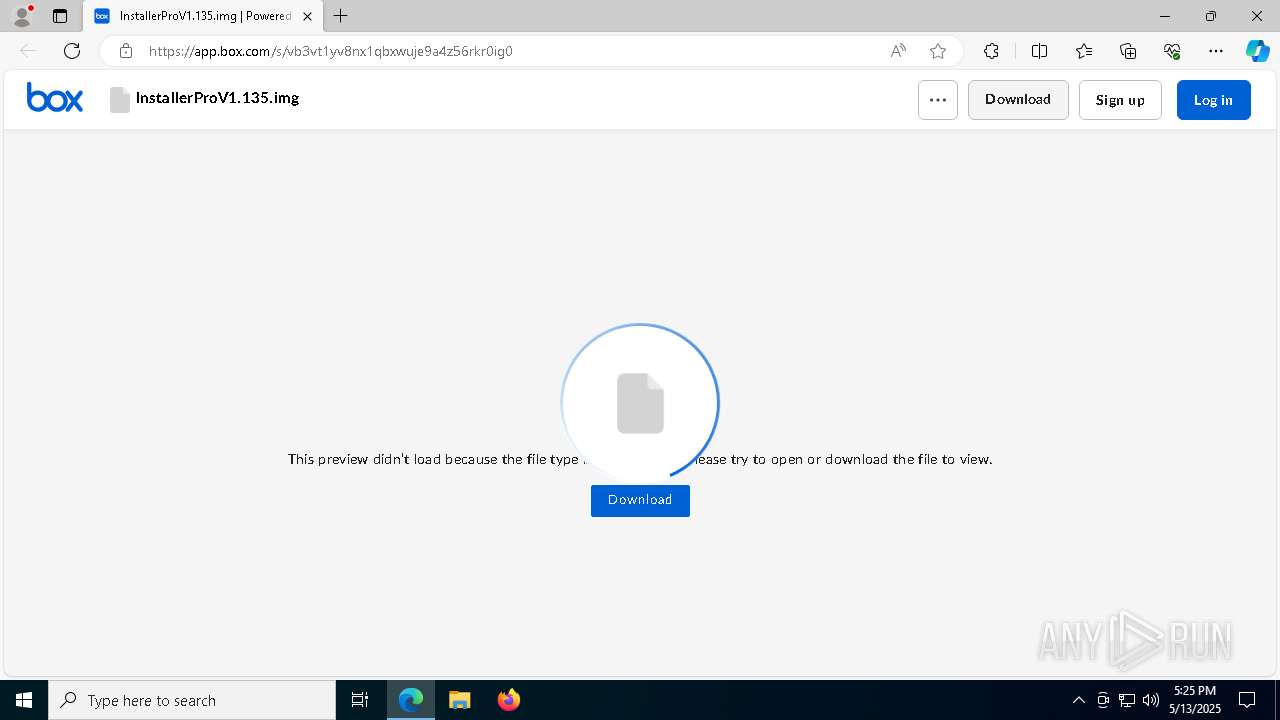
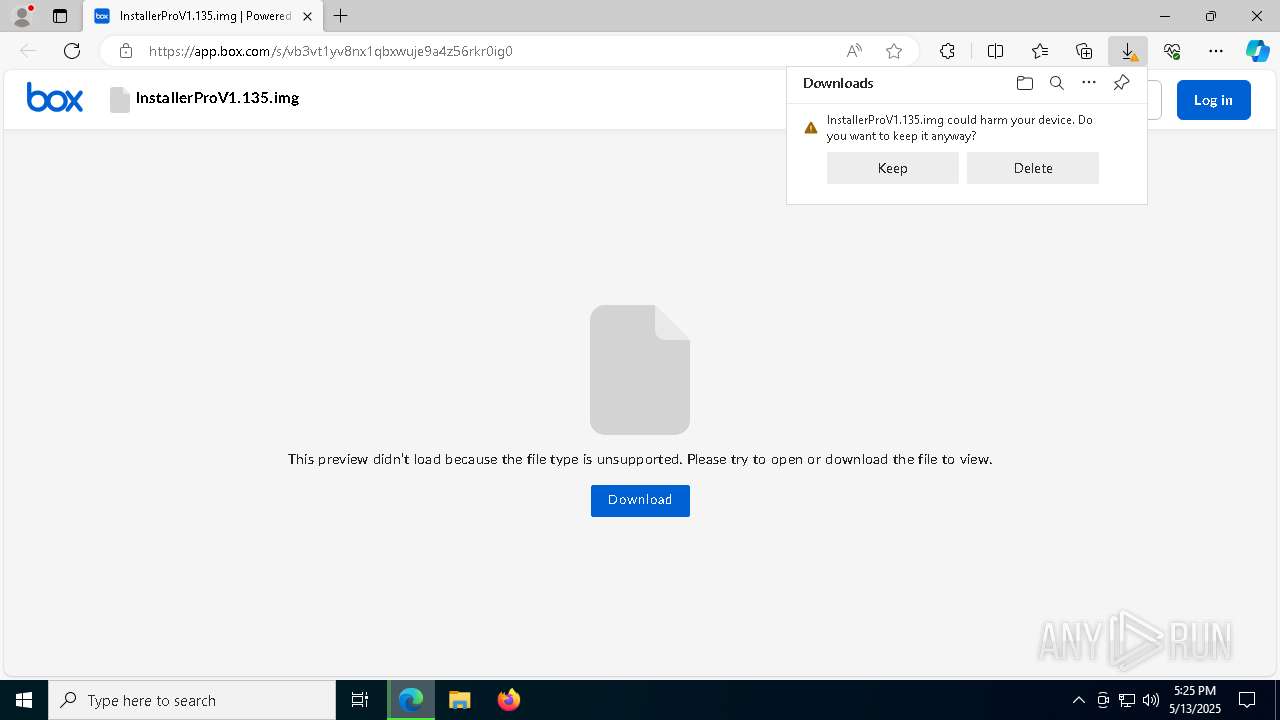
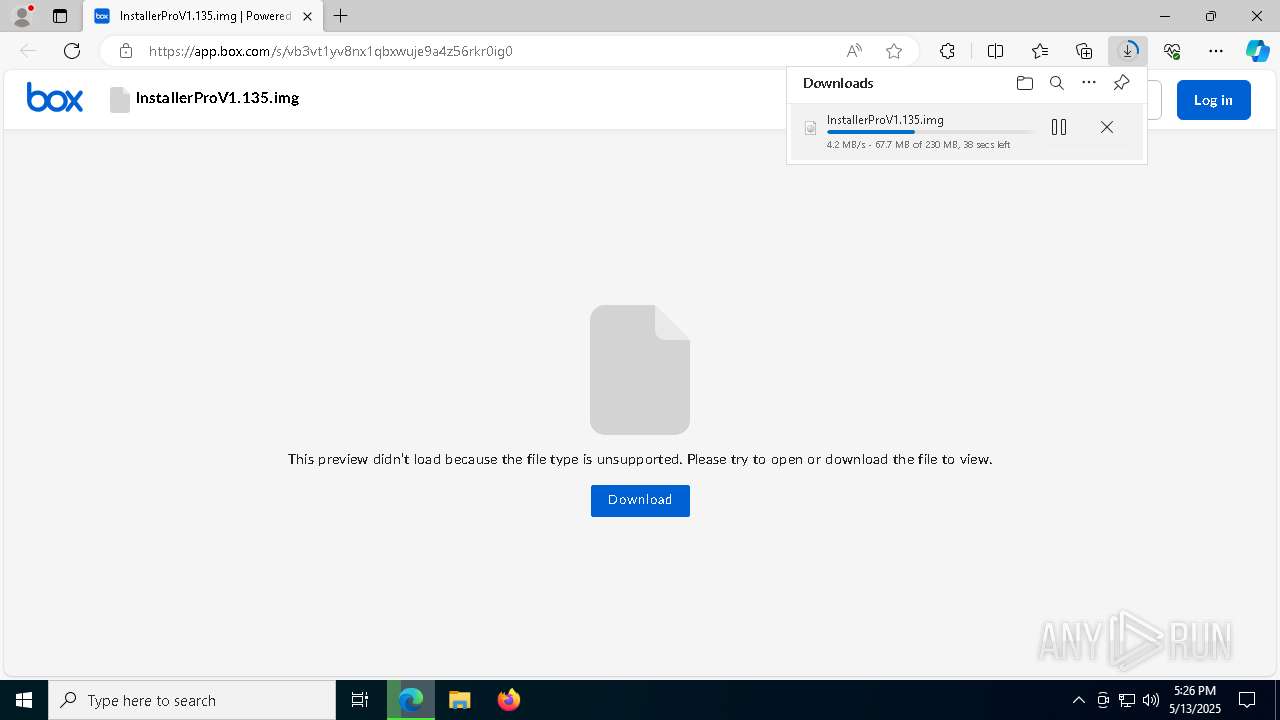
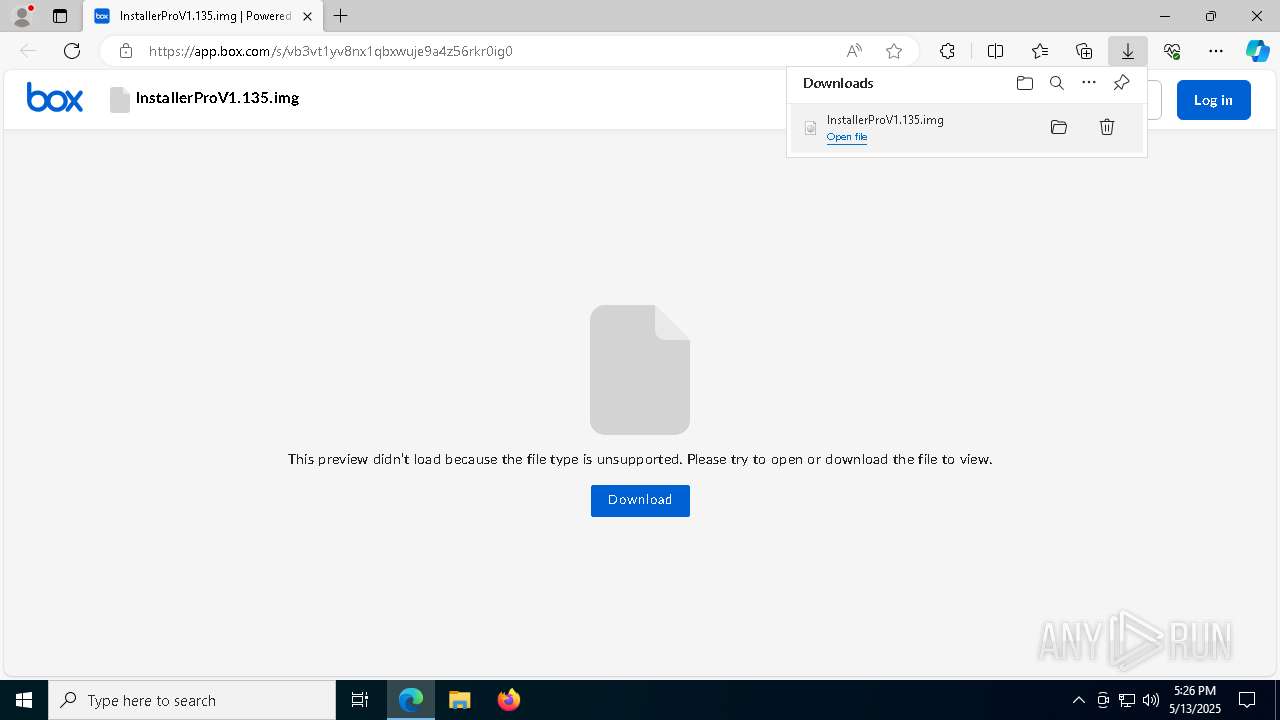
| URL: | https://app.box.com/s/vb3vt1yv8nx1qbxwuje9a4z56rkr0ig0 |
| Full analysis: | https://app.any.run/tasks/be704040-59d9-4dc3-b305-ba1c3fb9ea4d |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | May 13, 2025, 17:25:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E5A517851E821422BB11162FDC6FC171 |
| SHA1: | E81218FB7CF592DBC2DC2CD2FA1698DC2C7FBE09 |
| SHA256: | 3EFA8BB56B11F0E2EF981F930064C4810BE415CD5DF89C7298E199FFB09860BD |
| SSDEEP: | 3:N8aqLdm6IU05afQbOXVMCVn:2aqkXn8fQb4VJ |
MALICIOUS
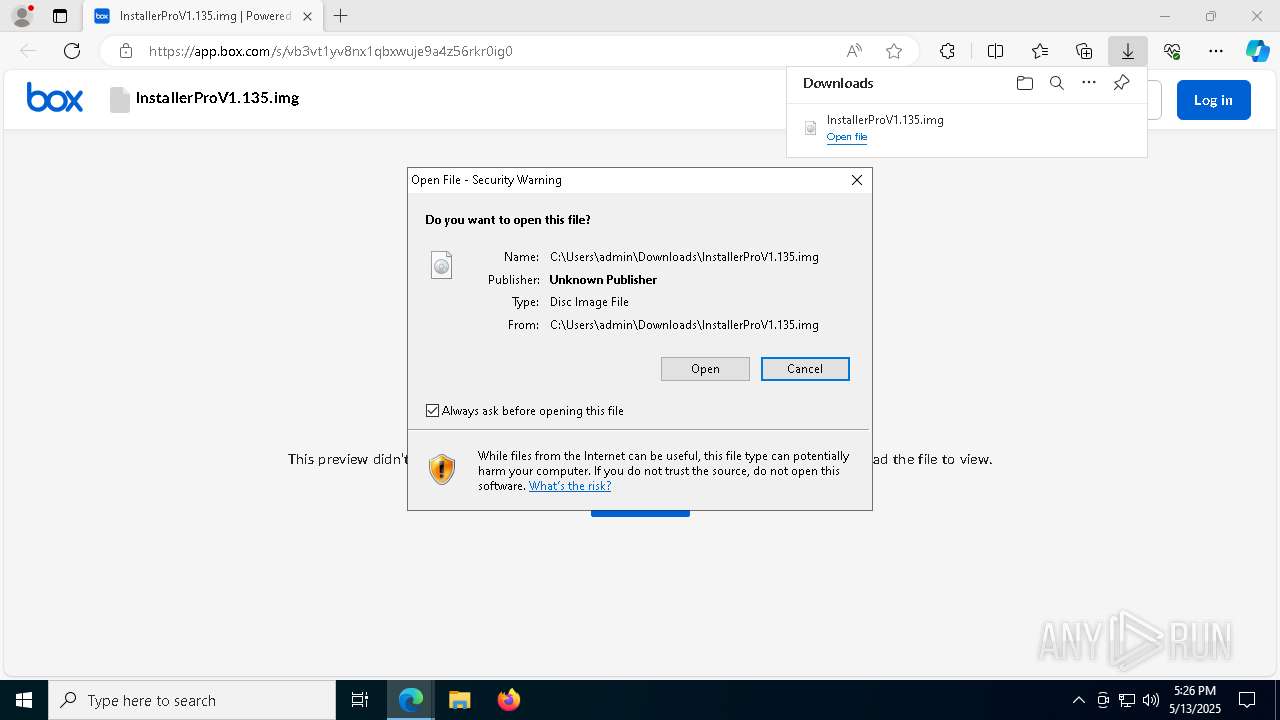
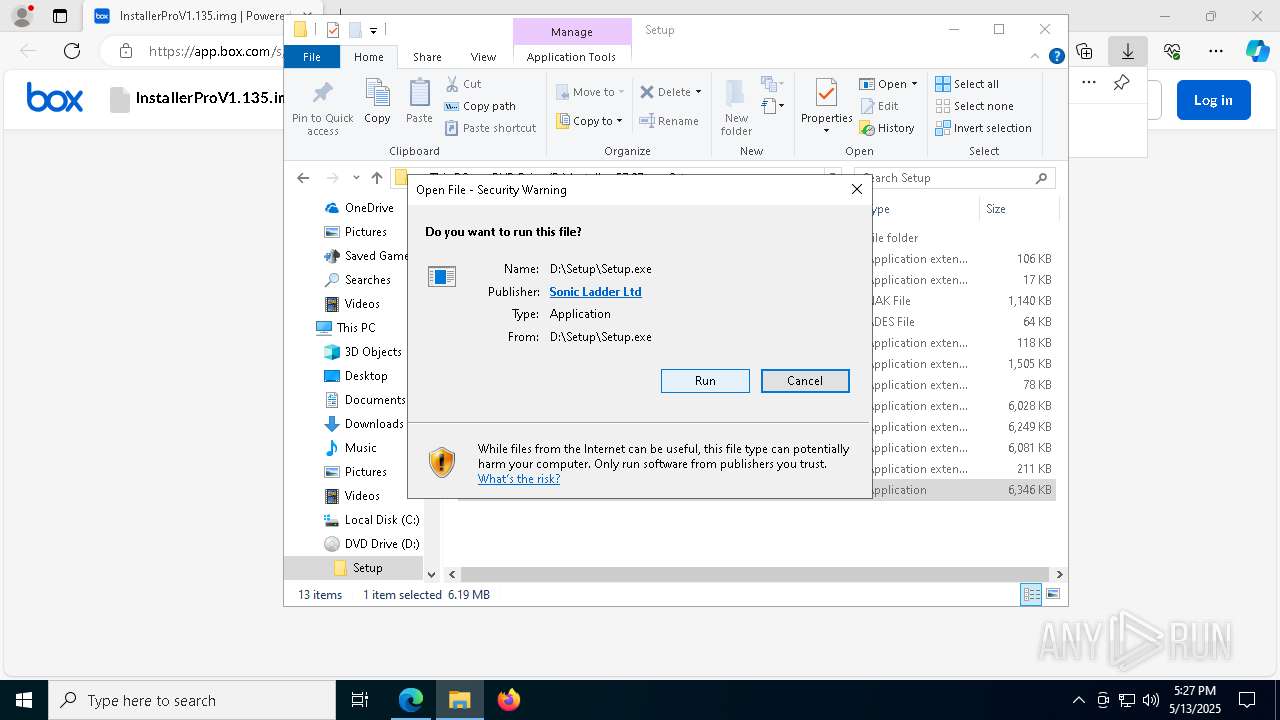
Executing a file with an untrusted certificate
- XPFix.exe (PID: 7188)
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA has been detected (SURICATA)
- SigmaScop86.exe (PID: 728)
- svchost.exe (PID: 2196)
LUMMA mutex has been found
- SigmaScop86.exe (PID: 728)
Steals credentials from Web Browsers
- SigmaScop86.exe (PID: 728)
Actions looks like stealing of personal data
- SigmaScop86.exe (PID: 728)
SUSPICIOUS
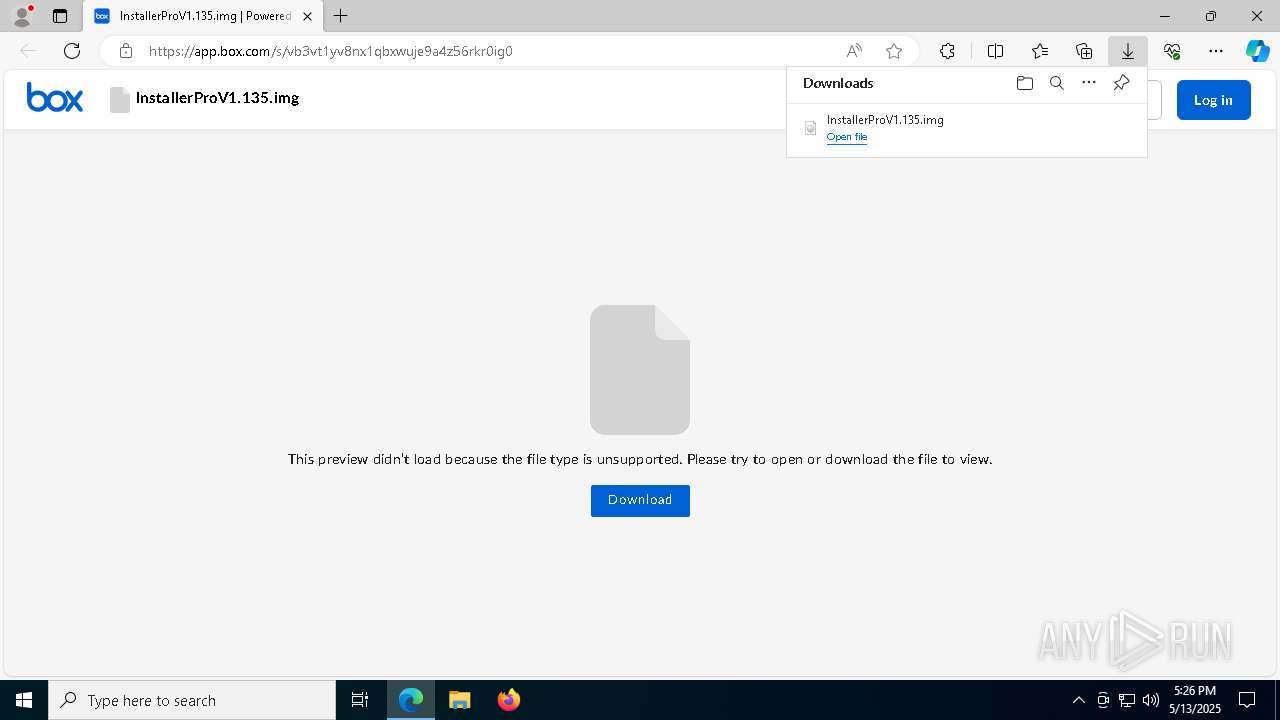
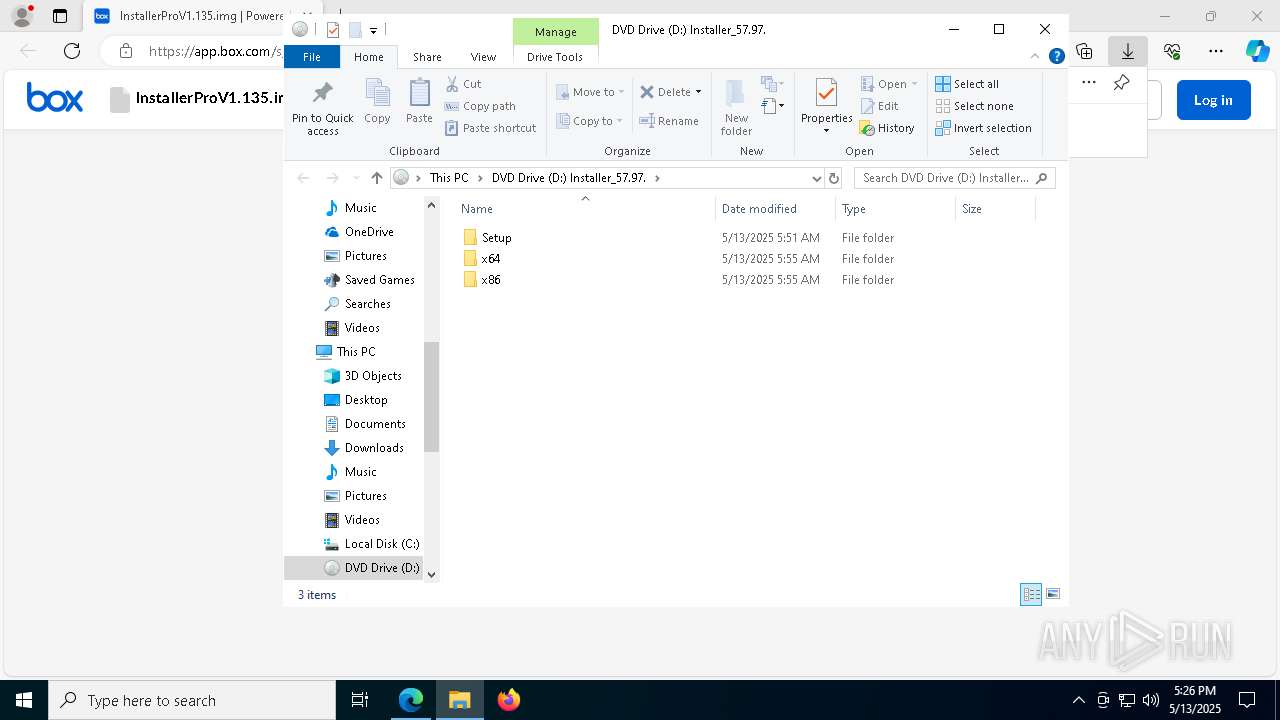
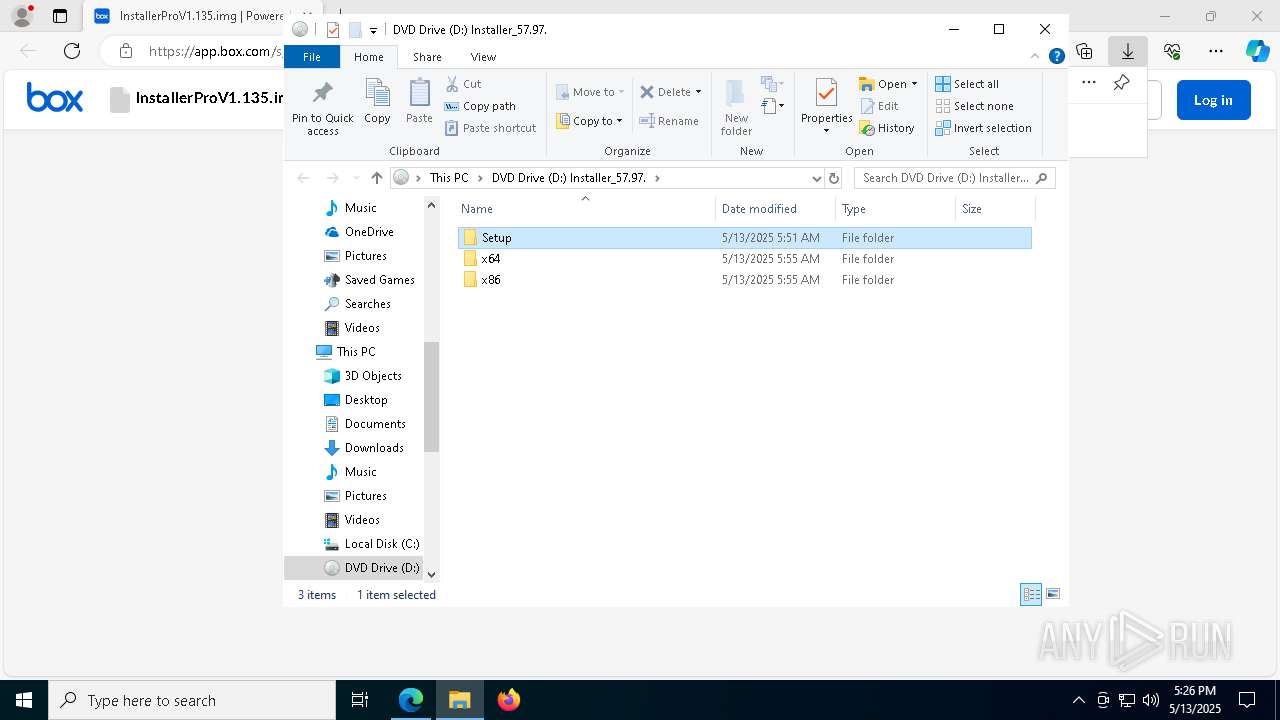
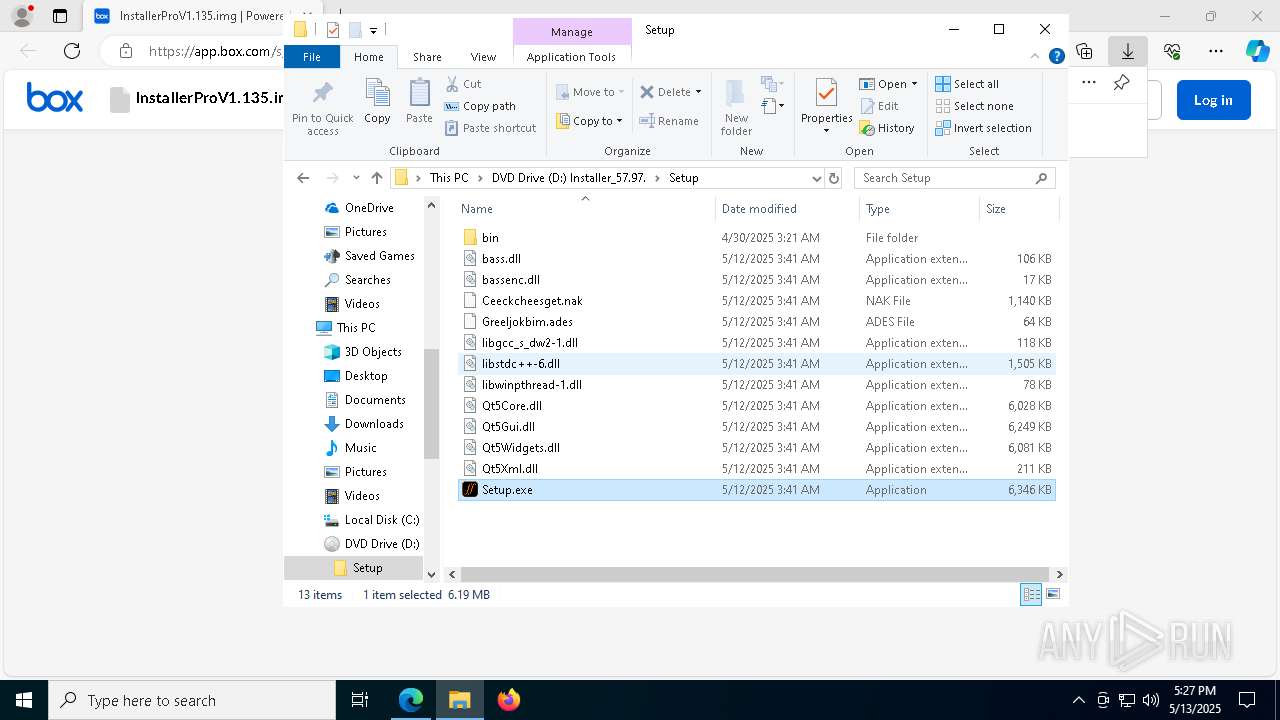
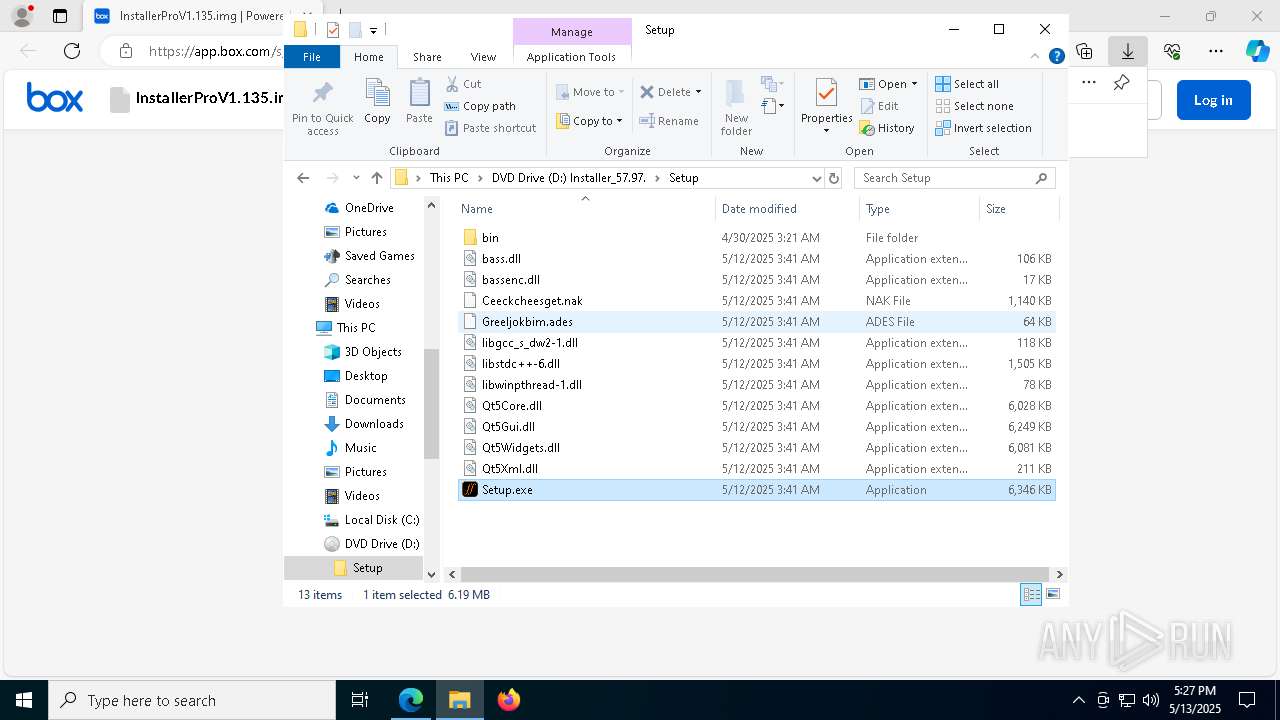
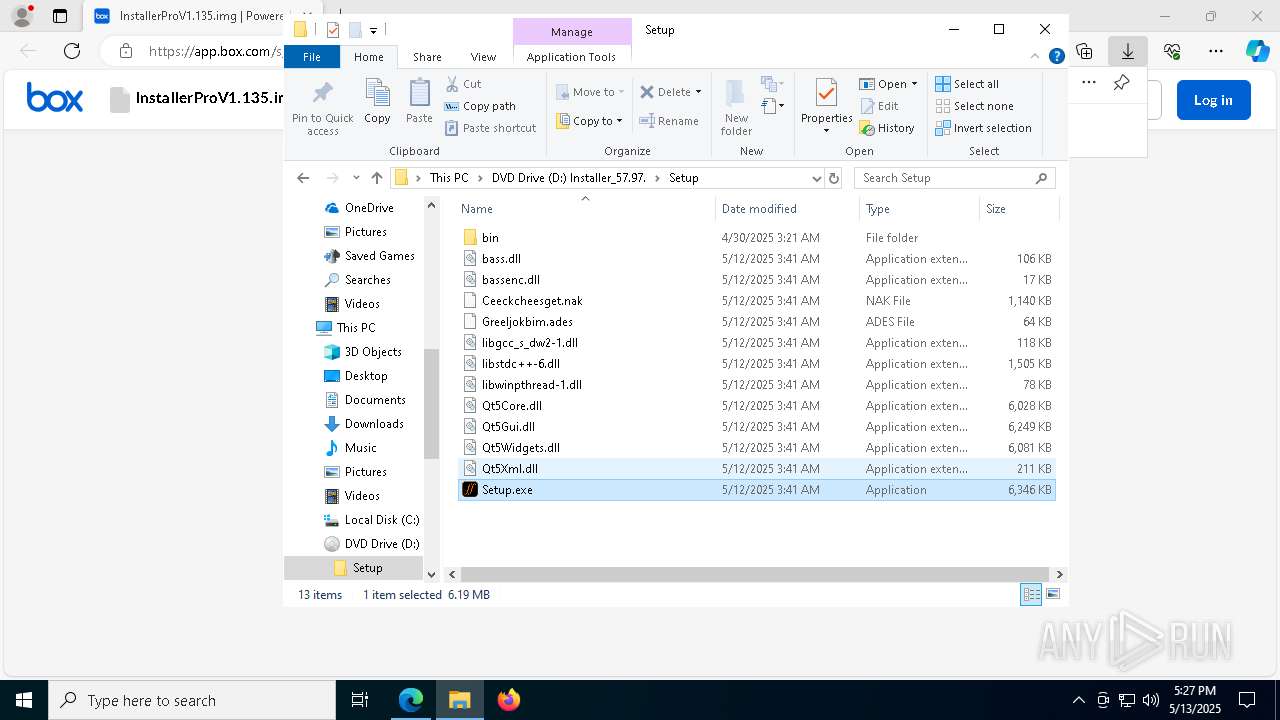
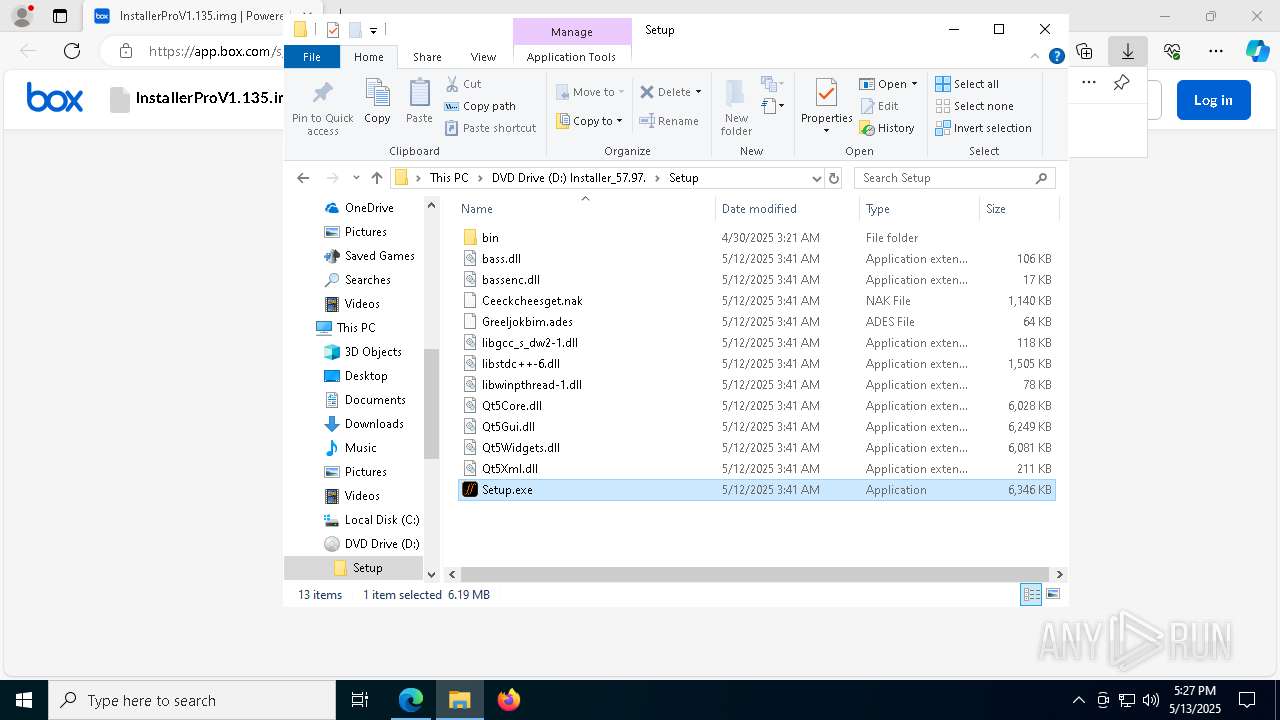
Image mount has been detect
- explorer.exe (PID: 5492)
Executable content was dropped or overwritten
- Setup.exe (PID: 664)
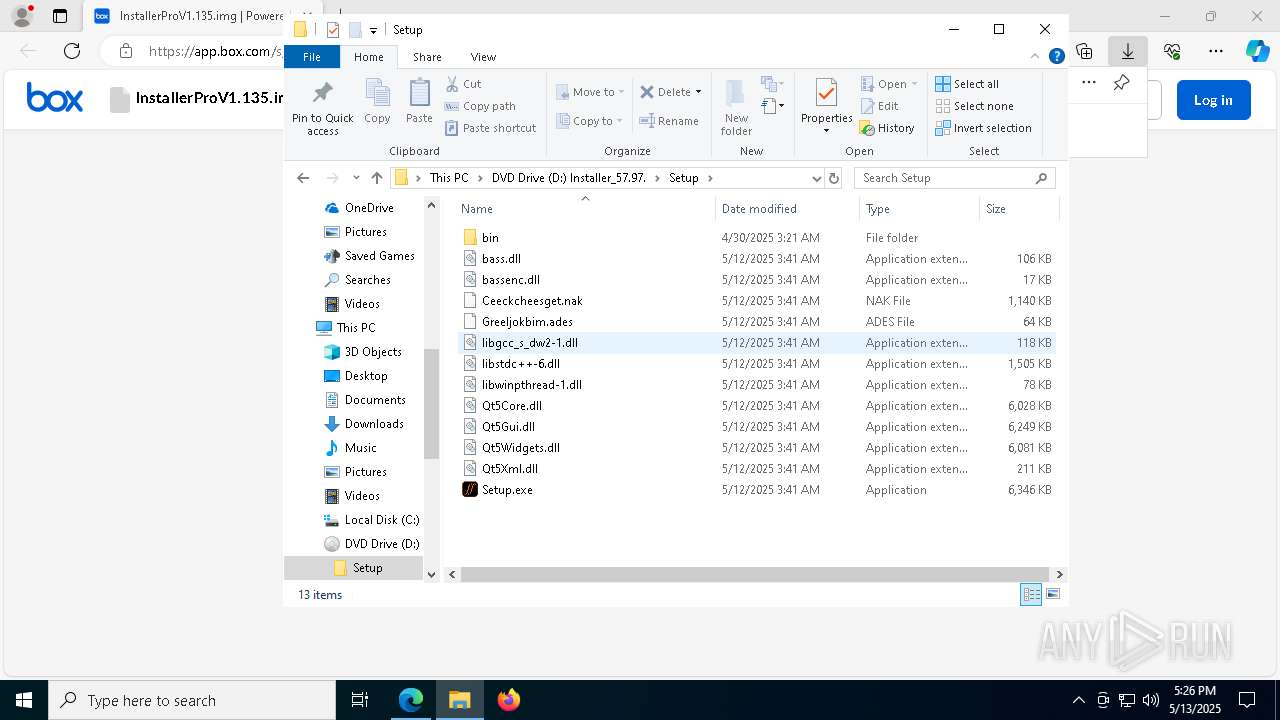
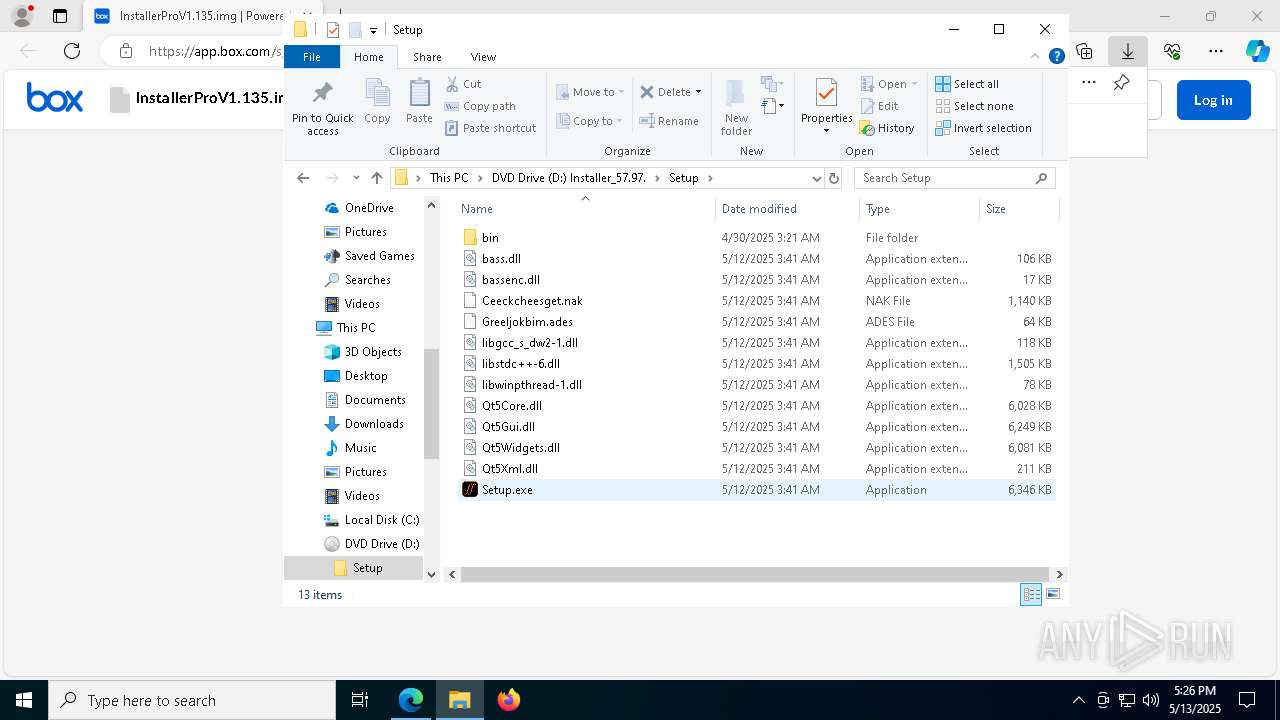
Loading modules from mounted disk drive
- Setup.exe (PID: 664)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- SigmaScop86.exe (PID: 728)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- SigmaScop86.exe (PID: 728)
Searches for installed software
- SigmaScop86.exe (PID: 728)
INFO
Application launched itself
- msedge.exe (PID: 7572)
Reads the computer name
- identity_helper.exe (PID: 5344)
- Setup.exe (PID: 664)
- SigmaScop86.exe (PID: 728)
- XPFix.exe (PID: 7188)
Checks supported languages
- identity_helper.exe (PID: 5344)
- Setup.exe (PID: 664)
- SigmaScop86.exe (PID: 728)
- XPFix.exe (PID: 7188)
Reads Environment values
- identity_helper.exe (PID: 5344)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7572)
Reads the software policy settings
- slui.exe (PID: 7360)
- explorer.exe (PID: 5492)
- SigmaScop86.exe (PID: 728)
- slui.exe (PID: 8036)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5492)
Creates files or folders in the user directory
- explorer.exe (PID: 5492)
- Setup.exe (PID: 664)
Checks proxy server information
- explorer.exe (PID: 5492)
- slui.exe (PID: 8036)
The sample compiled with english language support
- Setup.exe (PID: 664)
- msedge.exe (PID: 2596)
Creates files in the program directory
- Setup.exe (PID: 664)
The sample compiled with chinese language support
- Setup.exe (PID: 664)
Create files in a temporary directory
- Setup.exe (PID: 664)
Executable content was dropped or overwritten
- msedge.exe (PID: 2596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
198
Monitored processes
64
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 664 | "D:\Setup\Setup.exe" | D:\Setup\Setup.exe | explorer.exe | |
User: admin Company: Sonic Ladder Integrity Level: MEDIUM Description: Riffstation v1.6.3.0 Exit code: 0 Version: 1.6.3.0 | ||||
| 728 | C:\ProgramData\SigmaScop86.exe | C:\ProgramData\SigmaScop86.exe | Setup.exe | |
User: admin Integrity Level: MEDIUM | ||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5904 --field-trial-handle=2324,i,8272333139738106789,9585291818119387912,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5800 --field-trial-handle=2324,i,8272333139738106789,9585291818119387912,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4196 --field-trial-handle=2324,i,8272333139738106789,9585291818119387912,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5388 --field-trial-handle=2324,i,8272333139738106789,9585291818119387912,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5932 --field-trial-handle=2324,i,8272333139738106789,9585291818119387912,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 1240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7052 --field-trial-handle=2324,i,8272333139738106789,9585291818119387912,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 1600 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4384 --field-trial-handle=2324,i,8272333139738106789,9585291818119387912,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 1760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5780 --field-trial-handle=2324,i,8272333139738106789,9585291818119387912,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
22
Suspicious files
467
Text files
74
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b98e.TMP | — | |
MD5:— | SHA256:— | |||
| 7572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b98e.TMP | — | |
MD5:— | SHA256:— | |||
| 7572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b98e.TMP | — | |
MD5:— | SHA256:— | |||
| 7572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b99d.TMP | — | |
MD5:— | SHA256:— | |||
| 7572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b99d.TMP | — | |
MD5:— | SHA256:— | |||
| 7572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
100
DNS requests
101
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6392 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6392 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6584 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6584 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4740 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747700501&P2=404&P3=2&P4=RGi7Wk%2f3hFzPf4ESrzINKr%2bcf6Vhhw6FpEH%2f3sD1D9dRdWYwvJj0RsHY88PSxpf2rAbFrv%2bMNjonjHPT20xBtQ%3d%3d | unknown | — | — | whitelisted |
4740 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747700501&P2=404&P3=2&P4=RGi7Wk%2f3hFzPf4ESrzINKr%2bcf6Vhhw6FpEH%2f3sD1D9dRdWYwvJj0RsHY88PSxpf2rAbFrv%2bMNjonjHPT20xBtQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7824 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7572 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7824 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
app.box.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
728 | SigmaScop86.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
728 | SigmaScop86.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (lancery .digital in TLS SNI) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (lancery .digital) |
728 | SigmaScop86.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (lancery .digital in TLS SNI) |
728 | SigmaScop86.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (lancery .digital in TLS SNI) |
728 | SigmaScop86.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (lancery .digital in TLS SNI) |
728 | SigmaScop86.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (lancery .digital in TLS SNI) |
728 | SigmaScop86.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (lancery .digital in TLS SNI) |