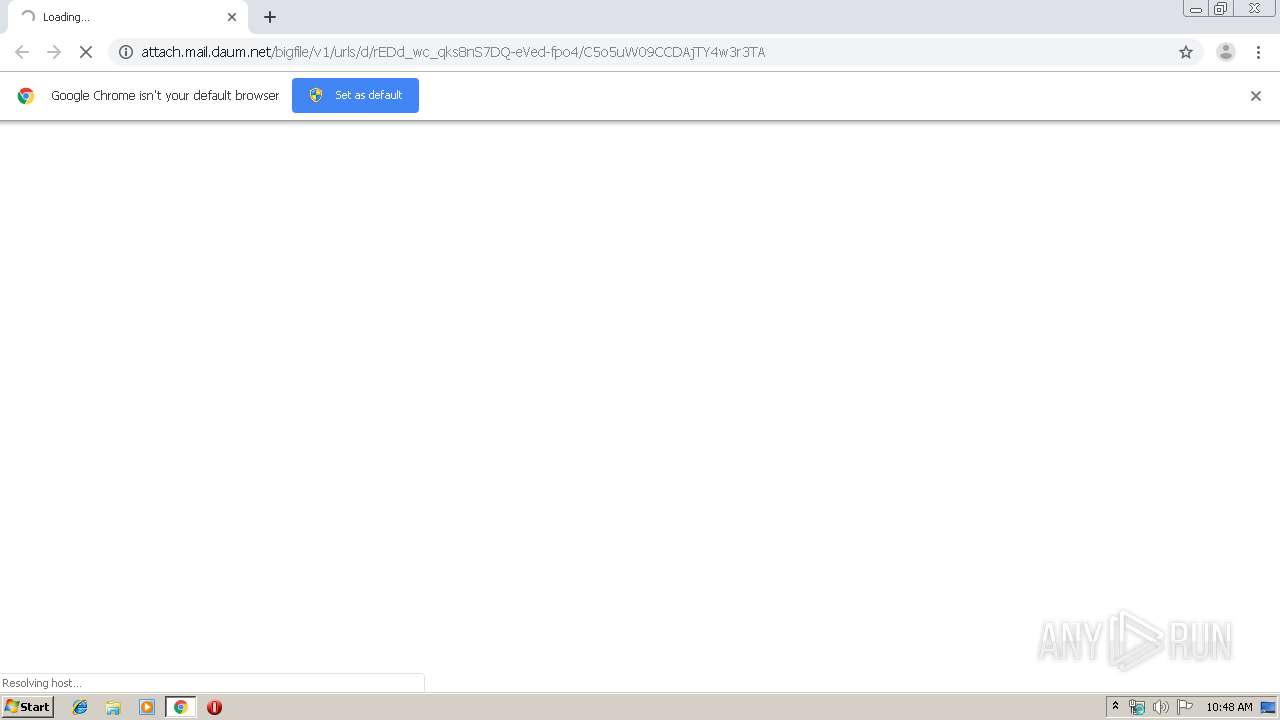
| URL: | http://attach.mail.daum.net/bigfile/v1/urls/d/rEDd_wc_qks8nS7DQ-eVed-fpo4/C5o5uW09CCDAjTY4w3r3TA |
| Full analysis: | https://app.any.run/tasks/c7d4c256-d54b-4cc7-9e91-fec8fa50836f |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | January 08, 2020, 10:47:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F4DB239C99CFD8DA2D0A8445C335B690 |
| SHA1: | 9C42D772EFF2C9153BD207B7FE36A6BBDBDE673F |
| SHA256: | 3FCC604449DCD7C8B503E4C8811B2D5A79134CA58F27882E7D9341CDE6F52105 |
| SSDEEP: | 3:N1KfOlFDIL0RgxGY5G/DCHIAs+EsnLQy2RAAStk:CAFDhF/DCoAmY2RAAJ |
MALICIOUS
FORMBOOK was detected
- mstsc.exe (PID: 1556)
- explorer.exe (PID: 352)
- Firefox.exe (PID: 884)
Changes the autorun value in the registry
- mstsc.exe (PID: 1556)
Actions looks like stealing of personal data
- mstsc.exe (PID: 1556)
Stealing of credential data
- mstsc.exe (PID: 1556)
Connects to CnC server
- explorer.exe (PID: 352)
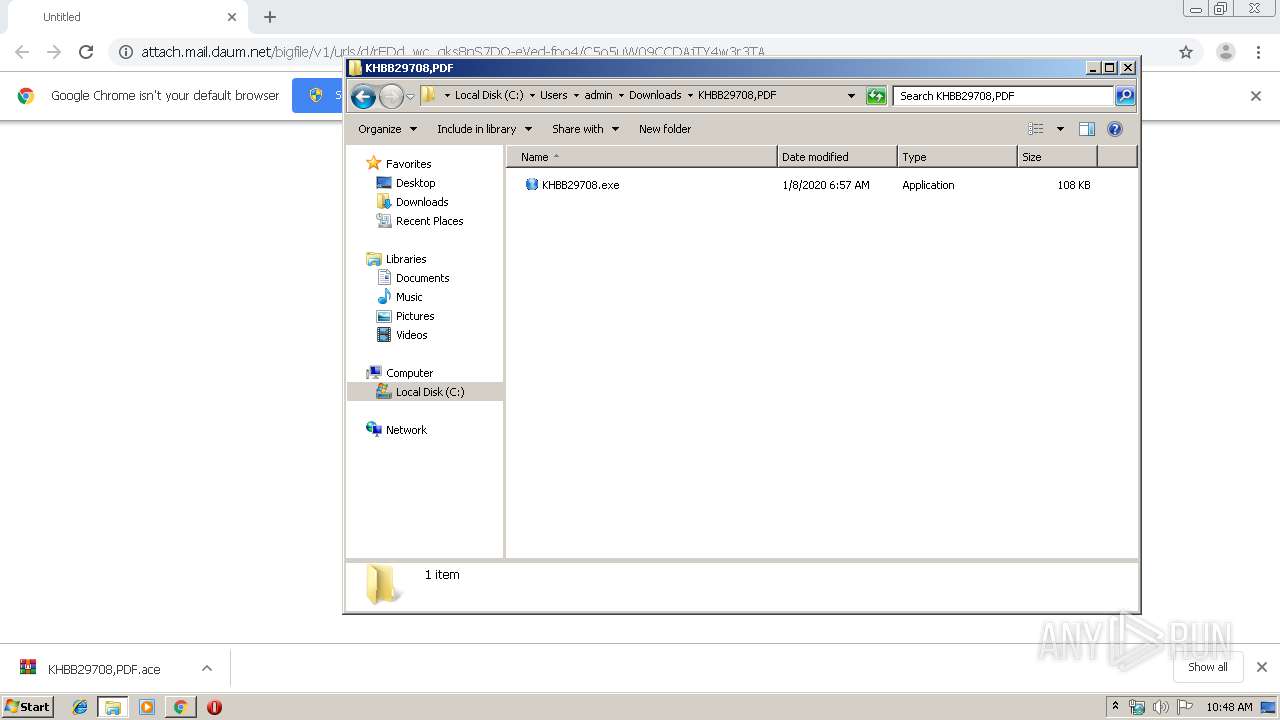
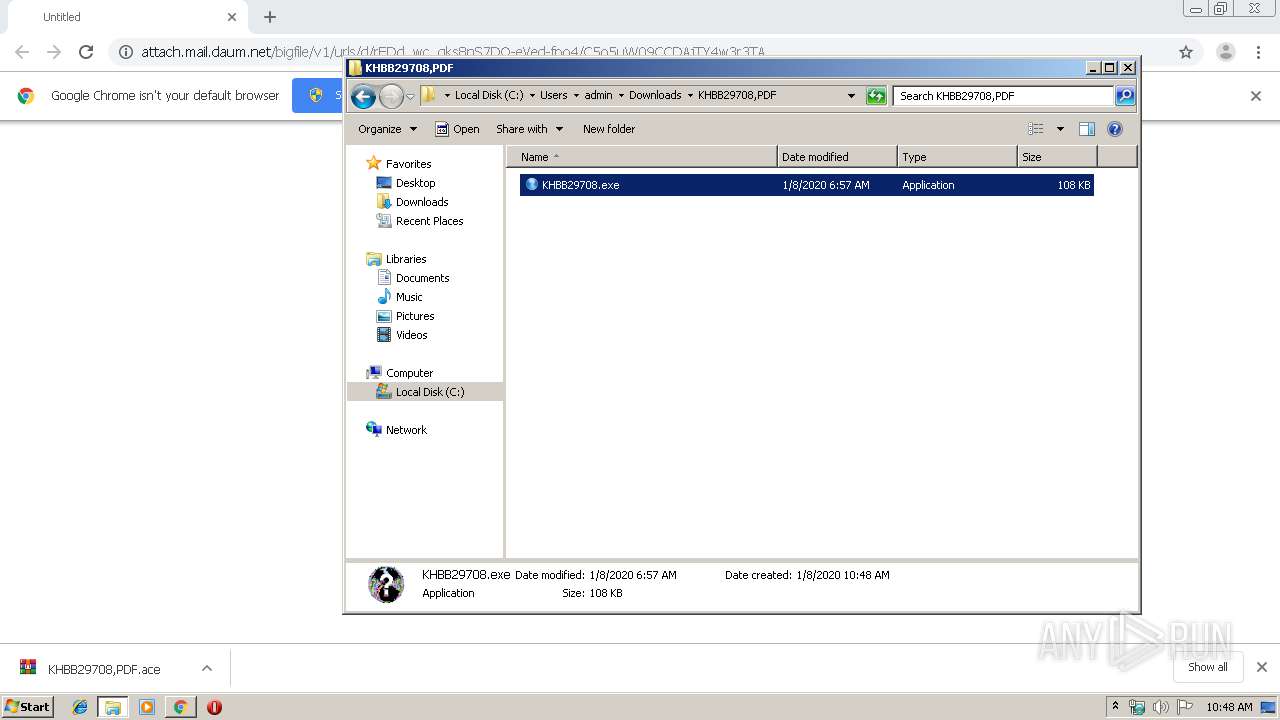
Application was dropped or rewritten from another process
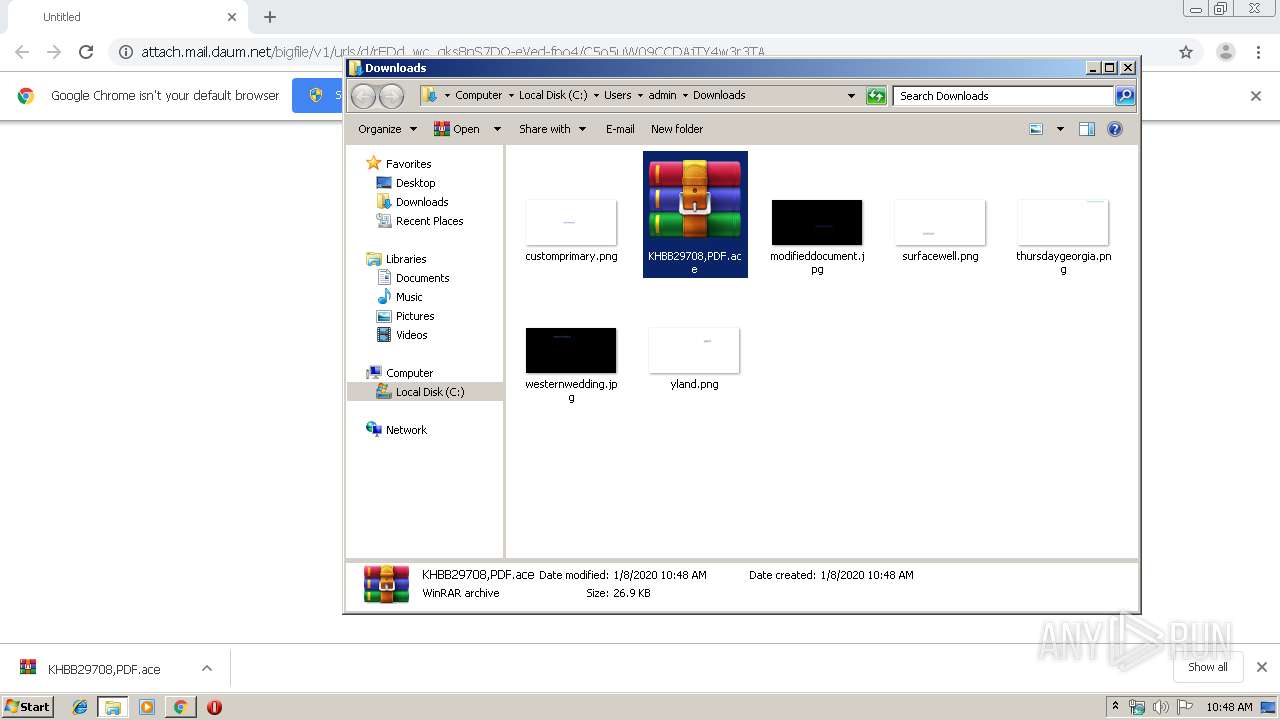
- KHBB29708.exe (PID: 2864)
- KHBB29708.exe (PID: 3864)
SUSPICIOUS
Starts CMD.EXE for commands execution
- mstsc.exe (PID: 1556)
Creates files in the user directory
- mstsc.exe (PID: 1556)
- explorer.exe (PID: 352)
- KHBB29708.exe (PID: 3864)
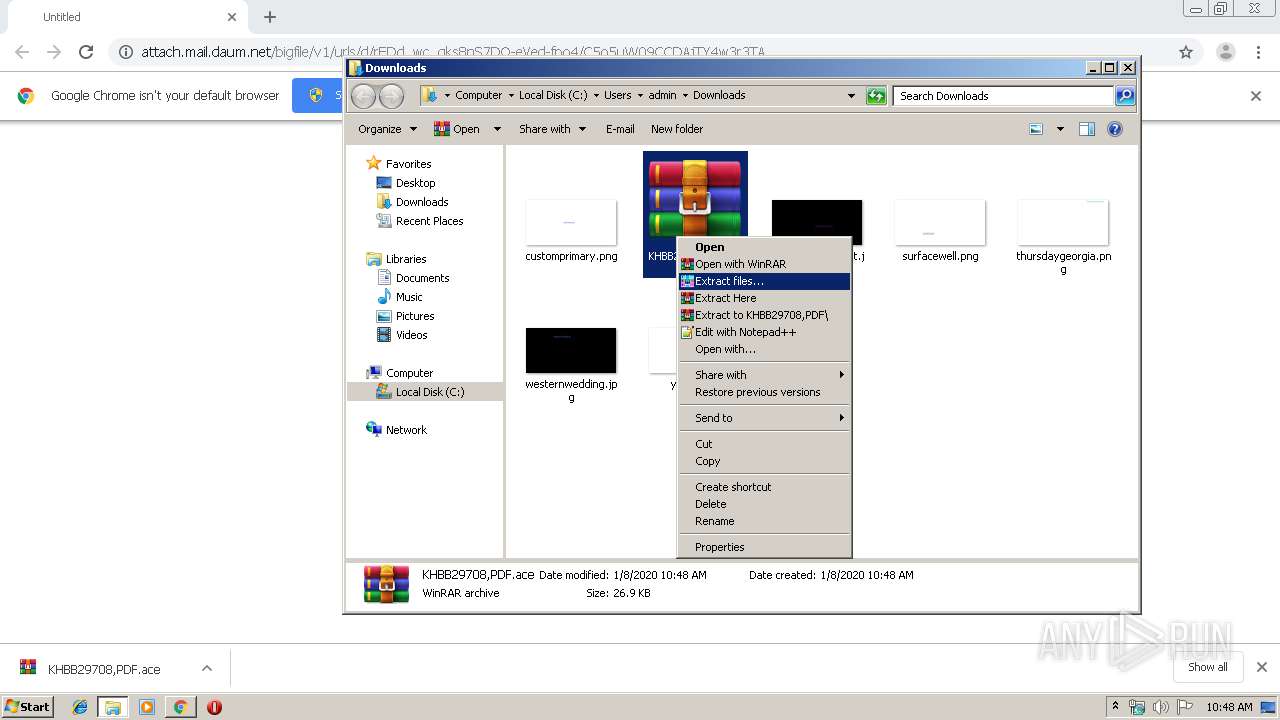
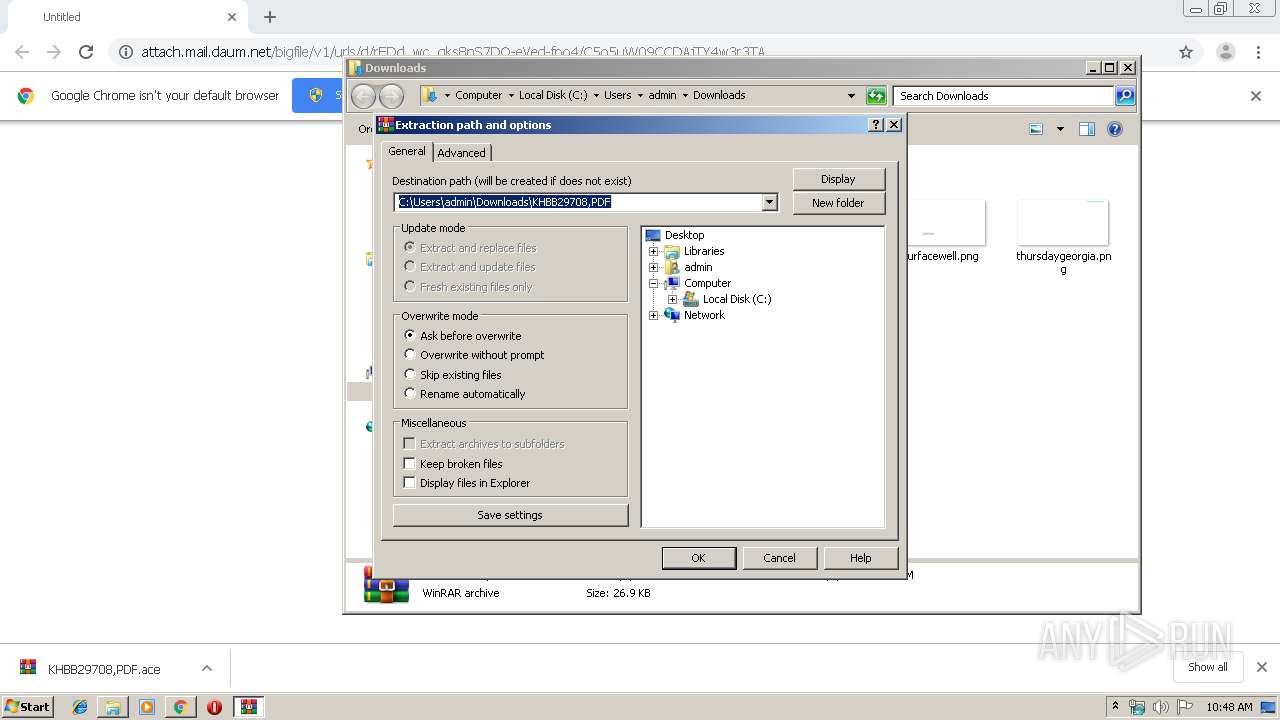
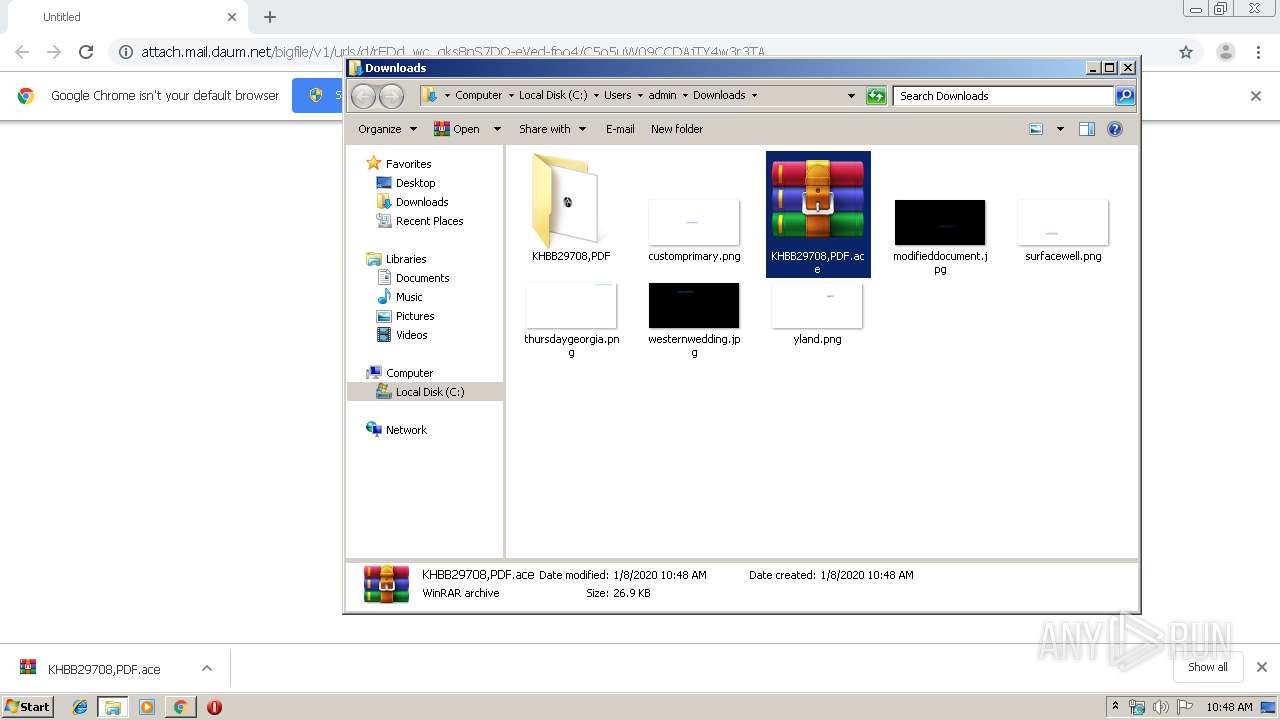
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3860)
Application launched itself
- KHBB29708.exe (PID: 2864)
Loads DLL from Mozilla Firefox
- mstsc.exe (PID: 1556)
INFO
Manual execution by user
- WinRAR.exe (PID: 3860)
- mstsc.exe (PID: 1556)
- KHBB29708.exe (PID: 2864)
Application launched itself
- chrome.exe (PID: 2608)
Reads the hosts file
- mstsc.exe (PID: 1556)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 184)
Reads Internet Cache Settings
- chrome.exe (PID: 2608)
Creates files in the user directory
- Firefox.exe (PID: 884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
18
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16319182642035176294 --mojo-platform-channel-handle=1520 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3491870220119411935 --mojo-platform-channel-handle=988 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | mstsc.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1248 | /c del "C:\Users\admin\Downloads\KHBB29708,PDF\KHBB29708.exe" | C:\Windows\System32\cmd.exe | — | mstsc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10112112075316952155 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1556 | "C:\Windows\System32\mstsc.exe" | C:\Windows\System32\mstsc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Remote Desktop Connection Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3722436061618304446 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15018578928713391385 --mojo-platform-channel-handle=3868 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13323232545093458829 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 938
Read events
1 696
Write events
239
Delete events
3
Modification events
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2608-13222954091518750 |
Value: 259 | |||
| (PID) Process: | (2608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2608) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
1
Suspicious files
97
Text files
66
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\799d63a3-a486-4c03-8518-65cf2e2abe79.tmp | — | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a91b.TMP | text | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a91b.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
22
DNS requests
16
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
184 | chrome.exe | GET | 302 | 113.29.190.53:80 | http://attach.mail.daum.net/bigfile/v1/urls/d/rEDd_wc_qks8nS7DQ-eVed-fpo4/C5o5uW09CCDAjTY4w3r3TA | KR | — | — | whitelisted |
352 | explorer.exe | GET | 302 | 50.116.72.183:80 | http://www.atlantacannabismagazine.com/t209/?QLr=uTm8ThkX1Jklx&Rz7tLh=/NUHYjD0vjOfz1uUsUzUSjFfsdiRdyl2RHin82h0QvC6nlgVl3R/VkJo8MEEh1MX5Soxvw==&sql=1 | US | html | 230 b | malicious |
352 | explorer.exe | POST | — | 50.116.72.183:80 | http://www.atlantacannabismagazine.com/t209/ | US | — | — | malicious |
352 | explorer.exe | GET | 404 | 63.250.34.167:80 | http://www.mansiobok.com/t209/?QLr=uTm8ThkX1Jklx&Rz7tLh=BaP8CQkg8xLuiDFDT24KUuOEVYfEcAMFjV6CkRctY5s5mFadI4Q/odfToIUauSLsUnBfgg== | US | html | 328 b | malicious |
352 | explorer.exe | POST | — | 50.116.72.183:80 | http://www.atlantacannabismagazine.com/t209/ | US | — | — | malicious |
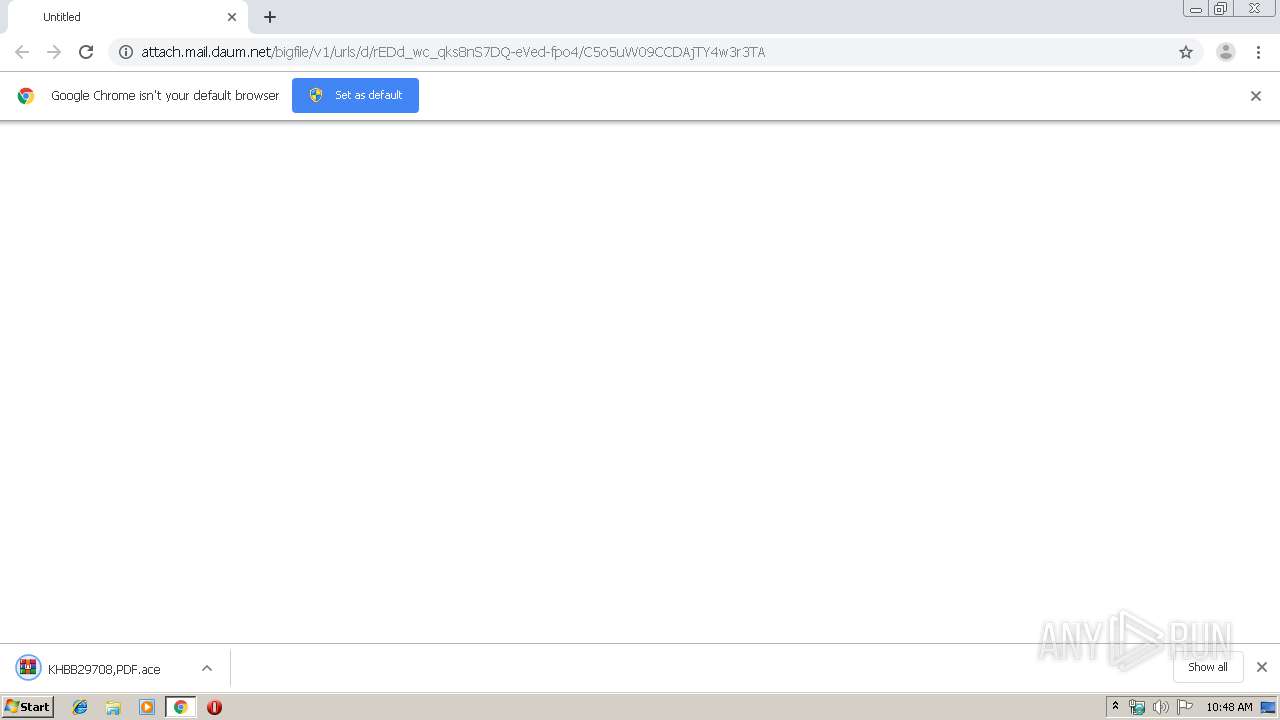
184 | chrome.exe | GET | 200 | 113.29.184.216:80 | http://maildn.daumcdn.net/mail_bigfile/jungjw222%40hanmail.net/attach/157846502768930/81530526_1/KHBB29708%2CPDF.ace?Expires=1578480793&TWGServiceId=mail_bigfile&Signature=i17iDZv4YQCzpipDQ1WUjT%2BSB0U%3D&x-content-disposition=attachment | KR | compressed | 26.9 Kb | whitelisted |
352 | explorer.exe | POST | — | 50.116.72.183:80 | http://www.atlantacannabismagazine.com/t209/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
184 | chrome.exe | 172.217.23.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 113.29.190.53:80 | attach.mail.daum.net | Kakao Corp | KR | unknown |
3864 | KHBB29708.exe | 172.217.21.206:443 | drive.google.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3864 | KHBB29708.exe | 172.217.21.193:443 | doc-04-9g-docs.googleusercontent.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 172.217.23.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 172.217.18.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 113.29.184.216:80 | maildn.daumcdn.net | Kakao Corp | KR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
attach.mail.daum.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
maildn.daumcdn.net |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
drive.google.com |
| shared |
doc-04-9g-docs.googleusercontent.com |
| shared |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
352 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
352 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
352 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
352 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
4 ETPRO signatures available at the full report