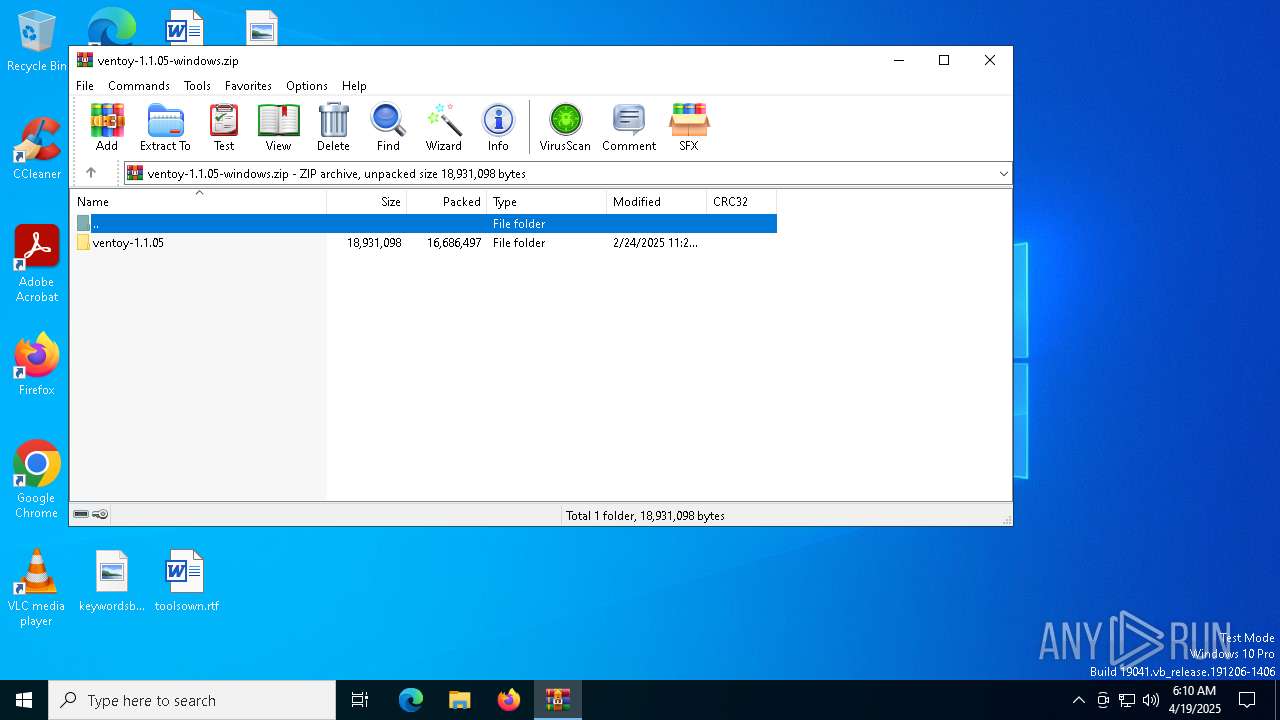
| File name: | ventoy-1.1.05-windows.zip |
| Full analysis: | https://app.any.run/tasks/cafbade9-fffa-4594-9959-cd1ffdfb6425 |
| Verdict: | Malicious activity |
| Threats: | A backdoor is a type of cybersecurity threat that allows attackers to secretly compromise a system and conduct malicious activities, such as stealing data and modifying files. Backdoors can be difficult to detect, as they often use legitimate system applications to evade defense mechanisms. Threat actors often utilize special malware, such as PlugX, to establish backdoors on target devices. |
| Analysis date: | April 19, 2025, 06:10:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 7B9C291D141A9895E285CCD8BB2A6889 |
| SHA1: | BE68F08CE7CC75D34656DB263B3F08EC024BFA4B |
| SHA256: | 3DC1F0A5209C6FA260AF9F08951BC4421127B56D4EFA3EDD2C979AF74B1941E5 |
| SSDEEP: | 98304:e4DVwnquTOk6TNWUCOgTwQB6+v0t2Da8jWHi+BOmWImIiT4Mdu+MaoQ6Fn2zfYVX:/qZ3BBQ6RLh/3q+hv5u/hr |
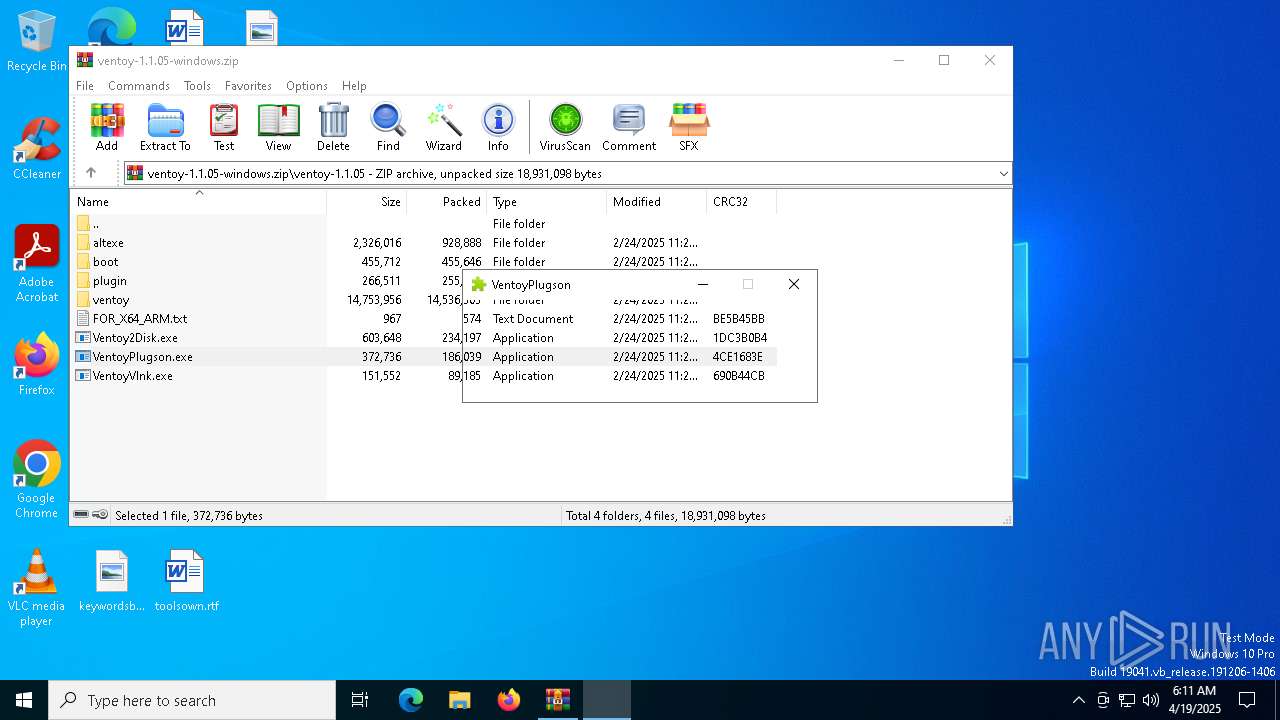
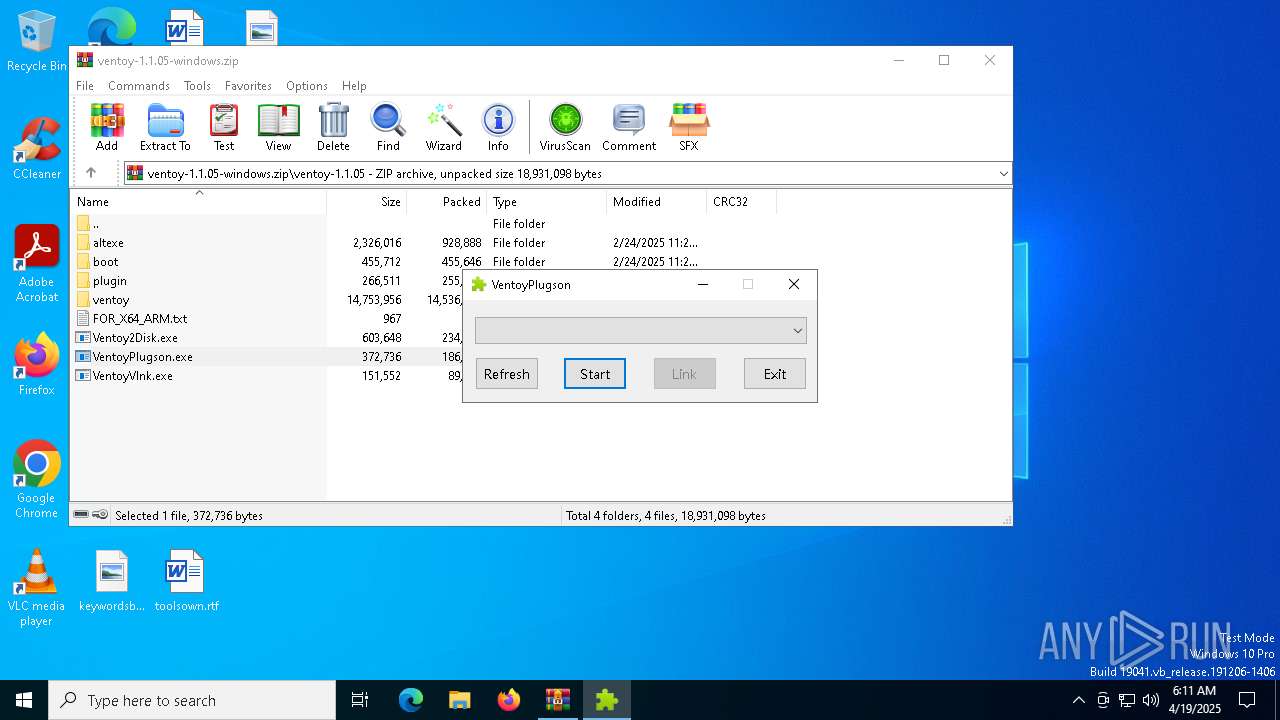
MALICIOUS
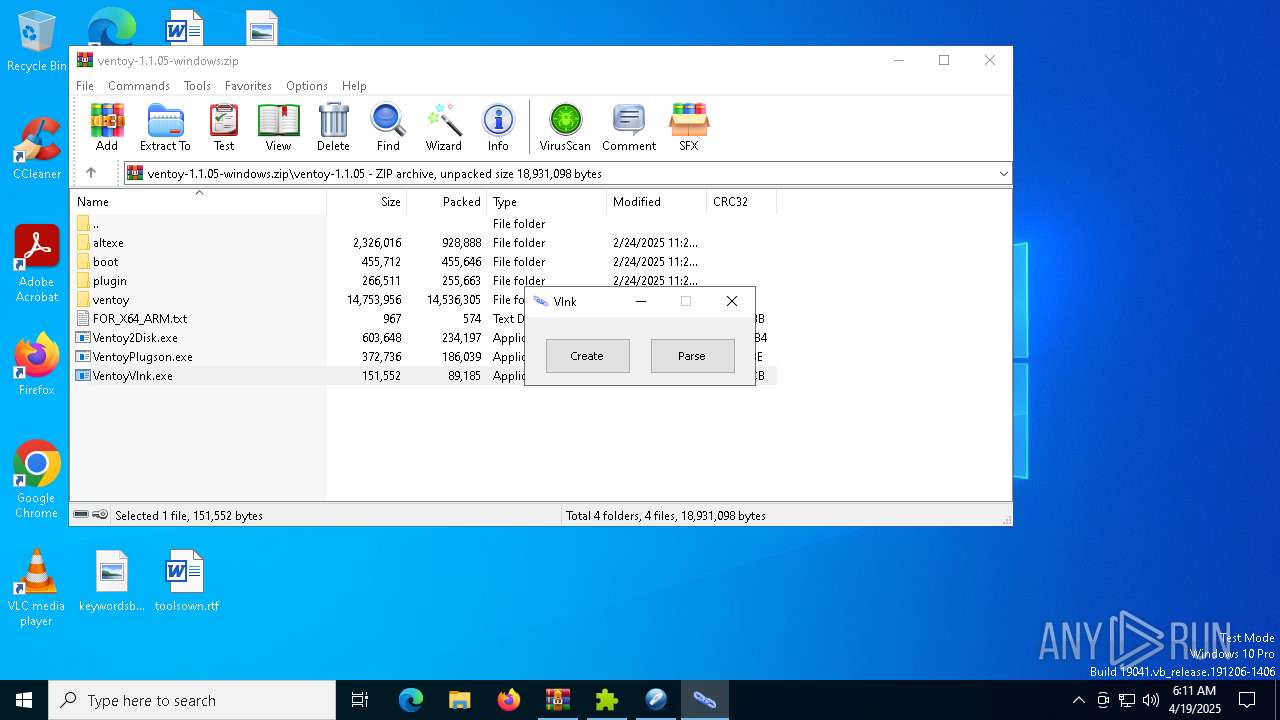
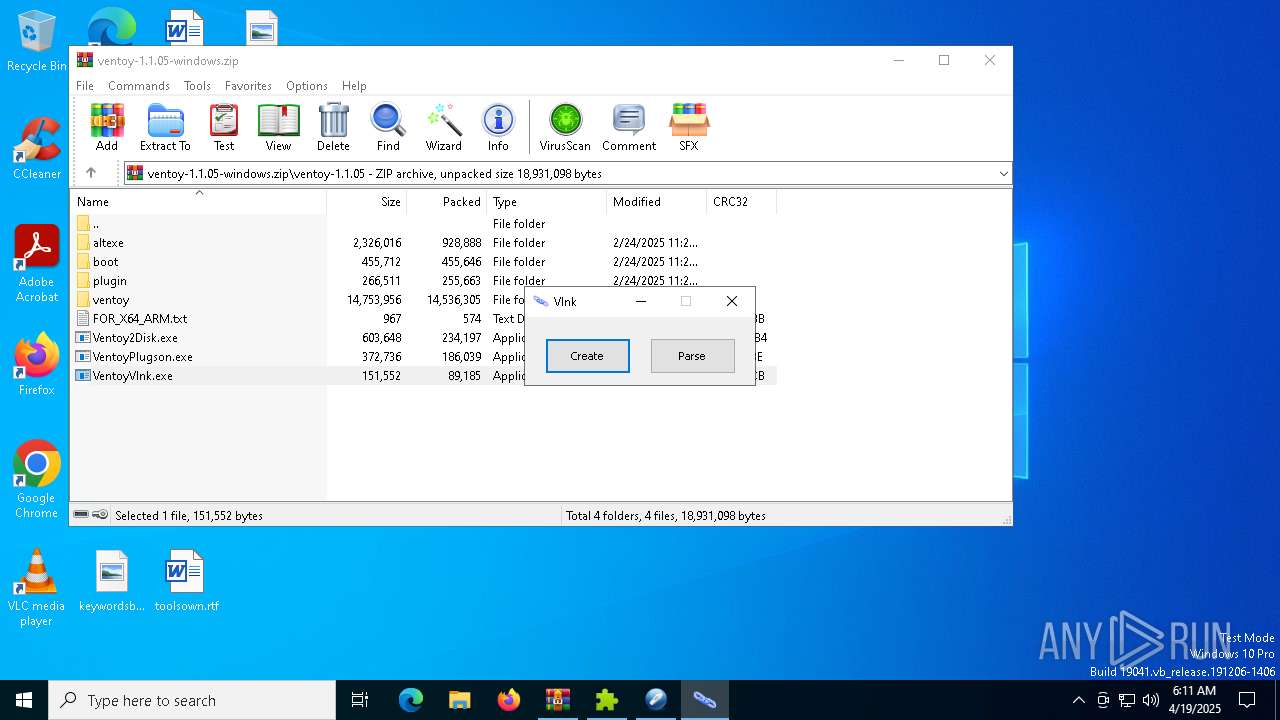
Generic archive extractor
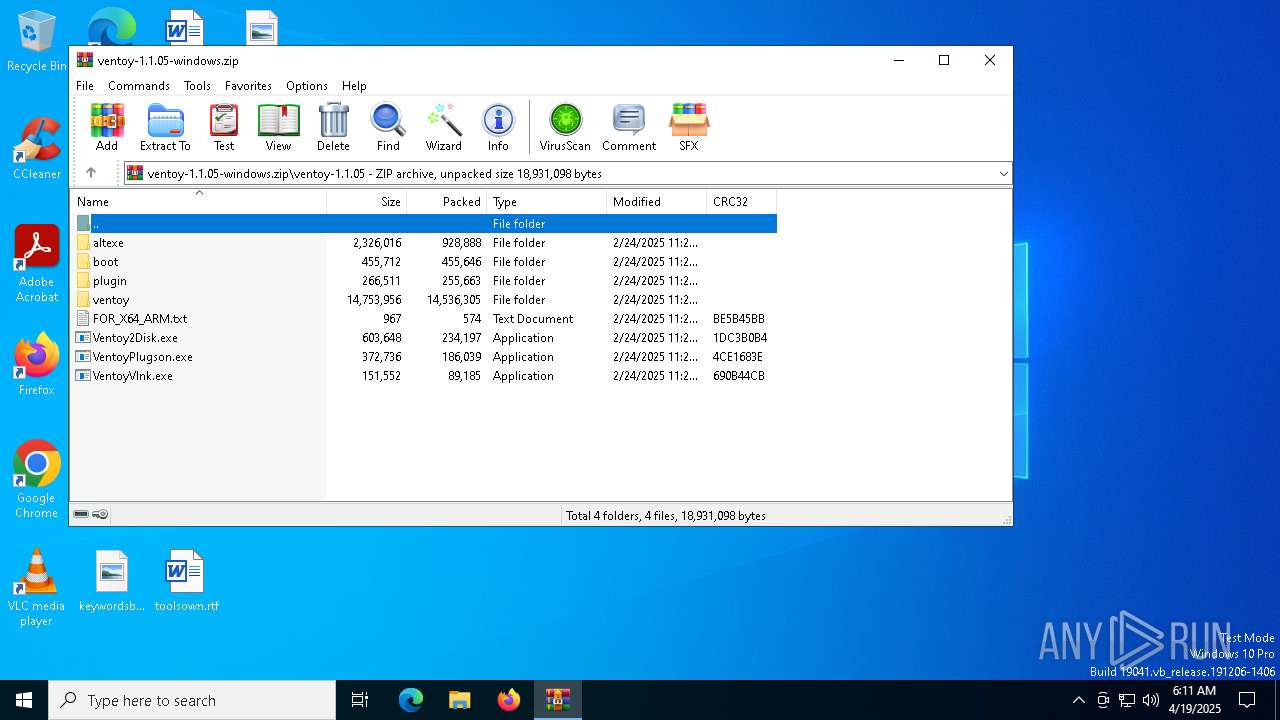
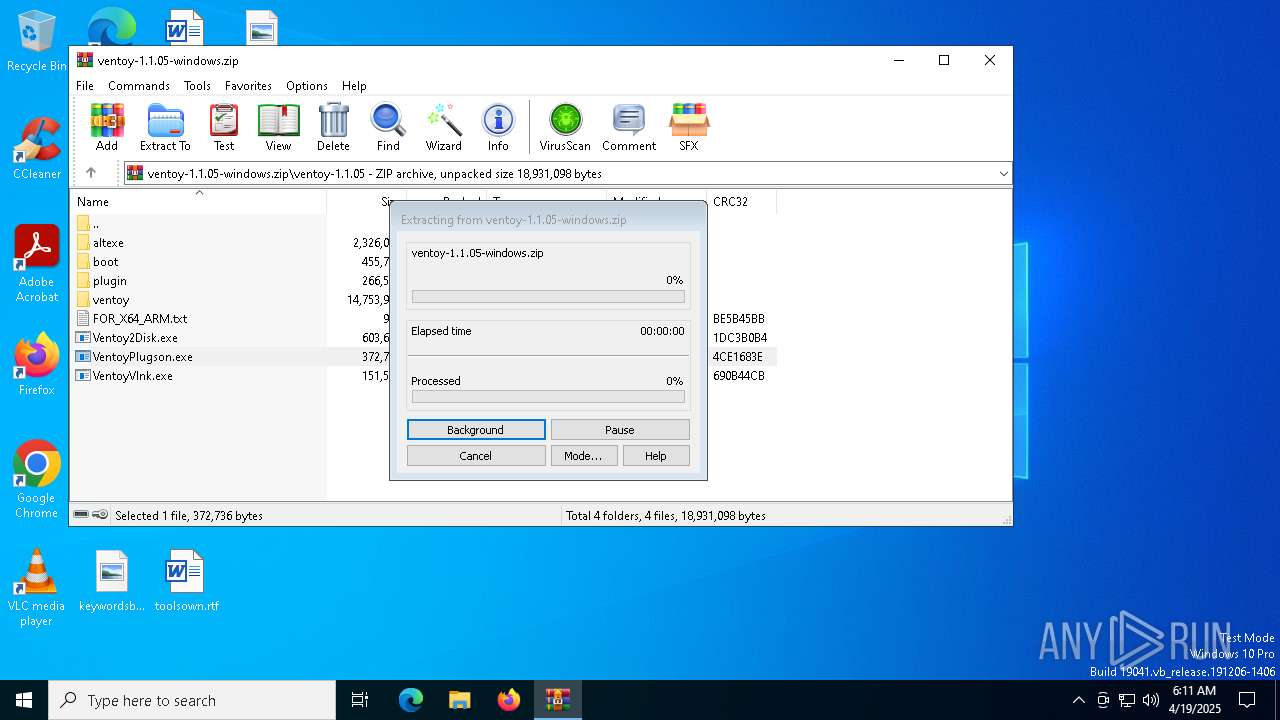
- WinRAR.exe (PID: 7308)
FLOXIF mutex has been found
- VentoyPlugson.exe (PID: 7832)
- VentoyVlnk.exe (PID: 8076)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7308)
- VentoyVlnk.exe (PID: 8076)
INFO
Reads the computer name
- Ventoy2Disk.exe (PID: 8004)
- VentoyVlnk.exe (PID: 8076)
- VentoyPlugson.exe (PID: 7832)
Checks supported languages
- VentoyPlugson.exe (PID: 7832)
- VentoyVlnk.exe (PID: 8076)
- Ventoy2Disk.exe (PID: 8004)
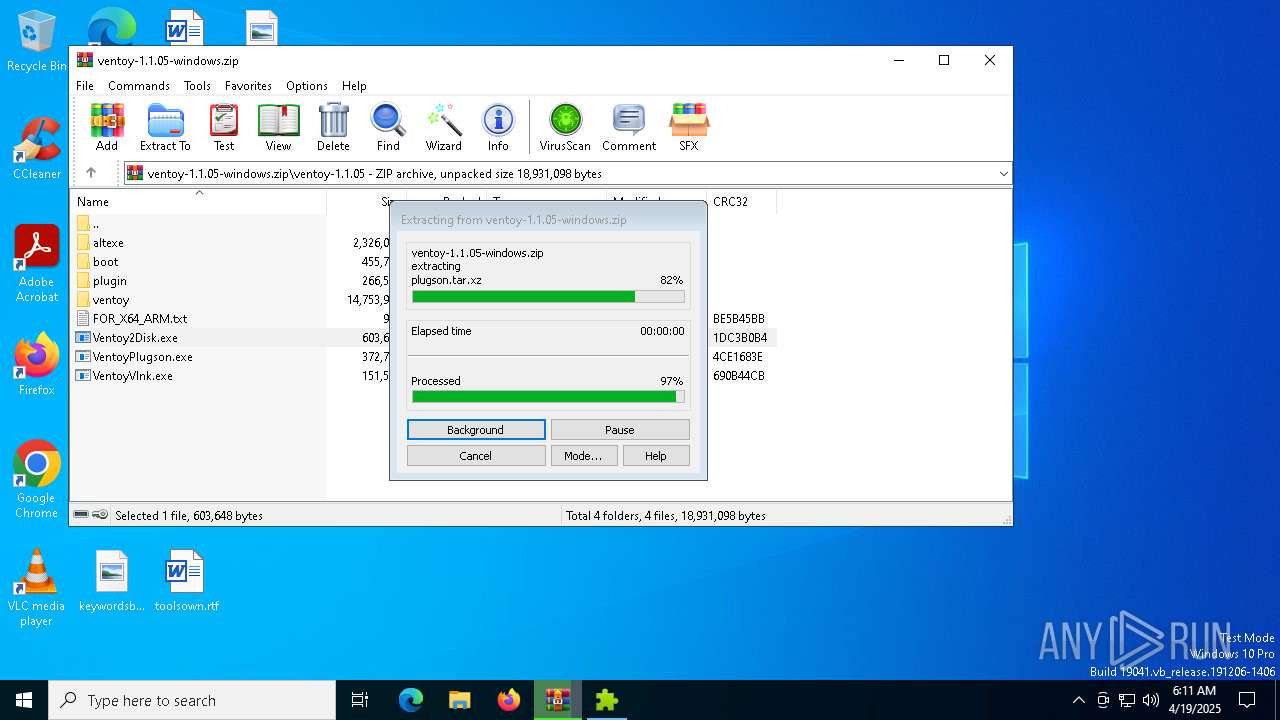
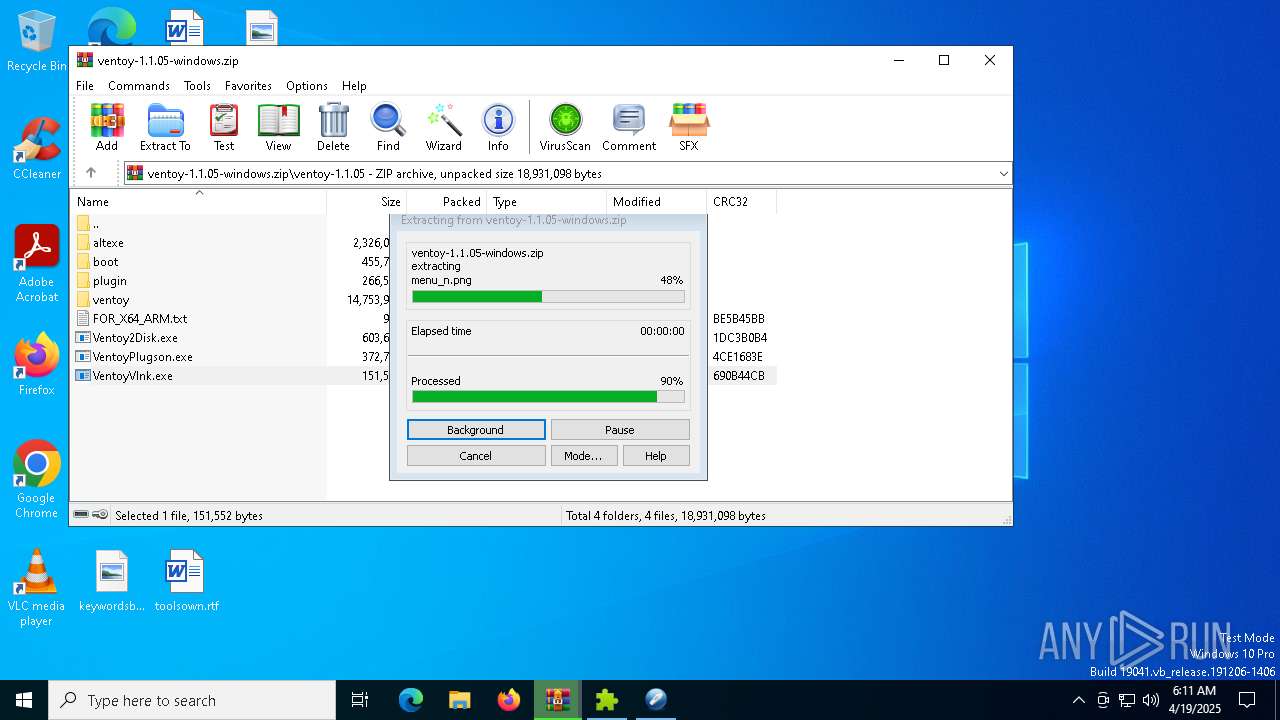
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7308)
Create files in a temporary directory
- Ventoy2Disk.exe (PID: 8004)
- VentoyPlugson.exe (PID: 7832)
- VentoyVlnk.exe (PID: 8076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:02:24 19:21:26 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | ventoy-1.1.05/ |
Total processes
138
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4776 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7308 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\ventoy-1.1.05-windows.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7756 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.37411\ventoy-1.1.05\VentoyPlugson.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.37411\ventoy-1.1.05\VentoyPlugson.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 7832 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.37411\ventoy-1.1.05\VentoyPlugson.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.37411\ventoy-1.1.05\VentoyPlugson.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
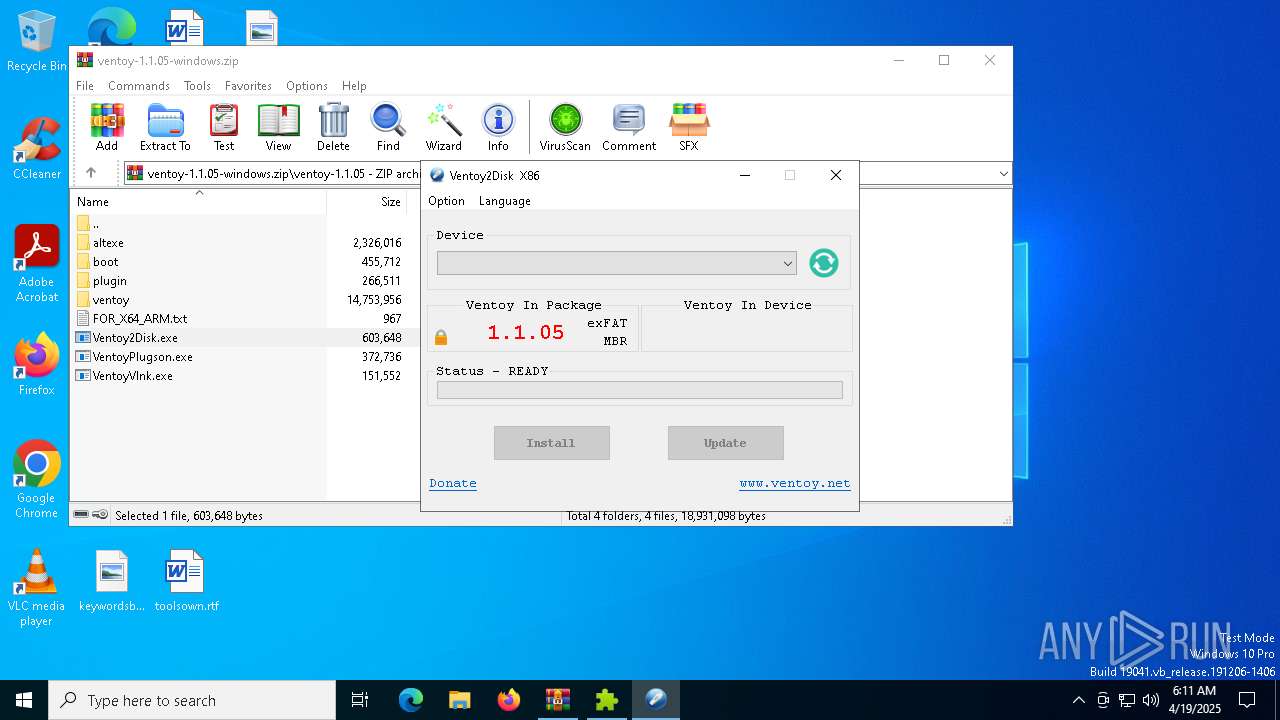
| 7956 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.38176\ventoy-1.1.05\Ventoy2Disk.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.38176\ventoy-1.1.05\Ventoy2Disk.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Ventoy2Disk Exit code: 3221226540 Version: 1.1.0.3 Modules
| |||||||||||||||
| 8004 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.38176\ventoy-1.1.05\Ventoy2Disk.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.38176\ventoy-1.1.05\Ventoy2Disk.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Ventoy2Disk Version: 1.1.0.3 Modules
| |||||||||||||||
| 8028 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.38662\ventoy-1.1.05\VentoyVlnk.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.38662\ventoy-1.1.05\VentoyVlnk.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 8076 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.38662\ventoy-1.1.05\VentoyVlnk.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.38662\ventoy-1.1.05\VentoyVlnk.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
5 292
Read events
5 251
Write events
40
Delete events
1
Modification events
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ventoy-1.1.05-windows.zip | |||
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8076) VentoyVlnk.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (8076) VentoyVlnk.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 04000000030000000E00000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
Executable files
24
Suspicious files
15
Text files
96
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.37411\ventoy-1.1.05\ventoy\ventoy.disk.img.xz | — | |
MD5:— | SHA256:— | |||
| 7308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.37411\ventoy-1.1.05\FOR_X64_ARM.txt | text | |
MD5:94998E1249F884640F91DBDF91FE45C9 | SHA256:906FE8433B8D6F392755954D25A1E2FFCAC4E9D7E7C02C147E695A9BF2649DD1 | |||
| 7308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.37411\ventoy-1.1.05\altexe\Ventoy2Disk_ARM.exe | executable | |
MD5:3EF7A218A214A3C082FD1EEC85607A26 | SHA256:3F06A5BE5F46425750E23094B8CEA59B3647A3A2065B7C038BBCB494BA69E064 | |||
| 7308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.37411\ventoy-1.1.05\altexe\Ventoy2Disk_ARM64.exe | executable | |
MD5:A04080599309CFA6D95543D184716C95 | SHA256:4D91F1BEF6A3A5C27640540EE8AC46F9DFBCF64D104665361383BF0276735454 | |||
| 7308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.37411\ventoy-1.1.05\altexe\VentoyPlugson_X64.exe | executable | |
MD5:B12066183B66C7238A5CDF916DCBF58E | SHA256:CC50E92DFACBBAB0D436C6F7C283C5CE7CAB0E4578F137D8306237BDD4FD5F25 | |||
| 7308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.37411\ventoy-1.1.05\altexe\Ventoy2Disk_X64.exe | executable | |
MD5:6767AAF12C74283D4DCD853F0CE2C4A4 | SHA256:1FDFFA92C3BF2C95F821B34A74F2D58F35E2C5DFCBC075E9287CE37B21CB9C8A | |||
| 7308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.37411\ventoy-1.1.05\VentoyPlugson.exe | executable | |
MD5:38F18EBB5B81B4481B732F68D2B9FE90 | SHA256:A27BEF270ABB8E0649358D89A004573B45156C7A2BB520FB62CFE1F50300145B | |||
| 7308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.37411\ventoy-1.1.05\boot\core.img.xz | binary | |
MD5:30C17978EA9A85751287B1452D93E84F | SHA256:0EEB0E0AF219722714FAF2011F62F89F1829EDC4B8E005E2D15707A89DF11F96 | |||
| 7308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.37411\ventoy-1.1.05\ventoy\languages.json | text | |
MD5:50B0C382465A4454AEC97CB28D2300A3 | SHA256:23864542277AE383290BA34D7D2070D72951B8C14B4DB2D3BAE60BF00BB2FD77 | |||
| 7308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7308.37411\ventoy-1.1.05\plugin\ventoy\theme\icons\vtoyiso.png | image | |
MD5:A59484CD7AC471F710C1516DBDE0A069 | SHA256:963F1B227C86E7B544DF9409C6CDE34F4B9341DDD526F3B9367AF29D03D022E8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
19
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7716 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7716 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7716 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |