| File name: | 2025-06-21_cfa2253cf9e3a2e9a9ae6d4a84aef344_amadey_elex_smoke-loader_stop |
| Full analysis: | https://app.any.run/tasks/a61ba9fb-6dc3-48b0-8adb-3833033fdc34 |
| Verdict: | Malicious activity |
| Threats: | BlackMoon also known as KrBanker is a trojan aimed at stealing payment credentials. It specializes in man-in-the-browser (MitB) attacks, web injection, and credential theft to compromise users' online banking accounts. It was first noticed in early 2014 attacking banks in South Korea and has impressively evolved since by adding a number of new infiltration techniques and information stealing methods. |
| Analysis date: | June 21, 2025, 21:07:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | CFA2253CF9E3A2E9A9AE6D4A84AEF344 |
| SHA1: | D197741EE73603BE51E795E9C820654AF98B7D16 |
| SHA256: | 414C8B873000C09E3B11EEC5A3D219F6A0CC45A55F8C2C9FE77766590DA58B76 |
| SSDEEP: | 98304:hcusHHRqyk4ER1fRVSYSn5MhKM3zjl04I2D/iC4/XO5mL2bwzc5ZdZu0cH208KVG:bca1kBgBs+qW |
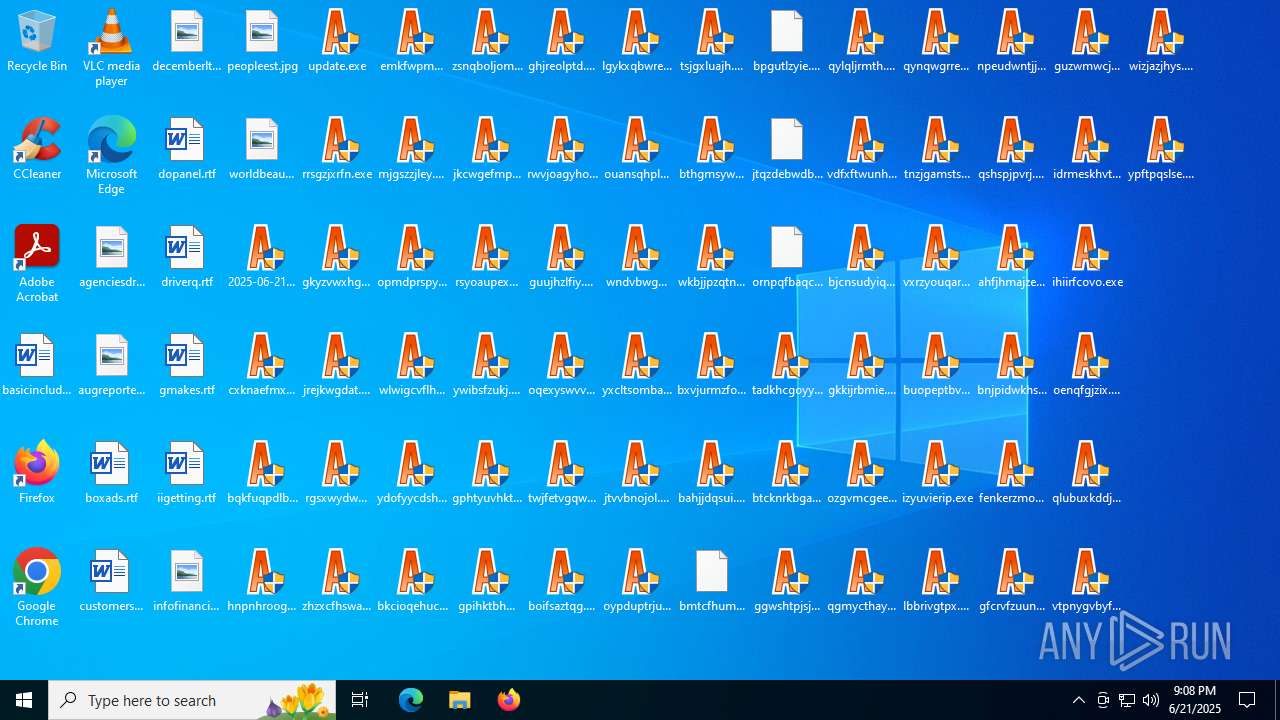
MALICIOUS
BLACKMOON has been detected (YARA)
- tadkhcgoyy.exe (PID: 4680)
- bnjpidwkhs.exe (PID: 3652)
- guzwmwcjol.exe (PID: 4680)
- qlzfzmbhqw.exe (PID: 4708)
- cxrtbyvmec.exe (PID: 6344)
- wyigahjzua.exe (PID: 6776)
- hkpozwzyeq.exe (PID: 5496)
- icmzuytkwc.exe (PID: 4832)
- didhiexbrx.exe (PID: 4664)
- yfnepxjyep.exe (PID: 3048)
- ddkmdqjkap.exe (PID: 1352)
- szdafouumb.exe (PID: 316)
- mywtnfquvh.exe (PID: 3740)
- sqsrnvnour.exe (PID: 6840)
- ubunlldvki.exe (PID: 7164)
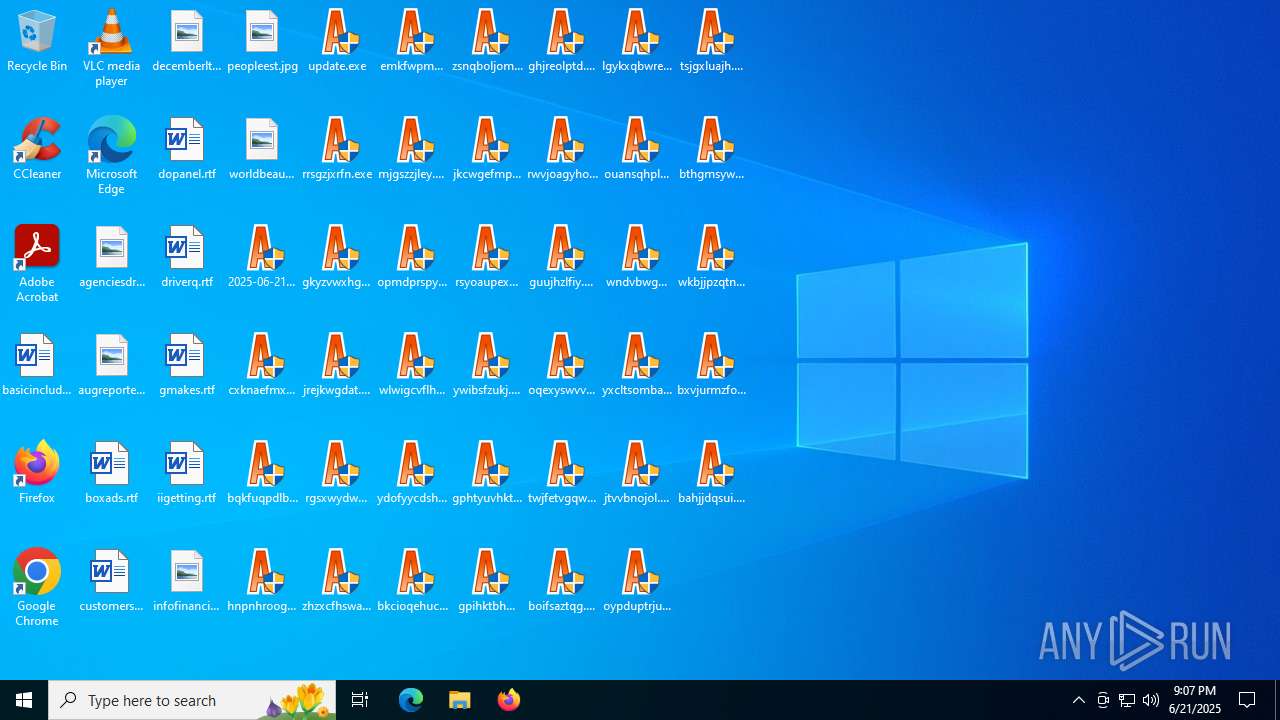
SUSPICIOUS
Starts itself from another location
- 2025-06-21_cfa2253cf9e3a2e9a9ae6d4a84aef344_amadey_elex_smoke-loader_stop.exe (PID: 4968)
- cxknaefmxp.exe (PID: 2808)
- bqkfuqpdlb.exe (PID: 5008)
- hnpnhroogk.exe (PID: 5400)
- rrsgzjxrfn.exe (PID: 4760)
- jrejkwgdat.exe (PID: 1352)
- gkyzvwxhgh.exe (PID: 2220)
- rgsxwydwwq.exe (PID: 3884)
- zhzxcfhswa.exe (PID: 1720)
- emkfwpmsqb.exe (PID: 5168)
- mjgszzjley.exe (PID: 3196)
- opmdprspyk.exe (PID: 2792)
- wlwigcvflh.exe (PID: 6940)
- ydofyycdsh.exe (PID: 7092)
- bkcioqehuc.exe (PID: 5808)
- zsnqboljom.exe (PID: 5372)
- jkcwgefmpk.exe (PID: 5904)
- rsyoaupexm.exe (PID: 4680)
- ywibsfzukj.exe (PID: 5900)
- gphtyuvhkt.exe (PID: 4768)
- gpihktbhmr.exe (PID: 5424)
- ghjreolptd.exe (PID: 5476)
- rwvjoagyho.exe (PID: 3092)
- guujhzlfiy.exe (PID: 3788)
- oqexyswvvv.exe (PID: 1204)
- twjfetvgqw.exe (PID: 5556)
- boifsaztqg.exe (PID: 888)
- ouansqhplq.exe (PID: 6896)
- lgykxqbwre.exe (PID: 2072)
- wndvbwgnua.exe (PID: 4172)
- yxcltsomba.exe (PID: 6700)
- jtvvbnojol.exe (PID: 1232)
- oypduptrju.exe (PID: 6348)
- tsjgxluajh.exe (PID: 1752)
- wkbjjpzqtn.exe (PID: 3652)
- bthgmsywjr.exe (PID: 3876)
- bxvjurmzfo.exe (PID: 2276)
- bahjjdqsui.exe (PID: 4648)
- bmtcfhumbt.exe (PID: 4808)
- bpgutlzyie.exe (PID: 6840)
- jtqzdebwdb.exe (PID: 1964)
- ornpqfbaqc.exe (PID: 1216)
- tadkhcgoyy.exe (PID: 4680)
- btcknrkbga.exe (PID: 5008)
- ggwshtpjsj.exe (PID: 3780)
- qylqljrmth.exe (PID: 1496)
- vdfxftwunh.exe (PID: 4880)
- bjcnsudyiq.exe (PID: 4836)
- gkkijrbmie.exe (PID: 4512)
- qgmycthayv.exe (PID: 6408)
- ozgvmcgeeb.exe (PID: 6876)
- qynqwgrreh.exe (PID: 5712)
- tnzjgamsts.exe (PID: 4156)
- vxrzyouqar.exe (PID: 4692)
- buopeptbva.exe (PID: 6216)
- izyuvierip.exe (PID: 4804)
- lbbrivgtpx.exe (PID: 6940)
- npeudwntjj.exe (PID: 1752)
- qshspjpvrj.exe (PID: 5496)
- vtpnygvbyf.exe (PID: 6936)
- bnjpidwkhs.exe (PID: 3652)
- fenkerzmoo.exe (PID: 2276)
- ihiirfcovo.exe (PID: 4648)
- qlubuxkddj.exe (PID: 4060)
- oenqfgjzix.exe (PID: 3836)
- wizjazjhys.exe (PID: 3736)
- ahfjhmajze.exe (PID: 5476)
- ypftpqslse.exe (PID: 1180)
- gfcrvfzuun.exe (PID: 472)
- guzwmwcjol.exe (PID: 4680)
- idrmeskhvt.exe (PID: 2188)
- dzsqvzsext.exe (PID: 3672)
- fyftrfyvsx.exe (PID: 6540)
- ielyojxmjc.exe (PID: 1156)
- linohldjzl.exe (PID: 1700)
- smzgkwmrhg.exe (PID: 6160)
- kpdtythytj.exe (PID: 4916)
- dlergcrijd.exe (PID: 2120)
- vwqecsmpog.exe (PID: 2664)
- iuumxhxojz.exe (PID: 6380)
- ktbhgmiisx.exe (PID: 1740)
- inveruhexk.exe (PID: 4692)
- qnvkrjiras.exe (PID: 1800)
- yvsqpypbub.exe (PID: 4688)
- vpdfhgoxag.exe (PID: 3740)
- cilpihuboc.exe (PID: 6292)
- pksknuedwz.exe (PID: 5372)
- igifvibnjk.exe (PID: 5900)
- vemnqqemfv.exe (PID: 3924)
- argbuagltc.exe (PID: 2976)
- afuigwkzej.exe (PID: 420)
- ayegmqrinb.exe (PID: 3960)
- kfjrqpxzqx.exe (PID: 5124)
- febwzjrlib.exe (PID: 3908)
- qgsmgucfpl.exe (PID: 7124)
- scdunupxle.exe (PID: 7076)
- qseevyhzee.exe (PID: 5424)
- snqmbgtrsp.exe (PID: 2716)
- xlncpzsvny.exe (PID: 3400)
- fmmcvowqoa.exe (PID: 5460)
- kqfkpqbyij.exe (PID: 5020)
- psmfmclaqg.exe (PID: 3588)
- qlzfzmbhqw.exe (PID: 4708)
- szbibtmvkb.exe (PID: 2072)
- admbemudao.exe (PID: 5284)
- xxyypvlhfc.exe (PID: 6512)
- nftwbyeeiu.exe (PID: 4860)
- fjjqsntonx.exe (PID: 5348)
- vgswqnaziw.exe (PID: 6256)
- xfhrzstmqc.exe (PID: 5244)
- ckcjzylpdt.exe (PID: 2320)
- czbucolvry.exe (PID: 728)
- cozzbxwjtw.exe (PID: 6344)
- ksbekqzhfl.exe (PID: 2696)
- xjfufycgbe.exe (PID: 2528)
- myppahidag.exe (PID: 4476)
- klmqkkmhjb.exe (PID: 6428)
- csnpvdimis.exe (PID: 3644)
- spwvtvpxey.exe (PID: 1480)
- vszsgirzly.exe (PID: 3976)
- xcrqyezxsy.exe (PID: 5952)
- cwkljbzgtt.exe (PID: 6612)
- ngbjhmlsid.exe (PID: 5600)
- hjetcleonu.exe (PID: 2880)
- pnplxdmvcp.exe (PID: 6148)
- xypegxaarl.exe (PID: 1700)
- uoxgnbsbcl.exe (PID: 3760)
- chfzwcynrh.exe (PID: 1948)
- fkawjqbpyg.exe (PID: 6160)
- ifduvddigo.exe (PID: 6348)
- nolpeijwob.exe (PID: 3108)
- cespfpwdpm.exe (PID: 2380)
- hnbkvnujwi.exe (PID: 436)
- upqfshekef.exe (PID: 5716)
- miunykusxv.exe (PID: 4808)
- cbsftfcbgp.exe (PID: 620)
- elsdlbkzmp.exe (PID: 188)
- epfgcaykim.exe (PID: 2808)
- honbyombuo.exe (PID: 4196)
- esrgqevepf.exe (PID: 6776)
- cxrtbyvmec.exe (PID: 6344)
- fefeqpeiyp.exe (PID: 3780)
- miprhbhflm.exe (PID: 7096)
- zhlzcqkehw.exe (PID: 5552)
- ujoropltmo.exe (PID: 7092)
- fitusoqkok.exe (PID: 3864)
- ppgfouvbjh.exe (PID: 6176)
- miauzdufpu.exe (PID: 1488)
- uqpaeabhrc.exe (PID: 4648)
- uukdnqpsmz.exe (PID: 6304)
- rowaxzowsn.exe (PID: 5008)
- efaaubbltj.exe (PID: 2800)
- zowgynqbmv.exe (PID: 2764)
- muooxeyepg.exe (PID: 3588)
- cnuotzynqa.exe (PID: 4692)
- uvnomscspq.exe (PID: 1520)
- hafomjlvka.exe (PID: 1948)
- mbwrcgrbrw.exe (PID: 6160)
- rztzqhqnex.exe (PID: 7000)
- wnlhqyzihq.exe (PID: 504)
- zarzxouanh.exe (PID: 3108)
- jpscnkjjpn.exe (PID: 3092)
- htpzskujnt.exe (PID: 7052)
- reopzugcdc.exe (PID: 3564)
- wclxeofgyl.exe (PID: 3148)
- erhdkluqst.exe (PID: 5992)
- zxoazouhry.exe (PID: 3956)
- mkgdzzqlad.exe (PID: 2276)
- wyigahjzua.exe (PID: 6776)
- ogjfusfetq.exe (PID: 3732)
- cscildbicn.exe (PID: 6344)
- rxlojvqtpu.exe (PID: 7096)
- jxmouomypk.exe (PID: 3780)
- ueryyvrpsh.exe (PID: 7092)
- wororrznzh.exe (PID: 5460)
- edebutwgmd.exe (PID: 3864)
- rfmwzfgiub.exe (PID: 2792)
- mhpomezwza.exe (PID: 1488)
- bpkuyikbct.exe (PID: 5724)
- zgkxgucdvl.exe (PID: 2864)
- hrsppoqhjg.exe (PID: 2604)
- orrpvctcsq.exe (PID: 6012)
- wsqhkjxqsa.exe (PID: 2536)
- btykapdwzo.exe (PID: 4824)
- gkelicmybi.exe (PID: 6212)
- hrdsgichmx.exe (PID: 2072)
- okdlojqtbk.exe (PID: 4692)
- bmkglvsmjq.exe (PID: 5348)
- wpnqgutjoh.exe (PID: 6980)
- hkpozwzyeq.exe (PID: 5496)
- dbvohkiafl.exe (PID: 2696)
- jrwyooacyl.exe (PID: 4764)
- jkdjxqogng.exe (PID: 7052)
- tqibzbjgbj.exe (PID: 5244)
- tjjutotxid.exe (PID: 3924)
- byehfyrqvs.exe (PID: 4224)
- oalcclardx.exe (PID: 2976)
- jzdhmfueec.exe (PID: 6180)
- tjuxsqgxll.exe (PID: 3960)
- zhzfyjfjgu.exe (PID: 6656)
- dusnrtkrav.exe (PID: 4080)
- jvaiiyqxar.exe (PID: 6876)
- rzmaljyepm.exe (PID: 3100)
- oqmlsnqgie.exe (PID: 7164)
- tgslajaijy.exe (PID: 4648)
- bhrlhpdvki.exe (PID: 1896)
- lcswokebxt.exe (PID: 2188)
- raxmcllesu.exe (PID: 3884)
- wnqlvnqmnd.exe (PID: 3000)
- dufrbkxwpl.exe (PID: 5340)
- blnbjopyae.exe (PID: 5904)
- gbtcqcgajy.exe (PID: 756)
- jhzegthwdl.exe (PID: 2604)
- twmxifdwsv.exe (PID: 2128)
- ymkxptuztq.exe (PID: 3588)
- zxusykjcrr.exe (PID: 3888)
- lscfpjcuna.exe (PID: 7128)
- gqukzmwogn.exe (PID: 4688)
- qefsubfuci.exe (PID: 888)
- rmwiagddow.exe (PID: 4196)
- yfdtihipds.exe (PID: 472)
- wdaiojqtys.exe (PID: 4984)
- iitjwzywsl.exe (PID: 1068)
- aiuihkubsb.exe (PID: 3748)
- nkbleeecaz.exe (PID: 7072)
- qjtwonabvl.exe (PID: 6956)
- ycawduexvv.exe (PID: 6808)
- burmvqmvcd.exe (PID: 5124)
- dekpzurlmb.exe (PID: 7124)
- epukheoxkc.exe (PID: 3584)
- lxsahnfxsw.exe (PID: 5172)
- ookkjeawnj.exe (PID: 6684)
- jbpxmnqwzk.exe (PID: 3760)
- yklntmlkpf.exe (PID: 2520)
- fgwakxwacc.exe (PID: 4052)
- vsuxbqdmig.exe (PID: 4916)
- osyaldmzdm.exe (PID: 1440)
- vatbfswjlw.exe (PID: 1984)
- dbsbmzaely.exe (PID: 7048)
- otiyrxchmw.exe (PID: 3876)
- qzwjgpddgr.exe (PID: 1880)
- veirzrilbr.exe (PID: 4708)
- anymqwnrin.exe (PID: 1204)
- icmzuytkwc.exe (PID: 4832)
- dtfcrnunxy.exe (PID: 2168)
- didhiexbrx.exe (PID: 4664)
- igipwfemmf.exe (PID: 5352)
- oqqkmckstt.exe (PID: 2220)
- yagprsevur.exe (PID: 5716)
- dqdkngqybn.exe (PID: 2460)
- lnyxrjvrpk.exe (PID: 6172)
- ilvfekuckl.exe (PID: 504)
- qeuglzyxku.exe (PID: 7052)
- nfmtpckzys.exe (PID: 5244)
- tzyozzciyg.exe (PID: 3924)
- bdjgurlxob.exe (PID: 424)
- dvjennsvvj.exe (PID: 3936)
- vfmypqlmta.exe (PID: 4984)
- dczjewwkwh.exe (PID: 1480)
- ilpeubbqwv.exe (PID: 3976)
- qbcrgehjss.exe (PID: 3640)
- yfnepxjyep.exe (PID: 3048)
- ddkmdqjkap.exe (PID: 1352)
- ipduwavsmy.exe (PID: 480)
- qicudgrnui.exe (PID: 4560)
- xmmauzcdhx.exe (PID: 6260)
- ngkaqvcmqr.exe (PID: 3768)
- fjavyczwdu.exe (PID: 6772)
- gyzgjsicrr.exe (PID: 7164)
- vkunzgncco.exe (PID: 1688)
- sergjiqylj.exe (PID: 3628)
- imbiesodkl.exe (PID: 3668)
- xfzjzowmtx.exe (PID: 5904)
- yniolnudov.exe (PID: 3196)
- imorhuzuqa.exe (PID: 4692)
- ndsmdakxxo.exe (PID: 2128)
- dscwexhlie.exe (PID: 2296)
- qckwnroesa.exe (PID: 4684)
- yvjwtykssk.exe (PID: 1164)
- nhhcfgeznr.exe (PID: 3632)
- fztkljvhfh.exe (PID: 7080)
- fhqpqgcrhq.exe (PID: 4216)
- nlauarehuf.exe (PID: 1328)
- xvqkhcqbjw.exe (PID: 1800)
- suipqwkvca.exe (PID: 3736)
- kxyfeoacru.exe (PID: 4444)
- flefkentxl.exe (PID: 4224)
- kjkgssxoyf.exe (PID: 2976)
- vtadxiyrzd.exe (PID: 3960)
- kbudgmmwhp.exe (PID: 6620)
- zgtlqslzue.exe (PID: 5252)
- scujybnjkx.exe (PID: 1056)
- snwehtkviz.exe (PID: 6876)
- fimryrwffq.exe (PID: 5744)
- zkpbsqxbjh.exe (PID: 2808)
- vxzeqjxttp.exe (PID: 3504)
- ahpzgodzal.exe (PID: 856)
- pdncnmxkst.exe (PID: 6776)
- crhpzklxhk.exe (PID: 3972)
- kguckmiqdh.exe (PID: 1440)
- kydvfzshjt.exe (PID: 6540)
- qtpqpwsqsg.exe (PID: 5724)
- szdafouumb.exe (PID: 316)
- vjvqxkbstb.exe (PID: 2520)
- ckuqeyfgtk.exe (PID: 4708)
- kctqsfjbcm.exe (PID: 3888)
- ppvdxpubqt.exe (PID: 3880)
- mywtnfquvh.exe (PID: 3740)
- swcoegvxlo.exe (PID: 3000)
- swcggbfnra.exe (PID: 1488)
- xuhomuezma.exe (PID: 5716)
- xyscdnppzx.exe (PID: 2864)
- fnfphpmimu.exe (PID: 7080)
- kdlppdvkwg.exe (PID: 7052)
- hxxezmugbu.exe (PID: 4796)
- ngonbrxdeo.exe (PID: 5244)
- ulystkabql.exe (PID: 1752)
- zbwsaxrvsx.exe (PID: 6676)
- ezbiozqhng.exe (PID: 6520)
- aivigdhflm.exe (PID: 1700)
- mdlnxktxav.exe (PID: 7124)
- aqeqpnxbia.exe (PID: 6408)
- fzmlftdhqo.exe (PID: 5416)
- upovgirnbf.exe (PID: 5168)
- mhadzimzpy.exe (PID: 4844)
- pkdbmvhaxy.exe (PID: 6680)
- pkeoydmsae.exe (PID: 1208)
- sqsrnvnour.exe (PID: 6840)
- cmtkvpotic.exe (PID: 7104)
- jiehgnjsjk.exe (PID: 2764)
- ezwmqqdmbo.exe (PID: 6940)
- ubunlldvki.exe (PID: 7164)
- cxescwokxx.exe (PID: 5424)
- nlikeijtli.exe (PID: 2072)
- rcffawuwse.exe (PID: 3944)
- xwzadlvfss.exe (PID: 5988)
- cueqrmuqna.exe (PID: 4760)
- kygvifwgax.exe (PID: 316)
- rgcbgueqcg.exe (PID: 3092)
- miftabeehx.exe (PID: 2348)
- wxhbcxzfmc.exe (PID: 2064)
- cnqlkbrhxc.exe (PID: 4156)
- zgbbvjhddi.exe (PID: 4832)
- emvogzwyaz.exe (PID: 2168)
- jzowzjagua.exe (PID: 5924)
- oljjeslgjh.exe (PID: 2580)
- jomcqrmvny.exe (PID: 4544)
- plsxqaiydf.exe (PID: 3780)
- uvasgxoelb.exe (PID: 536)
- cnzsnmszld.exe (PID: 4224)
- ccxxmuvnnj.exe (PID: 4796)
- pbtfgcgmiu.exe (PID: 5244)
- jhzdvfgday.exe (PID: 3112)
- wyedrittbc.exe (PID: 1700)
- wfdtpnjcvr.exe (PID: 1752)
- hxrongykez.exe (PID: 1216)
- zesozauxvp.exe (PID: 6892)
- mjmbsqiktg.exe (PID: 7028)
- mrljydytem.exe (PID: 2144)
- mvyuhcnear.exe (PID: 3640)
- mkwzykqsbq.exe (PID: 6356)
- tduzmzuoca.exe (PID: 1096)
- zmdudwatjo.exe (PID: 4052)
- hbqhhhxmxk.exe (PID: 1080)
- jlqxzdflek.exe (PID: 436)
- ojnnmwewzt.exe (PID: 3476)
- rpbpcwnstf.exe (PID: 6392)
- zqaqicjnup.exe (PID: 2980)
- hulimvrvjl.exe (PID: 4880)
- bedgerztqk.exe (PID: 2792)
- jfcgkydoqu.exe (PID: 5904)
- orvgeiipkv.exe (PID: 1132)
- basnbyrmbp.exe (PID: 7040)
- ttfognlunp.exe (PID: 4688)
- btmoutphnz.exe (PID: 2836)
- ggxwfdcqha.exe (PID: 6360)
- eadcbndltc.exe (PID: 5716)
- bblrreimxh.exe (PID: 6368)
- ovtjrgzjvx.exe (PID: 236)
- txbeilfwcs.exe (PID: 2604)
- bqkcumqsmm.exe (PID: 7116)
- dicsmiyrsm.exe (PID: 424)
- ovigsmmjso.exe (PID: 6004)
Application launched itself
- hnpnhroogk.exe (PID: 5400)
- rrsgzjxrfn.exe (PID: 4760)
- gkyzvwxhgh.exe (PID: 2220)
- jrejkwgdat.exe (PID: 1352)
- rgsxwydwwq.exe (PID: 3884)
- zhzxcfhswa.exe (PID: 1720)
- emkfwpmsqb.exe (PID: 5168)
- mjgszzjley.exe (PID: 3196)
- opmdprspyk.exe (PID: 2792)
- wlwigcvflh.exe (PID: 6940)
- ydofyycdsh.exe (PID: 7092)
- zsnqboljom.exe (PID: 5372)
- rsyoaupexm.exe (PID: 4680)
- jkcwgefmpk.exe (PID: 5904)
- ywibsfzukj.exe (PID: 5900)
- gphtyuvhkt.exe (PID: 4768)
- gpihktbhmr.exe (PID: 5424)
- ghjreolptd.exe (PID: 5476)
- rwvjoagyho.exe (PID: 3092)
- guujhzlfiy.exe (PID: 3788)
- bkcioqehuc.exe (PID: 5808)
- oqexyswvvv.exe (PID: 1204)
- lgykxqbwre.exe (PID: 2072)
- boifsaztqg.exe (PID: 888)
- ouansqhplq.exe (PID: 6896)
- wndvbwgnua.exe (PID: 4172)
- yxcltsomba.exe (PID: 6700)
- jtvvbnojol.exe (PID: 1232)
- oypduptrju.exe (PID: 6348)
- tsjgxluajh.exe (PID: 1752)
- bthgmsywjr.exe (PID: 3876)
- wkbjjpzqtn.exe (PID: 3652)
- bxvjurmzfo.exe (PID: 2276)
- twjfetvgqw.exe (PID: 5556)
- bmtcfhumbt.exe (PID: 4808)
- bahjjdqsui.exe (PID: 4648)
- bpgutlzyie.exe (PID: 6840)
- jtqzdebwdb.exe (PID: 1964)
- ornpqfbaqc.exe (PID: 1216)
- tadkhcgoyy.exe (PID: 4680)
- btcknrkbga.exe (PID: 5008)
- ggwshtpjsj.exe (PID: 3780)
- qylqljrmth.exe (PID: 1496)
- vdfxftwunh.exe (PID: 4880)
- bjcnsudyiq.exe (PID: 4836)
- gkkijrbmie.exe (PID: 4512)
- ozgvmcgeeb.exe (PID: 6876)
- qgmycthayv.exe (PID: 6408)
- qynqwgrreh.exe (PID: 5712)
- tnzjgamsts.exe (PID: 4156)
- vxrzyouqar.exe (PID: 4692)
- buopeptbva.exe (PID: 6216)
- izyuvierip.exe (PID: 4804)
- lbbrivgtpx.exe (PID: 6940)
- npeudwntjj.exe (PID: 1752)
- qshspjpvrj.exe (PID: 5496)
- vtpnygvbyf.exe (PID: 6936)
- bnjpidwkhs.exe (PID: 3652)
- fenkerzmoo.exe (PID: 2276)
- ihiirfcovo.exe (PID: 4648)
- oenqfgjzix.exe (PID: 3836)
- qlubuxkddj.exe (PID: 4060)
- ypftpqslse.exe (PID: 1180)
- wizjazjhys.exe (PID: 3736)
- gfcrvfzuun.exe (PID: 472)
- ahfjhmajze.exe (PID: 5476)
- guzwmwcjol.exe (PID: 4680)
- idrmeskhvt.exe (PID: 2188)
- dzsqvzsext.exe (PID: 3672)
- ielyojxmjc.exe (PID: 1156)
- fyftrfyvsx.exe (PID: 6540)
- linohldjzl.exe (PID: 1700)
- kpdtythytj.exe (PID: 4916)
- smzgkwmrhg.exe (PID: 6160)
- vwqecsmpog.exe (PID: 2664)
- dlergcrijd.exe (PID: 2120)
- iuumxhxojz.exe (PID: 6380)
- inveruhexk.exe (PID: 4692)
- ktbhgmiisx.exe (PID: 1740)
- vpdfhgoxag.exe (PID: 3740)
- qnvkrjiras.exe (PID: 1800)
- yvsqpypbub.exe (PID: 4688)
- igifvibnjk.exe (PID: 5900)
- cilpihuboc.exe (PID: 6292)
- vemnqqemfv.exe (PID: 3924)
- pksknuedwz.exe (PID: 5372)
- afuigwkzej.exe (PID: 420)
- argbuagltc.exe (PID: 2976)
- ayegmqrinb.exe (PID: 3960)
- febwzjrlib.exe (PID: 3908)
- kfjrqpxzqx.exe (PID: 5124)
- qseevyhzee.exe (PID: 5424)
- qgsmgucfpl.exe (PID: 7124)
- scdunupxle.exe (PID: 7076)
- xlncpzsvny.exe (PID: 3400)
- snqmbgtrsp.exe (PID: 2716)
- fmmcvowqoa.exe (PID: 5460)
- kqfkpqbyij.exe (PID: 5020)
- qlzfzmbhqw.exe (PID: 4708)
- szbibtmvkb.exe (PID: 2072)
- psmfmclaqg.exe (PID: 3588)
- xxyypvlhfc.exe (PID: 6512)
- admbemudao.exe (PID: 5284)
- fjjqsntonx.exe (PID: 5348)
- nftwbyeeiu.exe (PID: 4860)
- vgswqnaziw.exe (PID: 6256)
- ckcjzylpdt.exe (PID: 2320)
- xfhrzstmqc.exe (PID: 5244)
- czbucolvry.exe (PID: 728)
- cozzbxwjtw.exe (PID: 6344)
- myppahidag.exe (PID: 4476)
- ksbekqzhfl.exe (PID: 2696)
- csnpvdimis.exe (PID: 3644)
- xjfufycgbe.exe (PID: 2528)
- klmqkkmhjb.exe (PID: 6428)
- vszsgirzly.exe (PID: 3976)
- spwvtvpxey.exe (PID: 1480)
- xcrqyezxsy.exe (PID: 5952)
- cwkljbzgtt.exe (PID: 6612)
- hjetcleonu.exe (PID: 2880)
- ngbjhmlsid.exe (PID: 5600)
- pnplxdmvcp.exe (PID: 6148)
- uoxgnbsbcl.exe (PID: 3760)
- xypegxaarl.exe (PID: 1700)
- fkawjqbpyg.exe (PID: 6160)
- chfzwcynrh.exe (PID: 1948)
- ifduvddigo.exe (PID: 6348)
- cespfpwdpm.exe (PID: 2380)
- nolpeijwob.exe (PID: 3108)
- miunykusxv.exe (PID: 4808)
- hnbkvnujwi.exe (PID: 436)
- upqfshekef.exe (PID: 5716)
- elsdlbkzmp.exe (PID: 188)
- cbsftfcbgp.exe (PID: 620)
- honbyombuo.exe (PID: 4196)
- esrgqevepf.exe (PID: 6776)
- epfgcaykim.exe (PID: 2808)
- cxrtbyvmec.exe (PID: 6344)
- miprhbhflm.exe (PID: 7096)
- fefeqpeiyp.exe (PID: 3780)
- ujoropltmo.exe (PID: 7092)
- fitusoqkok.exe (PID: 3864)
- zhlzcqkehw.exe (PID: 5552)
- miauzdufpu.exe (PID: 1488)
- ppgfouvbjh.exe (PID: 6176)
- uqpaeabhrc.exe (PID: 4648)
- rowaxzowsn.exe (PID: 5008)
- uukdnqpsmz.exe (PID: 6304)
- zowgynqbmv.exe (PID: 2764)
- efaaubbltj.exe (PID: 2800)
- uvnomscspq.exe (PID: 1520)
- muooxeyepg.exe (PID: 3588)
- hafomjlvka.exe (PID: 1948)
- cnuotzynqa.exe (PID: 4692)
- mbwrcgrbrw.exe (PID: 6160)
- rztzqhqnex.exe (PID: 7000)
- zarzxouanh.exe (PID: 3108)
- htpzskujnt.exe (PID: 7052)
- wnlhqyzihq.exe (PID: 504)
- jpscnkjjpn.exe (PID: 3092)
- wclxeofgyl.exe (PID: 3148)
- reopzugcdc.exe (PID: 3564)
- zxoazouhry.exe (PID: 3956)
- mkgdzzqlad.exe (PID: 2276)
- erhdkluqst.exe (PID: 5992)
- ogjfusfetq.exe (PID: 3732)
- cscildbicn.exe (PID: 6344)
- wyigahjzua.exe (PID: 6776)
- jxmouomypk.exe (PID: 3780)
- ueryyvrpsh.exe (PID: 7092)
- rxlojvqtpu.exe (PID: 7096)
- wororrznzh.exe (PID: 5460)
- edebutwgmd.exe (PID: 3864)
- mhpomezwza.exe (PID: 1488)
- zgkxgucdvl.exe (PID: 2864)
- rfmwzfgiub.exe (PID: 2792)
- bpkuyikbct.exe (PID: 5724)
- hrsppoqhjg.exe (PID: 2604)
- orrpvctcsq.exe (PID: 6012)
- wsqhkjxqsa.exe (PID: 2536)
- hrdsgichmx.exe (PID: 2072)
- btykapdwzo.exe (PID: 4824)
- gkelicmybi.exe (PID: 6212)
- wpnqgutjoh.exe (PID: 6980)
- okdlojqtbk.exe (PID: 4692)
- hkpozwzyeq.exe (PID: 5496)
- bmkglvsmjq.exe (PID: 5348)
- jrwyooacyl.exe (PID: 4764)
- dbvohkiafl.exe (PID: 2696)
- jkdjxqogng.exe (PID: 7052)
- tqibzbjgbj.exe (PID: 5244)
- byehfyrqvs.exe (PID: 4224)
- tjjutotxid.exe (PID: 3924)
- jzdhmfueec.exe (PID: 6180)
- tjuxsqgxll.exe (PID: 3960)
- oalcclardx.exe (PID: 2976)
- zhzfyjfjgu.exe (PID: 6656)
- dusnrtkrav.exe (PID: 4080)
- jvaiiyqxar.exe (PID: 6876)
- oqmlsnqgie.exe (PID: 7164)
- rzmaljyepm.exe (PID: 3100)
- tgslajaijy.exe (PID: 4648)
- bhrlhpdvki.exe (PID: 1896)
- raxmcllesu.exe (PID: 3884)
- lcswokebxt.exe (PID: 2188)
- blnbjopyae.exe (PID: 5904)
- wnqlvnqmnd.exe (PID: 3000)
- dufrbkxwpl.exe (PID: 5340)
- gbtcqcgajy.exe (PID: 756)
- jhzegthwdl.exe (PID: 2604)
- twmxifdwsv.exe (PID: 2128)
- zxusykjcrr.exe (PID: 3888)
- gqukzmwogn.exe (PID: 4688)
- ymkxptuztq.exe (PID: 3588)
- lscfpjcuna.exe (PID: 7128)
- yfdtihipds.exe (PID: 472)
- rmwiagddow.exe (PID: 4196)
- qefsubfuci.exe (PID: 888)
- aiuihkubsb.exe (PID: 3748)
- wdaiojqtys.exe (PID: 4984)
- iitjwzywsl.exe (PID: 1068)
- nkbleeecaz.exe (PID: 7072)
- qjtwonabvl.exe (PID: 6956)
- ycawduexvv.exe (PID: 6808)
- burmvqmvcd.exe (PID: 5124)
- epukheoxkc.exe (PID: 3584)
- jbpxmnqwzk.exe (PID: 3760)
- dekpzurlmb.exe (PID: 7124)
- ookkjeawnj.exe (PID: 6684)
- vsuxbqdmig.exe (PID: 4916)
- lxsahnfxsw.exe (PID: 5172)
- yklntmlkpf.exe (PID: 2520)
- fgwakxwacc.exe (PID: 4052)
- osyaldmzdm.exe (PID: 1440)
- vatbfswjlw.exe (PID: 1984)
- dbsbmzaely.exe (PID: 7048)
- otiyrxchmw.exe (PID: 3876)
- qzwjgpddgr.exe (PID: 1880)
- veirzrilbr.exe (PID: 4708)
- anymqwnrin.exe (PID: 1204)
- icmzuytkwc.exe (PID: 4832)
- dtfcrnunxy.exe (PID: 2168)
- didhiexbrx.exe (PID: 4664)
- igipwfemmf.exe (PID: 5352)
- oqqkmckstt.exe (PID: 2220)
- yagprsevur.exe (PID: 5716)
- dqdkngqybn.exe (PID: 2460)
- lnyxrjvrpk.exe (PID: 6172)
- ilvfekuckl.exe (PID: 504)
- qeuglzyxku.exe (PID: 7052)
- nfmtpckzys.exe (PID: 5244)
- tzyozzciyg.exe (PID: 3924)
- vfmypqlmta.exe (PID: 4984)
- bdjgurlxob.exe (PID: 424)
- dvjennsvvj.exe (PID: 3936)
- dczjewwkwh.exe (PID: 1480)
- ilpeubbqwv.exe (PID: 3976)
- qbcrgehjss.exe (PID: 3640)
- yfnepxjyep.exe (PID: 3048)
- ddkmdqjkap.exe (PID: 1352)
- ipduwavsmy.exe (PID: 480)
- qicudgrnui.exe (PID: 4560)
- xmmauzcdhx.exe (PID: 6260)
- fjavyczwdu.exe (PID: 6772)
- ngkaqvcmqr.exe (PID: 3768)
- vkunzgncco.exe (PID: 1688)
- gyzgjsicrr.exe (PID: 7164)
- imbiesodkl.exe (PID: 3668)
- sergjiqylj.exe (PID: 3628)
- xfzjzowmtx.exe (PID: 5904)
- yniolnudov.exe (PID: 3196)
- dscwexhlie.exe (PID: 2296)
- imorhuzuqa.exe (PID: 4692)
- ndsmdakxxo.exe (PID: 2128)
- yvjwtykssk.exe (PID: 1164)
- fztkljvhfh.exe (PID: 7080)
- qckwnroesa.exe (PID: 4684)
- fhqpqgcrhq.exe (PID: 4216)
- nhhcfgeznr.exe (PID: 3632)
- nlauarehuf.exe (PID: 1328)
- suipqwkvca.exe (PID: 3736)
- xvqkhcqbjw.exe (PID: 1800)
- flefkentxl.exe (PID: 4224)
- kxyfeoacru.exe (PID: 4444)
- kjkgssxoyf.exe (PID: 2976)
- vtadxiyrzd.exe (PID: 3960)
- zgtlqslzue.exe (PID: 5252)
- kbudgmmwhp.exe (PID: 6620)
- snwehtkviz.exe (PID: 6876)
- scujybnjkx.exe (PID: 1056)
- zkpbsqxbjh.exe (PID: 2808)
- pdncnmxkst.exe (PID: 6776)
- fimryrwffq.exe (PID: 5744)
- vxzeqjxttp.exe (PID: 3504)
- ahpzgodzal.exe (PID: 856)
- kguckmiqdh.exe (PID: 1440)
- kydvfzshjt.exe (PID: 6540)
- crhpzklxhk.exe (PID: 3972)
- qtpqpwsqsg.exe (PID: 5724)
- szdafouumb.exe (PID: 316)
- vjvqxkbstb.exe (PID: 2520)
- ckuqeyfgtk.exe (PID: 4708)
- kctqsfjbcm.exe (PID: 3888)
- mywtnfquvh.exe (PID: 3740)
- swcoegvxlo.exe (PID: 3000)
- ppvdxpubqt.exe (PID: 3880)
- swcggbfnra.exe (PID: 1488)
- xuhomuezma.exe (PID: 5716)
- fnfphpmimu.exe (PID: 7080)
- hxxezmugbu.exe (PID: 4796)
- xyscdnppzx.exe (PID: 2864)
- kdlppdvkwg.exe (PID: 7052)
- ngonbrxdeo.exe (PID: 5244)
- ulystkabql.exe (PID: 1752)
- aivigdhflm.exe (PID: 1700)
- ezbiozqhng.exe (PID: 6520)
- zbwsaxrvsx.exe (PID: 6676)
- upovgirnbf.exe (PID: 5168)
- mdlnxktxav.exe (PID: 7124)
- fzmlftdhqo.exe (PID: 5416)
- aqeqpnxbia.exe (PID: 6408)
- pkdbmvhaxy.exe (PID: 6680)
- mhadzimzpy.exe (PID: 4844)
- sqsrnvnour.exe (PID: 6840)
- cmtkvpotic.exe (PID: 7104)
- pkeoydmsae.exe (PID: 1208)
- ezwmqqdmbo.exe (PID: 6940)
- jiehgnjsjk.exe (PID: 2764)
- ubunlldvki.exe (PID: 7164)
- cxescwokxx.exe (PID: 5424)
- nlikeijtli.exe (PID: 2072)
- rcffawuwse.exe (PID: 3944)
- xwzadlvfss.exe (PID: 5988)
- cueqrmuqna.exe (PID: 4760)
- kygvifwgax.exe (PID: 316)
- miftabeehx.exe (PID: 2348)
- rgcbgueqcg.exe (PID: 3092)
- zgbbvjhddi.exe (PID: 4832)
- cnqlkbrhxc.exe (PID: 4156)
- wxhbcxzfmc.exe (PID: 2064)
- jzowzjagua.exe (PID: 5924)
- jomcqrmvny.exe (PID: 4544)
- emvogzwyaz.exe (PID: 2168)
- oljjeslgjh.exe (PID: 2580)
- plsxqaiydf.exe (PID: 3780)
- uvasgxoelb.exe (PID: 536)
- cnzsnmszld.exe (PID: 4224)
- ccxxmuvnnj.exe (PID: 4796)
- jhzdvfgday.exe (PID: 3112)
- pbtfgcgmiu.exe (PID: 5244)
- wfdtpnjcvr.exe (PID: 1752)
- zesozauxvp.exe (PID: 6892)
- wyedrittbc.exe (PID: 1700)
- mrljydytem.exe (PID: 2144)
- hxrongykez.exe (PID: 1216)
- mvyuhcnear.exe (PID: 3640)
- mjmbsqiktg.exe (PID: 7028)
- mkwzykqsbq.exe (PID: 6356)
- tduzmzuoca.exe (PID: 1096)
- zmdudwatjo.exe (PID: 4052)
- hbqhhhxmxk.exe (PID: 1080)
- ojnnmwewzt.exe (PID: 3476)
- rpbpcwnstf.exe (PID: 6392)
- jlqxzdflek.exe (PID: 436)
- zqaqicjnup.exe (PID: 2980)
- basnbyrmbp.exe (PID: 7040)
- bedgerztqk.exe (PID: 2792)
- jfcgkydoqu.exe (PID: 5904)
- orvgeiipkv.exe (PID: 1132)
- ovigsmmjso.exe (PID: 6004)
- hulimvrvjl.exe (PID: 4880)
- btmoutphnz.exe (PID: 2836)
- ggxwfdcqha.exe (PID: 6360)
- ttfognlunp.exe (PID: 4688)
- ovtjrgzjvx.exe (PID: 236)
Executable content was dropped or overwritten
- hnpnhroogk.exe (PID: 504)
- rrsgzjxrfn.exe (PID: 1180)
- gkyzvwxhgh.exe (PID: 5744)
- jrejkwgdat.exe (PID: 6656)
- rgsxwydwwq.exe (PID: 5628)
- zhzxcfhswa.exe (PID: 2696)
- emkfwpmsqb.exe (PID: 1700)
- 2025-06-21_cfa2253cf9e3a2e9a9ae6d4a84aef344_amadey_elex_smoke-loader_stop.exe (PID: 4968)
- mjgszzjley.exe (PID: 6160)
- opmdprspyk.exe (PID: 5908)
- wlwigcvflh.exe (PID: 3948)
- ydofyycdsh.exe (PID: 6232)
- zsnqboljom.exe (PID: 5348)
- jkcwgefmpk.exe (PID: 2664)
- rsyoaupexm.exe (PID: 3956)
- ywibsfzukj.exe (PID: 2120)
- gphtyuvhkt.exe (PID: 4684)
- gpihktbhmr.exe (PID: 1800)
- ghjreolptd.exe (PID: 6292)
- rwvjoagyho.exe (PID: 1096)
- guujhzlfiy.exe (PID: 1212)
- bkcioqehuc.exe (PID: 2808)
- oqexyswvvv.exe (PID: 1036)
- twjfetvgqw.exe (PID: 4080)
- boifsaztqg.exe (PID: 1068)
- lgykxqbwre.exe (PID: 7072)
- ouansqhplq.exe (PID: 1512)
- wndvbwgnua.exe (PID: 1896)
- yxcltsomba.exe (PID: 1080)
- jtvvbnojol.exe (PID: 6228)
- oypduptrju.exe (PID: 1520)
- tsjgxluajh.exe (PID: 7140)
- wkbjjpzqtn.exe (PID: 3148)
- bthgmsywjr.exe (PID: 4960)
- bxvjurmzfo.exe (PID: 6900)
- bahjjdqsui.exe (PID: 2380)
- bpgutlzyie.exe (PID: 4684)
- bmtcfhumbt.exe (PID: 1328)
- jtqzdebwdb.exe (PID: 6256)
- ornpqfbaqc.exe (PID: 6292)
- tadkhcgoyy.exe (PID: 5244)
- btcknrkbga.exe (PID: 3960)
- ggwshtpjsj.exe (PID: 1036)
- qylqljrmth.exe (PID: 4764)
- vdfxftwunh.exe (PID: 2764)
- gkkijrbmie.exe (PID: 6320)
- bjcnsudyiq.exe (PID: 3092)
- qgmycthayv.exe (PID: 4576)
- ozgvmcgeeb.exe (PID: 1728)
- qynqwgrreh.exe (PID: 1652)
- tnzjgamsts.exe (PID: 2632)
- vxrzyouqar.exe (PID: 4760)
- buopeptbva.exe (PID: 6160)
- izyuvierip.exe (PID: 2520)
- lbbrivgtpx.exe (PID: 3108)
- npeudwntjj.exe (PID: 6732)
- qshspjpvrj.exe (PID: 3844)
- vtpnygvbyf.exe (PID: 4684)
- fenkerzmoo.exe (PID: 6292)
- bnjpidwkhs.exe (PID: 5708)
- oenqfgjzix.exe (PID: 728)
- ihiirfcovo.exe (PID: 5900)
- qlubuxkddj.exe (PID: 2536)
- wizjazjhys.exe (PID: 2696)
- ypftpqslse.exe (PID: 3748)
- ahfjhmajze.exe (PID: 4196)
- gfcrvfzuun.exe (PID: 3092)
- guzwmwcjol.exe (PID: 1944)
- idrmeskhvt.exe (PID: 6504)
- dzsqvzsext.exe (PID: 6492)
- ielyojxmjc.exe (PID: 1564)
- fyftrfyvsx.exe (PID: 6896)
- linohldjzl.exe (PID: 4172)
- smzgkwmrhg.exe (PID: 4708)
- kpdtythytj.exe (PID: 4920)
- dlergcrijd.exe (PID: 1520)
- vwqecsmpog.exe (PID: 6228)
- iuumxhxojz.exe (PID: 6732)
- inveruhexk.exe (PID: 2292)
- ktbhgmiisx.exe (PID: 4960)
- qnvkrjiras.exe (PID: 6652)
- yvsqpypbub.exe (PID: 6140)
- vpdfhgoxag.exe (PID: 7000)
- cilpihuboc.exe (PID: 4544)
- pksknuedwz.exe (PID: 5808)
- igifvibnjk.exe (PID: 5496)
- afuigwkzej.exe (PID: 2708)
- vemnqqemfv.exe (PID: 4984)
- argbuagltc.exe (PID: 7072)
- febwzjrlib.exe (PID: 6684)
- ayegmqrinb.exe (PID: 5552)
- kfjrqpxzqx.exe (PID: 1488)
- qgsmgucfpl.exe (PID: 3100)
- qseevyhzee.exe (PID: 1932)
- scdunupxle.exe (PID: 3048)
- xlncpzsvny.exe (PID: 1688)
- snqmbgtrsp.exe (PID: 4324)
- fmmcvowqoa.exe (PID: 2792)
- qlzfzmbhqw.exe (PID: 4880)
- kqfkpqbyij.exe (PID: 6536)
- psmfmclaqg.exe (PID: 5172)
- xxyypvlhfc.exe (PID: 1352)
- szbibtmvkb.exe (PID: 5528)
- admbemudao.exe (PID: 3884)
- nftwbyeeiu.exe (PID: 5232)
- fjjqsntonx.exe (PID: 2520)
- vgswqnaziw.exe (PID: 2380)
- ckcjzylpdt.exe (PID: 5012)
- xfhrzstmqc.exe (PID: 3888)
- czbucolvry.exe (PID: 4684)
- cozzbxwjtw.exe (PID: 4804)
- ksbekqzhfl.exe (PID: 6180)
- xjfufycgbe.exe (PID: 2552)
- myppahidag.exe (PID: 4216)
- csnpvdimis.exe (PID: 1136)
- klmqkkmhjb.exe (PID: 4764)
- spwvtvpxey.exe (PID: 3936)
- xcrqyezxsy.exe (PID: 3732)
- vszsgirzly.exe (PID: 2276)
- cwkljbzgtt.exe (PID: 5444)
- ngbjhmlsid.exe (PID: 6336)
- hjetcleonu.exe (PID: 6852)
- pnplxdmvcp.exe (PID: 3160)
- xypegxaarl.exe (PID: 7116)
- uoxgnbsbcl.exe (PID: 7048)
- fkawjqbpyg.exe (PID: 1720)
- chfzwcynrh.exe (PID: 1352)
- ifduvddigo.exe (PID: 5168)
- cespfpwdpm.exe (PID: 6732)
- nolpeijwob.exe (PID: 2148)
- hnbkvnujwi.exe (PID: 5556)
- upqfshekef.exe (PID: 1164)
- miunykusxv.exe (PID: 3852)
- cbsftfcbgp.exe (PID: 2468)
- honbyombuo.exe (PID: 4544)
- elsdlbkzmp.exe (PID: 6940)
- epfgcaykim.exe (PID: 4832)
- cxrtbyvmec.exe (PID: 1180)
- esrgqevepf.exe (PID: 3608)
- fefeqpeiyp.exe (PID: 6680)
- ujoropltmo.exe (PID: 2116)
- miprhbhflm.exe (PID: 6756)
- zhlzcqkehw.exe (PID: 3908)
- miauzdufpu.exe (PID: 1480)
- fitusoqkok.exe (PID: 4172)
- ppgfouvbjh.exe (PID: 3976)
- uqpaeabhrc.exe (PID: 5952)
- rowaxzowsn.exe (PID: 6620)
- uukdnqpsmz.exe (PID: 2880)
- efaaubbltj.exe (PID: 1720)
- zowgynqbmv.exe (PID: 2972)
- uvnomscspq.exe (PID: 1132)
- muooxeyepg.exe (PID: 5172)
- cnuotzynqa.exe (PID: 6732)
- mbwrcgrbrw.exe (PID: 2536)
- hafomjlvka.exe (PID: 6768)
- zarzxouanh.exe (PID: 7120)
- rztzqhqnex.exe (PID: 5708)
- wnlhqyzihq.exe (PID: 6292)
- htpzskujnt.exe (PID: 3668)
- jpscnkjjpn.exe (PID: 1208)
- reopzugcdc.exe (PID: 5496)
- zxoazouhry.exe (PID: 188)
- wclxeofgyl.exe (PID: 620)
- erhdkluqst.exe (PID: 724)
- ogjfusfetq.exe (PID: 6936)
- mkgdzzqlad.exe (PID: 5372)
- wyigahjzua.exe (PID: 3640)
- cscildbicn.exe (PID: 6852)
- jxmouomypk.exe (PID: 4864)
- rxlojvqtpu.exe (PID: 3160)
- wororrznzh.exe (PID: 3504)
- ueryyvrpsh.exe (PID: 5952)
- edebutwgmd.exe (PID: 856)
- rfmwzfgiub.exe (PID: 6492)
- mhpomezwza.exe (PID: 5620)
- bpkuyikbct.exe (PID: 4916)
- zgkxgucdvl.exe (PID: 1700)
- hrsppoqhjg.exe (PID: 2664)
- orrpvctcsq.exe (PID: 4708)
- wsqhkjxqsa.exe (PID: 2800)
- btykapdwzo.exe (PID: 1164)
- gkelicmybi.exe (PID: 3288)
- hrdsgichmx.exe (PID: 6140)
- okdlojqtbk.exe (PID: 436)
- bmkglvsmjq.exe (PID: 5480)
- wpnqgutjoh.exe (PID: 4808)
- hkpozwzyeq.exe (PID: 7000)
- jrwyooacyl.exe (PID: 1100)
- dbvohkiafl.exe (PID: 188)
- jkdjxqogng.exe (PID: 1328)
- tqibzbjgbj.exe (PID: 1752)
- tjjutotxid.exe (PID: 3520)
- jzdhmfueec.exe (PID: 6680)
- byehfyrqvs.exe (PID: 5504)
- oalcclardx.exe (PID: 6756)
- zhzfyjfjgu.exe (PID: 3624)
- tjuxsqgxll.exe (PID: 1212)
- dusnrtkrav.exe (PID: 3504)
- jvaiiyqxar.exe (PID: 856)
- oqmlsnqgie.exe (PID: 6704)
- rzmaljyepm.exe (PID: 5620)
- bhrlhpdvki.exe (PID: 4680)
- tgslajaijy.exe (PID: 5628)
- wnqlvnqmnd.exe (PID: 6900)
- blnbjopyae.exe (PID: 5080)
- gbtcqcgajy.exe (PID: 6140)
- zxusykjcrr.exe (PID: 4832)
- ymkxptuztq.exe (PID: 3196)
- vfmypqlmta.exe (PID: 6536)
There is functionality for taking screenshot (YARA)
- tadkhcgoyy.exe (PID: 4680)
- bnjpidwkhs.exe (PID: 3652)
- guzwmwcjol.exe (PID: 4680)
- qlzfzmbhqw.exe (PID: 4708)
- cxrtbyvmec.exe (PID: 6344)
- wyigahjzua.exe (PID: 6776)
- hkpozwzyeq.exe (PID: 5496)
- icmzuytkwc.exe (PID: 4832)
- didhiexbrx.exe (PID: 4664)
- yfnepxjyep.exe (PID: 3048)
- ddkmdqjkap.exe (PID: 1352)
- szdafouumb.exe (PID: 316)
- mywtnfquvh.exe (PID: 3740)
- sqsrnvnour.exe (PID: 6840)
- ubunlldvki.exe (PID: 7164)
INFO
Checks supported languages
- hnpnhroogk.exe (PID: 5400)
- hnpnhroogk.exe (PID: 504)
- 2025-06-21_cfa2253cf9e3a2e9a9ae6d4a84aef344_amadey_elex_smoke-loader_stop.exe (PID: 4968)
- rrsgzjxrfn.exe (PID: 1180)
- gkyzvwxhgh.exe (PID: 2220)
- rrsgzjxrfn.exe (PID: 4760)
- gkyzvwxhgh.exe (PID: 5744)
- jrejkwgdat.exe (PID: 6656)
- bqkfuqpdlb.exe (PID: 5008)
- jrejkwgdat.exe (PID: 1352)
- rgsxwydwwq.exe (PID: 3884)
- rgsxwydwwq.exe (PID: 5628)
- zhzxcfhswa.exe (PID: 1720)
- zhzxcfhswa.exe (PID: 2696)
- emkfwpmsqb.exe (PID: 5168)
- emkfwpmsqb.exe (PID: 1700)
- cxknaefmxp.exe (PID: 2808)
- mjgszzjley.exe (PID: 6160)
- opmdprspyk.exe (PID: 5908)
- wlwigcvflh.exe (PID: 6940)
- wlwigcvflh.exe (PID: 3948)
- ydofyycdsh.exe (PID: 7092)
- ydofyycdsh.exe (PID: 6232)
- bkcioqehuc.exe (PID: 5808)
- bkcioqehuc.exe (PID: 2808)
- zsnqboljom.exe (PID: 5372)
- mjgszzjley.exe (PID: 3196)
- zsnqboljom.exe (PID: 5348)
- jkcwgefmpk.exe (PID: 5904)
- jkcwgefmpk.exe (PID: 2664)
- rsyoaupexm.exe (PID: 3956)
- rsyoaupexm.exe (PID: 4680)
- opmdprspyk.exe (PID: 2792)
- ywibsfzukj.exe (PID: 5900)
- ywibsfzukj.exe (PID: 2120)
- gphtyuvhkt.exe (PID: 4768)
- gphtyuvhkt.exe (PID: 4684)
- gpihktbhmr.exe (PID: 5424)
- gpihktbhmr.exe (PID: 1800)
- ghjreolptd.exe (PID: 6292)
- rwvjoagyho.exe (PID: 1096)
- guujhzlfiy.exe (PID: 1212)
- oqexyswvvv.exe (PID: 1036)
- twjfetvgqw.exe (PID: 4080)
- boifsaztqg.exe (PID: 1068)
- ghjreolptd.exe (PID: 5476)
- lgykxqbwre.exe (PID: 7072)
- rwvjoagyho.exe (PID: 3092)
- ouansqhplq.exe (PID: 6896)
- ouansqhplq.exe (PID: 1512)
- guujhzlfiy.exe (PID: 3788)
- wndvbwgnua.exe (PID: 4172)
- wndvbwgnua.exe (PID: 1896)
- yxcltsomba.exe (PID: 6700)
- yxcltsomba.exe (PID: 1080)
- twjfetvgqw.exe (PID: 5556)
- jtvvbnojol.exe (PID: 1232)
- jtvvbnojol.exe (PID: 6228)
- oqexyswvvv.exe (PID: 1204)
- oypduptrju.exe (PID: 6348)
- boifsaztqg.exe (PID: 888)
- lgykxqbwre.exe (PID: 2072)
- oypduptrju.exe (PID: 1520)
- tsjgxluajh.exe (PID: 1752)
- tsjgxluajh.exe (PID: 7140)
- bthgmsywjr.exe (PID: 3876)
- bthgmsywjr.exe (PID: 4960)
- wkbjjpzqtn.exe (PID: 3652)
- wkbjjpzqtn.exe (PID: 3148)
- bahjjdqsui.exe (PID: 4648)
- bahjjdqsui.exe (PID: 2380)
- bxvjurmzfo.exe (PID: 6900)
- bpgutlzyie.exe (PID: 4684)
- jtqzdebwdb.exe (PID: 6256)
- bmtcfhumbt.exe (PID: 1328)
- bxvjurmzfo.exe (PID: 2276)
- tadkhcgoyy.exe (PID: 5244)
- ornpqfbaqc.exe (PID: 6292)
- bmtcfhumbt.exe (PID: 4808)
- btcknrkbga.exe (PID: 3960)
- ggwshtpjsj.exe (PID: 3780)
- btcknrkbga.exe (PID: 5008)
- bpgutlzyie.exe (PID: 6840)
- qylqljrmth.exe (PID: 4764)
- jtqzdebwdb.exe (PID: 1964)
- ggwshtpjsj.exe (PID: 1036)
- tadkhcgoyy.exe (PID: 4680)
- bjcnsudyiq.exe (PID: 3092)
- bjcnsudyiq.exe (PID: 4836)
- ornpqfbaqc.exe (PID: 1216)
- vdfxftwunh.exe (PID: 2764)
- gkkijrbmie.exe (PID: 6320)
- gkkijrbmie.exe (PID: 4512)
- ozgvmcgeeb.exe (PID: 1728)
- qylqljrmth.exe (PID: 1496)
- qgmycthayv.exe (PID: 4576)
- vdfxftwunh.exe (PID: 4880)
- tnzjgamsts.exe (PID: 4156)
- tnzjgamsts.exe (PID: 2632)
- qynqwgrreh.exe (PID: 1652)
- buopeptbva.exe (PID: 6160)
- ozgvmcgeeb.exe (PID: 6876)
- qgmycthayv.exe (PID: 6408)
- vxrzyouqar.exe (PID: 4760)
- izyuvierip.exe (PID: 2520)
- lbbrivgtpx.exe (PID: 3108)
- qynqwgrreh.exe (PID: 5712)
- npeudwntjj.exe (PID: 6732)
- qshspjpvrj.exe (PID: 5496)
- vxrzyouqar.exe (PID: 4692)
- qshspjpvrj.exe (PID: 3844)
- vtpnygvbyf.exe (PID: 4684)
- bnjpidwkhs.exe (PID: 3652)
- bnjpidwkhs.exe (PID: 5708)
- izyuvierip.exe (PID: 4804)
- vtpnygvbyf.exe (PID: 6936)
- buopeptbva.exe (PID: 6216)
- fenkerzmoo.exe (PID: 2276)
- lbbrivgtpx.exe (PID: 6940)
- fenkerzmoo.exe (PID: 6292)
- ihiirfcovo.exe (PID: 4648)
- oenqfgjzix.exe (PID: 3836)
- oenqfgjzix.exe (PID: 728)
- npeudwntjj.exe (PID: 1752)
- ihiirfcovo.exe (PID: 5900)
- qlubuxkddj.exe (PID: 2536)
- qlubuxkddj.exe (PID: 4060)
- wizjazjhys.exe (PID: 3736)
- ypftpqslse.exe (PID: 1180)
- ypftpqslse.exe (PID: 3748)
- wizjazjhys.exe (PID: 2696)
- ahfjhmajze.exe (PID: 4196)
- gfcrvfzuun.exe (PID: 3092)
- ahfjhmajze.exe (PID: 5476)
- guzwmwcjol.exe (PID: 1944)
- guzwmwcjol.exe (PID: 4680)
- gfcrvfzuun.exe (PID: 472)
- idrmeskhvt.exe (PID: 2188)
- idrmeskhvt.exe (PID: 6504)
- dzsqvzsext.exe (PID: 3672)
- dzsqvzsext.exe (PID: 6492)
- ielyojxmjc.exe (PID: 1156)
- ielyojxmjc.exe (PID: 1564)
- fyftrfyvsx.exe (PID: 6540)
- fyftrfyvsx.exe (PID: 6896)
- linohldjzl.exe (PID: 1700)
- kpdtythytj.exe (PID: 4916)
- linohldjzl.exe (PID: 4172)
- vwqecsmpog.exe (PID: 6228)
- kpdtythytj.exe (PID: 4920)
- smzgkwmrhg.exe (PID: 4708)
- dlergcrijd.exe (PID: 1520)
- inveruhexk.exe (PID: 4692)
- inveruhexk.exe (PID: 2292)
- iuumxhxojz.exe (PID: 6732)
- ktbhgmiisx.exe (PID: 4960)
- vwqecsmpog.exe (PID: 2664)
- qnvkrjiras.exe (PID: 1800)
- ktbhgmiisx.exe (PID: 1740)
- smzgkwmrhg.exe (PID: 6160)
- dlergcrijd.exe (PID: 2120)
- qnvkrjiras.exe (PID: 6652)
- vpdfhgoxag.exe (PID: 3740)
- vpdfhgoxag.exe (PID: 7000)
- yvsqpypbub.exe (PID: 6140)
- cilpihuboc.exe (PID: 6292)
- iuumxhxojz.exe (PID: 6380)
- igifvibnjk.exe (PID: 5900)
- igifvibnjk.exe (PID: 5496)
- cilpihuboc.exe (PID: 4544)
- pksknuedwz.exe (PID: 5372)
- pksknuedwz.exe (PID: 5808)
- afuigwkzej.exe (PID: 420)
- yvsqpypbub.exe (PID: 4688)
- afuigwkzej.exe (PID: 2708)
- vemnqqemfv.exe (PID: 4984)
- argbuagltc.exe (PID: 7072)
- ayegmqrinb.exe (PID: 3960)
- argbuagltc.exe (PID: 2976)
- febwzjrlib.exe (PID: 3908)
- febwzjrlib.exe (PID: 6684)
- ayegmqrinb.exe (PID: 5552)
- kfjrqpxzqx.exe (PID: 1488)
- qgsmgucfpl.exe (PID: 7124)
- vemnqqemfv.exe (PID: 3924)
- kfjrqpxzqx.exe (PID: 5124)
- qseevyhzee.exe (PID: 5424)
- qseevyhzee.exe (PID: 1932)
- qgsmgucfpl.exe (PID: 3100)
- scdunupxle.exe (PID: 3048)
- scdunupxle.exe (PID: 7076)
- xlncpzsvny.exe (PID: 3400)
- snqmbgtrsp.exe (PID: 4324)
- xlncpzsvny.exe (PID: 1688)
- fmmcvowqoa.exe (PID: 2792)
- kqfkpqbyij.exe (PID: 5020)
- kqfkpqbyij.exe (PID: 6536)
- fmmcvowqoa.exe (PID: 5460)
- qlzfzmbhqw.exe (PID: 4708)
- qlzfzmbhqw.exe (PID: 4880)
- szbibtmvkb.exe (PID: 2072)
- psmfmclaqg.exe (PID: 3588)
- psmfmclaqg.exe (PID: 5172)
- snqmbgtrsp.exe (PID: 2716)
- xxyypvlhfc.exe (PID: 6512)
- xxyypvlhfc.exe (PID: 1352)
- szbibtmvkb.exe (PID: 5528)
- admbemudao.exe (PID: 3884)
- admbemudao.exe (PID: 5284)
- nftwbyeeiu.exe (PID: 4860)
- fjjqsntonx.exe (PID: 2520)
- nftwbyeeiu.exe (PID: 5232)
- ckcjzylpdt.exe (PID: 5012)
- vgswqnaziw.exe (PID: 2380)
- xfhrzstmqc.exe (PID: 3888)
- czbucolvry.exe (PID: 728)
- fjjqsntonx.exe (PID: 5348)
- xfhrzstmqc.exe (PID: 5244)
- czbucolvry.exe (PID: 4684)
- cozzbxwjtw.exe (PID: 6344)
- cozzbxwjtw.exe (PID: 4804)
- vgswqnaziw.exe (PID: 6256)
- myppahidag.exe (PID: 4216)
- ckcjzylpdt.exe (PID: 2320)
- ksbekqzhfl.exe (PID: 2696)
- ksbekqzhfl.exe (PID: 6180)
- myppahidag.exe (PID: 4476)
- xjfufycgbe.exe (PID: 2552)
- csnpvdimis.exe (PID: 3644)
- xjfufycgbe.exe (PID: 2528)
- klmqkkmhjb.exe (PID: 6428)
- csnpvdimis.exe (PID: 1136)
- klmqkkmhjb.exe (PID: 4764)
- vszsgirzly.exe (PID: 2276)
- spwvtvpxey.exe (PID: 1480)
- spwvtvpxey.exe (PID: 3936)
- xcrqyezxsy.exe (PID: 5952)
- xcrqyezxsy.exe (PID: 3732)
- cwkljbzgtt.exe (PID: 6612)
- hjetcleonu.exe (PID: 2880)
- hjetcleonu.exe (PID: 6852)
- cwkljbzgtt.exe (PID: 5444)
- ngbjhmlsid.exe (PID: 6336)
- pnplxdmvcp.exe (PID: 6148)
- pnplxdmvcp.exe (PID: 3160)
- ngbjhmlsid.exe (PID: 5600)
- vszsgirzly.exe (PID: 3976)
- uoxgnbsbcl.exe (PID: 7048)
- uoxgnbsbcl.exe (PID: 3760)
- chfzwcynrh.exe (PID: 1948)
- xypegxaarl.exe (PID: 1700)
- xypegxaarl.exe (PID: 7116)
- fkawjqbpyg.exe (PID: 6160)
- chfzwcynrh.exe (PID: 1352)
- fkawjqbpyg.exe (PID: 1720)
- ifduvddigo.exe (PID: 5168)
- nolpeijwob.exe (PID: 3108)
- cespfpwdpm.exe (PID: 2380)
- nolpeijwob.exe (PID: 2148)
- cespfpwdpm.exe (PID: 6732)
- hnbkvnujwi.exe (PID: 5556)
- miunykusxv.exe (PID: 4808)
- miunykusxv.exe (PID: 3852)
- upqfshekef.exe (PID: 1164)
- cbsftfcbgp.exe (PID: 620)
- ifduvddigo.exe (PID: 6348)
- elsdlbkzmp.exe (PID: 188)
- elsdlbkzmp.exe (PID: 6940)
- cbsftfcbgp.exe (PID: 2468)
- hnbkvnujwi.exe (PID: 436)
- honbyombuo.exe (PID: 4196)
- honbyombuo.exe (PID: 4544)
- upqfshekef.exe (PID: 5716)
- esrgqevepf.exe (PID: 6776)
- epfgcaykim.exe (PID: 4832)
- esrgqevepf.exe (PID: 3608)
- cxrtbyvmec.exe (PID: 6344)
- fefeqpeiyp.exe (PID: 6680)
- miprhbhflm.exe (PID: 7096)
- miprhbhflm.exe (PID: 6756)
- ujoropltmo.exe (PID: 2116)
- cxrtbyvmec.exe (PID: 1180)
- epfgcaykim.exe (PID: 2808)
- fitusoqkok.exe (PID: 3864)
- fitusoqkok.exe (PID: 4172)
- zhlzcqkehw.exe (PID: 5552)
- zhlzcqkehw.exe (PID: 3908)
- miauzdufpu.exe (PID: 1488)
- miauzdufpu.exe (PID: 1480)
- fefeqpeiyp.exe (PID: 3780)
- ujoropltmo.exe (PID: 7092)
- ppgfouvbjh.exe (PID: 6176)
- ppgfouvbjh.exe (PID: 3976)
- uqpaeabhrc.exe (PID: 4648)
- rowaxzowsn.exe (PID: 5008)
- rowaxzowsn.exe (PID: 6620)
- uqpaeabhrc.exe (PID: 5952)
- uukdnqpsmz.exe (PID: 2880)
- uukdnqpsmz.exe (PID: 6304)
- zowgynqbmv.exe (PID: 2972)
- efaaubbltj.exe (PID: 1720)
- muooxeyepg.exe (PID: 3588)
- uvnomscspq.exe (PID: 1132)
- muooxeyepg.exe (PID: 5172)
- cnuotzynqa.exe (PID: 6732)
- hafomjlvka.exe (PID: 6768)
- cnuotzynqa.exe (PID: 4692)
- mbwrcgrbrw.exe (PID: 2536)
- efaaubbltj.exe (PID: 2800)
- rztzqhqnex.exe (PID: 7000)
- zowgynqbmv.exe (PID: 2764)
- rztzqhqnex.exe (PID: 5708)
- uvnomscspq.exe (PID: 1520)
- htpzskujnt.exe (PID: 3668)
- wnlhqyzihq.exe (PID: 6292)
- zarzxouanh.exe (PID: 7120)
- jpscnkjjpn.exe (PID: 1208)
- hafomjlvka.exe (PID: 1948)
- mbwrcgrbrw.exe (PID: 6160)
- wclxeofgyl.exe (PID: 3148)
- zarzxouanh.exe (PID: 3108)
- reopzugcdc.exe (PID: 5496)
- zxoazouhry.exe (PID: 3956)
- wnlhqyzihq.exe (PID: 504)
- zxoazouhry.exe (PID: 188)
- wclxeofgyl.exe (PID: 620)
- jpscnkjjpn.exe (PID: 3092)
- erhdkluqst.exe (PID: 5992)
- erhdkluqst.exe (PID: 724)
- htpzskujnt.exe (PID: 7052)
- ogjfusfetq.exe (PID: 6936)
- reopzugcdc.exe (PID: 3564)
- mkgdzzqlad.exe (PID: 5372)
- cscildbicn.exe (PID: 6852)
- cscildbicn.exe (PID: 6344)
- wyigahjzua.exe (PID: 6776)
- wyigahjzua.exe (PID: 3640)
- jxmouomypk.exe (PID: 3780)
- jxmouomypk.exe (PID: 4864)
- rxlojvqtpu.exe (PID: 3160)
- ueryyvrpsh.exe (PID: 7092)
- ueryyvrpsh.exe (PID: 5952)
- rxlojvqtpu.exe (PID: 7096)
- mkgdzzqlad.exe (PID: 2276)
- wororrznzh.exe (PID: 3504)
- edebutwgmd.exe (PID: 3864)
- ogjfusfetq.exe (PID: 3732)
- mhpomezwza.exe (PID: 1488)
- mhpomezwza.exe (PID: 5620)
- edebutwgmd.exe (PID: 856)
- zgkxgucdvl.exe (PID: 1700)
- rfmwzfgiub.exe (PID: 2792)
- rfmwzfgiub.exe (PID: 6492)
- zgkxgucdvl.exe (PID: 2864)
- bpkuyikbct.exe (PID: 4916)
- wororrznzh.exe (PID: 5460)
- orrpvctcsq.exe (PID: 6012)
- orrpvctcsq.exe (PID: 4708)
- hrsppoqhjg.exe (PID: 2604)
- hrsppoqhjg.exe (PID: 2664)
- wsqhkjxqsa.exe (PID: 2800)
- wsqhkjxqsa.exe (PID: 2536)
- hrdsgichmx.exe (PID: 2072)
- hrdsgichmx.exe (PID: 6140)
- btykapdwzo.exe (PID: 4824)
- btykapdwzo.exe (PID: 1164)
- gkelicmybi.exe (PID: 6212)
- gkelicmybi.exe (PID: 3288)
- bpkuyikbct.exe (PID: 5724)
- wpnqgutjoh.exe (PID: 4808)
- okdlojqtbk.exe (PID: 4692)
- okdlojqtbk.exe (PID: 436)
- bmkglvsmjq.exe (PID: 5480)
- hkpozwzyeq.exe (PID: 5496)
- bmkglvsmjq.exe (PID: 5348)
- hkpozwzyeq.exe (PID: 7000)
- jrwyooacyl.exe (PID: 1100)
- dbvohkiafl.exe (PID: 188)
- jkdjxqogng.exe (PID: 7052)
- wpnqgutjoh.exe (PID: 6980)
- jkdjxqogng.exe (PID: 1328)
- dbvohkiafl.exe (PID: 2696)
- tqibzbjgbj.exe (PID: 5244)
- tqibzbjgbj.exe (PID: 1752)
- byehfyrqvs.exe (PID: 4224)
- byehfyrqvs.exe (PID: 5504)
- tjjutotxid.exe (PID: 3924)
- tjjutotxid.exe (PID: 3520)
- jzdhmfueec.exe (PID: 6180)
- jrwyooacyl.exe (PID: 4764)
- jzdhmfueec.exe (PID: 6680)
- tjuxsqgxll.exe (PID: 3960)
- tjuxsqgxll.exe (PID: 1212)
- oalcclardx.exe (PID: 2976)
- oalcclardx.exe (PID: 6756)
- zhzfyjfjgu.exe (PID: 6656)
- zhzfyjfjgu.exe (PID: 3624)
- jvaiiyqxar.exe (PID: 856)
- jvaiiyqxar.exe (PID: 6876)
- dusnrtkrav.exe (PID: 4080)
- dusnrtkrav.exe (PID: 3504)
- oqmlsnqgie.exe (PID: 7164)
- oqmlsnqgie.exe (PID: 6704)
- rzmaljyepm.exe (PID: 5620)
- tgslajaijy.exe (PID: 4648)
- rzmaljyepm.exe (PID: 3100)
- bhrlhpdvki.exe (PID: 1896)
- tgslajaijy.exe (PID: 5628)
- bhrlhpdvki.exe (PID: 4680)
- raxmcllesu.exe (PID: 3884)
- raxmcllesu.exe (PID: 6768)
- lcswokebxt.exe (PID: 2188)
- lcswokebxt.exe (PID: 6516)
- blnbjopyae.exe (PID: 5904)
- blnbjopyae.exe (PID: 5080)
- wnqlvnqmnd.exe (PID: 3000)
- wnqlvnqmnd.exe (PID: 6900)
- dufrbkxwpl.exe (PID: 5008)
- gbtcqcgajy.exe (PID: 756)
- dufrbkxwpl.exe (PID: 5340)
- gbtcqcgajy.exe (PID: 6140)
- jhzegthwdl.exe (PID: 2604)
- jhzegthwdl.exe (PID: 4456)
- twmxifdwsv.exe (PID: 2128)
- zxusykjcrr.exe (PID: 4832)
- twmxifdwsv.exe (PID: 436)
- zxusykjcrr.exe (PID: 3888)
- gqukzmwogn.exe (PID: 4688)
- ymkxptuztq.exe (PID: 3588)
- ymkxptuztq.exe (PID: 3196)
- lscfpjcuna.exe (PID: 6420)
- rmwiagddow.exe (PID: 4196)
- gqukzmwogn.exe (PID: 4664)
- lscfpjcuna.exe (PID: 7128)
- qefsubfuci.exe (PID: 888)
- qefsubfuci.exe (PID: 6160)
- yfdtihipds.exe (PID: 472)
- yfdtihipds.exe (PID: 3900)
- rmwiagddow.exe (PID: 1948)
- wdaiojqtys.exe (PID: 4984)
- aiuihkubsb.exe (PID: 3748)
- wdaiojqtys.exe (PID: 5808)
- iitjwzywsl.exe (PID: 1068)
- iitjwzywsl.exe (PID: 4216)
- nkbleeecaz.exe (PID: 7072)
- nkbleeecaz.exe (PID: 6320)
- aiuihkubsb.exe (PID: 5476)
- qjtwonabvl.exe (PID: 6956)
- qjtwonabvl.exe (PID: 6936)
- ycawduexvv.exe (PID: 6808)
- ycawduexvv.exe (PID: 424)
- epukheoxkc.exe (PID: 1480)
- burmvqmvcd.exe (PID: 3936)
- epukheoxkc.exe (PID: 3584)
- burmvqmvcd.exe (PID: 5124)
- jbpxmnqwzk.exe (PID: 3760)
- dekpzurlmb.exe (PID: 7124)
- dekpzurlmb.exe (PID: 3976)
- jbpxmnqwzk.exe (PID: 1472)
- lxsahnfxsw.exe (PID: 3048)
- ookkjeawnj.exe (PID: 6684)
- ookkjeawnj.exe (PID: 1352)
- vsuxbqdmig.exe (PID: 4916)
- vsuxbqdmig.exe (PID: 480)
- yklntmlkpf.exe (PID: 2520)
- yklntmlkpf.exe (PID: 3688)
- fgwakxwacc.exe (PID: 4052)
- osyaldmzdm.exe (PID: 1440)
- fgwakxwacc.exe (PID: 6148)
- osyaldmzdm.exe (PID: 3948)
- lxsahnfxsw.exe (PID: 5172)
- vatbfswjlw.exe (PID: 1984)
- vatbfswjlw.exe (PID: 1096)
- dbsbmzaely.exe (PID: 7048)
- otiyrxchmw.exe (PID: 3876)
- dbsbmzaely.exe (PID: 2632)
- otiyrxchmw.exe (PID: 6304)
- qzwjgpddgr.exe (PID: 1880)
- qzwjgpddgr.exe (PID: 1816)
- veirzrilbr.exe (PID: 4708)
- veirzrilbr.exe (PID: 7056)
- anymqwnrin.exe (PID: 1204)
- anymqwnrin.exe (PID: 6004)
- icmzuytkwc.exe (PID: 4832)
- icmzuytkwc.exe (PID: 3108)
- dtfcrnunxy.exe (PID: 756)
- dtfcrnunxy.exe (PID: 2168)
- didhiexbrx.exe (PID: 5116)
- igipwfemmf.exe (PID: 6368)
- oqqkmckstt.exe (PID: 2220)
- igipwfemmf.exe (PID: 5352)
- oqqkmckstt.exe (PID: 3704)
- yagprsevur.exe (PID: 5716)
- didhiexbrx.exe (PID: 4664)
- yagprsevur.exe (PID: 4860)
- dqdkngqybn.exe (PID: 2460)
- dqdkngqybn.exe (PID: 4804)
- lnyxrjvrpk.exe (PID: 6172)
- lnyxrjvrpk.exe (PID: 5992)
- ilvfekuckl.exe (PID: 504)
- ilvfekuckl.exe (PID: 4544)
- qeuglzyxku.exe (PID: 2580)
- nfmtpckzys.exe (PID: 5244)
- nfmtpckzys.exe (PID: 6348)
- tzyozzciyg.exe (PID: 3924)
- qeuglzyxku.exe (PID: 7052)
- tzyozzciyg.exe (PID: 6936)
- vfmypqlmta.exe (PID: 4984)
- vfmypqlmta.exe (PID: 6536)
- bdjgurlxob.exe (PID: 424)
- bdjgurlxob.exe (PID: 3748)
- dvjennsvvj.exe (PID: 3936)
- dvjennsvvj.exe (PID: 1068)
- dczjewwkwh.exe (PID: 1480)
- dczjewwkwh.exe (PID: 5564)
- ilpeubbqwv.exe (PID: 3976)
- ilpeubbqwv.exe (PID: 5552)
- qbcrgehjss.exe (PID: 3640)
- qbcrgehjss.exe (PID: 1472)
- yfnepxjyep.exe (PID: 3048)
- yfnepxjyep.exe (PID: 4844)
- ddkmdqjkap.exe (PID: 1352)
- ddkmdqjkap.exe (PID: 3852)
- ipduwavsmy.exe (PID: 3112)
- qicudgrnui.exe (PID: 4560)
- qicudgrnui.exe (PID: 4048)
- ipduwavsmy.exe (PID: 480)
- xmmauzcdhx.exe (PID: 6260)
- xmmauzcdhx.exe (PID: 2972)
- fjavyczwdu.exe (PID: 2468)
- fjavyczwdu.exe (PID: 6772)
- ngkaqvcmqr.exe (PID: 6868)
- vkunzgncco.exe (PID: 1688)
- vkunzgncco.exe (PID: 6140)
- ngkaqvcmqr.exe (PID: 3768)
- gyzgjsicrr.exe (PID: 7164)
- gyzgjsicrr.exe (PID: 6192)
- imbiesodkl.exe (PID: 5600)
- imbiesodkl.exe (PID: 3668)
- sergjiqylj.exe (PID: 6492)
- xfzjzowmtx.exe (PID: 5904)
- xfzjzowmtx.exe (PID: 316)
- sergjiqylj.exe (PID: 3628)
- yniolnudov.exe (PID: 3196)
- yniolnudov.exe (PID: 6212)
- dscwexhlie.exe (PID: 2296)
- dscwexhlie.exe (PID: 4676)
- ndsmdakxxo.exe (PID: 2128)
- ndsmdakxxo.exe (PID: 2800)
- qckwnroesa.exe (PID: 4684)
- imorhuzuqa.exe (PID: 4692)
- imorhuzuqa.exe (PID: 2356)
- qckwnroesa.exe (PID: 3740)
- yvjwtykssk.exe (PID: 7068)
- fztkljvhfh.exe (PID: 7080)
- fztkljvhfh.exe (PID: 6532)
- yvjwtykssk.exe (PID: 1164)
- nhhcfgeznr.exe (PID: 188)
- fhqpqgcrhq.exe (PID: 4216)
- nhhcfgeznr.exe (PID: 3632)
- nlauarehuf.exe (PID: 1328)
- nlauarehuf.exe (PID: 4824)
- suipqwkvca.exe (PID: 3736)
- suipqwkvca.exe (PID: 4768)
- fhqpqgcrhq.exe (PID: 4060)
- xvqkhcqbjw.exe (PID: 1800)
- xvqkhcqbjw.exe (PID: 2708)
- kxyfeoacru.exe (PID: 2680)
- kjkgssxoyf.exe (PID: 2976)
- kjkgssxoyf.exe (PID: 6836)
- kxyfeoacru.exe (PID: 4444)
- flefkentxl.exe (PID: 4224)
- flefkentxl.exe (PID: 7128)
- vtadxiyrzd.exe (PID: 3960)
- vtadxiyrzd.exe (PID: 5644)
- zgtlqslzue.exe (PID: 5252)
- zgtlqslzue.exe (PID: 3576)
- kbudgmmwhp.exe (PID: 6620)
- kbudgmmwhp.exe (PID: 5496)
- snwehtkviz.exe (PID: 6876)
- zkpbsqxbjh.exe (PID: 2808)
- scujybnjkx.exe (PID: 2144)
- snwehtkviz.exe (PID: 3716)
- scujybnjkx.exe (PID: 1056)
- fimryrwffq.exe (PID: 5744)
- fimryrwffq.exe (PID: 5628)
- pdncnmxkst.exe (PID: 4080)
- pdncnmxkst.exe (PID: 6776)
- zkpbsqxbjh.exe (PID: 5952)
- vxzeqjxttp.exe (PID: 3504)
- ahpzgodzal.exe (PID: 6512)
- ahpzgodzal.exe (PID: 856)
- vxzeqjxttp.exe (PID: 6892)
- kguckmiqdh.exe (PID: 1440)
- kguckmiqdh.exe (PID: 3100)
- kydvfzshjt.exe (PID: 6540)
- crhpzklxhk.exe (PID: 3972)
- crhpzklxhk.exe (PID: 6192)
- qtpqpwsqsg.exe (PID: 5724)
- qtpqpwsqsg.exe (PID: 3768)
- szdafouumb.exe (PID: 316)
- szdafouumb.exe (PID: 1688)
- kydvfzshjt.exe (PID: 6840)
- vjvqxkbstb.exe (PID: 7164)
- ckuqeyfgtk.exe (PID: 4648)
- ckuqeyfgtk.exe (PID: 4708)
- vjvqxkbstb.exe (PID: 2520)
- kctqsfjbcm.exe (PID: 3888)
- kctqsfjbcm.exe (PID: 5904)
- mywtnfquvh.exe (PID: 3740)
- mywtnfquvh.exe (PID: 4764)
- ppvdxpubqt.exe (PID: 756)
- swcoegvxlo.exe (PID: 3000)
- swcoegvxlo.exe (PID: 4196)
- ppvdxpubqt.exe (PID: 3880)
- swcggbfnra.exe (PID: 1488)
- swcggbfnra.exe (PID: 1356)
- xuhomuezma.exe (PID: 6360)
- xyscdnppzx.exe (PID: 2864)
- xuhomuezma.exe (PID: 5716)
- fnfphpmimu.exe (PID: 7080)
- fnfphpmimu.exe (PID: 2620)
- hxxezmugbu.exe (PID: 4796)
- hxxezmugbu.exe (PID: 7128)
- xyscdnppzx.exe (PID: 620)
- kdlppdvkwg.exe (PID: 7052)
- kdlppdvkwg.exe (PID: 2680)
- ngonbrxdeo.exe (PID: 5244)
- ngonbrxdeo.exe (PID: 6836)
- aivigdhflm.exe (PID: 1700)
- ulystkabql.exe (PID: 5808)
- aivigdhflm.exe (PID: 6936)
- ulystkabql.exe (PID: 1752)
- zbwsaxrvsx.exe (PID: 892)
- ezbiozqhng.exe (PID: 6520)
- ezbiozqhng.exe (PID: 6320)
- zbwsaxrvsx.exe (PID: 6676)
- upovgirnbf.exe (PID: 5168)
- upovgirnbf.exe (PID: 2648)
- mdlnxktxav.exe (PID: 7124)
- mdlnxktxav.exe (PID: 1128)
- fzmlftdhqo.exe (PID: 5416)
- fzmlftdhqo.exe (PID: 1704)
- aqeqpnxbia.exe (PID: 6408)
- aqeqpnxbia.exe (PID: 5504)
- pkdbmvhaxy.exe (PID: 6680)
- pkdbmvhaxy.exe (PID: 5620)
- mhadzimzpy.exe (PID: 4844)
- mhadzimzpy.exe (PID: 6704)
- sqsrnvnour.exe (PID: 6840)
- sqsrnvnour.exe (PID: 5528)
- cmtkvpotic.exe (PID: 7104)
- pkeoydmsae.exe (PID: 1208)
- pkeoydmsae.exe (PID: 6900)
- cmtkvpotic.exe (PID: 6732)
- ezwmqqdmbo.exe (PID: 6940)
- ezwmqqdmbo.exe (PID: 6216)
- jiehgnjsjk.exe (PID: 2764)
- jiehgnjsjk.exe (PID: 3972)
- ubunlldvki.exe (PID: 7164)
- ubunlldvki.exe (PID: 6652)
- cxescwokxx.exe (PID: 5424)
- cxescwokxx.exe (PID: 5080)
- nlikeijtli.exe (PID: 2072)
- nlikeijtli.exe (PID: 1576)
- rcffawuwse.exe (PID: 3944)
- rcffawuwse.exe (PID: 1564)
- xwzadlvfss.exe (PID: 5988)
- xwzadlvfss.exe (PID: 2760)
- cueqrmuqna.exe (PID: 4760)
- cueqrmuqna.exe (PID: 4476)
- kygvifwgax.exe (PID: 316)
- kygvifwgax.exe (PID: 2380)
- miftabeehx.exe (PID: 2348)
- miftabeehx.exe (PID: 6420)
- rgcbgueqcg.exe (PID: 3092)
- rgcbgueqcg.exe (PID: 4060)
- zgbbvjhddi.exe (PID: 4832)
- zgbbvjhddi.exe (PID: 3788)
- cnqlkbrhxc.exe (PID: 4156)
- cnqlkbrhxc.exe (PID: 4684)
- wxhbcxzfmc.exe (PID: 2064)
- wxhbcxzfmc.exe (PID: 6360)
- jzowzjagua.exe (PID: 5924)
- jomcqrmvny.exe (PID: 7128)
- jzowzjagua.exe (PID: 5284)
- jomcqrmvny.exe (PID: 4544)
- emvogzwyaz.exe (PID: 2168)
- emvogzwyaz.exe (PID: 3884)
- plsxqaiydf.exe (PID: 3780)
- oljjeslgjh.exe (PID: 2580)
- oljjeslgjh.exe (PID: 3148)
- uvasgxoelb.exe (PID: 536)
- uvasgxoelb.exe (PID: 6172)
- cnzsnmszld.exe (PID: 4224)
- cnzsnmszld.exe (PID: 6936)
- plsxqaiydf.exe (PID: 2228)
- ccxxmuvnnj.exe (PID: 4796)
- ccxxmuvnnj.exe (PID: 892)
- jhzdvfgday.exe (PID: 6320)
- jhzdvfgday.exe (PID: 3112)
- pbtfgcgmiu.exe (PID: 6236)
- wfdtpnjcvr.exe (PID: 1752)
- pbtfgcgmiu.exe (PID: 5244)
- wyedrittbc.exe (PID: 4680)
- zesozauxvp.exe (PID: 6892)
- zesozauxvp.exe (PID: 6868)
- wfdtpnjcvr.exe (PID: 7140)
- wyedrittbc.exe (PID: 1700)
- hxrongykez.exe (PID: 6140)
- mrljydytem.exe (PID: 2144)
- hxrongykez.exe (PID: 1216)
- mjmbsqiktg.exe (PID: 1136)
- mvyuhcnear.exe (PID: 3640)
- mvyuhcnear.exe (PID: 5628)
- mrljydytem.exe (PID: 7124)
- mjmbsqiktg.exe (PID: 7028)
- mkwzykqsbq.exe (PID: 6356)
- tduzmzuoca.exe (PID: 1096)
- tduzmzuoca.exe (PID: 5460)
- mkwzykqsbq.exe (PID: 360)
- zmdudwatjo.exe (PID: 2876)
- hbqhhhxmxk.exe (PID: 1080)
- hbqhhhxmxk.exe (PID: 4456)
- jlqxzdflek.exe (PID: 436)
- zmdudwatjo.exe (PID: 4052)
- ojnnmwewzt.exe (PID: 3476)
- ojnnmwewzt.exe (PID: 2632)
- rpbpcwnstf.exe (PID: 6392)
- rpbpcwnstf.exe (PID: 5340)
- jlqxzdflek.exe (PID: 2120)
- basnbyrmbp.exe (PID: 7040)
- zqaqicjnup.exe (PID: 3876)
- zqaqicjnup.exe (PID: 2980)
- hulimvrvjl.exe (PID: 5020)
- bedgerztqk.exe (PID: 2792)
- bedgerztqk.exe (PID: 2028)
- basnbyrmbp.exe (PID: 4676)
- hulimvrvjl.exe (PID: 4880)
Reads the computer name
- hnpnhroogk.exe (PID: 504)
- rrsgzjxrfn.exe (PID: 1180)
- gkyzvwxhgh.exe (PID: 5744)
- bqkfuqpdlb.exe (PID: 5008)
- jrejkwgdat.exe (PID: 6656)
- rgsxwydwwq.exe (PID: 5628)
- hnpnhroogk.exe (PID: 5400)
- zhzxcfhswa.exe (PID: 2696)
- emkfwpmsqb.exe (PID: 1700)
- rrsgzjxrfn.exe (PID: 4760)
- cxknaefmxp.exe (PID: 2808)
- 2025-06-21_cfa2253cf9e3a2e9a9ae6d4a84aef344_amadey_elex_smoke-loader_stop.exe (PID: 4968)
- mjgszzjley.exe (PID: 6160)
- gkyzvwxhgh.exe (PID: 2220)
- jrejkwgdat.exe (PID: 1352)
- opmdprspyk.exe (PID: 5908)
- wlwigcvflh.exe (PID: 3948)
- rgsxwydwwq.exe (PID: 3884)
- zhzxcfhswa.exe (PID: 1720)
- ydofyycdsh.exe (PID: 6232)
- emkfwpmsqb.exe (PID: 5168)
- mjgszzjley.exe (PID: 3196)
- zsnqboljom.exe (PID: 5348)
- opmdprspyk.exe (PID: 2792)
- jkcwgefmpk.exe (PID: 2664)
- wlwigcvflh.exe (PID: 6940)
- rsyoaupexm.exe (PID: 3956)
- ywibsfzukj.exe (PID: 2120)
- ydofyycdsh.exe (PID: 7092)
- bkcioqehuc.exe (PID: 5808)
- gphtyuvhkt.exe (PID: 4684)
- zsnqboljom.exe (PID: 5372)
- gpihktbhmr.exe (PID: 1800)
- ghjreolptd.exe (PID: 6292)
- jkcwgefmpk.exe (PID: 5904)
- rsyoaupexm.exe (PID: 4680)
- rwvjoagyho.exe (PID: 1096)
- ywibsfzukj.exe (PID: 5900)
- guujhzlfiy.exe (PID: 1212)
- bkcioqehuc.exe (PID: 2808)
- gphtyuvhkt.exe (PID: 4768)
- oqexyswvvv.exe (PID: 1036)
- gpihktbhmr.exe (PID: 5424)
- twjfetvgqw.exe (PID: 4080)
- boifsaztqg.exe (PID: 1068)
- ghjreolptd.exe (PID: 5476)
- lgykxqbwre.exe (PID: 7072)
- rwvjoagyho.exe (PID: 3092)
- ouansqhplq.exe (PID: 1512)
- guujhzlfiy.exe (PID: 3788)
- wndvbwgnua.exe (PID: 1896)
- twjfetvgqw.exe (PID: 5556)
- oqexyswvvv.exe (PID: 1204)
- yxcltsomba.exe (PID: 1080)
- boifsaztqg.exe (PID: 888)
- lgykxqbwre.exe (PID: 2072)
- oypduptrju.exe (PID: 1520)
- jtvvbnojol.exe (PID: 6228)
- ouansqhplq.exe (PID: 6896)
- wndvbwgnua.exe (PID: 4172)
- bthgmsywjr.exe (PID: 4960)
- tsjgxluajh.exe (PID: 7140)
- yxcltsomba.exe (PID: 6700)
- wkbjjpzqtn.exe (PID: 3148)
- jtvvbnojol.exe (PID: 1232)
- bxvjurmzfo.exe (PID: 6900)
- oypduptrju.exe (PID: 6348)
- bahjjdqsui.exe (PID: 2380)
- tsjgxluajh.exe (PID: 1752)
- bmtcfhumbt.exe (PID: 1328)
- bthgmsywjr.exe (PID: 3876)
- bpgutlzyie.exe (PID: 4684)
- wkbjjpzqtn.exe (PID: 3652)
- jtqzdebwdb.exe (PID: 6256)
- bxvjurmzfo.exe (PID: 2276)
- ornpqfbaqc.exe (PID: 6292)
- btcknrkbga.exe (PID: 3960)
- bmtcfhumbt.exe (PID: 4808)
- tadkhcgoyy.exe (PID: 5244)
- bahjjdqsui.exe (PID: 4648)
- ggwshtpjsj.exe (PID: 1036)
- bpgutlzyie.exe (PID: 6840)
- qylqljrmth.exe (PID: 4764)
- jtqzdebwdb.exe (PID: 1964)
- bjcnsudyiq.exe (PID: 3092)
- tadkhcgoyy.exe (PID: 4680)
- vdfxftwunh.exe (PID: 2764)
- ornpqfbaqc.exe (PID: 1216)
- btcknrkbga.exe (PID: 5008)
- ozgvmcgeeb.exe (PID: 1728)
- gkkijrbmie.exe (PID: 6320)
- ggwshtpjsj.exe (PID: 3780)
- qylqljrmth.exe (PID: 1496)
- vdfxftwunh.exe (PID: 4880)
- qgmycthayv.exe (PID: 4576)
- bjcnsudyiq.exe (PID: 4836)
- tnzjgamsts.exe (PID: 2632)
- gkkijrbmie.exe (PID: 4512)
- qynqwgrreh.exe (PID: 1652)
- vxrzyouqar.exe (PID: 4760)
- ozgvmcgeeb.exe (PID: 6876)
- buopeptbva.exe (PID: 6160)
- izyuvierip.exe (PID: 2520)
- qynqwgrreh.exe (PID: 5712)
- lbbrivgtpx.exe (PID: 3108)
- tnzjgamsts.exe (PID: 4156)
- qgmycthayv.exe (PID: 6408)
- npeudwntjj.exe (PID: 6732)
- vxrzyouqar.exe (PID: 4692)
- qshspjpvrj.exe (PID: 3844)
- vtpnygvbyf.exe (PID: 4684)
- izyuvierip.exe (PID: 4804)
- buopeptbva.exe (PID: 6216)
- fenkerzmoo.exe (PID: 6292)
- bnjpidwkhs.exe (PID: 5708)
- lbbrivgtpx.exe (PID: 6940)
- ihiirfcovo.exe (PID: 5900)
- qshspjpvrj.exe (PID: 5496)
- oenqfgjzix.exe (PID: 728)
- npeudwntjj.exe (PID: 1752)
- qlubuxkddj.exe (PID: 2536)
- bnjpidwkhs.exe (PID: 3652)
- vtpnygvbyf.exe (PID: 6936)
- fenkerzmoo.exe (PID: 2276)
- ypftpqslse.exe (PID: 3748)
- wizjazjhys.exe (PID: 2696)
- ihiirfcovo.exe (PID: 4648)
- oenqfgjzix.exe (PID: 3836)
- ahfjhmajze.exe (PID: 4196)
- gfcrvfzuun.exe (PID: 3092)
- qlubuxkddj.exe (PID: 4060)
- guzwmwcjol.exe (PID: 1944)
- ypftpqslse.exe (PID: 1180)
- wizjazjhys.exe (PID: 3736)
- ahfjhmajze.exe (PID: 5476)
- gfcrvfzuun.exe (PID: 472)
- idrmeskhvt.exe (PID: 6504)
- dzsqvzsext.exe (PID: 6492)
- ielyojxmjc.exe (PID: 1564)
- fyftrfyvsx.exe (PID: 6896)
- idrmeskhvt.exe (PID: 2188)
- kpdtythytj.exe (PID: 4920)
- guzwmwcjol.exe (PID: 4680)
- linohldjzl.exe (PID: 4172)
- dzsqvzsext.exe (PID: 3672)
- ielyojxmjc.exe (PID: 1156)
- smzgkwmrhg.exe (PID: 4708)
- dlergcrijd.exe (PID: 1520)
- fyftrfyvsx.exe (PID: 6540)
- vwqecsmpog.exe (PID: 6228)
- iuumxhxojz.exe (PID: 6732)
- kpdtythytj.exe (PID: 4916)
- linohldjzl.exe (PID: 1700)
- inveruhexk.exe (PID: 2292)
- vwqecsmpog.exe (PID: 2664)
- smzgkwmrhg.exe (PID: 6160)
- ktbhgmiisx.exe (PID: 4960)
- dlergcrijd.exe (PID: 2120)
- vpdfhgoxag.exe (PID: 7000)
- qnvkrjiras.exe (PID: 6652)
- inveruhexk.exe (PID: 4692)
- iuumxhxojz.exe (PID: 6380)
- yvsqpypbub.exe (PID: 6140)
- ktbhgmiisx.exe (PID: 1740)
- igifvibnjk.exe (PID: 5496)
- cilpihuboc.exe (PID: 4544)
- qnvkrjiras.exe (PID: 1800)
- pksknuedwz.exe (PID: 5808)
- yvsqpypbub.exe (PID: 4688)
- afuigwkzej.exe (PID: 2708)
- vpdfhgoxag.exe (PID: 3740)
- vemnqqemfv.exe (PID: 4984)
- igifvibnjk.exe (PID: 5900)
- cilpihuboc.exe (PID: 6292)
- argbuagltc.exe (PID: 7072)
- pksknuedwz.exe (PID: 5372)
- febwzjrlib.exe (PID: 6684)
- ayegmqrinb.exe (PID: 5552)
- kfjrqpxzqx.exe (PID: 1488)
- vemnqqemfv.exe (PID: 3924)
- qseevyhzee.exe (PID: 1932)
- argbuagltc.exe (PID: 2976)
- afuigwkzej.exe (PID: 420)
- qgsmgucfpl.exe (PID: 3100)
- scdunupxle.exe (PID: 3048)
- febwzjrlib.exe (PID: 3908)
- ayegmqrinb.exe (PID: 3960)
- kfjrqpxzqx.exe (PID: 5124)
- xlncpzsvny.exe (PID: 1688)
- snqmbgtrsp.exe (PID: 4324)
- qgsmgucfpl.exe (PID: 7124)
- fmmcvowqoa.exe (PID: 2792)
- qlzfzmbhqw.exe (PID: 4880)
- scdunupxle.exe (PID: 7076)
- kqfkpqbyij.exe (PID: 6536)
- qseevyhzee.exe (PID: 5424)
- snqmbgtrsp.exe (PID: 2716)
- psmfmclaqg.exe (PID: 5172)
- xxyypvlhfc.exe (PID: 1352)
- xlncpzsvny.exe (PID: 3400)
- szbibtmvkb.exe (PID: 5528)
- fmmcvowqoa.exe (PID: 5460)
- admbemudao.exe (PID: 3884)
- qlzfzmbhqw.exe (PID: 4708)
- kqfkpqbyij.exe (PID: 5020)
- psmfmclaqg.exe (PID: 3588)
- nftwbyeeiu.exe (PID: 5232)
- fjjqsntonx.exe (PID: 2520)
- szbibtmvkb.exe (PID: 2072)
- xxyypvlhfc.exe (PID: 6512)
- ckcjzylpdt.exe (PID: 5012)
- vgswqnaziw.exe (PID: 2380)
- xfhrzstmqc.exe (PID: 3888)
- admbemudao.exe (PID: 5284)
- fjjqsntonx.exe (PID: 5348)
- czbucolvry.exe (PID: 4684)
- nftwbyeeiu.exe (PID: 4860)
- cozzbxwjtw.exe (PID: 4804)
- vgswqnaziw.exe (PID: 6256)
- ckcjzylpdt.exe (PID: 2320)
- myppahidag.exe (PID: 4216)
- ksbekqzhfl.exe (PID: 6180)
- xfhrzstmqc.exe (PID: 5244)
- xjfufycgbe.exe (PID: 2552)
- klmqkkmhjb.exe (PID: 4764)
- csnpvdimis.exe (PID: 1136)
- czbucolvry.exe (PID: 728)
- ksbekqzhfl.exe (PID: 2696)
- spwvtvpxey.exe (PID: 3936)
- myppahidag.exe (PID: 4476)
- cozzbxwjtw.exe (PID: 6344)
- xjfufycgbe.exe (PID: 2528)
- xcrqyezxsy.exe (PID: 3732)
- vszsgirzly.exe (PID: 2276)
- cwkljbzgtt.exe (PID: 5444)
- klmqkkmhjb.exe (PID: 6428)
- csnpvdimis.exe (PID: 3644)
- ngbjhmlsid.exe (PID: 6336)
- hjetcleonu.exe (PID: 6852)
- spwvtvpxey.exe (PID: 1480)
- xcrqyezxsy.exe (PID: 5952)
- uoxgnbsbcl.exe (PID: 7048)
- vszsgirzly.exe (PID: 3976)
- pnplxdmvcp.exe (PID: 3160)
- xypegxaarl.exe (PID: 7116)
- cwkljbzgtt.exe (PID: 6612)
- ngbjhmlsid.exe (PID: 5600)
- fkawjqbpyg.exe (PID: 1720)
- hjetcleonu.exe (PID: 2880)
- chfzwcynrh.exe (PID: 1352)
- ifduvddigo.exe (PID: 5168)
- uoxgnbsbcl.exe (PID: 3760)
- pnplxdmvcp.exe (PID: 6148)
- cespfpwdpm.exe (PID: 6732)
- nolpeijwob.exe (PID: 2148)
- xypegxaarl.exe (PID: 1700)
- hnbkvnujwi.exe (PID: 5556)
- fkawjqbpyg.exe (PID: 6160)
- chfzwcynrh.exe (PID: 1948)
- upqfshekef.exe (PID: 1164)
- ifduvddigo.exe (PID: 6348)
- miunykusxv.exe (PID: 3852)
- cbsftfcbgp.exe (PID: 2468)
- cespfpwdpm.exe (PID: 2380)
- elsdlbkzmp.exe (PID: 6940)
- nolpeijwob.exe (PID: 3108)
- hnbkvnujwi.exe (PID: 436)
- miunykusxv.exe (PID: 4808)
- honbyombuo.exe (PID: 4544)
- upqfshekef.exe (PID: 5716)
- epfgcaykim.exe (PID: 4832)
- elsdlbkzmp.exe (PID: 188)
- cxrtbyvmec.exe (PID: 1180)
- cbsftfcbgp.exe (PID: 620)
- esrgqevepf.exe (PID: 3608)
- honbyombuo.exe (PID: 4196)
- fefeqpeiyp.exe (PID: 6680)
- epfgcaykim.exe (PID: 2808)
- ujoropltmo.exe (PID: 2116)
- miprhbhflm.exe (PID: 6756)
- esrgqevepf.exe (PID: 6776)
- fitusoqkok.exe (PID: 4172)
- zhlzcqkehw.exe (PID: 3908)
- miauzdufpu.exe (PID: 1480)
- fefeqpeiyp.exe (PID: 3780)
- cxrtbyvmec.exe (PID: 6344)
- ujoropltmo.exe (PID: 7092)
- miprhbhflm.exe (PID: 7096)
- ppgfouvbjh.exe (PID: 3976)
- zhlzcqkehw.exe (PID: 5552)
- rowaxzowsn.exe (PID: 6620)
- uqpaeabhrc.exe (PID: 5952)
- miauzdufpu.exe (PID: 1488)
- fitusoqkok.exe (PID: 3864)
- uukdnqpsmz.exe (PID: 2880)
- efaaubbltj.exe (PID: 1720)
- zowgynqbmv.exe (PID: 2972)
- ppgfouvbjh.exe (PID: 6176)
- muooxeyepg.exe (PID: 5172)
- uvnomscspq.exe (PID: 1132)
- rowaxzowsn.exe (PID: 5008)
- uqpaeabhrc.exe (PID: 4648)
- uukdnqpsmz.exe (PID: 6304)
- cnuotzynqa.exe (PID: 6732)
- efaaubbltj.exe (PID: 2800)
- hafomjlvka.exe (PID: 6768)
- zowgynqbmv.exe (PID: 2764)
- mbwrcgrbrw.exe (PID: 2536)
- rztzqhqnex.exe (PID: 5708)
- zarzxouanh.exe (PID: 7120)
- uvnomscspq.exe (PID: 1520)
- muooxeyepg.exe (PID: 3588)
- cnuotzynqa.exe (PID: 4692)
- htpzskujnt.exe (PID: 3668)
- wnlhqyzihq.exe (PID: 6292)
- jpscnkjjpn.exe (PID: 1208)
- mbwrcgrbrw.exe (PID: 6160)
- hafomjlvka.exe (PID: 1948)
- zarzxouanh.exe (PID: 3108)
- reopzugcdc.exe (PID: 5496)
- rztzqhqnex.exe (PID: 7000)
- wnlhqyzihq.exe (PID: 504)
- zxoazouhry.exe (PID: 188)
- wclxeofgyl.exe (PID: 620)
- jpscnkjjpn.exe (PID: 3092)
- htpzskujnt.exe (PID: 7052)
- erhdkluqst.exe (PID: 724)
- mkgdzzqlad.exe (PID: 5372)
- reopzugcdc.exe (PID: 3564)
- ogjfusfetq.exe (PID: 6936)
- wyigahjzua.exe (PID: 3640)
- wclxeofgyl.exe (PID: 3148)
- cscildbicn.exe (PID: 6852)
- jxmouomypk.exe (PID: 4864)
- zxoazouhry.exe (PID: 3956)
- erhdkluqst.exe (PID: 5992)
- mkgdzzqlad.exe (PID: 2276)
- rxlojvqtpu.exe (PID: 3160)
- wororrznzh.exe (PID: 3504)
- wyigahjzua.exe (PID: 6776)
- ogjfusfetq.exe (PID: 3732)
- ueryyvrpsh.exe (PID: 5952)
- edebutwgmd.exe (PID: 856)
- jxmouomypk.exe (PID: 3780)
- mhpomezwza.exe (PID: 5620)
- cscildbicn.exe (PID: 6344)
- rfmwzfgiub.exe (PID: 6492)
- rxlojvqtpu.exe (PID: 7096)
- zgkxgucdvl.exe (PID: 1700)
- bpkuyikbct.exe (PID: 4916)
- wororrznzh.exe (PID: 5460)
- ueryyvrpsh.exe (PID: 7092)
- edebutwgmd.exe (PID: 3864)
- orrpvctcsq.exe (PID: 4708)
- hrsppoqhjg.exe (PID: 2664)
- wsqhkjxqsa.exe (PID: 2800)
- rfmwzfgiub.exe (PID: 2792)
- mhpomezwza.exe (PID: 1488)
- zgkxgucdvl.exe (PID: 2864)
- bpkuyikbct.exe (PID: 5724)
- btykapdwzo.exe (PID: 1164)
- gkelicmybi.exe (PID: 3288)
- hrdsgichmx.exe (PID: 6140)
- hrsppoqhjg.exe (PID: 2604)
- okdlojqtbk.exe (PID: 436)
- orrpvctcsq.exe (PID: 6012)
- wpnqgutjoh.exe (PID: 4808)
- wsqhkjxqsa.exe (PID: 2536)
- bmkglvsmjq.exe (PID: 5480)
- btykapdwzo.exe (PID: 4824)
- gkelicmybi.exe (PID: 6212)
- jrwyooacyl.exe (PID: 1100)
- hrdsgichmx.exe (PID: 2072)
- hkpozwzyeq.exe (PID: 7000)
- dbvohkiafl.exe (PID: 188)
- wpnqgutjoh.exe (PID: 6980)
- okdlojqtbk.exe (PID: 4692)
- bmkglvsmjq.exe (PID: 5348)
- tqibzbjgbj.exe (PID: 1752)
- jkdjxqogng.exe (PID: 1328)
- tjjutotxid.exe (PID: 3520)
- hkpozwzyeq.exe (PID: 5496)
- jzdhmfueec.exe (PID: 6680)
- dbvohkiafl.exe (PID: 2696)
- jrwyooacyl.exe (PID: 4764)
- byehfyrqvs.exe (PID: 5504)
- jkdjxqogng.exe (PID: 7052)
- tjuxsqgxll.exe (PID: 1212)
- oalcclardx.exe (PID: 6756)
- tjjutotxid.exe (PID: 3924)
- zhzfyjfjgu.exe (PID: 3624)
- tqibzbjgbj.exe (PID: 5244)
- dusnrtkrav.exe (PID: 3504)
- jzdhmfueec.exe (PID: 6180)
- byehfyrqvs.exe (PID: 4224)
- oalcclardx.exe (PID: 2976)
- oqmlsnqgie.exe (PID: 6704)
- jvaiiyqxar.exe (PID: 856)
- rzmaljyepm.exe (PID: 5620)
- zhzfyjfjgu.exe (PID: 6656)
- tjuxsqgxll.exe (PID: 3960)
- bhrlhpdvki.exe (PID: 4680)
- dusnrtkrav.exe (PID: 4080)
- tgslajaijy.exe (PID: 5628)
- oqmlsnqgie.exe (PID: 7164)
- lcswokebxt.exe (PID: 6516)
- jvaiiyqxar.exe (PID: 6876)
- wnqlvnqmnd.exe (PID: 6900)
- rzmaljyepm.exe (PID: 3100)
- tgslajaijy.exe (PID: 4648)
- dufrbkxwpl.exe (PID: 5008)
- blnbjopyae.exe (PID: 5080)
- raxmcllesu.exe (PID: 6768)
- bhrlhpdvki.exe (PID: 1896)
- gbtcqcgajy.exe (PID: 6140)
- lcswokebxt.exe (PID: 2188)
- raxmcllesu.exe (PID: 3884)
- jhzegthwdl.exe (PID: 4456)
- zxusykjcrr.exe (PID: 4832)
- wnqlvnqmnd.exe (PID: 3000)
- twmxifdwsv.exe (PID: 436)
- blnbjopyae.exe (PID: 5904)
- ymkxptuztq.exe (PID: 3196)
- gbtcqcgajy.exe (PID: 756)
- dufrbkxwpl.exe (PID: 5340)
- jhzegthwdl.exe (PID: 2604)
- twmxifdwsv.exe (PID: 2128)
- gqukzmwogn.exe (PID: 4664)
- lscfpjcuna.exe (PID: 6420)
- rmwiagddow.exe (PID: 1948)
- qefsubfuci.exe (PID: 6160)
- zxusykjcrr.exe (PID: 3888)
- gqukzmwogn.exe (PID: 4688)
- ymkxptuztq.exe (PID: 3588)
- yfdtihipds.exe (PID: 3900)
- wdaiojqtys.exe (PID: 5808)
- rmwiagddow.exe (PID: 4196)
- aiuihkubsb.exe (PID: 5476)
- lscfpjcuna.exe (PID: 7128)
- iitjwzywsl.exe (PID: 4216)
- nkbleeecaz.exe (PID: 6320)
- yfdtihipds.exe (PID: 472)
- wdaiojqtys.exe (PID: 4984)
- ycawduexvv.exe (PID: 424)
- qefsubfuci.exe (PID: 888)
- qjtwonabvl.exe (PID: 6936)
- aiuihkubsb.exe (PID: 3748)
- iitjwzywsl.exe (PID: 1068)
- epukheoxkc.exe (PID: 1480)
- burmvqmvcd.exe (PID: 3936)
- dekpzurlmb.exe (PID: 3976)
- qjtwonabvl.exe (PID: 6956)
- jbpxmnqwzk.exe (PID: 1472)
- ycawduexvv.exe (PID: 6808)
- nkbleeecaz.exe (PID: 7072)
- lxsahnfxsw.exe (PID: 3048)
- burmvqmvcd.exe (PID: 5124)
- ookkjeawnj.exe (PID: 1352)
- epukheoxkc.exe (PID: 3584)
- vsuxbqdmig.exe (PID: 480)
- dekpzurlmb.exe (PID: 7124)
- fgwakxwacc.exe (PID: 6148)
- jbpxmnqwzk.exe (PID: 3760)
- yklntmlkpf.exe (PID: 3688)
- osyaldmzdm.exe (PID: 3948)
- vatbfswjlw.exe (PID: 1096)
- lxsahnfxsw.exe (PID: 5172)
- dbsbmzaely.exe (PID: 2632)
- vsuxbqdmig.exe (PID: 4916)
- otiyrxchmw.exe (PID: 6304)
- yklntmlkpf.exe (PID: 2520)
- qzwjgpddgr.exe (PID: 1816)
- fgwakxwacc.exe (PID: 4052)
- veirzrilbr.exe (PID: 7056)
- osyaldmzdm.exe (PID: 1440)
- vatbfswjlw.exe (PID: 1984)
- anymqwnrin.exe (PID: 6004)
- dbsbmzaely.exe (PID: 7048)
- icmzuytkwc.exe (PID: 3108)
- otiyrxchmw.exe (PID: 3876)
- dtfcrnunxy.exe (PID: 756)
- qzwjgpddgr.exe (PID: 1880)
- ookkjeawnj.exe (PID: 6684)
- igipwfemmf.exe (PID: 6368)
- anymqwnrin.exe (PID: 1204)
- oqqkmckstt.exe (PID: 3704)
- yagprsevur.exe (PID: 4860)
- icmzuytkwc.exe (PID: 4832)
- dqdkngqybn.exe (PID: 4804)
- dtfcrnunxy.exe (PID: 2168)
- lnyxrjvrpk.exe (PID: 5992)
- didhiexbrx.exe (PID: 4664)
- ilvfekuckl.exe (PID: 4544)
- igipwfemmf.exe (PID: 5352)
- qeuglzyxku.exe (PID: 2580)
- oqqkmckstt.exe (PID: 2220)
- yagprsevur.exe (PID: 5716)
- nfmtpckzys.exe (PID: 6348)
- dqdkngqybn.exe (PID: 2460)
- tzyozzciyg.exe (PID: 6936)
- lnyxrjvrpk.exe (PID: 6172)
- vfmypqlmta.exe (PID: 6536)
- ilvfekuckl.exe (PID: 504)
- bdjgurlxob.exe (PID: 3748)
- qeuglzyxku.exe (PID: 7052)
- dvjennsvvj.exe (PID: 1068)
- didhiexbrx.exe (PID: 5116)
- veirzrilbr.exe (PID: 4708)
- tzyozzciyg.exe (PID: 3924)
- dczjewwkwh.exe (PID: 5564)
- ilpeubbqwv.exe (PID: 5552)
- qbcrgehjss.exe (PID: 1472)
- yfnepxjyep.exe (PID: 4844)
- bdjgurlxob.exe (PID: 424)
- vfmypqlmta.exe (PID: 4984)
- dvjennsvvj.exe (PID: 3936)
- ipduwavsmy.exe (PID: 3112)
- dczjewwkwh.exe (PID: 1480)
- ddkmdqjkap.exe (PID: 3852)
- qicudgrnui.exe (PID: 4048)
- xmmauzcdhx.exe (PID: 2972)
- qbcrgehjss.exe (PID: 3640)
- fjavyczwdu.exe (PID: 2468)
- ilpeubbqwv.exe (PID: 3976)
- yfnepxjyep.exe (PID: 3048)
- ngkaqvcmqr.exe (PID: 6868)
- ddkmdqjkap.exe (PID: 1352)
- ipduwavsmy.exe (PID: 480)
- gyzgjsicrr.exe (PID: 6192)
- qicudgrnui.exe (PID: 4560)
- nfmtpckzys.exe (PID: 5244)
- vkunzgncco.exe (PID: 6140)
- xmmauzcdhx.exe (PID: 6260)
- sergjiqylj.exe (PID: 6492)
- fjavyczwdu.exe (PID: 6772)
- ngkaqvcmqr.exe (PID: 3768)
- imbiesodkl.exe (PID: 5600)
- yniolnudov.exe (PID: 6212)
- gyzgjsicrr.exe (PID: 7164)
- dscwexhlie.exe (PID: 4676)
- xfzjzowmtx.exe (PID: 316)
- vkunzgncco.exe (PID: 1688)
- imbiesodkl.exe (PID: 3668)
- imorhuzuqa.exe (PID: 2356)
- sergjiqylj.exe (PID: 3628)
- ndsmdakxxo.exe (PID: 2800)
- yvjwtykssk.exe (PID: 7068)
- yniolnudov.exe (PID: 3196)
- qckwnroesa.exe (PID: 3740)
- xfzjzowmtx.exe (PID: 5904)
- dscwexhlie.exe (PID: 2296)
- nhhcfgeznr.exe (PID: 188)
- imorhuzuqa.exe (PID: 4692)
- fhqpqgcrhq.exe (PID: 4060)
- fztkljvhfh.exe (PID: 6532)
- nlauarehuf.exe (PID: 4824)
- qckwnroesa.exe (PID: 4684)
- yvjwtykssk.exe (PID: 1164)
- ndsmdakxxo.exe (PID: 2128)
- flefkentxl.exe (PID: 7128)
- suipqwkvca.exe (PID: 4768)
- fztkljvhfh.exe (PID: 7080)
- kxyfeoacru.exe (PID: 2680)
- nlauarehuf.exe (PID: 1328)
- fhqpqgcrhq.exe (PID: 4216)
- xvqkhcqbjw.exe (PID: 2708)
- nhhcfgeznr.exe (PID: 3632)
- kjkgssxoyf.exe (PID: 6836)
- vtadxiyrzd.exe (PID: 5644)
- suipqwkvca.exe (PID: 3736)
- zgtlqslzue.exe (PID: 3576)
- kbudgmmwhp.exe (PID: 5496)
- flefkentxl.exe (PID: 4224)
- xvqkhcqbjw.exe (PID: 1800)
- scujybnjkx.exe (PID: 2144)
- kjkgssxoyf.exe (PID: 2976)
- zkpbsqxbjh.exe (PID: 5952)
- kxyfeoacru.exe (PID: 4444)
- snwehtkviz.exe (PID: 3716)
- zgtlqslzue.exe (PID: 5252)
- fimryrwffq.exe (PID: 5628)
- pdncnmxkst.exe (PID: 4080)
- kbudgmmwhp.exe (PID: 6620)
- vtadxiyrzd.exe (PID: 3960)
- vxzeqjxttp.exe (PID: 6892)
- snwehtkviz.exe (PID: 6876)
- ahpzgodzal.exe (PID: 6512)
- scujybnjkx.exe (PID: 1056)
- zkpbsqxbjh.exe (PID: 2808)
- crhpzklxhk.exe (PID: 6192)
- fimryrwffq.exe (PID: 5744)
- kguckmiqdh.exe (PID: 3100)
- pdncnmxkst.exe (PID: 6776)
- kydvfzshjt.exe (PID: 6840)
- vxzeqjxttp.exe (PID: 3504)
- qtpqpwsqsg.exe (PID: 3768)
- ahpzgodzal.exe (PID: 856)
- szdafouumb.exe (PID: 1688)
- crhpzklxhk.exe (PID: 3972)
- vjvqxkbstb.exe (PID: 7164)
- kguckmiqdh.exe (PID: 1440)
- ckuqeyfgtk.exe (PID: 4648)
- kctqsfjbcm.exe (PID: 5904)
- qtpqpwsqsg.exe (PID: 5724)
- mywtnfquvh.exe (PID: 4764)
- kydvfzshjt.exe (PID: 6540)
- szdafouumb.exe (PID: 316)
- ppvdxpubqt.exe (PID: 756)
- vjvqxkbstb.exe (PID: 2520)
- swcoegvxlo.exe (PID: 4196)
- swcggbfnra.exe (PID: 1356)
- kctqsfjbcm.exe (PID: 3888)
- xuhomuezma.exe (PID: 6360)
- ckuqeyfgtk.exe (PID: 4708)
- mywtnfquvh.exe (PID: 3740)
- ppvdxpubqt.exe (PID: 3880)
- fnfphpmimu.exe (PID: 2620)
- hxxezmugbu.exe (PID: 7128)
- xyscdnppzx.exe (PID: 620)
- swcoegvxlo.exe (PID: 3000)
- swcggbfnra.exe (PID: 1488)
- kdlppdvkwg.exe (PID: 2680)
- xuhomuezma.exe (PID: 5716)
- ngonbrxdeo.exe (PID: 6836)
- xyscdnppzx.exe (PID: 2864)
- fnfphpmimu.exe (PID: 7080)
- aivigdhflm.exe (PID: 6936)
- ulystkabql.exe (PID: 5808)
- zbwsaxrvsx.exe (PID: 892)
- kdlppdvkwg.exe (PID: 7052)
- ezbiozqhng.exe (PID: 6320)
- hxxezmugbu.exe (PID: 4796)
- mdlnxktxav.exe (PID: 1128)
- upovgirnbf.exe (PID: 2648)
- ulystkabql.exe (PID: 1752)
- ngonbrxdeo.exe (PID: 5244)
- aivigdhflm.exe (PID: 1700)
- zbwsaxrvsx.exe (PID: 6676)
- fzmlftdhqo.exe (PID: 1704)
- aqeqpnxbia.exe (PID: 5504)
- ezbiozqhng.exe (PID: 6520)
- mhadzimzpy.exe (PID: 6704)
- mdlnxktxav.exe (PID: 7124)
- pkdbmvhaxy.exe (PID: 5620)
- pkeoydmsae.exe (PID: 6900)
- aqeqpnxbia.exe (PID: 6408)
- sqsrnvnour.exe (PID: 5528)
- fzmlftdhqo.exe (PID: 5416)
- upovgirnbf.exe (PID: 5168)
- pkdbmvhaxy.exe (PID: 6680)
- mhadzimzpy.exe (PID: 4844)
- jiehgnjsjk.exe (PID: 3972)
- cmtkvpotic.exe (PID: 6732)
- ezwmqqdmbo.exe (PID: 6216)
- ubunlldvki.exe (PID: 6652)
- pkeoydmsae.exe (PID: 1208)
- cxescwokxx.exe (PID: 5080)
- nlikeijtli.exe (PID: 1576)
- cmtkvpotic.exe (PID: 7104)
- sqsrnvnour.exe (PID: 6840)
- rcffawuwse.exe (PID: 1564)
- ezwmqqdmbo.exe (PID: 6940)
- xwzadlvfss.exe (PID: 2760)
- jiehgnjsjk.exe (PID: 2764)
- cueqrmuqna.exe (PID: 4476)
- ubunlldvki.exe (PID: 7164)
- cxescwokxx.exe (PID: 5424)
- kygvifwgax.exe (PID: 2380)
- rcffawuwse.exe (PID: 3944)
- rgcbgueqcg.exe (PID: 4060)
- xwzadlvfss.exe (PID: 5988)
- zgbbvjhddi.exe (PID: 3788)
- nlikeijtli.exe (PID: 2072)
- miftabeehx.exe (PID: 6420)
- cueqrmuqna.exe (PID: 4760)
- kygvifwgax.exe (PID: 316)
- cnqlkbrhxc.exe (PID: 4684)
- wxhbcxzfmc.exe (PID: 6360)
- emvogzwyaz.exe (PID: 3884)
- rgcbgueqcg.exe (PID: 3092)
- jzowzjagua.exe (PID: 5284)
- miftabeehx.exe (PID: 2348)
- zgbbvjhddi.exe (PID: 4832)
- jomcqrmvny.exe (PID: 7128)
- oljjeslgjh.exe (PID: 3148)
- cnqlkbrhxc.exe (PID: 4156)
- wxhbcxzfmc.exe (PID: 2064)
- emvogzwyaz.exe (PID: 2168)
- uvasgxoelb.exe (PID: 6172)
- jzowzjagua.exe (PID: 5924)
- plsxqaiydf.exe (PID: 2228)
- ccxxmuvnnj.exe (PID: 892)
- jomcqrmvny.exe (PID: 4544)
- jhzdvfgday.exe (PID: 6320)
- oljjeslgjh.exe (PID: 2580)
- cnzsnmszld.exe (PID: 6936)
- plsxqaiydf.exe (PID: 3780)
- pbtfgcgmiu.exe (PID: 6236)
- uvasgxoelb.exe (PID: 536)
- wfdtpnjcvr.exe (PID: 7140)
- ccxxmuvnnj.exe (PID: 4796)
- wyedrittbc.exe (PID: 4680)
- zesozauxvp.exe (PID: 6868)
- cnzsnmszld.exe (PID: 4224)
- jhzdvfgday.exe (PID: 3112)
- hxrongykez.exe (PID: 6140)
- pbtfgcgmiu.exe (PID: 5244)
- wyedrittbc.exe (PID: 1700)
- mjmbsqiktg.exe (PID: 1136)
- mrljydytem.exe (PID: 7124)
- wfdtpnjcvr.exe (PID: 1752)
- hxrongykez.exe (PID: 1216)
- tduzmzuoca.exe (PID: 5460)
- mvyuhcnear.exe (PID: 5628)
- zesozauxvp.exe (PID: 6892)
- mkwzykqsbq.exe (PID: 360)
- mrljydytem.exe (PID: 2144)
- mjmbsqiktg.exe (PID: 7028)
- zmdudwatjo.exe (PID: 2876)
- hbqhhhxmxk.exe (PID: 4456)
- jlqxzdflek.exe (PID: 2120)
- mkwzykqsbq.exe (PID: 6356)
- ojnnmwewzt.exe (PID: 2632)
- tduzmzuoca.exe (PID: 1096)
- mvyuhcnear.exe (PID: 3640)
- rpbpcwnstf.exe (PID: 5340)
- zqaqicjnup.exe (PID: 3876)
- zmdudwatjo.exe (PID: 4052)
- hbqhhhxmxk.exe (PID: 1080)
- hulimvrvjl.exe (PID: 5020)
- basnbyrmbp.exe (PID: 4676)
Reads the machine GUID from the registry
- hnpnhroogk.exe (PID: 504)
- rrsgzjxrfn.exe (PID: 1180)
- gkyzvwxhgh.exe (PID: 5744)
- jrejkwgdat.exe (PID: 6656)
- bqkfuqpdlb.exe (PID: 5008)
- rgsxwydwwq.exe (PID: 5628)
- hnpnhroogk.exe (PID: 5400)
- zhzxcfhswa.exe (PID: 2696)
- emkfwpmsqb.exe (PID: 1700)
- rrsgzjxrfn.exe (PID: 4760)
- 2025-06-21_cfa2253cf9e3a2e9a9ae6d4a84aef344_amadey_elex_smoke-loader_stop.exe (PID: 4968)
- cxknaefmxp.exe (PID: 2808)
- mjgszzjley.exe (PID: 6160)
- gkyzvwxhgh.exe (PID: 2220)
- jrejkwgdat.exe (PID: 1352)
- opmdprspyk.exe (PID: 5908)
- wlwigcvflh.exe (PID: 3948)
- rgsxwydwwq.exe (PID: 3884)
- zhzxcfhswa.exe (PID: 1720)
- ydofyycdsh.exe (PID: 6232)
- emkfwpmsqb.exe (PID: 5168)
- mjgszzjley.exe (PID: 3196)
- zsnqboljom.exe (PID: 5348)
- opmdprspyk.exe (PID: 2792)
- jkcwgefmpk.exe (PID: 2664)
- wlwigcvflh.exe (PID: 6940)
- rsyoaupexm.exe (PID: 3956)
- ydofyycdsh.exe (PID: 7092)
- ywibsfzukj.exe (PID: 2120)
- gphtyuvhkt.exe (PID: 4684)
- bkcioqehuc.exe (PID: 5808)
- zsnqboljom.exe (PID: 5372)
- gpihktbhmr.exe (PID: 1800)
- ghjreolptd.exe (PID: 6292)
- jkcwgefmpk.exe (PID: 5904)
- rsyoaupexm.exe (PID: 4680)
- rwvjoagyho.exe (PID: 1096)
- ywibsfzukj.exe (PID: 5900)
- guujhzlfiy.exe (PID: 1212)
- bkcioqehuc.exe (PID: 2808)
- gphtyuvhkt.exe (PID: 4768)
- oqexyswvvv.exe (PID: 1036)
- gpihktbhmr.exe (PID: 5424)
- twjfetvgqw.exe (PID: 4080)
- boifsaztqg.exe (PID: 1068)
- rwvjoagyho.exe (PID: 3092)
- lgykxqbwre.exe (PID: 7072)
- ghjreolptd.exe (PID: 5476)
- ouansqhplq.exe (PID: 1512)
- guujhzlfiy.exe (PID: 3788)
- wndvbwgnua.exe (PID: 1896)
- oqexyswvvv.exe (PID: 1204)
- yxcltsomba.exe (PID: 1080)
- twjfetvgqw.exe (PID: 5556)
- jtvvbnojol.exe (PID: 6228)
- oypduptrju.exe (PID: 1520)
- lgykxqbwre.exe (PID: 2072)
- boifsaztqg.exe (PID: 888)
- ouansqhplq.exe (PID: 6896)
- tsjgxluajh.exe (PID: 7140)
- wndvbwgnua.exe (PID: 4172)
- bthgmsywjr.exe (PID: 4960)
- jtvvbnojol.exe (PID: 1232)
- yxcltsomba.exe (PID: 6700)
- wkbjjpzqtn.exe (PID: 3148)
- oypduptrju.exe (PID: 6348)
- tsjgxluajh.exe (PID: 1752)
- bahjjdqsui.exe (PID: 2380)
- bxvjurmzfo.exe (PID: 6900)
- bthgmsywjr.exe (PID: 3876)
- bpgutlzyie.exe (PID: 4684)
- wkbjjpzqtn.exe (PID: 3652)
- bmtcfhumbt.exe (PID: 1328)
- bxvjurmzfo.exe (PID: 2276)
- tadkhcgoyy.exe (PID: 5244)
- ornpqfbaqc.exe (PID: 6292)
- jtqzdebwdb.exe (PID: 6256)
- bmtcfhumbt.exe (PID: 4808)
- bahjjdqsui.exe (PID: 4648)
- btcknrkbga.exe (PID: 3960)
- ggwshtpjsj.exe (PID: 1036)
- bpgutlzyie.exe (PID: 6840)
- qylqljrmth.exe (PID: 4764)
- jtqzdebwdb.exe (PID: 1964)
- vdfxftwunh.exe (PID: 2764)
- ornpqfbaqc.exe (PID: 1216)
- bjcnsudyiq.exe (PID: 3092)
- tadkhcgoyy.exe (PID: 4680)
- gkkijrbmie.exe (PID: 6320)
- btcknrkbga.exe (PID: 5008)
- ggwshtpjsj.exe (PID: 3780)
- qylqljrmth.exe (PID: 1496)
- vdfxftwunh.exe (PID: 4880)
- ozgvmcgeeb.exe (PID: 1728)
- qgmycthayv.exe (PID: 4576)
- bjcnsudyiq.exe (PID: 4836)
- tnzjgamsts.exe (PID: 2632)
- gkkijrbmie.exe (PID: 4512)
- qynqwgrreh.exe (PID: 1652)
- ozgvmcgeeb.exe (PID: 6876)
- buopeptbva.exe (PID: 6160)
- vxrzyouqar.exe (PID: 4760)
- izyuvierip.exe (PID: 2520)
- qynqwgrreh.exe (PID: 5712)
- lbbrivgtpx.exe (PID: 3108)
- tnzjgamsts.exe (PID: 4156)
- qgmycthayv.exe (PID: 6408)
- npeudwntjj.exe (PID: 6732)
- vxrzyouqar.exe (PID: 4692)
- qshspjpvrj.exe (PID: 3844)
- buopeptbva.exe (PID: 6216)
- vtpnygvbyf.exe (PID: 4684)
- izyuvierip.exe (PID: 4804)
- lbbrivgtpx.exe (PID: 6940)
- fenkerzmoo.exe (PID: 6292)
- bnjpidwkhs.exe (PID: 5708)
- ihiirfcovo.exe (PID: 5900)
- qshspjpvrj.exe (PID: 5496)
- oenqfgjzix.exe (PID: 728)
- npeudwntjj.exe (PID: 1752)
- vtpnygvbyf.exe (PID: 6936)
- qlubuxkddj.exe (PID: 2536)
- fenkerzmoo.exe (PID: 2276)
- ypftpqslse.exe (PID: 3748)
- bnjpidwkhs.exe (PID: 3652)
- wizjazjhys.exe (PID: 2696)
- oenqfgjzix.exe (PID: 3836)
- ihiirfcovo.exe (PID: 4648)
- ahfjhmajze.exe (PID: 4196)
- gfcrvfzuun.exe (PID: 3092)
- guzwmwcjol.exe (PID: 1944)
- wizjazjhys.exe (PID: 3736)
- ypftpqslse.exe (PID: 1180)
- qlubuxkddj.exe (PID: 4060)
- ahfjhmajze.exe (PID: 5476)
- gfcrvfzuun.exe (PID: 472)
- idrmeskhvt.exe (PID: 6504)
- dzsqvzsext.exe (PID: 6492)
- ielyojxmjc.exe (PID: 1564)
- fyftrfyvsx.exe (PID: 6896)
- linohldjzl.exe (PID: 4172)
- kpdtythytj.exe (PID: 4920)
- guzwmwcjol.exe (PID: 4680)
- idrmeskhvt.exe (PID: 2188)
- dzsqvzsext.exe (PID: 3672)
- smzgkwmrhg.exe (PID: 4708)
- fyftrfyvsx.exe (PID: 6540)
- dlergcrijd.exe (PID: 1520)
- ielyojxmjc.exe (PID: 1156)
- vwqecsmpog.exe (PID: 6228)
- inveruhexk.exe (PID: 2292)
- linohldjzl.exe (PID: 1700)
- iuumxhxojz.exe (PID: 6732)
- kpdtythytj.exe (PID: 4916)
- smzgkwmrhg.exe (PID: 6160)
- ktbhgmiisx.exe (PID: 4960)
- vwqecsmpog.exe (PID: 2664)
- dlergcrijd.exe (PID: 2120)
- vpdfhgoxag.exe (PID: 7000)
- qnvkrjiras.exe (PID: 6652)
- yvsqpypbub.exe (PID: 6140)
- iuumxhxojz.exe (PID: 6380)
- ktbhgmiisx.exe (PID: 1740)
- igifvibnjk.exe (PID: 5496)
- inveruhexk.exe (PID: 4692)
- cilpihuboc.exe (PID: 4544)
- qnvkrjiras.exe (PID: 1800)
- pksknuedwz.exe (PID: 5808)
- vpdfhgoxag.exe (PID: 3740)
- yvsqpypbub.exe (PID: 4688)
- afuigwkzej.exe (PID: 2708)
- vemnqqemfv.exe (PID: 4984)
- igifvibnjk.exe (PID: 5900)
- cilpihuboc.exe (PID: 6292)
- argbuagltc.exe (PID: 7072)
- pksknuedwz.exe (PID: 5372)
- febwzjrlib.exe (PID: 6684)
- ayegmqrinb.exe (PID: 5552)
- kfjrqpxzqx.exe (PID: 1488)
- vemnqqemfv.exe (PID: 3924)
- qseevyhzee.exe (PID: 1932)
- afuigwkzej.exe (PID: 420)
- qgsmgucfpl.exe (PID: 3100)
- argbuagltc.exe (PID: 2976)
- scdunupxle.exe (PID: 3048)
- febwzjrlib.exe (PID: 3908)
- ayegmqrinb.exe (PID: 3960)
- kfjrqpxzqx.exe (PID: 5124)
- xlncpzsvny.exe (PID: 1688)
- snqmbgtrsp.exe (PID: 4324)
- fmmcvowqoa.exe (PID: 2792)
- qgsmgucfpl.exe (PID: 7124)
- scdunupxle.exe (PID: 7076)
- qlzfzmbhqw.exe (PID: 4880)
- kqfkpqbyij.exe (PID: 6536)
- qseevyhzee.exe (PID: 5424)
- snqmbgtrsp.exe (PID: 2716)
- psmfmclaqg.exe (PID: 5172)
- szbibtmvkb.exe (PID: 5528)
- xlncpzsvny.exe (PID: 3400)
- fmmcvowqoa.exe (PID: 5460)
- xxyypvlhfc.exe (PID: 1352)
- admbemudao.exe (PID: 3884)
- qlzfzmbhqw.exe (PID: 4708)
- kqfkpqbyij.exe (PID: 5020)
- psmfmclaqg.exe (PID: 3588)
- nftwbyeeiu.exe (PID: 5232)
- fjjqsntonx.exe (PID: 2520)
- szbibtmvkb.exe (PID: 2072)
- ckcjzylpdt.exe (PID: 5012)
- vgswqnaziw.exe (PID: 2380)
- xxyypvlhfc.exe (PID: 6512)
- fjjqsntonx.exe (PID: 5348)
- admbemudao.exe (PID: 5284)
- xfhrzstmqc.exe (PID: 3888)
- nftwbyeeiu.exe (PID: 4860)
- czbucolvry.exe (PID: 4684)
- cozzbxwjtw.exe (PID: 4804)
- vgswqnaziw.exe (PID: 6256)
- ckcjzylpdt.exe (PID: 2320)
- ksbekqzhfl.exe (PID: 6180)
- xjfufycgbe.exe (PID: 2552)
- myppahidag.exe (PID: 4216)
- xfhrzstmqc.exe (PID: 5244)
- czbucolvry.exe (PID: 728)
- klmqkkmhjb.exe (PID: 4764)
- csnpvdimis.exe (PID: 1136)
- ksbekqzhfl.exe (PID: 2696)
- myppahidag.exe (PID: 4476)
- cozzbxwjtw.exe (PID: 6344)
- spwvtvpxey.exe (PID: 3936)
- xjfufycgbe.exe (PID: 2528)
- xcrqyezxsy.exe (PID: 3732)
- vszsgirzly.exe (PID: 2276)
- csnpvdimis.exe (PID: 3644)
- cwkljbzgtt.exe (PID: 5444)
- klmqkkmhjb.exe (PID: 6428)
- spwvtvpxey.exe (PID: 1480)
- hjetcleonu.exe (PID: 6852)
- ngbjhmlsid.exe (PID: 6336)
- pnplxdmvcp.exe (PID: 3160)
- xcrqyezxsy.exe (PID: 5952)
- uoxgnbsbcl.exe (PID: 7048)
- vszsgirzly.exe (PID: 3976)
- cwkljbzgtt.exe (PID: 6612)
- hjetcleonu.exe (PID: 2880)
- xypegxaarl.exe (PID: 7116)
- ngbjhmlsid.exe (PID: 5600)
- fkawjqbpyg.exe (PID: 1720)
- chfzwcynrh.exe (PID: 1352)
- ifduvddigo.exe (PID: 5168)
- pnplxdmvcp.exe (PID: 6148)
- uoxgnbsbcl.exe (PID: 3760)
- cespfpwdpm.exe (PID: 6732)
- nolpeijwob.exe (PID: 2148)
- xypegxaarl.exe (PID: 1700)
- hnbkvnujwi.exe (PID: 5556)
- fkawjqbpyg.exe (PID: 6160)
- chfzwcynrh.exe (PID: 1948)
- upqfshekef.exe (PID: 1164)
- ifduvddigo.exe (PID: 6348)
- miunykusxv.exe (PID: 3852)
- elsdlbkzmp.exe (PID: 6940)
- nolpeijwob.exe (PID: 3108)
- cbsftfcbgp.exe (PID: 2468)
- cespfpwdpm.exe (PID: 2380)
- hnbkvnujwi.exe (PID: 436)
- honbyombuo.exe (PID: 4544)
- miunykusxv.exe (PID: 4808)
- upqfshekef.exe (PID: 5716)
- cbsftfcbgp.exe (PID: 620)
- epfgcaykim.exe (PID: 4832)
- esrgqevepf.exe (PID: 3608)
- elsdlbkzmp.exe (PID: 188)
- honbyombuo.exe (PID: 4196)
- miprhbhflm.exe (PID: 6756)
- fefeqpeiyp.exe (PID: 6680)
- epfgcaykim.exe (PID: 2808)
- ujoropltmo.exe (PID: 2116)
- cxrtbyvmec.exe (PID: 1180)
- esrgqevepf.exe (PID: 6776)
- zhlzcqkehw.exe (PID: 3908)
- fefeqpeiyp.exe (PID: 3780)
- miauzdufpu.exe (PID: 1480)
- fitusoqkok.exe (PID: 4172)
- cxrtbyvmec.exe (PID: 6344)
- miprhbhflm.exe (PID: 7096)
- ppgfouvbjh.exe (PID: 3976)
- ujoropltmo.exe (PID: 7092)
- zhlzcqkehw.exe (PID: 5552)
- uqpaeabhrc.exe (PID: 5952)
- rowaxzowsn.exe (PID: 6620)
- uukdnqpsmz.exe (PID: 2880)
- miauzdufpu.exe (PID: 1488)
- fitusoqkok.exe (PID: 3864)
- ppgfouvbjh.exe (PID: 6176)
- efaaubbltj.exe (PID: 1720)
- zowgynqbmv.exe (PID: 2972)
- uvnomscspq.exe (PID: 1132)
- muooxeyepg.exe (PID: 5172)
- uqpaeabhrc.exe (PID: 4648)
- cnuotzynqa.exe (PID: 6732)
- uukdnqpsmz.exe (PID: 6304)
- hafomjlvka.exe (PID: 6768)
- rowaxzowsn.exe (PID: 5008)
- mbwrcgrbrw.exe (PID: 2536)
- efaaubbltj.exe (PID: 2800)
- zowgynqbmv.exe (PID: 2764)
- rztzqhqnex.exe (PID: 5708)
- muooxeyepg.exe (PID: 3588)
- zarzxouanh.exe (PID: 7120)
- uvnomscspq.exe (PID: 1520)
- htpzskujnt.exe (PID: 3668)
- wnlhqyzihq.exe (PID: 6292)
- cnuotzynqa.exe (PID: 4692)
- jpscnkjjpn.exe (PID: 1208)
- hafomjlvka.exe (PID: 1948)
- mbwrcgrbrw.exe (PID: 6160)
- rztzqhqnex.exe (PID: 7000)
- zarzxouanh.exe (PID: 3108)
- wclxeofgyl.exe (PID: 620)
- reopzugcdc.exe (PID: 5496)
- wnlhqyzihq.exe (PID: 504)
- zxoazouhry.exe (PID: 188)
- jpscnkjjpn.exe (PID: 3092)
- erhdkluqst.exe (PID: 724)
- htpzskujnt.exe (PID: 7052)
- reopzugcdc.exe (PID: 3564)
- ogjfusfetq.exe (PID: 6936)
- mkgdzzqlad.exe (PID: 5372)
- wyigahjzua.exe (PID: 3640)
- wclxeofgyl.exe (PID: 3148)
- jxmouomypk.exe (PID: 4864)
- erhdkluqst.exe (PID: 5992)
- cscildbicn.exe (PID: 6852)
- zxoazouhry.exe (PID: 3956)
- rxlojvqtpu.exe (PID: 3160)
- mkgdzzqlad.exe (PID: 2276)
- wororrznzh.exe (PID: 3504)
- wyigahjzua.exe (PID: 6776)
- ogjfusfetq.exe (PID: 3732)
- ueryyvrpsh.exe (PID: 5952)
- edebutwgmd.exe (PID: 856)
- mhpomezwza.exe (PID: 5620)
- jxmouomypk.exe (PID: 3780)
- cscildbicn.exe (PID: 6344)
- rxlojvqtpu.exe (PID: 7096)
- rfmwzfgiub.exe (PID: 6492)
- bpkuyikbct.exe (PID: 4916)
- wororrznzh.exe (PID: 5460)
- zgkxgucdvl.exe (PID: 1700)
- ueryyvrpsh.exe (PID: 7092)
- edebutwgmd.exe (PID: 3864)
- orrpvctcsq.exe (PID: 4708)
- hrsppoqhjg.exe (PID: 2664)
- wsqhkjxqsa.exe (PID: 2800)
- rfmwzfgiub.exe (PID: 2792)
- mhpomezwza.exe (PID: 1488)
- zgkxgucdvl.exe (PID: 2864)
- bpkuyikbct.exe (PID: 5724)
- btykapdwzo.exe (PID: 1164)
- hrsppoqhjg.exe (PID: 2604)
- hrdsgichmx.exe (PID: 6140)
- gkelicmybi.exe (PID: 3288)
- orrpvctcsq.exe (PID: 6012)
- wsqhkjxqsa.exe (PID: 2536)
- okdlojqtbk.exe (PID: 436)
- bmkglvsmjq.exe (PID: 5480)
- btykapdwzo.exe (PID: 4824)
- wpnqgutjoh.exe (PID: 4808)
- gkelicmybi.exe (PID: 6212)
- jrwyooacyl.exe (PID: 1100)
- hrdsgichmx.exe (PID: 2072)
- hkpozwzyeq.exe (PID: 7000)
- dbvohkiafl.exe (PID: 188)
- okdlojqtbk.exe (PID: 4692)
- tqibzbjgbj.exe (PID: 1752)
- wpnqgutjoh.exe (PID: 6980)
- jkdjxqogng.exe (PID: 1328)
- bmkglvsmjq.exe (PID: 5348)
- hkpozwzyeq.exe (PID: 5496)
- tjjutotxid.exe (PID: 3520)
- jrwyooacyl.exe (PID: 4764)
- dbvohkiafl.exe (PID: 2696)
- byehfyrqvs.exe (PID: 5504)
- jzdhmfueec.exe (PID: 6680)
- oalcclardx.exe (PID: 6756)
- jkdjxqogng.exe (PID: 7052)
- zhzfyjfjgu.exe (PID: 3624)
- tjjutotxid.exe (PID: 3924)
- tjuxsqgxll.exe (PID: 1212)
- tqibzbjgbj.exe (PID: 5244)
- dusnrtkrav.exe (PID: 3504)
- byehfyrqvs.exe (PID: 4224)
- oalcclardx.exe (PID: 2976)
- oqmlsnqgie.exe (PID: 6704)
- jzdhmfueec.exe (PID: 6180)
- jvaiiyqxar.exe (PID: 856)
- rzmaljyepm.exe (PID: 5620)
- zhzfyjfjgu.exe (PID: 6656)
- tjuxsqgxll.exe (PID: 3960)
- bhrlhpdvki.exe (PID: 4680)
- dusnrtkrav.exe (PID: 4080)
- tgslajaijy.exe (PID: 5628)
- lcswokebxt.exe (PID: 6516)
- raxmcllesu.exe (PID: 6768)
- oqmlsnqgie.exe (PID: 7164)
- jvaiiyqxar.exe (PID: 6876)
- tgslajaijy.exe (PID: 4648)
- wnqlvnqmnd.exe (PID: 6900)
- rzmaljyepm.exe (PID: 3100)
- bhrlhpdvki.exe (PID: 1896)
- dufrbkxwpl.exe (PID: 5008)
- blnbjopyae.exe (PID: 5080)
- lcswokebxt.exe (PID: 2188)
- gbtcqcgajy.exe (PID: 6140)
- raxmcllesu.exe (PID: 3884)
- jhzegthwdl.exe (PID: 4456)
- wnqlvnqmnd.exe (PID: 3000)
- zxusykjcrr.exe (PID: 4832)
- twmxifdwsv.exe (PID: 436)
- blnbjopyae.exe (PID: 5904)
- ymkxptuztq.exe (PID: 3196)
- gbtcqcgajy.exe (PID: 756)
- dufrbkxwpl.exe (PID: 5340)
- jhzegthwdl.exe (PID: 2604)
- lscfpjcuna.exe (PID: 6420)
- twmxifdwsv.exe (PID: 2128)
- gqukzmwogn.exe (PID: 4664)
- zxusykjcrr.exe (PID: 3888)
- qefsubfuci.exe (PID: 6160)
- rmwiagddow.exe (PID: 1948)
- gqukzmwogn.exe (PID: 4688)
- wdaiojqtys.exe (PID: 5808)
- ymkxptuztq.exe (PID: 3588)
- yfdtihipds.exe (PID: 3900)
- iitjwzywsl.exe (PID: 4216)
- rmwiagddow.exe (PID: 4196)
- qefsubfuci.exe (PID: 888)
- aiuihkubsb.exe (PID: 5476)
- lscfpjcuna.exe (PID: 7128)
- yfdtihipds.exe (PID: 472)
- wdaiojqtys.exe (PID: 4984)
- ycawduexvv.exe (PID: 424)
- nkbleeecaz.exe (PID: 6320)
- qjtwonabvl.exe (PID: 6936)
- aiuihkubsb.exe (PID: 3748)
- burmvqmvcd.exe (PID: 3936)
- iitjwzywsl.exe (PID: 1068)
- epukheoxkc.exe (PID: 1480)
- qjtwonabvl.exe (PID: 6956)
- dekpzurlmb.exe (PID: 3976)
- ycawduexvv.exe (PID: 6808)
- jbpxmnqwzk.exe (PID: 1472)
- nkbleeecaz.exe (PID: 7072)
- ookkjeawnj.exe (PID: 1352)
- epukheoxkc.exe (PID: 3584)
- lxsahnfxsw.exe (PID: 3048)
- burmvqmvcd.exe (PID: 5124)
- vsuxbqdmig.exe (PID: 480)
- dekpzurlmb.exe (PID: 7124)
- yklntmlkpf.exe (PID: 3688)
- fgwakxwacc.exe (PID: 6148)
- jbpxmnqwzk.exe (PID: 3760)
- lxsahnfxsw.exe (PID: 5172)
- vatbfswjlw.exe (PID: 1096)
- ookkjeawnj.exe (PID: 6684)
- osyaldmzdm.exe (PID: 3948)
- dbsbmzaely.exe (PID: 2632)
- vsuxbqdmig.exe (PID: 4916)
- otiyrxchmw.exe (PID: 6304)
- yklntmlkpf.exe (PID: 2520)
- qzwjgpddgr.exe (PID: 1816)
- fgwakxwacc.exe (PID: 4052)
- veirzrilbr.exe (PID: 7056)
- osyaldmzdm.exe (PID: 1440)
- anymqwnrin.exe (PID: 6004)
- vatbfswjlw.exe (PID: 1984)
- dbsbmzaely.exe (PID: 7048)
- icmzuytkwc.exe (PID: 3108)
- otiyrxchmw.exe (PID: 3876)
- dtfcrnunxy.exe (PID: 756)
- qzwjgpddgr.exe (PID: 1880)
- veirzrilbr.exe (PID: 4708)
- didhiexbrx.exe (PID: 5116)
- igipwfemmf.exe (PID: 6368)
- anymqwnrin.exe (PID: 1204)
- oqqkmckstt.exe (PID: 3704)
- yagprsevur.exe (PID: 4860)
- icmzuytkwc.exe (PID: 4832)
- dqdkngqybn.exe (PID: 4804)
- dtfcrnunxy.exe (PID: 2168)
- lnyxrjvrpk.exe (PID: 5992)
- didhiexbrx.exe (PID: 4664)
- ilvfekuckl.exe (PID: 4544)
- igipwfemmf.exe (PID: 5352)
- oqqkmckstt.exe (PID: 2220)
- qeuglzyxku.exe (PID: 2580)
- yagprsevur.exe (PID: 5716)
- nfmtpckzys.exe (PID: 6348)
- dqdkngqybn.exe (PID: 2460)
- tzyozzciyg.exe (PID: 6936)
- lnyxrjvrpk.exe (PID: 6172)
- vfmypqlmta.exe (PID: 6536)
- ilvfekuckl.exe (PID: 504)
- bdjgurlxob.exe (PID: 3748)
- qeuglzyxku.exe (PID: 7052)
- dvjennsvvj.exe (PID: 1068)
- nfmtpckzys.exe (PID: 5244)
- dczjewwkwh.exe (PID: 5564)
- tzyozzciyg.exe (PID: 3924)
- ilpeubbqwv.exe (PID: 5552)
- qbcrgehjss.exe (PID: 1472)
- yfnepxjyep.exe (PID: 4844)
- bdjgurlxob.exe (PID: 424)
- ddkmdqjkap.exe (PID: 3852)
- dvjennsvvj.exe (PID: 3936)
- ipduwavsmy.exe (PID: 3112)
- dczjewwkwh.exe (PID: 1480)
- qicudgrnui.exe (PID: 4048)
- ilpeubbqwv.exe (PID: 3976)
- xmmauzcdhx.exe (PID: 2972)
- qbcrgehjss.exe (PID: 3640)
- fjavyczwdu.exe (PID: 2468)
- ngkaqvcmqr.exe (PID: 6868)
- vkunzgncco.exe (PID: 6140)
- yfnepxjyep.exe (PID: 3048)
- ddkmdqjkap.exe (PID: 1352)
- ipduwavsmy.exe (PID: 480)
- gyzgjsicrr.exe (PID: 6192)
- qicudgrnui.exe (PID: 4560)
- vfmypqlmta.exe (PID: 4984)
- xmmauzcdhx.exe (PID: 6260)
- sergjiqylj.exe (PID: 6492)
- fjavyczwdu.exe (PID: 6772)
- ngkaqvcmqr.exe (PID: 3768)
- imbiesodkl.exe (PID: 5600)
- vkunzgncco.exe (PID: 1688)
- yniolnudov.exe (PID: 6212)
- gyzgjsicrr.exe (PID: 7164)
- dscwexhlie.exe (PID: 4676)
- xfzjzowmtx.exe (PID: 316)
- imbiesodkl.exe (PID: 3668)
- imorhuzuqa.exe (PID: 2356)
- sergjiqylj.exe (PID: 3628)
- ndsmdakxxo.exe (PID: 2800)
- qckwnroesa.exe (PID: 3740)
- xfzjzowmtx.exe (PID: 5904)
- yvjwtykssk.exe (PID: 7068)
- yniolnudov.exe (PID: 3196)
- imorhuzuqa.exe (PID: 4692)
- nhhcfgeznr.exe (PID: 188)
- fhqpqgcrhq.exe (PID: 4060)
- dscwexhlie.exe (PID: 2296)
- fztkljvhfh.exe (PID: 6532)
- nlauarehuf.exe (PID: 4824)
- qckwnroesa.exe (PID: 4684)
- yvjwtykssk.exe (PID: 1164)
- ndsmdakxxo.exe (PID: 2128)
- xvqkhcqbjw.exe (PID: 2708)
- fztkljvhfh.exe (PID: 7080)
- nhhcfgeznr.exe (PID: 3632)
- suipqwkvca.exe (PID: 4768)
- fhqpqgcrhq.exe (PID: 4216)
- flefkentxl.exe (PID: 7128)
- kxyfeoacru.exe (PID: 2680)
- suipqwkvca.exe (PID: 3736)
- zgtlqslzue.exe (PID: 3576)
- nlauarehuf.exe (PID: 1328)
- kjkgssxoyf.exe (PID: 6836)
- vtadxiyrzd.exe (PID: 5644)
- kbudgmmwhp.exe (PID: 5496)
- xvqkhcqbjw.exe (PID: 1800)
- flefkentxl.exe (PID: 4224)
- scujybnjkx.exe (PID: 2144)
- kjkgssxoyf.exe (PID: 2976)
- zkpbsqxbjh.exe (PID: 5952)
- snwehtkviz.exe (PID: 3716)
- kxyfeoacru.exe (PID: 4444)
- fimryrwffq.exe (PID: 5628)
- zgtlqslzue.exe (PID: 5252)
- pdncnmxkst.exe (PID: 4080)
- kbudgmmwhp.exe (PID: 6620)
- vtadxiyrzd.exe (PID: 3960)
- vxzeqjxttp.exe (PID: 6892)
- snwehtkviz.exe (PID: 6876)
- ahpzgodzal.exe (PID: 6512)
- scujybnjkx.exe (PID: 1056)
- zkpbsqxbjh.exe (PID: 2808)
- crhpzklxhk.exe (PID: 6192)
- fimryrwffq.exe (PID: 5744)
- kguckmiqdh.exe (PID: 3100)
- vxzeqjxttp.exe (PID: 3504)
- qtpqpwsqsg.exe (PID: 3768)
- ahpzgodzal.exe (PID: 856)
- szdafouumb.exe (PID: 1688)
- pdncnmxkst.exe (PID: 6776)
- kydvfzshjt.exe (PID: 6840)
- vjvqxkbstb.exe (PID: 7164)
- ckuqeyfgtk.exe (PID: 4648)
- kguckmiqdh.exe (PID: 1440)
- crhpzklxhk.exe (PID: 3972)
- kydvfzshjt.exe (PID: 6540)
- kctqsfjbcm.exe (PID: 5904)
- qtpqpwsqsg.exe (PID: 5724)
- mywtnfquvh.exe (PID: 4764)
- szdafouumb.exe (PID: 316)
- ppvdxpubqt.exe (PID: 756)
- swcoegvxlo.exe (PID: 4196)
- ckuqeyfgtk.exe (PID: 4708)
- vjvqxkbstb.exe (PID: 2520)
- swcggbfnra.exe (PID: 1356)
- kctqsfjbcm.exe (PID: 3888)
- xuhomuezma.exe (PID: 6360)
- xyscdnppzx.exe (PID: 620)
- ppvdxpubqt.exe (PID: 3880)
- fnfphpmimu.exe (PID: 2620)
- hxxezmugbu.exe (PID: 7128)
- mywtnfquvh.exe (PID: 3740)
- swcggbfnra.exe (PID: 1488)
- kdlppdvkwg.exe (PID: 2680)
- xuhomuezma.exe (PID: 5716)
- swcoegvxlo.exe (PID: 3000)
- ngonbrxdeo.exe (PID: 6836)
- xyscdnppzx.exe (PID: 2864)
- ulystkabql.exe (PID: 5808)
- fnfphpmimu.exe (PID: 7080)
- aivigdhflm.exe (PID: 6936)
- zbwsaxrvsx.exe (PID: 892)
- kdlppdvkwg.exe (PID: 7052)
- ezbiozqhng.exe (PID: 6320)
- hxxezmugbu.exe (PID: 4796)
- mdlnxktxav.exe (PID: 1128)
- ngonbrxdeo.exe (PID: 5244)
- ulystkabql.exe (PID: 1752)
- upovgirnbf.exe (PID: 2648)
- aivigdhflm.exe (PID: 1700)
- fzmlftdhqo.exe (PID: 1704)
- zbwsaxrvsx.exe (PID: 6676)
- aqeqpnxbia.exe (PID: 5504)
- mhadzimzpy.exe (PID: 6704)
- ezbiozqhng.exe (PID: 6520)
- mdlnxktxav.exe (PID: 7124)
- pkdbmvhaxy.exe (PID: 5620)
- pkeoydmsae.exe (PID: 6900)
- aqeqpnxbia.exe (PID: 6408)
- sqsrnvnour.exe (PID: 5528)
- fzmlftdhqo.exe (PID: 5416)
- upovgirnbf.exe (PID: 5168)
- cmtkvpotic.exe (PID: 6732)
- mhadzimzpy.exe (PID: 4844)
- jiehgnjsjk.exe (PID: 3972)
- ezwmqqdmbo.exe (PID: 6216)
- ubunlldvki.exe (PID: 6652)
- pkeoydmsae.exe (PID: 1208)
- cxescwokxx.exe (PID: 5080)
- sqsrnvnour.exe (PID: 6840)
- pkdbmvhaxy.exe (PID: 6680)
- nlikeijtli.exe (PID: 1576)
- cmtkvpotic.exe (PID: 7104)
- rcffawuwse.exe (PID: 1564)
- ezwmqqdmbo.exe (PID: 6940)
- xwzadlvfss.exe (PID: 2760)
- jiehgnjsjk.exe (PID: 2764)
- cueqrmuqna.exe (PID: 4476)
- cxescwokxx.exe (PID: 5424)
- kygvifwgax.exe (PID: 2380)
- nlikeijtli.exe (PID: 2072)
- ubunlldvki.exe (PID: 7164)
- rcffawuwse.exe (PID: 3944)
- rgcbgueqcg.exe (PID: 4060)
- zgbbvjhddi.exe (PID: 3788)
- xwzadlvfss.exe (PID: 5988)
- miftabeehx.exe (PID: 6420)
- cnqlkbrhxc.exe (PID: 4684)
- wxhbcxzfmc.exe (PID: 6360)
- kygvifwgax.exe (PID: 316)
- cueqrmuqna.exe (PID: 4760)
- emvogzwyaz.exe (PID: 3884)
- rgcbgueqcg.exe (PID: 3092)
- jzowzjagua.exe (PID: 5284)
- miftabeehx.exe (PID: 2348)
- jomcqrmvny.exe (PID: 7128)
- cnqlkbrhxc.exe (PID: 4156)
- oljjeslgjh.exe (PID: 3148)
- wxhbcxzfmc.exe (PID: 2064)
- zgbbvjhddi.exe (PID: 4832)
- emvogzwyaz.exe (PID: 2168)
- jzowzjagua.exe (PID: 5924)
- uvasgxoelb.exe (PID: 6172)
- plsxqaiydf.exe (PID: 2228)
- ccxxmuvnnj.exe (PID: 892)
- oljjeslgjh.exe (PID: 2580)
- cnzsnmszld.exe (PID: 6936)
- jomcqrmvny.exe (PID: 4544)
- plsxqaiydf.exe (PID: 3780)
- wfdtpnjcvr.exe (PID: 7140)
- uvasgxoelb.exe (PID: 536)
- jhzdvfgday.exe (PID: 6320)
- pbtfgcgmiu.exe (PID: 6236)
- wyedrittbc.exe (PID: 4680)
- zesozauxvp.exe (PID: 6868)
- cnzsnmszld.exe (PID: 4224)
- ccxxmuvnnj.exe (PID: 4796)
- jhzdvfgday.exe (PID: 3112)
- pbtfgcgmiu.exe (PID: 5244)
- hxrongykez.exe (PID: 6140)
- mjmbsqiktg.exe (PID: 1136)
- wyedrittbc.exe (PID: 1700)
- mrljydytem.exe (PID: 7124)
- wfdtpnjcvr.exe (PID: 1752)
- zesozauxvp.exe (PID: 6892)
- mkwzykqsbq.exe (PID: 360)
- hxrongykez.exe (PID: 1216)
- tduzmzuoca.exe (PID: 5460)
- mvyuhcnear.exe (PID: 5628)
- zmdudwatjo.exe (PID: 2876)
- hbqhhhxmxk.exe (PID: 4456)
- mjmbsqiktg.exe (PID: 7028)
- mrljydytem.exe (PID: 2144)
- mvyuhcnear.exe (PID: 3640)
- jlqxzdflek.exe (PID: 2120)
- mkwzykqsbq.exe (PID: 6356)
- ojnnmwewzt.exe (PID: 2632)
- zmdudwatjo.exe (PID: 4052)
- zqaqicjnup.exe (PID: 3876)
- tduzmzuoca.exe (PID: 1096)
- rpbpcwnstf.exe (PID: 5340)
- hbqhhhxmxk.exe (PID: 1080)
- hulimvrvjl.exe (PID: 5020)
- basnbyrmbp.exe (PID: 4676)
The sample compiled with chinese language support
- hnpnhroogk.exe (PID: 504)
- 2025-06-21_cfa2253cf9e3a2e9a9ae6d4a84aef344_amadey_elex_smoke-loader_stop.exe (PID: 4968)
- rrsgzjxrfn.exe (PID: 1180)
- gkyzvwxhgh.exe (PID: 5744)
- jrejkwgdat.exe (PID: 6656)
- rgsxwydwwq.exe (PID: 5628)
- zhzxcfhswa.exe (PID: 2696)
- emkfwpmsqb.exe (PID: 1700)
- mjgszzjley.exe (PID: 6160)
- opmdprspyk.exe (PID: 5908)
- wlwigcvflh.exe (PID: 3948)
- ydofyycdsh.exe (PID: 6232)
- zsnqboljom.exe (PID: 5348)
- jkcwgefmpk.exe (PID: 2664)
- rsyoaupexm.exe (PID: 3956)
- ywibsfzukj.exe (PID: 2120)
- gphtyuvhkt.exe (PID: 4684)
- gpihktbhmr.exe (PID: 1800)
- ghjreolptd.exe (PID: 6292)
- rwvjoagyho.exe (PID: 1096)
- bkcioqehuc.exe (PID: 2808)
- guujhzlfiy.exe (PID: 1212)
- oqexyswvvv.exe (PID: 1036)
- twjfetvgqw.exe (PID: 4080)
- boifsaztqg.exe (PID: 1068)
- lgykxqbwre.exe (PID: 7072)
- ouansqhplq.exe (PID: 1512)
- wndvbwgnua.exe (PID: 1896)
- yxcltsomba.exe (PID: 1080)
- jtvvbnojol.exe (PID: 6228)
- tsjgxluajh.exe (PID: 7140)
- oypduptrju.exe (PID: 1520)
- bthgmsywjr.exe (PID: 4960)
- wkbjjpzqtn.exe (PID: 3148)
- bxvjurmzfo.exe (PID: 6900)
- bahjjdqsui.exe (PID: 2380)
- bmtcfhumbt.exe (PID: 1328)
- bpgutlzyie.exe (PID: 4684)
- jtqzdebwdb.exe (PID: 6256)
- ornpqfbaqc.exe (PID: 6292)
- tadkhcgoyy.exe (PID: 5244)
- btcknrkbga.exe (PID: 3960)
- ggwshtpjsj.exe (PID: 1036)
- qylqljrmth.exe (PID: 4764)
- vdfxftwunh.exe (PID: 2764)
- bjcnsudyiq.exe (PID: 3092)
- gkkijrbmie.exe (PID: 6320)
- ozgvmcgeeb.exe (PID: 1728)
- qgmycthayv.exe (PID: 4576)
- tnzjgamsts.exe (PID: 2632)
- qynqwgrreh.exe (PID: 1652)
- vxrzyouqar.exe (PID: 4760)
- buopeptbva.exe (PID: 6160)
- izyuvierip.exe (PID: 2520)
- lbbrivgtpx.exe (PID: 3108)
- npeudwntjj.exe (PID: 6732)
- qshspjpvrj.exe (PID: 3844)
- vtpnygvbyf.exe (PID: 4684)
- bnjpidwkhs.exe (PID: 5708)
- fenkerzmoo.exe (PID: 6292)
- ihiirfcovo.exe (PID: 5900)
- oenqfgjzix.exe (PID: 728)
- qlubuxkddj.exe (PID: 2536)
- ypftpqslse.exe (PID: 3748)
- wizjazjhys.exe (PID: 2696)
- ahfjhmajze.exe (PID: 4196)
- gfcrvfzuun.exe (PID: 3092)
- guzwmwcjol.exe (PID: 1944)
- idrmeskhvt.exe (PID: 6504)
- dzsqvzsext.exe (PID: 6492)
- ielyojxmjc.exe (PID: 1564)
- linohldjzl.exe (PID: 4172)
- fyftrfyvsx.exe (PID: 6896)
- smzgkwmrhg.exe (PID: 4708)
- kpdtythytj.exe (PID: 4920)
- dlergcrijd.exe (PID: 1520)
- vwqecsmpog.exe (PID: 6228)
- iuumxhxojz.exe (PID: 6732)
- ktbhgmiisx.exe (PID: 4960)
- inveruhexk.exe (PID: 2292)
- qnvkrjiras.exe (PID: 6652)
- yvsqpypbub.exe (PID: 6140)
- vpdfhgoxag.exe (PID: 7000)
- cilpihuboc.exe (PID: 4544)
- pksknuedwz.exe (PID: 5808)
- igifvibnjk.exe (PID: 5496)
- vemnqqemfv.exe (PID: 4984)
- argbuagltc.exe (PID: 7072)
- afuigwkzej.exe (PID: 2708)
- ayegmqrinb.exe (PID: 5552)
- febwzjrlib.exe (PID: 6684)
- kfjrqpxzqx.exe (PID: 1488)
- qgsmgucfpl.exe (PID: 3100)
- scdunupxle.exe (PID: 3048)
- qseevyhzee.exe (PID: 1932)
- snqmbgtrsp.exe (PID: 4324)
- fmmcvowqoa.exe (PID: 2792)
- xlncpzsvny.exe (PID: 1688)
- kqfkpqbyij.exe (PID: 6536)
- psmfmclaqg.exe (PID: 5172)
- qlzfzmbhqw.exe (PID: 4880)
- szbibtmvkb.exe (PID: 5528)
- xxyypvlhfc.exe (PID: 1352)
- admbemudao.exe (PID: 3884)
- fjjqsntonx.exe (PID: 2520)
- nftwbyeeiu.exe (PID: 5232)
- vgswqnaziw.exe (PID: 2380)
- xfhrzstmqc.exe (PID: 3888)
- ckcjzylpdt.exe (PID: 5012)
- czbucolvry.exe (PID: 4684)
- cozzbxwjtw.exe (PID: 4804)
- ksbekqzhfl.exe (PID: 6180)
- xjfufycgbe.exe (PID: 2552)
- myppahidag.exe (PID: 4216)
- csnpvdimis.exe (PID: 1136)
- klmqkkmhjb.exe (PID: 4764)
- spwvtvpxey.exe (PID: 3936)
- xcrqyezxsy.exe (PID: 3732)
- vszsgirzly.exe (PID: 2276)
- cwkljbzgtt.exe (PID: 5444)
- ngbjhmlsid.exe (PID: 6336)
- hjetcleonu.exe (PID: 6852)
- pnplxdmvcp.exe (PID: 3160)
- xypegxaarl.exe (PID: 7116)
- uoxgnbsbcl.exe (PID: 7048)
- chfzwcynrh.exe (PID: 1352)
- ifduvddigo.exe (PID: 5168)
- fkawjqbpyg.exe (PID: 1720)
- nolpeijwob.exe (PID: 2148)
- cespfpwdpm.exe (PID: 6732)
- hnbkvnujwi.exe (PID: 5556)
- upqfshekef.exe (PID: 1164)
- miunykusxv.exe (PID: 3852)
- cbsftfcbgp.exe (PID: 2468)
- elsdlbkzmp.exe (PID: 6940)
- honbyombuo.exe (PID: 4544)
- epfgcaykim.exe (PID: 4832)
- esrgqevepf.exe (PID: 3608)
- cxrtbyvmec.exe (PID: 1180)
- fefeqpeiyp.exe (PID: 6680)
- ujoropltmo.exe (PID: 2116)
- miprhbhflm.exe (PID: 6756)
- zhlzcqkehw.exe (PID: 3908)
- fitusoqkok.exe (PID: 4172)
- ppgfouvbjh.exe (PID: 3976)
- miauzdufpu.exe (PID: 1480)
- uqpaeabhrc.exe (PID: 5952)
- rowaxzowsn.exe (PID: 6620)
- uukdnqpsmz.exe (PID: 2880)
- zowgynqbmv.exe (PID: 2972)
- efaaubbltj.exe (PID: 1720)
- muooxeyepg.exe (PID: 5172)
- uvnomscspq.exe (PID: 1132)
- cnuotzynqa.exe (PID: 6732)
- hafomjlvka.exe (PID: 6768)
- mbwrcgrbrw.exe (PID: 2536)
- rztzqhqnex.exe (PID: 5708)
- zarzxouanh.exe (PID: 7120)
- wnlhqyzihq.exe (PID: 6292)
- jpscnkjjpn.exe (PID: 1208)
- htpzskujnt.exe (PID: 3668)
- reopzugcdc.exe (PID: 5496)
- zxoazouhry.exe (PID: 188)
- wclxeofgyl.exe (PID: 620)
- erhdkluqst.exe (PID: 724)
- ogjfusfetq.exe (PID: 6936)
- mkgdzzqlad.exe (PID: 5372)
- wyigahjzua.exe (PID: 3640)
- cscildbicn.exe (PID: 6852)
- rxlojvqtpu.exe (PID: 3160)
- jxmouomypk.exe (PID: 4864)
- ueryyvrpsh.exe (PID: 5952)
- wororrznzh.exe (PID: 3504)
- edebutwgmd.exe (PID: 856)
- rfmwzfgiub.exe (PID: 6492)
- mhpomezwza.exe (PID: 5620)
- zgkxgucdvl.exe (PID: 1700)
- bpkuyikbct.exe (PID: 4916)
- hrsppoqhjg.exe (PID: 2664)
- wsqhkjxqsa.exe (PID: 2800)
- orrpvctcsq.exe (PID: 4708)
- btykapdwzo.exe (PID: 1164)
- hrdsgichmx.exe (PID: 6140)
- gkelicmybi.exe (PID: 3288)
- okdlojqtbk.exe (PID: 436)
- bmkglvsmjq.exe (PID: 5480)
- wpnqgutjoh.exe (PID: 4808)
- hkpozwzyeq.exe (PID: 7000)
- jrwyooacyl.exe (PID: 1100)
- dbvohkiafl.exe (PID: 188)
- tqibzbjgbj.exe (PID: 1752)
- jkdjxqogng.exe (PID: 1328)
- tjjutotxid.exe (PID: 3520)
- byehfyrqvs.exe (PID: 5504)
- oalcclardx.exe (PID: 6756)
- jzdhmfueec.exe (PID: 6680)
- tjuxsqgxll.exe (PID: 1212)
- dusnrtkrav.exe (PID: 3504)
- zhzfyjfjgu.exe (PID: 3624)
- jvaiiyqxar.exe (PID: 856)
- rzmaljyepm.exe (PID: 5620)
- oqmlsnqgie.exe (PID: 6704)
- tgslajaijy.exe (PID: 5628)
- bhrlhpdvki.exe (PID: 4680)
- blnbjopyae.exe (PID: 5080)
- wnqlvnqmnd.exe (PID: 6900)
- gbtcqcgajy.exe (PID: 6140)
- ymkxptuztq.exe (PID: 3196)
- zxusykjcrr.exe (PID: 4832)
- vfmypqlmta.exe (PID: 6536)
Reads the software policy settings
- slui.exe (PID: 6264)
Checks proxy server information
- slui.exe (PID: 6264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (64.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (13.5) |
| .exe | | | Win32 Executable (generic) (9.3) |
| .exe | | | Win16/32 Executable Delphi generic (4.2) |
| .exe | | | Generic Win/DOS Executable (4.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:07:10 19:51:56+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 1601536 |
| InitializedDataSize: | 585728 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x98caa5 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
| FileDescription: | 易语言程序 |
| ProductName: | 千年3_多开 |
| ProductVersion: | 1.0.0.0 |
| CompanyName: | QQ:6365272 |
| LegalCopyright: | QQ:6365272 |
| Comments: | 本程序使用易语言编写(http://www.eyuyan.com) |
Total processes
899
Monitored processes
766
Malicious processes
121
Suspicious processes
84
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | C:\Users\admin\Desktop\elsdlbkzmp.exe | C:\Users\admin\Desktop\elsdlbkzmp.exe | — | cbsftfcbgp.exe | |||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 188 | C:\Users\admin\Desktop\zxoazouhry.exe update erhdkluqst.exe | C:\Users\admin\Desktop\zxoazouhry.exe | zxoazouhry.exe | ||||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 188 | C:\Users\admin\Desktop\dbvohkiafl.exe update jkdjxqogng.exe | C:\Users\admin\Desktop\dbvohkiafl.exe | dbvohkiafl.exe | ||||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 188 | C:\Users\admin\Desktop\nhhcfgeznr.exe update fhqpqgcrhq.exe | C:\Users\admin\Desktop\nhhcfgeznr.exe | — | nhhcfgeznr.exe | |||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 236 | C:\Users\admin\Desktop\ovtjrgzjvx.exe | C:\Users\admin\Desktop\ovtjrgzjvx.exe | — | ggxwfdcqha.exe | |||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 | |||||||||||||||
| 316 | C:\Users\admin\Desktop\xfzjzowmtx.exe update yniolnudov.exe | C:\Users\admin\Desktop\xfzjzowmtx.exe | — | xfzjzowmtx.exe | |||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 316 | C:\Users\admin\Desktop\szdafouumb.exe | C:\Users\admin\Desktop\szdafouumb.exe | qtpqpwsqsg.exe | ||||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 316 | C:\Users\admin\Desktop\kygvifwgax.exe | C:\Users\admin\Desktop\kygvifwgax.exe | — | cueqrmuqna.exe | |||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 360 | C:\Users\admin\Desktop\mkwzykqsbq.exe update tduzmzuoca.exe | C:\Users\admin\Desktop\mkwzykqsbq.exe | — | mkwzykqsbq.exe | |||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 420 | C:\Users\admin\Desktop\afuigwkzej.exe | C:\Users\admin\Desktop\afuigwkzej.exe | — | vemnqqemfv.exe | |||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
132 243
Read events
132 243
Write events
0
Delete events
0
Modification events
Executable files
210
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4968 | 2025-06-21_cfa2253cf9e3a2e9a9ae6d4a84aef344_amadey_elex_smoke-loader_stop.exe | C:\Users\admin\Desktop\update.exe | executable | |
MD5:914FB249B54113FE0374423A98DAA401 | SHA256:C2E5D45478CF32703EA224DD4644A25C5F16273B65CE9254CD9A03E22C51CFD7 | |||
| 1180 | rrsgzjxrfn.exe | C:\Users\admin\Desktop\gkyzvwxhgh.exe | executable | |
MD5:4F681136AD08CC89517A605BE652D945 | SHA256:32D360760867B8AE5007C51738CE14052BDE90A855CE649CF133DCE2B03EF426 | |||
| 6160 | mjgszzjley.exe | C:\Users\admin\Desktop\opmdprspyk.exe | executable | |
MD5:123A7EDE9E8BE8942C876D481345E4AA | SHA256:01D507AFE0D571550B45EACEB65DB24E04E49BBE6D5033367A8584DEBA7F7D9A | |||
| 504 | hnpnhroogk.exe | C:\Users\admin\Desktop\rrsgzjxrfn.exe | executable | |
MD5:140D0F311F0C243DEAE896C3F2C4CF62 | SHA256:18696A5AC89195257A10E7698AB541D93D92ACA307017C69476BD3DB1FA1ACA9 | |||
| 2696 | zhzxcfhswa.exe | C:\Users\admin\Desktop\emkfwpmsqb.exe | executable | |
MD5:5569E56379469525FF1F7712B8A6D840 | SHA256:E4E7D38672B977F57FC1E3A64619F07EECFA6F4E588AE55CC3056E22F8899E82 | |||
| 5744 | gkyzvwxhgh.exe | C:\Users\admin\Desktop\jrejkwgdat.exe | executable | |
MD5:6BA802343BCE27C5DCC1AD902C5ED34D | SHA256:3B85F2FB5E05BEFFB0E67A67BD970173B0648E00E731D45A57B820AFE372F8F1 | |||
| 6656 | jrejkwgdat.exe | C:\Users\admin\Desktop\rgsxwydwwq.exe | executable | |
MD5:5000D4D0A01DD772FC075B842B04A3A4 | SHA256:E1B5DD0B4FF0BBA1ADF0B9CA87A10930753C9A34D371EE06CBECFA7DEA40B8E0 | |||
| 5628 | rgsxwydwwq.exe | C:\Users\admin\Desktop\zhzxcfhswa.exe | executable | |
MD5:F3881AB69DA67C4678A5EE37A04A5C32 | SHA256:559F6AF6FC691AFE75B966020F8B496103843251FE192EA2EA3630BCA9A65342 | |||
| 5908 | opmdprspyk.exe | C:\Users\admin\Desktop\wlwigcvflh.exe | executable | |
MD5:114DFDB65E1362C76DE731994E713401 | SHA256:CF13B77711B2644B94D6C5E5963930BE761C6BE21285BD7434D7798E22A368F3 | |||
| 6232 | ydofyycdsh.exe | C:\Users\admin\Desktop\bkcioqehuc.exe | executable | |
MD5:8087E92D9159CC236DBB7785AC2EFDA5 | SHA256:D54E110B56B6742E2B909E4B37C1A5DF24D28A8D27F7F68E831E4F5F6C8F483A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
19
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.18.121.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.18.121.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2792 | RUXIMICS.exe | GET | 200 | 2.18.121.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2792 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2792 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.18.121.147:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
2792 | RUXIMICS.exe | 2.18.121.147:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
1268 | svchost.exe | 2.18.121.147:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2792 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |