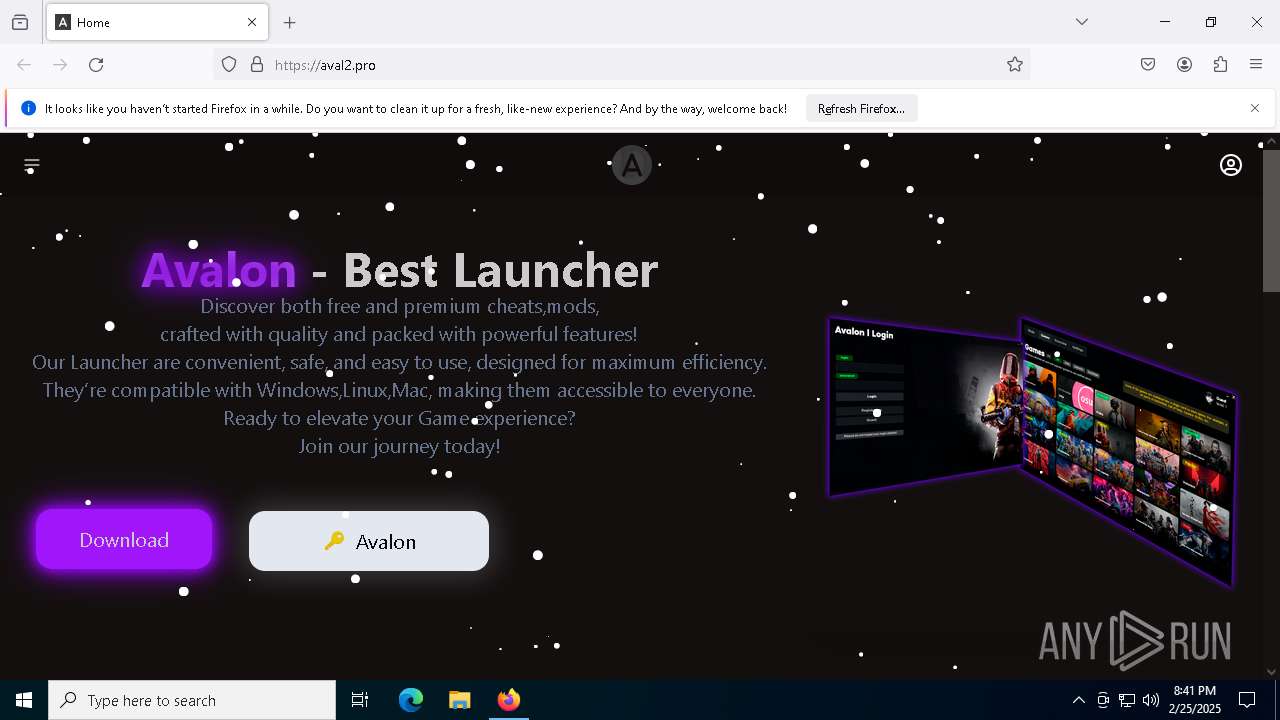
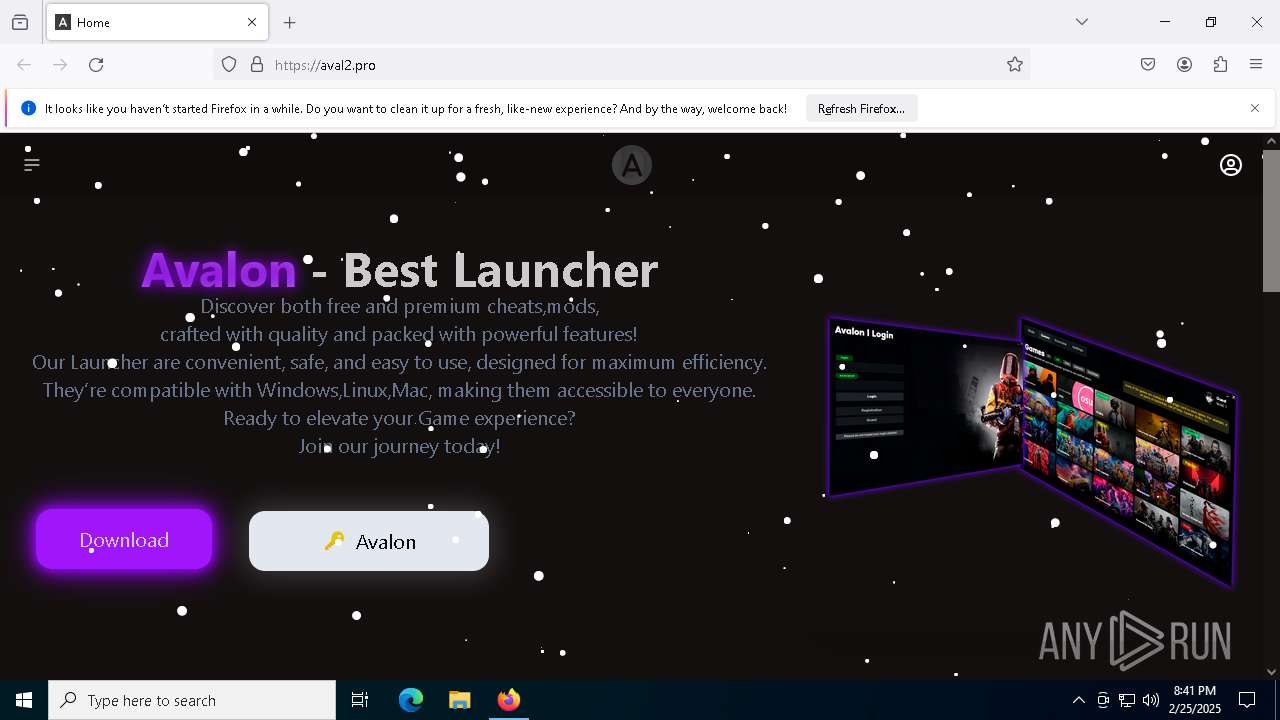
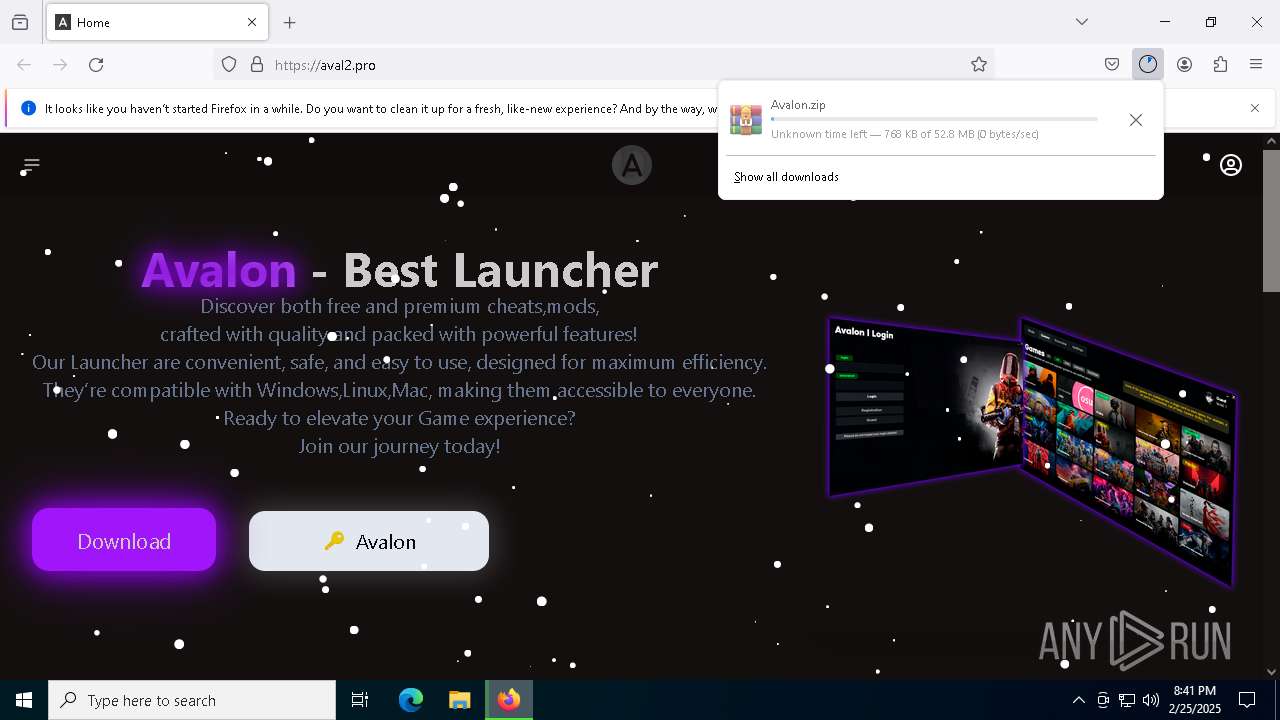
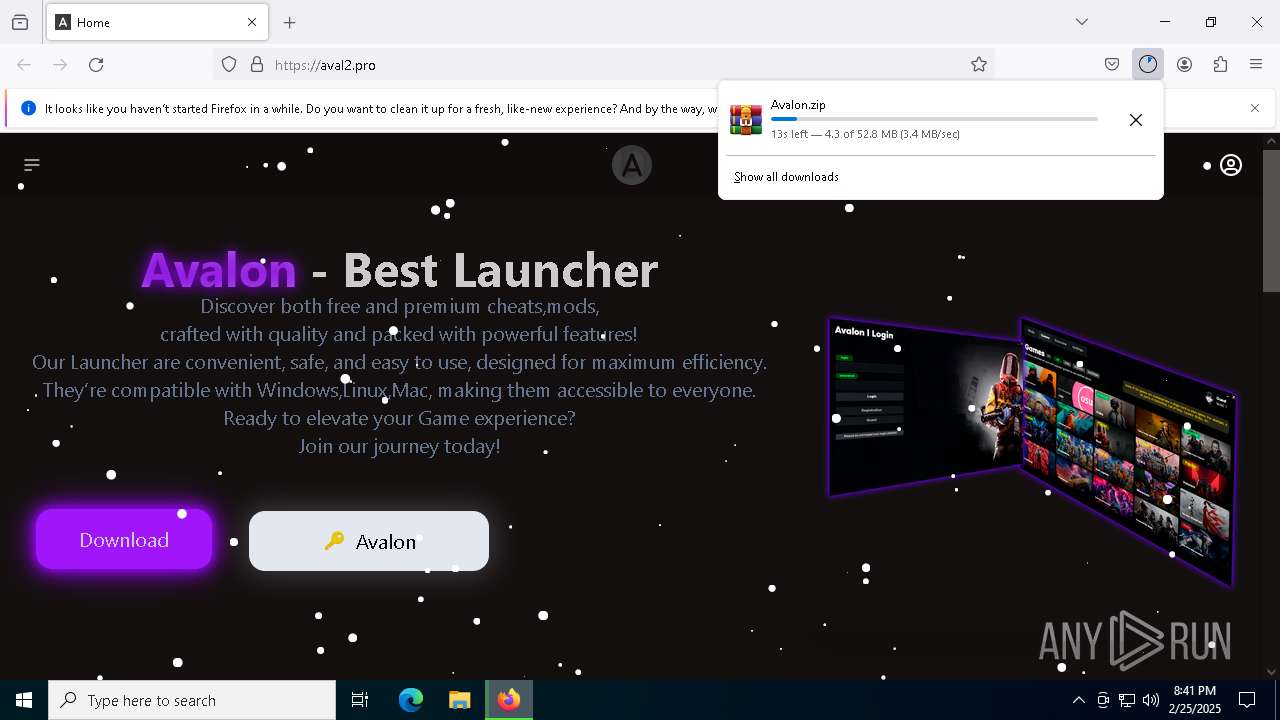
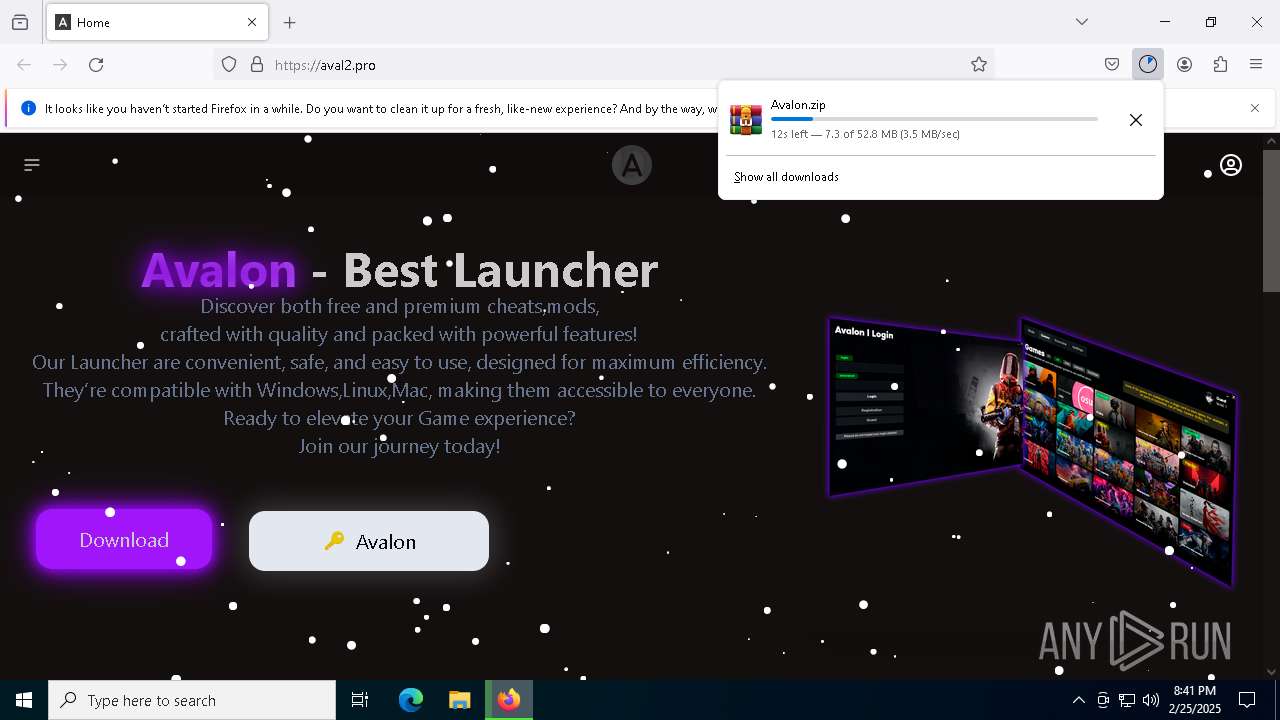
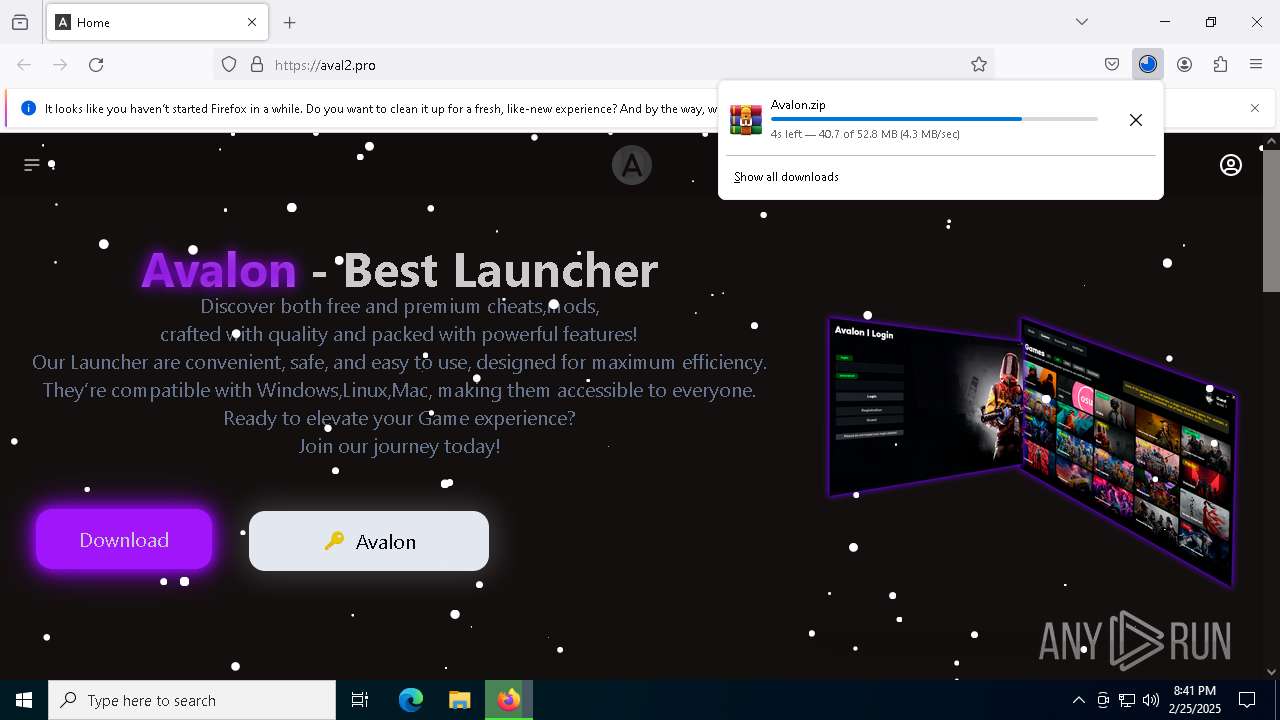
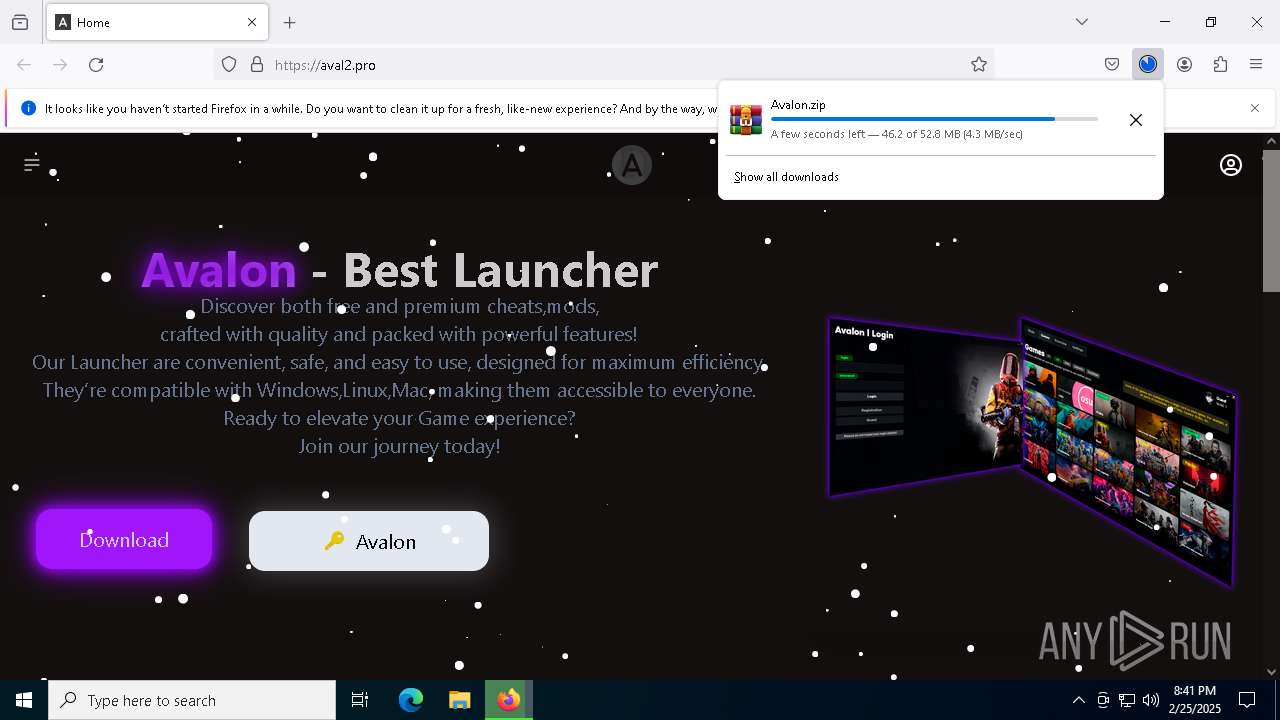
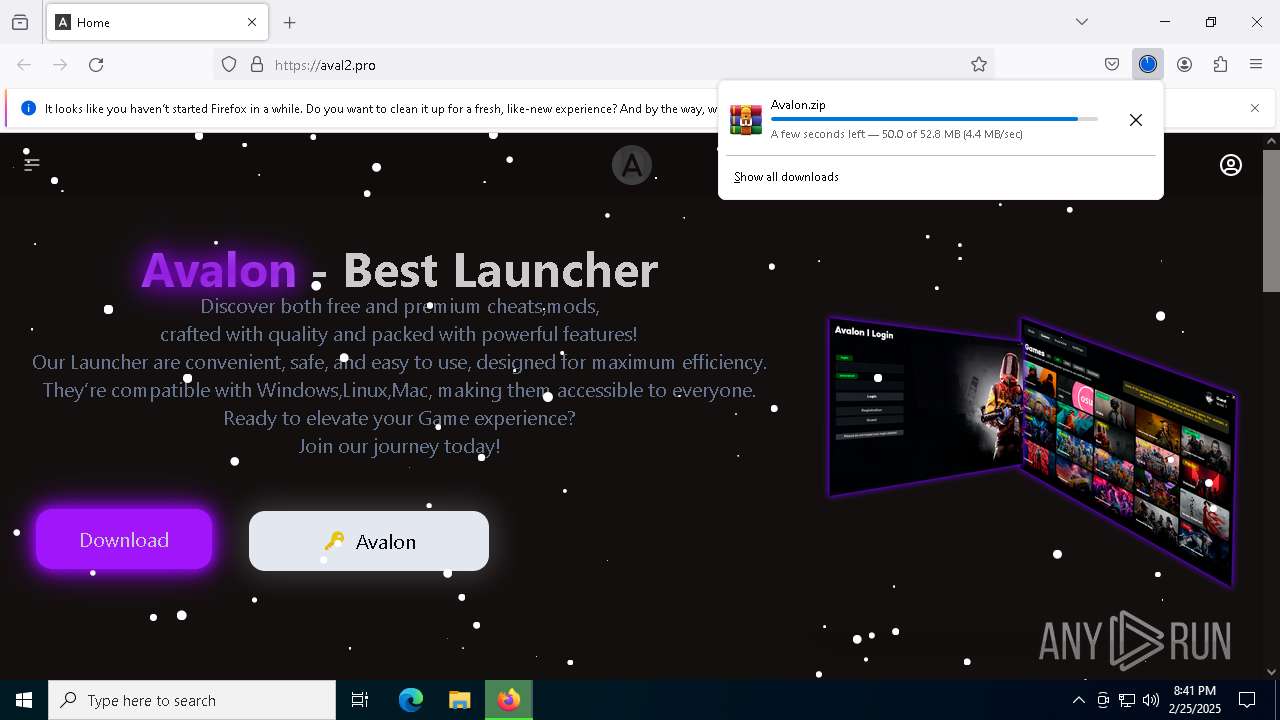
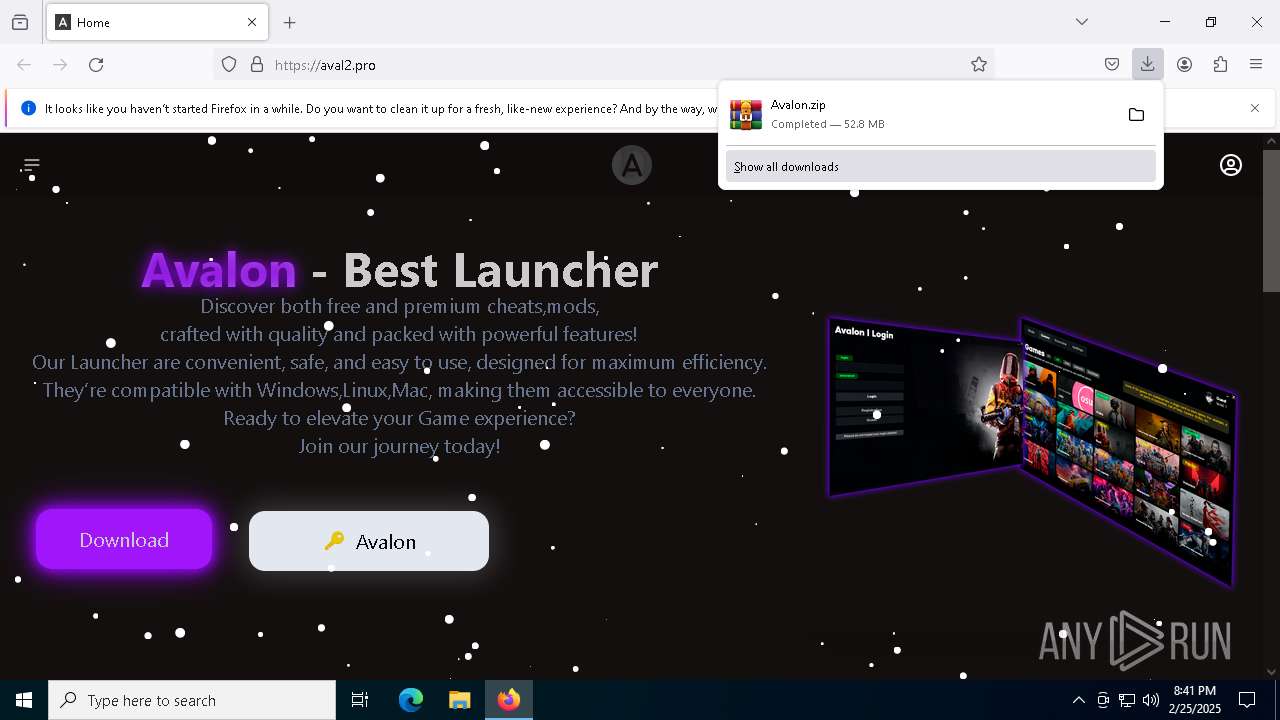
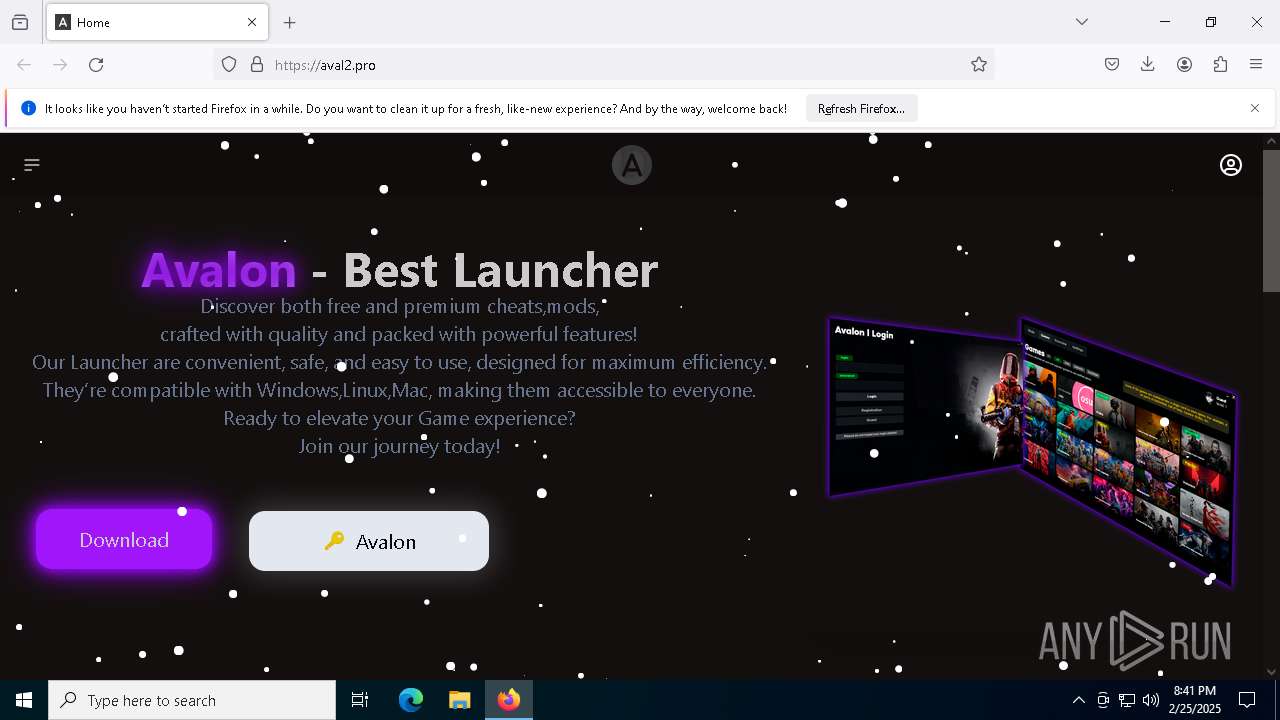
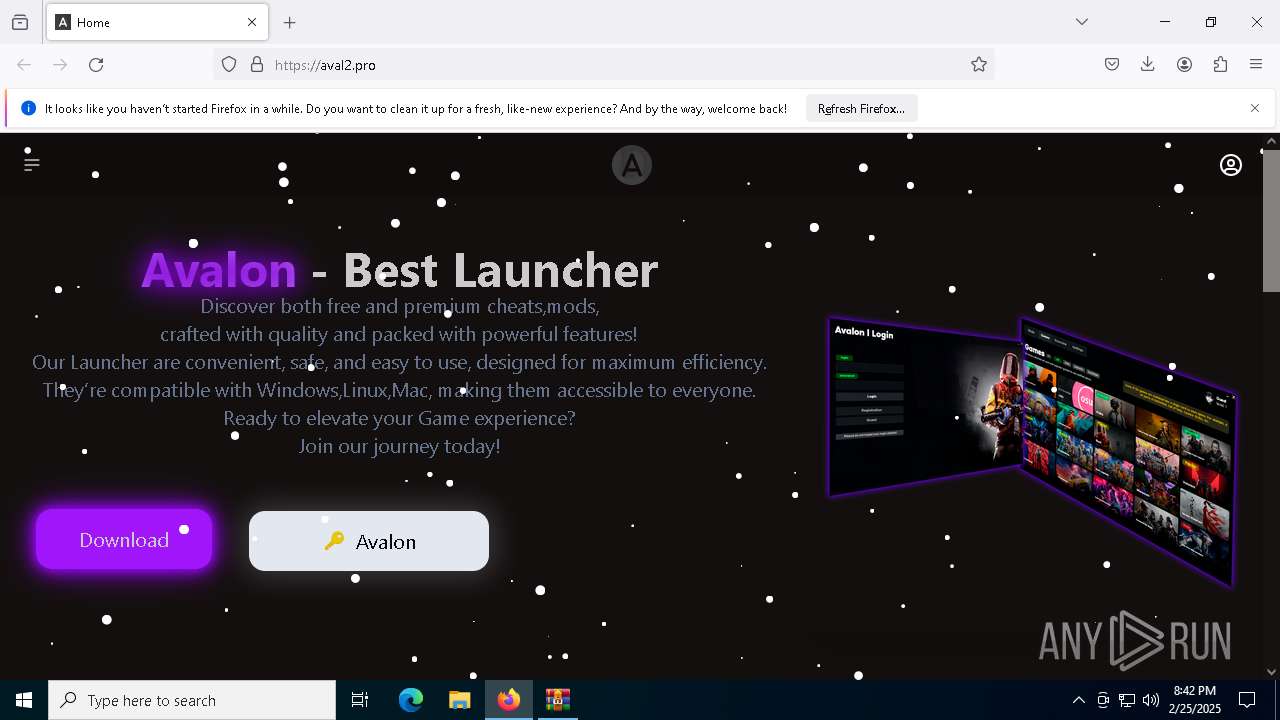
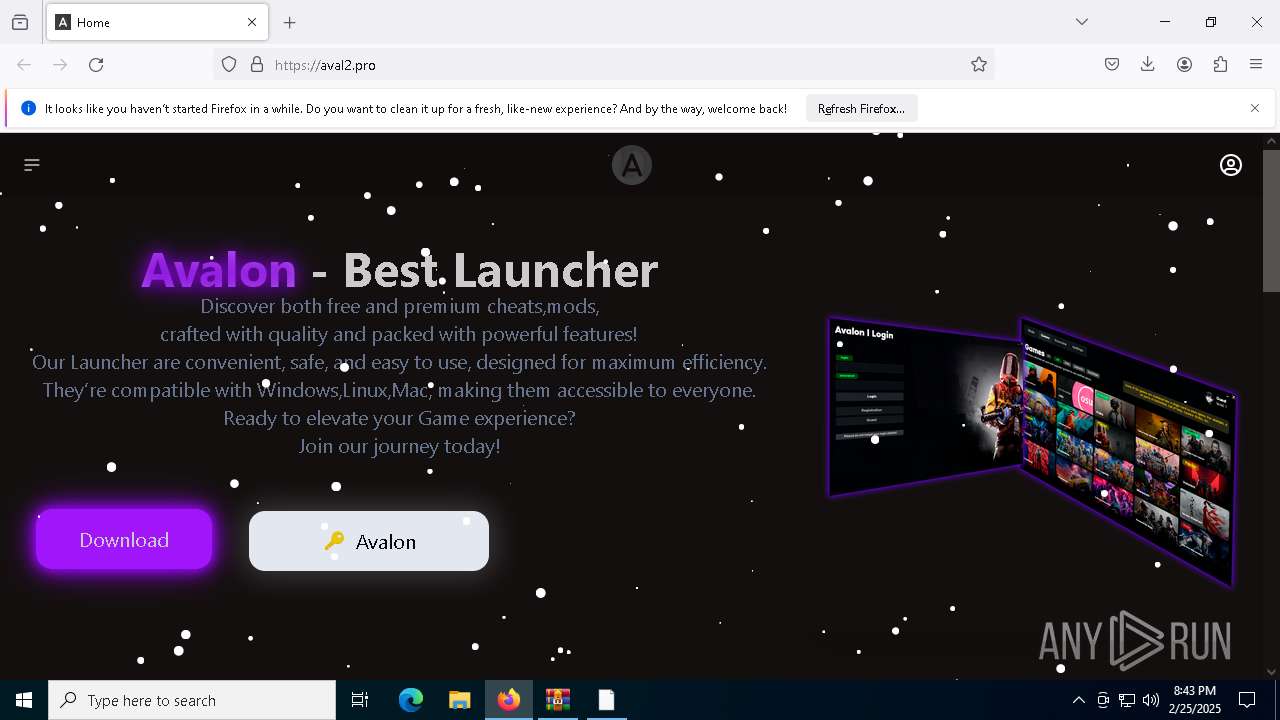
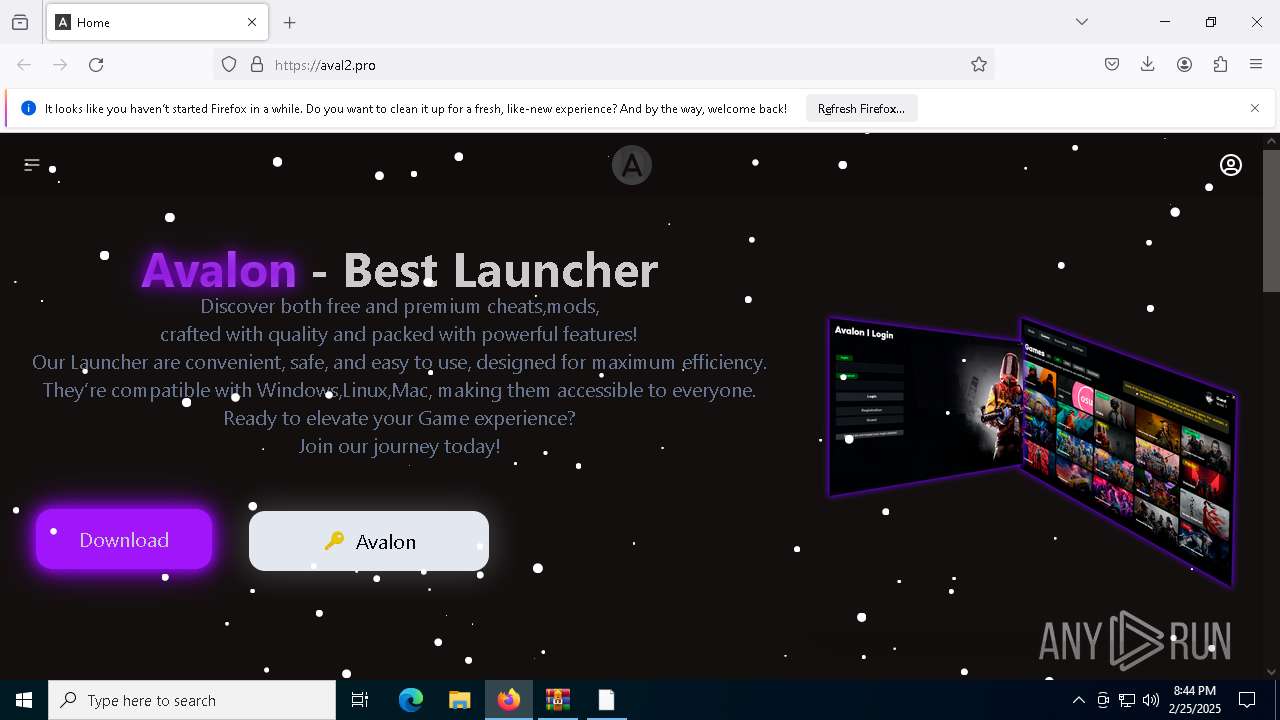
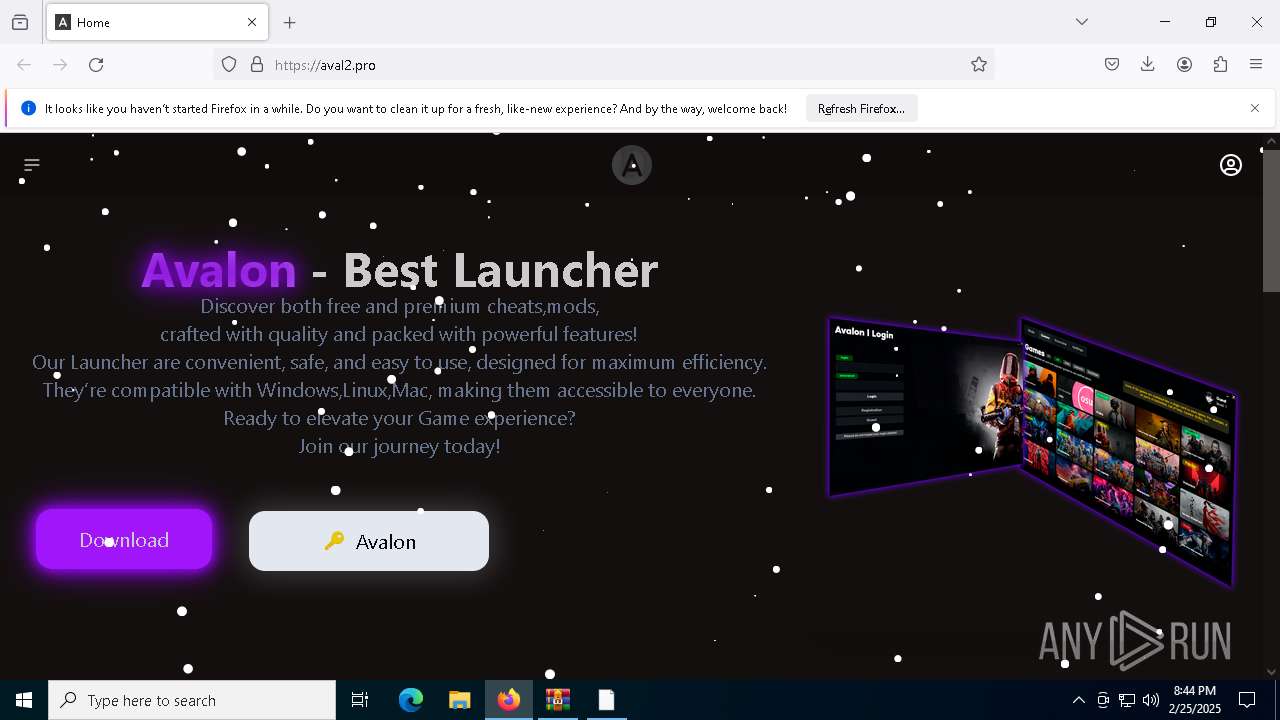
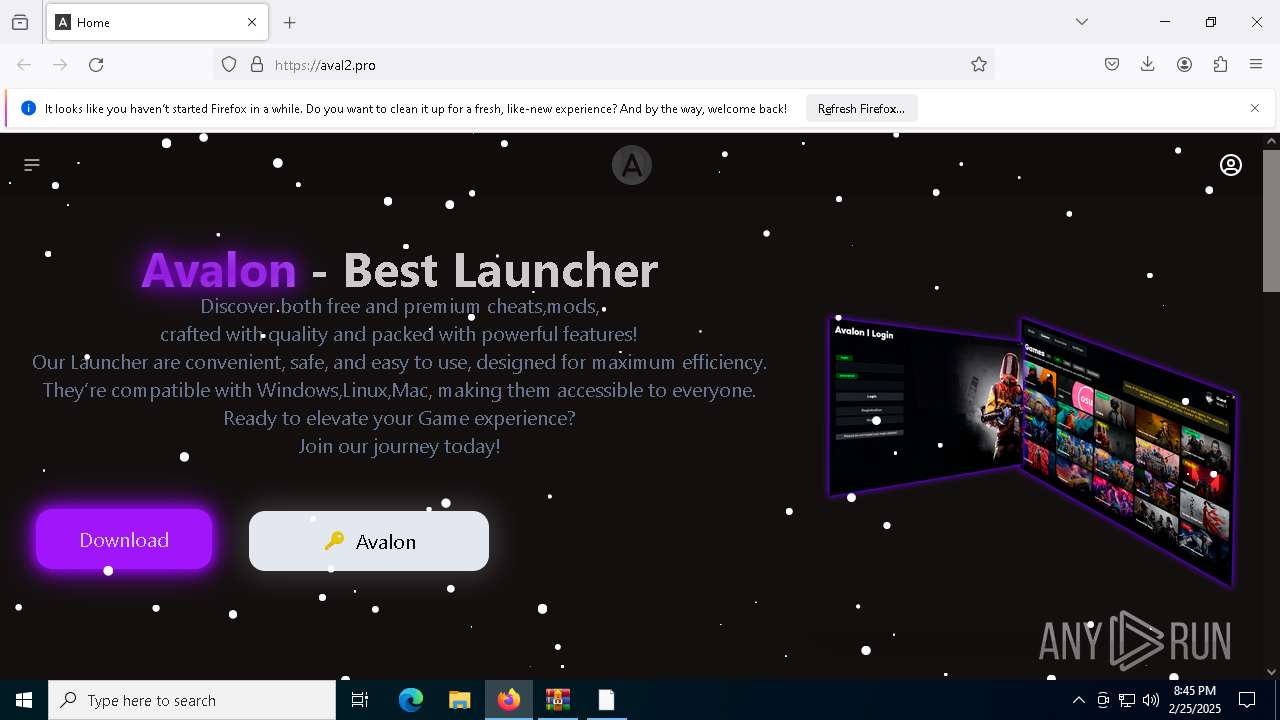
| URL: | https://aval2.pro/ |
| Full analysis: | https://app.any.run/tasks/45707ce3-001e-4c53-a232-0f15ae6014e4 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | February 25, 2025, 20:41:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 90DAD350411C6EA10E03419F0798B1D8 |
| SHA1: | F9FDE955ADF9ECA5789A348348DC58DE45FF4E24 |
| SHA256: | 40A7C1348D3DD67BF75D0AC047D52FCCAB2E633ED3B5723C8C841362F1826BED |
| SSDEEP: | 3:N8b:2b |
MALICIOUS
Steals credentials from Web Browsers
- Slovakia.com (PID: 8144)
Actions looks like stealing of personal data
- Slovakia.com (PID: 8144)
LUMMA mutex has been found
- Slovakia.com (PID: 8144)
SUSPICIOUS
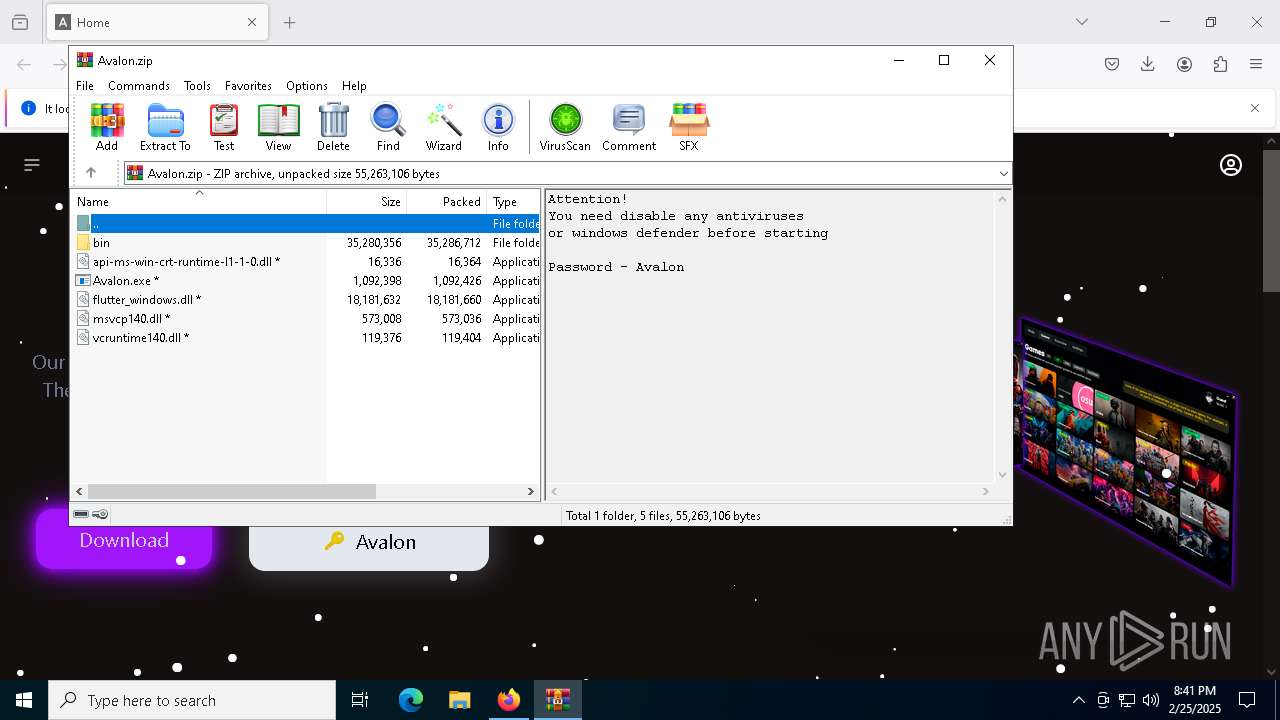
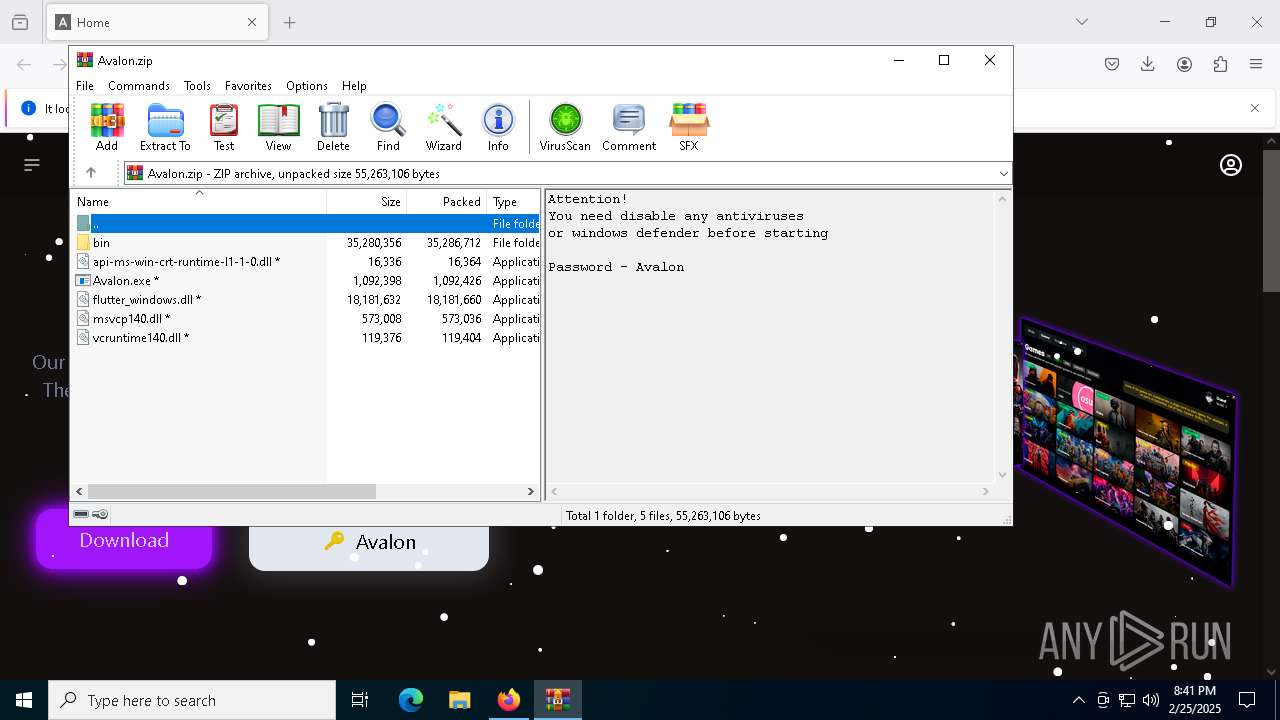
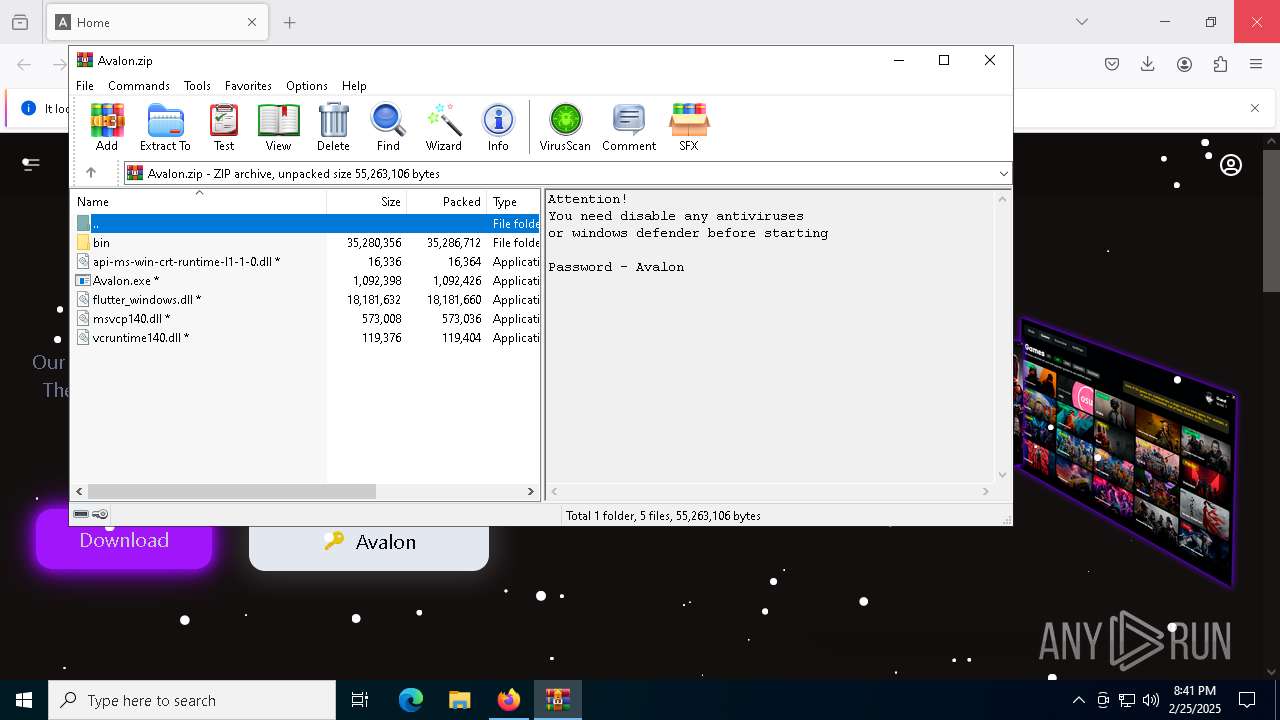
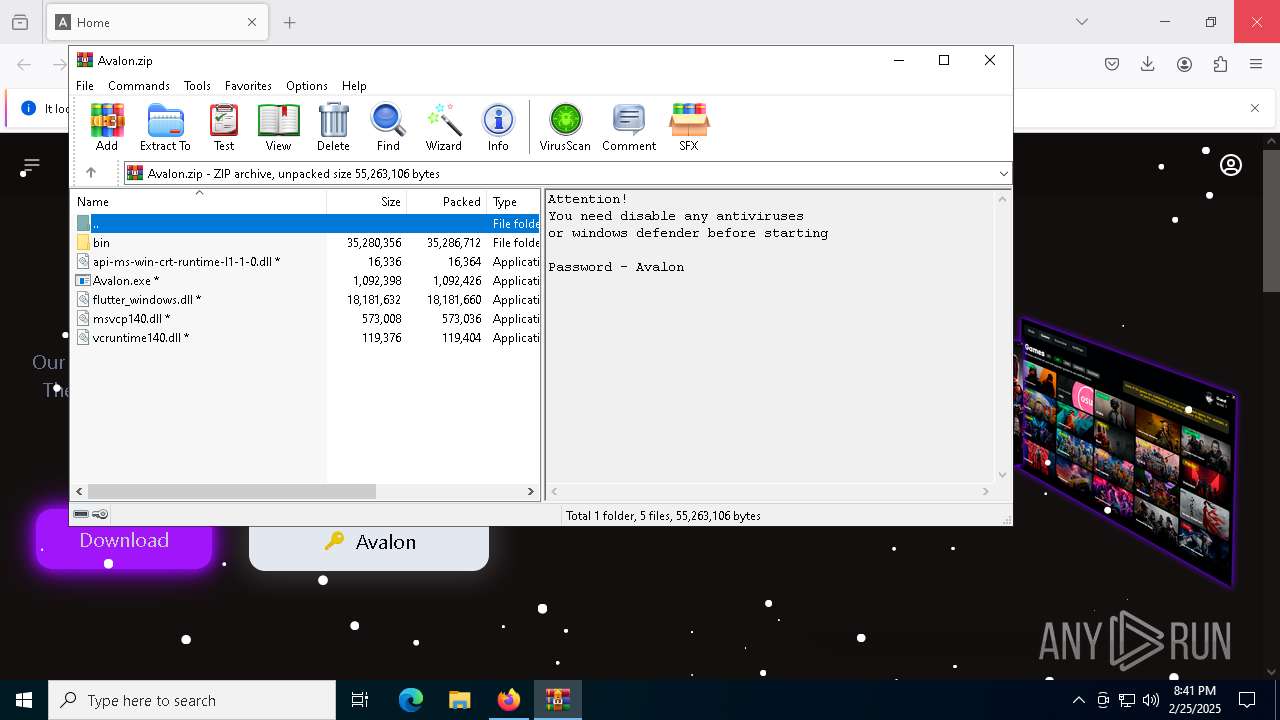
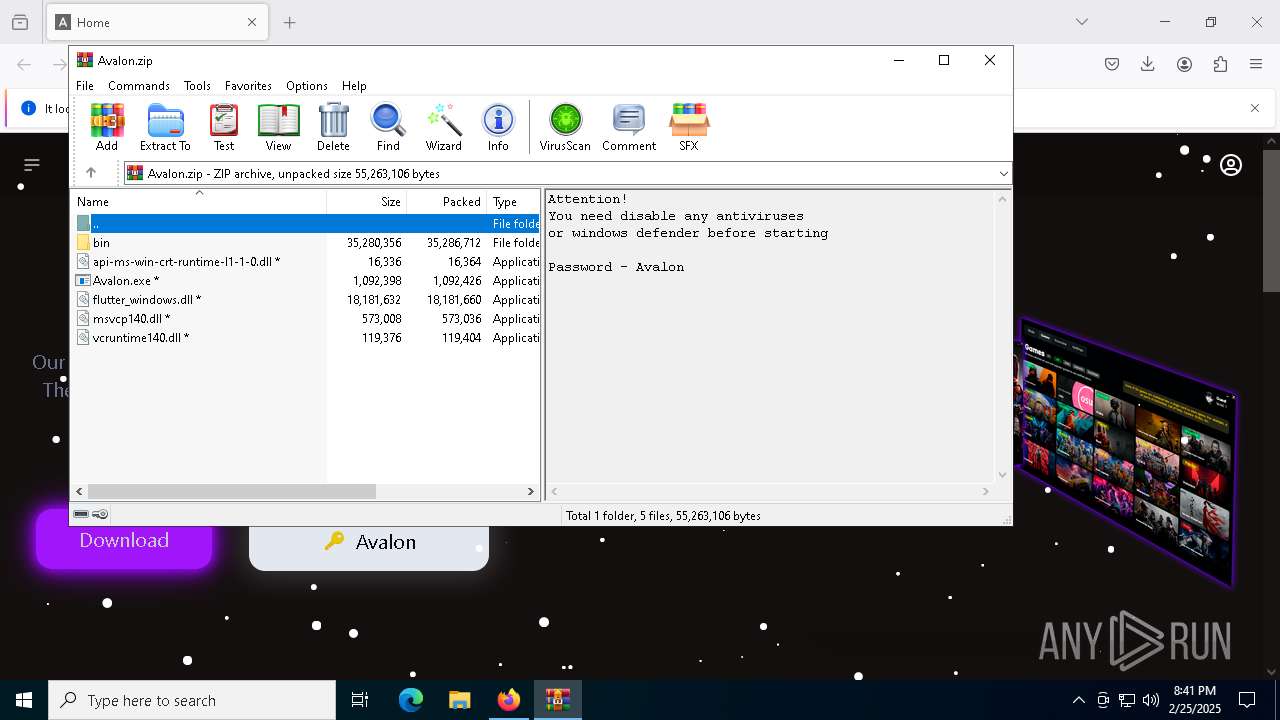
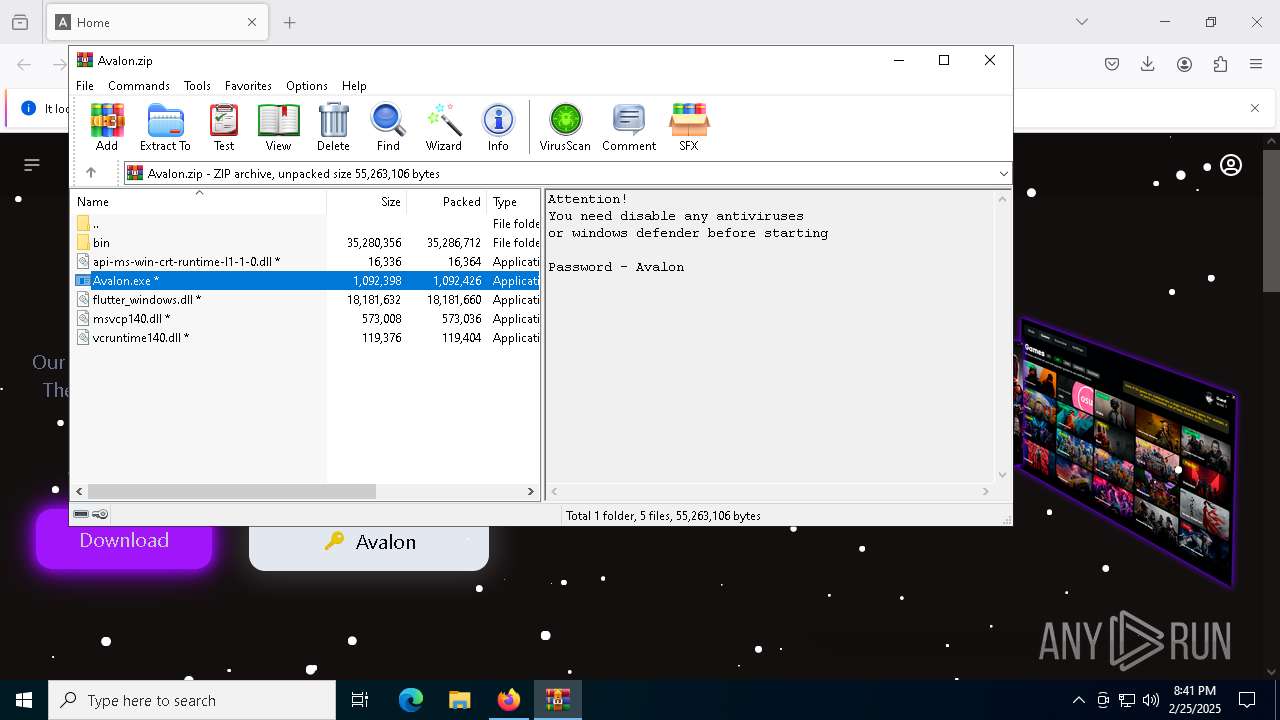
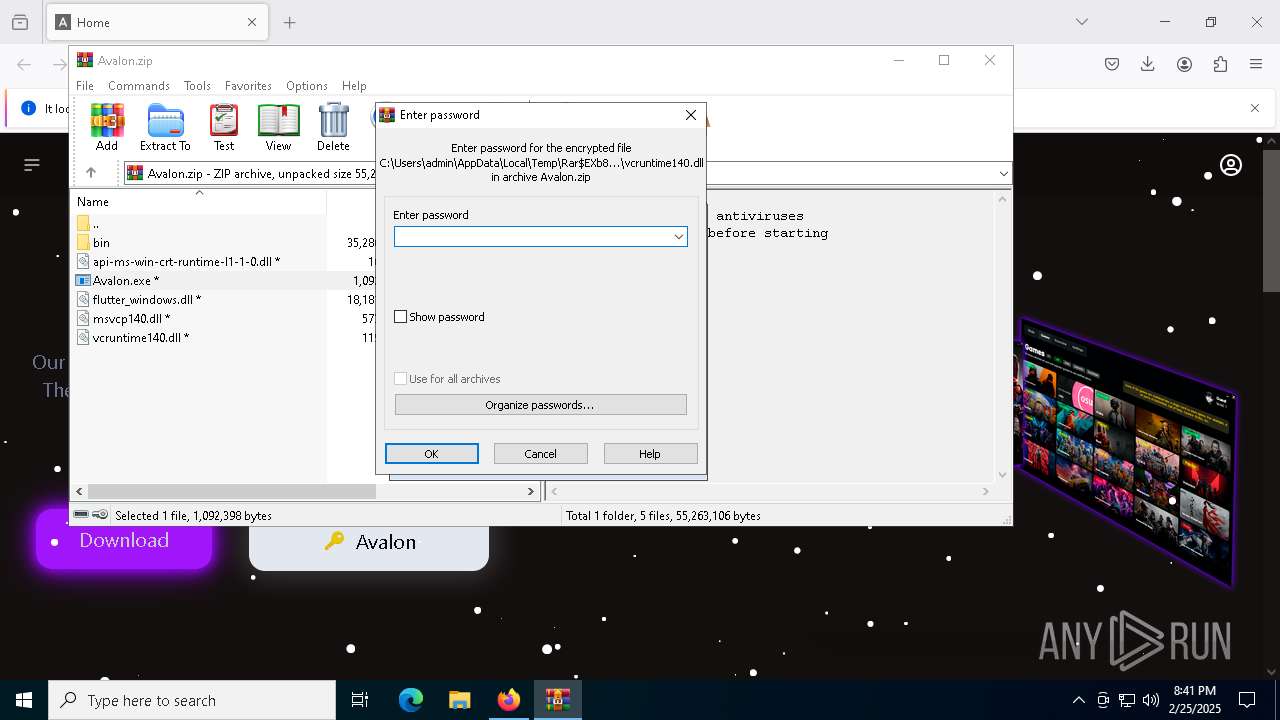
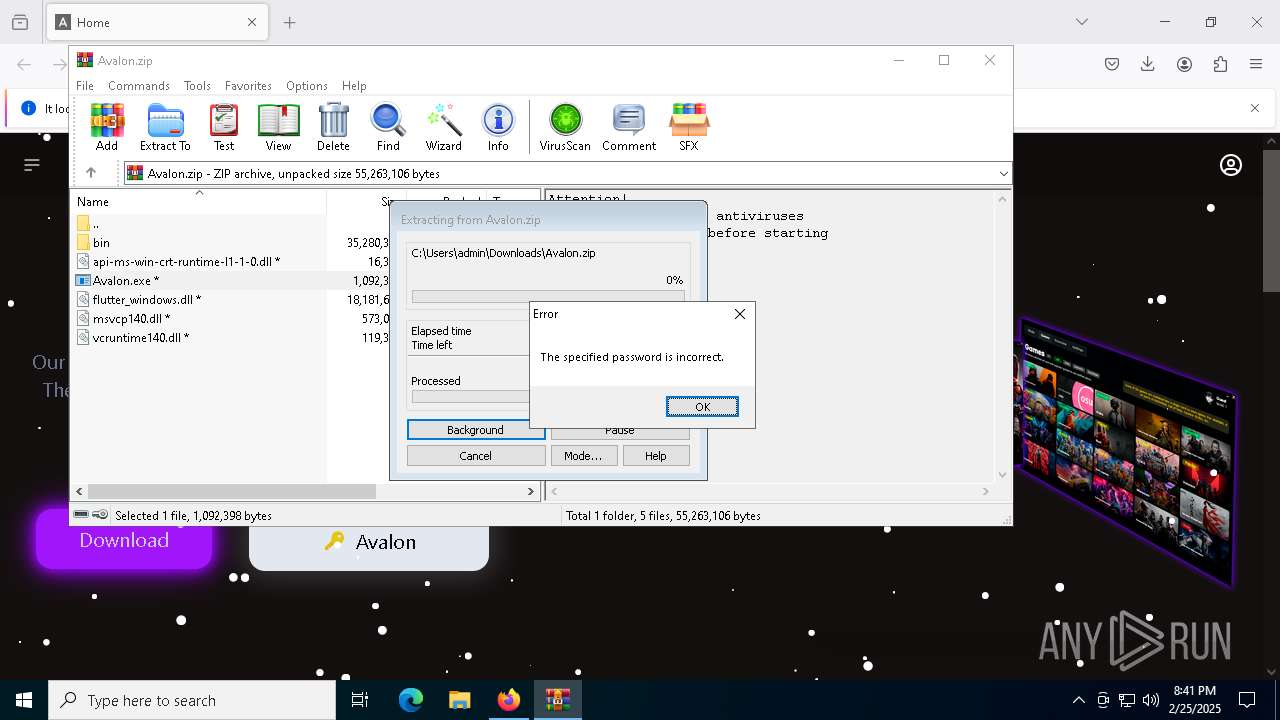
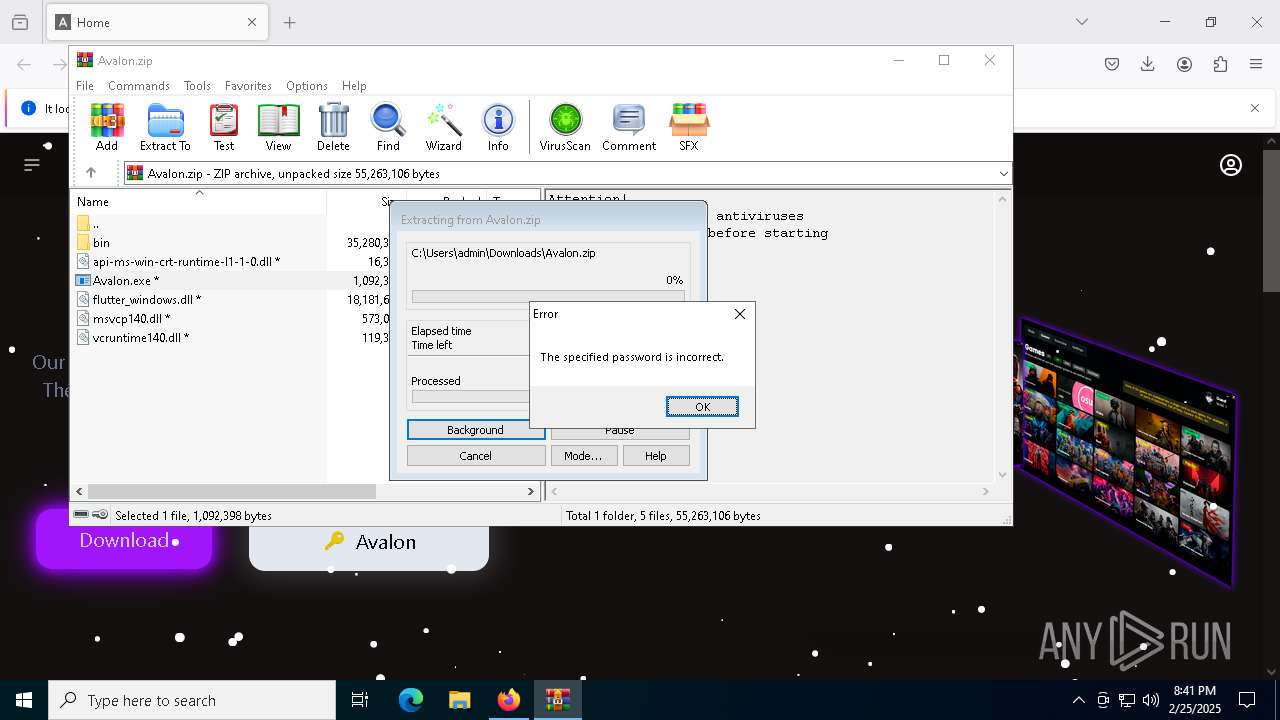
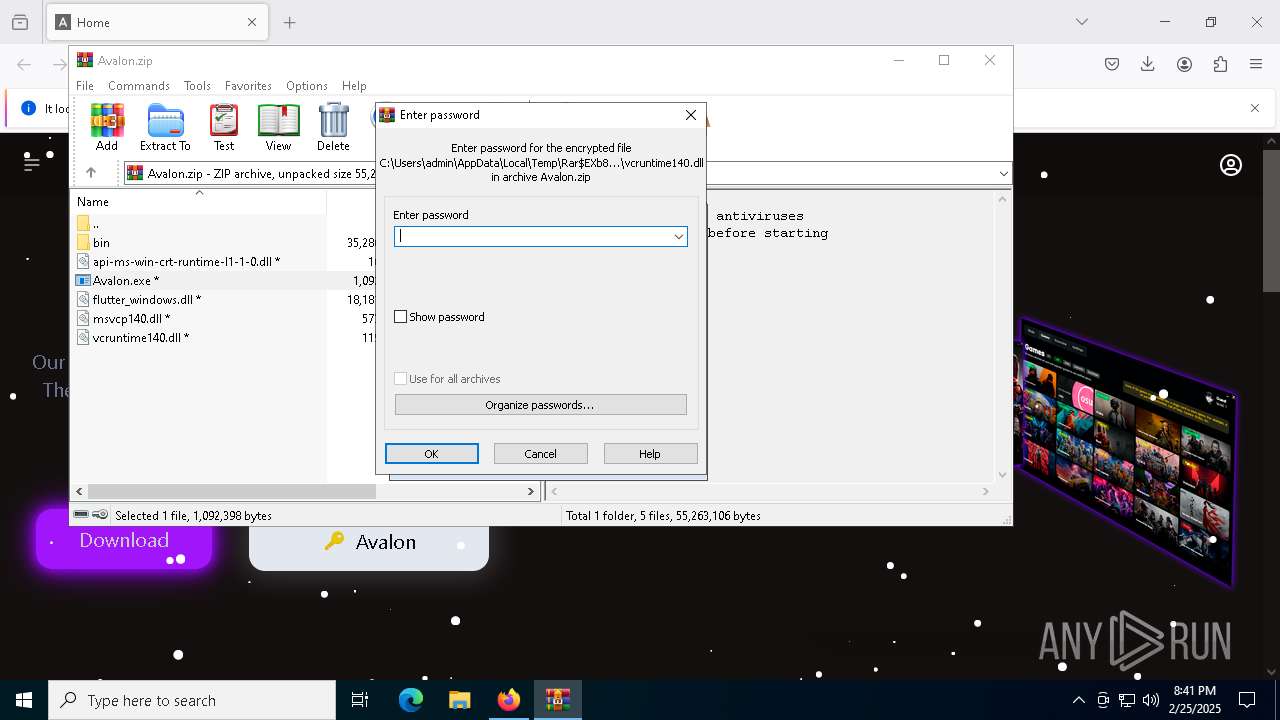
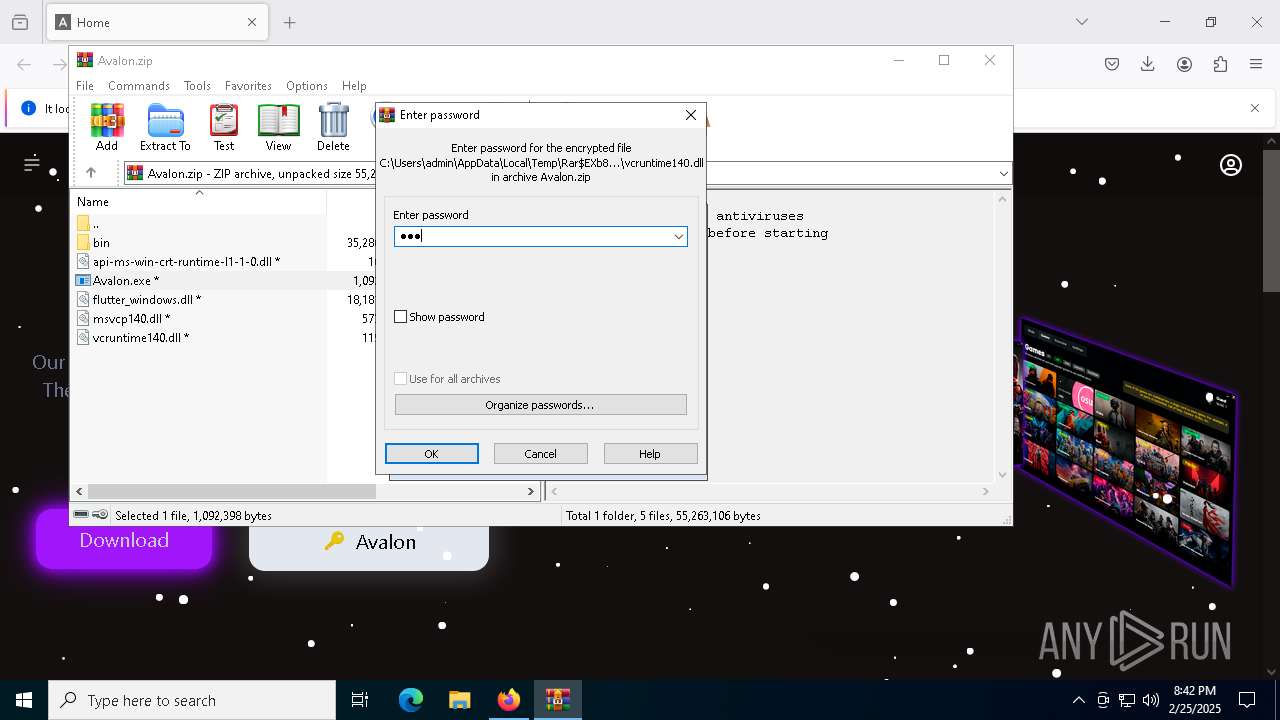
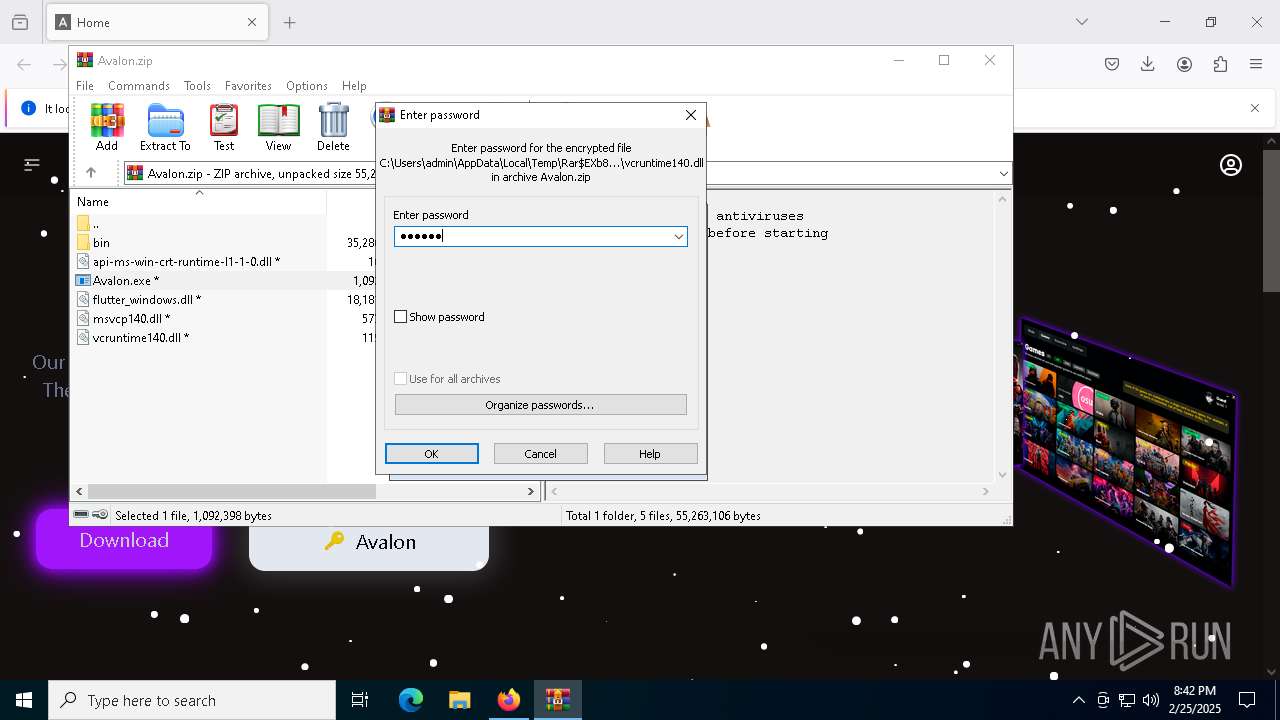
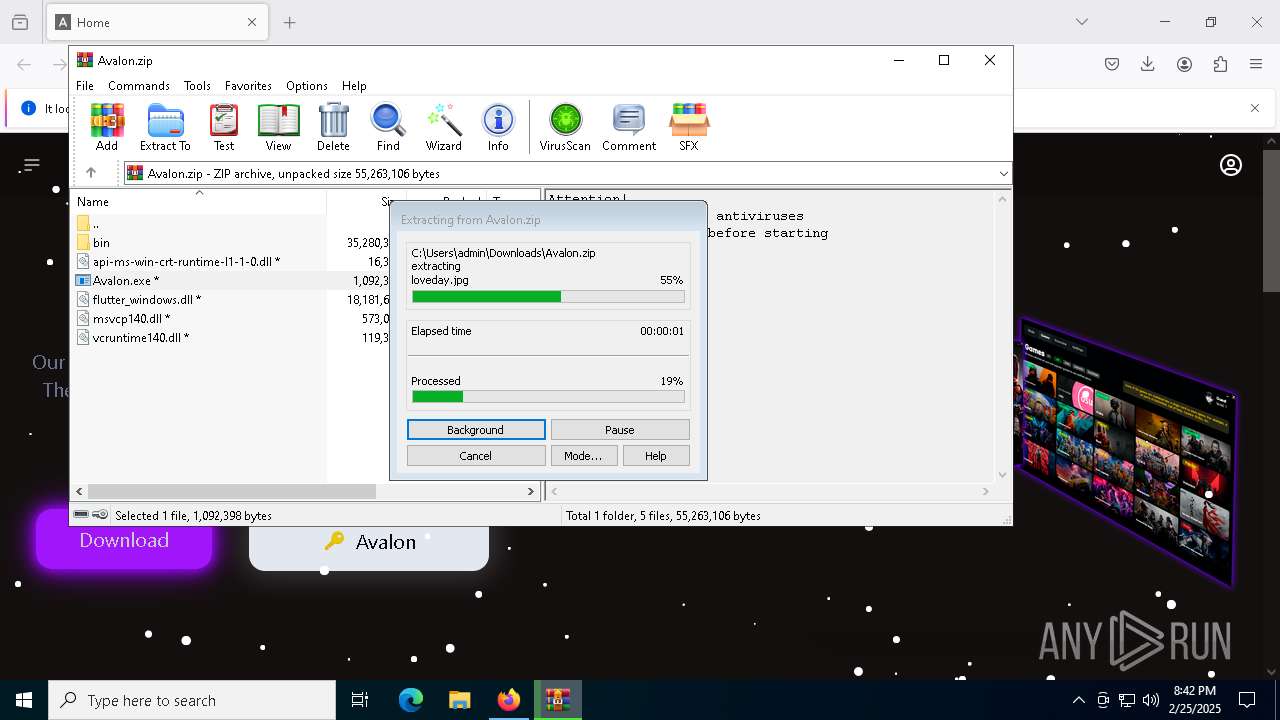
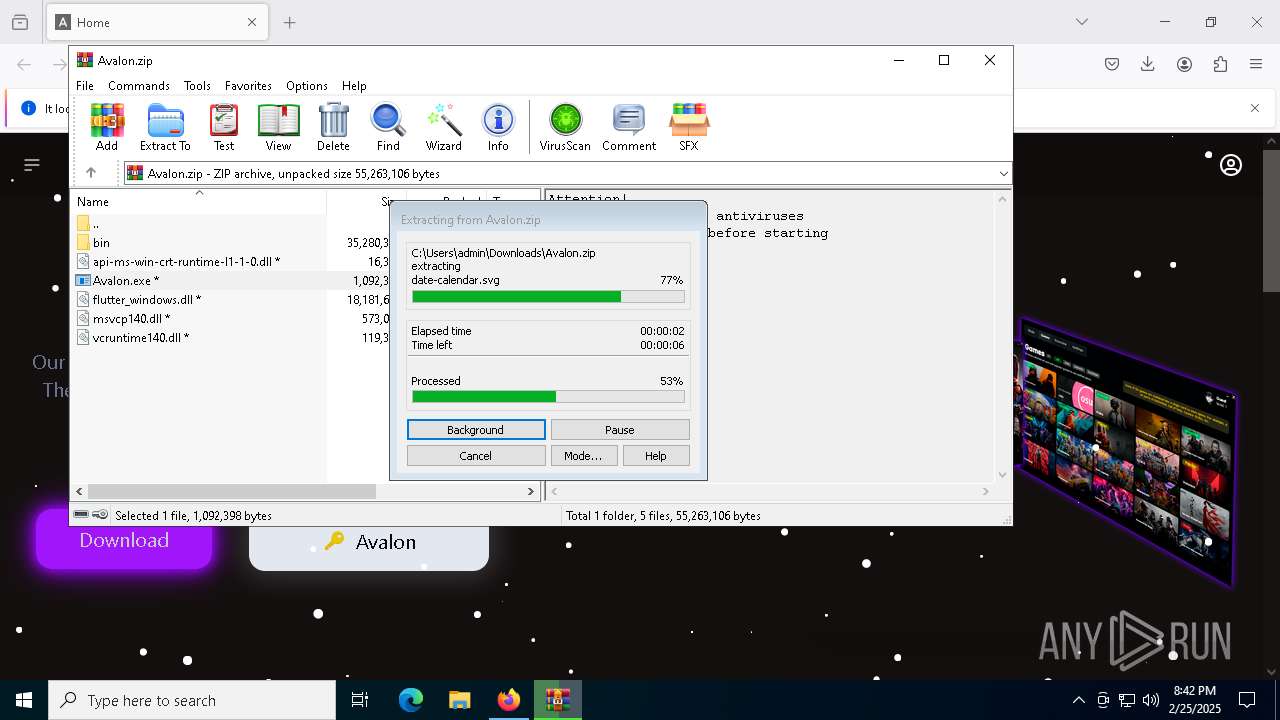
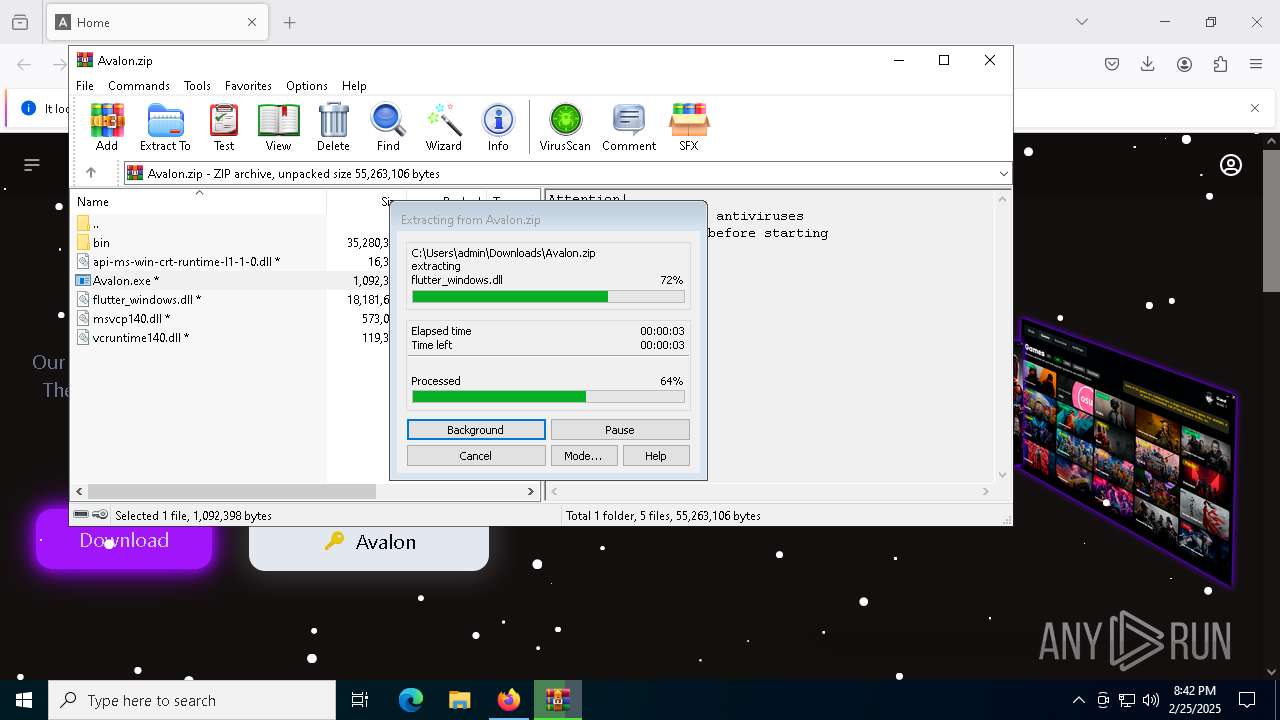
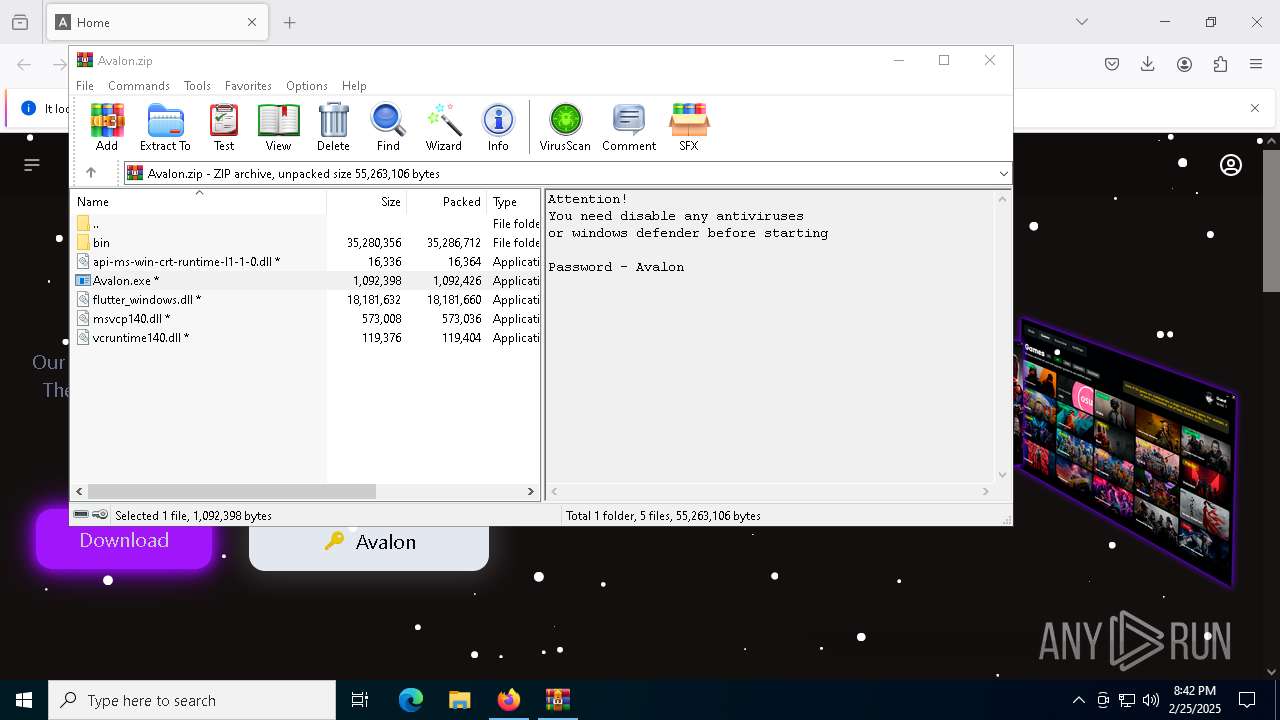
Process drops legitimate windows executable
- WinRAR.exe (PID: 8376)
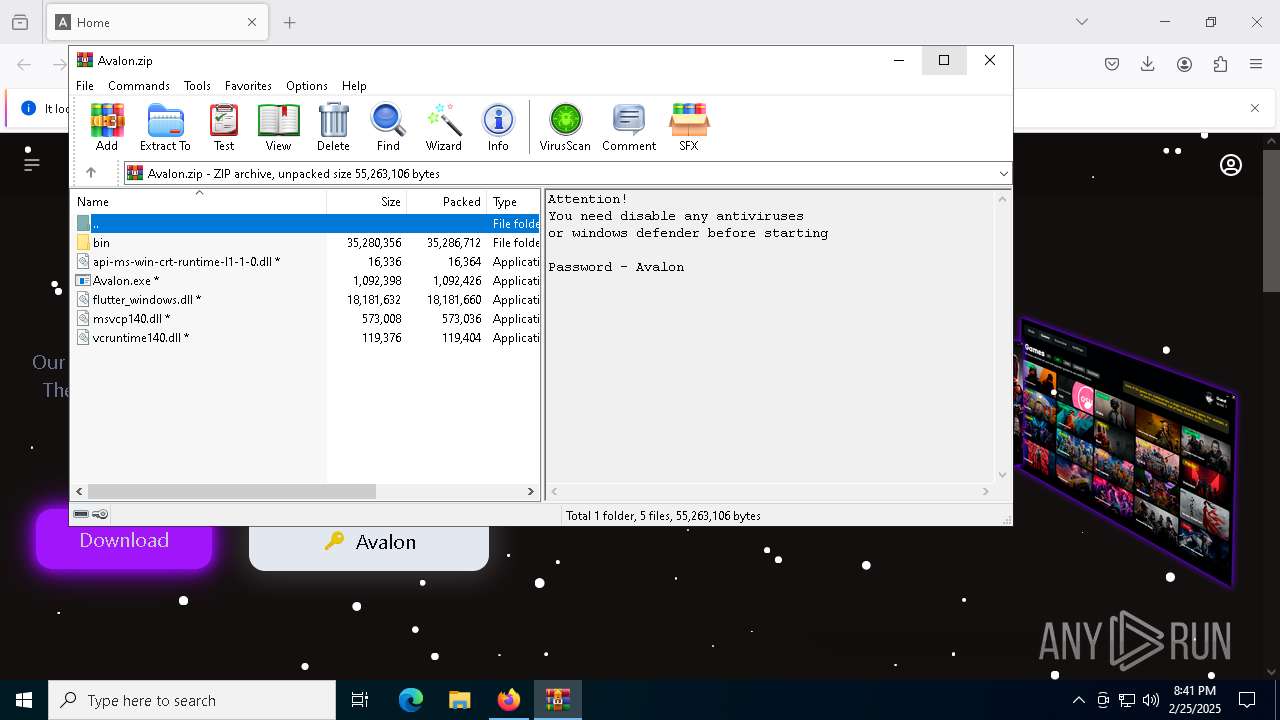
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8376)
- Avalon.exe (PID: 8776)
Executing commands from a ".bat" file
- Avalon.exe (PID: 8776)
Starts CMD.EXE for commands execution
- Avalon.exe (PID: 8776)
- cmd.exe (PID: 7772)
Get information on the list of running processes
- cmd.exe (PID: 7772)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7772)
Application launched itself
- cmd.exe (PID: 7772)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7772)
Starts application with an unusual extension
- cmd.exe (PID: 7772)
The executable file from the user directory is run by the CMD process
- Slovakia.com (PID: 8144)
Searches for installed software
- Slovakia.com (PID: 8144)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8780)
- BackgroundTransferHost.exe (PID: 2616)
- BackgroundTransferHost.exe (PID: 9028)
- BackgroundTransferHost.exe (PID: 8432)
- BackgroundTransferHost.exe (PID: 9212)
Application launched itself
- firefox.exe (PID: 1072)
- firefox.exe (PID: 6180)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 9028)
- slui.exe (PID: 5488)
Reads the computer name
- Avalon.exe (PID: 8776)
- extrac32.exe (PID: 8232)
- Slovakia.com (PID: 8144)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8376)
- firefox.exe (PID: 1072)
Create files in a temporary directory
- Avalon.exe (PID: 8776)
- extrac32.exe (PID: 8232)
- expand.exe (PID: 9096)
Process checks computer location settings
- Avalon.exe (PID: 8776)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 9028)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 9028)
- Slovakia.com (PID: 8144)
- slui.exe (PID: 5488)
Checks supported languages
- expand.exe (PID: 9096)
- extrac32.exe (PID: 8232)
- Slovakia.com (PID: 8144)
- Avalon.exe (PID: 8776)
Creates a new folder
- cmd.exe (PID: 6452)
Creates files in the program directory
- Slovakia.com (PID: 8144)
Reads mouse settings
- Slovakia.com (PID: 8144)
The sample compiled with english language support
- WinRAR.exe (PID: 8376)
Manual execution by a user
- WinRAR.exe (PID: 8376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
173
Monitored processes
35
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1012 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2092 -parentBuildID 20240213221259 -prefsHandle 2084 -prefMapHandle 2072 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {31737e4e-6117-4cf2-ac02-7b97305523e6} 1072 "\\.\pipe\gecko-crash-server-pipe.1072" 1fa3d781f10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 | |||||||||||||||
| 1072 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://aval2.pro/ | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1096 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 2616 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3008 | findstr /V "Wait" Characteristics | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5488 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5540 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2584 -childID 1 -isForBrowser -prefsHandle 2668 -prefMapHandle 2660 -prefsLen 26911 -prefMapSize 244583 -jsInitHandle 1300 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {cd1f1966-006b-493d-9d39-f315e15dfc08} 1072 "\\.\pipe\gecko-crash-server-pipe.1072" 1fa4eccdf50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 | |||||||||||||||
| 6180 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://aval2.pro/" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6324 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1364 -parentBuildID 20240213221259 -prefsHandle 1756 -prefMapHandle 1748 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {28c24233-48e8-4462-aced-59878c0333fc} 1072 "\\.\pipe\gecko-crash-server-pipe.1072" 1fa495cbe10 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 | |||||||||||||||
| 6452 | cmd /c md 9880 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 900
Read events
7 875
Write events
25
Delete events
0
Modification events
| (PID) Process: | (8780) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8780) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8780) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (9028) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (9028) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (9028) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (9212) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (9212) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (9212) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2616) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
10
Suspicious files
233
Text files
234
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1072 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 1072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 1072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 1072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.bin | binary | |
MD5:F759EB25271E6A6F0A3500520813E5FE | SHA256:015E515D432DD64FDC9502ABE9C723EEF544E7AF11C36BDFE8B38412597CA1EC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
105
DNS requests
148
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1072 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
1072 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
1072 | firefox.exe | POST | 200 | 184.24.77.47:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
1072 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 142.250.181.227:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
1072 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
1072 | firefox.exe | POST | 200 | 184.24.77.47:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | — | 142.250.181.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | POST | 200 | 142.250.181.227:80 | http://o.pki.goog/s/wr3/UTA | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 188.114.97.3:443 | aval2.pro | CLOUDFLARENET | NL | unknown |
1072 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
1072 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
1072 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
1072 | firefox.exe | 184.24.77.47:80 | r11.o.lencr.org | Akamai International B.V. | DE | whitelisted |
1072 | firefox.exe | 184.24.77.45:80 | r11.o.lencr.org | Akamai International B.V. | DE | whitelisted |
— | — | 142.250.181.227:80 | o.pki.goog | GOOGLE | US | whitelisted |
1072 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
aval2.pro |
| unknown |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
prod.content-signature-chains.prod.webservices.mozgcp.net |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
prod.ads.prod.webservices.mozgcp.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |