| File name: | 1.exe |
| Full analysis: | https://app.any.run/tasks/e3e4b168-e439-47bd-8da0-4b4d48a39d24 |
| Verdict: | Malicious activity |
| Threats: | A backdoor is a type of cybersecurity threat that allows attackers to secretly compromise a system and conduct malicious activities, such as stealing data and modifying files. Backdoors can be difficult to detect, as they often use legitimate system applications to evade defense mechanisms. Threat actors often utilize special malware, such as PlugX, to establish backdoors on target devices. |
| Analysis date: | July 07, 2024, 10:28:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | BB2B1CD32CFA51137D5EDE0892F76223 |
| SHA1: | 1E31B1BD8D72677498F9C4800C5321FA0C1D3B5D |
| SHA256: | 3DC6414F1C8447A3A73A713D660BC7B7AB809A54FD4A1B7543C874B81D2AEA74 |
| SSDEEP: | 6144:aB1QWXQkN7z2NAH06pGkYnQFV10CU4/KqfC6cvvs6Ksd3Ha/NjUYyl5El9iqGuRU:Q1QWgkrgkYnAEqa60KsSNM6l9iog |
MALICIOUS
Drops the executable file immediately after the start
- 1.exe (PID: 1204)
Connects to the CnC server
- office.exe (PID: 6580)
PURPLEFOX has been detected (SURICATA)
- office.exe (PID: 6580)
GH0ST has been detected (SURICATA)
- office.exe (PID: 6580)
Changes the autorun value in the registry
- A.exe (PID: 5872)
SUSPICIOUS
Process requests binary or script from the Internet
- 1.exe (PID: 1204)
Potential Corporate Privacy Violation
- 1.exe (PID: 1204)
Executable content was dropped or overwritten
- 1.exe (PID: 1204)
Connects to unusual port
- 1.exe (PID: 1204)
- office.exe (PID: 6580)
Creates file in the systems drive root
- explorer.exe (PID: 6632)
Likely accesses (executes) a file from the Public directory
- A.exe (PID: 5872)
- explorer.exe (PID: 6600)
- Remover.exe (PID: 6552)
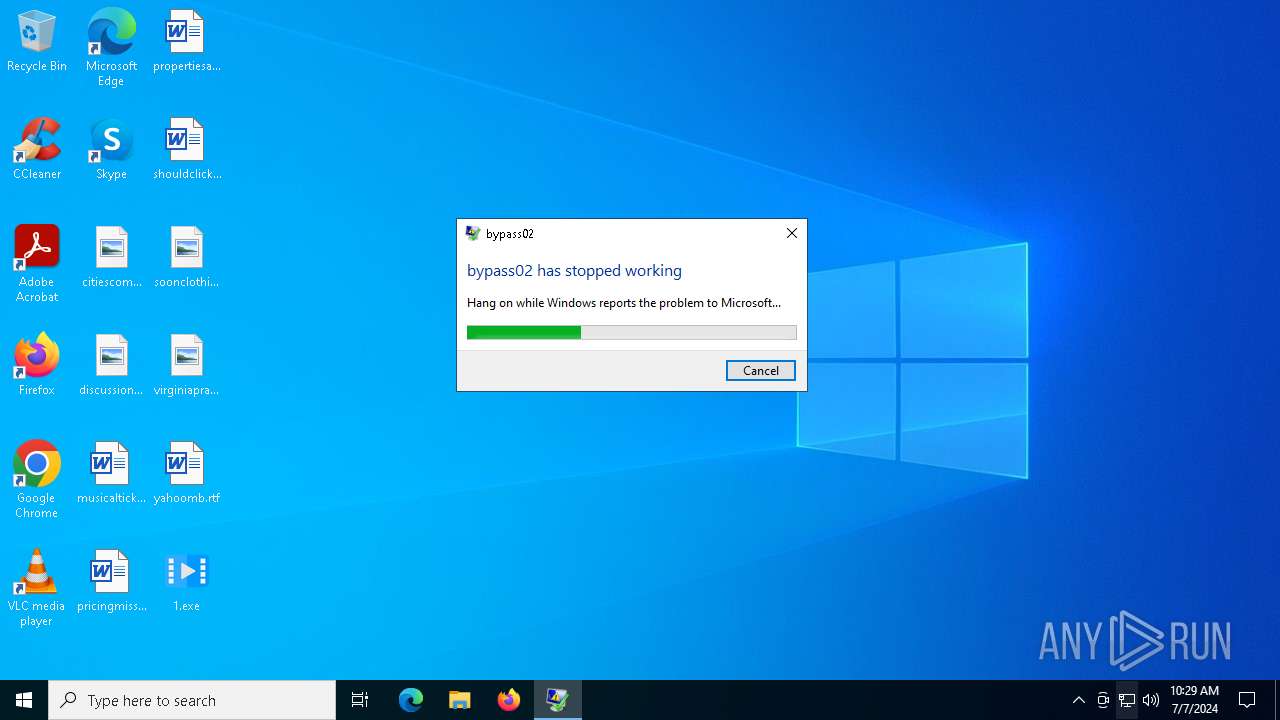
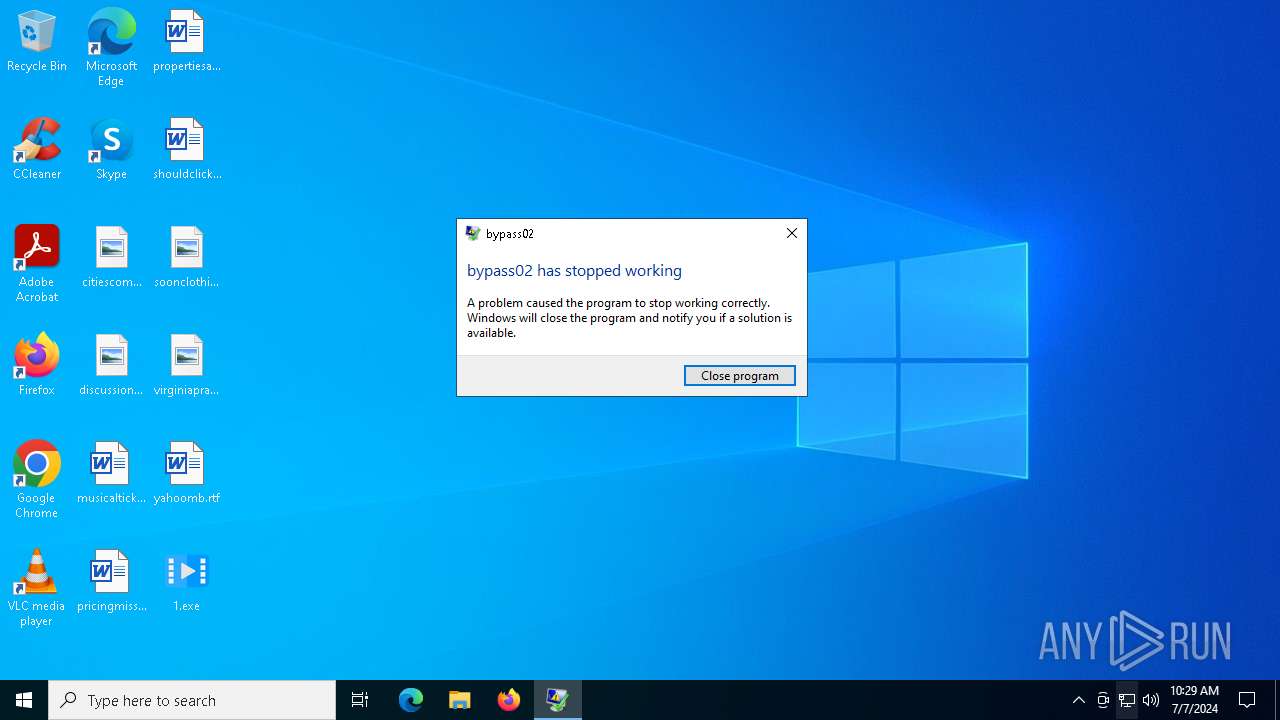
Executes application which crashes
- Remover.exe (PID: 6552)
The process verifies whether the antivirus software is installed
- A.exe (PID: 5872)
Contacting a server suspected of hosting an CnC
- office.exe (PID: 6580)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 6632)
Checks supported languages
- 1.exe (PID: 1204)
- Remover.exe (PID: 6552)
- office.exe (PID: 6580)
- A.exe (PID: 5872)
Reads the computer name
- A.exe (PID: 5872)
- office.exe (PID: 6580)
Checks proxy server information
- WerFault.exe (PID: 652)
Reads the software policy settings
- WerFault.exe (PID: 652)
Reads CPU info
- office.exe (PID: 6580)
Creates files or folders in the user directory
- WerFault.exe (PID: 652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:06:20 11:50:59+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 299520 |
| InitializedDataSize: | 108032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x208f0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
153
Monitored processes
10
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 652 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6552 -s 624 | C:\Windows\SysWOW64\WerFault.exe | Remover.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1204 | "C:\Users\admin\Desktop\1.exe" | C:\Users\admin\Desktop\1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4148 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5872 | "C:\Users\Public\serupdate\A.exe" | C:\Users\Public\serupdate\A.exe | explorer.exe | ||||||||||||
User: admin Company: G DATA Software AG Integrity Level: MEDIUM Description: G DATA AntiSpam UI Exit code: 243974658 Version: 25.1.24025.1146 Modules
| |||||||||||||||
| 6180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | office.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6552 | C:\Users\Public\serupdate\Remover.exe | C:\Users\Public\serupdate\Remover.exe | 1.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: bypass02 Exit code: 3221225477 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 6580 | office.exe | C:\Users\Public\serupdate\office.exe | A.exe | ||||||||||||
User: admin Company: 网易灵犀 Integrity Level: MEDIUM Description: 网易灵犀办公 Version: 1.40.2 Modules
| |||||||||||||||
| 6600 | explorer.exe C:\Users\Public\serupdate | C:\Windows\SysWOW64\explorer.exe | — | Remover.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6632 | C:\WINDOWS\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7104 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 806
Read events
16 759
Write events
45
Delete events
2
Modification events
| (PID) Process: | (6632) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (6632) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000E00000003000000000000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (6632) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (6632) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Ribbon |
| Operation: | write | Name: | MinimizedStateTabletModeOff |
Value: 0 | |||
| (PID) Process: | (6632) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Ribbon |
| Operation: | write | Name: | QatItems |
Value: 3C7369713A637573746F6D554920786D6C6E733A7369713D22687474703A2F2F736368656D61732E6D6963726F736F66742E636F6D2F77696E646F77732F323030392F726962626F6E2F716174223E3C7369713A726962626F6E206D696E696D697A65643D2266616C7365223E3C7369713A71617420706F736974696F6E3D2230223E3C7369713A736861726564436F6E74726F6C733E3C7369713A636F6E74726F6C206964513D227369713A3136313238222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3136313239222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333532222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333834222076697369626C653D22747275652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333336222076697369626C653D22747275652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333537222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C2F7369713A736861726564436F6E74726F6C733E3C2F7369713A7161743E3C2F7369713A726962626F6E3E3C2F7369713A637573746F6D55493E | |||
| (PID) Process: | (6632) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar\ShellBrowser |
| Operation: | write | Name: | ITBar7Layout |
Value: 13000000000000000000000020000000100000000000000001000000010700005E01000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6632) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\0\4 |
| Operation: | write | Name: | 1 |
Value: 7C00310000000000E7589A5311005075626C69630000660009000400EFBE874FDB49E758A0532E0000005AC700000000030000000000000000003C0000000000614B08015000750062006C0069006300000040007300680065006C006C00330032002E0064006C006C002C002D0032003100380031003600000016000000 | |||
| (PID) Process: | (6632) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\0\4\1 |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (6632) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\0\4 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
| (PID) Process: | (6632) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\0\4\1 |
| Operation: | write | Name: | 0 |
Value: 5C00310000000000E758A05310005345525550447E310000440009000400EFBEE7589A53E758A0532E0000009A5F05000000070000000000000000000000000000007761E700730065007200750070006400610074006500000018000000 | |||
Executable files
4
Suspicious files
6
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 652 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_Remover.exe_70db5ed651cac3d44cd3c0bcfdd88c8cb26b26_3aff6587_0b97031e-c7a8-49ac-927b-e71d2b5db316\Report.wer | — | |
MD5:— | SHA256:— | |||
| 652 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | der | |
MD5:979F91388D4DF2F2D68497400C9830DD | SHA256:A9F27E26AA818BC97449D30D5707254EDCA571D21D36B4576C7CD9A56FB18BC5 | |||
| 652 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | der | |
MD5:CBA2426F2AAFE31899569ACE05E89796 | SHA256:A465FEBE8A024E3CDB548A3731B2EA60C7B2919E941A24B9A42890B2B039B85A | |||
| 1204 | 1.exe | C:\Users\Public\serupdate\A.exe | executable | |
MD5:90372D5D20E02DBACEA89C48DDD1F200 | SHA256:FC66BB6617584CC8EACBCEA1CC4D2DFA4890B89F5AFB643B21647EFE7F516B39 | |||
| 652 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER522A.tmp.dmp | dmp | |
MD5:8B84213FCD825ADA6A5FD50B8CDDDFEB | SHA256:2ED46DEC3844F5E29C51E14D12321A675FEBD6DFE4181EBACF61FC0157CBBF20 | |||
| 652 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\Remover.exe.6552.dmp | binary | |
MD5:ABFB9B81720BBCE1545FA18133BEFFE1 | SHA256:760DC8D76C9954818DF3330F646FEB1822FD8C4B76A07C3AF54D8E5793841C45 | |||
| 1204 | 1.exe | C:\Users\Public\serupdate\Remover.exe | executable | |
MD5:52037E4DA344B53FF60C42FA92918D3F | SHA256:B97B88DE39C5CFA9F568194682708AD521AE920AB26DD57986DC70F92CD9C9EE | |||
| 1204 | 1.exe | C:\Users\Public\serupdate\ask.dll | executable | |
MD5:544728F37DC9E4A605CF143748DB4BB1 | SHA256:4010B3F5DA5D7CE3DADEC745ACBAB6A49469CF17BC7E864CFE4400281F683838 | |||
| 652 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER5306.tmp.xml | xml | |
MD5:FE8B0C750F39934C96E513D540F260AC | SHA256:FA8A4B627E9FB3260ABA8B64B1F843B7F9B0E6E5473C222ACFCA09903924454D | |||
| 1204 | 1.exe | C:\Users\Public\serupdate\office.exe | executable | |
MD5:5DEE06E2307259C4628B8AE213C80492 | SHA256:ED746438D971E50835C87707945102A52E1FE763FCB576869E08807D425F9511 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
78
DNS requests
20
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2072 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
2072 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1204 | 1.exe | GET | 200 | 104.233.187.248:3000 | http://104.233.187.248:3000/Public/ask.dll | unknown | — | — | unknown |
1204 | 1.exe | GET | 200 | 104.233.187.248:3000 | http://104.233.187.248:3000/Public/Remover.exe | unknown | — | — | unknown |
1204 | 1.exe | GET | 200 | 104.233.187.248:3000 | http://104.233.187.248:3000/Public/A.exe | unknown | — | — | unknown |
3760 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
2032 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
1204 | 1.exe | GET | 200 | 104.233.187.248:3000 | http://104.233.187.248:3000/Public/office.exe | unknown | — | — | unknown |
2032 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2072 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1292 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
776 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2072 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2072 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
2072 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
1204 | 1.exe | 104.233.187.248:3000 | — | PEGTECHINC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1204 | 1.exe | A Network Trojan was detected | ET MALWARE Single char EXE direct download likely trojan (multiple families) |
1204 | 1.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1204 | 1.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
1204 | 1.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1204 | 1.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
1204 | 1.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host DLL Request |
1204 | 1.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1204 | 1.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1204 | 1.exe | Misc activity | ET INFO Packed Executable Download |
1204 | 1.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
10 ETPRO signatures available at the full report