFA15C9F41E0F474 | |||
| 3588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3588.21353\Redline Stealer\Libraries\MetroSet UI.dll | odttf | |
MD5:F13DC3CFFEF729D26C4DA102674561CF | SHA256:D490C04E6E89462FD46099D3454985F319F57032176C67403B3B92C86CA58BCB | |||
| 3588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3588.21353\Redline Stealer\Libraries\builder.pdb | pdb | |
MD5:418DC008EF956465E179EC29D3C3C245 | SHA256:8C7E21B37540211D56C5FDBB7E731655A96945AA83F2988E33D5ADB8AA7C8DF1 | |||
| 3588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3588.21353\Redline Stealer\Libraries\Newtonsoft.Json.dll | executable | |
MD5:6815034209687816D8CF401877EC8133 | SHA256:7F912B28A07C226E0BE3ACFB2F57F050538ABA0100FA1F0BF2C39F1A1F1DA814 | |||
| 3588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3588.21353\Redline Stealer\Libraries\System.Drawing.Pen.dll | executable | |
MD5:1D4E91345A76C90E0849C9389E66FE8C | SHA256:1D820D1C1E9D661603CD32177FB128C9A6844FE2492B6FBB3120BD37553663B0 | |||
| 3588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3588.21353\Redline Stealer\Libraries\README.md | text | |
MD5:8CF8463B34CAA8AC871A52D5DD7AD1EF | SHA256:EB4BD64F7014F7D42E9D358035802242741B974E8DFCD37C59F9C21CE29D781E | |||
| 3588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3588.21353\Redline Stealer\Libraries\Mono.Cecil.pdb | binary | |
MD5:C0A69F1B0C50D4F133CD0B278AC2A531 | SHA256:A4F79C99D8923BD6C30EFAFA39363C18BABE95F6609BBAD242BCA44342CCC7BB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report