| File name: | javaw.exe |
| Full analysis: | https://app.any.run/tasks/487fd0d6-a72d-4730-87e4-5318a83ddb75 |
| Verdict: | Malicious activity |
| Threats: | BlueSky ransomware, first identified in June 2022, shares code similarities with other well-known ransomware families like Conti and Babuk. It primarily spreads via phishing emails and malicious links and can propagate through networks using SMB protocols. BlueSky uses advanced evasion techniques, such as hiding its processes from debuggers via the NtSetInformationThread API, making it difficult for analysts to detect and mitigate its attacks. |
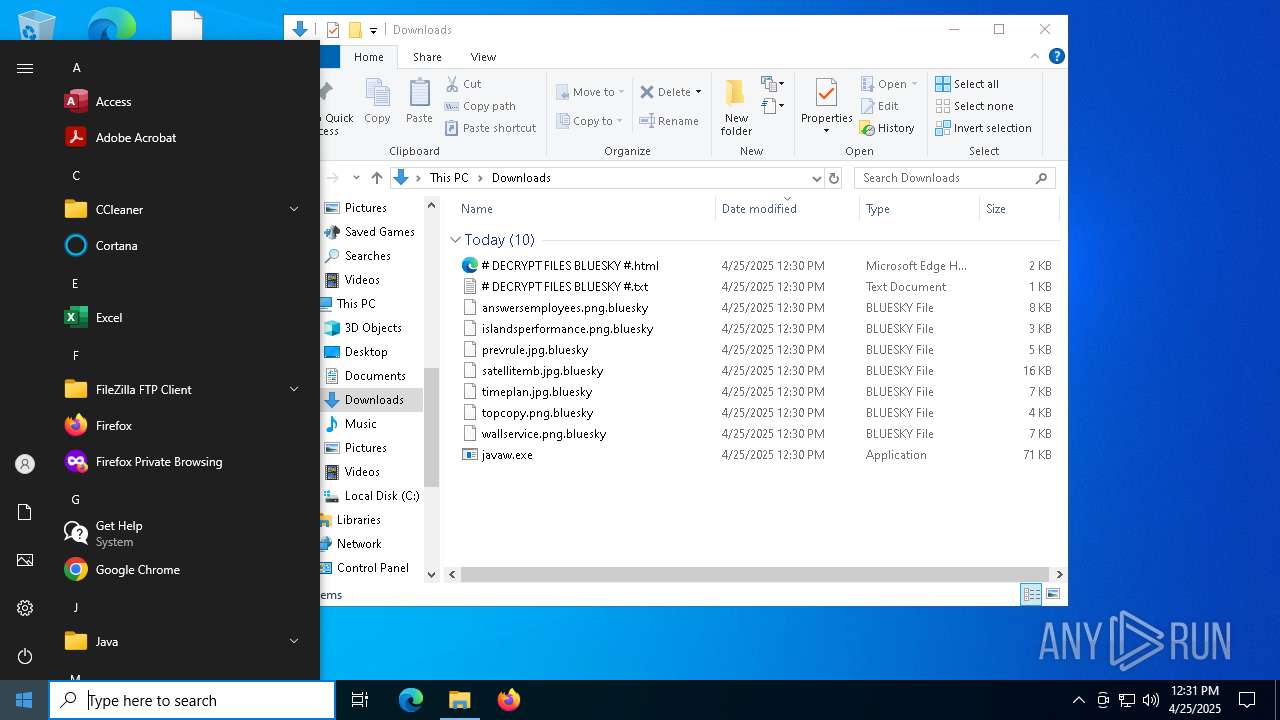
| Analysis date: | April 25, 2025, 12:30:18 |
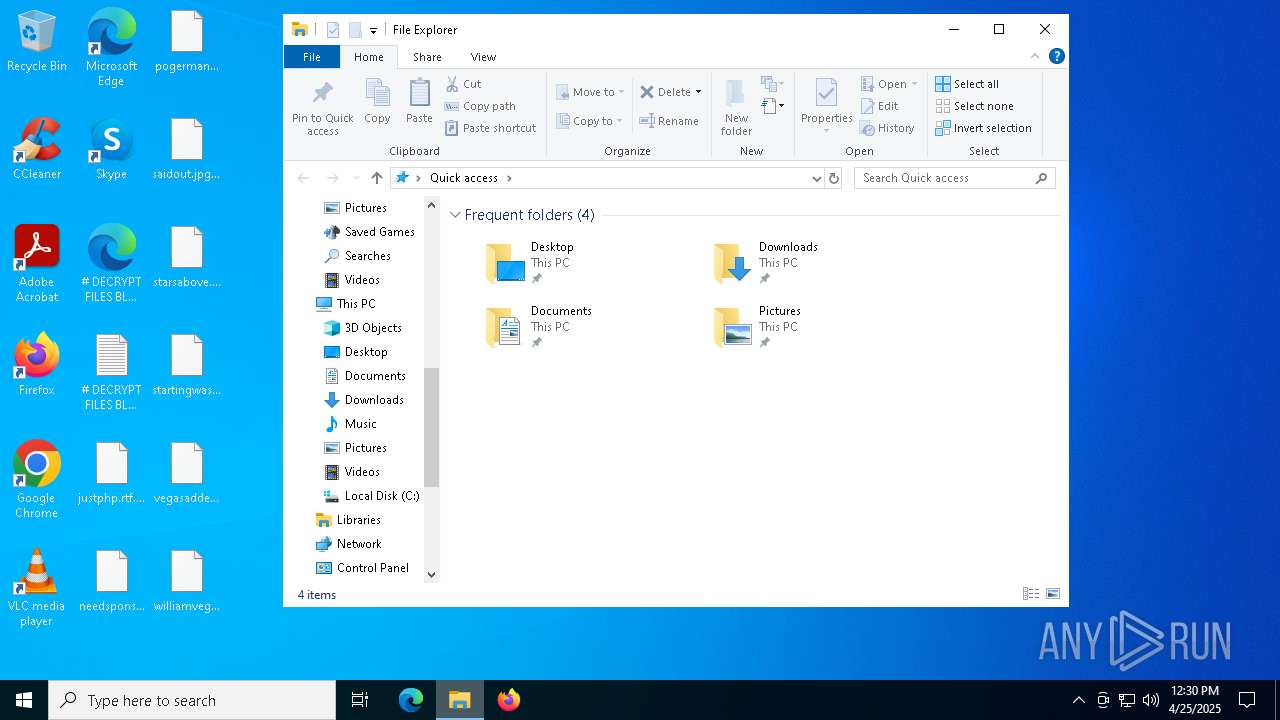
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | D8A44D2ED34B5FEE7C8E24D998F805D9 |
| SHA1: | D8369CB0D8CCEC95B2A49BA34AA7749B60998661 |
| SHA256: | 3E035F2D7D30869CE53171EF5A0F761BFB9C14D94D9FE6DA385E20B8D96DC2FB |
| SSDEEP: | 1536:wBrE2D2ZjyKBQs8swOVWCqBTXdXu3+MkNCMm2i9w4:iBD2RfQ/7OVWS3+1rm2i9w4 |
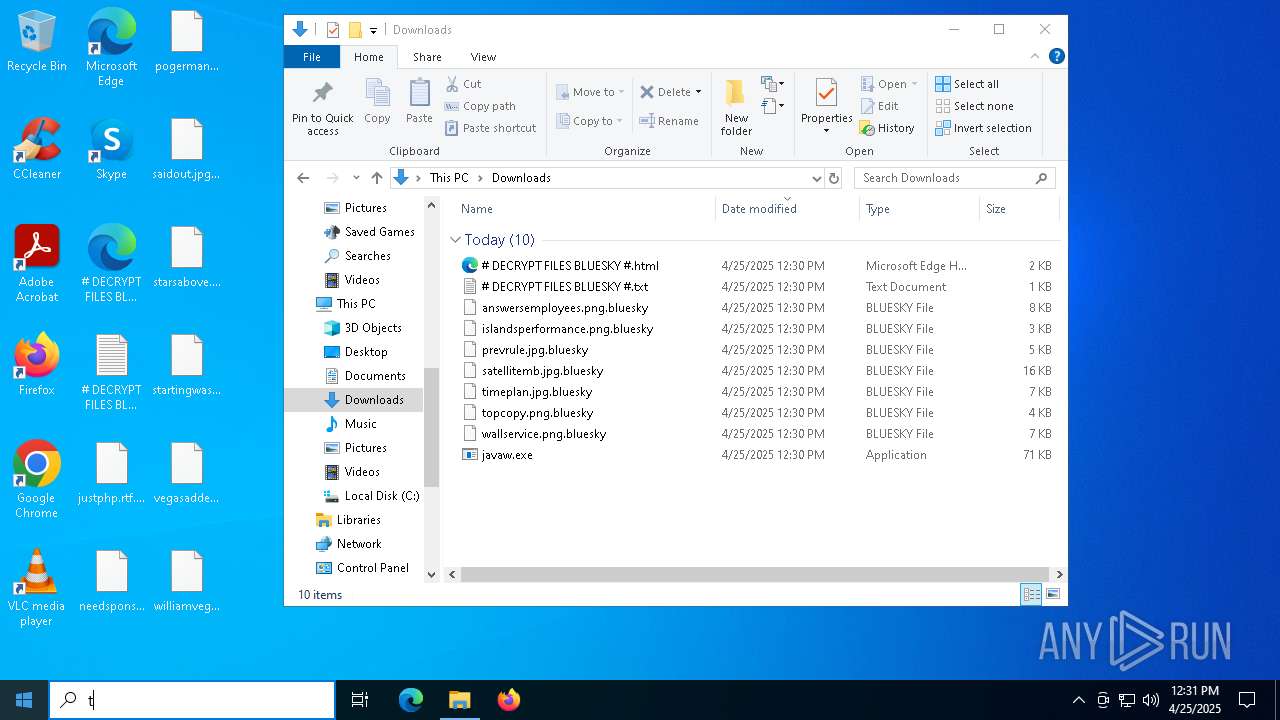
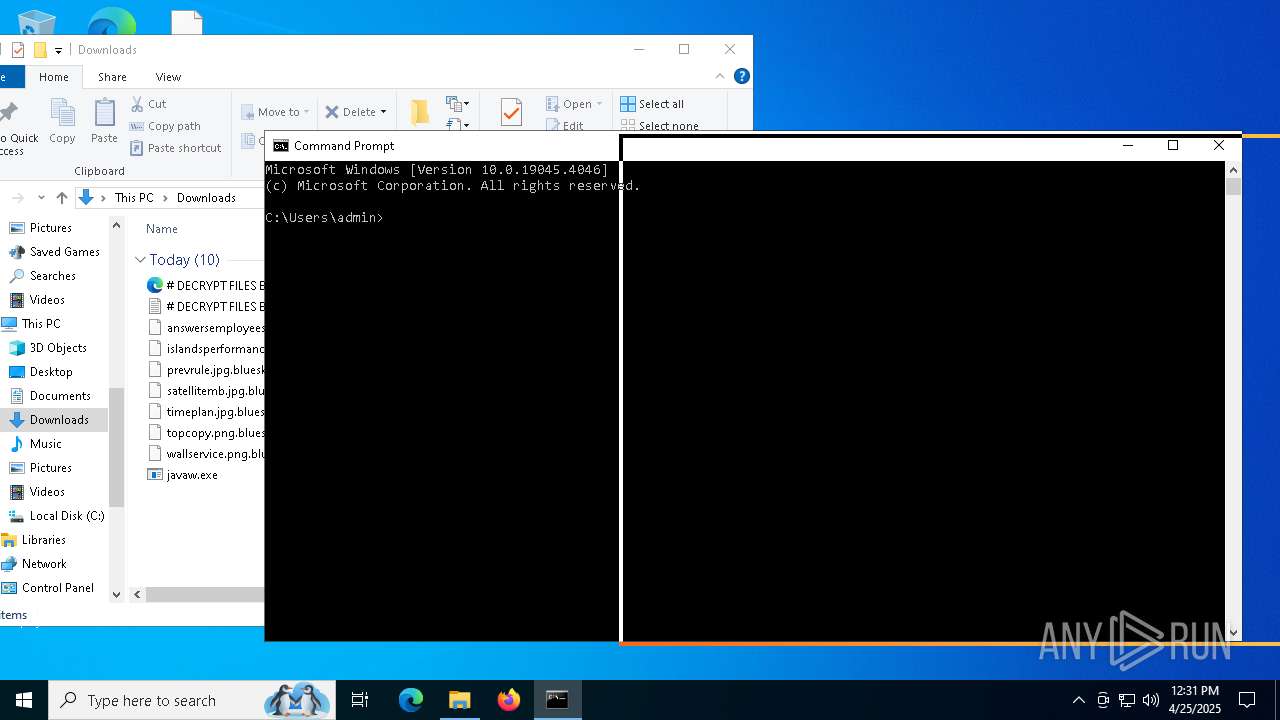
MALICIOUS
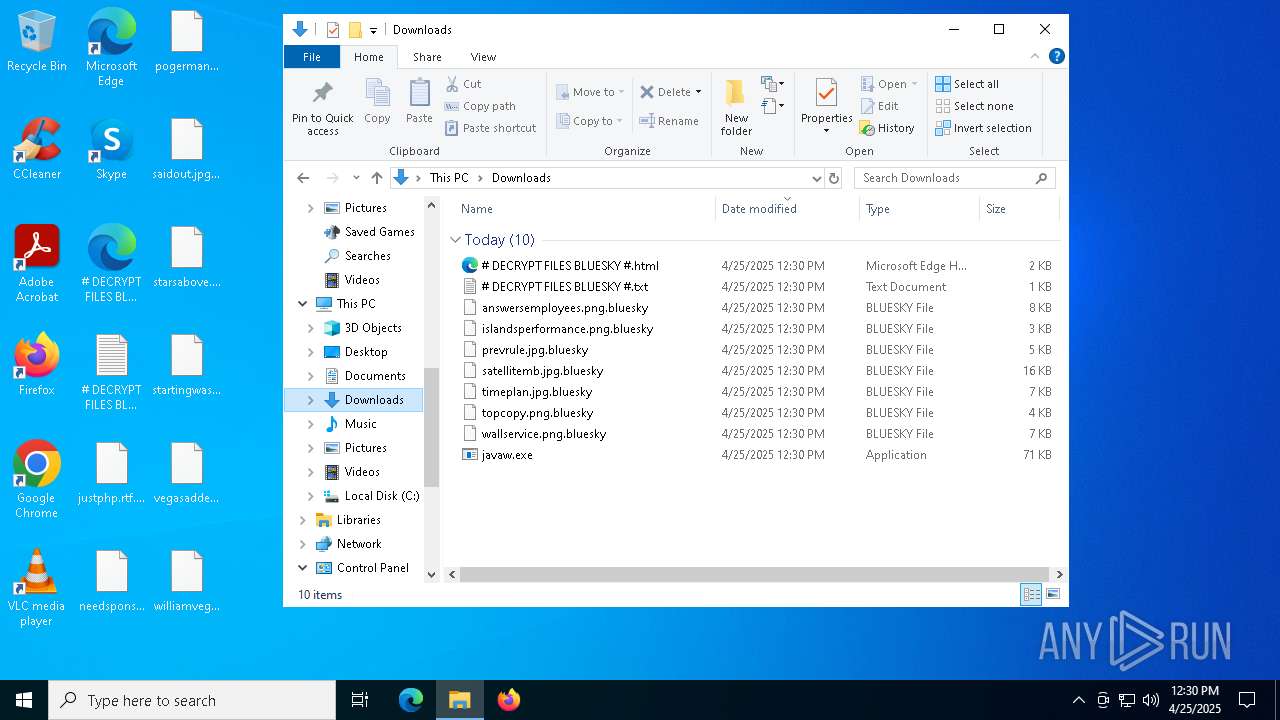
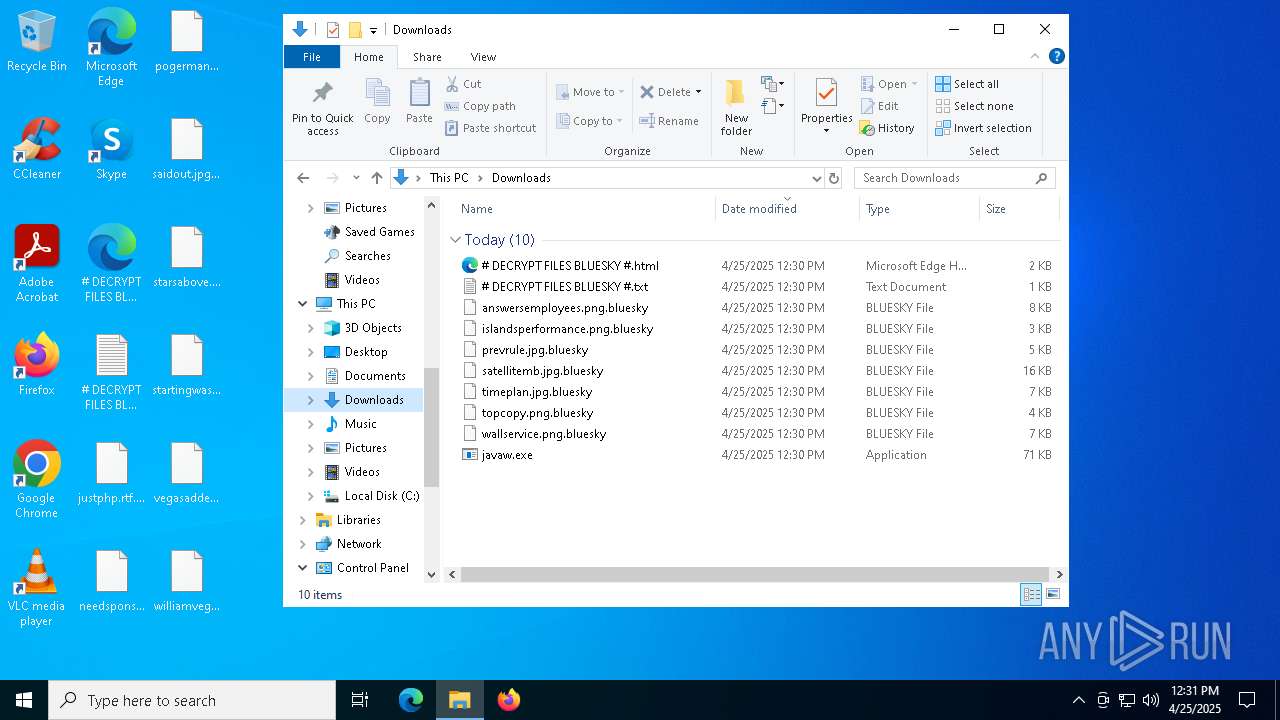
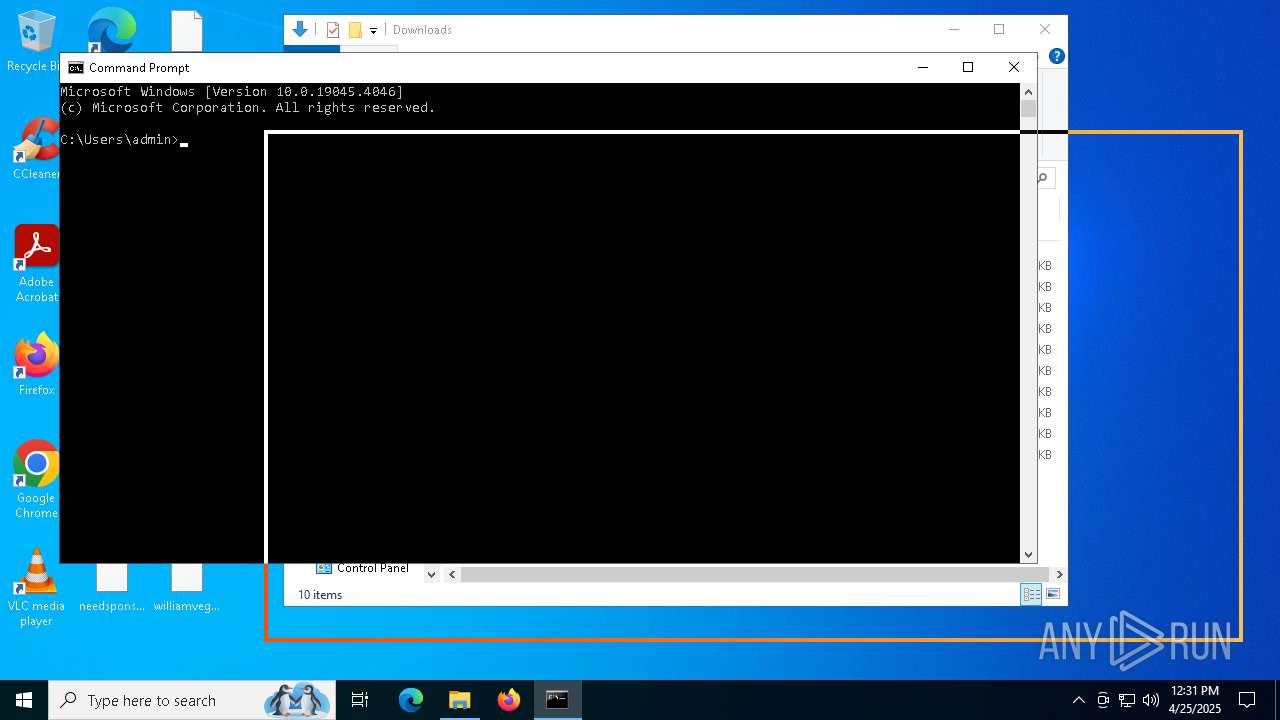
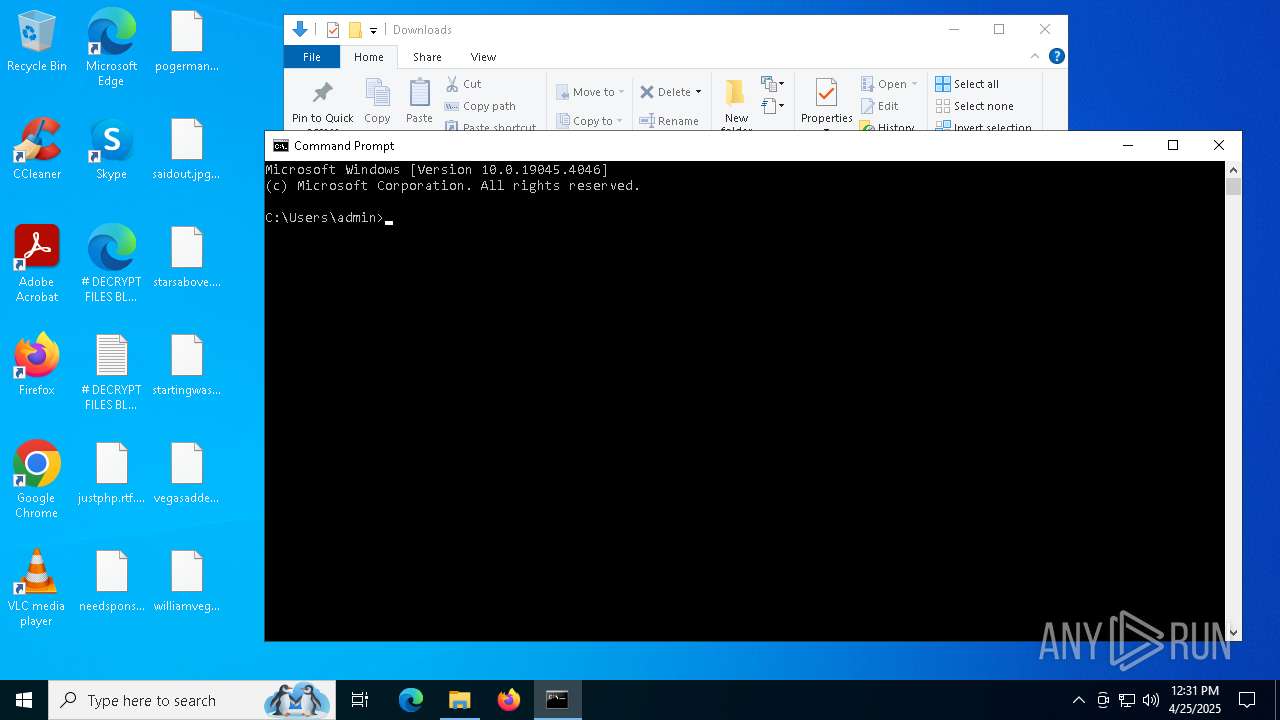
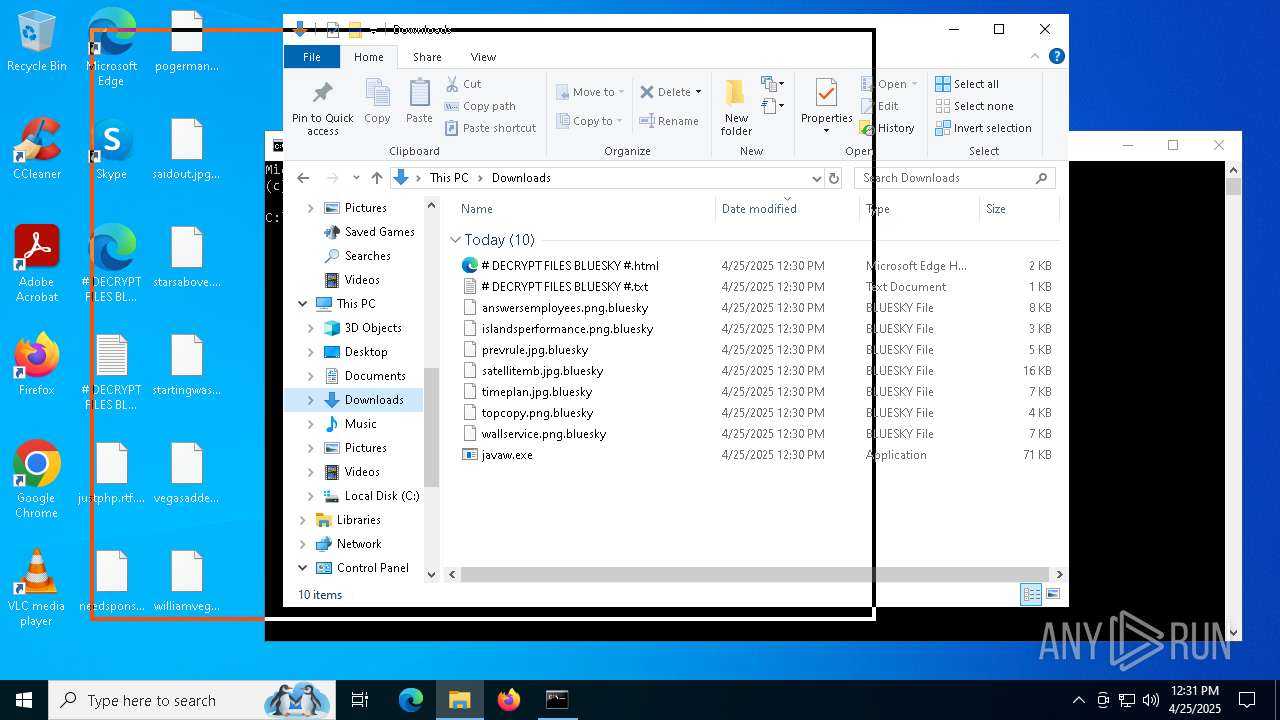
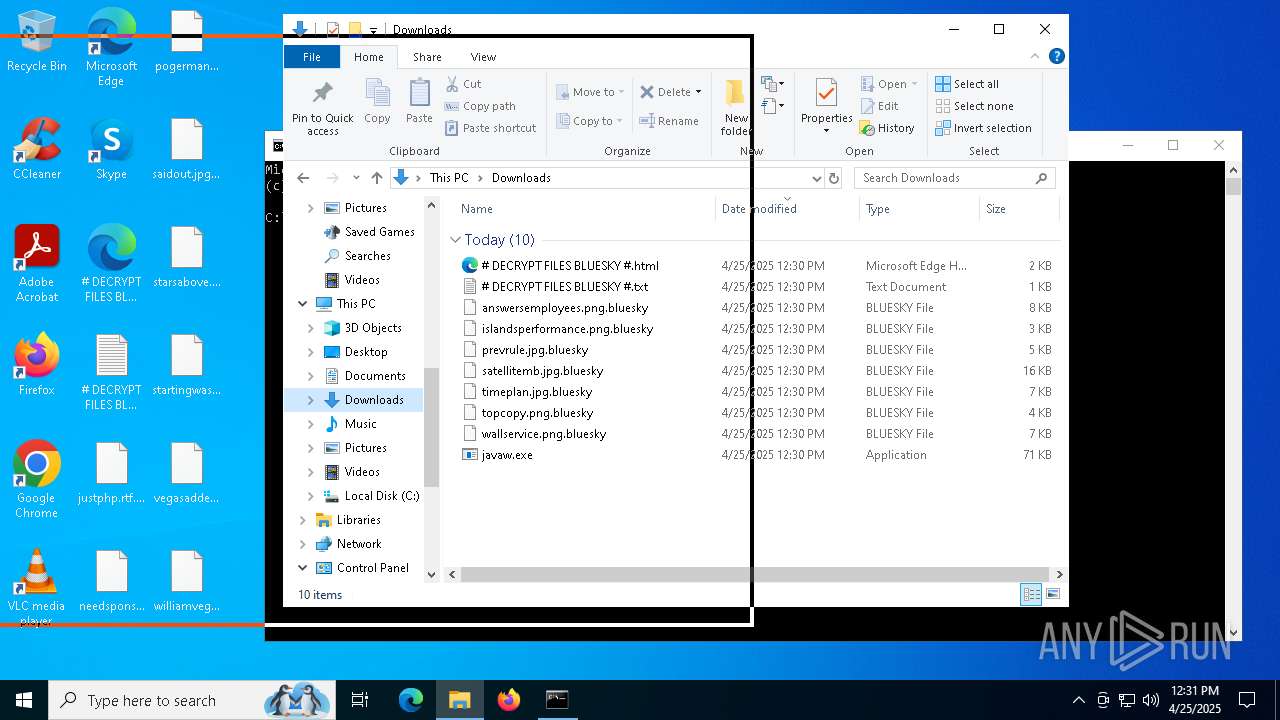
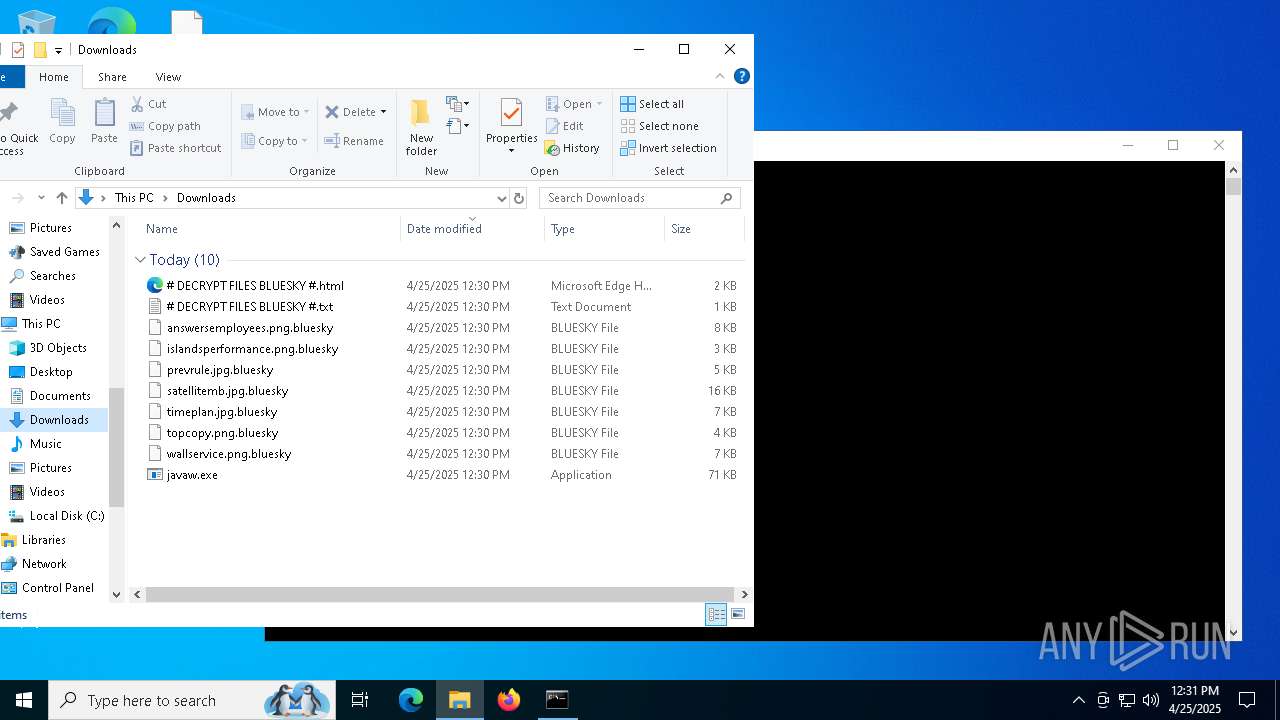
Bluesky note has been found
- javaw.exe (PID: 4300)
Renames files like ransomware
- javaw.exe (PID: 4300)
RANSOMWARE has been detected
- javaw.exe (PID: 4300)
SUSPICIOUS
Reads the date of Windows installation
- javaw.exe (PID: 4300)
INFO
Reads the machine GUID from the registry
- javaw.exe (PID: 4300)
Checks supported languages
- javaw.exe (PID: 4300)
Reads the computer name
- javaw.exe (PID: 4300)
Creates files or folders in the user directory
- javaw.exe (PID: 4300)
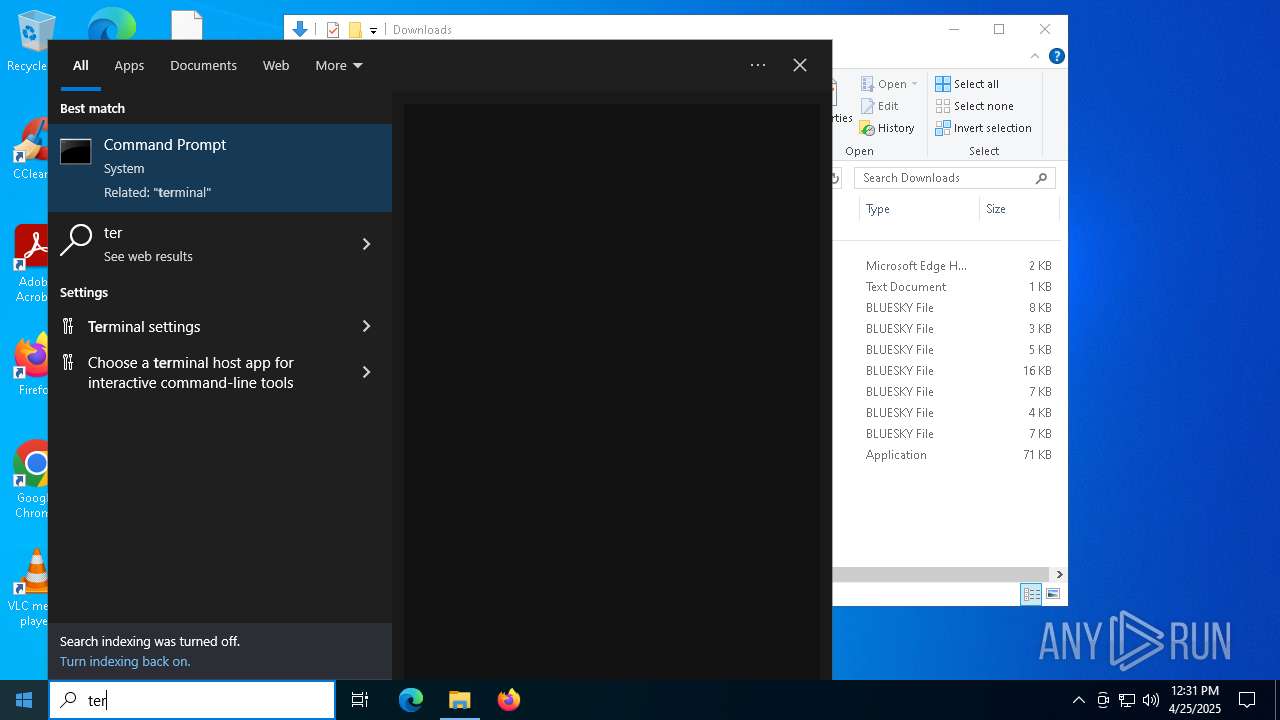
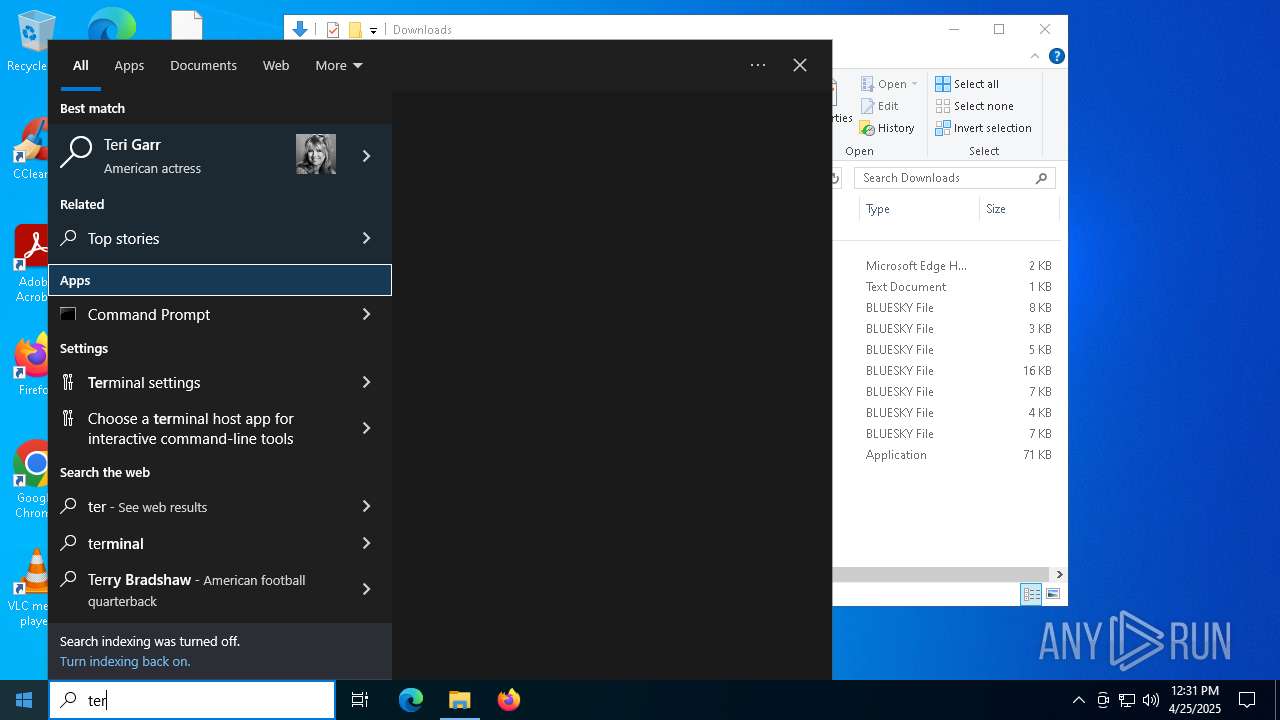
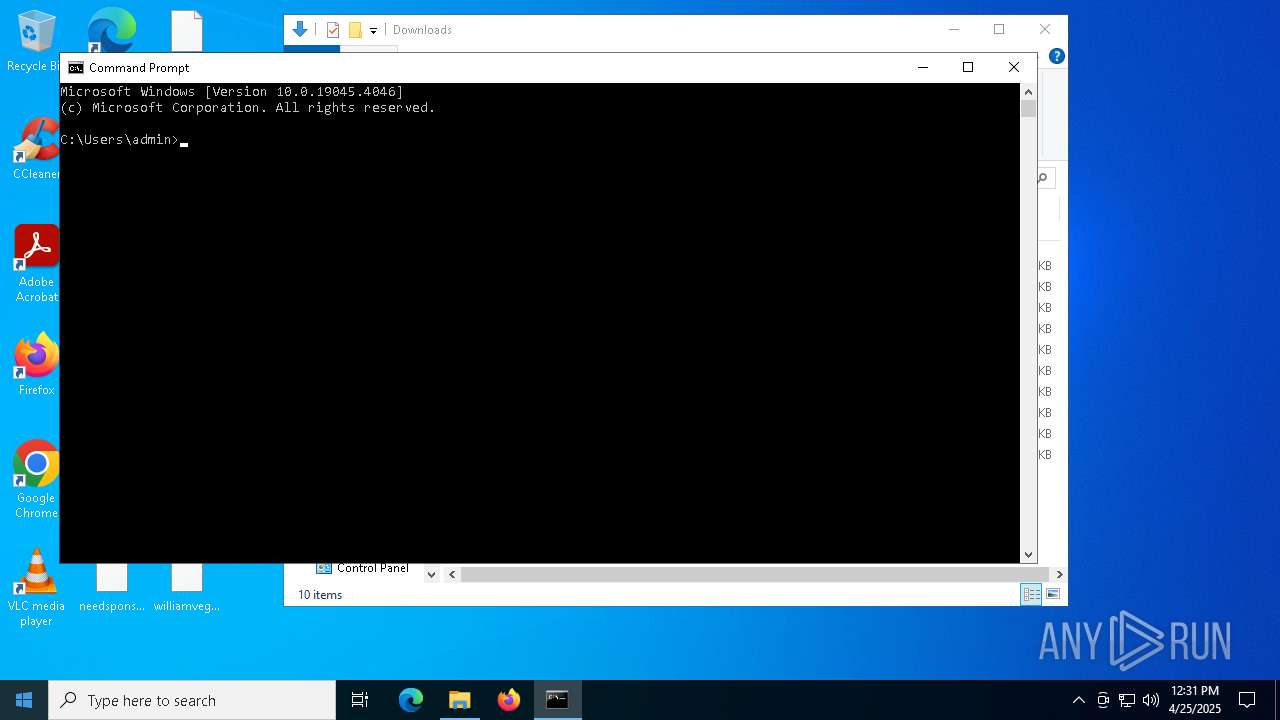
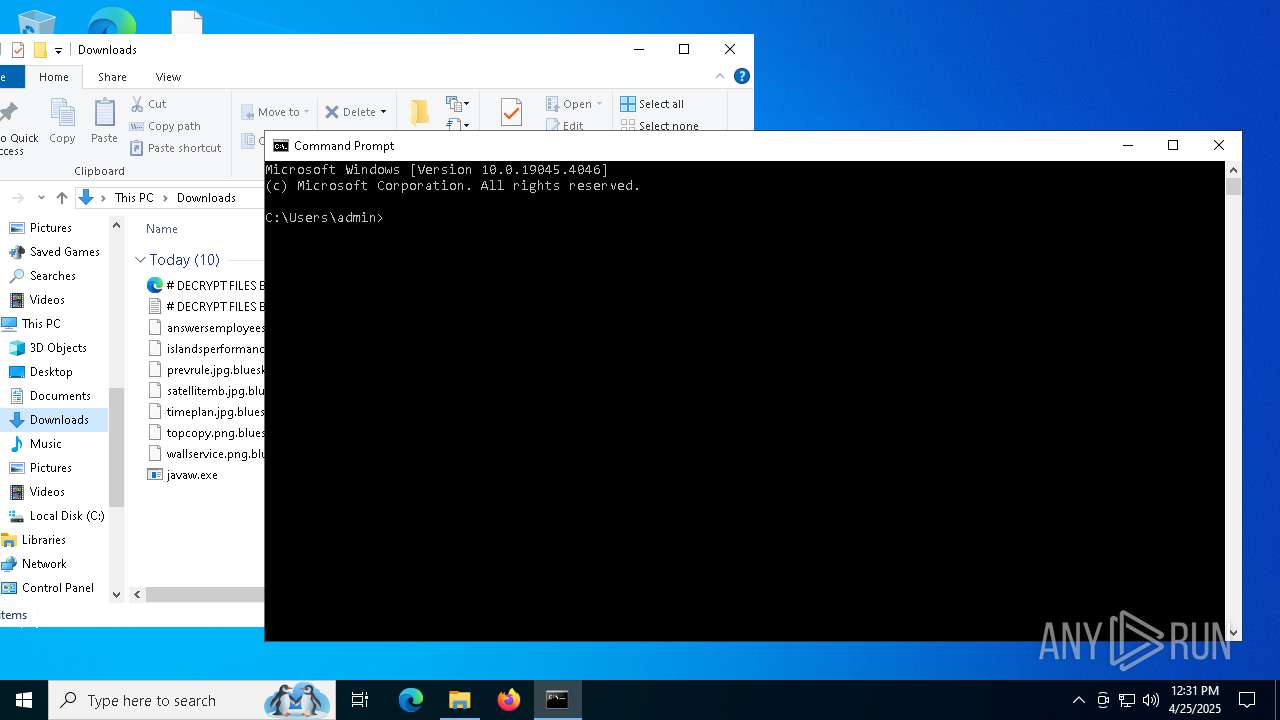
Manual execution by a user
- cmd.exe (PID: 5164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2085:02:07 16:05:31+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 94.8 |
| CodeSize: | 67584 |
| InitializedDataSize: | 7168 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xe880 |
| OSVersion: | 5.1 |
| ImageVersion: | 48623.16013 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
134
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1532 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4300 | "C:\Users\admin\Downloads\javaw.exe" | C:\Users\admin\Downloads\javaw.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5164 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5552 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6436 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
956
Read events
952
Write events
4
Delete events
0
Modification events
| (PID) Process: | (4300) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\EA408C6BF0D12F526F821798C3F54C9A |
| Operation: | write | Name: | RECOVERYBLOB |
Value: E265B72D33C587D024A8067D625D44B4AEDA8DA0AC680E08E10A342A5CB4A7983B1A2079A0D50ED5116FA91E00B3AEFEC2054A4210A0AD83DF28AEDDD70F0D106EC2285E78FD348A27BBC13C6201A353D0CFDB50F667283C1233AAD4CA372B7A6B52BB60768B51610D92B8AE0ECF3150490B3B31AA76C047 | |||
| (PID) Process: | (4300) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\EA408C6BF0D12F526F821798C3F54C9A |
| Operation: | write | Name: | x25519_public |
Value: 88791AFE72DB94897242B16F9E5E68043DD773AEAF7B5CE9F18488FDCC80C444 | |||
| (PID) Process: | (4300) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\EA408C6BF0D12F526F821798C3F54C9A |
| Operation: | write | Name: | completed |
Value: 0 | |||
| (PID) Process: | (4300) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\EA408C6BF0D12F526F821798C3F54C9A |
| Operation: | write | Name: | completed |
Value: 1 | |||
Executable files
0
Suspicious files
78
Text files
110
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4300 | javaw.exe | C:\Users\admin\AppData\Local\VirtualStore\# DECRYPT FILES BLUESKY #.html | html | |
MD5:F48FCDF1974ABB5361BF32CF6A3B4475 | SHA256:DF2E8BBAB9B38187D1CEF2C34212609A2A3E87C37B95EE7461992EF53F22431D | |||
| 4300 | javaw.exe | C:\Users\admin\# DECRYPT FILES BLUESKY #.html | html | |
MD5:F48FCDF1974ABB5361BF32CF6A3B4475 | SHA256:DF2E8BBAB9B38187D1CEF2C34212609A2A3E87C37B95EE7461992EF53F22431D | |||
| 4300 | javaw.exe | C:\Users\admin\3D Objects\# DECRYPT FILES BLUESKY #.html | html | |
MD5:F48FCDF1974ABB5361BF32CF6A3B4475 | SHA256:DF2E8BBAB9B38187D1CEF2C34212609A2A3E87C37B95EE7461992EF53F22431D | |||
| 4300 | javaw.exe | C:\Users\admin\Desktop\# DECRYPT FILES BLUESKY #.txt | text | |
MD5:06C7B698AD70D0BB7EE5AD6C000D563D | SHA256:A3FB95011DCDA59C945A6EB7A3771E1DB632219A4C53C75E88E852504C6441E4 | |||
| 4300 | javaw.exe | C:\Users\admin\Desktop\justphp.rtf | binary | |
MD5:001EEA7F9FDA8361A011FDC57707D6AE | SHA256:0F72410C2B8776CCAEBF849D551996C389E1995A7758363505A89D343AB460F4 | |||
| 4300 | javaw.exe | C:\Users\admin\Contacts\# DECRYPT FILES BLUESKY #.html | html | |
MD5:F48FCDF1974ABB5361BF32CF6A3B4475 | SHA256:DF2E8BBAB9B38187D1CEF2C34212609A2A3E87C37B95EE7461992EF53F22431D | |||
| 4300 | javaw.exe | C:\Users\admin\Desktop\justphp.rtf.bluesky | binary | |
MD5:001EEA7F9FDA8361A011FDC57707D6AE | SHA256:0F72410C2B8776CCAEBF849D551996C389E1995A7758363505A89D343AB460F4 | |||
| 4300 | javaw.exe | C:\Users\admin\# DECRYPT FILES BLUESKY #.txt | text | |
MD5:06C7B698AD70D0BB7EE5AD6C000D563D | SHA256:A3FB95011DCDA59C945A6EB7A3771E1DB632219A4C53C75E88E852504C6441E4 | |||
| 4300 | javaw.exe | C:\Users\admin\.ms-ad\# DECRYPT FILES BLUESKY #.html | html | |
MD5:F48FCDF1974ABB5361BF32CF6A3B4475 | SHA256:DF2E8BBAB9B38187D1CEF2C34212609A2A3E87C37B95EE7461992EF53F22431D | |||
| 4300 | javaw.exe | C:\Users\admin\Desktop\pogermany.rtf.bluesky | binary | |
MD5:07AA6B870A2D3146BA71710D8B65AB49 | SHA256:11C45E9E0F8593D077562DF1540661C82DC9EF3B9B74555C4223F53395FBBCF4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
50
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.51.224:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.51.224:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.189.232:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.189.232:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4268 | SIHClient.exe | GET | 200 | 2.16.189.232:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4268 | SIHClient.exe | GET | 200 | 2.16.189.232:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 2.19.51.224:80 | crl.microsoft.com | Akamai International B.V. | GR | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.51.224:80 | crl.microsoft.com | Akamai International B.V. | GR | whitelisted |
— | — | 2.16.189.232:80 | www.microsoft.com | Akamai International B.V. | BR | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.189.232:80 | www.microsoft.com | Akamai International B.V. | BR | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |