| File name: | Swift Copy_0.005242019.tar |
| Full analysis: | https://app.any.run/tasks/4c4a382a-d248-4ba7-a9b1-190b0ba698c4 |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | May 24, 2019, 14:17:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
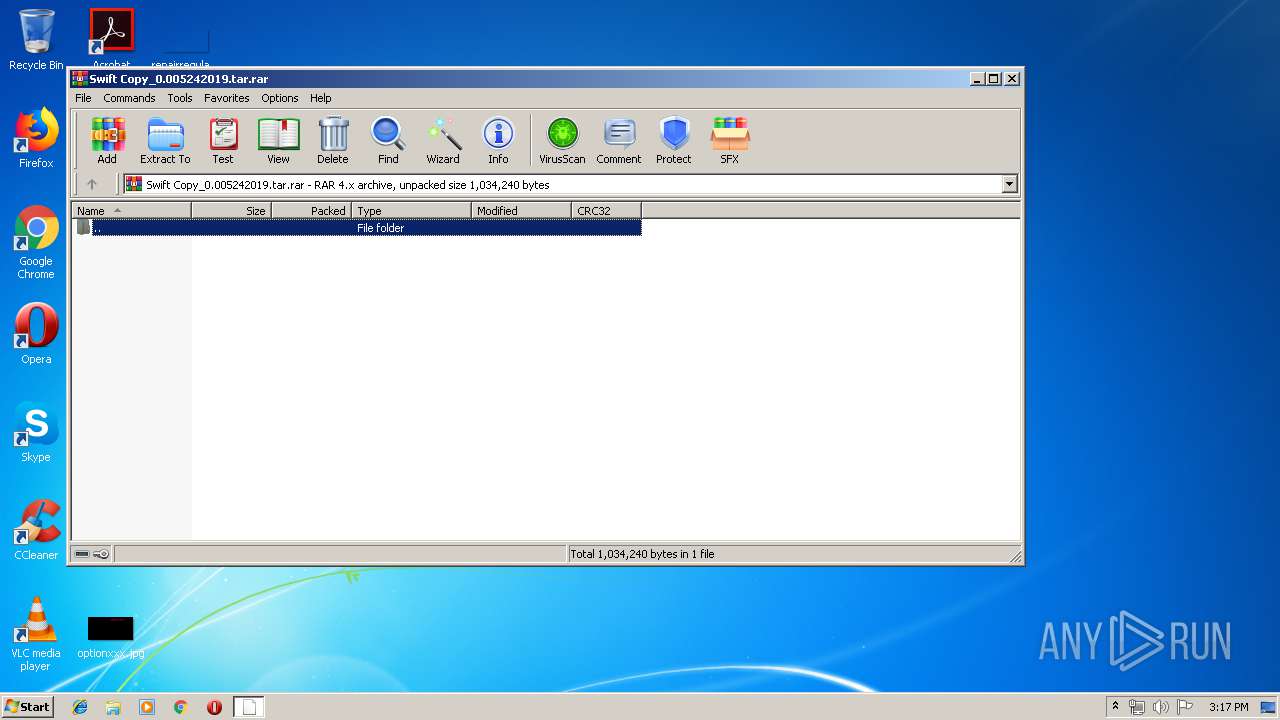
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 64C6B689B6D5912E62DB1DAAF382FEF4 |
| SHA1: | 6AA1F510B25BC4765DE1EBF81DB3E4509262DB1A |
| SHA256: | 3E19EADEE2F5A1E03FC4BD305DD14D1C5A67B10280BD5AD1088AC3FADC8EBCA4 |
| SSDEEP: | 12288:ysRPnbkFYUwGX7El2L00e5aJtTtPQZ+MQIqyl:vRPbkFYU5XxLq5aJxtPQ8nYl |
MALICIOUS
Application was dropped or rewritten from another process
- Swift Copy_0.005242019.exe (PID: 3252)
Actions looks like stealing of personal data
- vbc.exe (PID: 2432)
Detected Hawkeye Keylogger
- RegAsm.exe (PID: 404)
SUSPICIOUS
Executes scripts
- RegAsm.exe (PID: 404)
Checks for external IP
- RegAsm.exe (PID: 404)
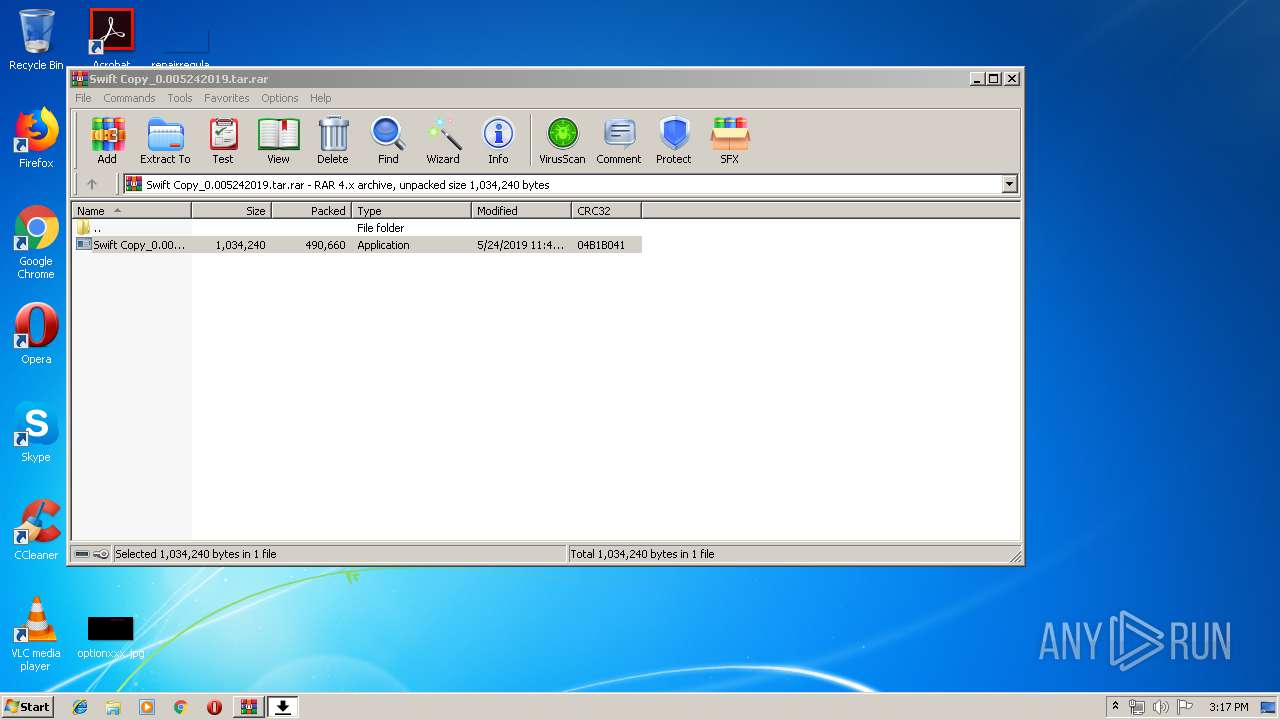
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2844)
Creates files in the user directory
- RegAsm.exe (PID: 404)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 3236)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 490712 |
|---|---|
| UncompressedSize: | 1034240 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2019:05:24 11:41:07 |
| PackingMethod: | Normal |
| ArchivedFileName: | Swift Copy_0.005242019.exe |
Total processes
38
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2844.44830\Swift Copy_0.005242019.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | Swift Copy_0.005242019.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2432 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe /stext "C:\Users\admin\AppData\Local\Temp\holdermail.txt" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 2844 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Swift Copy_0.005242019.tar.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3236 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe /stext "C:\Users\admin\AppData\Local\Temp\holderwb.txt" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | — | RegAsm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3252 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2844.44830\Swift Copy_0.005242019.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2844.44830\Swift Copy_0.005242019.exe | WinRAR.exe | ||||||||||||
User: admin Company: defection's Integrity Level: MEDIUM Description: Orthos Exit code: 0 Version: 1.5.5.3 Modules
| |||||||||||||||
Total events
547
Read events
522
Write events
25
Delete events
0
Modification events
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Swift Copy_0.005242019.tar.rar | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2432 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holdermail.txt | — | |
MD5:— | SHA256:— | |||
| 3236 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holderwb.txt | — | |
MD5:— | SHA256:— | |||
| 2844 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2844.44830\Swift Copy_0.005242019.exe | executable | |
MD5:— | SHA256:— | |||
| 404 | RegAsm.exe | C:\Users\admin\AppData\Roaming\pidloc.txt | text | |
MD5:EFD1636CFC3CC38FD7BABAE5CAC9EDE0 | SHA256:F827D5B11C1EB3902D601C3E0B59BA32FE11C0B573FBF22FB2AF86BFD4651BBA | |||
| 404 | RegAsm.exe | C:\Users\admin\AppData\Roaming\pid.txt | text | |
MD5:4F4ADCBF8C6F66DCFC8A3282AC2BF10A | SHA256:6B3C238EBCF1F3C07CF0E556FAA82C6B8FE96840FF4B6B7E9962A2D855843A0B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
404 | RegAsm.exe | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
404 | RegAsm.exe | 104.16.155.36:80 | whatismyipaddress.com | Cloudflare Inc | US | shared |
404 | RegAsm.exe | 202.71.109.28:587 | mail.fluiten.com.my | TM-VADS DC Hosting | MY | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
whatismyipaddress.com |
| shared |
mail.fluiten.com.my |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
404 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spyware.HawkEyeKeyLogger (IP Chck) |
404 | RegAsm.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
404 | RegAsm.exe | A Network Trojan was detected | ET TROJAN HawkEye Keylogger Report SMTP |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
Swift Copy_0.005242019.exe | User32.dll |
Swift Copy_0.005242019.exe | User32.dll |
Swift Copy_0.005242019.exe | User32.dll |
Swift Copy_0.005242019.exe | User32.dll |
Swift Copy_0.005242019.exe | User32.dll |
Swift Copy_0.005242019.exe | User32.dll |
Swift Copy_0.005242019.exe | User32.dll |
Swift Copy_0.005242019.exe | User32.dll |
Swift Copy_0.005242019.exe | User32.dll |
Swift Copy_0.005242019.exe | User32.dll |