| File name: | C:\Users\admin\Downloads\remittance.jar |
| Full analysis: | https://app.any.run/tasks/d05b40bb-3aeb-41c9-96f7-78912144d037 |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | December 06, 2019, 12:03:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | AED8FD9B39E80005382ED49386759695 |
| SHA1: | 5F1ADF02279D9E6EE1FE128346D4E98C44B226B9 |
| SHA256: | 3F3D921F46C70C73CECCAAAD84411837A8A0CEA214F75E867BC00E127D6D0F44 |
| SSDEEP: | 12288:RO/KRfz/18dA5tVmXn91zKB0S9S3KAQbMU9Q91UEsnDxwp:NL5t0Xn9Y0S9EBjFAxm |
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 1952)
Loads dropped or rewritten executable
- javaw.exe (PID: 2580)
- explorer.exe (PID: 352)
- java.exe (PID: 2620)
- javaw.exe (PID: 2192)
- java.exe (PID: 2456)
AdWind was detected
- java.exe (PID: 2620)
- java.exe (PID: 2456)
Application was dropped or rewritten from another process
- javaw.exe (PID: 2580)
- javaw.exe (PID: 2192)
- java.exe (PID: 2456)
- java.exe (PID: 2620)
UAC/LUA settings modification
- regedit.exe (PID: 2180)
Turns off system restore
- regedit.exe (PID: 2180)
Uses TASKKILL.EXE to kill security tools
- javaw.exe (PID: 2192)
Changes Image File Execution Options
- regedit.exe (PID: 2180)
SUSPICIOUS
Executes JAVA applets
- explorer.exe (PID: 352)
- javaw.exe (PID: 2580)
Starts CMD.EXE for commands execution
- java.exe (PID: 2620)
- javaw.exe (PID: 2580)
- java.exe (PID: 2456)
- javaw.exe (PID: 2192)
Executes scripts
- cmd.exe (PID: 2824)
- cmd.exe (PID: 2660)
- cmd.exe (PID: 4028)
- cmd.exe (PID: 2836)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 1712)
- cmd.exe (PID: 2748)
- cmd.exe (PID: 2424)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 2580)
Starts itself from another location
- javaw.exe (PID: 2580)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 2580)
Creates files in the user directory
- javaw.exe (PID: 2580)
- xcopy.exe (PID: 3244)
Executable content was dropped or overwritten
- xcopy.exe (PID: 3244)
Uses TASKKILL.EXE to kill process
- javaw.exe (PID: 2192)
Modifies files in Chrome extension folder
- chrome.exe (PID: 4000)
INFO
Application launched itself
- chrome.exe (PID: 4000)
Reads the hosts file
- chrome.exe (PID: 4000)
- chrome.exe (PID: 1796)
Reads settings of System Certificates
- chrome.exe (PID: 1796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:04 21:38:01 |
| ZipCRC: | 0x0f27fae3 |
| ZipCompressedSize: | 75 |
| ZipUncompressedSize: | 76 |
| ZipFileName: | META-INF/MANIFEST.MF |
Total processes
334
Monitored processes
174
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | cmd.exe /c regedit.exe /s C:\Users\admin\AppData\Local\Temp\hgpHoNIhTi3086353408738960250.reg | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 236 | taskkill /IM V3Medic.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 292 | taskkill /IM AdAwareDesktop.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 324 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive1150458452519449255.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,10913685257485516162,3517160792425623643,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3000070870936647539 --mojo-platform-channel-handle=3100 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 332 | taskkill /IM V3Main.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 388 | taskkill /IM fshoster32.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,10913685257485516162,3517160792425623643,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1387857110613058155 --mojo-platform-channel-handle=3560 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 504 | taskkill /IM text2pcap.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 484
Read events
1 172
Write events
307
Delete events
5
Modification events
| (PID) Process: | (1952) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | yRpnOmZRSSr |
Value: "C:\Users\admin\AppData\Roaming\Oracle\bin\javaw.exe" -jar "C:\Users\admin\bbqnTeeAXxI\.jar.hpbBjQ" | |||
| (PID) Process: | (184) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (184) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2180) regedit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Attachments |
| Operation: | write | Name: | SaveZoneInformation |
Value: 1 | |||
| (PID) Process: | (2180) regedit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Associations |
| Operation: | write | Name: | LowRiskFileTypes |
Value: .avi;.bat;.com;.cmd;.exe;.htm;.html;.lnk;.mpg;.mpeg;.mov;.mp3;.msi;.m3u;.rar;.reg;.txt;.vbs;.wav;.zip;.jar; | |||
| (PID) Process: | (2180) regedit.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | SEE_MASK_NOZONECHECKS |
Value: 1 | |||
| (PID) Process: | (2180) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager\Environment |
| Operation: | write | Name: | SEE_MASK_NOZONECHECKS |
Value: 1 | |||
| (PID) Process: | (2180) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\UserAccountControlSettings.exe |
| Operation: | write | Name: | debugger |
Value: svchost.exe | |||
| (PID) Process: | (2180) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
| (PID) Process: | (2180) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorUser |
Value: 0 | |||
Executable files
109
Suspicious files
35
Text files
330
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | javaw.exe | C:\Users\admin\AppData\Local\Temp\Retrive1150458452519449255.vbs | — | |
MD5:— | SHA256:— | |||
| 2620 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2580 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2580 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 3244 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\README.txt | text | |
MD5:0F1123976B959AC5E8B89EB8C245C4BD | SHA256:963095CF8DB76FB8071FD19A3110718A42F2AB42B27A3ADFD9EC58981C3E88D2 | |||
| 2580 | javaw.exe | C:\Users\admin\AppData\Local\Temp\Retrive5158151549950653909.vbs | text | |
MD5:3BDFD33017806B85949B6FAA7D4B98E4 | SHA256:9DA575DD2D5B7C1E9BAB8B51A16CDE457B3371C6DCDB0537356CF1497FA868F6 | |||
| 3244 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\THIRDPARTYLICENSEREADME-JAVAFX.txt | text | |
MD5:AB9DB8D553033C0326BD2D38D77F84C1 | SHA256:38995534DF44E0526F8C8C8D479C778A4B34627CFD69F19213CFBE019A7261BA | |||
| 3244 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\release | text | |
MD5:1BCCC3A965156E53BE3136B3D583B7B6 | SHA256:03A4DB27DEA69374EFBAF121C332D0AF05840D16D0C1FBF127D00E65054B118A | |||
| 3244 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\bin\bci.dll | executable | |
MD5:6D8D8A26450EE4BA0BE405629EA0A511 | SHA256:7945365A3CD40D043DAE47849E6645675166920958300E64DEA76A865BC479AF | |||
| 3244 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\LICENSE | text | |
MD5:98F46AB6481D87C4D77E0E91A6DBC15F | SHA256:23F9A5C12FA839650595A32872B7360B9E030C7213580FB27DD9185538A5828C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
33
DNS requests
20
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1796 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 507 b | whitelisted |
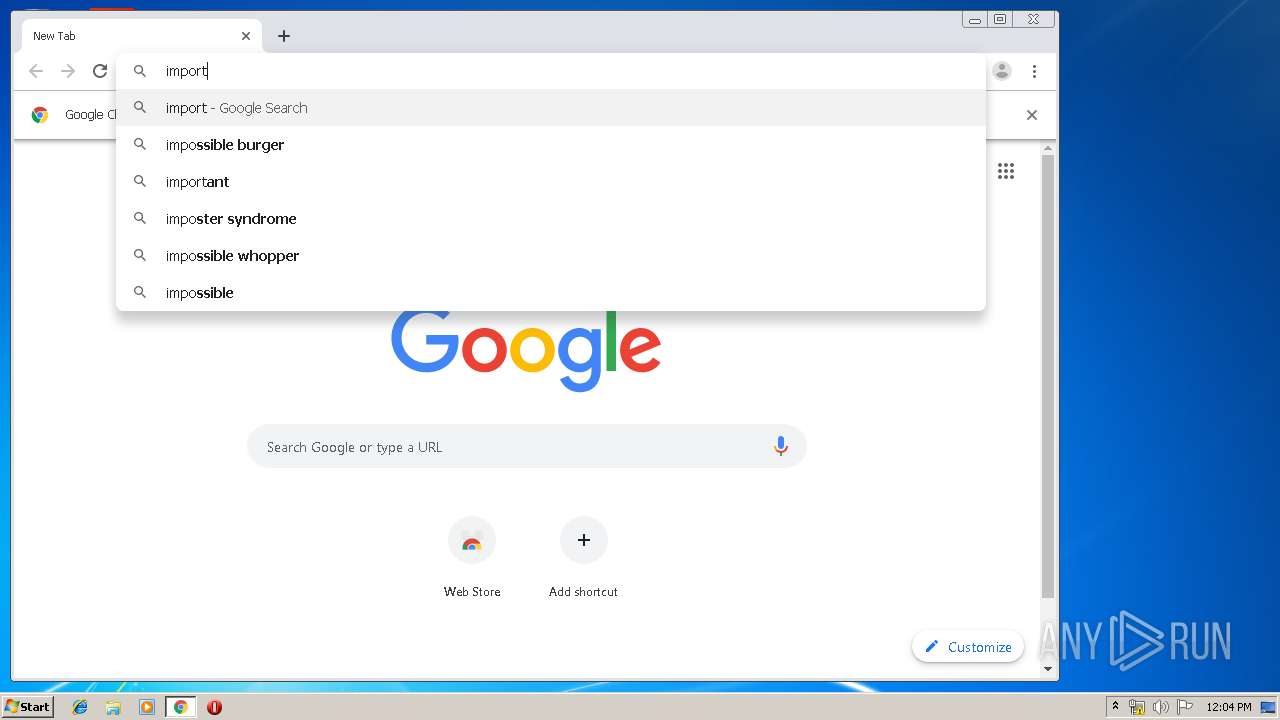
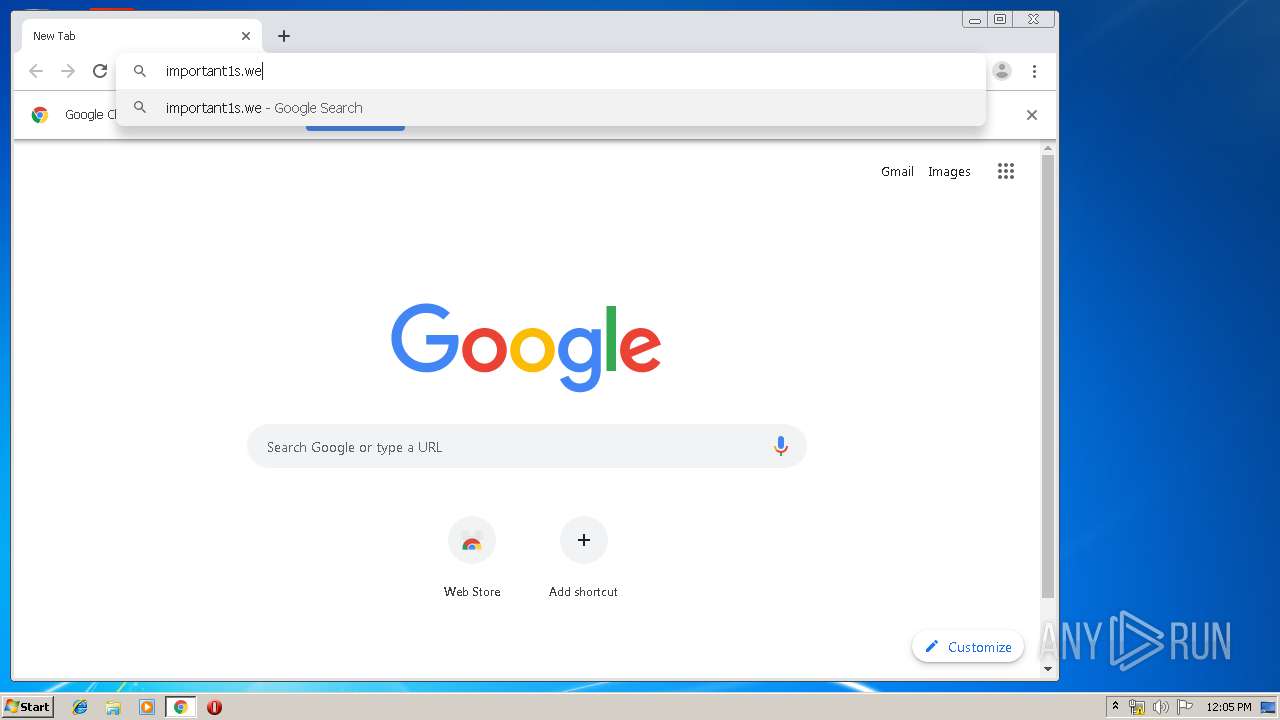
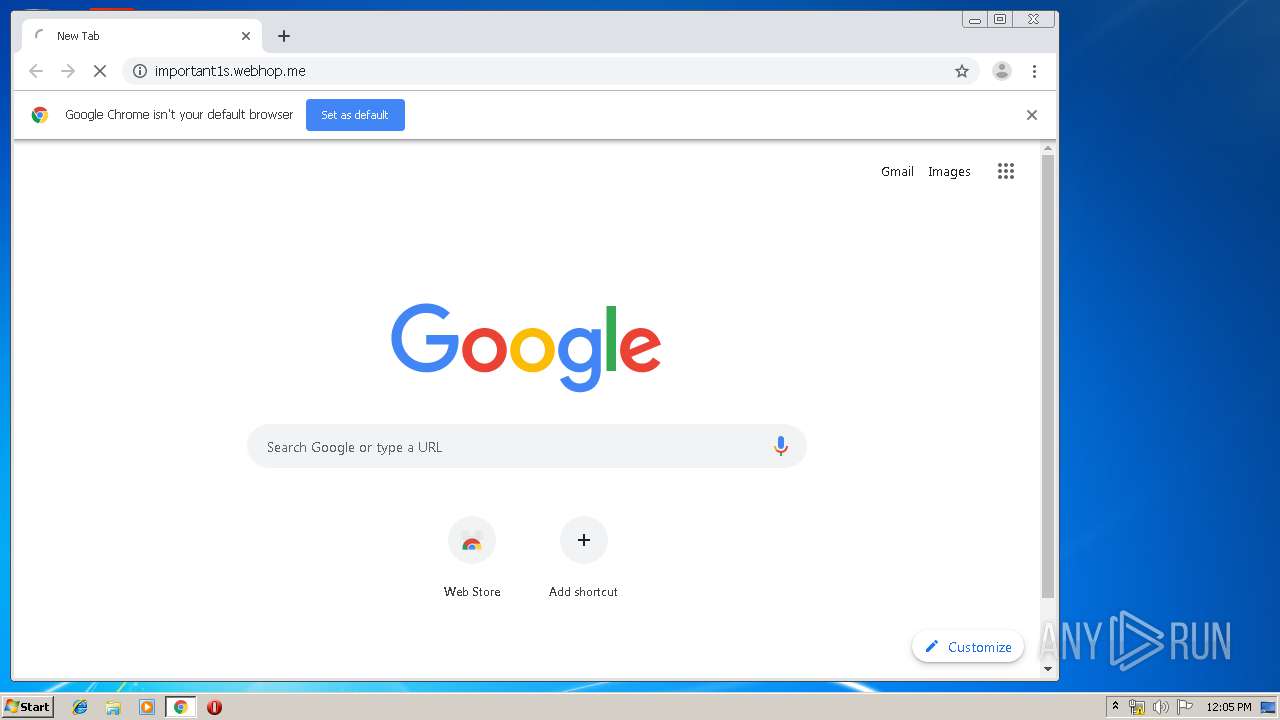
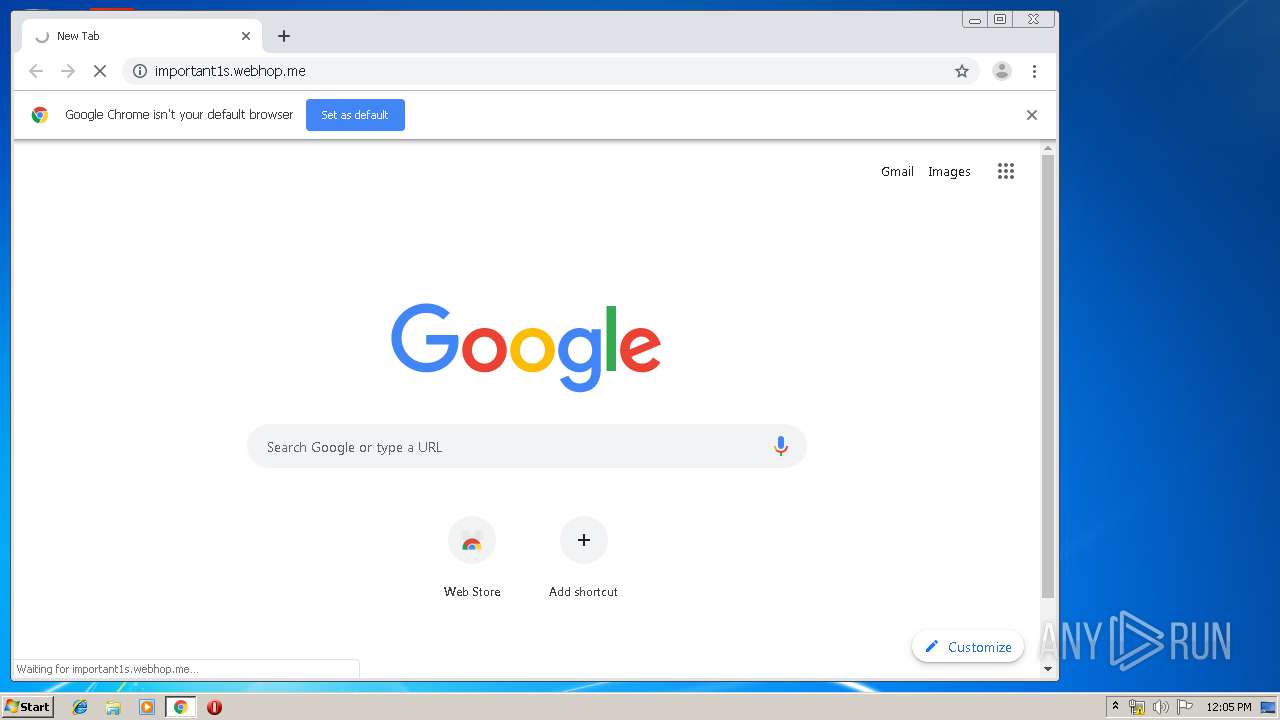
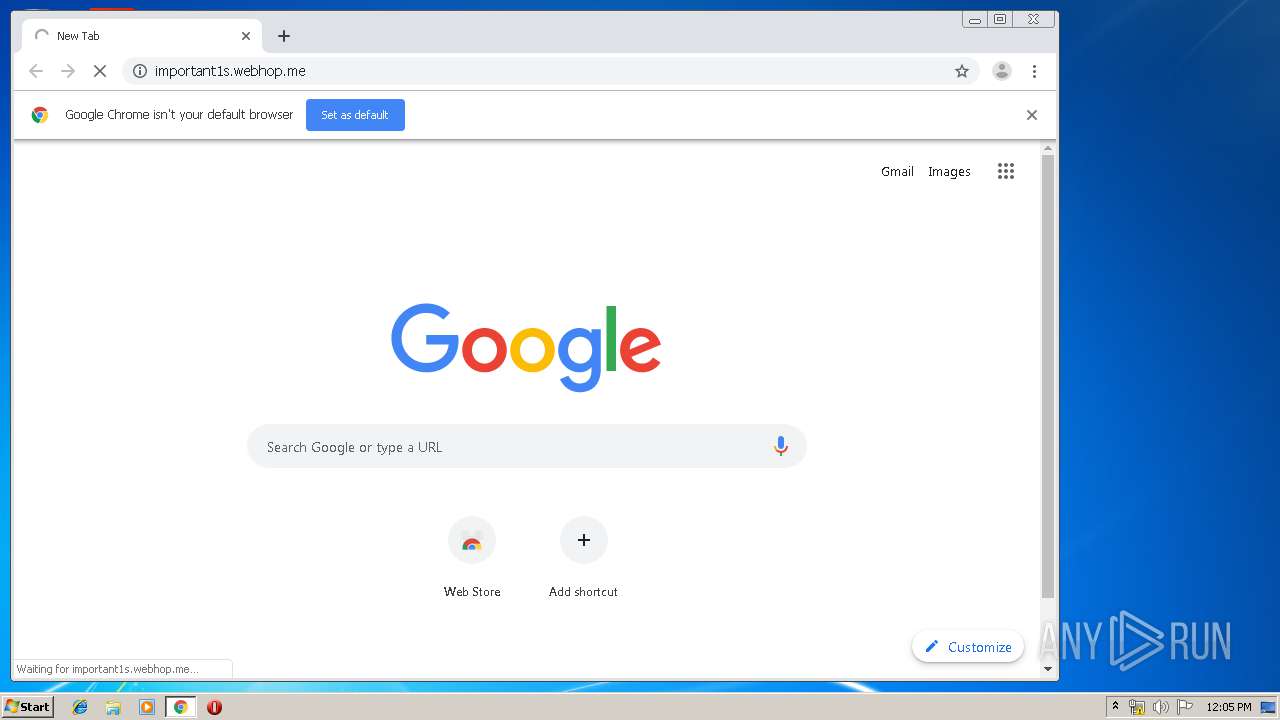
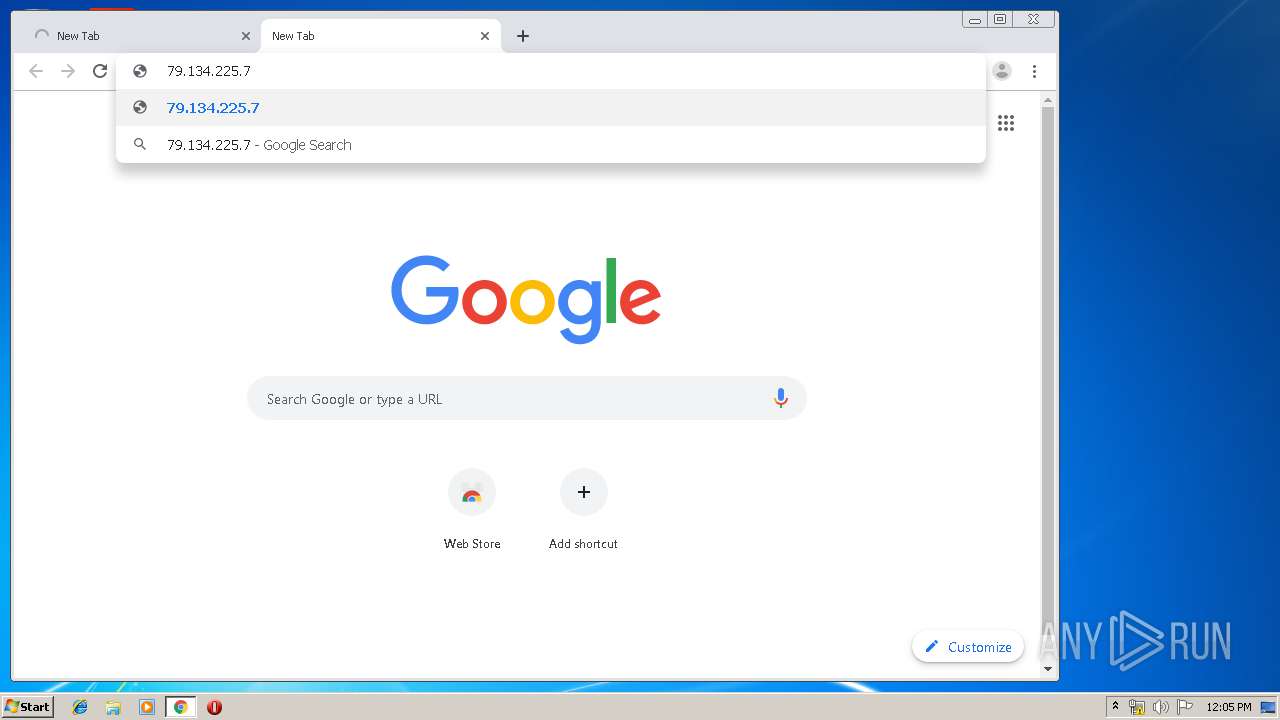
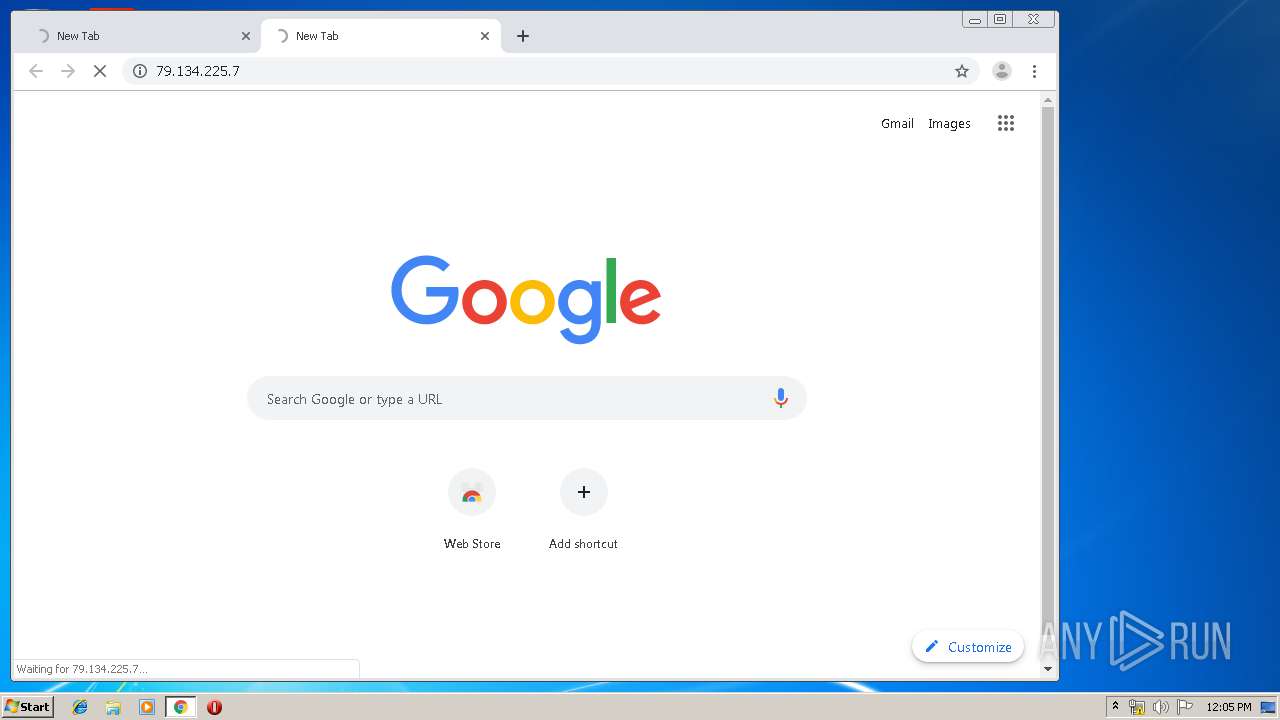
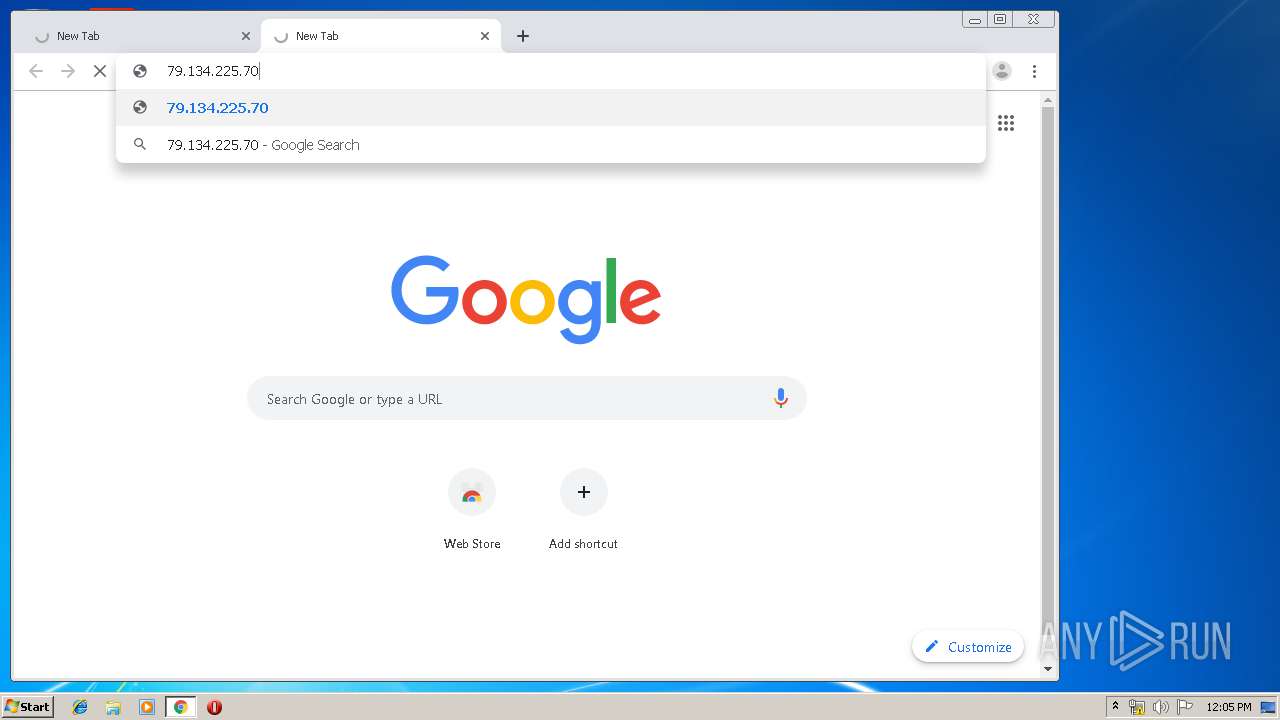
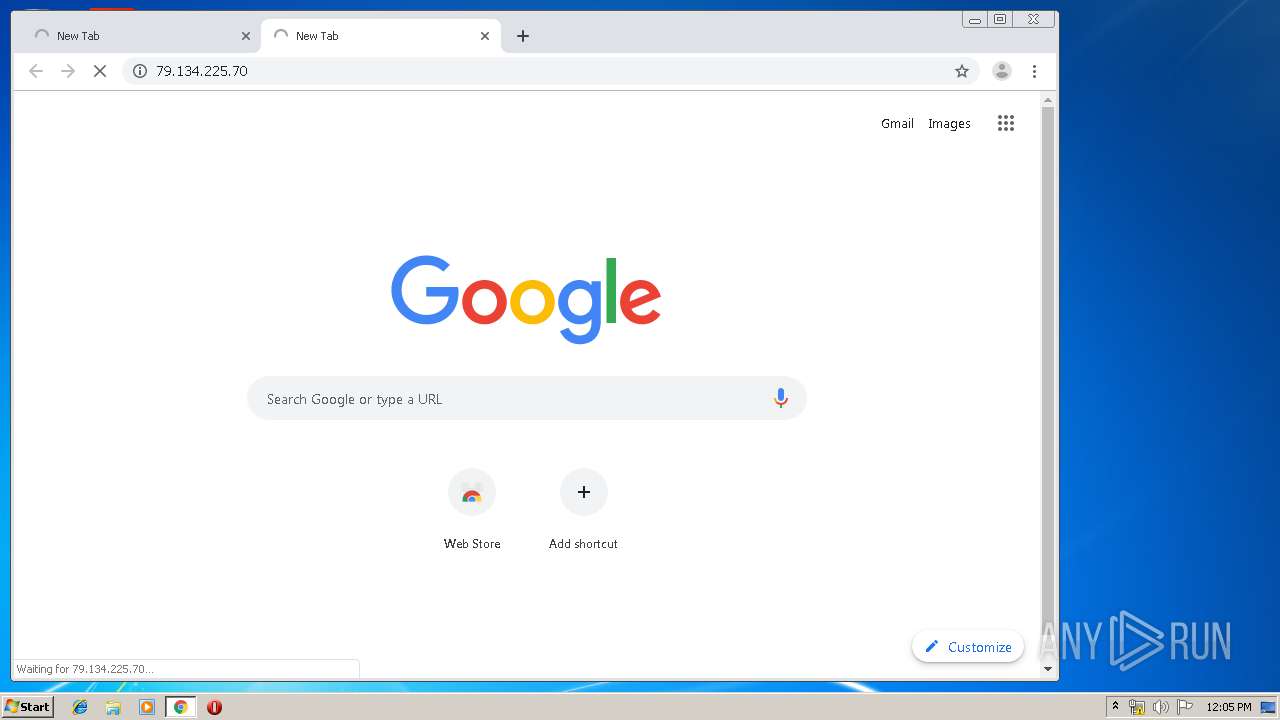
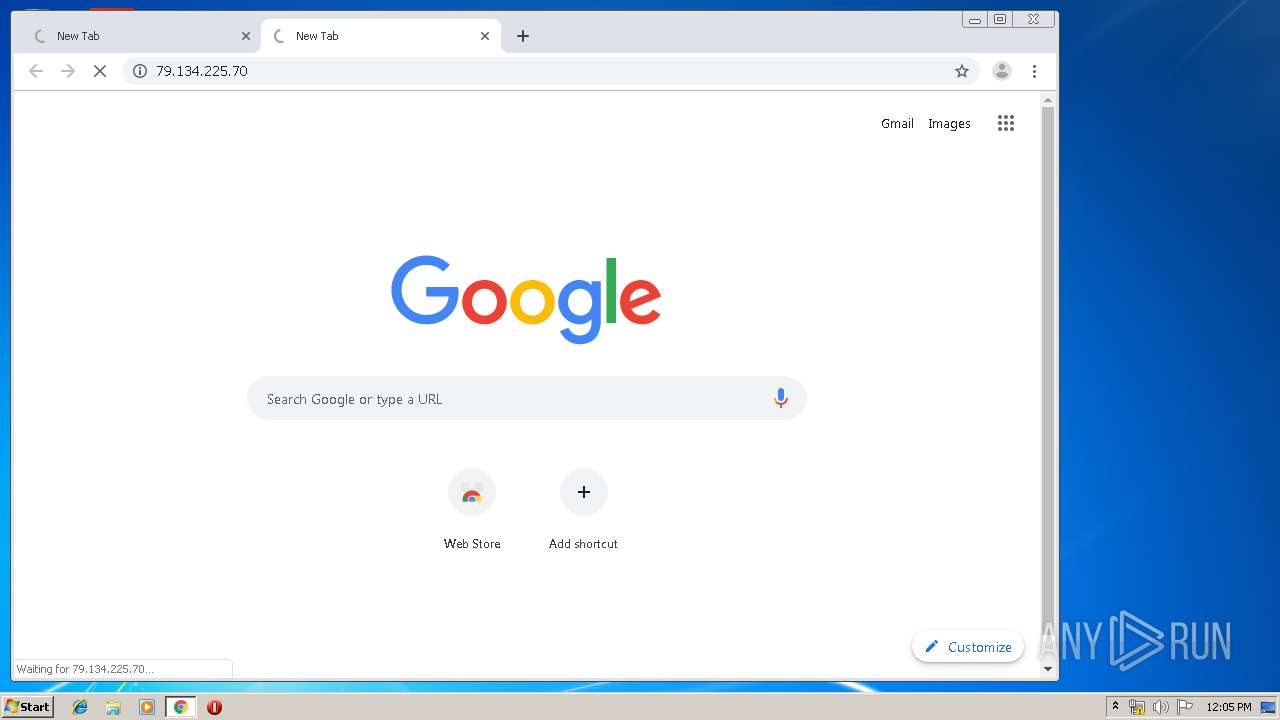
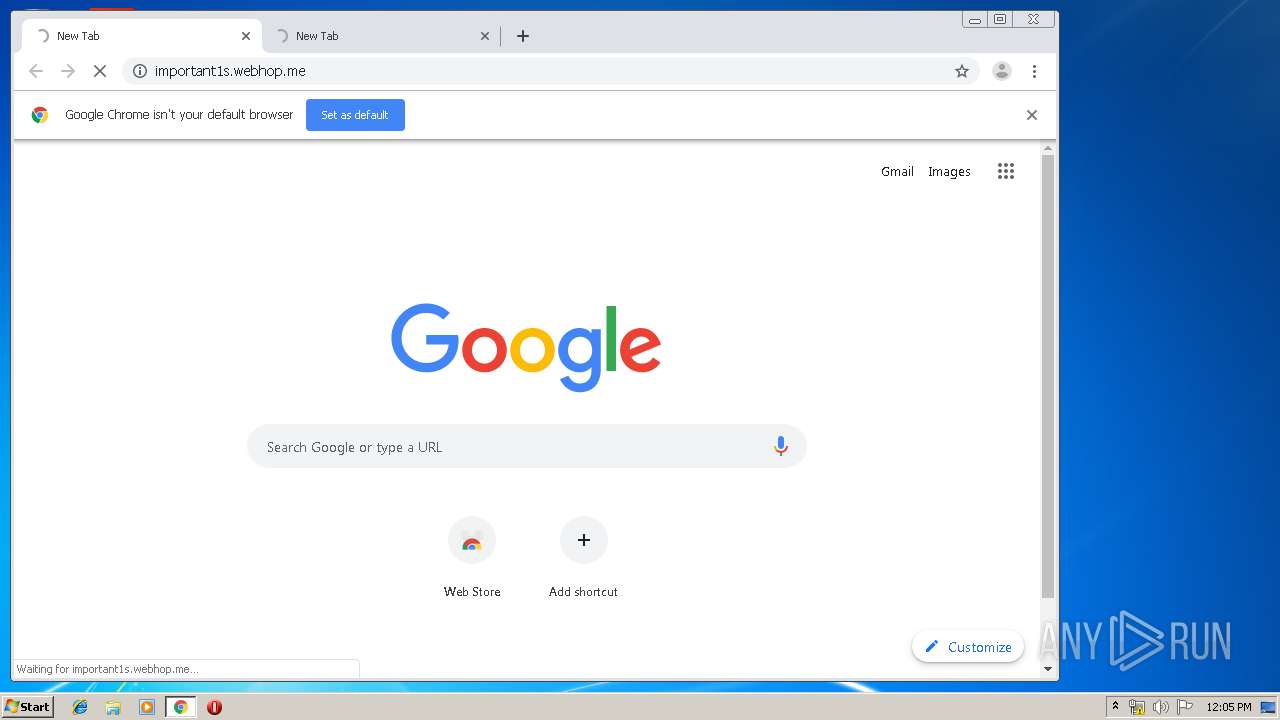
1796 | chrome.exe | GET | — | 79.134.225.70:80 | http://important1s.webhop.me/ | CH | — | — | malicious |
1796 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
1796 | chrome.exe | GET | 200 | 173.194.7.89:80 | http://r3---sn-p5qs7n7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.20.5&mm=28&mn=sn-p5qs7n7e&ms=nvh&mt=1575633797&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
1796 | chrome.exe | GET | — | 79.134.225.7:80 | http://79.134.225.7/ | CH | — | — | malicious |
1796 | chrome.exe | GET | 200 | 172.217.135.6:80 | http://r1---sn-p5qlsndk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.203.20.5&mm=28&mn=sn-p5qlsndk&ms=nvh&mt=1575633797&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
1796 | chrome.exe | GET | — | 79.134.225.7:80 | http://79.134.225.7/ | CH | — | — | malicious |
1796 | chrome.exe | GET | — | 79.134.225.70:80 | http://79.134.225.70/ | CH | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1796 | chrome.exe | 172.217.18.14:443 | ogs.google.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 172.217.18.110:443 | apis.google.com | Google Inc. | US | whitelisted |
2192 | javaw.exe | 79.134.225.70:8884 | important1s.webhop.me | Andreas Fink trading as Fink Telecom Services | CH | malicious |
1796 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 172.217.18.110:80 | apis.google.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 172.217.22.33:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 172.217.135.6:80 | r1---sn-p5qlsndk.gvt1.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.33:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 79.134.225.70:80 | important1s.webhop.me | Andreas Fink trading as Fink Telecom Services | CH | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
important1s.webhop.me |
| malicious |
dns.msftncsi.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.webhop .me |
1080 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.webhop .me |
1080 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.webhop .me |