| File name: | random.exe |
| Full analysis: | https://app.any.run/tasks/e8ba9112-7fe1-4176-8469-e70a83b05f62 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 17, 2025, 21:35:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 88570E726B985EBED8C69E14A9084834 |
| SHA1: | D7C04E725F4F6733D3CA892D98592828A3E96D1B |
| SHA256: | 3DAE3A00989EA5126D0B77288CA376D9E530CF88085BE83A0C14C0C3083969C9 |
| SSDEEP: | 49152:wPPkzemqoSut3Jh4+QQ/btosJwIA4hHmZlKH2Tw/Pq83zw0bCjvk9G661QGtBBXo:yP/mp7t3T4+B/btosJwIA4hHmZlKH2TJ |
MALICIOUS
Script downloads file (POWERSHELL)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 5008)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 5176)
- cmd.exe (PID: 5740)
- cmd.exe (PID: 4000)
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 5968)
- powershell.exe (PID: 5008)
- powershell.exe (PID: 4016)
- powershell.exe (PID: 8728)
AMADEY mutex has been found
- TempYDNCOH9PUEQPRYSD7ETYY3PGCB4UVZNE.EXE (PID: 2392)
- ramez.exe (PID: 7152)
- TempYDNCOH9PUEQPRYSD7ETYY3PGCB4UVZNE.EXE (PID: 6392)
- amnew.exe (PID: 1164)
- saren.exe (PID: 4812)
- saren.exe (PID: 5504)
- ramez.exe (PID: 1228)
Run PowerShell with an invisible window
- powershell.exe (PID: 5008)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 3020)
- powershell.exe (PID: 4016)
- powershell.exe (PID: 8728)
AMADEY has been detected (SURICATA)
- ramez.exe (PID: 7152)
- saren.exe (PID: 4812)
Connects to the CnC server
- ramez.exe (PID: 7152)
- svchost.exe (PID: 2196)
- saren.exe (PID: 4812)
- cmd.exe (PID: 7956)
LUMMA has been detected (SURICATA)
- MSBuild.exe (PID: 5116)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 5964)
- MSBuild.exe (PID: 5892)
- MSBuild.exe (PID: 6080)
- MSBuild.exe (PID: 5072)
- MSBuild.exe (PID: 2664)
- 2Z34FFh.exe (PID: 4172)
- a5cf1a229c.exe (PID: 3760)
AMADEY has been detected (YARA)
- ramez.exe (PID: 7152)
- saren.exe (PID: 4812)
LUMMA mutex has been found
- MSBuild.exe (PID: 5116)
- MSBuild.exe (PID: 5964)
- MSBuild.exe (PID: 5892)
- MSBuild.exe (PID: 6080)
- MSBuild.exe (PID: 4756)
- MSBuild.exe (PID: 5072)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 5116)
- MSBuild.exe (PID: 5964)
- MSBuild.exe (PID: 5892)
- MSBuild.exe (PID: 4756)
- MSBuild.exe (PID: 6080)
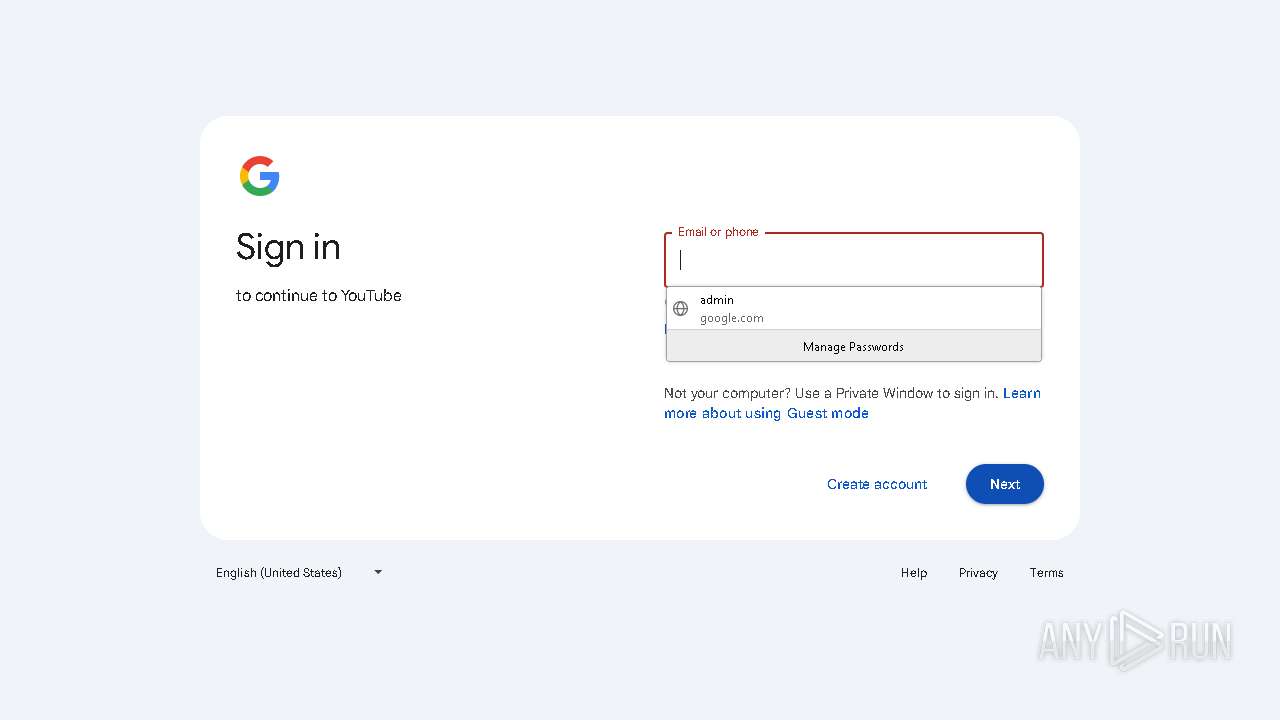
Steals credentials from Web Browsers
- MSBuild.exe (PID: 5116)
- MSBuild.exe (PID: 5964)
- MSBuild.exe (PID: 5892)
- MSBuild.exe (PID: 6080)
- MSBuild.exe (PID: 4756)
Executing a file with an untrusted certificate
- ra02W4S.exe (PID: 6576)
- 18b231ab42.exe (PID: 7324)
LUMMA has been detected (YARA)
- MSBuild.exe (PID: 5116)
- MSBuild.exe (PID: 5964)
- MSBuild.exe (PID: 5892)
- MSBuild.exe (PID: 6080)
Changes the autorun value in the registry
- A2vn0Mb.exe (PID: 1272)
- instasfdasda.exe (PID: 5124)
Application was injected by another process
- explorer.exe (PID: 5492)
Runs injected code in another process
- A2vn0Mb.exe (PID: 1272)
Known privilege escalation attack
- dllhost.exe (PID: 5084)
- dllhost.exe (PID: 6540)
GCLEANER has been detected (SURICATA)
- ra02W4S.exe (PID: 6576)
- cvtres.exe (PID: 7732)
Create files in the Startup directory
- instasfdasda.exe (PID: 5124)
Changes Windows Defender settings
- WinTemp-v4.exe (PID: 2416)
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
- NSudoLG.exe (PID: 4336)
Adds process to the Windows Defender exclusion list
- WinTemp-v4.exe (PID: 2416)
Uses Task Scheduler to autorun other applications
- WinTemp-v4.exe (PID: 2416)
Starts REAGENTC.EXE to disable the Windows Recovery Environment
- ReAgentc.exe (PID: 8152)
Starts CMD.EXE for self-deleting
- 4jL990O.exe (PID: 7440)
- LUM5DJ0945LIYDH79PRZ93.exe (PID: 7620)
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
MINER has been detected (SURICATA)
- cmd.exe (PID: 7956)
Adds path to the Windows Defender exclusion list
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
- cmd.exe (PID: 7400)
- NSudoLG.exe (PID: 4336)
Adds extension to the Windows Defender exclusion list
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 7784)
Deletes shadow copies
- cmd.exe (PID: 7336)
Possible tool for stealing has been detected
- 5b297f13de.exe (PID: 7848)
- firefox.exe (PID: 7396)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 5968)
- TempYDNCOH9PUEQPRYSD7ETYY3PGCB4UVZNE.EXE (PID: 2392)
- ramez.exe (PID: 7152)
- amnew.exe (PID: 1164)
- saren.exe (PID: 4812)
- A2vn0Mb.exe (PID: 1272)
- oxDU0MW.exe (PID: 4008)
- instasfdasda.exe (PID: 5124)
- MSBuild.exe (PID: 5892)
- triplehfswindowstool.exe (PID: 7628)
- WinTemp-v4.exe (PID: 2416)
- cn.exe (PID: 7552)
- cn.tmp (PID: 7568)
- 4jL990O.exe (PID: 7440)
- LUM5DJ0945LIYDH79PRZ93.exe (PID: 7300)
- b593c1a36e.exe (PID: 7916)
- b593c1a36e.tmp (PID: 7928)
- caa237fc3b.exe (PID: 7236)
- csc.exe (PID: 7624)
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
- powershell.exe (PID: 4016)
- a5cf1a229c.exe (PID: 3760)
- csc.exe (PID: 9924)
- powershell.exe (PID: 8728)
- 7z.exe (PID: 3800)
- Unlocker.exe (PID: 3156)
- csc.exe (PID: 7468)
Process requests binary or script from the Internet
- powershell.exe (PID: 5968)
- powershell.exe (PID: 5008)
- ramez.exe (PID: 7152)
- 4jL990O.exe (PID: 7440)
- powershell.exe (PID: 4016)
- a5cf1a229c.exe (PID: 3760)
- powershell.exe (PID: 8728)
Starts CMD.EXE for commands execution
- random.exe (PID: 660)
- WinTemp-v4.exe (PID: 2416)
- 4jL990O.exe (PID: 7440)
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 4884)
- LUM5DJ0945LIYDH79PRZ93.exe (PID: 7620)
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
- powershell.exe (PID: 3020)
- cmd.exe (PID: 4400)
- caa237fc3b.exe (PID: 7236)
- cmd.exe (PID: 8056)
- nircmd.exe (PID: 7388)
- NSudoLG.exe (PID: 4736)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7400)
- 3c60e807bc.exe (PID: 4692)
- Unlocker.exe (PID: 7740)
- Unlocker.exe (PID: 3156)
Found IP address in command line
- powershell.exe (PID: 5968)
- powershell.exe (PID: 5008)
- powershell.exe (PID: 4016)
- powershell.exe (PID: 8728)
Manipulates environment variables
- powershell.exe (PID: 5968)
- powershell.exe (PID: 5008)
- powershell.exe (PID: 4016)
- powershell.exe (PID: 8728)
Connects to the server without a host name
- powershell.exe (PID: 5968)
- ramez.exe (PID: 7152)
- powershell.exe (PID: 5008)
- saren.exe (PID: 4812)
- explorer.exe (PID: 5492)
- ra02W4S.exe (PID: 6576)
- 4jL990O.exe (PID: 7440)
- cvtres.exe (PID: 7732)
- powershell.exe (PID: 4016)
- a5cf1a229c.exe (PID: 3760)
- powershell.exe (PID: 8728)
Potential Corporate Privacy Violation
- powershell.exe (PID: 5968)
- powershell.exe (PID: 5008)
- ramez.exe (PID: 7152)
- 4jL990O.exe (PID: 7440)
- cmd.exe (PID: 7956)
- powershell.exe (PID: 4016)
- a5cf1a229c.exe (PID: 3760)
- powershell.exe (PID: 8728)
Reads security settings of Internet Explorer
- TempYDNCOH9PUEQPRYSD7ETYY3PGCB4UVZNE.EXE (PID: 2392)
- ramez.exe (PID: 7152)
- amnew.exe (PID: 1164)
- saren.exe (PID: 4812)
- ra02W4S.exe (PID: 6576)
Starts itself from another location
- TempYDNCOH9PUEQPRYSD7ETYY3PGCB4UVZNE.EXE (PID: 2392)
- amnew.exe (PID: 1164)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 5352)
- mshta.exe (PID: 5504)
- WinTemp-v4.exe (PID: 2416)
- triplehfswindowstool.exe (PID: 7628)
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 4884)
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
- MSBuild.exe (PID: 6108)
- mshta.exe (PID: 7620)
- NSudoLG.exe (PID: 4336)
- mshta.exe (PID: 8888)
Probably download files using WebClient
- mshta.exe (PID: 5352)
- mshta.exe (PID: 5504)
- mshta.exe (PID: 7620)
- mshta.exe (PID: 8888)
Starts process via Powershell
- powershell.exe (PID: 5008)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 3020)
- powershell.exe (PID: 4016)
- powershell.exe (PID: 8728)
Contacting a server suspected of hosting an CnC
- ramez.exe (PID: 7152)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 5116)
- MSBuild.exe (PID: 5964)
- saren.exe (PID: 4812)
- MSBuild.exe (PID: 5892)
- MSBuild.exe (PID: 6080)
- MSBuild.exe (PID: 5072)
- MSBuild.exe (PID: 2664)
- 2Z34FFh.exe (PID: 4172)
- a5cf1a229c.exe (PID: 3760)
There is functionality for taking screenshot (YARA)
- ramez.exe (PID: 7152)
- MSBuild.exe (PID: 5116)
- saren.exe (PID: 4812)
- MSBuild.exe (PID: 5964)
- MSBuild.exe (PID: 5892)
- MSBuild.exe (PID: 6080)
There is functionality for enable RDP (YARA)
- ramez.exe (PID: 7152)
- saren.exe (PID: 4812)
Searches for installed software
- MSBuild.exe (PID: 5116)
- MSBuild.exe (PID: 5964)
- MSBuild.exe (PID: 5892)
- MSBuild.exe (PID: 6080)
- MSBuild.exe (PID: 4756)
The process creates files with name similar to system file names
- A2vn0Mb.exe (PID: 1272)
Reads the BIOS version
- oxDU0MW.exe (PID: 4008)
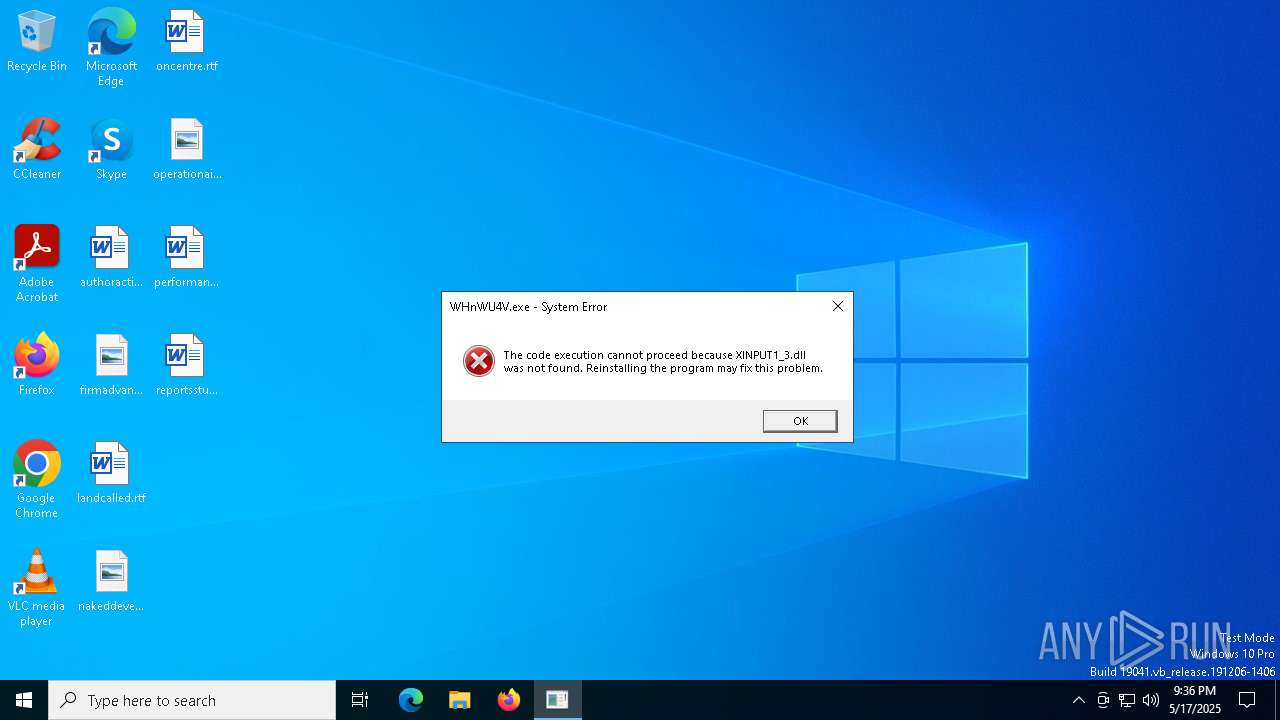
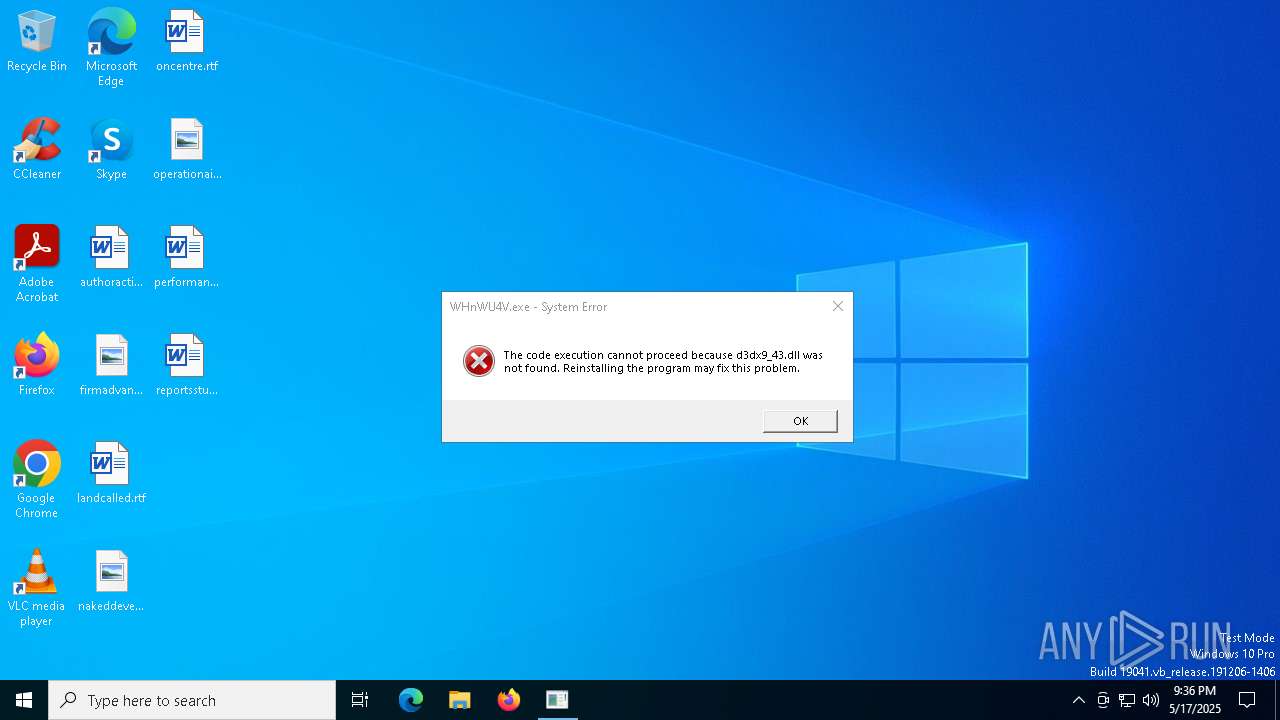
Executes application which crashes
- WinTemp-v4.exe (PID: 5936)
- Win-v42.exe (PID: 732)
- core.exe (PID: 1276)
The process executes via Task Scheduler
- saren.exe (PID: 5504)
- ramez.exe (PID: 1228)
- ramez.exe (PID: 7200)
- UserOOBEBroker.exe (PID: 3884)
- saren.exe (PID: 7712)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 4756)
- MSBuild.exe (PID: 7516)
- 4jL990O.exe (PID: 7440)
- MSBuild.exe (PID: 6108)
- MSBuild.exe (PID: 9376)
The process checks if it is being run in the virtual environment
- FxefytI.exe (PID: 1132)
Checks for external IP
- svchost.exe (PID: 2196)
- instasfdasda.exe (PID: 5124)
- WinTemp-v4.exe (PID: 2416)
Script adds exclusion process to Windows Defender
- WinTemp-v4.exe (PID: 2416)
Script adds exclusion path to Windows Defender
- WinTemp-v4.exe (PID: 2416)
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
- NSudoLG.exe (PID: 4336)
Process drops legitimate windows executable
- cn.tmp (PID: 7568)
- 4jL990O.exe (PID: 7440)
- LUM5DJ0945LIYDH79PRZ93.exe (PID: 7300)
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
Connects to unusual port
- instasfdasda.exe (PID: 5124)
- WinTemp-v4.exe (PID: 2416)
- cmd.exe (PID: 7956)
The process drops C-runtime libraries
- cn.tmp (PID: 7568)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 2344)
- cmd.exe (PID: 6080)
Uses powercfg.exe to modify the power settings
- WinTemp-v4.exe (PID: 2416)
- cmd.exe (PID: 4988)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 3156)
- cmd.exe (PID: 7976)
Hides command output
- cmd.exe (PID: 8008)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 6072)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 7356)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 5972)
- net.exe (PID: 5008)
- cmd.exe (PID: 8172)
- net.exe (PID: 7520)
Starts a Microsoft application from unusual location
- LUM5DJ0945LIYDH79PRZ93.exe (PID: 7300)
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 4884)
- LUM5DJ0945LIYDH79PRZ93.exe (PID: 7620)
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1676)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 6072)
Lists all scheduled tasks
- schtasks.exe (PID: 7736)
Application launched itself
- LUM5DJ0945LIYDH79PRZ93.exe (PID: 7300)
- cmd.exe (PID: 4400)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7400)
Starts SC.EXE for service management
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
- cmd.exe (PID: 7988)
- cmd.exe (PID: 7908)
- cmd.exe (PID: 7400)
Stops a currently running service
- sc.exe (PID: 7512)
- sc.exe (PID: 5640)
- sc.exe (PID: 1764)
- sc.exe (PID: 6564)
- sc.exe (PID: 8140)
Windows service management via SC.EXE
- sc.exe (PID: 7664)
- sc.exe (PID: 6416)
- sc.exe (PID: 5756)
- sc.exe (PID: 7412)
- sc.exe (PID: 4756)
- sc.exe (PID: 4868)
- sc.exe (PID: 8244)
- sc.exe (PID: 8368)
- sc.exe (PID: 8112)
- sc.exe (PID: 7396)
The executable file from the user directory is run by the CMD process
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
- nircmd.exe (PID: 7388)
- NSudoLG.exe (PID: 4736)
- NSudoLG.exe (PID: 4336)
- 7z.exe (PID: 3800)
- Unlocker.exe (PID: 7740)
- Unlocker.exe (PID: 3156)
Drops 7-zip archiver for unpacking
- caa237fc3b.exe (PID: 7236)
The process deletes folder without confirmation
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
Script adds exclusion extension to Windows Defender
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
BASE64 encoded PowerShell command has been detected
- MSBuild.exe (PID: 6108)
The process bypasses the loading of PowerShell profile settings
- MSBuild.exe (PID: 6108)
Executing commands from a ".bat" file
- cmd.exe (PID: 4400)
- caa237fc3b.exe (PID: 7236)
- cmd.exe (PID: 8056)
- nircmd.exe (PID: 7388)
- cmd.exe (PID: 7452)
- NSudoLG.exe (PID: 4736)
Starts application with an unusual extension
- cmd.exe (PID: 6136)
- cmd.exe (PID: 5408)
- cmd.exe (PID: 7400)
Base64-obfuscated command line is found
- MSBuild.exe (PID: 6108)
Process uninstalls Windows update
- wusa.exe (PID: 7736)
The process hide an interactive prompt from the user
- MSBuild.exe (PID: 6108)
CSC.EXE is used to compile C# code
- csc.exe (PID: 7624)
- csc.exe (PID: 9924)
- csc.exe (PID: 7468)
Uses TASKKILL.EXE to kill Browsers
- 5b297f13de.exe (PID: 7848)
Executes as Windows Service
- VSSVC.exe (PID: 208)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7400)
- cmd.exe (PID: 5408)
Get information on the list of running processes
- cmd.exe (PID: 7400)
- cmd.exe (PID: 7436)
Uses TASKKILL.EXE to kill process
- 5b297f13de.exe (PID: 7848)
- cmd.exe (PID: 8320)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 7936)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7400)
Drops a system driver (possible attempt to evade defenses)
- Unlocker.exe (PID: 3156)
INFO
Reads the computer name
- random.exe (PID: 660)
- TempYDNCOH9PUEQPRYSD7ETYY3PGCB4UVZNE.EXE (PID: 2392)
- ramez.exe (PID: 7152)
- MSBuild.exe (PID: 5116)
- MSBuild.exe (PID: 5964)
- amnew.exe (PID: 1164)
- saren.exe (PID: 4812)
- FxefytI.exe (PID: 1132)
- ra02W4S.exe (PID: 6576)
- oxDU0MW.exe (PID: 4008)
- MSBuild.exe (PID: 5892)
- MSBuild.exe (PID: 4756)
- MSBuild.exe (PID: 6080)
- instasfdasda.exe (PID: 5124)
- MSBuild.exe (PID: 5072)
- win_init.exe (PID: 6244)
- Microsoft365.exe (PID: 5304)
Create files in a temporary directory
- random.exe (PID: 660)
- TempYDNCOH9PUEQPRYSD7ETYY3PGCB4UVZNE.EXE (PID: 2392)
- ramez.exe (PID: 7152)
- amnew.exe (PID: 1164)
- saren.exe (PID: 4812)
- oxDU0MW.exe (PID: 4008)
- win_init.exe (PID: 6244)
- MSBuild.exe (PID: 5892)
The sample compiled with english language support
- random.exe (PID: 660)
- ramez.exe (PID: 7152)
- cn.tmp (PID: 7568)
- 4jL990O.exe (PID: 7440)
- LUM5DJ0945LIYDH79PRZ93.exe (PID: 7300)
- caa237fc3b.exe (PID: 7236)
- 9Q1IC7BQ78TUEPWEP0SN7JTUWQWPWY7.exe (PID: 6372)
- Unlocker.exe (PID: 3156)
Reads mouse settings
- random.exe (PID: 660)
Auto-launch of the file from Task Scheduler
- cmd.exe (PID: 5176)
- cmd.exe (PID: 4000)
Checks supported languages
- random.exe (PID: 660)
- TempYDNCOH9PUEQPRYSD7ETYY3PGCB4UVZNE.EXE (PID: 2392)
- ramez.exe (PID: 7152)
- TempYDNCOH9PUEQPRYSD7ETYY3PGCB4UVZNE.EXE (PID: 6392)
- hF05RdW.exe (PID: 6004)
- 6GqsSIs.exe (PID: 2136)
- MSBuild.exe (PID: 5116)
- MSBuild.exe (PID: 5964)
- ra02W4S.exe (PID: 6576)
- amnew.exe (PID: 1164)
- saren.exe (PID: 4812)
- FxefytI.exe (PID: 1132)
- legedddd.exe (PID: 4188)
- A2vn0Mb.exe (PID: 1272)
- MSBuild.exe (PID: 5892)
- System.exe (PID: 2568)
- cron.exe (PID: 2340)
- oxDU0MW.exe (PID: 4008)
- saren.exe (PID: 5504)
- ramez.exe (PID: 1228)
- alex12312321312.exe (PID: 2344)
- MSBuild.exe (PID: 4756)
- MSBuild.exe (PID: 6080)
- 08IyOOF.exe (PID: 3240)
- MSBuild.exe (PID: 5072)
- instasfdasda.exe (PID: 5124)
- win_init.exe (PID: 6244)
- WinTemp-v4.exe (PID: 2416)
- Microsoft365.exe (PID: 5304)
Reads Internet Explorer settings
- mshta.exe (PID: 5504)
- mshta.exe (PID: 5352)
The executable file from the user directory is run by the Powershell process
- TempYDNCOH9PUEQPRYSD7ETYY3PGCB4UVZNE.EXE (PID: 2392)
- TempYDNCOH9PUEQPRYSD7ETYY3PGCB4UVZNE.EXE (PID: 6392)
- TempOVLFJKQWI62GVSZVQGQIEM0FSDQP7RFK.EXE (PID: 9812)
- TempOVLFJKQWI62GVSZVQGQIEM0FSDQP7RFK.EXE (PID: 8964)
Process checks computer location settings
- TempYDNCOH9PUEQPRYSD7ETYY3PGCB4UVZNE.EXE (PID: 2392)
- ramez.exe (PID: 7152)
- amnew.exe (PID: 1164)
- saren.exe (PID: 4812)
Checks proxy server information
- ramez.exe (PID: 7152)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 5008)
- saren.exe (PID: 4812)
- ra02W4S.exe (PID: 6576)
- instasfdasda.exe (PID: 5124)
Disables trace logs
- powershell.exe (PID: 5008)
- powershell.exe (PID: 5968)
- instasfdasda.exe (PID: 5124)
Manual execution by a user
- mshta.exe (PID: 5352)
Creates files or folders in the user directory
- ramez.exe (PID: 7152)
- ra02W4S.exe (PID: 6576)
- A2vn0Mb.exe (PID: 1272)
- WerFault.exe (PID: 6972)
- saren.exe (PID: 4812)
- instasfdasda.exe (PID: 5124)
Reads the software policy settings
- MSBuild.exe (PID: 5116)
- MSBuild.exe (PID: 5964)
- saren.exe (PID: 4812)
- ra02W4S.exe (PID: 6576)
- MSBuild.exe (PID: 5892)
- MSBuild.exe (PID: 4756)
- MSBuild.exe (PID: 6080)
- MSBuild.exe (PID: 5072)
Reads the machine GUID from the registry
- FxefytI.exe (PID: 1132)
- ra02W4S.exe (PID: 6576)
- oxDU0MW.exe (PID: 4008)
- saren.exe (PID: 4812)
- instasfdasda.exe (PID: 5124)
- win_init.exe (PID: 6244)
- Microsoft365.exe (PID: 5304)
Auto-launch of the file from Registry key
- A2vn0Mb.exe (PID: 1272)
- instasfdasda.exe (PID: 5124)
Checks transactions between databases Windows and Oracle
- oxDU0MW.exe (PID: 4008)
- win_init.exe (PID: 6244)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 5084)
- dllhost.exe (PID: 6540)
Attempting to use instant messaging service
- MSBuild.exe (PID: 4756)
- MSBuild.exe (PID: 7516)
- 4jL990O.exe (PID: 7440)
- MSBuild.exe (PID: 6108)
Reads Environment values
- instasfdasda.exe (PID: 5124)
Auto-launch of the file from Startup directory
- instasfdasda.exe (PID: 5124)
Changes the registry key values via Powershell
- triplehfswindowstool.exe (PID: 7628)
Application launched itself
- chrome.exe (PID: 6456)
- firefox.exe (PID: 7396)
- chrome.exe (PID: 5412)
- firefox.exe (PID: 7436)
- chrome.exe (PID: 540)
- chrome.exe (PID: 9788)
Changes the display of characters in the console
- cmd.exe (PID: 6136)
- cmd.exe (PID: 5408)
- cmd.exe (PID: 7400)
NirSoft software is detected
- nircmd.exe (PID: 7388)
Starts MODE.COM to configure console settings
- mode.com (PID: 2120)
Checks operating system version
- cmd.exe (PID: 7400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(7152) ramez.exe
C2185.156.72.96
URLhttp://185.156.72.96/te4h2nus/index.php
Version5.34
Options
Drop directoryd610cf342e
Drop nameramez.exe
Strings (125)lv:
msi
Kaspersky Lab
av:
|
#
"
\App
00000422
dm:
Powershell.exe
ProgramData\
ps1
rundll32
http://
Content-Disposition: form-data; name="data"; filename="
SOFTWARE\Microsoft\Windows NT\CurrentVersion
dll
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
id:
VideoID
cred.dll|clip.dll|
0000043f
cmd
00000423
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
-executionpolicy remotesigned -File "
2022
------
2016
og:
\0000
CurrentBuild
2019
:::
S-%lu-
" && timeout 1 && del
ProductName
Panda Security
ESET
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
/k
+++
?scr=1
Doctor Web
GET
SYSTEM\ControlSet001\Services\BasicDisplay\Video
/quiet
.jpg
d610cf342e
vs:
sd:
rundll32.exe
"taskkill /f /im "
pc:
random
=
360TotalSecurity
<d>
wb
Content-Type: multipart/form-data; boundary=----
Startup
Norton
&& Exit"
os:
https://
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
2025
Avira
%-lu
zip
POST
"
Content-Type: application/octet-stream
Rem
/te4h2nus/index.php
------
5.34
<c>
clip.dll
AVAST Software
\
shell32.dll
" && ren
e3
ramez.exe
kernel32.dll
DefaultSettings.XResolution
d1
DefaultSettings.YResolution
185.156.72.96
r=
cred.dll
--
GetNativeSystemInfo
-%lu
ComputerName
&unit=
Keyboard Layout\Preload
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
ar:
Sophos
%USERPROFILE%
exe
e1
e2
st=s
Programs
0123456789
un:
rb
bi:
abcdefghijklmnopqrstuvwxyz0123456789-_
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
cmd /C RMDIR /s/q
Bitdefender
-unicode-
AVG
WinDefender
&&
shutdown -s -t 0
Comodo
00000419
Content-Type: application/x-www-form-urlencoded
/Plugins/
Main
(PID) Process(4812) saren.exe
C277.83.207.69
URLhttp://77.83.207.69/rob75u9v/index.php
Version5.34
Options
Drop directory02106dbc20
Drop namesaren.exe
Strings (125)lv:
msi
Kaspersky Lab
av:
|
#
"
\App
00000422
dm:
Powershell.exe
ProgramData\
ps1
rundll32
http://
Content-Disposition: form-data; name="data"; filename="
SOFTWARE\Microsoft\Windows NT\CurrentVersion
dll
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
id:
VideoID
cred.dll|clip.dll|
0000043f
cmd
00000423
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
-executionpolicy remotesigned -File "
2022
------
2016
og:
\0000
02106dbc20
CurrentBuild
2019
:::
S-%lu-
" && timeout 1 && del
ProductName
Panda Security
ESET
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
/k
+++
?scr=1
Doctor Web
GET
SYSTEM\ControlSet001\Services\BasicDisplay\Video
/quiet
.jpg
saren.exe
vs:
sd:
rundll32.exe
"taskkill /f /im "
pc:
random
=
360TotalSecurity
<d>
wb
Content-Type: multipart/form-data; boundary=----
Startup
Norton
&& Exit"
os:
https://
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
/rob75u9v/index.php
2025
Avira
%-lu
zip
POST
"
Content-Type: application/octet-stream
Rem
77.83.207.69
------
5.34
<c>
clip.dll
AVAST Software
\
shell32.dll
" && ren
e3
kernel32.dll
DefaultSettings.XResolution
d1
DefaultSettings.YResolution
r=
cred.dll
--
GetNativeSystemInfo
-%lu
ComputerName
&unit=
Keyboard Layout\Preload
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
ar:
Sophos
%USERPROFILE%
exe
e1
e2
st=s
Programs
0123456789
un:
rb
bi:
abcdefghijklmnopqrstuvwxyz0123456789-_
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
cmd /C RMDIR /s/q
Bitdefender
-unicode-
AVG
WinDefender
&&
shutdown -s -t 0
Comodo
00000419
Content-Type: application/x-www-form-urlencoded
/Plugins/
Main
Lumma
(PID) Process(5116) MSBuild.exe
C2 (9)onehunqpom.life/zpxd
narrathfpt.top/tekq
featurlyin.top/pdal
overcovtcg.top/juhd
laminaflbx.shop/twoq
cornerdurv.top/adwq
posseswsnc.top/akds
jackthyfuc.run/xpas
blackswmxc.top/bgry
(PID) Process(5964) MSBuild.exe
C2 (9)onehunqpom.life/zpxd
narrathfpt.top/tekq
featurlyin.top/pdal
overcovtcg.top/juhd
laminaflbx.shop/twoq
cornerdurv.top/adwq
posseswsnc.top/akds
jackthyfuc.run/xpas
blackswmxc.top/bgry
(PID) Process(5892) MSBuild.exe
C2 (9)featurlyin.top/pdal
overcovtcg.top/juhd
meteorplyp.live/lekp
zmedtipp.live/mnvzx
flowerexju.bet/lanz
posseswsnc.top/akds
araucahkbm.live/baneb
blackswmxc.top/bgry
easterxeen.run/zavc
(PID) Process(6080) MSBuild.exe
C2 (8)featurlyin.top/pdal
overcovtcg.top/juhd
zmedtipp.live/mnvzx
flowerexju.bet/lanz
posseswsnc.top/akds
araucahkbm.live/baneb
blackswmxc.top/bgry
easterxeen.run/zavc
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:05:17 20:14:12+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 633856 |
| InitializedDataSize: | 326144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20577 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Total processes
514
Monitored processes
370
Malicious processes
57
Suspicious processes
15
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | reg add "HKU\S-1-5-18\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize" /v "AppsUseLightTheme" /t reg_dword /d 0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | MSBuild.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 660 | "C:\Users\admin\AppData\Local\Temp\random.exe" | C:\Users\admin\AppData\Local\Temp\random.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2252 --field-trial-handle=1828,i,13187124136585761296,6211353266772974600,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 1 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | C:\Windows\System32\Win-v42.exe | C:\Windows\System32\Win-v42.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 864 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 4HV551S4YY12YLTP7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
142 024
Read events
141 739
Write events
200
Delete events
85
Modification events
| (PID) Process: | (5504) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5504) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5504) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:0000000000040288 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:0000000000040288 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5968) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5968) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5968) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5968) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5968) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
115
Suspicious files
251
Text files
151
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 660 | random.exe | C:\Users\admin\AppData\Local\Temp\DU6HQ5Dhu.hta | html | |
MD5:3ABE13301BCAA47E8CFC84D170F1892A | SHA256:4F200B4134BF773DAF51F0469F6DBB18EB364B6A465E6717C5FF0EB7BA6B8701 | |||
| 5968 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cjyawoaj.2xa.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5492 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 5968 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_aeh4eh31.krm.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5008 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tzoldbms.y5t.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7152 | ramez.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\hF05RdW[1].exe | executable | |
MD5:D879A63D1D5E28709B1797CDBCF459FE | SHA256:57144091DA4770926911FFD13A68C002CF7096F73AA0DFCE50029296D7C74586 | |||
| 7152 | ramez.exe | C:\Users\admin\AppData\Local\Temp\10135380101\6GqsSIs.exe | executable | |
MD5:3B5A6F02E79A326E3979B266F2EC5A60 | SHA256:E9C5B1AE71A3EED23EC9C01B4A231FFB3435365BEFABDA688C62F7751403517D | |||
| 5008 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_h1xgjgpj.dxt.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2392 | TempYDNCOH9PUEQPRYSD7ETYY3PGCB4UVZNE.EXE | C:\Windows\Tasks\ramez.job | binary | |
MD5:30E613A40B70A3DD355623AB87173DBC | SHA256:551D4A69BB36A64C614777D405175D075C2FFF8F2CB2D53B7D873C86C02D9A80 | |||
| 5968 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:AF416286E8C3E9E9659E2C8C3E3C2266 | SHA256:C4CA75ADA01B1402A63A2BDD4503076429A90C431DAAF42406C26F8CDFFBC871 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
130
TCP/UDP connections
290
DNS requests
196
Threats
168
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5968 | powershell.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/testmine/random.exe | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7152 | ramez.exe | POST | 200 | 185.156.72.96:80 | http://185.156.72.96/te4h2nus/index.php | unknown | — | — | malicious |
7152 | ramez.exe | POST | 200 | 185.156.72.96:80 | http://185.156.72.96/te4h2nus/index.php | unknown | — | — | malicious |
7152 | ramez.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/files/6925266445/6GqsSIs.exe | unknown | — | — | unknown |
7152 | ramez.exe | POST | 200 | 185.156.72.96:80 | http://185.156.72.96/te4h2nus/index.php | unknown | — | — | malicious |
5008 | powershell.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/testmine/random.exe | unknown | — | — | unknown |
7152 | ramez.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/files/5517536483/hF05RdW.exe | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5968 | powershell.exe | 185.156.72.2:80 | — | Tov Vaiz Partner | RU | unknown |
6544 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cornerdurv.top |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5968 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
5968 | powershell.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
5968 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
5968 | powershell.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
5968 | powershell.exe | Misc activity | ET INFO Packed Executable Download |
7152 | ramez.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
5008 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
5008 | powershell.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
5008 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
5008 | powershell.exe | Misc activity | ET INFO Packed Executable Download |