| File name: | Document.doc |
| Full analysis: | https://app.any.run/tasks/cbf9f448-1716-49db-83a3-57fd7ec6206c |
| Verdict: | Malicious activity |
| Threats: | A keylogger is a type of spyware that infects a system and has the ability to record every keystroke made on the device. This lets attackers collect personal information of victims, which may include their online banking credentials, as well as personal conversations. The most widespread vector of attack leading to a keylogger infection begins with a phishing email or link. Keylogging is also often present in remote access trojans as part of an extended set of malicious tools. |
| Analysis date: | July 18, 2019, 05:07:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | BEB86A6171A5311949C82F451B8EB934 |
| SHA1: | 479D29D8F03DCC67E3F490ECC9B304C25FBAB506 |
| SHA256: | 3F7978A8ACCF0041A9F01DE14134256C7C6E8B667183641F21349C947CE92346 |
| SSDEEP: | 1536:mrokUe1ehegeqfD3oZ1OkHFRIxPILSQWns3R:mroeZmxgLSQWno |
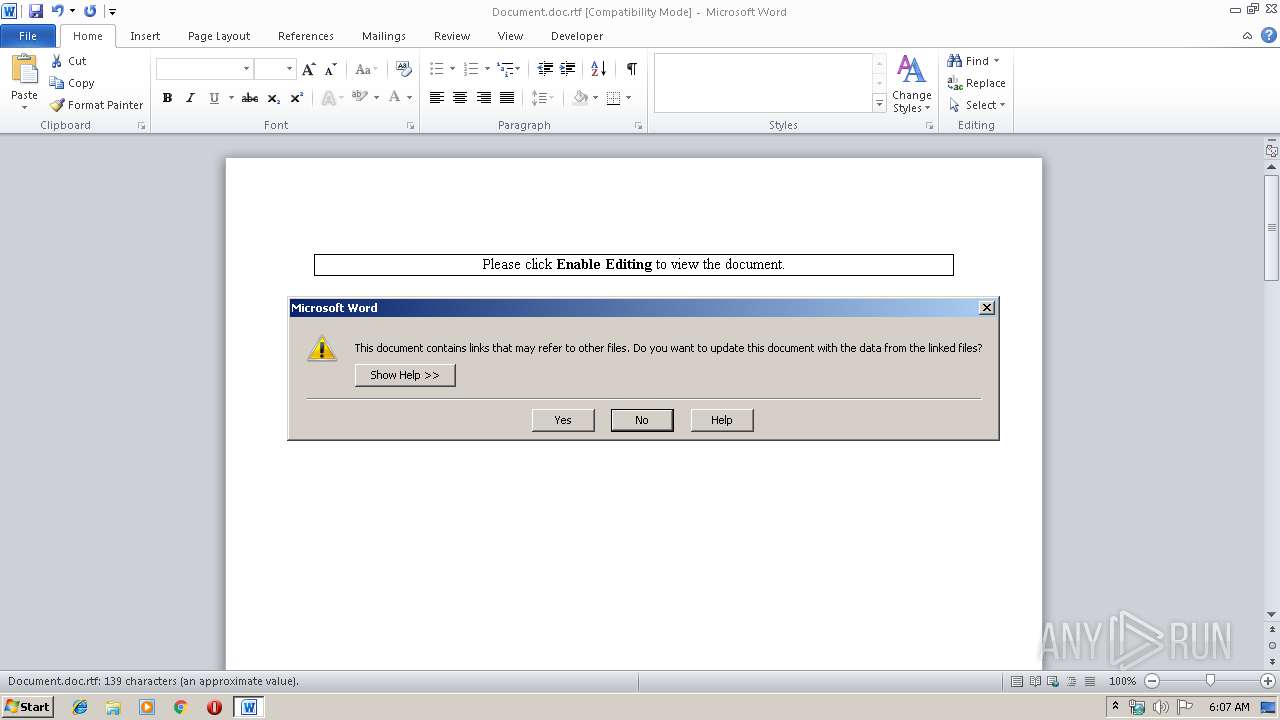
MALICIOUS
Requests a remote executable file from MS Office
- WINWORD.EXE (PID: 2856)
Uses Task Scheduler to run other applications
- u.exe (PID: 2988)
Connects to CnC server
- vbc.exe (PID: 3912)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2240)
- schtasks.exe (PID: 3484)
Application was dropped or rewritten from another process
- u.exe (PID: 2988)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2856)
Detected logs from REMCOS RAT
- vbc.exe (PID: 3912)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2856)
REMCOS was detected
- vbc.exe (PID: 3912)
SUSPICIOUS
Creates files in the user directory
- vbc.exe (PID: 3912)
Writes files like Keylogger logs
- vbc.exe (PID: 3912)
Executes scripts
- u.exe (PID: 2988)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2856)
Creates files in the user directory
- WINWORD.EXE (PID: 2856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
39
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2240 | "schtasks.exe" /query | C:\Windows\system32\schtasks.exe | — | u.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2856 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Document.doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2988 | C:\Users\admin\AppData\Roaming\u.exe | C:\Users\admin\AppData\Roaming\u.exe | — | WINWORD.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3484 | "schtasks.exe" /create /sc MINUTE /tn microsoft /MO 1 /tr C:\Users\admin\AppData\Roaming\u.exe | C:\Windows\system32\schtasks.exe | — | u.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3912 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | u.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
Total events
643
Read events
616
Write events
26
Delete events
1
Modification events
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | n)< |
Value: 6E293C00280B0000010000000000000000000000 | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1324482590 | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324482704 | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324482705 | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 280B0000B42206AC263DD50100000000 | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | '+< |
Value: 272B3C00280B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | '+< |
Value: 272B3C00280B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
1
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDDEE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\387B71FA.png | — | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3912 | vbc.exe | C:\Users\admin\AppData\Roaming\remcos\logs.dat | text | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\u.exe | executable | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\u[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Abctfhghghghghg.sct | binary | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$cument.doc.rtf | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2856 | WINWORD.EXE | GET | 200 | 108.170.57.54:80 | http://danmaxexpress.com/ssl/u.exe | US | executable | 518 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2856 | WINWORD.EXE | 108.170.57.54:80 | danmaxexpress.com | SECURED SERVERS LLC | US | suspicious |
3912 | vbc.exe | 185.247.228.189:7535 | princedaniels.duckdns.org | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
danmaxexpress.com |
| malicious |
princedaniels.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2856 | WINWORD.EXE | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
2856 | WINWORD.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Possible Malicious Macro DL EXE Feb 2016 |
2856 | WINWORD.EXE | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2856 | WINWORD.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1044 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
3912 | vbc.exe | A Network Trojan was detected | ET TROJAN Remcos RAT Checkin 23 |
3912 | vbc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Remcos RAT Checkin |
3912 | vbc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Remcos RAT |
3912 | vbc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Remcos RAT Checkin |
3912 | vbc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Remcos RAT |