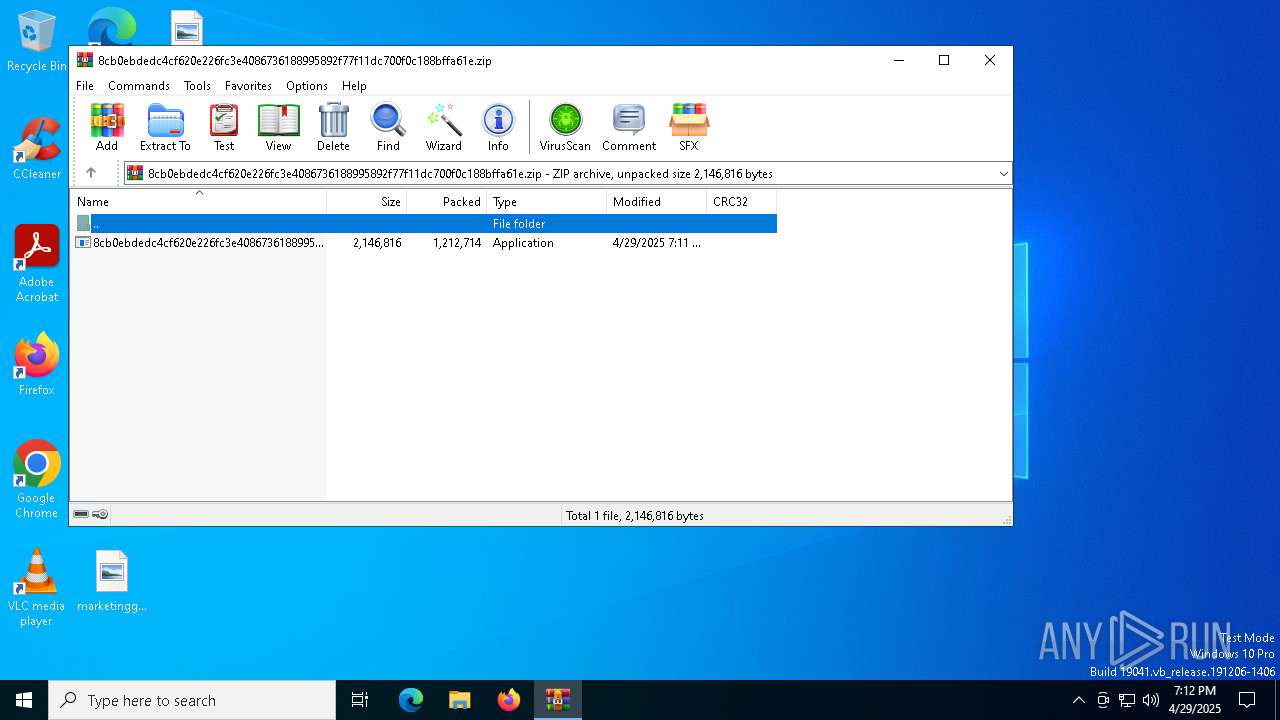
| File name: | 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.zip |
| Full analysis: | https://app.any.run/tasks/1833b1e2-87c6-4d22-be88-068bc02e6407 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 29, 2025, 19:11:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
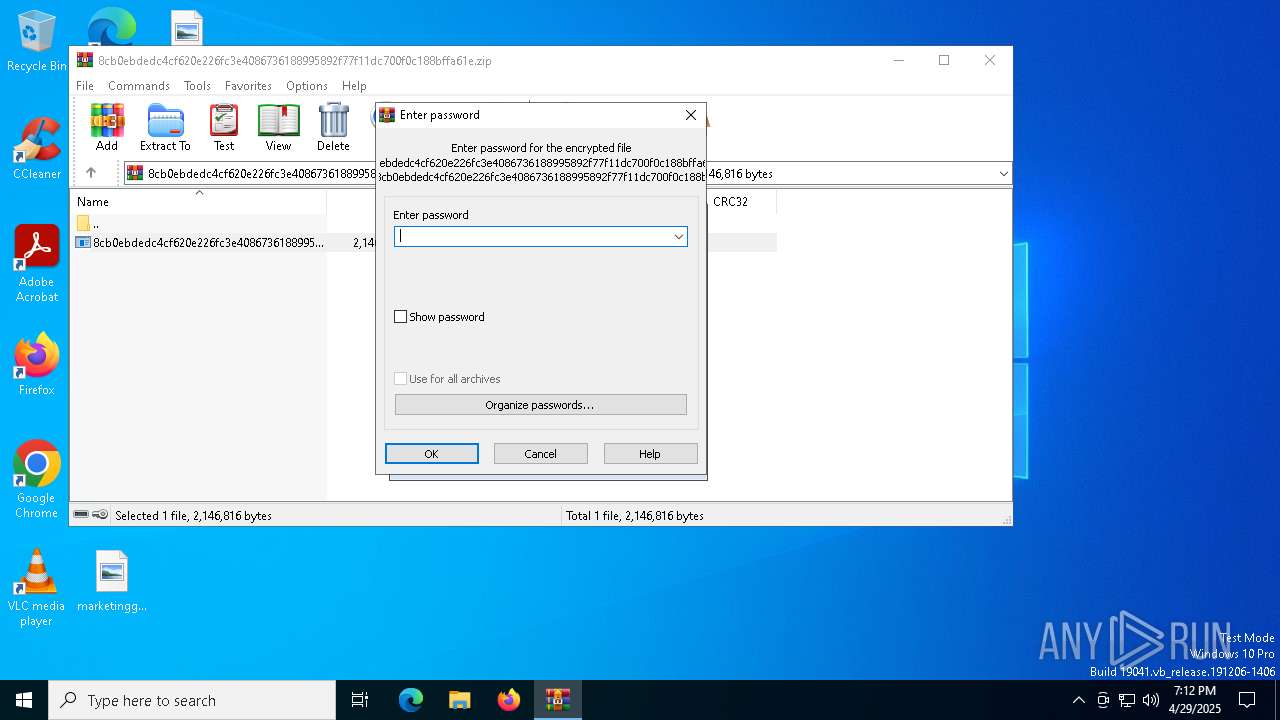
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | FC789296B48C5CDBF2095FC5D89660D2 |
| SHA1: | A63AEB1FC7C09B2B6ACE982FA55294D8F7148FFE |
| SHA256: | 4023C8A18B82A9212C6331DE8AEF395E0154223098A8C6C31C5242517ED6345F |
| SSDEEP: | 49152:rPJBsc2ETOyCXeajDYpaZt3rJgLMS82JKZ3GOtpHQm6ayHU+sOTD35kziihUXGx1:L2ETOyCjMUjSIZpwBL9Tz5qXhUXGxecN |
MALICIOUS
Runs injected code in another process
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4120)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 1388)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4620)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2092)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 6252)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2516)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 5528)
Actions looks like stealing of personal data
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4120)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 1388)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4620)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2092)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 6252)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2516)
Application was injected by another process
- explorer.exe (PID: 5492)
ASYNCRAT has been detected (SURICATA)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4120)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 1388)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4620)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2092)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 6252)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2516)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5544)
Connects to unusual port
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4120)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 1388)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4620)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2092)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 6252)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2516)
Contacting a server suspected of hosting an CnC
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4120)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 1388)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4620)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 6252)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2092)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2516)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 5544)
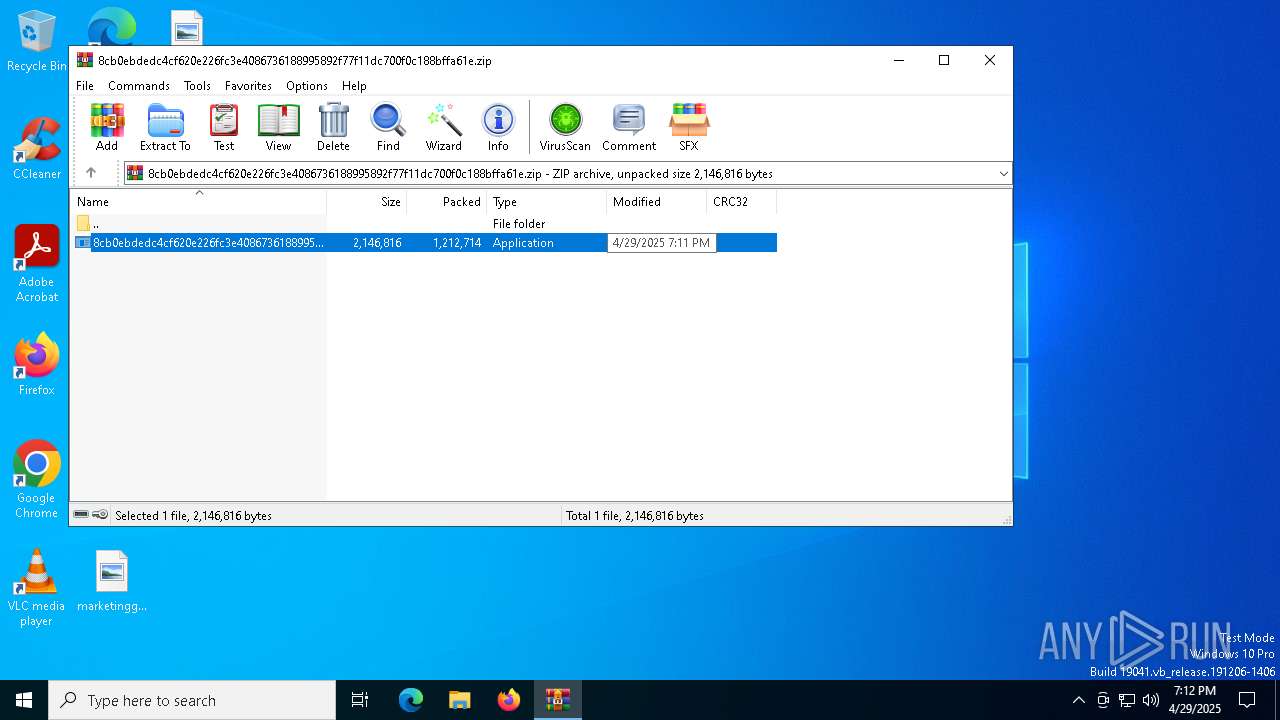
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5544)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5492)
Checks supported languages
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4120)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 1388)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4620)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2092)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 6252)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 5528)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2516)
Reads the computer name
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4120)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 1388)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4620)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2092)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 6252)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2516)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 5528)
Reads the machine GUID from the registry
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4120)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 1388)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4620)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2092)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 6252)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2516)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 5528)
Reads the software policy settings
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4120)
- slui.exe (PID: 6736)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4620)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 1388)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 6252)
- slui.exe (PID: 3008)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2092)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2516)
Manual execution by a user
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 1388)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 4620)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2092)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 6252)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 5528)
- 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe (PID: 2516)
Checks proxy server information
- slui.exe (PID: 3008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:04:29 19:11:32 |
| ZipCRC: | 0x7f455aed |
| ZipCompressedSize: | 1212714 |
| ZipUncompressedSize: | 2146816 |
| ZipFileName: | 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe |
Total processes
139
Monitored processes
13
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1388 | C:\WINDOWS\Explorer.EXE | C:\Users\admin\AppData\Local\Temp\Rar$EXb5544.23646\8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | explorer.exe | ||||||||||||
User: admin Company: Steganos Software GmbH Integrity Level: MEDIUM Description: Steganos Trace Destructor Browser Monitor Exit code: 0 Version: 22.5.4.14015 Modules
| |||||||||||||||
| 2092 | C:\WINDOWS\Explorer.EXE | C:\Users\admin\AppData\Local\Temp\Rar$EXb5544.23646\8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | explorer.exe | ||||||||||||
User: admin Company: Steganos Software GmbH Integrity Level: MEDIUM Description: Steganos Trace Destructor Browser Monitor Exit code: 0 Version: 22.5.4.14015 Modules
| |||||||||||||||
| 2140 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2516 | C:\WINDOWS\Explorer.EXE | C:\Users\admin\AppData\Local\Temp\Rar$EXb5544.23646\8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | explorer.exe | ||||||||||||
User: admin Company: Steganos Software GmbH Integrity Level: MEDIUM Description: Steganos Trace Destructor Browser Monitor Exit code: 0 Version: 22.5.4.14015 Modules
| |||||||||||||||
| 3008 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb5544.23646\8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb5544.23646\8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | WinRAR.exe | ||||||||||||
User: admin Company: Steganos Software GmbH Integrity Level: MEDIUM Description: Steganos Trace Destructor Browser Monitor Exit code: 0 Version: 22.5.4.14015 Modules
| |||||||||||||||
| 4620 | C:\WINDOWS\Explorer.EXE | C:\Users\admin\AppData\Local\Temp\Rar$EXb5544.23646\8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | explorer.exe | ||||||||||||
User: admin Company: Steganos Software GmbH Integrity Level: MEDIUM Description: Steganos Trace Destructor Browser Monitor Exit code: 0 Version: 22.5.4.14015 Modules
| |||||||||||||||
| 5492 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5528 | C:\WINDOWS\Explorer.EXE | C:\Users\admin\AppData\Local\Temp\Rar$EXb5544.23646\8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | explorer.exe | ||||||||||||
User: admin Company: Steganos Software GmbH Integrity Level: MEDIUM Description: Steganos Trace Destructor Browser Monitor Version: 22.5.4.14015 Modules
| |||||||||||||||
Total events
23 862
Read events
23 850
Write events
12
Delete events
0
Modification events
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000000000000000000000 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:000000000006028A |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.zip | |||
| (PID) Process: | (5544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb5544.23646\8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | executable | |
MD5:89C7CB1B3E5CDA82DF568CD433D5A36A | SHA256:8CB0EBDEDC4CF620E226FC3E4086736188995892F77F11DC700F0C188BFFA61E | |||
| 5492 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
26
DNS requests
14
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4008 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4008 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4008 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
micromissingservicx86checksup.com |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4120 | 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
4120 | 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 31 |
4120 | 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
1388 | 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
1388 | 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
4620 | 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
4620 | 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
2092 | 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
2092 | 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
6252 | 8cb0ebdedc4cf620e226fc3e4086736188995892f77f11dc700f0c188bffa61e.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |