| File name: | bmcon.exe |
| Full analysis: | https://app.any.run/tasks/7e80d2f6-ddd0-4614-9aea-fa6e54cd022b |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | September 02, 2019, 09:56:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 2731697E36FC09A4D8B4568DFFA42EFD |
| SHA1: | 39D8AC780A74BF62E87D7EE8348DB992134220D9 |
| SHA256: | 40883E27922D357F0A3F15544ED9623475C9F430435F918D57A212F5BD11DA34 |
| SSDEEP: | 6144:Q05FLSZa4WZRfJqINr8Ch/phs6u2/Vkz18h63V:Q0WZ0XfJdykpy6u2/VkU6l |
MALICIOUS
Application was dropped or rewritten from another process
- bm-xmrig-x32.exe (PID: 3892)
- bmstart.exe (PID: 4060)
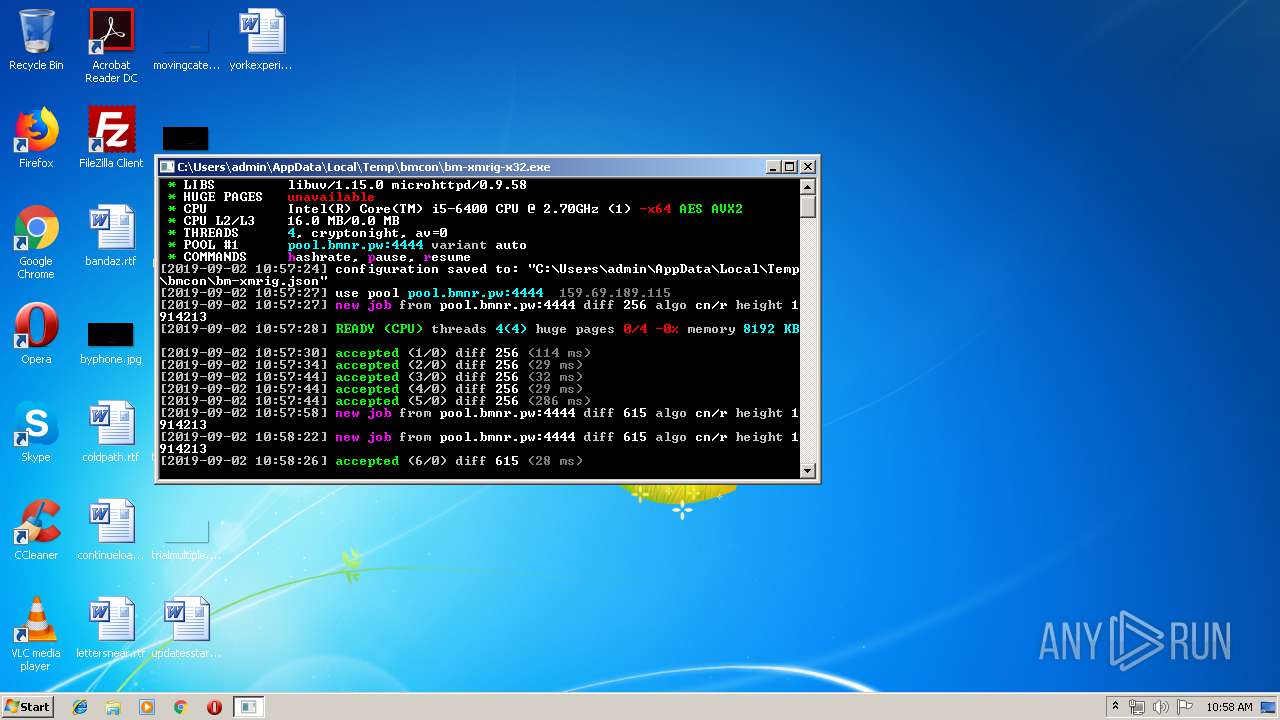
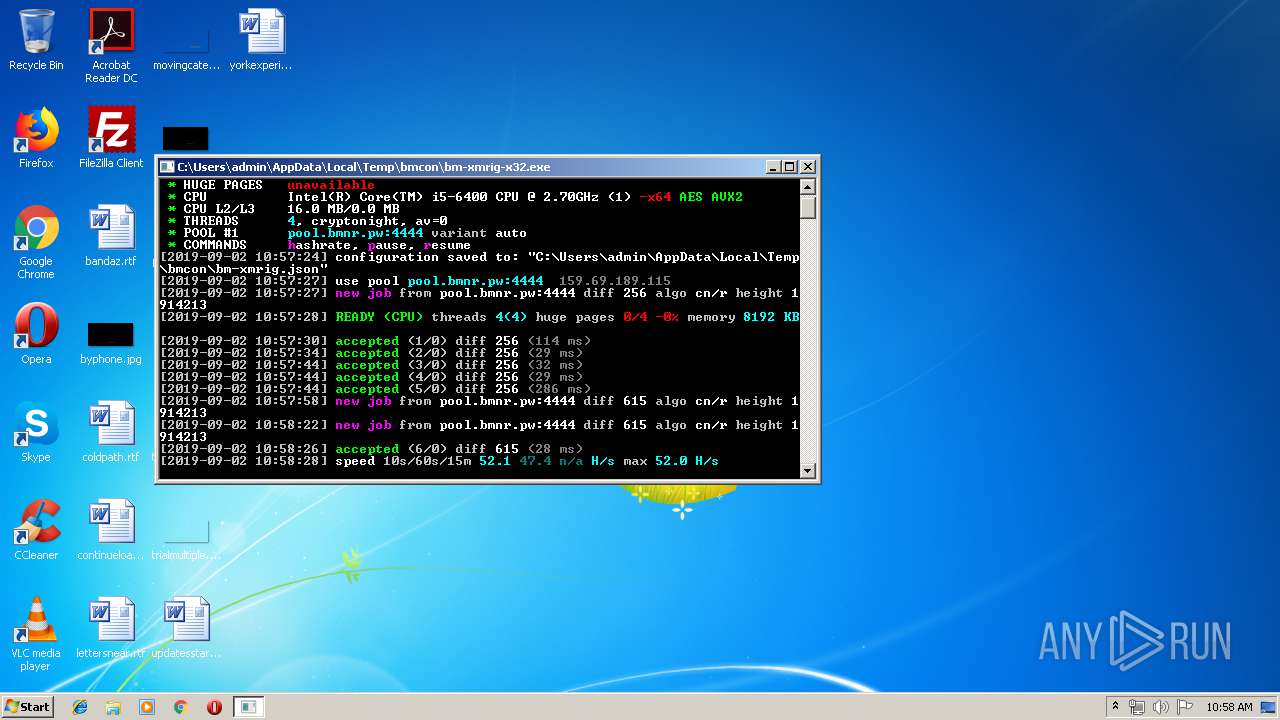
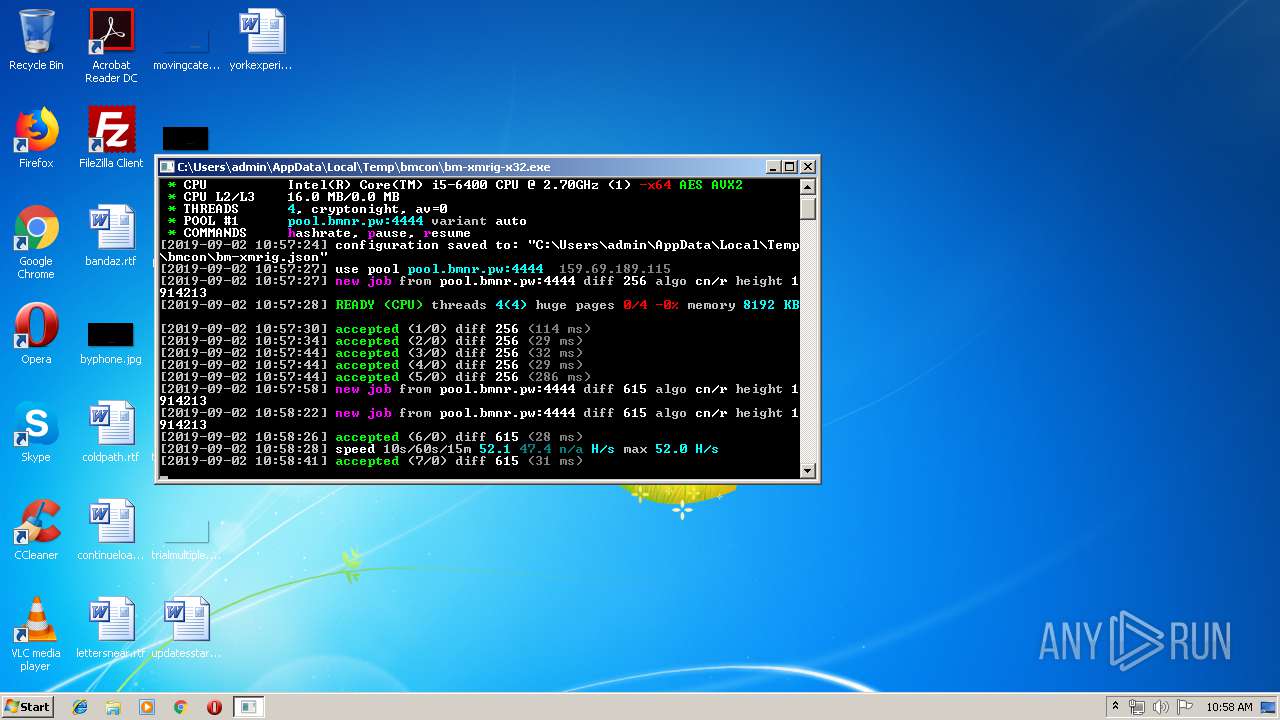
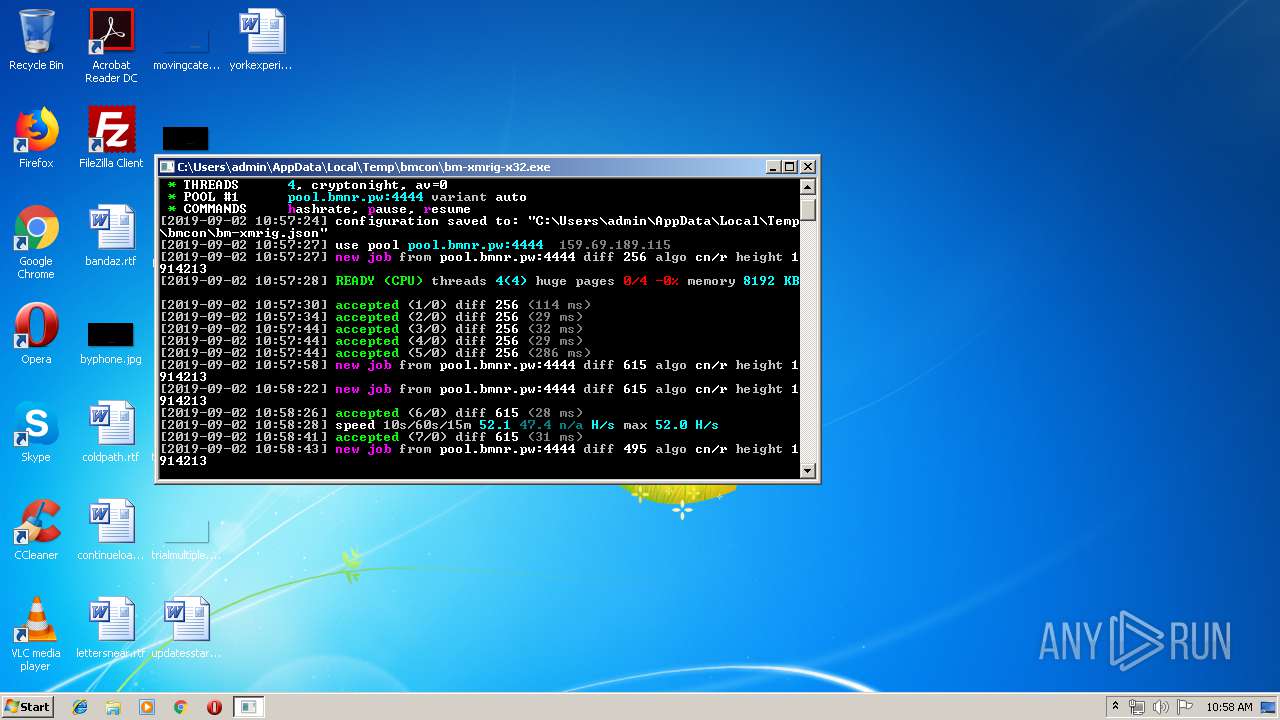
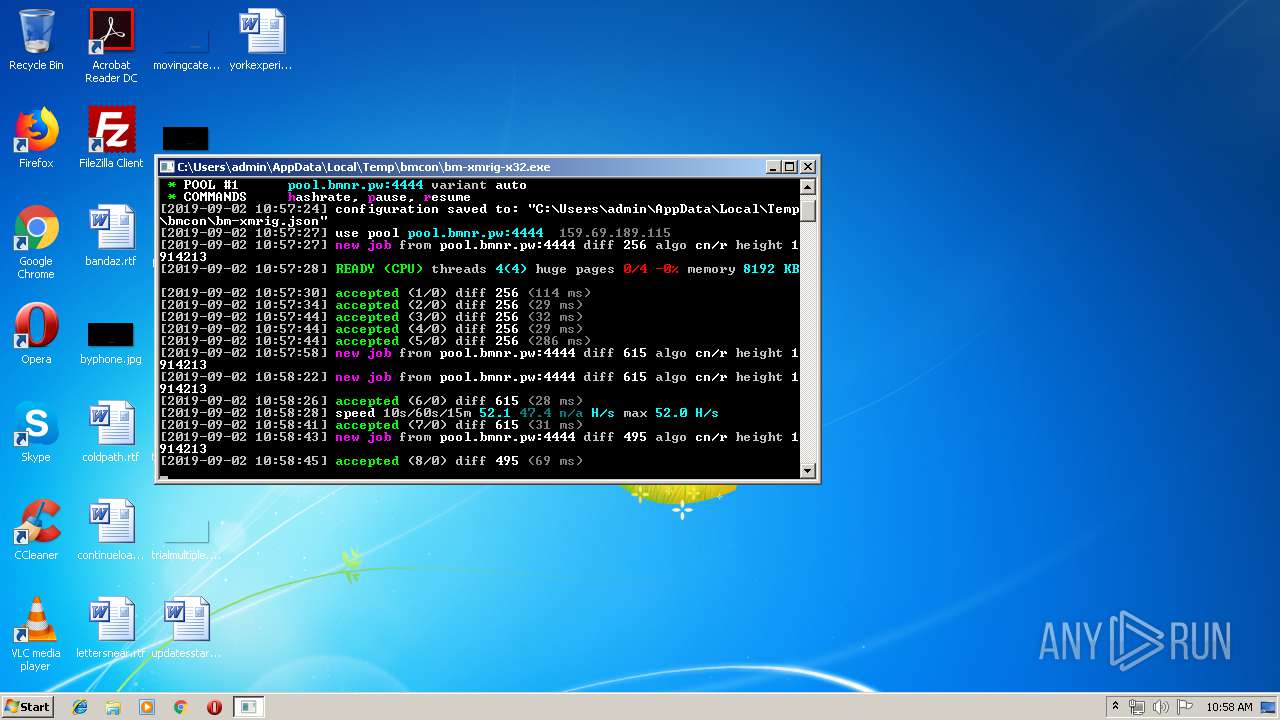
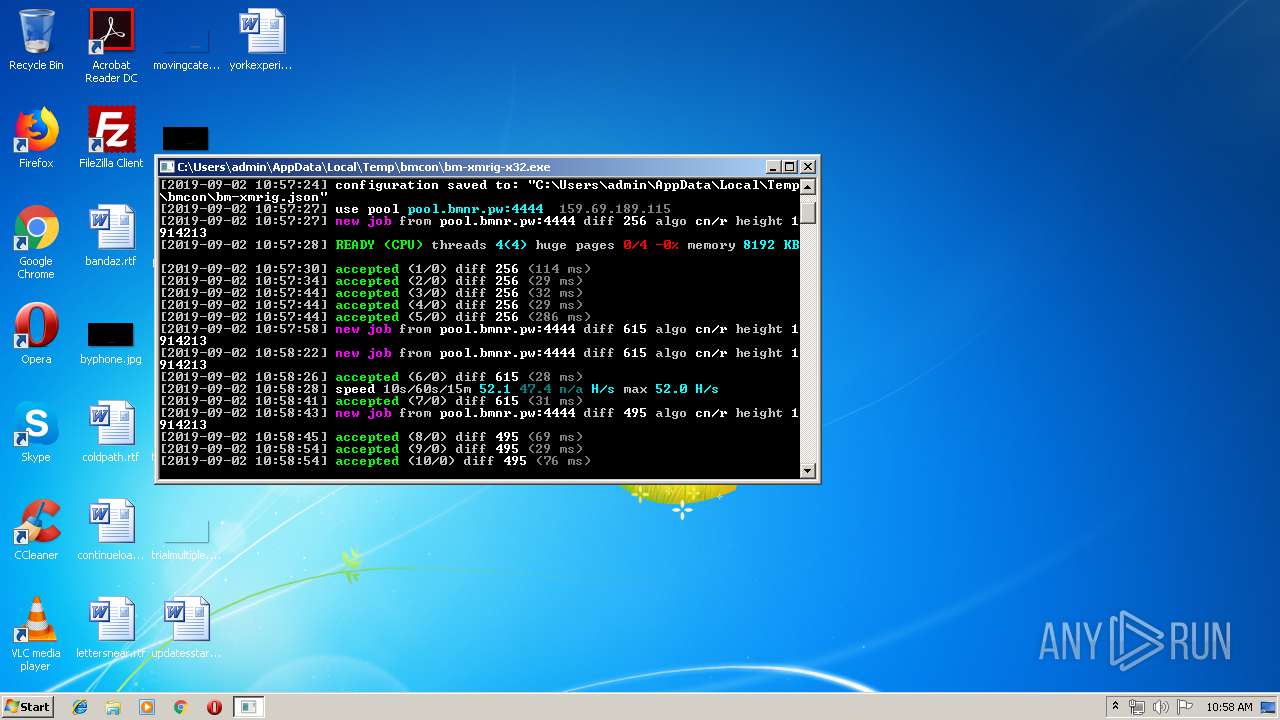
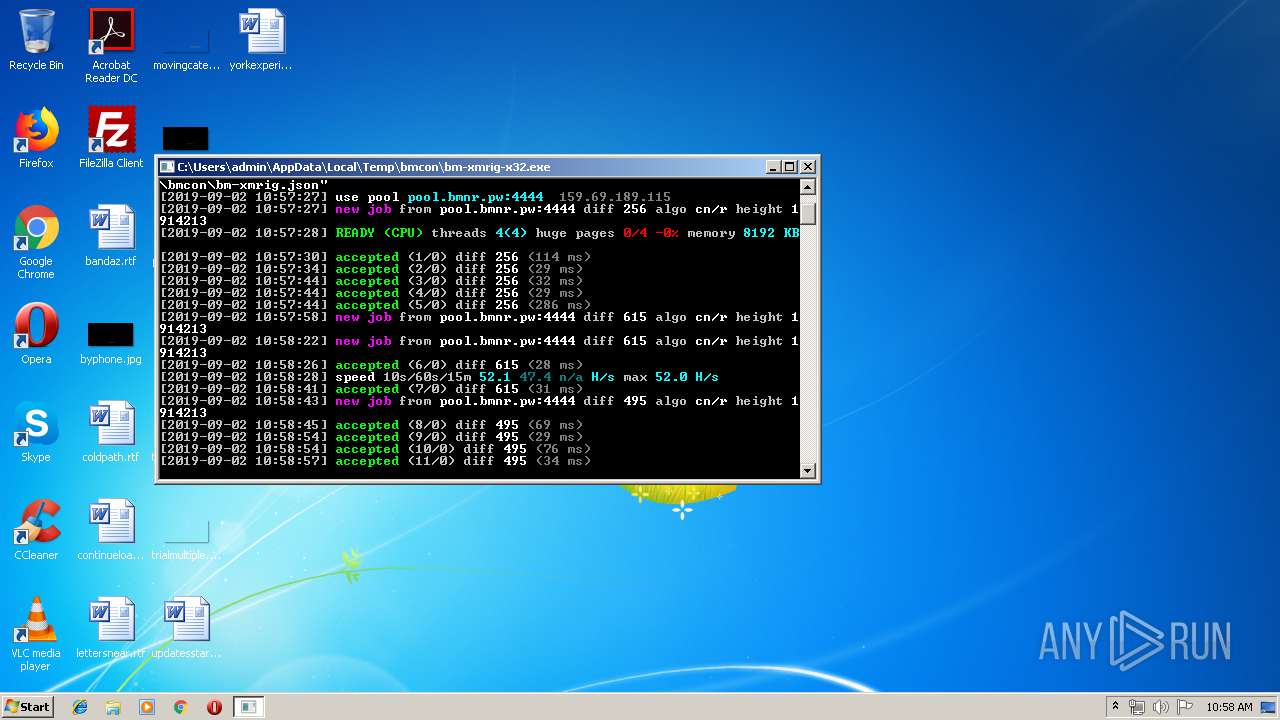
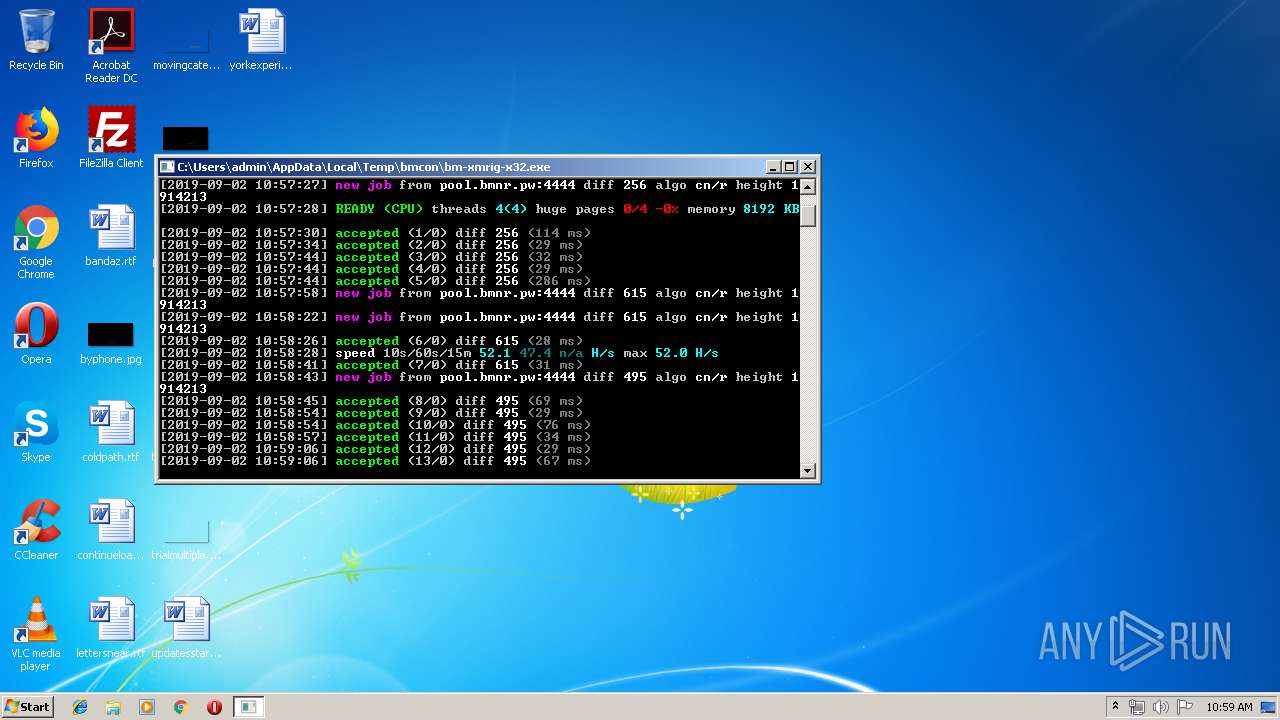
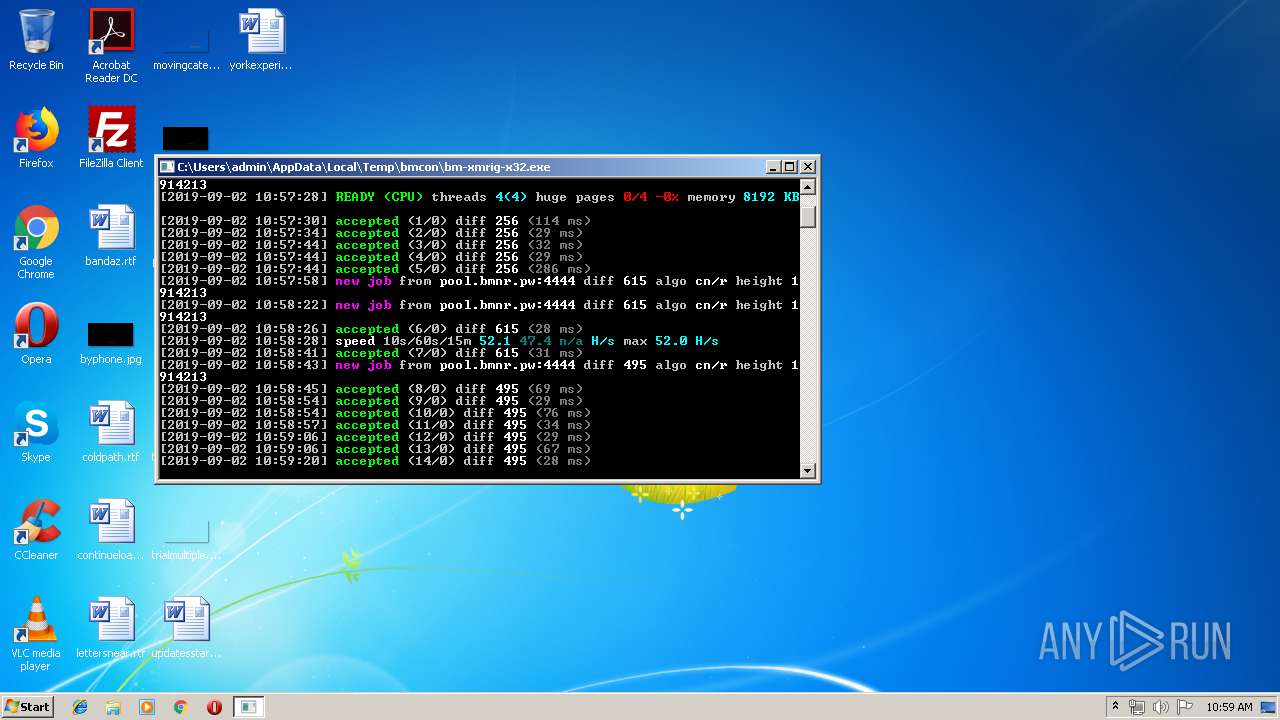
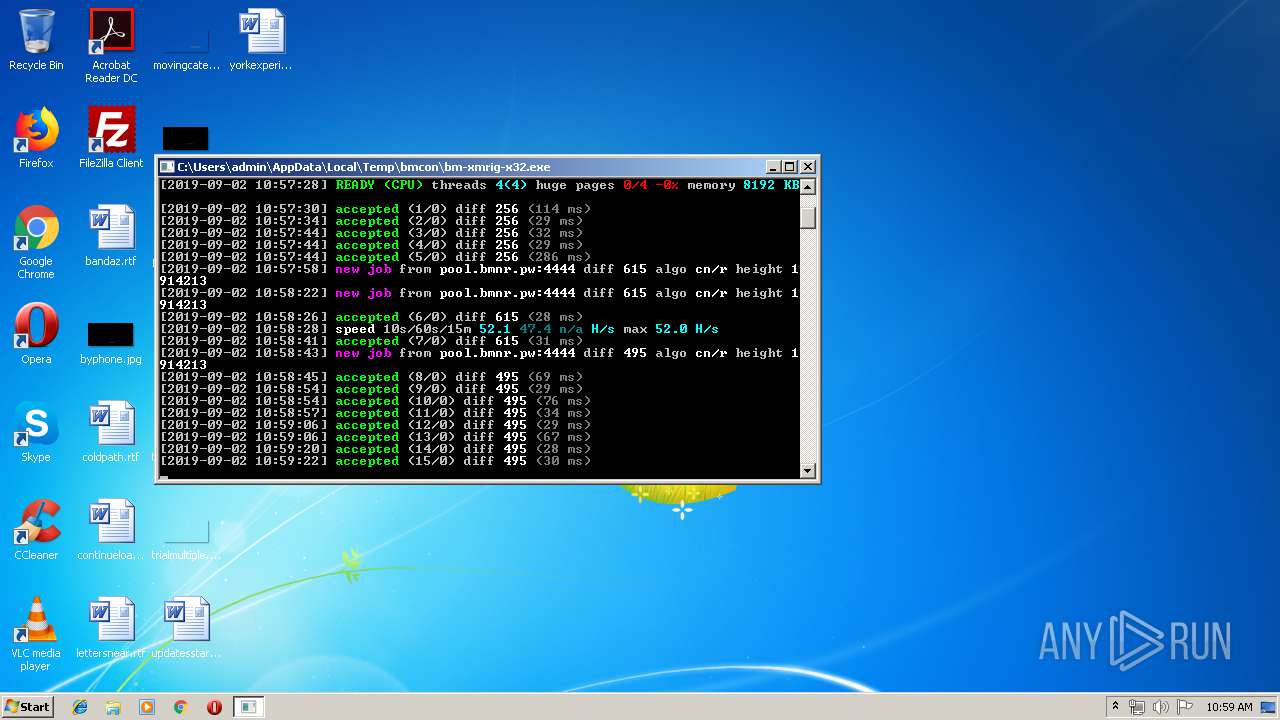
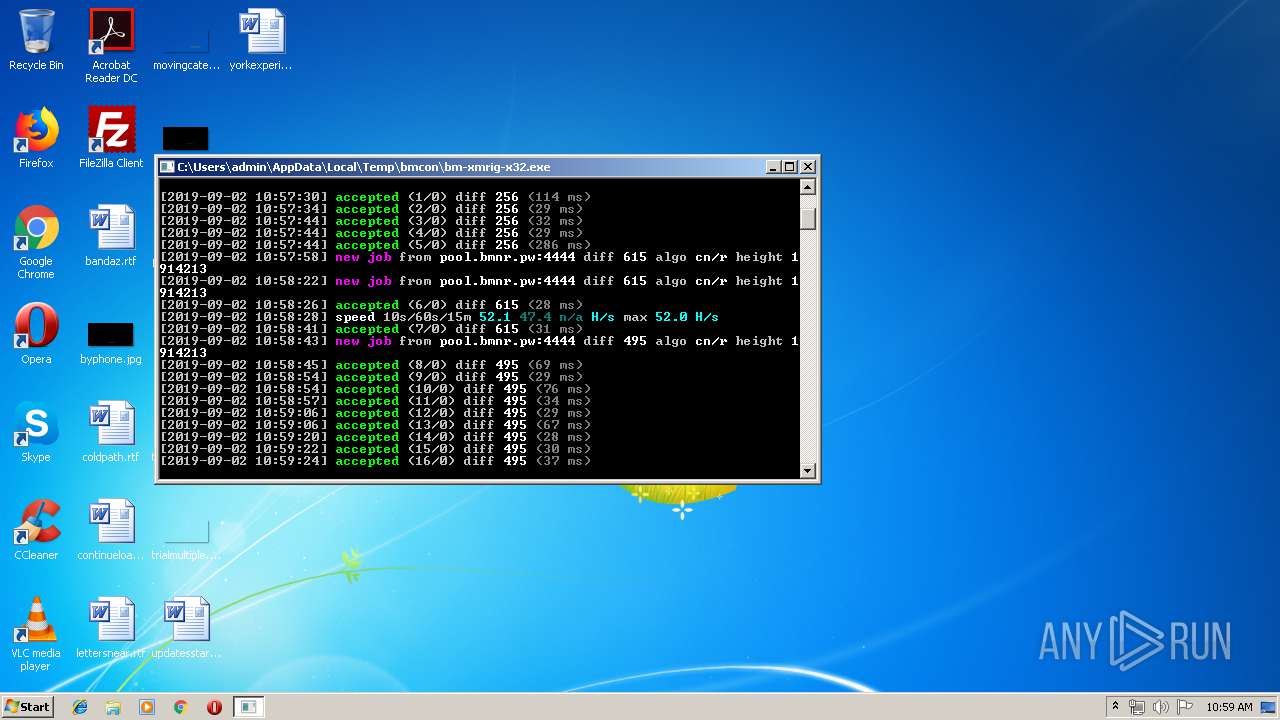
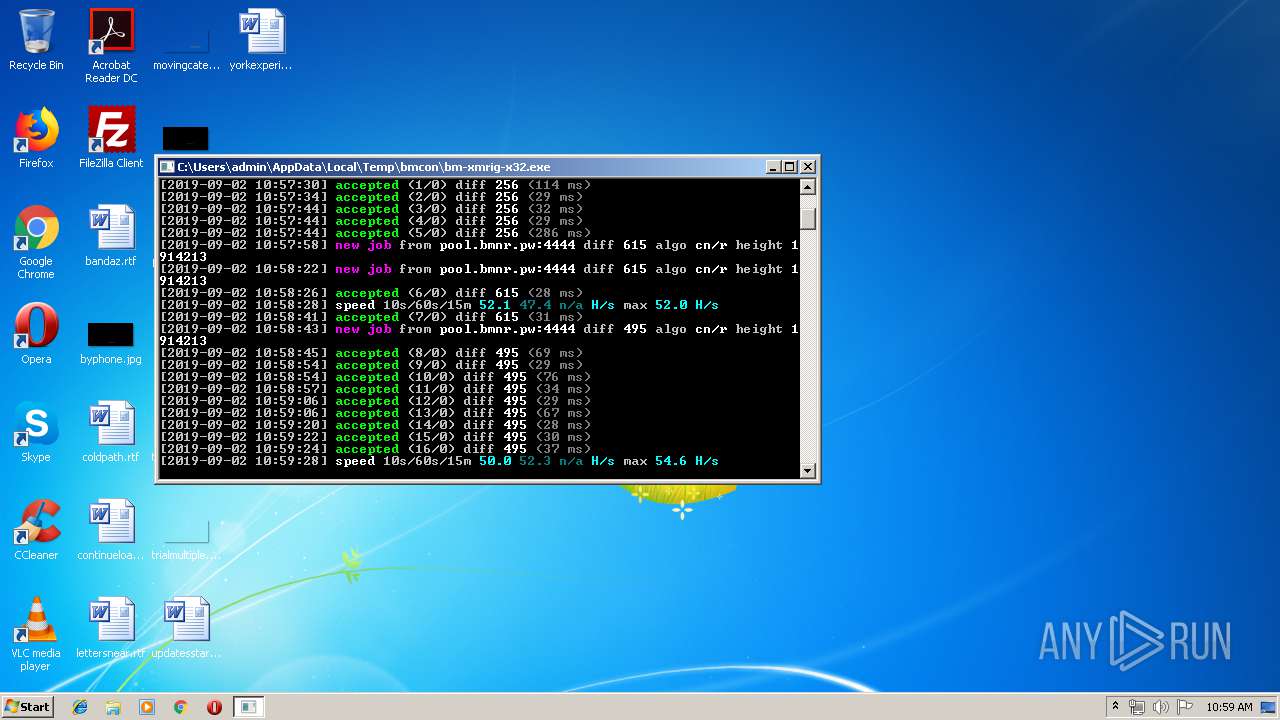
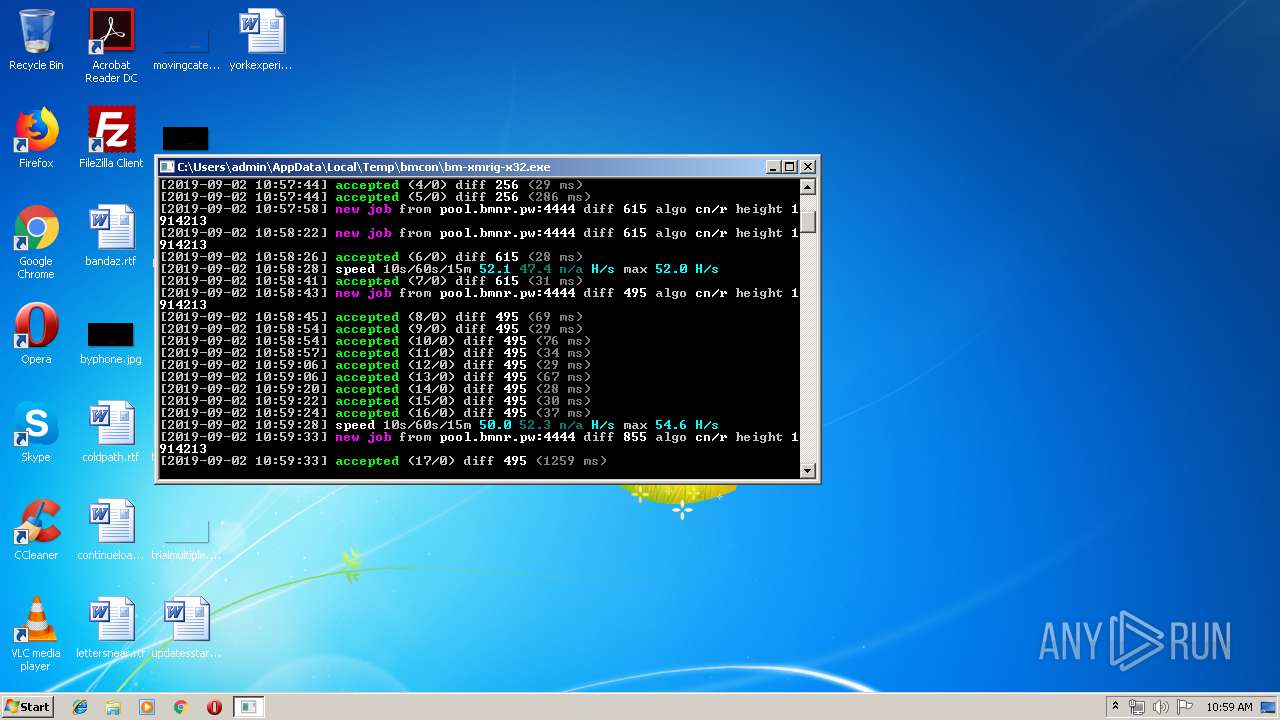
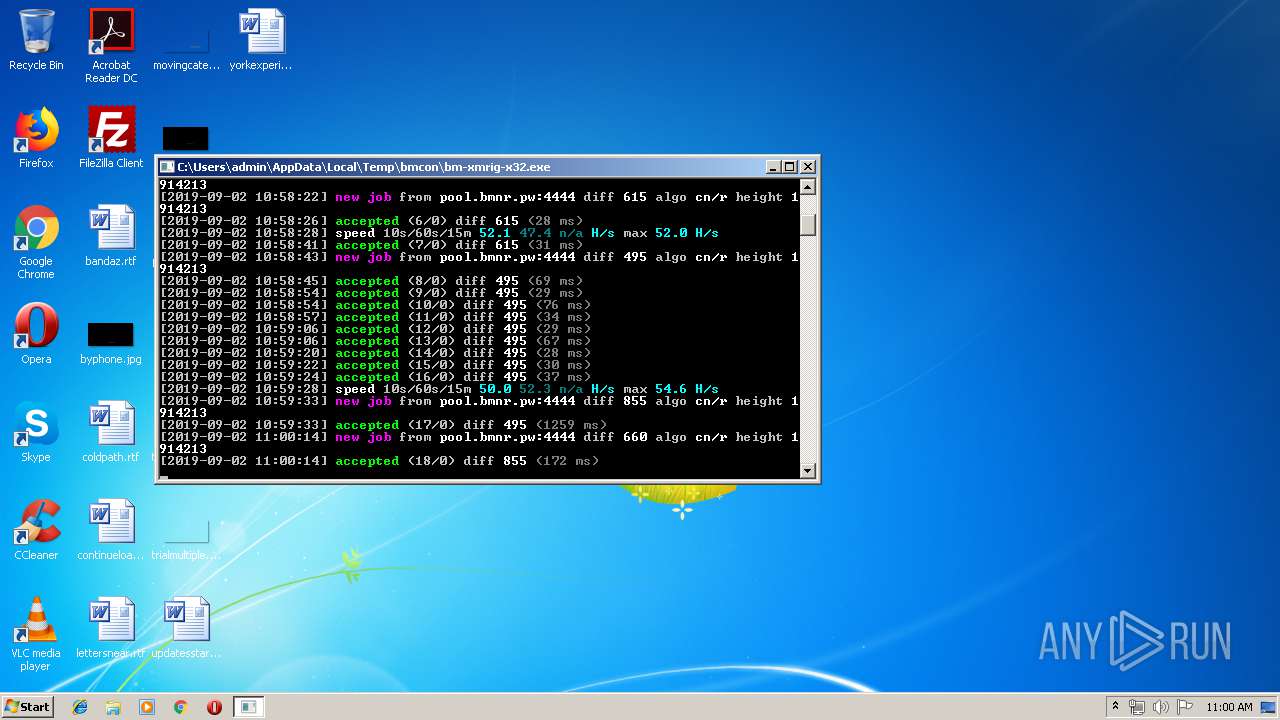
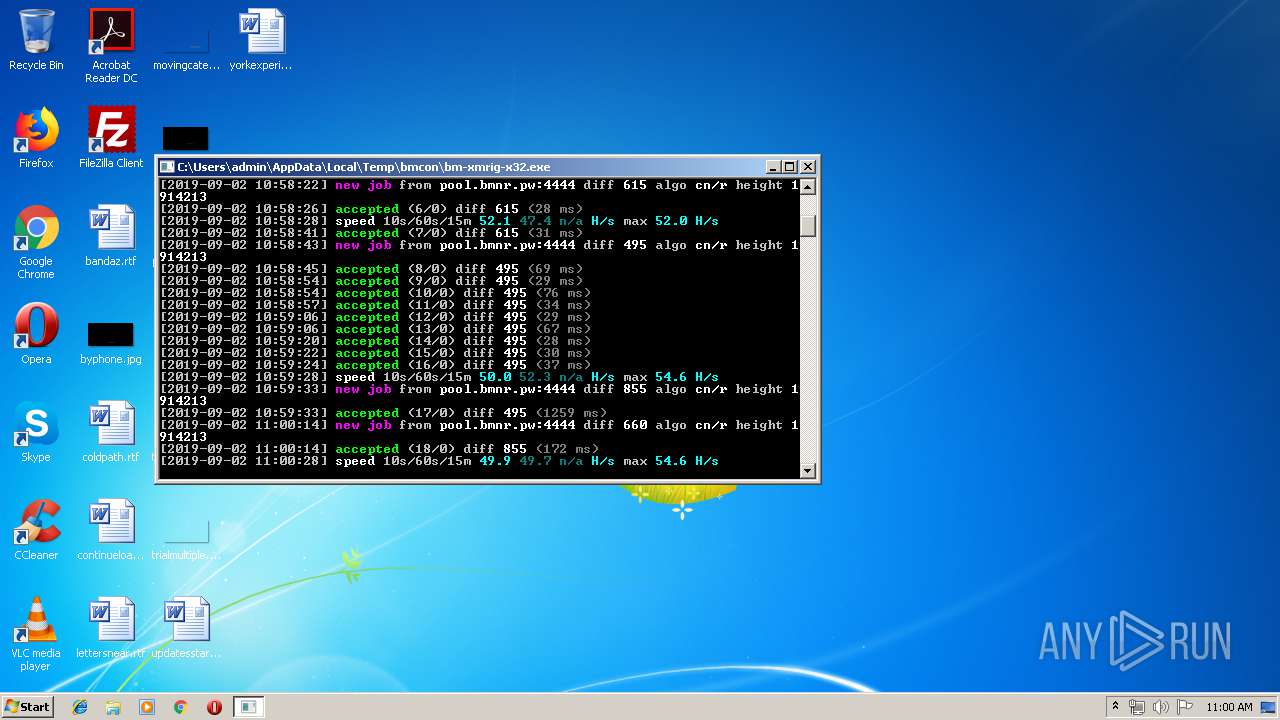
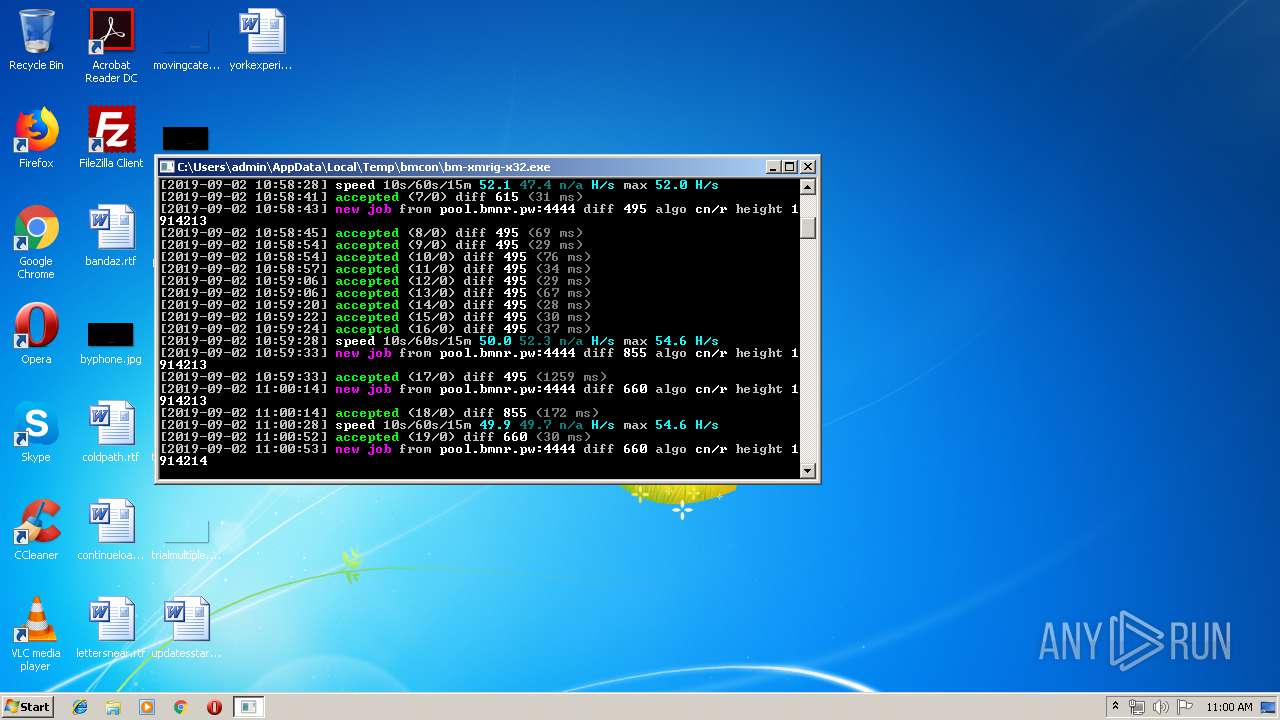
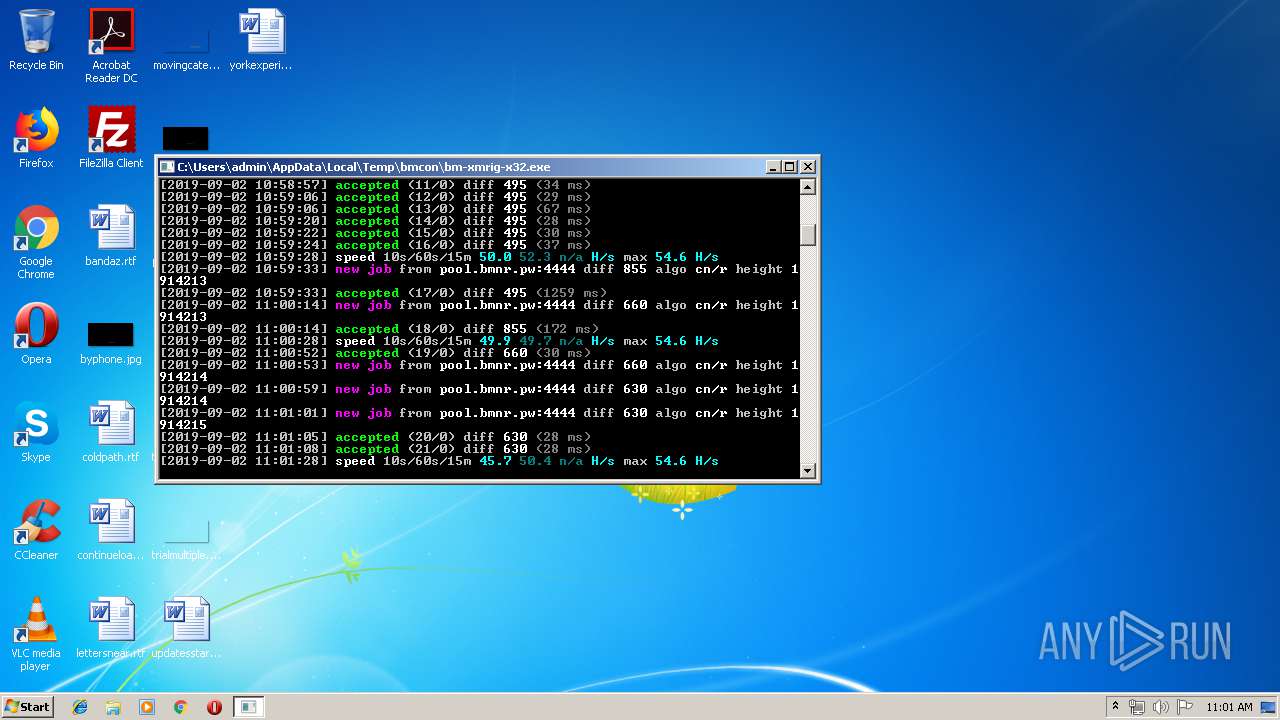
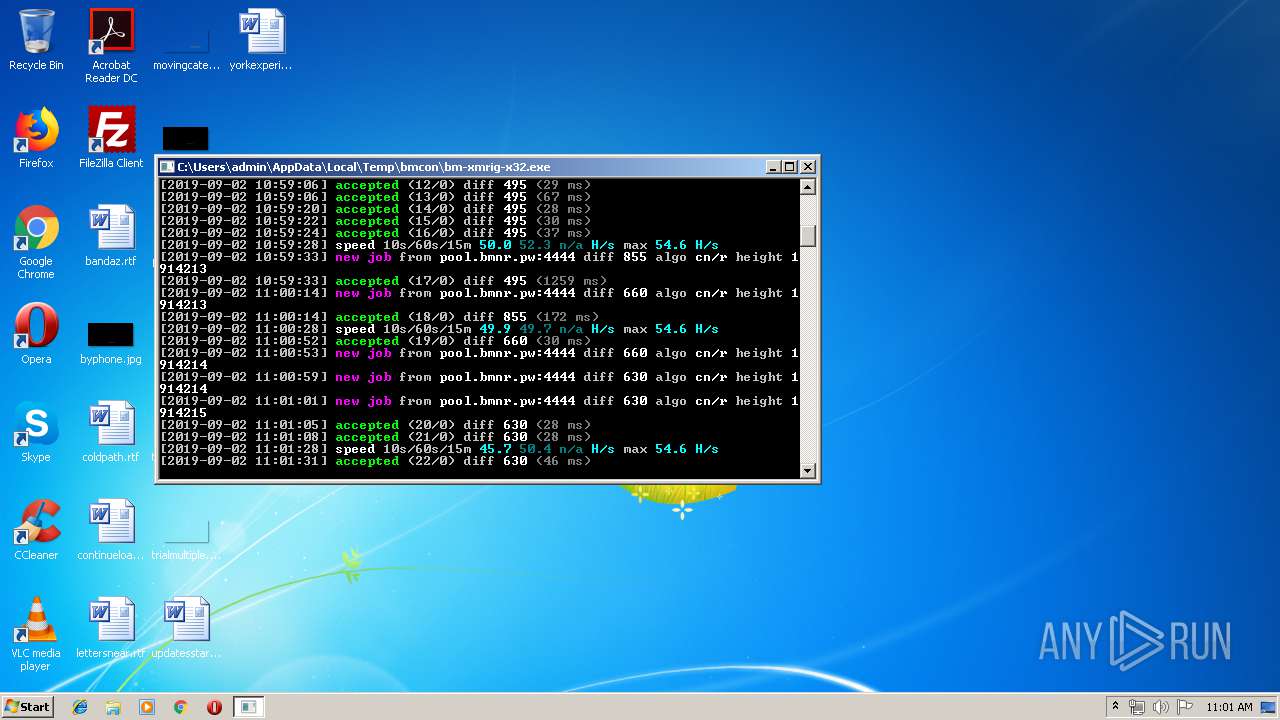
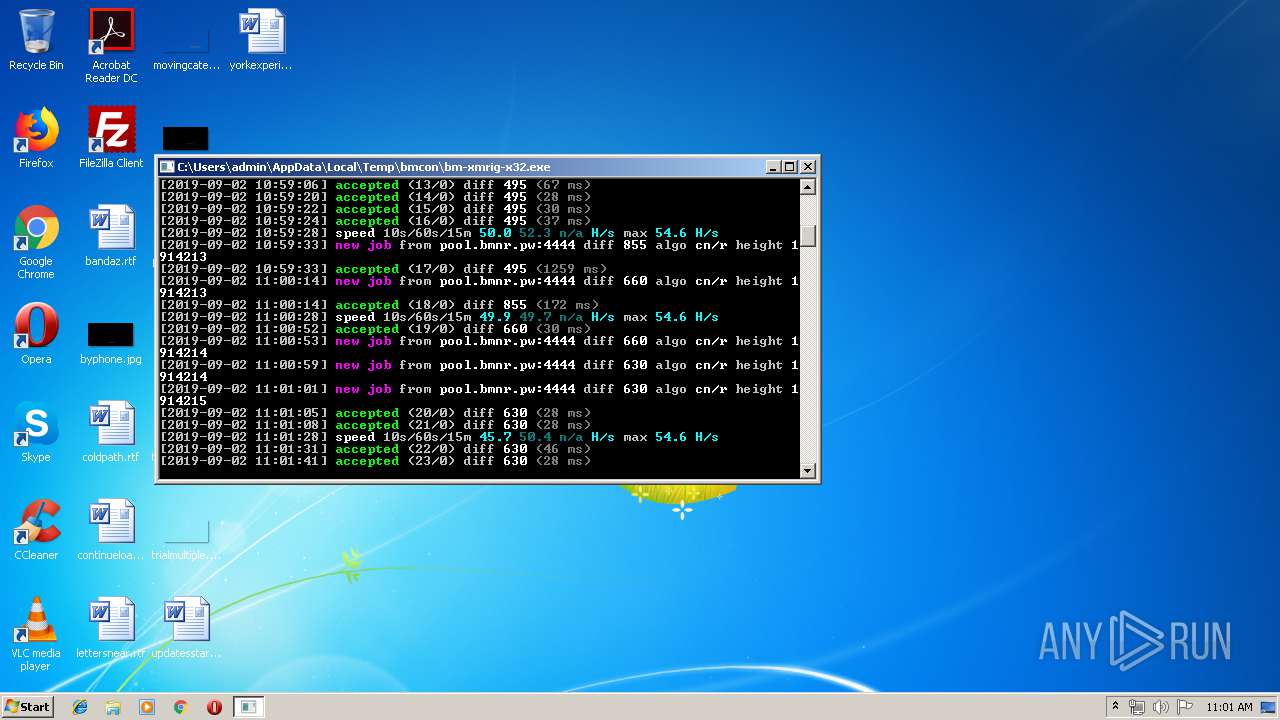
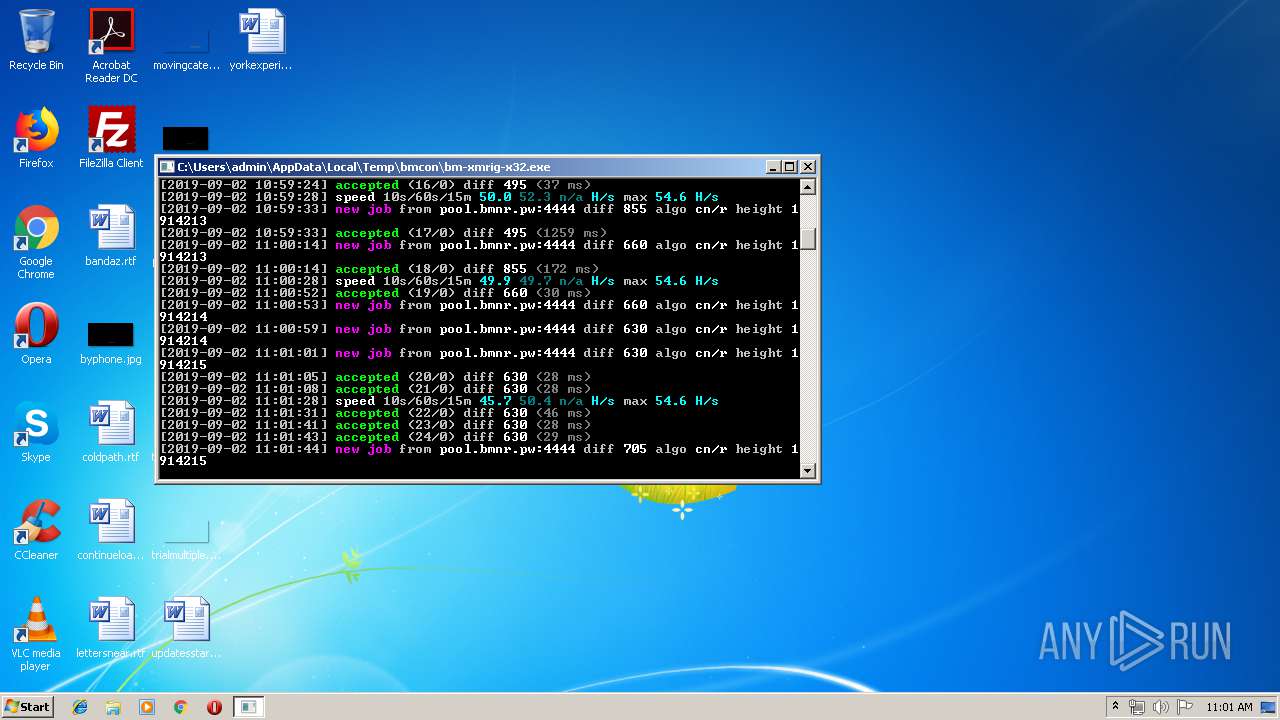
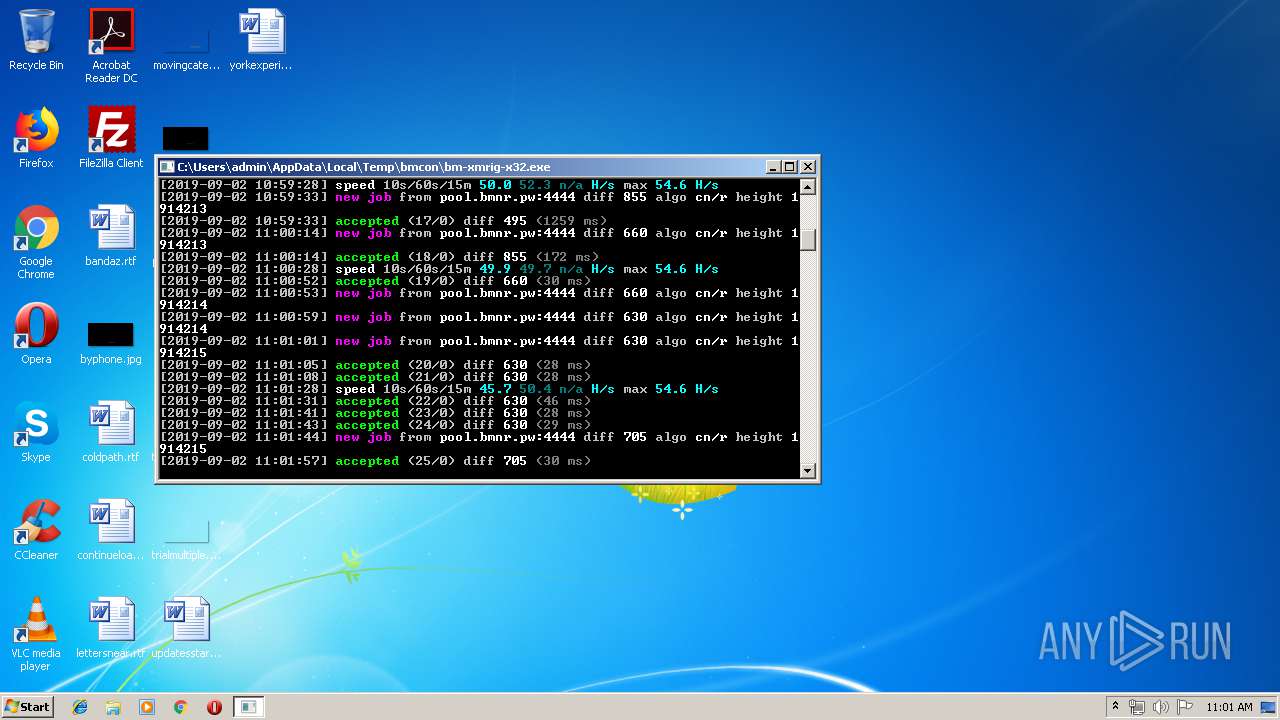
MINER was detected
- bm-xmrig-x32.exe (PID: 3892)
Connects to CnC server
- bm-xmrig-x32.exe (PID: 3892)
Changes settings of System certificates
- bmcon.exe (PID: 3016)
SUSPICIOUS
Adds / modifies Windows certificates
- bmcon.exe (PID: 3016)
Executable content was dropped or overwritten
- bmcon.exe (PID: 3016)
Connects to unusual port
- bm-xmrig-x32.exe (PID: 3892)
INFO
Drop XMRig executable file
- bmcon.exe (PID: 3016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (61.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.8) |
| .exe | | | Win32 Executable (generic) (10.1) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:03 01:42:21+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 360448 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 1069056 |
| EntryPoint: | 0x15db50 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 03-Nov-2018 00:42:21 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 03-Nov-2018 00:42:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00105000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00106000 | 0x00058000 | 0x00057E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92639 |
.rsrc | 0x0015E000 | 0x00001000 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.00727 |
Imports
KERNEL32.DLL |
advapi32.dll |
msvcrt.dll |
netapi32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
wininet.dll |
wsock32.dll |
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
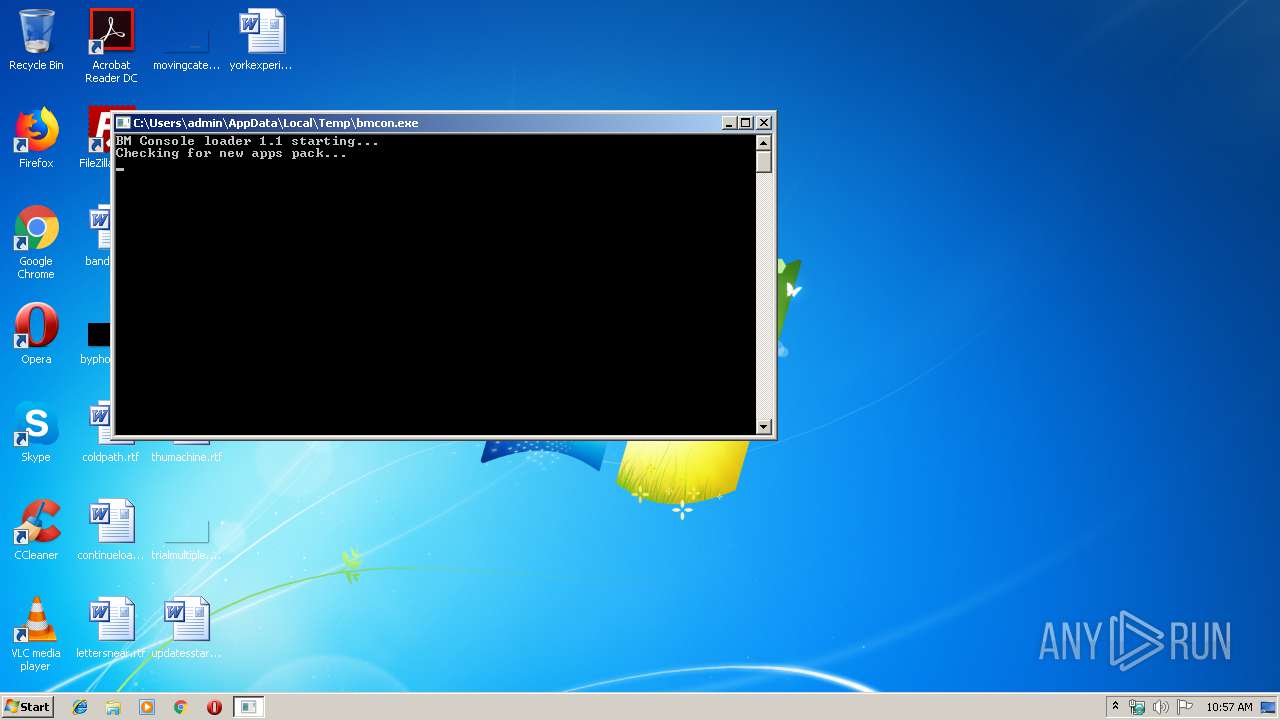
| 3016 | "C:\Users\admin\AppData\Local\Temp\bmcon.exe" | C:\Users\admin\AppData\Local\Temp\bmcon.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
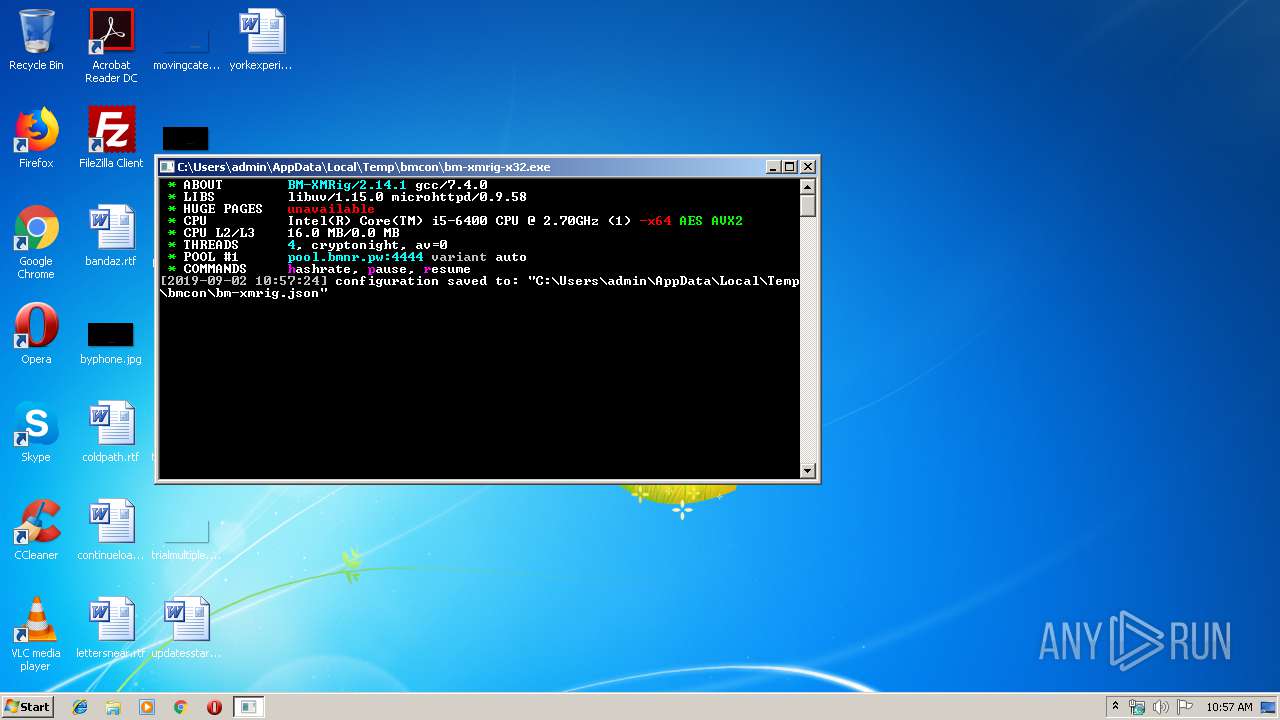
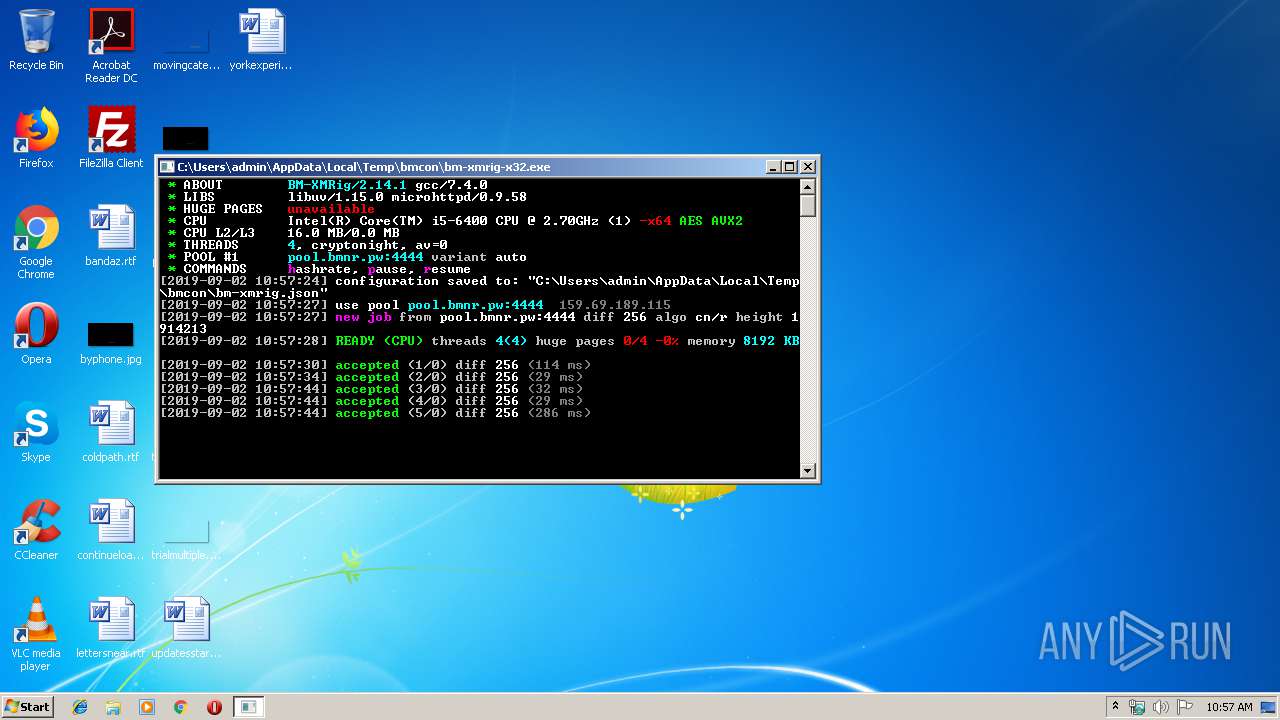
| 3892 | "C:\Users\admin\AppData\Local\Temp\bmcon\bm-xmrig-x32.exe" | C:\Users\admin\AppData\Local\Temp\bmcon\bm-xmrig-x32.exe | bmstart.exe | ||||||||||||
User: admin Company: www.xmrig.com Integrity Level: MEDIUM Description: BM-XMRig CPU miner Exit code: 0 Version: 2.14.1 Modules
| |||||||||||||||
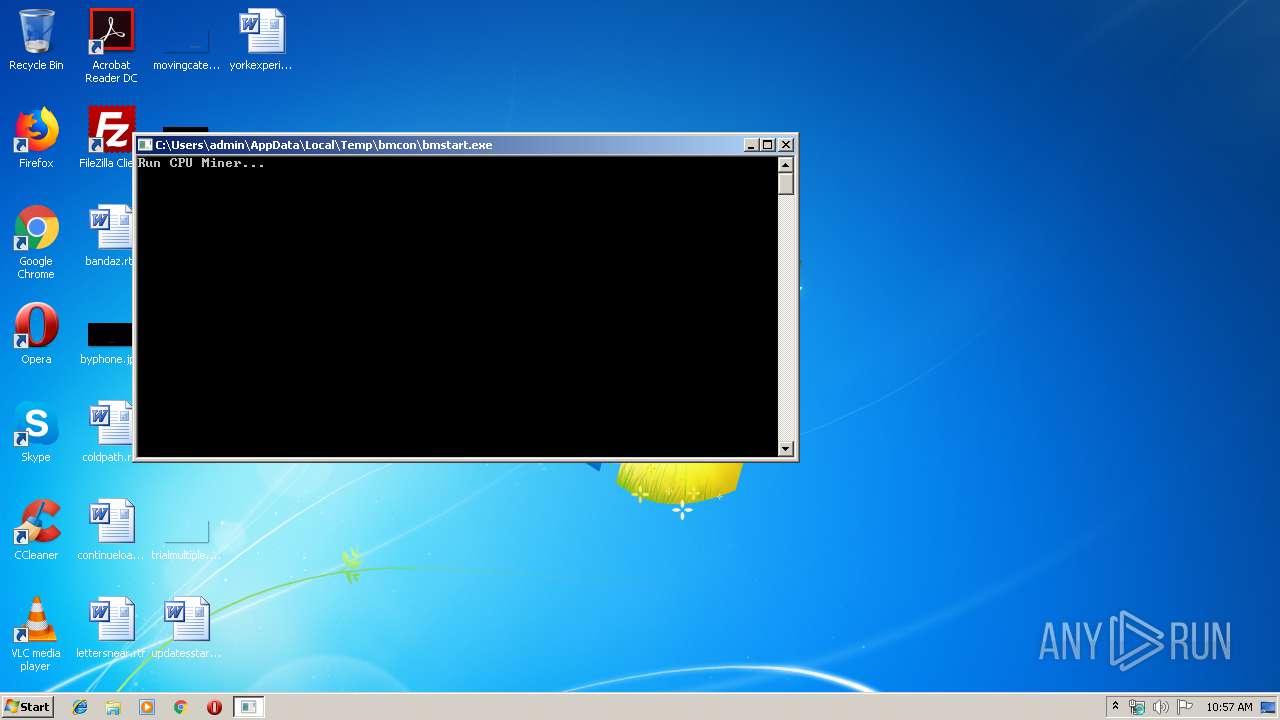
| 4060 | "C:\Users\admin\AppData\Local\Temp\bmcon\bmstart.exe" --conf="C:\Users\admin\AppData\Local\Temp\bmcon.json" | C:\Users\admin\AppData\Local\Temp\bmcon\bmstart.exe | — | bmcon.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
756
Read events
721
Write events
34
Delete events
1
Modification events
| (PID) Process: | (3016) bmcon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bmcon_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3016) bmcon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bmcon_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3016) bmcon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bmcon_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3016) bmcon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bmcon_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3016) bmcon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bmcon_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3016) bmcon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bmcon_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3016) bmcon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bmcon_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3016) bmcon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bmcon_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3016) bmcon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bmcon_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3016) bmcon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bmcon_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
11
Suspicious files
1
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3016 | bmcon.exe | C:\Users\admin\AppData\Local\Temp\bmcon\bm-xmrig-nvidia-cuda8.exe | executable | |
MD5:— | SHA256:— | |||
| 3016 | bmcon.exe | C:\Users\admin\AppData\Local\Temp\bmcon\bm-xmrig-amd.exe | executable | |
MD5:— | SHA256:— | |||
| 3016 | bmcon.exe | C:\Users\admin\AppData\Local\Temp\bmcon\apps.json | text | |
MD5:— | SHA256:— | |||
| 3016 | bmcon.exe | C:\Users\admin\AppData\Local\Temp\apps.temp.zip | compressed | |
MD5:— | SHA256:— | |||
| 3016 | bmcon.exe | C:\Users\admin\AppData\Local\Temp\bmcon\bm-xmrig-nvidia.exe | executable | |
MD5:— | SHA256:— | |||
| 3016 | bmcon.exe | C:\Users\admin\AppData\Local\Temp\bmcon\bmstart.exe | executable | |
MD5:— | SHA256:— | |||
| 3016 | bmcon.exe | C:\Users\admin\AppData\Local\Temp\bmcon\bm-xmrig.exe | executable | |
MD5:— | SHA256:— | |||
| 3016 | bmcon.exe | C:\Users\admin\AppData\Local\Temp\bmcon\bm-xmrig-x32.exe | executable | |
MD5:— | SHA256:— | |||
| 3016 | bmcon.exe | C:\Users\admin\AppData\Local\Temp\bmcon\nvrtc-builtins64_80.dll | executable | |
MD5:— | SHA256:— | |||
| 3016 | bmcon.exe | C:\Users\admin\AppData\Local\Temp\bmcon\nvrtc-builtins64_100.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
2
Threats
10
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3016 | bmcon.exe | 88.99.38.225:443 | dl.browsermine.com | Hetzner Online GmbH | DE | unknown |
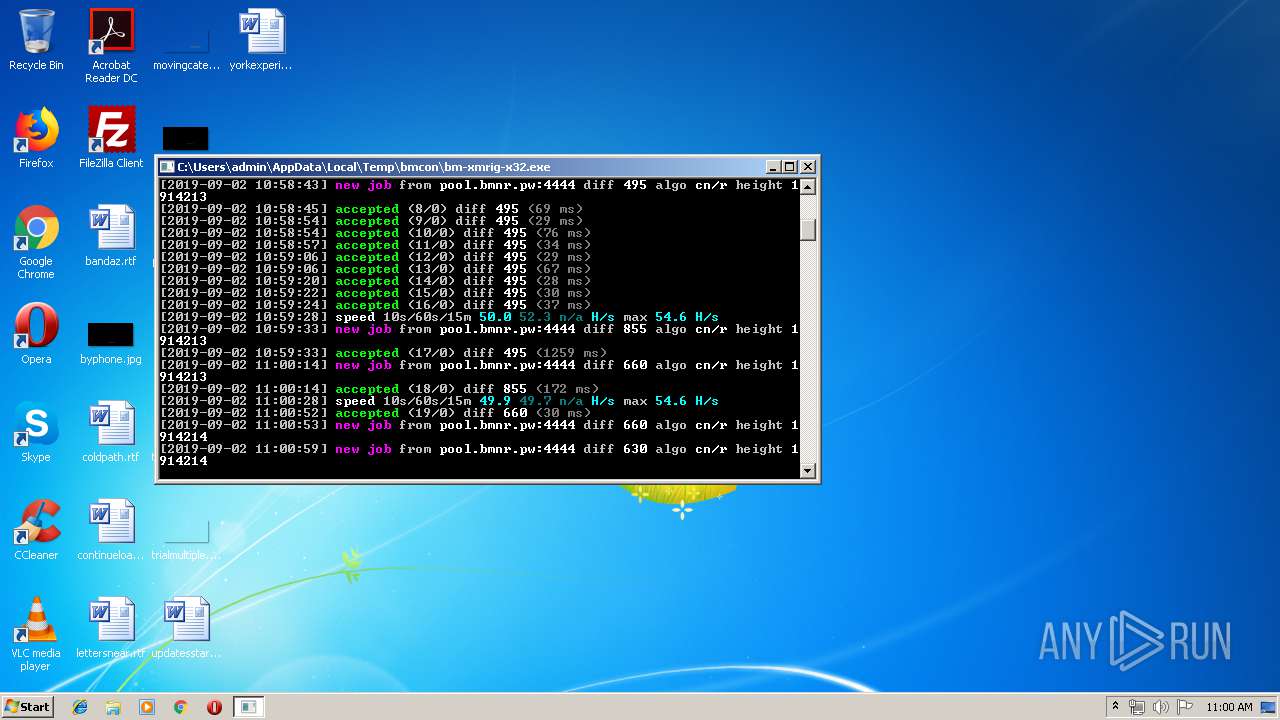
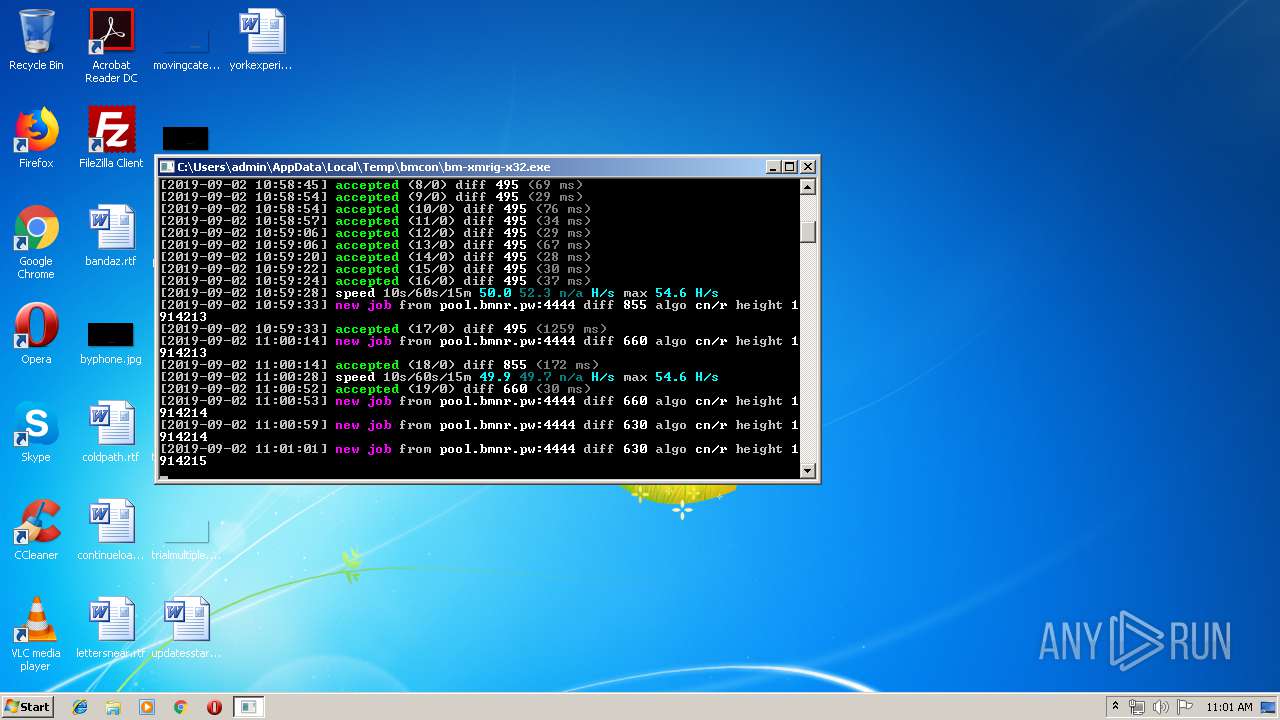
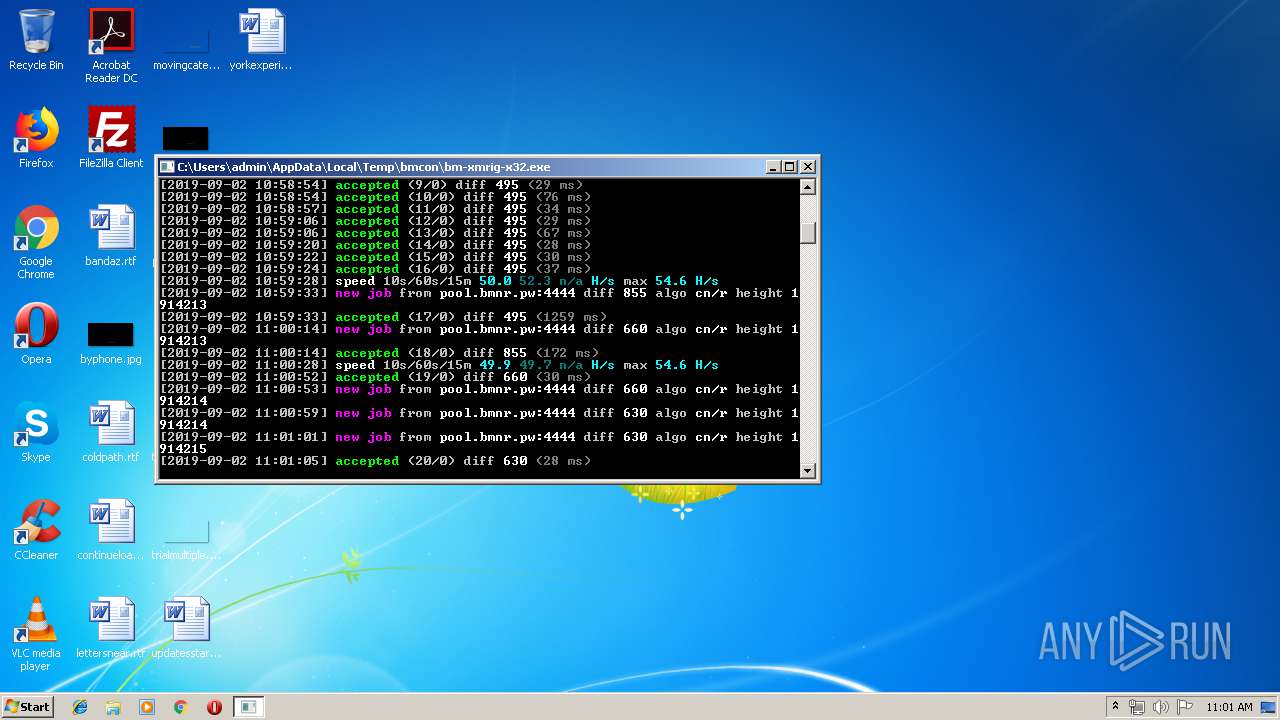
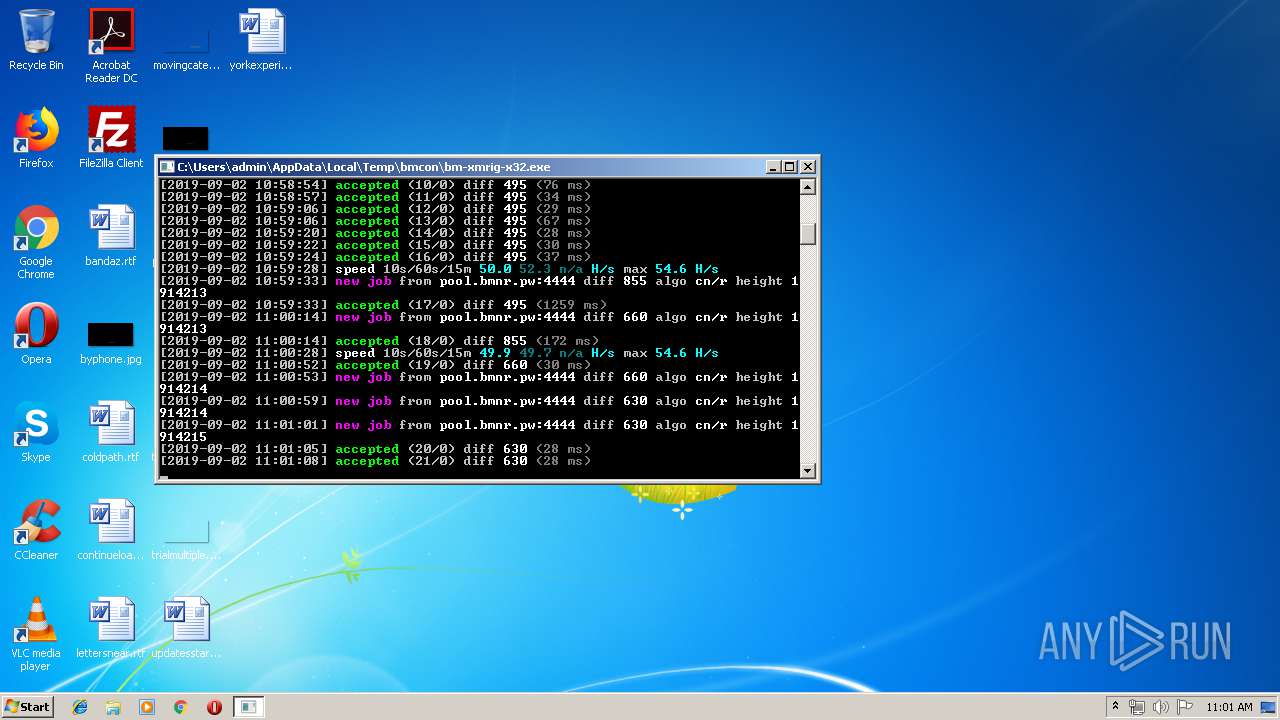
3892 | bm-xmrig-x32.exe | 159.69.189.115:4444 | pool.bmnr.pw | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.browsermine.com |
| unknown |
pool.bmnr.pw |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
3892 | bm-xmrig-x32.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
3892 | bm-xmrig-x32.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
3892 | bm-xmrig-x32.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight algo JSON_RPC server Response |
3892 | bm-xmrig-x32.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
3892 | bm-xmrig-x32.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight algo JSON_RPC server Response |
3892 | bm-xmrig-x32.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
3892 | bm-xmrig-x32.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight algo JSON_RPC server Response |
2 ETPRO signatures available at the full report