| File name: | explorer .exe |
| Full analysis: | https://app.any.run/tasks/54e1e32a-b2fc-4106-a6ea-4526fd5f602e |
| Verdict: | Malicious activity |
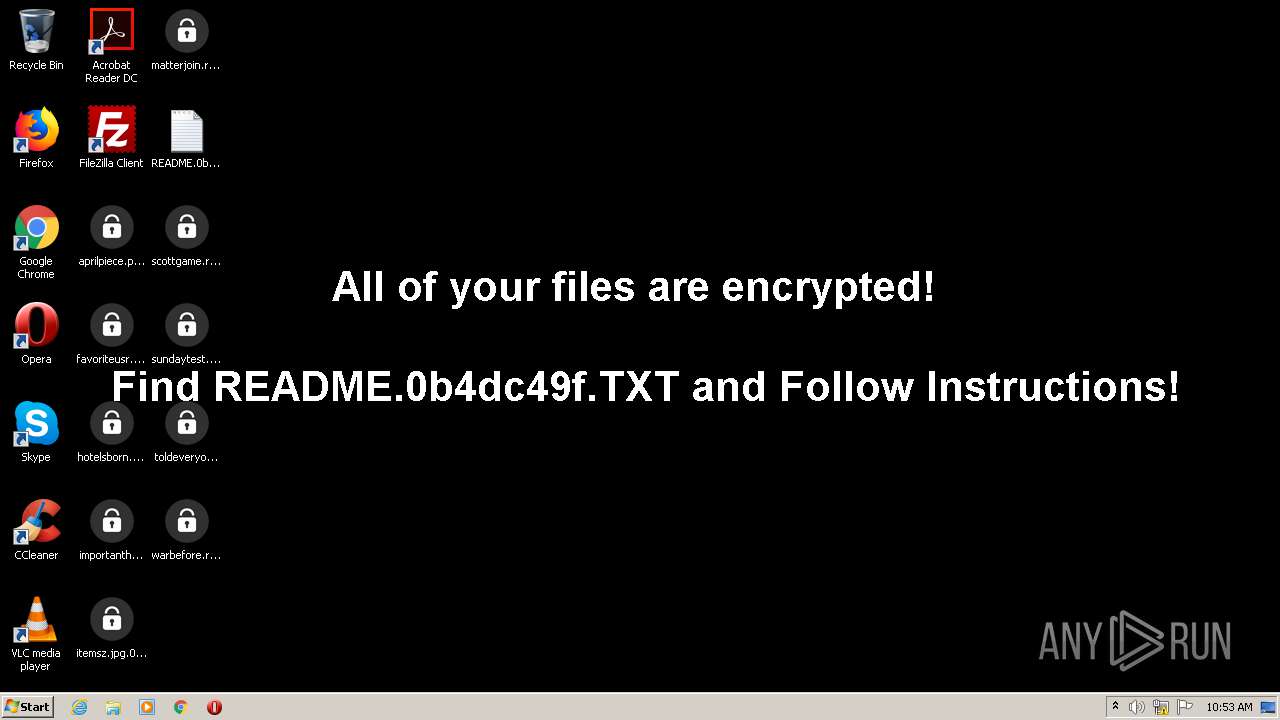
| Threats: | DarkSide ransomware is a novel ransomware strain involved in high-profile incidents. Its attacks lead to data theft and encryption, causing significant damage to victims. |
| Analysis date: | May 13, 2021, 09:51:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 794C5AA1B0E1F9CF2FC7FE5F22117C3F |
| SHA1: | 1821FE210298B1D22B25F1A544ABCFE092999FF7 |
| SHA256: | 4098B54C9D27B00CE34D04FFAC24213ED28993A2854827851B157D63407C2E4E |
| SSDEEP: | 98304:psCGaED3PF1pAJsqh8rltswCN6N7hqts6G5WWLF3/EDhRKYmKH7dEpuo5jv59Ndr:pMjbpKsZXCNntspWK3/EDLtp7dRopvXP |
MALICIOUS
Darkside was detected
- explorer .exe (PID: 560)
Known privilege escalation attack
- DllHost.exe (PID: 2544)
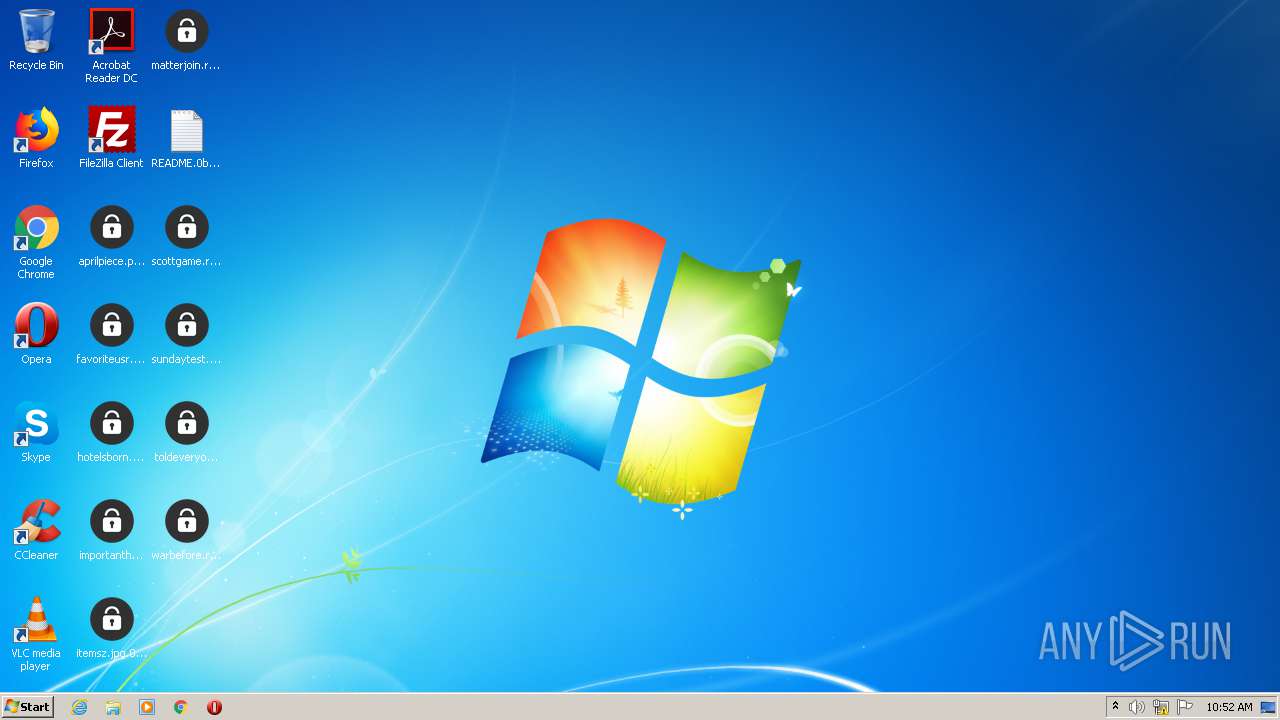
Darkside note found
- explorer .exe (PID: 560)
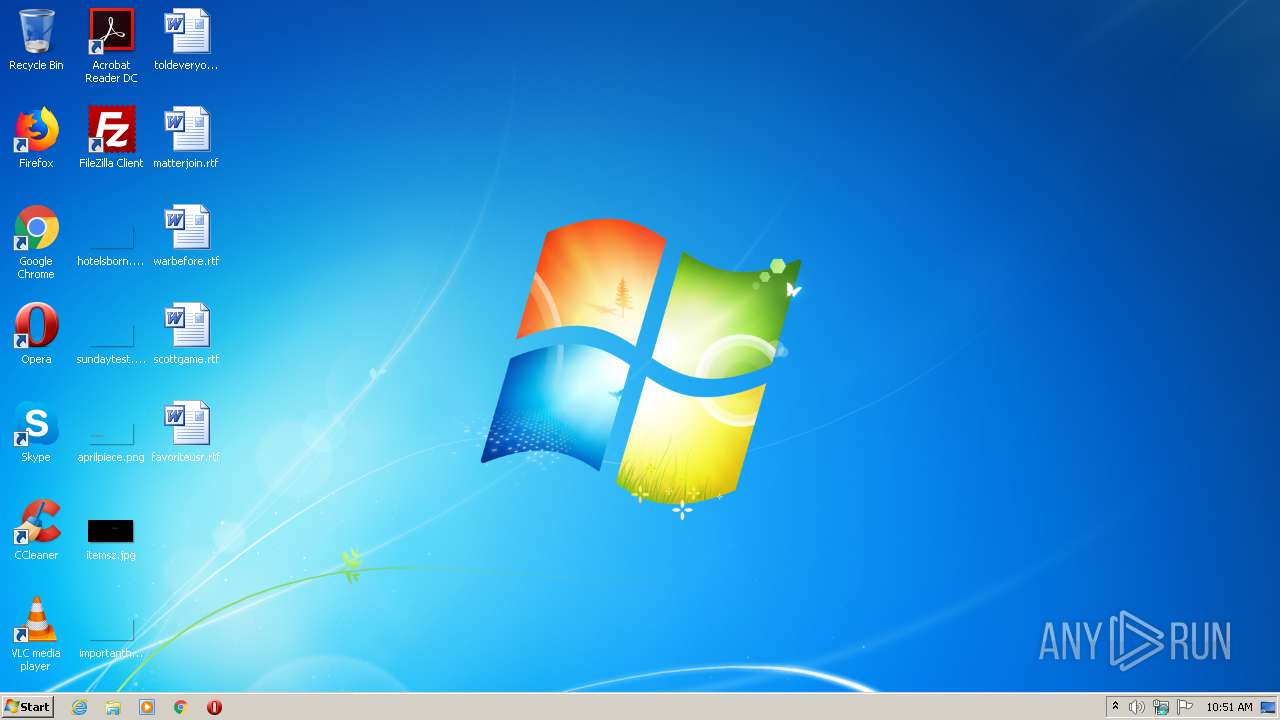
Renames files like Ransomware
- explorer .exe (PID: 560)
Connects to CnC server
- explorer .exe (PID: 560)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 2544)
Creates files like Ransomware instruction
- explorer .exe (PID: 560)
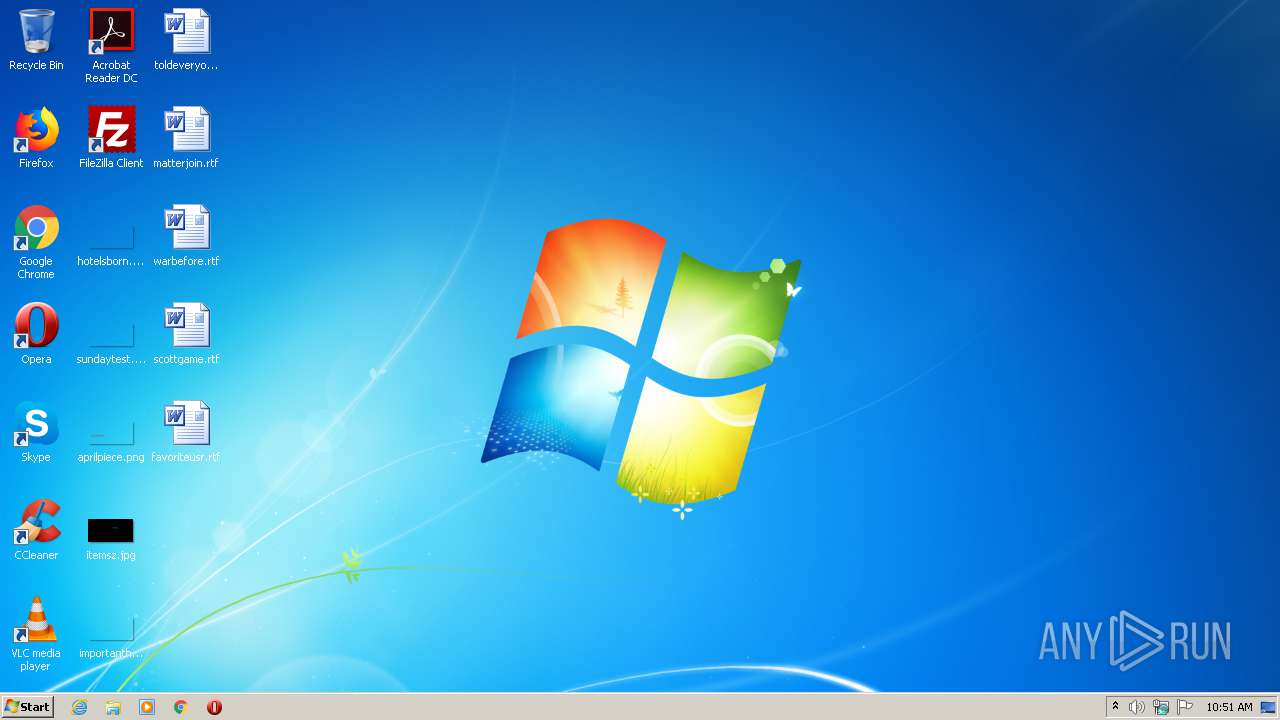
Changes the desktop background image
- explorer .exe (PID: 560)
Starts CMD.EXE for self-deleting
- explorer .exe (PID: 560)
Creates files in the program directory
- explorer .exe (PID: 560)
Drops a file with a compile date too recent
- explorer .exe (PID: 560)
Starts CMD.EXE for commands execution
- explorer .exe (PID: 560)
INFO
Dropped object may contain TOR URL's
- explorer .exe (PID: 560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x952962 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 37888 |
| CodeSize: | 29184 |
| LinkerVersion: | 14.12 |
| PEType: | PE32 |
| TimeStamp: | 2020:12:23 18:01:07+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Dec-2020 17:01:07 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 23-Dec-2020 17:01:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000071D3 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.rdata | 0x00009000 | 0x00000176 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.data | 0x0000A000 | 0x0000844C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.vmp0 | 0x00013000 | 0x003B4788 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.vmp1 | 0x003C8000 | 0x005DEA30 | 0x005DEC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.95876 |
.reloc | 0x009A7000 | 0x000005FC | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.33151 |
Imports
KERNEL32.dll |
USER32.dll |
WTSAPI32.dll |
Total processes
46
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Users\admin\AppData\Local\Temp\explorer .exe" | C:\Users\admin\AppData\Local\Temp\explorer .exe | DllHost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1196 | "C:\Windows\system32\cmd.exe" /C DEL /F /Q C:\Users\admin\AppData\Local\Temp\EXPLOR~1.EXE >> NUL | C:\Windows\system32\cmd.exe | — | explorer .exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2264 | "C:\Users\admin\AppData\Local\Temp\explorer .exe" | C:\Users\admin\AppData\Local\Temp\explorer .exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2544 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
432
Read events
414
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2544) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2544) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (560) explorer .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.0b4dc49f |
| Operation: | write | Name: | (default) |
Value: 0b4dc49f | |||
| (PID) Process: | (560) explorer .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\0b4dc49f\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: C:\Users\admin\AppData\Local\0b4dc49f.ico | |||
| (PID) Process: | (560) explorer .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 74 | |||
| (PID) Process: | (560) explorer .exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (560) explorer .exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (560) explorer .exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (560) explorer .exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (560) explorer .exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
153
Text files
44
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 560 | explorer .exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.0b4dc49f | — | |
MD5:— | SHA256:— | |||
| 560 | explorer .exe | C:\Users\admin\Desktop\hotelsborn.png.0b4dc49f | — | |
MD5:— | SHA256:— | |||
| 560 | explorer .exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp.0b4dc49f | binary | |
MD5:— | SHA256:— | |||
| 560 | explorer .exe | C:\Users\admin\Desktop\importanthours.png.0b4dc49f | binary | |
MD5:— | SHA256:— | |||
| 560 | explorer .exe | C:\Users\admin\Contacts\admin.contact.0b4dc49f | binary | |
MD5:— | SHA256:— | |||
| 560 | explorer .exe | C:\Users\admin\Desktop\favoriteusr.rtf.0b4dc49f | binary | |
MD5:— | SHA256:— | |||
| 560 | explorer .exe | C:\Users\admin\Desktop\sundaytest.png.0b4dc49f | binary | |
MD5:— | SHA256:— | |||
| 560 | explorer .exe | C:\Users\admin\Desktop\scottgame.rtf.0b4dc49f | binary | |
MD5:— | SHA256:— | |||
| 560 | explorer .exe | C:\Users\admin\Desktop\toldeveryone.rtf.0b4dc49f | binary | |
MD5:— | SHA256:— | |||
| 560 | explorer .exe | C:\Users\admin\Desktop\matterjoin.rtf.0b4dc49f | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
3
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
560 | explorer .exe | 185.105.109.19:443 | securebestapp20.com | Proweb LLC | UA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
securebestapp20.com |
| malicious |
1.100.168.192.in-addr.arpa |
| unknown |
2.100.168.192.in-addr.arpa |
| whitelisted |
Threats
2 ETPRO signatures available at the full report