| File name: | defebnder test.exe |
| Full analysis: | https://app.any.run/tasks/187c9704-f3e8-4486-867c-f6839d566c83 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | May 15, 2025, 17:17:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 76D0E6F4FA88CC77A14FCEA9E86A9225 |
| SHA1: | 1804B6E6FFE6FC4334AAAE963B828BB7256C5974 |
| SHA256: | 3F0756421FDBA3C07A117BA9E4575AB28E4200FEDCF945F49B6458A10A39E9DC |
| SSDEEP: | 49152:7BgGOhX02hD2nPiLq3A6770DODdl/rADxXhCk/3Dg4WNEtEhI/fsbWWzqhLoGdvM:22nP6q3A6770DODdl/rADxRLDgbWdk |
MALICIOUS
QUASAR has been detected (YARA)
- defebnder test.exe (PID: 7336)
- Client.exe (PID: 3268)
Uses Task Scheduler to autorun other applications
- defebnder test.exe (PID: 7284)
- Client.exe (PID: 3268)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- defebnder test.exe (PID: 7336)
- Client.exe (PID: 3268)
Executable content was dropped or overwritten
- defebnder test.exe (PID: 7284)
Starts itself from another location
- defebnder test.exe (PID: 7284)
Connects to unusual port
- Client.exe (PID: 3268)
INFO
Reads the computer name
- defebnder test.exe (PID: 7336)
- defebnder test.exe (PID: 7284)
- Client.exe (PID: 3268)
Checks supported languages
- defebnder test.exe (PID: 7336)
- defebnder test.exe (PID: 7284)
- Client.exe (PID: 3268)
Reads the machine GUID from the registry
- defebnder test.exe (PID: 7336)
- defebnder test.exe (PID: 7284)
- Client.exe (PID: 3268)
Reads Environment values
- defebnder test.exe (PID: 7336)
- defebnder test.exe (PID: 7284)
- Client.exe (PID: 3268)
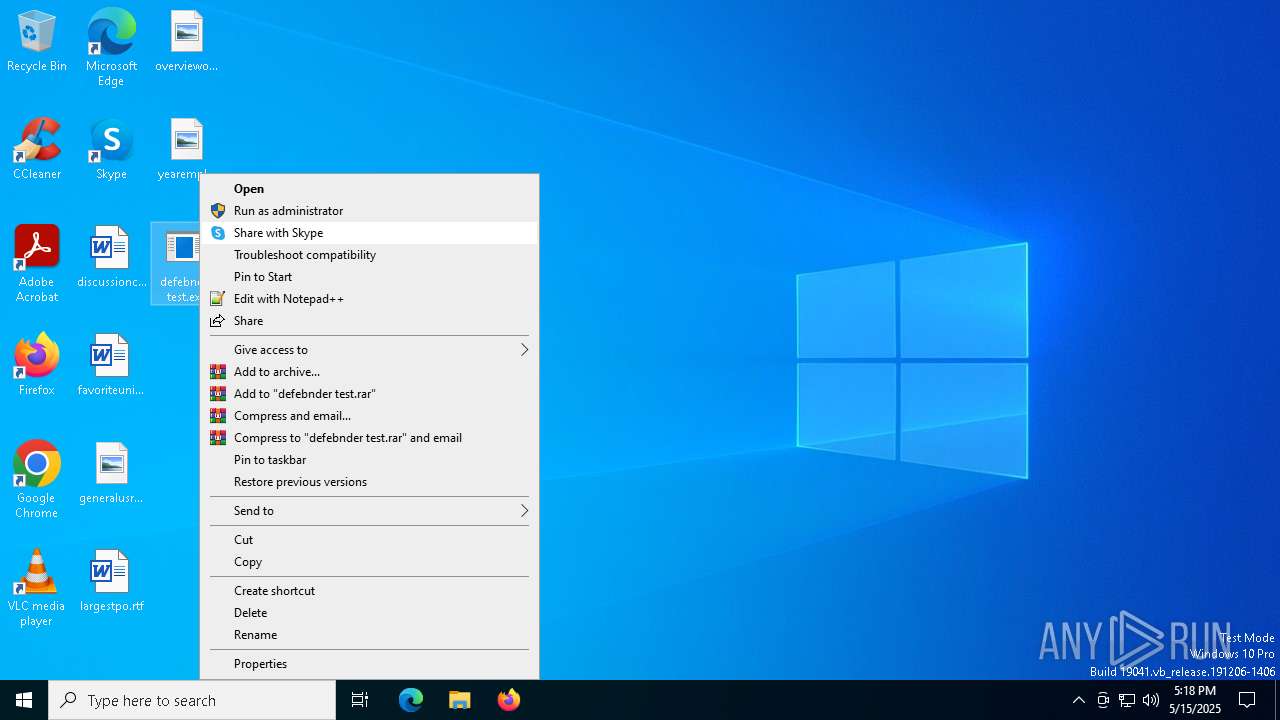
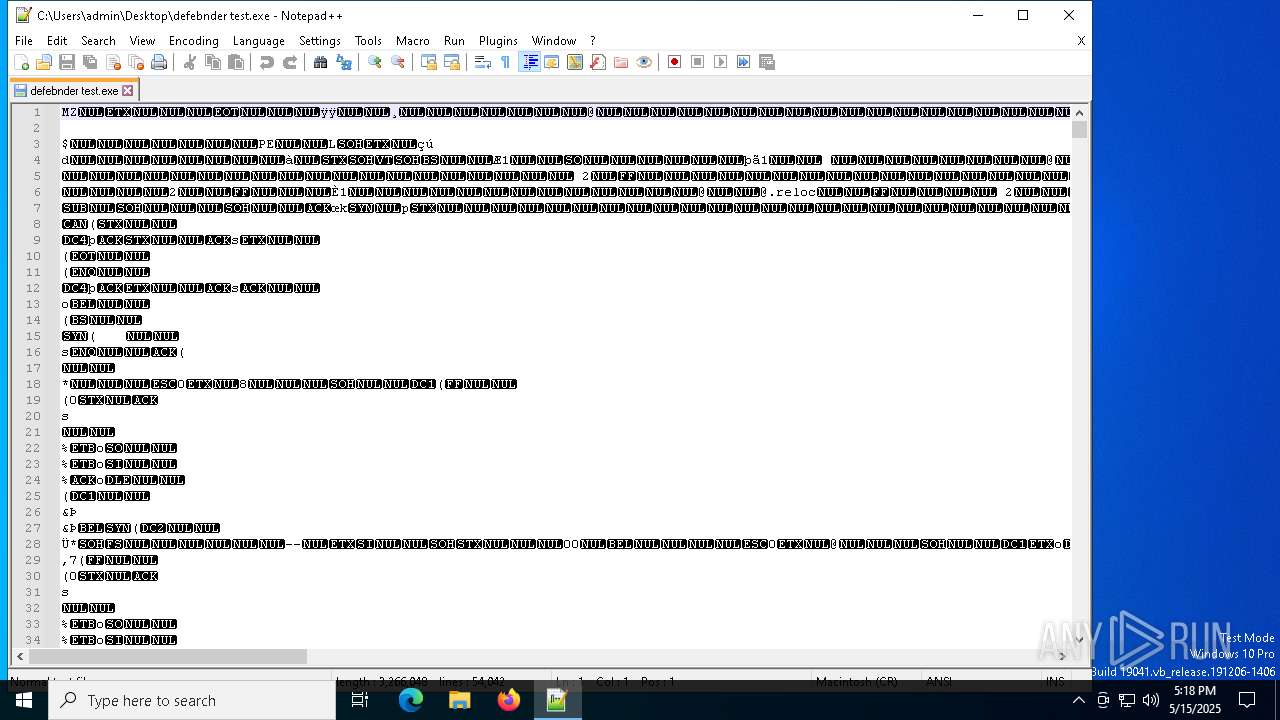
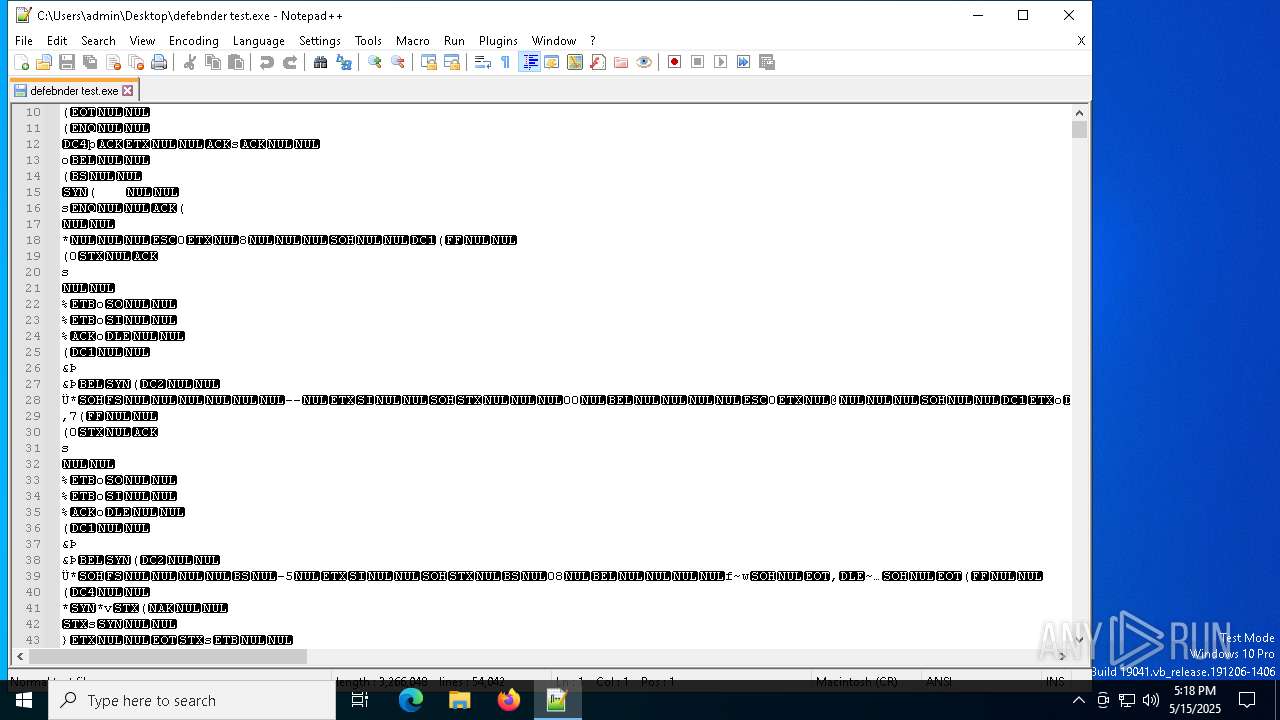
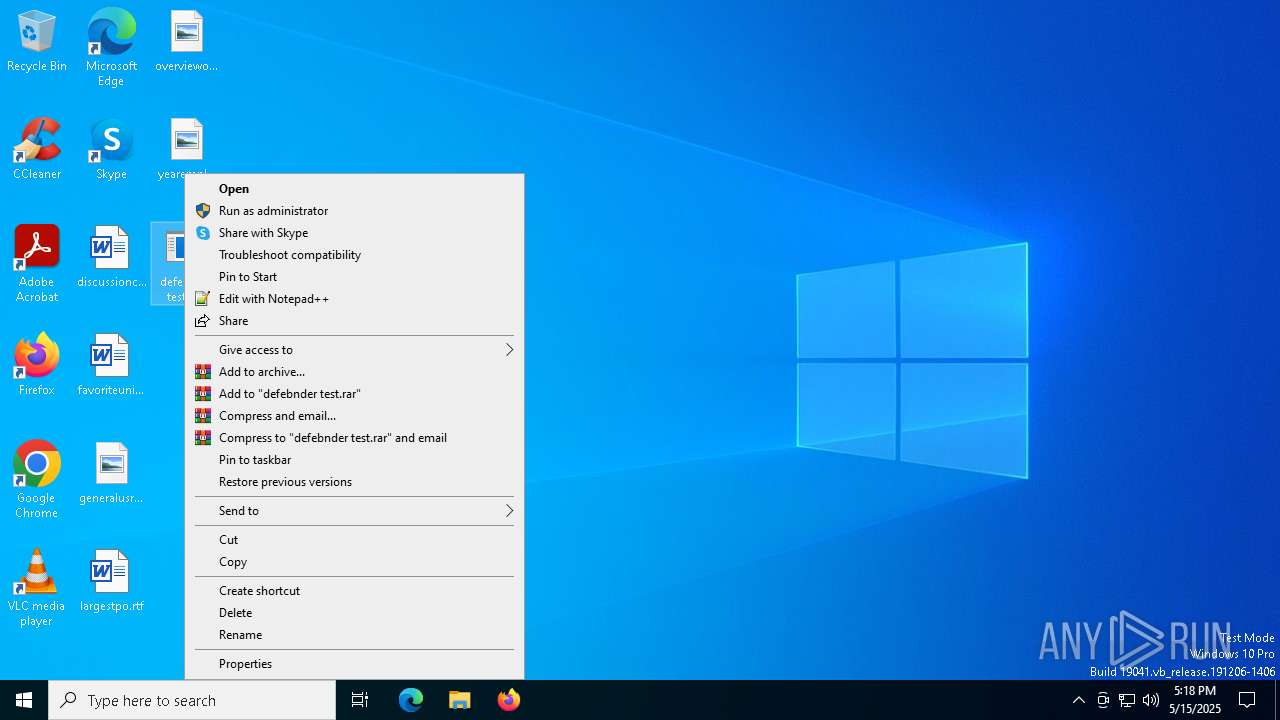
Manual execution by a user
- notepad++.exe (PID: 8172)
- defebnder test.exe (PID: 7284)
Reads the software policy settings
- slui.exe (PID: 7404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(7336) defebnder test.exe
Version1.4.1
C2 (2)213.134.190.18:4782
Sub_DirSubDir
Install_NameClient.exe
Mutexc0c427ee-236b-43ed-8934-072a1b61994a
StartupVindowsDefender
TagTestGryhol
LogDirLogs
SignatureC8phl3ATEznYLynH3HKAisi4oXnKlsswvjV/hE3MWvlKkXngBC0mTcLrJ2M+wM1vwZzq+CcqPB+sKCngox8723LR9j7O+egtMLBK1xPzSEAXdM9vGg9rr677iRIPmwHbhhYumuyaHejhwDCwLxvQvXNOjc8fXcOIjPoWqP2B4VLAZhqeqyQymgLvz6zYMmPKgccrcb3QQ6l3i1o/odAWGB2NxT/sPwwf2yt+lG0QsfMIfRGytKQ9O3lL5IHBpNaWqQgNNBN4gGh3ze47tpu4WbS+drN5xdcL2S7bB1339tsC...
CertificateMIIE9DCCAtygAwIBAgIQAPWt5S5ZA0gf0iId7KdLhzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI1MDUxMzE2NTQwNVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAmRIFy3SLnHO1nhcfXfp3em9vWYvqsjzqo1+OvU4opT55bVHiGQqO1+Xva0XJ9t1MBM9QJBHb...
(PID) Process(3268) Client.exe
Version1.4.1
C2 (2)213.134.190.18:4782
Sub_DirSubDir
Install_NameClient.exe
Mutexc0c427ee-236b-43ed-8934-072a1b61994a
StartupVindowsDefender
TagTestGryhol
LogDirLogs
SignatureC8phl3ATEznYLynH3HKAisi4oXnKlsswvjV/hE3MWvlKkXngBC0mTcLrJ2M+wM1vwZzq+CcqPB+sKCngox8723LR9j7O+egtMLBK1xPzSEAXdM9vGg9rr677iRIPmwHbhhYumuyaHejhwDCwLxvQvXNOjc8fXcOIjPoWqP2B4VLAZhqeqyQymgLvz6zYMmPKgccrcb3QQ6l3i1o/odAWGB2NxT/sPwwf2yt+lG0QsfMIfRGytKQ9O3lL5IHBpNaWqQgNNBN4gGh3ze47tpu4WbS+drN5xdcL2S7bB1339tsC...
CertificateMIIE9DCCAtygAwIBAgIQAPWt5S5ZA0gf0iId7KdLhzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI1MDUxMzE2NTQwNVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAmRIFy3SLnHO1nhcfXfp3em9vWYvqsjzqo1+OvU4opT55bVHiGQqO1+Xva0XJ9t1MBM9QJBHb...
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:03:12 16:16:39+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 3261952 |
| InitializedDataSize: | 3584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31e3fe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.1.0 |
| ProductVersionNumber: | 1.4.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Quasar Client |
| FileVersion: | 1.4.1 |
| InternalName: | Client.exe |
| LegalCopyright: | Copyright © MaxXor 2023 |
| LegalTrademarks: | - |
| OriginalFileName: | Client.exe |
| ProductName: | Quasar |
| ProductVersion: | 1.4.1 |
| AssemblyVersion: | 1.4.1.0 |
Total processes
141
Monitored processes
11
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | "schtasks" /create /tn "VindowsDefender" /sc ONLOGON /tr "C:\WINDOWS\system32\SubDir\Client.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3268 | "C:\WINDOWS\system32\SubDir\Client.exe" | C:\Windows\System32\SubDir\Client.exe | defebnder test.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Quasar Client Version: 1.4.1 Modules
Quasar(PID) Process(3268) Client.exe Version1.4.1 C2 (2)213.134.190.18:4782 Sub_DirSubDir Install_NameClient.exe Mutexc0c427ee-236b-43ed-8934-072a1b61994a StartupVindowsDefender TagTestGryhol LogDirLogs SignatureC8phl3ATEznYLynH3HKAisi4oXnKlsswvjV/hE3MWvlKkXngBC0mTcLrJ2M+wM1vwZzq+CcqPB+sKCngox8723LR9j7O+egtMLBK1xPzSEAXdM9vGg9rr677iRIPmwHbhhYumuyaHejhwDCwLxvQvXNOjc8fXcOIjPoWqP2B4VLAZhqeqyQymgLvz6zYMmPKgccrcb3QQ6l3i1o/odAWGB2NxT/sPwwf2yt+lG0QsfMIfRGytKQ9O3lL5IHBpNaWqQgNNBN4gGh3ze47tpu4WbS+drN5xdcL2S7bB1339tsC... CertificateMIIE9DCCAtygAwIBAgIQAPWt5S5ZA0gf0iId7KdLhzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI1MDUxMzE2NTQwNVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAmRIFy3SLnHO1nhcfXfp3em9vWYvqsjzqo1+OvU4opT55bVHiGQqO1+Xva0XJ9t1MBM9QJBHb... | |||||||||||||||
| 4008 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6184 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7284 | "C:\Users\admin\Desktop\defebnder test.exe" | C:\Users\admin\Desktop\defebnder test.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Quasar Client Exit code: 3 Version: 1.4.1 Modules
| |||||||||||||||
| 7328 | "schtasks" /create /tn "VindowsDefender" /sc ONLOGON /tr "C:\WINDOWS\system32\SubDir\Client.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | defebnder test.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7336 | "C:\Users\admin\Desktop\defebnder test.exe" | C:\Users\admin\Desktop\defebnder test.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Version: 1.4.1 Modules
Quasar(PID) Process(7336) defebnder test.exe Version1.4.1 C2 (2)213.134.190.18:4782 Sub_DirSubDir Install_NameClient.exe Mutexc0c427ee-236b-43ed-8934-072a1b61994a StartupVindowsDefender TagTestGryhol LogDirLogs SignatureC8phl3ATEznYLynH3HKAisi4oXnKlsswvjV/hE3MWvlKkXngBC0mTcLrJ2M+wM1vwZzq+CcqPB+sKCngox8723LR9j7O+egtMLBK1xPzSEAXdM9vGg9rr677iRIPmwHbhhYumuyaHejhwDCwLxvQvXNOjc8fXcOIjPoWqP2B4VLAZhqeqyQymgLvz6zYMmPKgccrcb3QQ6l3i1o/odAWGB2NxT/sPwwf2yt+lG0QsfMIfRGytKQ9O3lL5IHBpNaWqQgNNBN4gGh3ze47tpu4WbS+drN5xdcL2S7bB1339tsC... CertificateMIIE9DCCAtygAwIBAgIQAPWt5S5ZA0gf0iId7KdLhzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI1MDUxMzE2NTQwNVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAmRIFy3SLnHO1nhcfXfp3em9vWYvqsjzqo1+OvU4opT55bVHiGQqO1+Xva0XJ9t1MBM9QJBHb... | |||||||||||||||
| 7368 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7404 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 444
Read events
1 444
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8172 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:312281C4126FA897EF21A7E8CCB8D495 | SHA256:53B4BE3ED1CFD712E53542B30CFE30C5DB35CC48BE7C57727DFEC26C9E882E90 | |||
| 8172 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
| 8172 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:F11D96162BC521F5CF49FFE6B6841C9B | SHA256:BE9AEAEAB5A2E4899BA7E582274BA592C1B9BAF688B340A754B8EF32B23CFA9C | |||
| 8172 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:99D37B9A400CCCF21FE24886DCBEA52C | SHA256:F0535E4243387A70D72A255BA98DFC1889520C2CBF7EFFF6061DB3E123EE68DC | |||
| 7284 | defebnder test.exe | C:\Windows\System32\SubDir\Client.exe | executable | |
MD5:76D0E6F4FA88CC77A14FCEA9E86A9225 | SHA256:3F0756421FDBA3C07A117BA9E4575AB28E4200FEDCF945F49B6458A10A39E9DC | |||
| 8172 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:A2ED875AA42589077C4D08F4F8912018 | SHA256:77B0174D655F327C1FC9520B4F8831ECD82E98351B26BB9C2EDD98FF0CD63A2D | |||
| 8172 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:FE22EC5755BC98988F9656F73B2E6FB8 | SHA256:F972C425CE176E960F6347F1CA2F64A8CE2B95A375C33A03E57538052BA0624D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
61
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7820 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7820 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.1:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7820 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |