| File name: | 3fb42de7bef728db9db776ce892a5893f84b24c433253988d849c514a4008b67 |
| Full analysis: | https://app.any.run/tasks/e6fe2b8a-b2eb-4050-8934-39a85fe77612 |
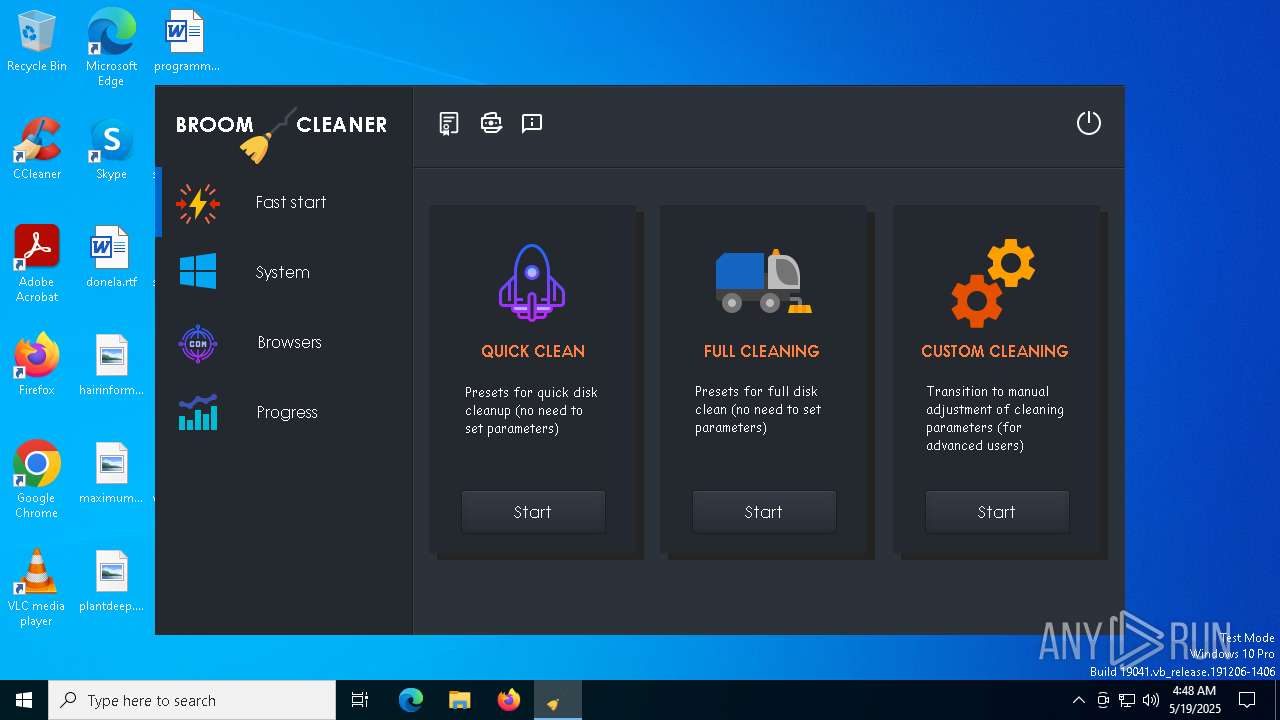
| Verdict: | Malicious activity |
| Threats: | Glupteba is a loader with information-stealing and traffic routing functionality. It is designed primarily to install other viruses on infected PCs but can do much more than that. In addition, it is being constantly updated, making this virus one to watch out for. |
| Analysis date: | May 19, 2025, 04:48:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | E2982DF7BD07C80FFDD02A7D680B64BC |
| SHA1: | 85D6417C7B391BEA381EB07D56EFF39EFE051A04 |
| SHA256: | 3FB42DE7BEF728DB9DB776CE892A5893F84B24C433253988D849C514A4008B67 |
| SSDEEP: | 98304:LtStDySVEiwIUBaoX7SUHsxMTsHcOXyJ4Stdt+9kzNtQ3uzrK+3jIC5pqtJRVZN8:BRig+vInDo7Oj3h1Hk30Wu/d |
MALICIOUS
Executing a file with an untrusted certificate
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5392)
- latestX.exe (PID: 4208)
- latestX.exe (PID: 1660)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 900)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 1040)
- csrss.exe (PID: 7200)
- updater.exe (PID: 7900)
Bypass User Account Control (fodhelper)
- fodhelper.exe (PID: 1912)
Application was injected by another process
- explorer.exe (PID: 5492)
Runs injected code in another process
- toolspub2.exe (PID: 7152)
Bypass User Account Control (Modify registry)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5392)
Changes the autorun value in the registry
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 1040)
SMOKE mutex has been found
- explorer.exe (PID: 5492)
Modifies exclusions in Windows Defender
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 1040)
Glupteba is detected
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 1040)
SMOKE has been detected (SURICATA)
- explorer.exe (PID: 5492)
Uses Task Scheduler to autorun other applications
- csrss.exe (PID: 7200)
Adds path to the Windows Defender exclusion list
- explorer.exe (PID: 5492)
Changes Windows Defender settings
- explorer.exe (PID: 5492)
SUSPICIOUS
Reads security settings of Internet Explorer
- 3fb42de7bef728db9db776ce892a5893f84b24c433253988d849c514a4008b67.exe (PID: 6004)
Executable content was dropped or overwritten
- 3fb42de7bef728db9db776ce892a5893f84b24c433253988d849c514a4008b67.exe (PID: 6004)
- InstallSetup5.exe (PID: 5064)
- explorer.exe (PID: 5492)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 1040)
- csrss.exe (PID: 7200)
- latestX.exe (PID: 1660)
Application launched itself
- toolspub2.exe (PID: 2152)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 900)
Changes default file association
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5392)
Starts CMD.EXE for commands execution
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5392)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 1040)
- csrss.exe (PID: 7200)
- explorer.exe (PID: 5492)
The process hides Powershell's copyright startup banner
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 900)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 1040)
- csrss.exe (PID: 7200)
The process bypasses the loading of PowerShell profile settings
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 900)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 1040)
- csrss.exe (PID: 7200)
Starts POWERSHELL.EXE for commands execution
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 900)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 1040)
- csrss.exe (PID: 7200)
- explorer.exe (PID: 5492)
Executes application which crashes
- toolspub2.exe (PID: 7152)
There is functionality for taking screenshot (YARA)
- InstallSetup5.exe (PID: 5064)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 4932)
There is functionality for VM detection VirtualPC (YARA)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5392)
There is functionality for VM detection VirtualBox (YARA)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5392)
The process creates files with name similar to system file names
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 1040)
Starts itself from another location
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 1040)
There is functionality for VM detection Parallels (YARA)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5392)
There is functionality for VM detection VMWare (YARA)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5392)
Creates a software uninstall entry
- csrss.exe (PID: 7200)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 7516)
Script adds exclusion path to Windows Defender
- explorer.exe (PID: 5492)
Manipulates environment variables
- powershell.exe (PID: 7840)
Drops a system driver (possible attempt to evade defenses)
- csrss.exe (PID: 7200)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 7452)
Windows service management via SC.EXE
- sc.exe (PID: 6944)
- sc.exe (PID: 812)
- sc.exe (PID: 6068)
Stops a currently running service
- sc.exe (PID: 7224)
- sc.exe (PID: 5552)
- sc.exe (PID: 7400)
- sc.exe (PID: 7432)
- sc.exe (PID: 7384)
Starts SC.EXE for service management
- cmd.exe (PID: 7248)
The process executes via Task Scheduler
- updater.exe (PID: 7900)
INFO
Reads the computer name
- 3fb42de7bef728db9db776ce892a5893f84b24c433253988d849c514a4008b67.exe (PID: 6004)
- Broom.exe (PID: 1760)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5392)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 900)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 1040)
- csrss.exe (PID: 7200)
Process checks computer location settings
- 3fb42de7bef728db9db776ce892a5893f84b24c433253988d849c514a4008b67.exe (PID: 6004)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5492)
- cmd.exe (PID: 5864)
- fodhelper.exe (PID: 1912)
Checks supported languages
- 3fb42de7bef728db9db776ce892a5893f84b24c433253988d849c514a4008b67.exe (PID: 6004)
- InstallSetup5.exe (PID: 5064)
- toolspub2.exe (PID: 2152)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5392)
- Broom.exe (PID: 1760)
- latestX.exe (PID: 1660)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 900)
- toolspub2.exe (PID: 7152)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 1040)
- csrss.exe (PID: 7200)
Create files in a temporary directory
- InstallSetup5.exe (PID: 5064)
- 3fb42de7bef728db9db776ce892a5893f84b24c433253988d849c514a4008b67.exe (PID: 6004)
The sample compiled with english language support
- InstallSetup5.exe (PID: 5064)
- csrss.exe (PID: 7200)
Drops encrypted JS script (Microsoft Script Encoder)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 900)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 1040)
- csrss.exe (PID: 7200)
Checks current location (POWERSHELL)
- powershell.exe (PID: 5056)
- powershell.exe (PID: 3240)
- powershell.exe (PID: 2420)
- powershell.exe (PID: 4932)
- powershell.exe (PID: 7324)
- powershell.exe (PID: 7576)
- powershell.exe (PID: 7768)
Creates files or folders in the user directory
- WerFault.exe (PID: 5680)
- explorer.exe (PID: 5492)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5056)
- powershell.exe (PID: 2420)
- powershell.exe (PID: 3240)
- powershell.exe (PID: 4932)
- powershell.exe (PID: 7576)
- powershell.exe (PID: 7324)
- powershell.exe (PID: 7768)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5056)
- powershell.exe (PID: 3240)
- powershell.exe (PID: 2420)
- powershell.exe (PID: 4932)
- powershell.exe (PID: 7576)
- powershell.exe (PID: 7324)
- powershell.exe (PID: 7768)
Application based on Golang
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5392)
Detects GO elliptic curve encryption (YARA)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5392)
Checks proxy server information
- explorer.exe (PID: 5492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:11:10 09:26:36+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 13186048 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc9533e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 1.0.0.0 |
| InternalName: | latestumma.exe |
| LegalCopyright: | |
| OriginalFileName: | latestumma.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
211
Monitored processes
76
Malicious processes
10
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | schtasks /CREATE /SC ONLOGON /RL HIGHEST /TR "C:\WINDOWS\rss\csrss.exe" /TN csrss /F | C:\Windows\System32\schtasks.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | netsh advfirewall firewall add rule name="csrss" dir=in action=allow program="C:\WINDOWS\rss\csrss.exe" enable=yes | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | sc sdset WinmonFS D:(A;;CCLCSWRPWPDTLOCRRC;;;SY)(A;;CCDCLCSWRPLOCRSDRCWDWO;;;BA)(D;;WPDT;;;BA)(A;;CCLCSWLOCRRC;;;IU)(A;;CCLCSWLOCRRC;;;SU)S:(AU;FA;CCDCLCSWRPWPDTLOCRSDRCWDWO;;;WD) | C:\Windows\SysWOW64\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | "C:\Users\admin\AppData\Local\Temp\e0cbefcb1af40c7d4aff4aca26621a98.exe" | C:\Users\admin\AppData\Local\Temp\e0cbefcb1af40c7d4aff4aca26621a98.exe | — | fodhelper.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1040 | "C:\Users\admin\AppData\Local\Temp\e0cbefcb1af40c7d4aff4aca26621a98.exe" | C:\Users\admin\AppData\Local\Temp\e0cbefcb1af40c7d4aff4aca26621a98.exe | e0cbefcb1af40c7d4aff4aca26621a98.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | "C:\Users\admin\AppData\Local\Temp\latestX.exe" | C:\Users\admin\AppData\Local\Temp\latestX.exe | 3fb42de7bef728db9db776ce892a5893f84b24c433253988d849c514a4008b67.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1760 | C:\Users\admin\AppData\Local\Temp\Broom.exe | C:\Users\admin\AppData\Local\Temp\Broom.exe | — | InstallSetup5.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Broom Version: 1.0.0.0 Modules
| |||||||||||||||
| 1912 | "C:\WINDOWS\system32\fodhelper.exe" | C:\Windows\System32\fodhelper.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Features On Demand Helper Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
54 559
Read events
54 512
Write events
45
Delete events
2
Modification events
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000000000000000000000 | |||
| (PID) Process: | (1760) Broom.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Broom |
| Operation: | write | Name: | Key |
Value: XZWEN-27MCX-Z9JD1-USCSW | |||
| (PID) Process: | (1760) Broom.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Broom |
| Operation: | write | Name: | Date |
Value: 1DE5116A865CE640 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:00000000000802B0 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5392) e0cbefcb1af40c7d4aff4aca26621a98.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\fde20f96 |
| Operation: | write | Name: | OSCaption |
Value: Microsoft Windows 10 Pro | |||
| (PID) Process: | (5392) e0cbefcb1af40c7d4aff4aca26621a98.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\fde20f96 |
| Operation: | write | Name: | OSArchitecture |
Value: 64-bit | |||
| (PID) Process: | (5392) e0cbefcb1af40c7d4aff4aca26621a98.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\fde20f96 |
| Operation: | write | Name: | CPU |
Value: Intel(R) Core(TM) i5-6400 CPU @ 2.70GHz | |||
| (PID) Process: | (5392) e0cbefcb1af40c7d4aff4aca26621a98.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\fde20f96 |
| Operation: | write | Name: | GPU |
Value: Microsoft Basic Display Adapter | |||
| (PID) Process: | (5392) e0cbefcb1af40c7d4aff4aca26621a98.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\shell\open\command |
| Operation: | write | Name: | DelegateExecute |
Value: | |||
| (PID) Process: | (5392) e0cbefcb1af40c7d4aff4aca26621a98.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\fde20f96 |
| Operation: | write | Name: | Servers |
Value: https://allstatsin.ru | |||
Executable files
11
Suspicious files
7
Text files
34
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5680 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_toolspub2.exe_8f8e1097927c53afee23f2d6c37daa56a28a43_6c449747_5ab9ca1c-9cd5-4522-91c7-8fde9a5cb0ad\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6004 | 3fb42de7bef728db9db776ce892a5893f84b24c433253988d849c514a4008b67.exe | C:\Users\admin\AppData\Local\Temp\InstallSetup5.exe | executable | |
MD5:BC3354A4CD405A2F2F98E8B343A7D08D | SHA256:FFFC160A4C555057143383FEC606841CD2C319F79F52596E0D27322A677DCA0B | |||
| 5064 | InstallSetup5.exe | C:\Users\admin\AppData\Local\Temp\Broom.exe | executable | |
MD5:00E93456AA5BCF9F60F84B0C0760A212 | SHA256:FF3025F9CF19323C5972D14F00F01296D6D7A71547ECA7E4016BFD0E1F27B504 | |||
| 6004 | 3fb42de7bef728db9db776ce892a5893f84b24c433253988d849c514a4008b67.exe | C:\Users\admin\AppData\Local\Temp\e0cbefcb1af40c7d4aff4aca26621a98.exe | executable | |
MD5:2A92DBDA3DF9502DEF5E1C9009950699 | SHA256:2CDE7B9FC5ACD7964916D023E78D42AE7AC6D511C5CD7CA57B066A94882A67EC | |||
| 6004 | 3fb42de7bef728db9db776ce892a5893f84b24c433253988d849c514a4008b67.exe | C:\Users\admin\AppData\Local\Temp\latestX.exe | executable | |
MD5:BAE29E49E8190BFBBF0D77FFAB8DE59D | SHA256:F91E4FF7811A5848561463D970C51870C9299A80117A89FB86A698B9F727DE87 | |||
| 5680 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\toolspub2.exe.7152.dmp | binary | |
MD5:561A286C6A3F0E82EC7D0BD4C06AF48E | SHA256:3C3CC5155AF5B461F890A3BB3DF23CC263D0D2874CC06B2AA841115371ED08A7 | |||
| 5492 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 5680 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERDC89.tmp.xml | xml | |
MD5:E01CEF7ABDDA6E441D9F82BCF3686D48 | SHA256:CC81D5C842B5C42CDFD47910716A22F488F440608D32F5C2A52B57ACC9B22A2E | |||
| 5056 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_eejl2fx4.jzq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5680 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERDC49.tmp.WERInternalMetadata.xml | binary | |
MD5:73ED0C04CE59876940DD4C3872021BB4 | SHA256:43F517E9A6D6D4D667204A71BB528107DCE83DEFBFBDAAD23E1AD0F293DD1262 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
21
DNS requests
18
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5492 | explorer.exe | POST | 404 | 188.40.141.211:80 | http://host-file-host6.com/ | unknown | — | — | malicious |
7224 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7224 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5492 | explorer.exe | POST | 404 | 188.40.141.211:80 | http://host-file-host6.com/ | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5492 | explorer.exe | 188.40.141.211:80 | host-file-host6.com | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
host-file-host6.com |
| malicious |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
e4db5d15-21bc-4438-b50b-d0852f03e219.uuid.allstatsin.ru |
| unknown |
stun.sipgate.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5492 | explorer.exe | A Network Trojan was detected | LOADER [ANY.RUN] Smokeloader HTTP Header |
5492 | explorer.exe | A Network Trojan was detected | LOADER [ANY.RUN] Smokeloader HTTP Header |
2196 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7200 | csrss.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |