| File name: | 3e18bdf74f3caef770a7edcf748bdaf0e6a4a21664e69.exe |
| Full analysis: | https://app.any.run/tasks/0d54cfb2-ad52-4d3d-815f-669f60e8cf1f |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | January 07, 2025, 16:12:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 46441DA6848047284FDD6A2DFA19B802 |
| SHA1: | BBAFC91BE5B5C0A1248AAC8E485AEA1A7A4FA03C |
| SHA256: | 3E18BDF74F3CAEF770A7EDCF748BDAF0E6A4A21664E69BF765371529AA07DB9F |
| SSDEEP: | 49152:yaMXCbhTrB07zgfEHfCEBkgRra3r3dOx6xeEr51idYwjy9B4osUk0kbSzgARxCnF:yFXaraXgfwde2ra3rN46JadYwaJs+kbw |
MALICIOUS
ASYNCRAT has been detected (MUTEX)
- MSBuild.exe (PID: 6916)
Steals credentials from Web Browsers
- MSBuild.exe (PID: 6916)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 6916)
ASYNCRAT has been detected (SURICATA)
- MSBuild.exe (PID: 6916)
ASYNCRAT has been detected (YARA)
- MSBuild.exe (PID: 6916)
SUSPICIOUS
Executable content was dropped or overwritten
- 3e18bdf74f3caef770a7edcf748bdaf0e6a4a21664e69.exe (PID: 6732)
Connects to unusual port
- MSBuild.exe (PID: 6916)
Contacting a server suspected of hosting an CnC
- MSBuild.exe (PID: 6916)
INFO
Reads the computer name
- 3e18bdf74f3caef770a7edcf748bdaf0e6a4a21664e69.exe (PID: 6732)
- MSBuild.exe (PID: 6916)
Reads the machine GUID from the registry
- 3e18bdf74f3caef770a7edcf748bdaf0e6a4a21664e69.exe (PID: 6732)
- MSBuild.exe (PID: 6916)
Checks supported languages
- 3e18bdf74f3caef770a7edcf748bdaf0e6a4a21664e69.exe (PID: 6732)
- MSBuild.exe (PID: 6916)
Manual execution by a user
- MSBuild.exe (PID: 6916)
Reads the software policy settings
- MSBuild.exe (PID: 6916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:01:03 23:29:33+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 1086976 |
| InitializedDataSize: | 103936 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x10b59e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | L-Connect |
| CompanyName: | GitHub, Inc. |
| FileDescription: | L-Connect |
| FileVersion: | 1.0.0.0 |
| InternalName: | Wpmutnro.exe |
| LegalCopyright: | Copyright (C) 2015 GitHub, Inc. All rights reserved. |
| LegalTrademarks: | - |
| OriginalFileName: | Wpmutnro.exe |
| ProductName: | L-Connect |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
124
Monitored processes
3
Malicious processes
1
Suspicious processes
0
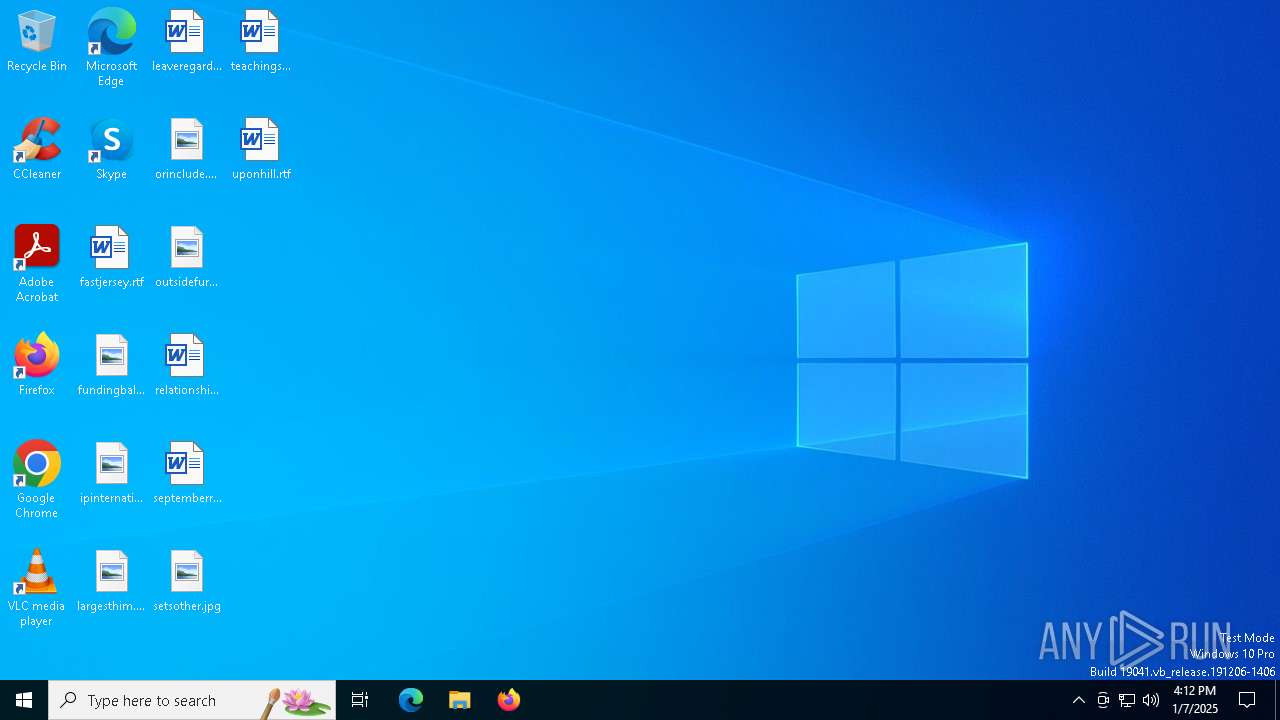
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6732 | "C:\Users\admin\AppData\Local\Temp\3e18bdf74f3caef770a7edcf748bdaf0e6a4a21664e69.exe" | C:\Users\admin\AppData\Local\Temp\3e18bdf74f3caef770a7edcf748bdaf0e6a4a21664e69.exe | explorer.exe | ||||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: L-Connect Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6916 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
3 671
Read events
3 671
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6732 | 3e18bdf74f3caef770a7edcf748bdaf0e6a4a21664e69.exe | C:\Users\admin\AppData\Local\smcdll.exe | executable | |
MD5:46441DA6848047284FDD6A2DFA19B802 | SHA256:3E18BDF74F3CAEF770A7EDCF748BDAF0E6A4A21664E69BF765371529AA07DB9F | |||
| 6732 | 3e18bdf74f3caef770a7edcf748bdaf0e6a4a21664e69.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\smcdll.vbs | text | |
MD5:5EDACA73A5D855947542EBD2BDEEB705 | SHA256:5E3A24DA87E50143C734BA3DA0524DF809C61E3EE37ABF7C40479ECD9EEAC9B7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
33
DNS requests
18
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 96.16.53.165:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.22.57.219:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4652 | svchost.exe | GET | 200 | 2.22.57.219:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6564 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6428 | SIHClient.exe | GET | 200 | 2.22.57.219:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6428 | SIHClient.exe | GET | 200 | 2.22.57.219:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.16.27.225:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 96.16.53.165:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.22.57.219:80 | www.microsoft.com | AKAMAI-AS | FR | whitelisted |
4652 | svchost.exe | 2.22.57.219:80 | www.microsoft.com | AKAMAI-AS | FR | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| unknown |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
jojo.ath.cx |
| malicious |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to ath .cx Domain |
6916 | MSBuild.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
6916 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
6916 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
2 ETPRO signatures available at the full report