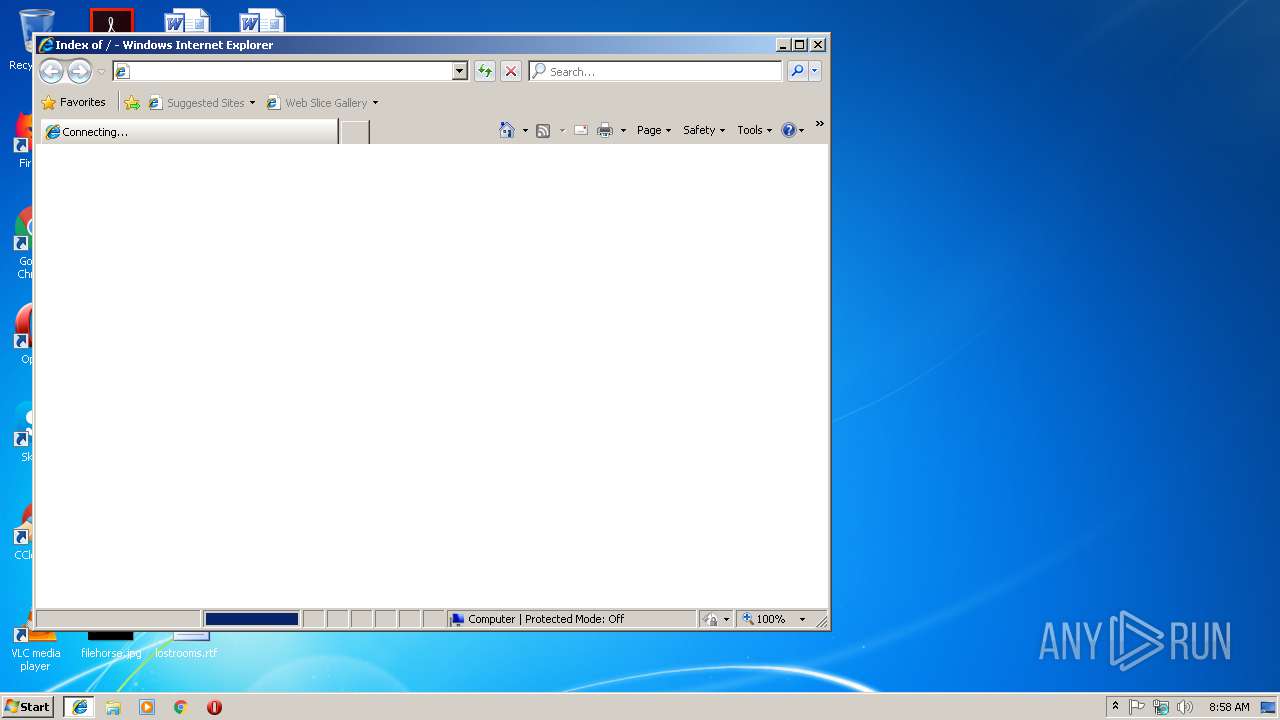
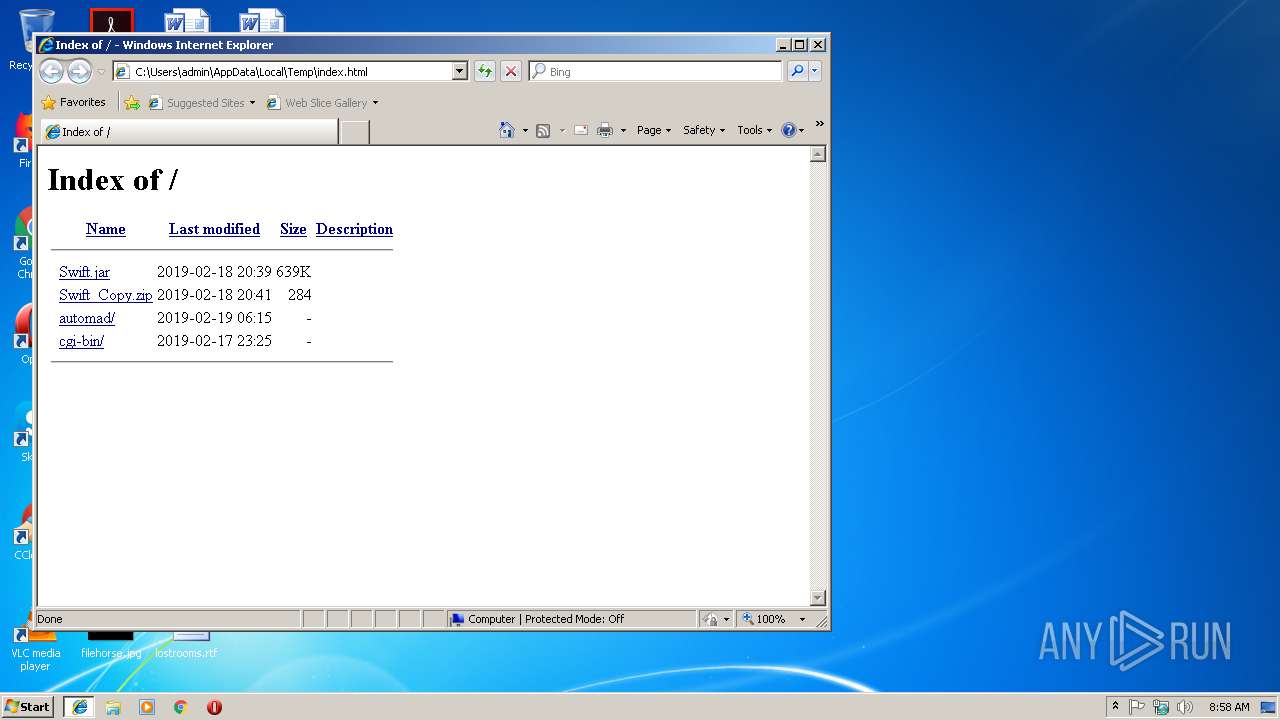
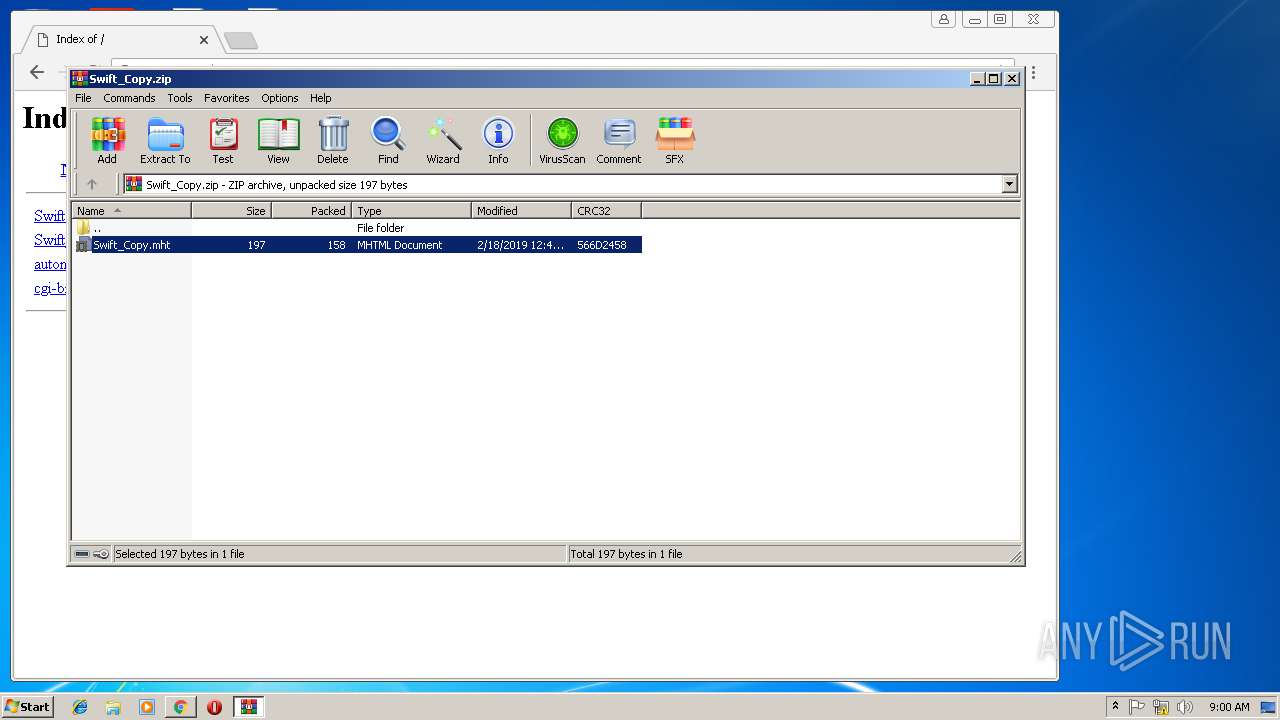
| download: | index.html |
| Full analysis: | https://app.any.run/tasks/34fe2353-2f9e-483a-9d76-0f847a3b7a26 |
| Verdict: | Malicious activity |
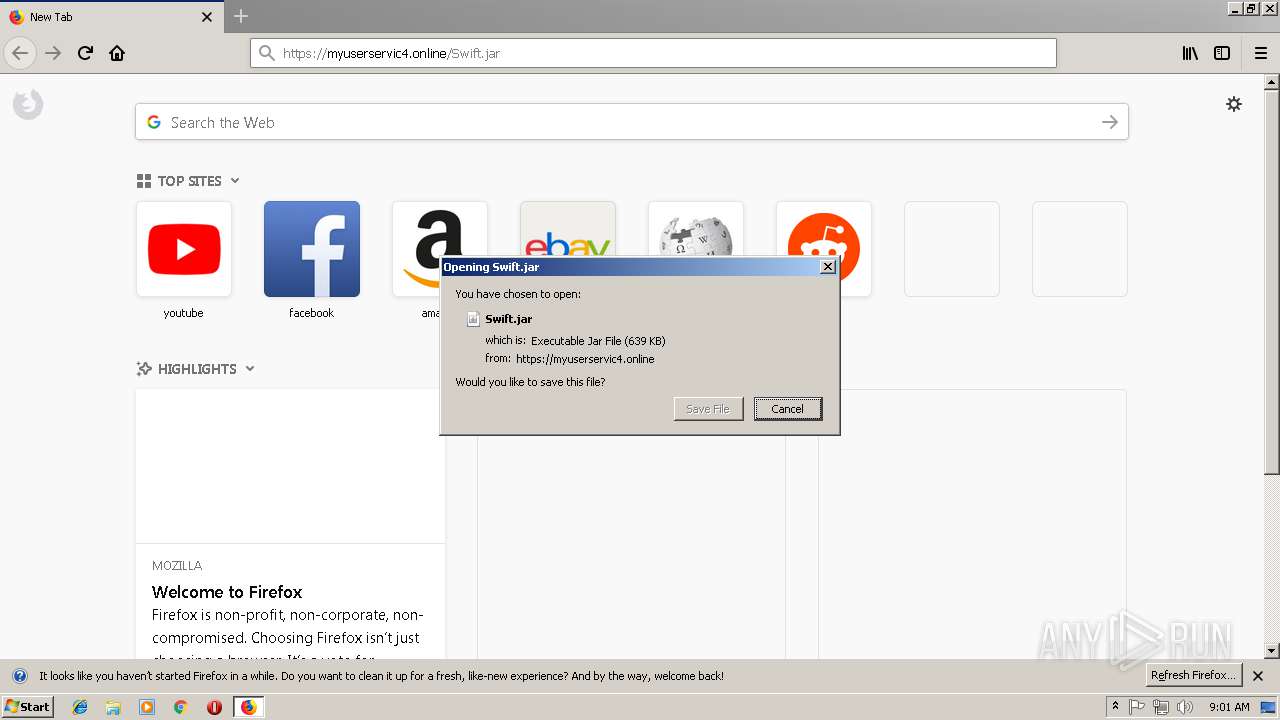
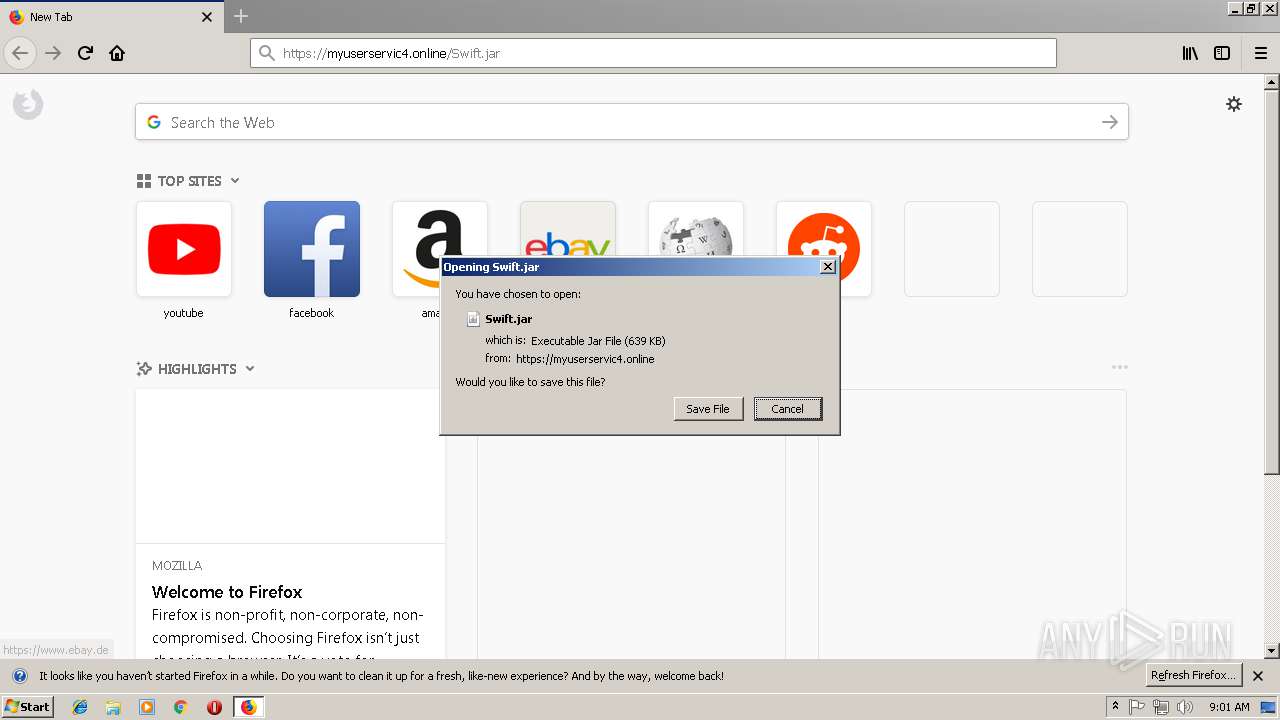
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
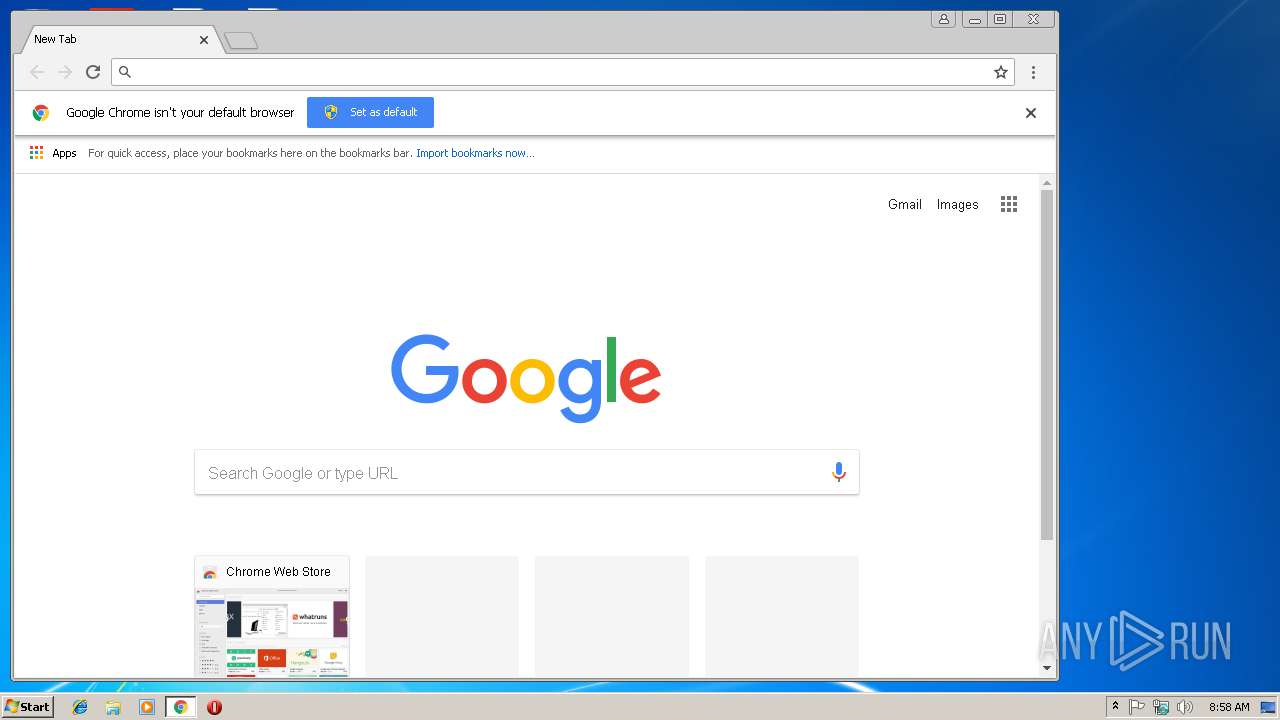
| Analysis date: | February 19, 2019, 08:58:23 |
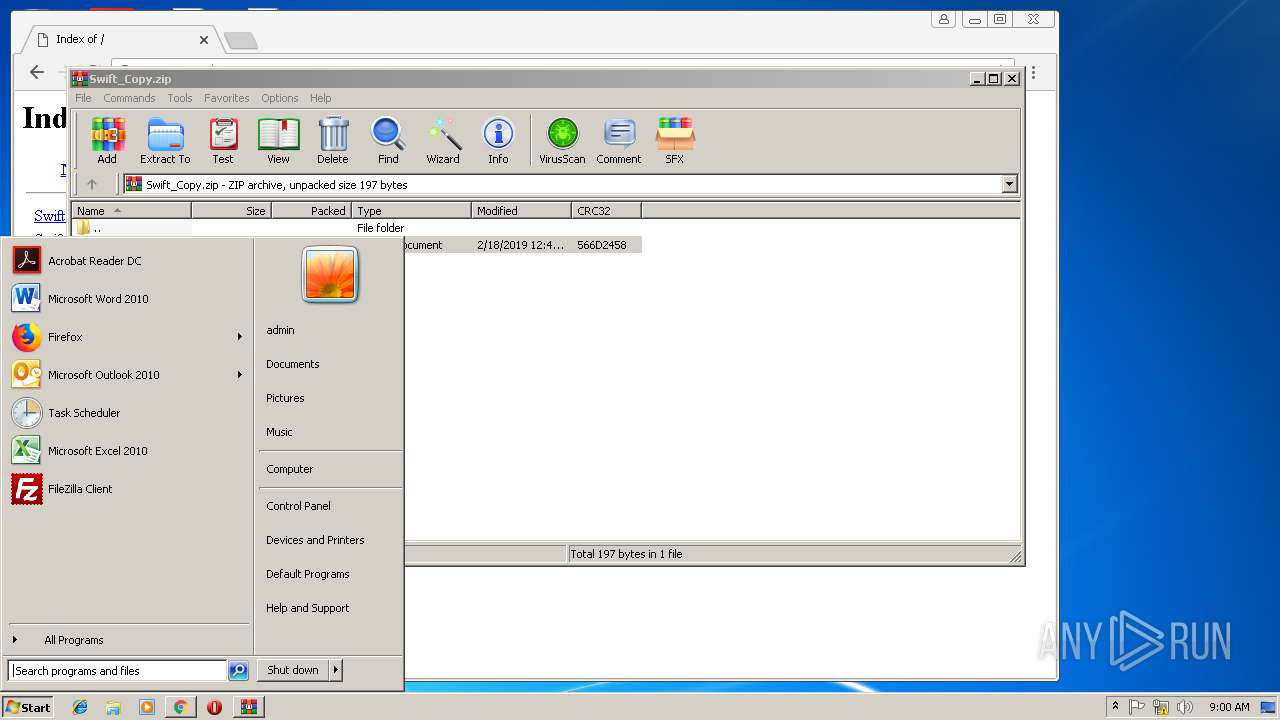
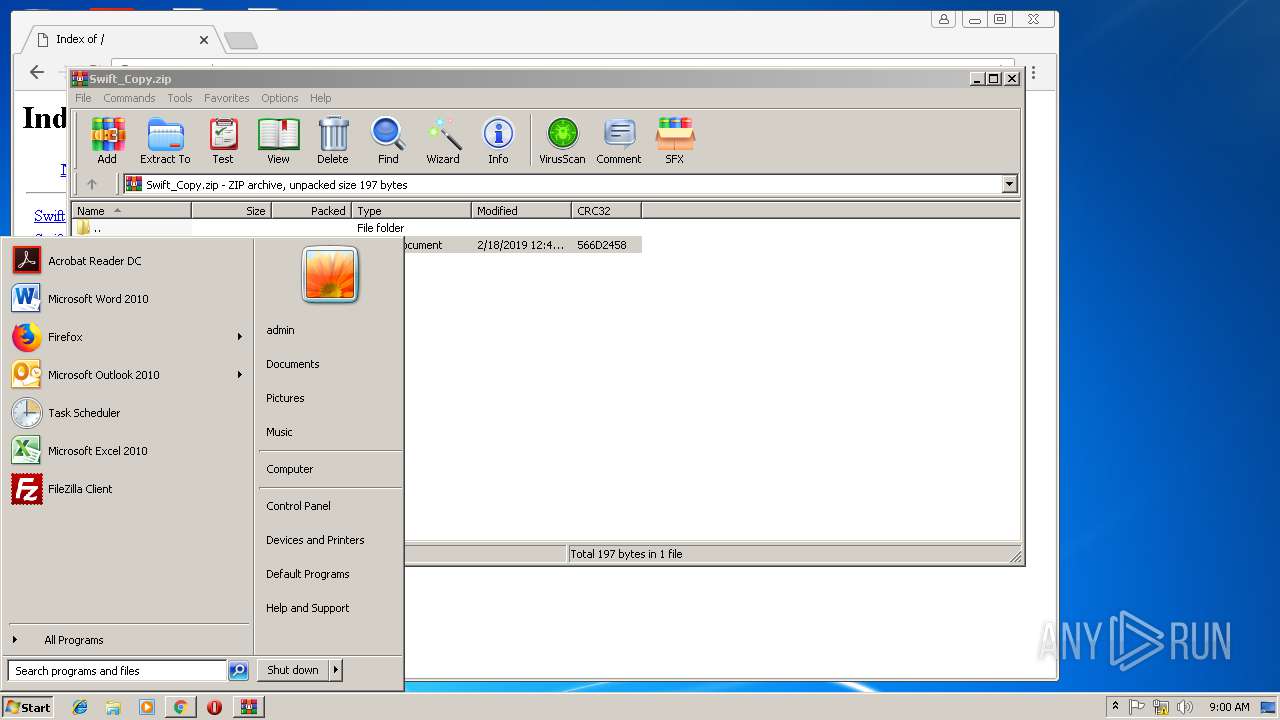
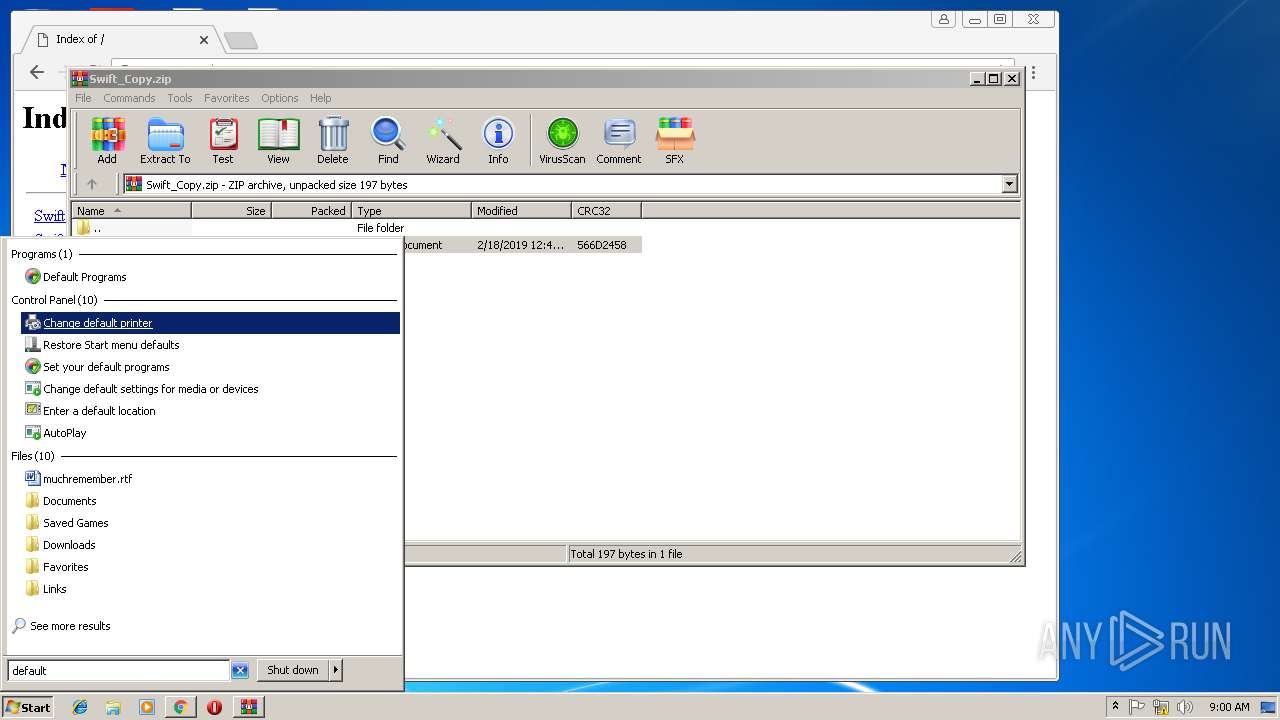
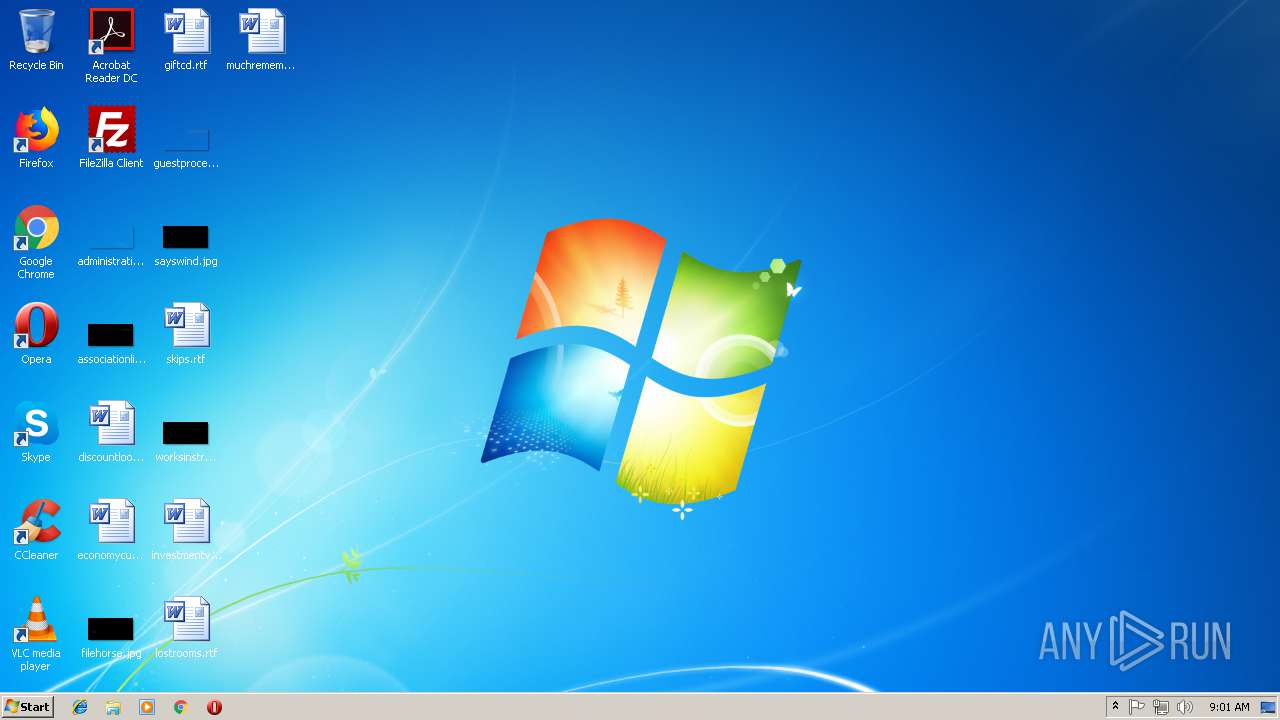
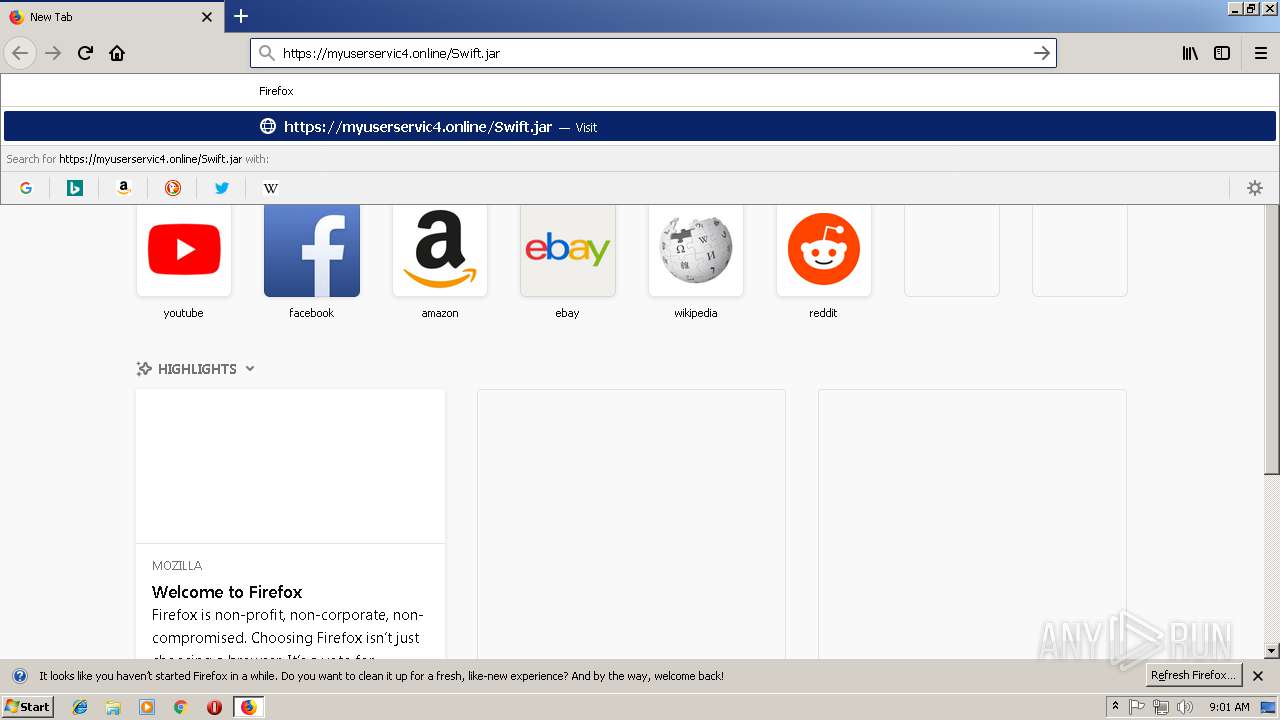
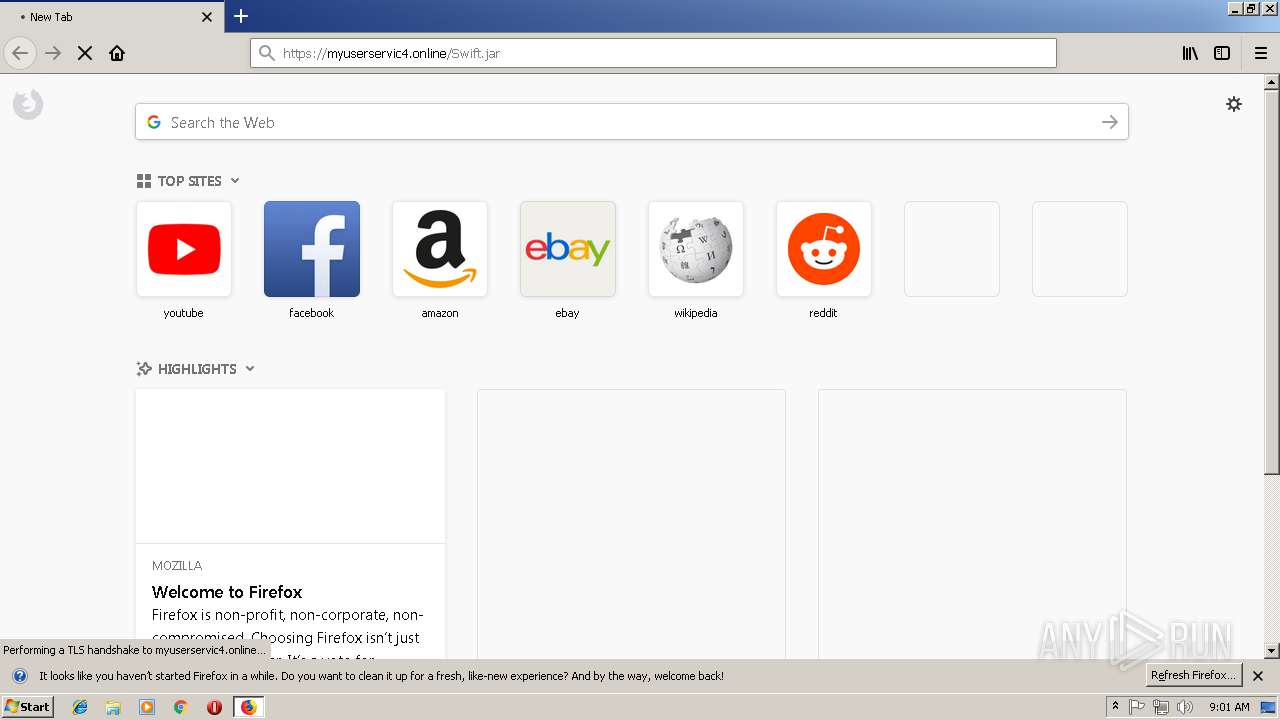
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text |
| MD5: | 7C51ED880A1BC921185635CE1FC779A6 |
| SHA1: | 18DE80D656DF0EB9DD795038747A8799858147DD |
| SHA256: | 3D9F8C26F5C629120BDDDA4B4D3C7865A02E6ADD12A4DBE2B654DF575A46633A |
| SSDEEP: | 24:Wlux+49snxeWZyoft9el9xmi7pT2Kk3C9xmeRQKR59xmEFYKTEJ9xmMFYKxEp5g:qS+gmeWQolGmiVT2Kk32m8QKRxmsYKTU |
MALICIOUS
Changes the autorun value in the registry
- wscript.exe (PID: 2376)
- WScript.exe (PID: 3432)
- reg.exe (PID: 2544)
- wscript.exe (PID: 4052)
- WScript.exe (PID: 972)
- reg.exe (PID: 2816)
- wscript.exe (PID: 3924)
- WScript.exe (PID: 3596)
- reg.exe (PID: 3548)
Writes to a start menu file
- WScript.exe (PID: 3432)
- WScript.exe (PID: 972)
- WScript.exe (PID: 3596)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3528)
- schtasks.exe (PID: 2296)
- schtasks.exe (PID: 4068)
- schtasks.exe (PID: 2380)
- schtasks.exe (PID: 1840)
- schtasks.exe (PID: 4836)
- schtasks.exe (PID: 4596)
- schtasks.exe (PID: 5872)
- schtasks.exe (PID: 4192)
- schtasks.exe (PID: 5216)
Uses Task Scheduler to run other applications
- WScript.exe (PID: 3432)
- WScript.exe (PID: 972)
- WScript.exe (PID: 3596)
AdWind was detected
- java.exe (PID: 272)
- java.exe (PID: 4004)
- java.exe (PID: 4012)
- java.exe (PID: 2852)
- java.exe (PID: 2728)
- java.exe (PID: 3512)
Loads dropped or rewritten executable
- javaw.exe (PID: 3988)
- iexplore.exe (PID: 2324)
- iexplore.exe (PID: 2460)
- java.exe (PID: 272)
- iexplore.exe (PID: 624)
- svchost.exe (PID: 816)
- wscript.exe (PID: 2376)
- iexplore.exe (PID: 3236)
- iexplore.exe (PID: 3392)
- chrome.exe (PID: 3860)
- javaw.exe (PID: 3672)
- javaw.exe (PID: 328)
- java.exe (PID: 4004)
- javaw.exe (PID: 2576)
- wscript.exe (PID: 4052)
- javaw.exe (PID: 2336)
- java.exe (PID: 4012)
- javaw.exe (PID: 2644)
- java.exe (PID: 3512)
- firefox.exe (PID: 3172)
- javaw.exe (PID: 2840)
- javaw.exe (PID: 3452)
- wscript.exe (PID: 3924)
- java.exe (PID: 2852)
- javaw.exe (PID: 3808)
- java.exe (PID: 2728)
Application was dropped or rewritten from another process
- java.exe (PID: 4004)
- java.exe (PID: 4012)
- javaw.exe (PID: 2576)
- javaw.exe (PID: 3672)
- javaw.exe (PID: 3988)
- javaw.exe (PID: 328)
- java.exe (PID: 272)
- javaw.exe (PID: 2644)
- java.exe (PID: 3512)
- javaw.exe (PID: 2840)
- javaw.exe (PID: 3452)
- java.exe (PID: 2852)
- java.exe (PID: 2728)
- javaw.exe (PID: 3808)
- javaw.exe (PID: 2336)
ADWIND was detected
- javaw.exe (PID: 328)
- javaw.exe (PID: 2644)
- javaw.exe (PID: 3808)
SUSPICIOUS
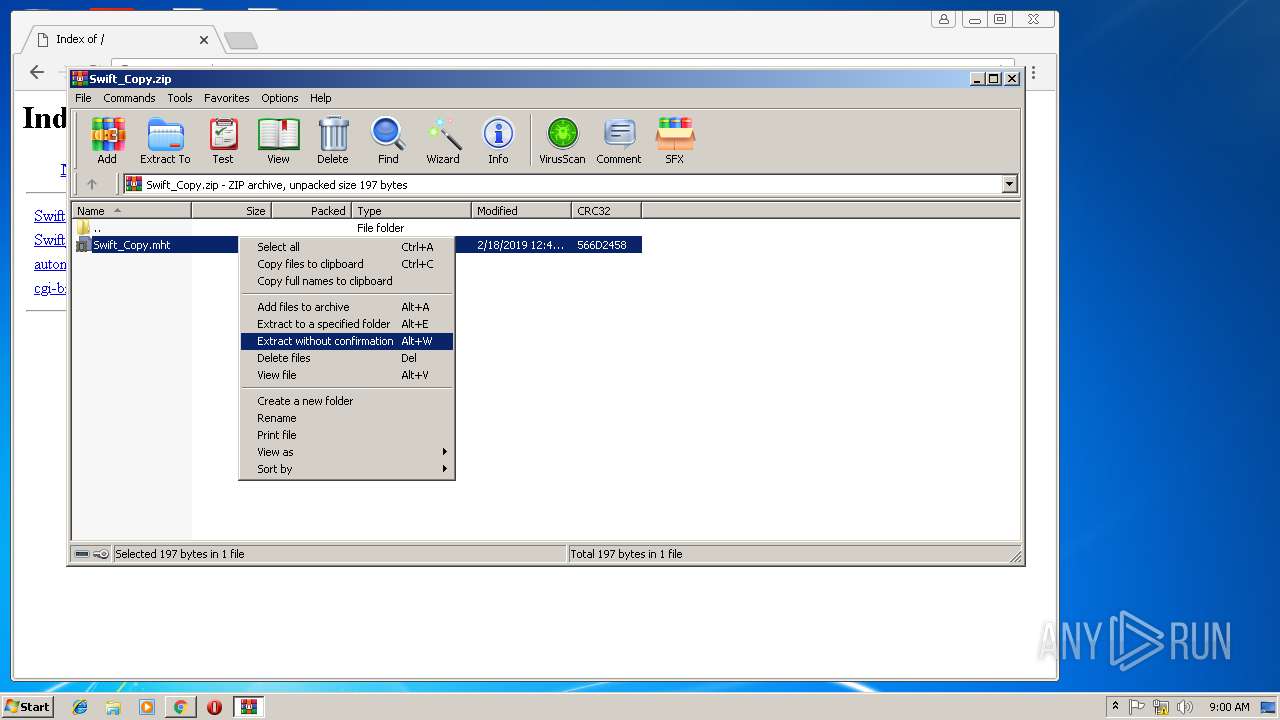
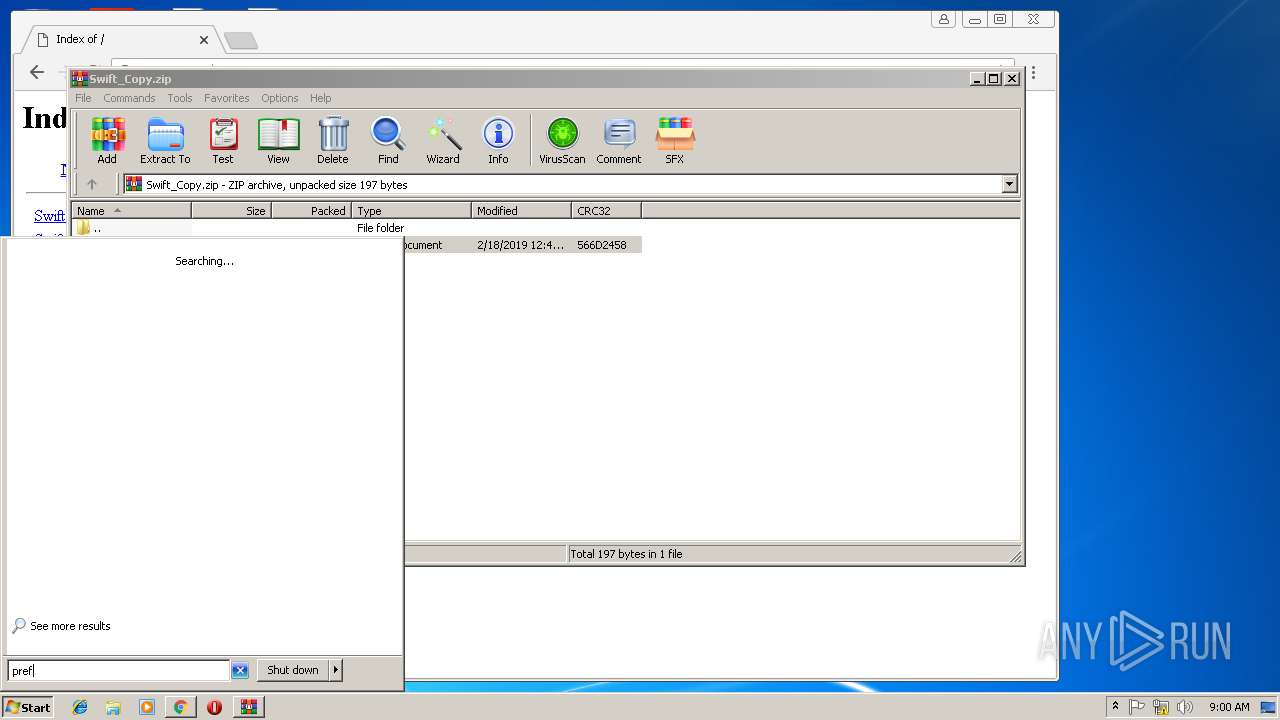
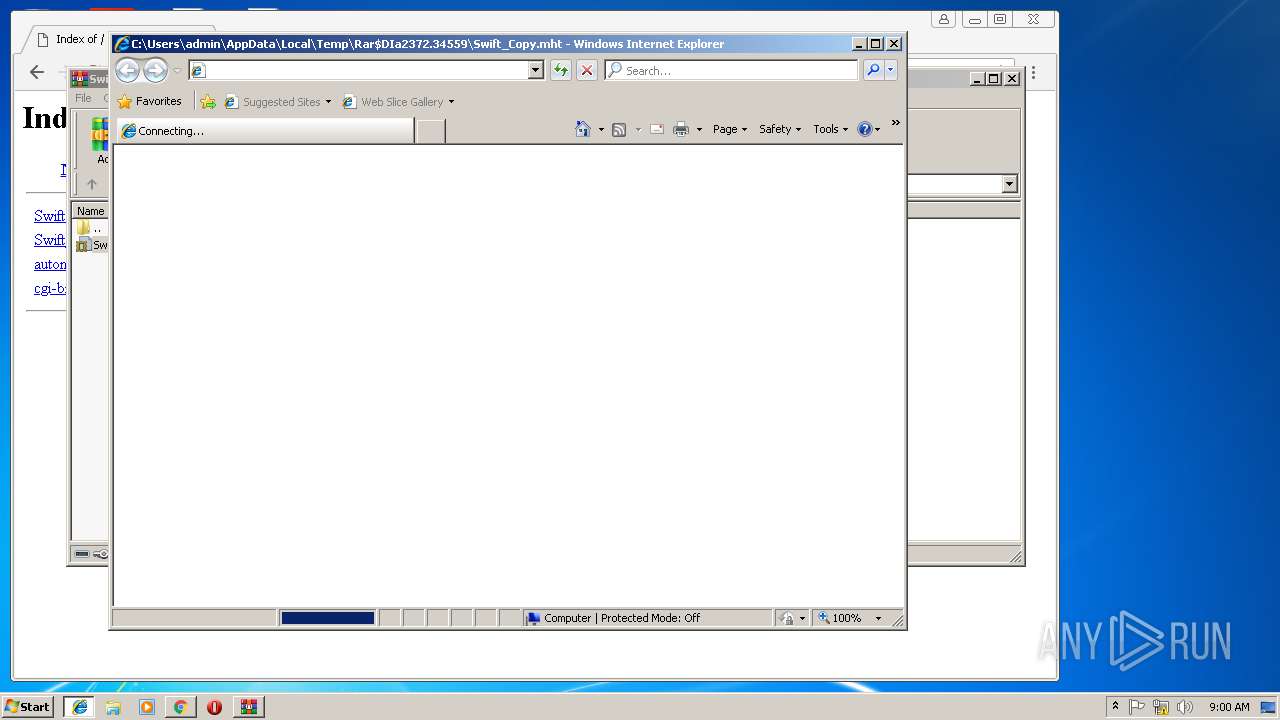
Starts Internet Explorer
- WinRAR.exe (PID: 2372)
Creates files in the user directory
- javaw.exe (PID: 3672)
- WScript.exe (PID: 3432)
- wscript.exe (PID: 2376)
- xcopy.exe (PID: 2764)
- wscript.exe (PID: 4052)
- wscript.exe (PID: 3924)
Executes scripts
- javaw.exe (PID: 3672)
- wscript.exe (PID: 2376)
- cmd.exe (PID: 584)
- cmd.exe (PID: 3844)
- cmd.exe (PID: 3376)
- cmd.exe (PID: 1296)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 1892)
- javaw.exe (PID: 2576)
- cmd.exe (PID: 312)
- cmd.exe (PID: 1692)
- wscript.exe (PID: 4052)
- cmd.exe (PID: 2952)
- cmd.exe (PID: 3360)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 1488)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 252)
- cmd.exe (PID: 3632)
- javaw.exe (PID: 2840)
- wscript.exe (PID: 3924)
- cmd.exe (PID: 2880)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 1016)
- cmd.exe (PID: 1012)
- cmd.exe (PID: 4180)
- cmd.exe (PID: 2232)
- cmd.exe (PID: 1356)
- cmd.exe (PID: 4120)
- cmd.exe (PID: 3084)
Application launched itself
- wscript.exe (PID: 2376)
- wscript.exe (PID: 4052)
- wscript.exe (PID: 3924)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 3988)
- java.exe (PID: 272)
- javaw.exe (PID: 328)
- java.exe (PID: 4004)
- javaw.exe (PID: 2336)
- java.exe (PID: 4012)
- javaw.exe (PID: 2644)
- javaw.exe (PID: 3452)
- java.exe (PID: 2852)
- javaw.exe (PID: 3808)
- java.exe (PID: 2728)
- java.exe (PID: 3512)
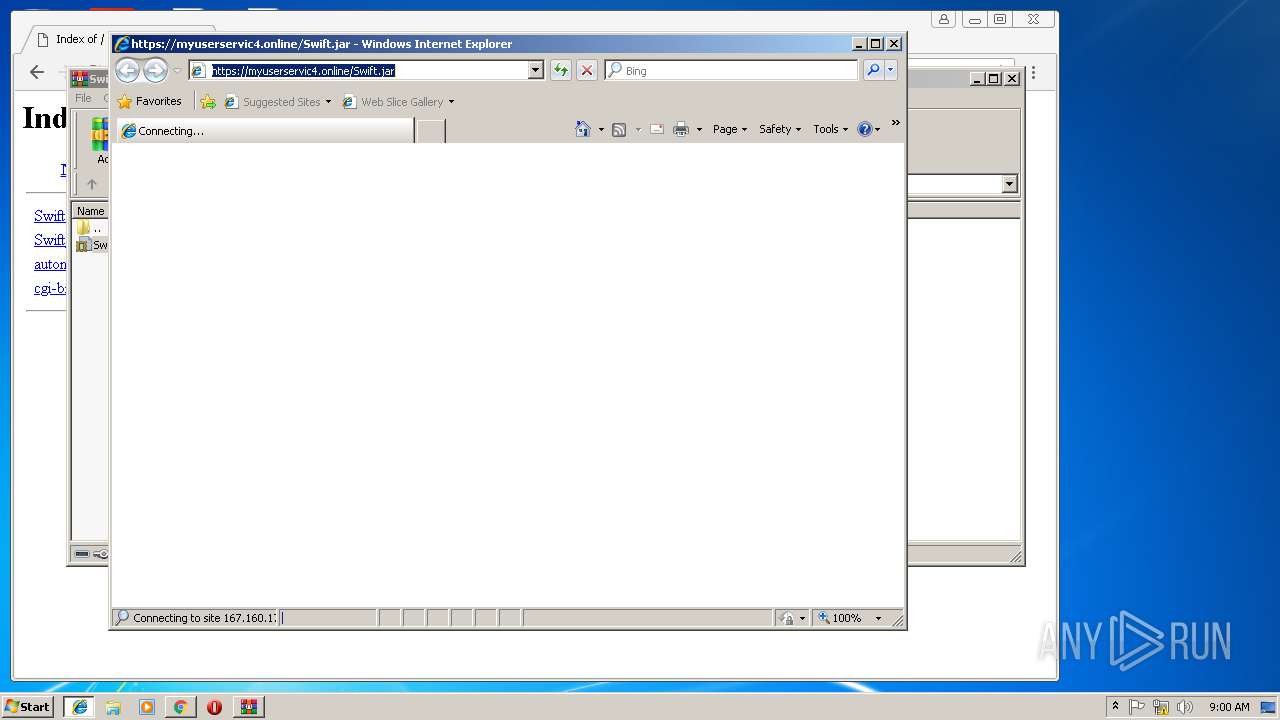
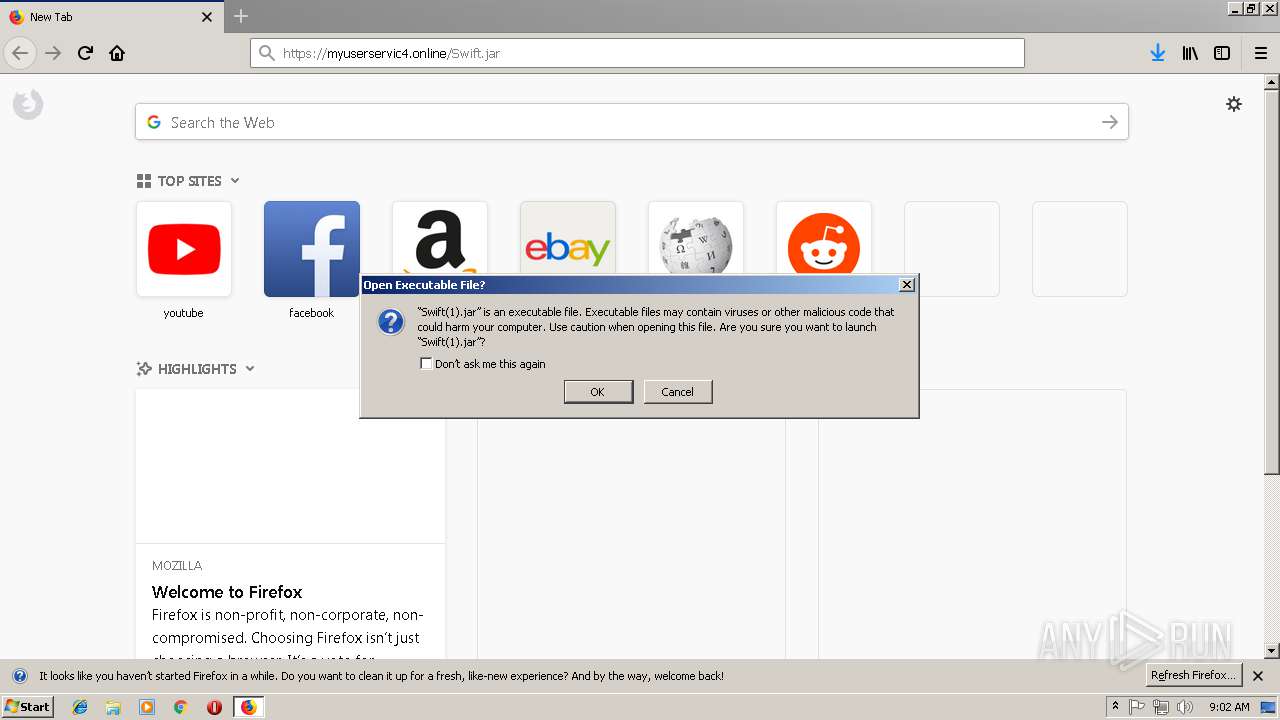
Executes JAVA applets
- chrome.exe (PID: 3860)
- wscript.exe (PID: 2376)
- javaw.exe (PID: 3988)
- wscript.exe (PID: 4052)
- javaw.exe (PID: 2336)
- firefox.exe (PID: 3172)
- javaw.exe (PID: 3452)
- wscript.exe (PID: 3924)
Connects to unusual port
- WScript.exe (PID: 3432)
- WScript.exe (PID: 972)
- javaw.exe (PID: 328)
- javaw.exe (PID: 2644)
- WScript.exe (PID: 3596)
- javaw.exe (PID: 3808)
Executable content was dropped or overwritten
- xcopy.exe (PID: 2764)
- javaw.exe (PID: 328)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 3988)
- javaw.exe (PID: 2336)
- javaw.exe (PID: 3452)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 3988)
- javaw.exe (PID: 2336)
- javaw.exe (PID: 3452)
Starts itself from another location
- javaw.exe (PID: 3988)
- javaw.exe (PID: 2336)
- javaw.exe (PID: 3452)
INFO
Application launched itself
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 3612)
- chrome.exe (PID: 3860)
- iexplore.exe (PID: 1572)
- firefox.exe (PID: 3172)
Reads internet explorer settings
- iexplore.exe (PID: 3392)
- iexplore.exe (PID: 2324)
- iexplore.exe (PID: 624)
- iexplore.exe (PID: 2460)
- iexplore.exe (PID: 3236)
Reads settings of System Certificates
- chrome.exe (PID: 3860)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 2372)
- iexplore.exe (PID: 3612)
- iexplore.exe (PID: 1572)
Changes internet zones settings
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 3612)
- iexplore.exe (PID: 1572)
Reads Internet Cache Settings
- iexplore.exe (PID: 3392)
- iexplore.exe (PID: 624)
- chrome.exe (PID: 3860)
- iexplore.exe (PID: 2460)
- iexplore.exe (PID: 3236)
Reads CPU info
- firefox.exe (PID: 4084)
- firefox.exe (PID: 3172)
- firefox.exe (PID: 2736)
- firefox.exe (PID: 2760)
Creates files in the user directory
- firefox.exe (PID: 3172)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
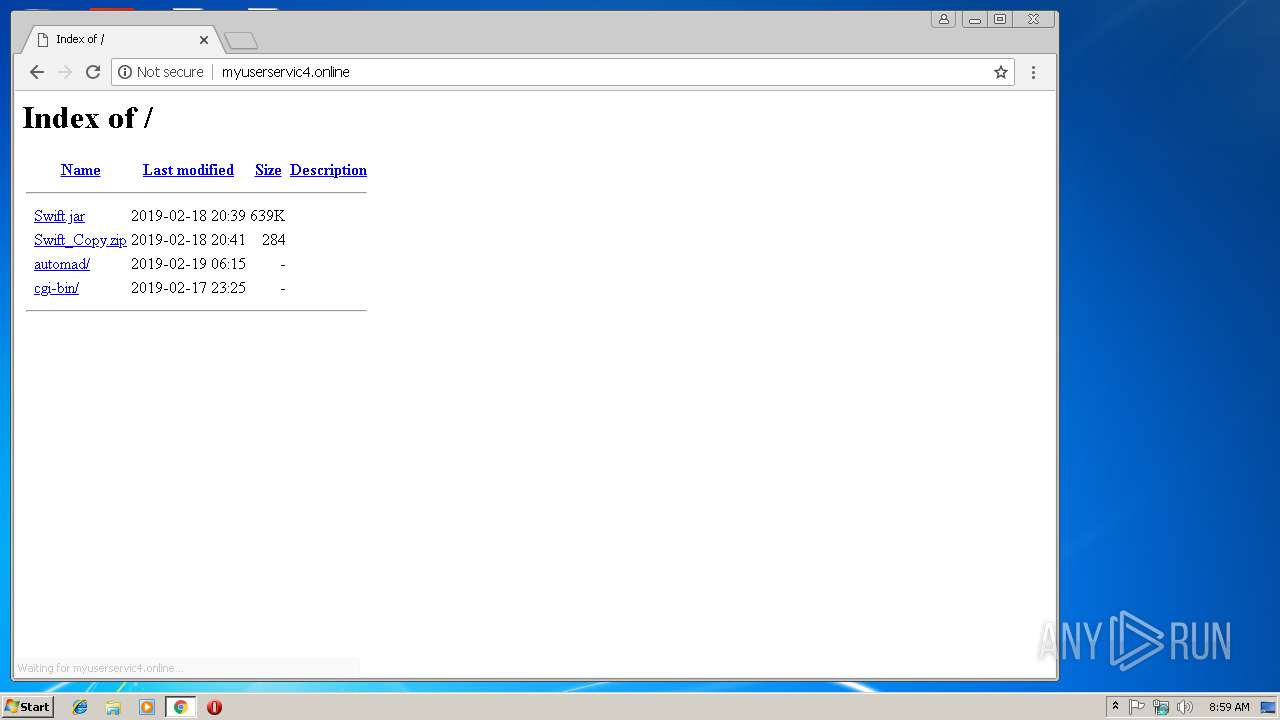
| Title: | Index of / |
|---|
Total processes
208
Monitored processes
121
Malicious processes
25
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive8888069109395361580.vbs | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 272 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -jar C:\Users\admin\AppData\Local\Temp\_0.233055923108832945588497486019276923.class | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 312 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive2814065519847341934.vbs | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 328 | C:\Users\admin\AppData\Roaming\Oracle\bin\javaw.exe -jar C:\Users\admin\gcjkquQGaeh\cLZjkVKTfWI.xfYHdS | C:\Users\admin\AppData\Roaming\Oracle\bin\javaw.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 584 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive6436887922365470745.vbs | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 624 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1572 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 816 | C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 972 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\pfPuoqhvjS.js" | C:\Windows\System32\WScript.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1012 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive3517152797817137392.vbs | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1016 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive8888598081209649541.vbs | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
5 905
Read events
5 556
Write events
341
Delete events
8
Modification events
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {8D63858F-3424-11E9-AA93-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30702000200130008003A002A00FF00 | |||
Executable files
117
Suspicious files
166
Text files
272
Unknown types
60
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF98C934709AB7C9C1.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF52D62BE7F4C715A4.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF54CFBE0028D6B81E.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{8D638590-3424-11E9-AA93-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF020A2F329C6F620A.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{8D63858F-3424-11E9-AA93-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\582c9aa4-a75a-479b-9eb2-343a262f5d89.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
71
DNS requests
84
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
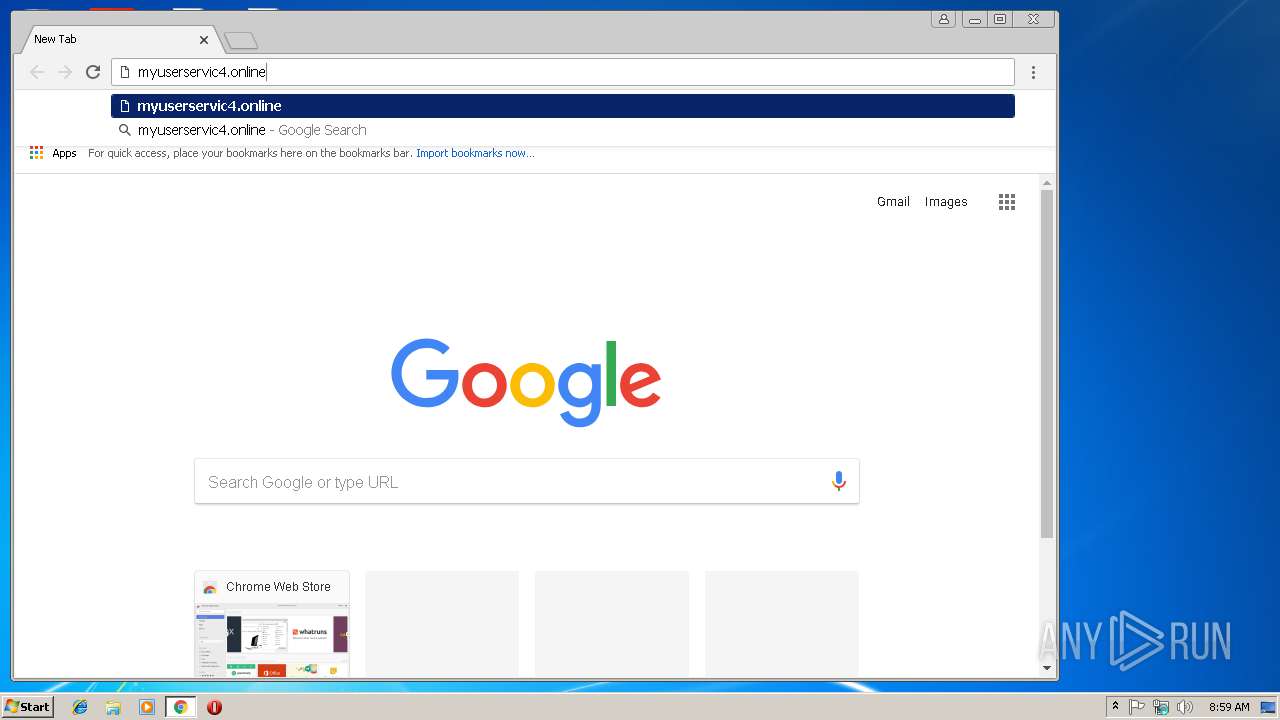
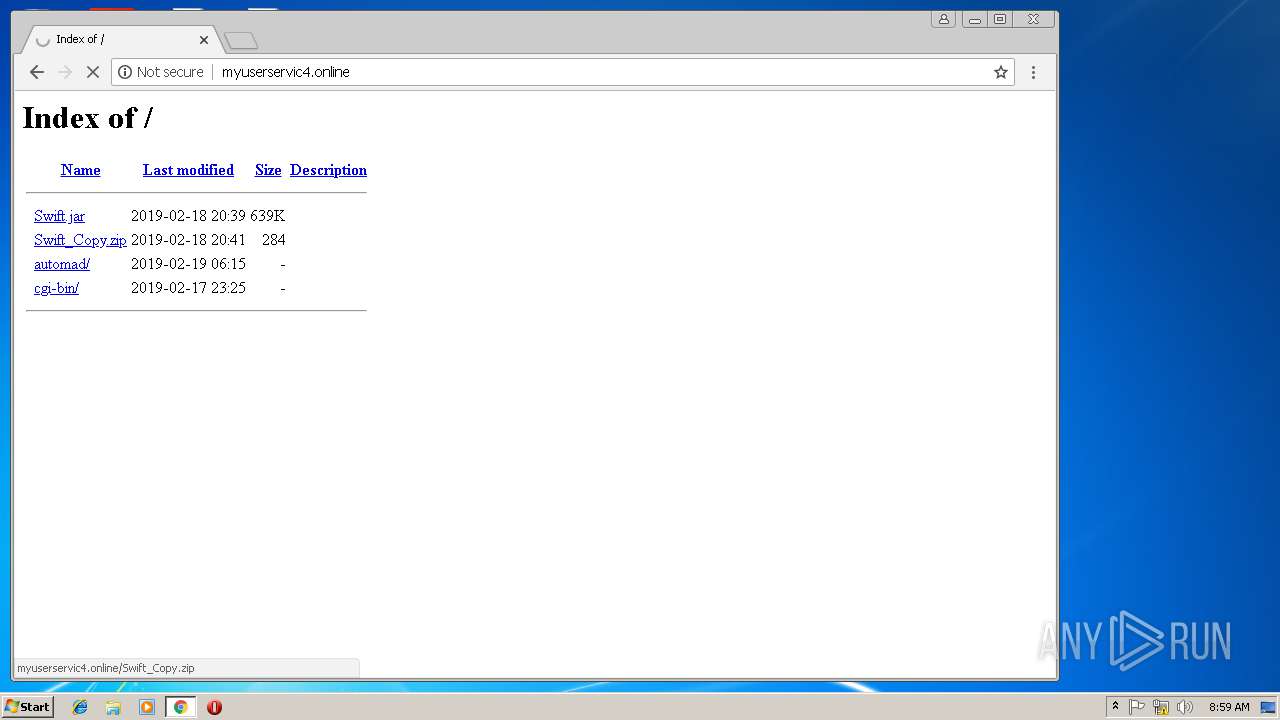
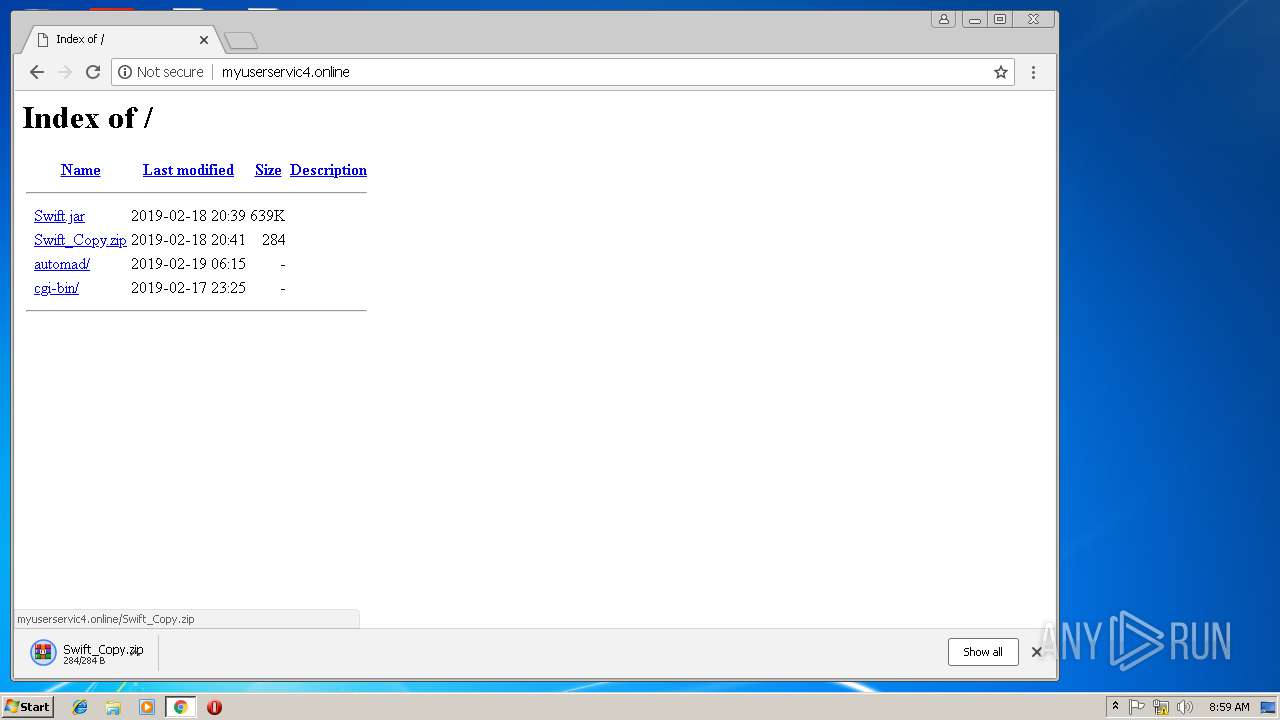
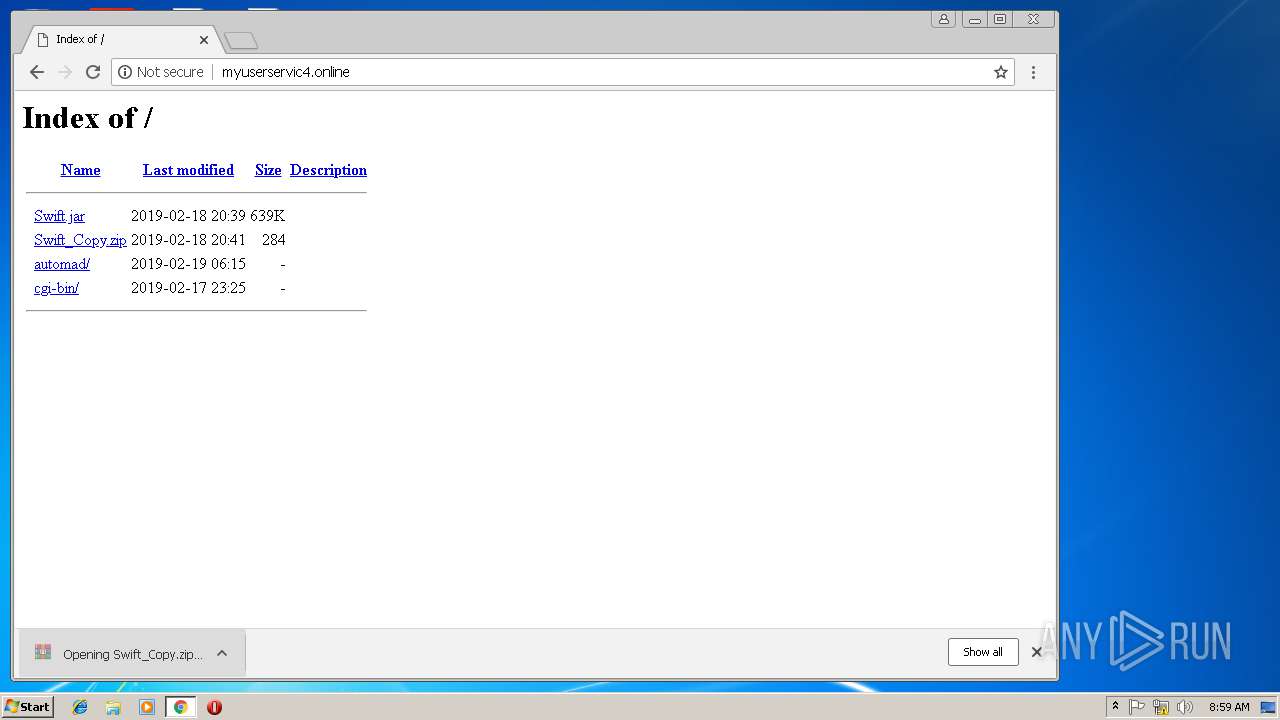
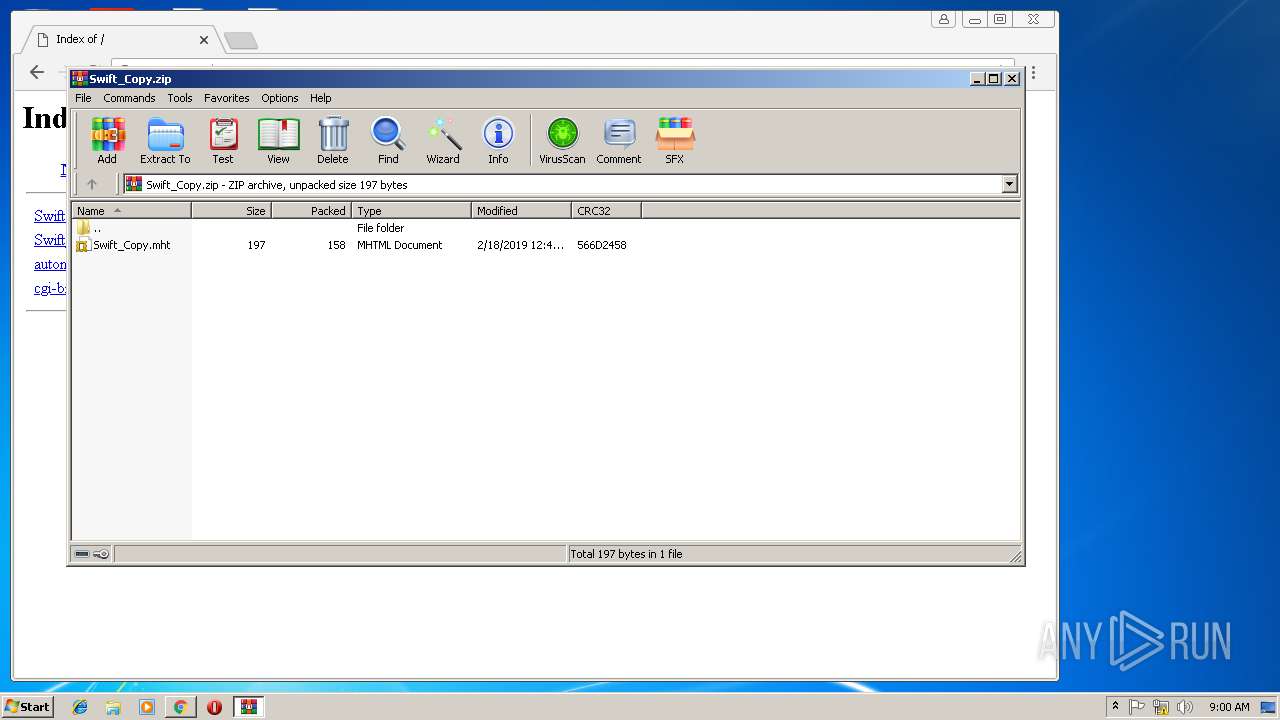
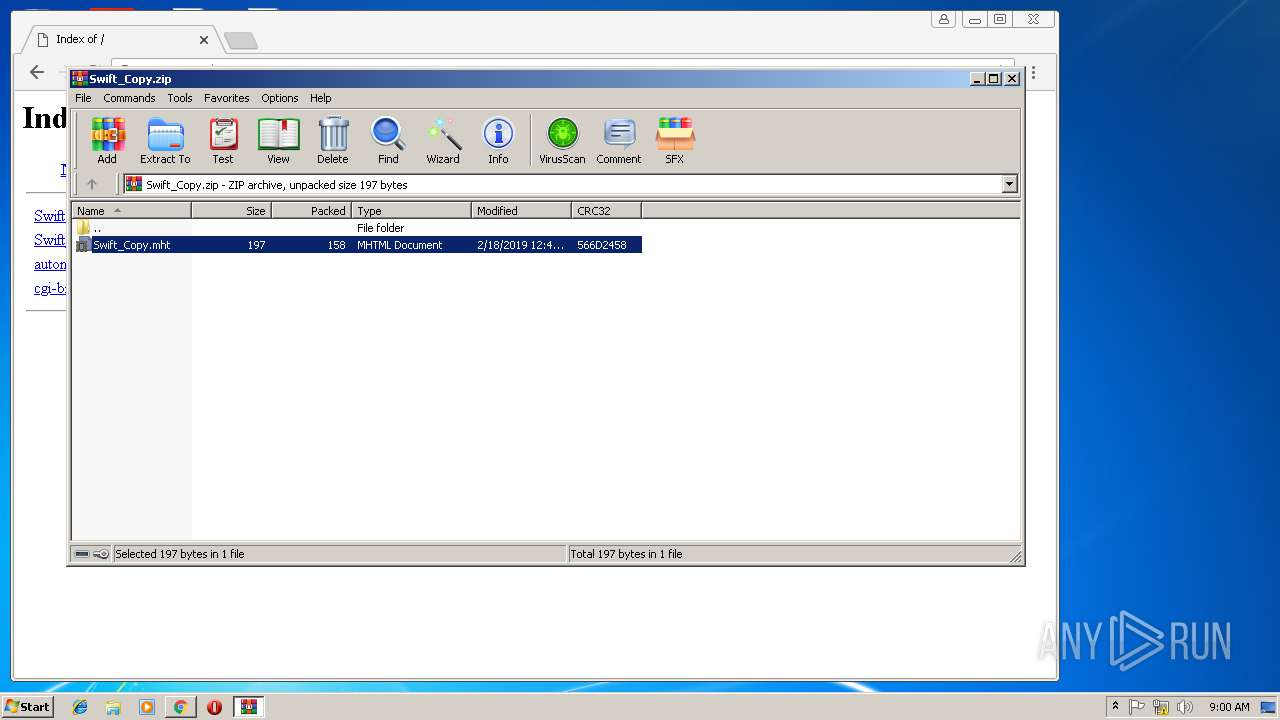
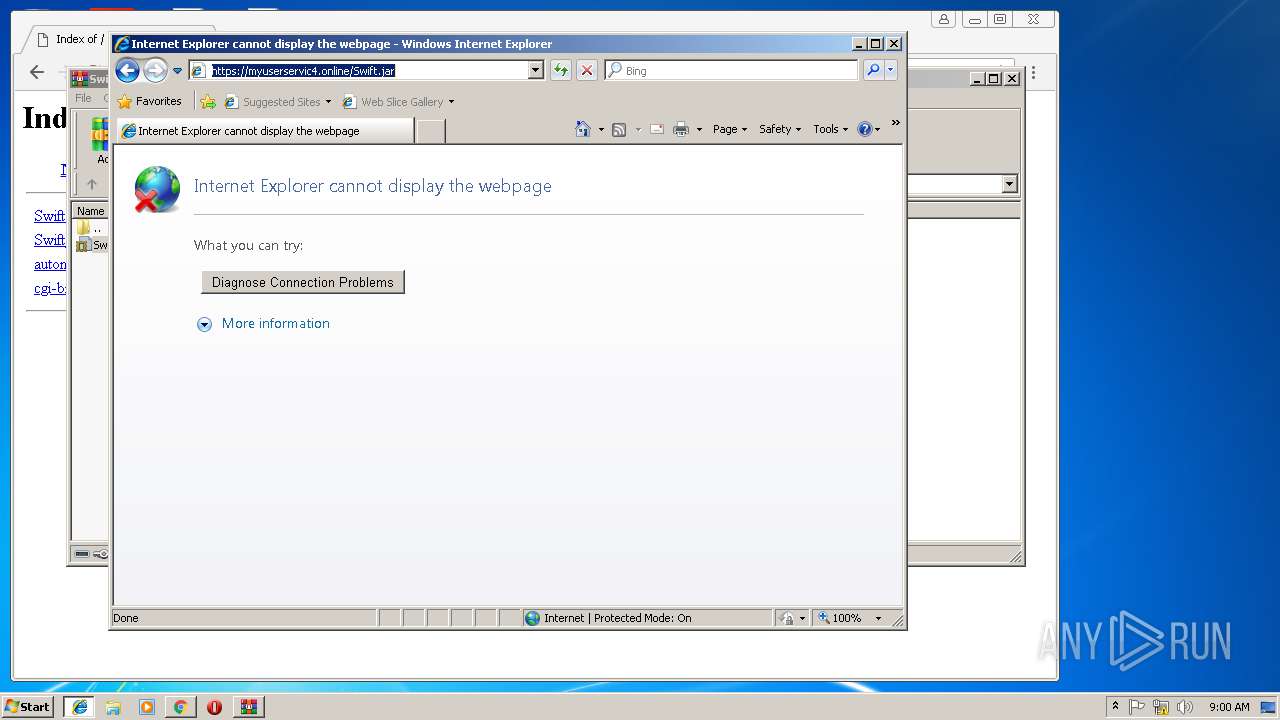
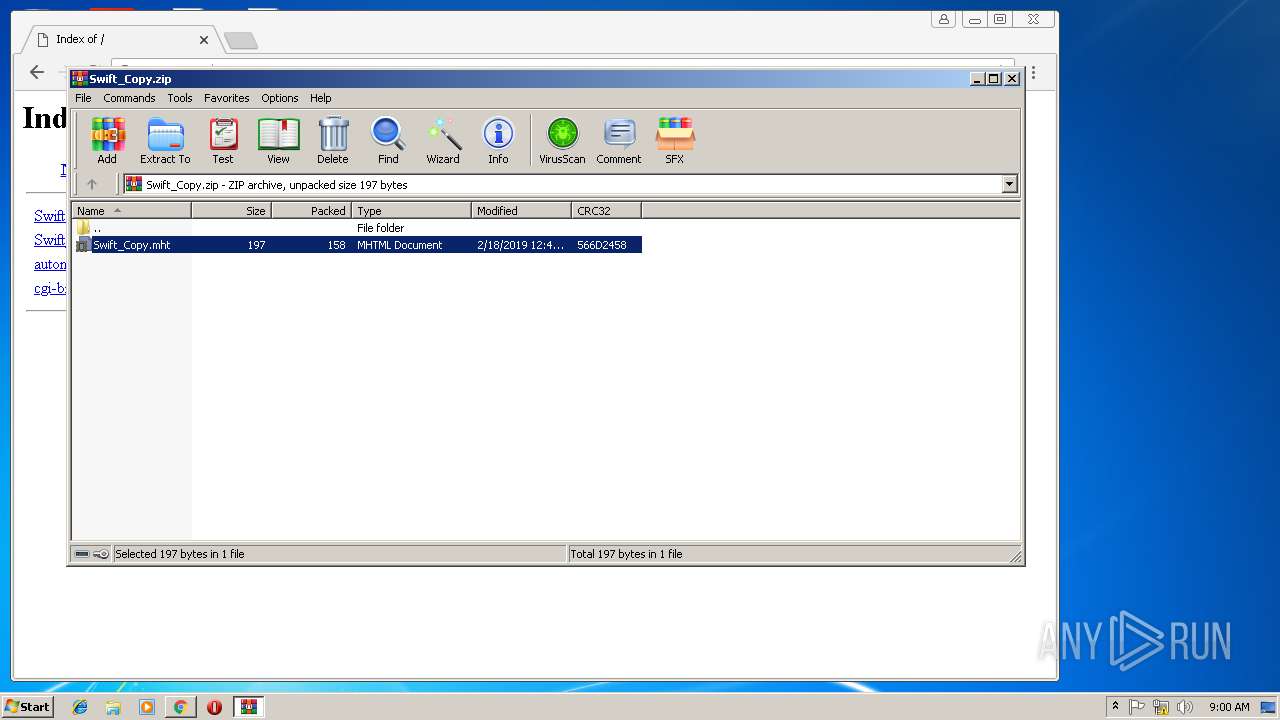
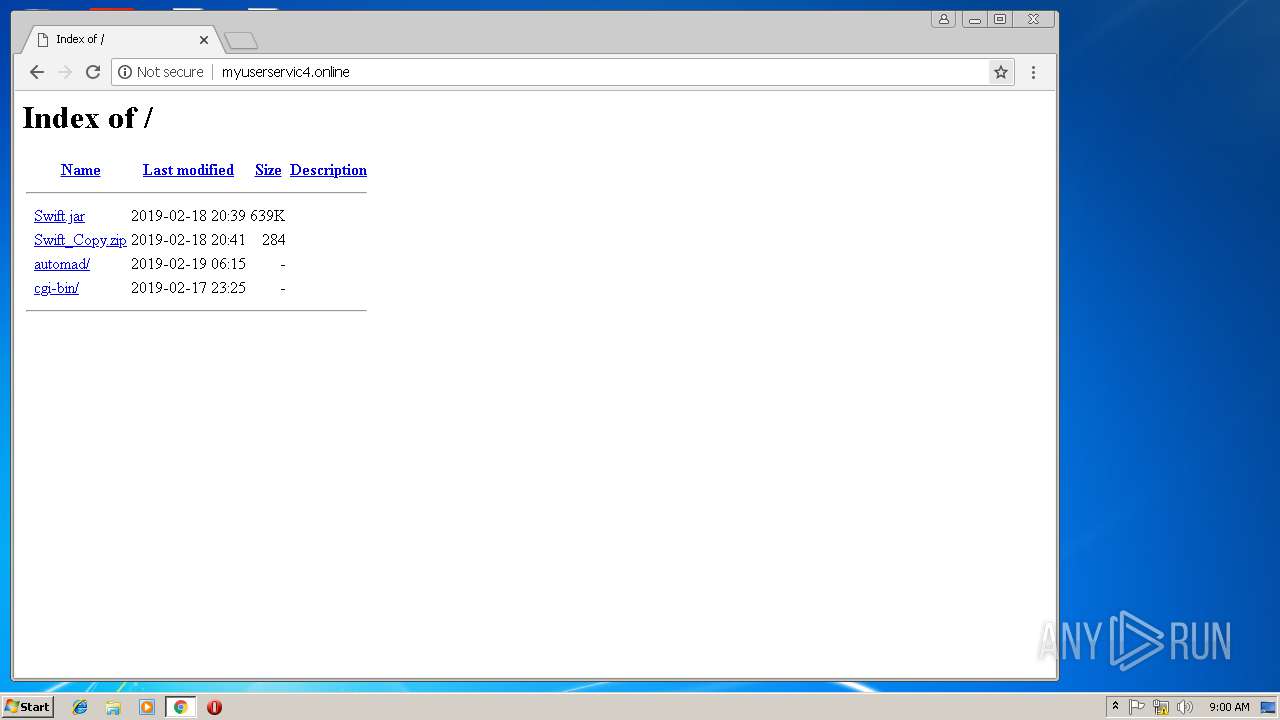
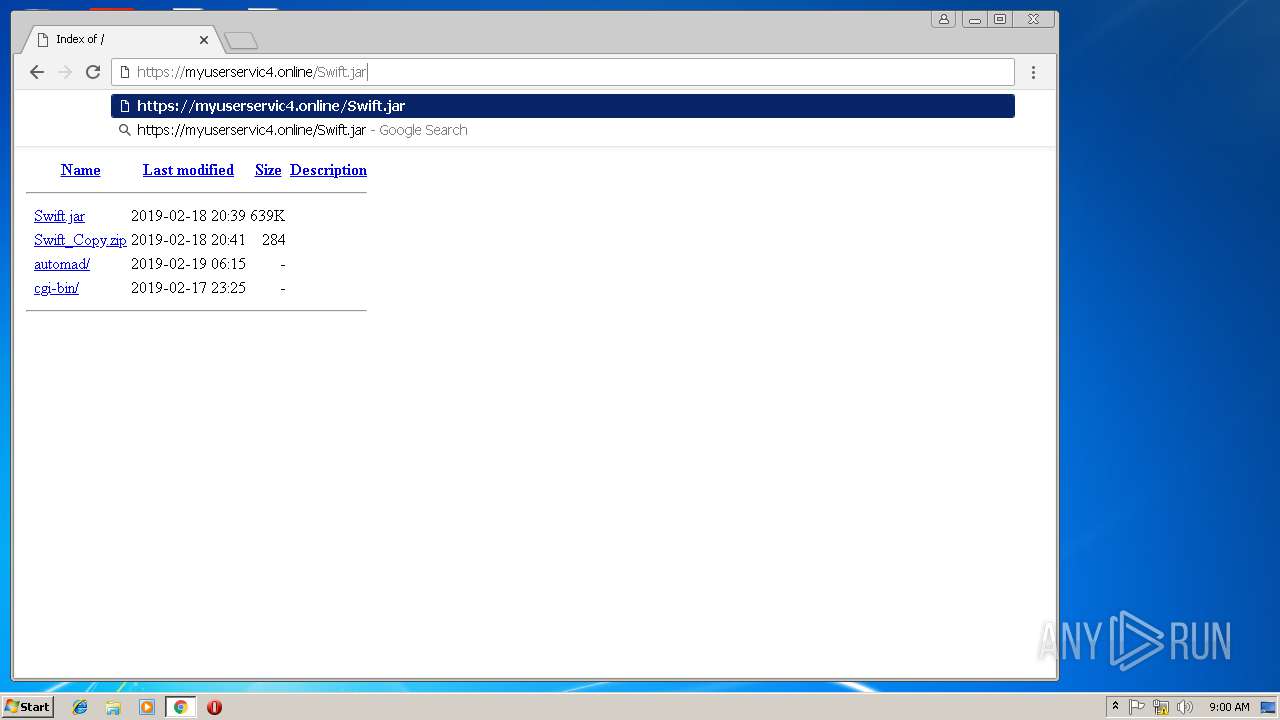
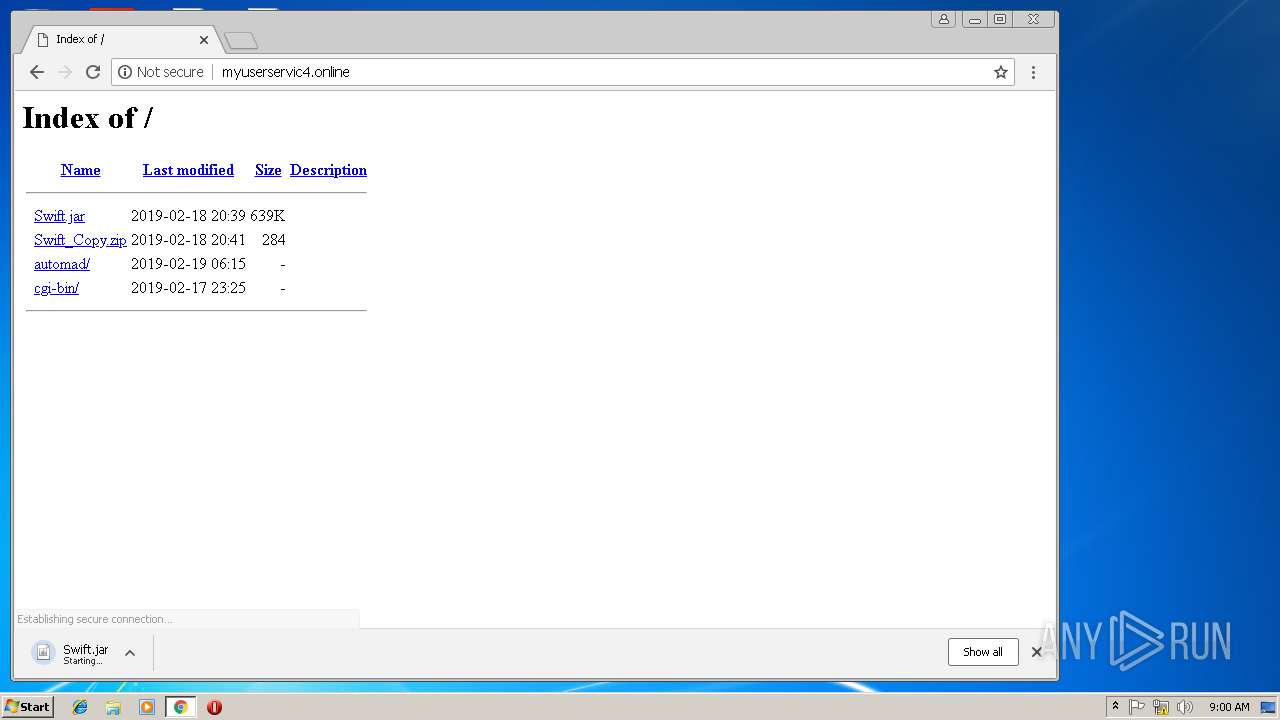
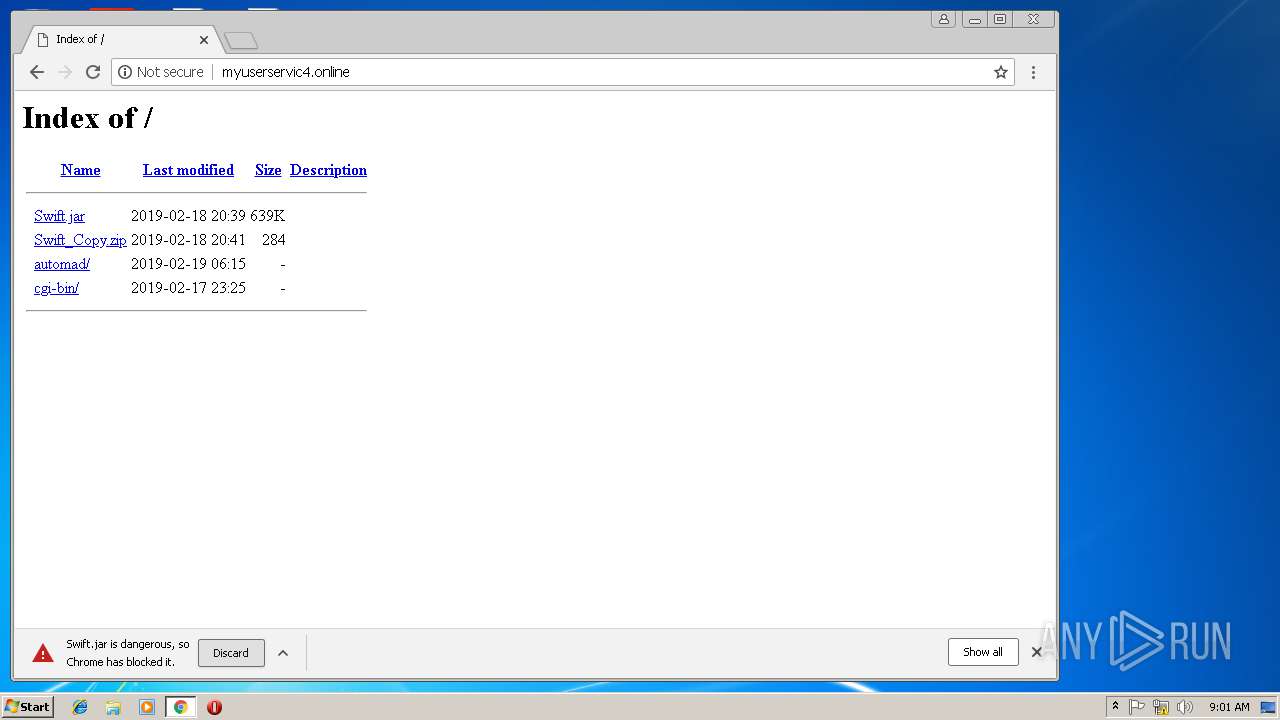
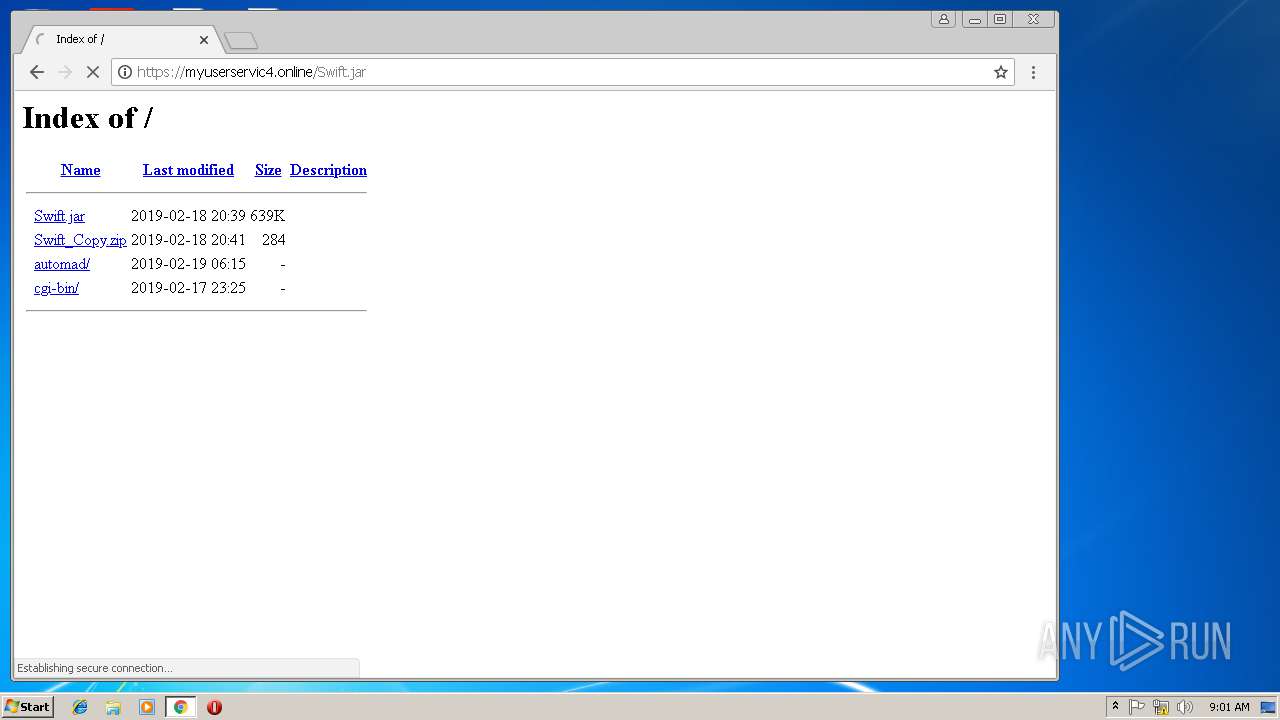
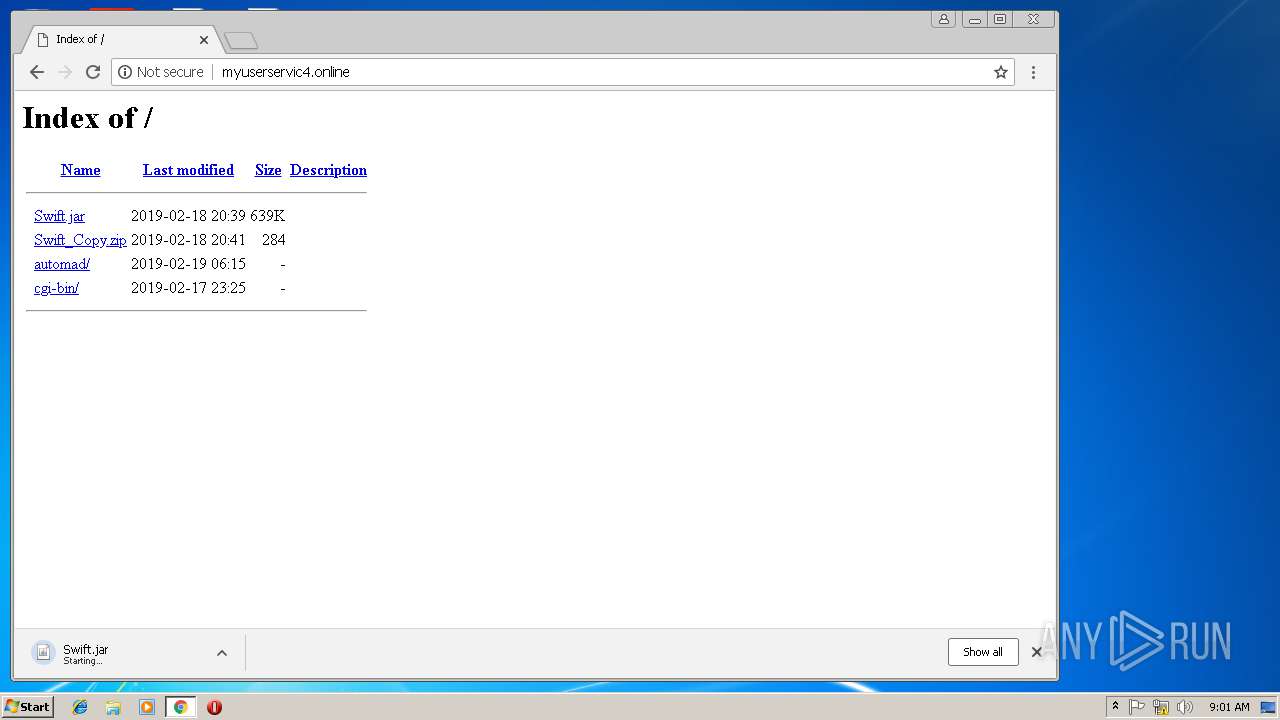
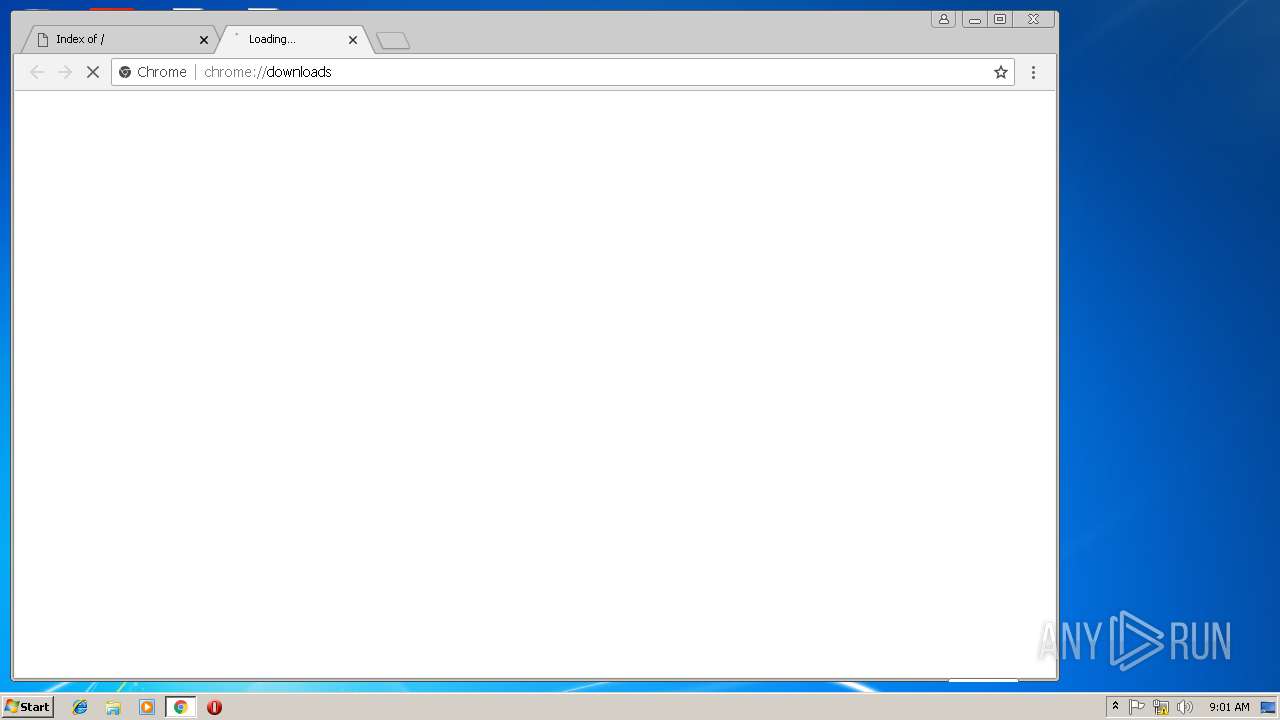
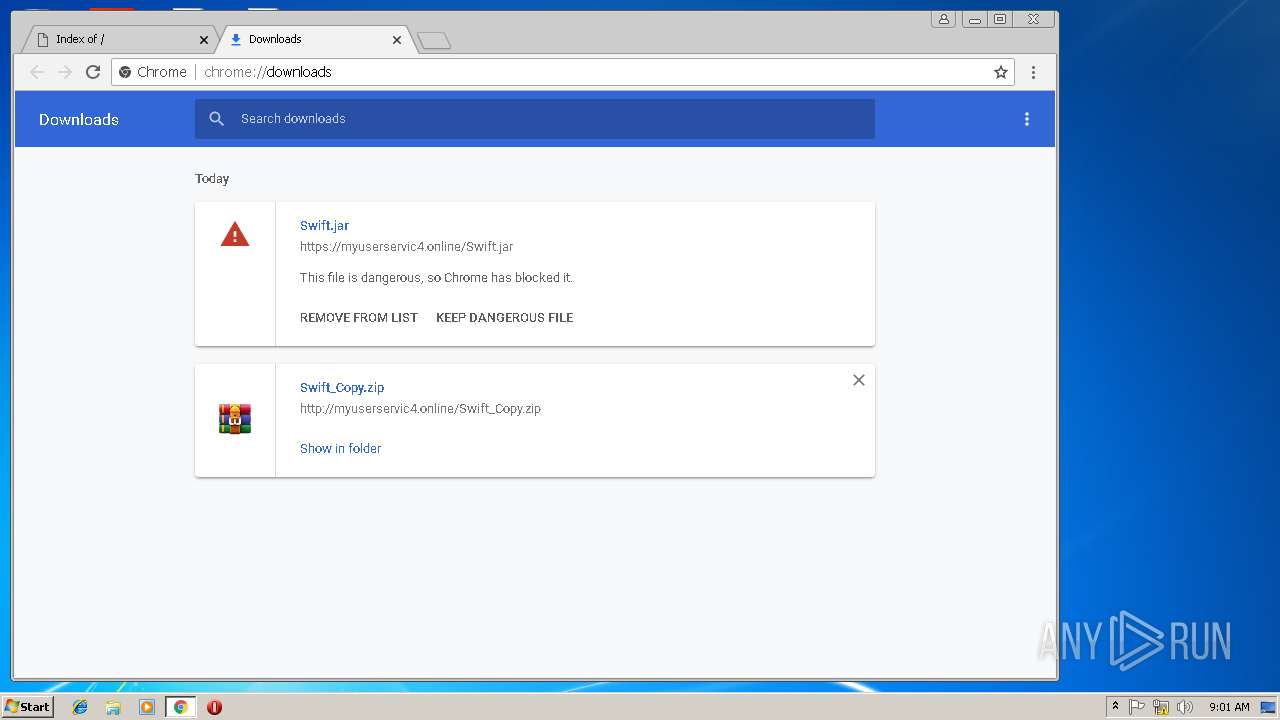
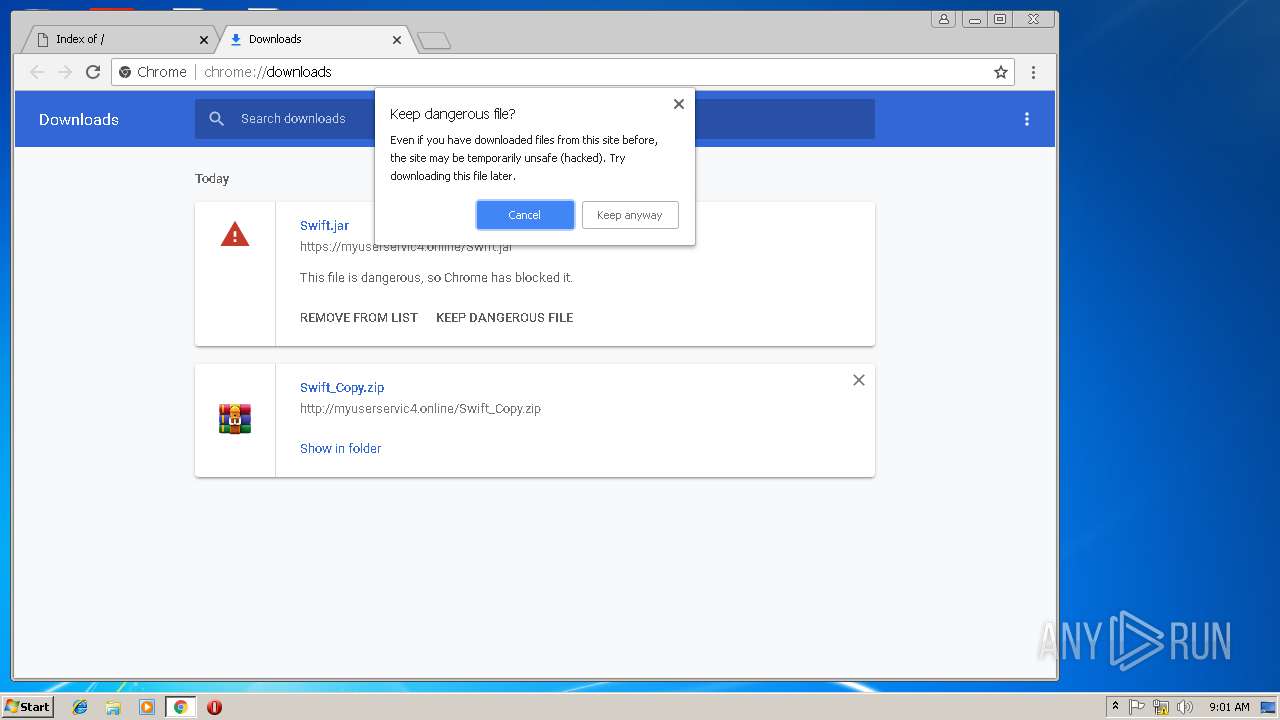
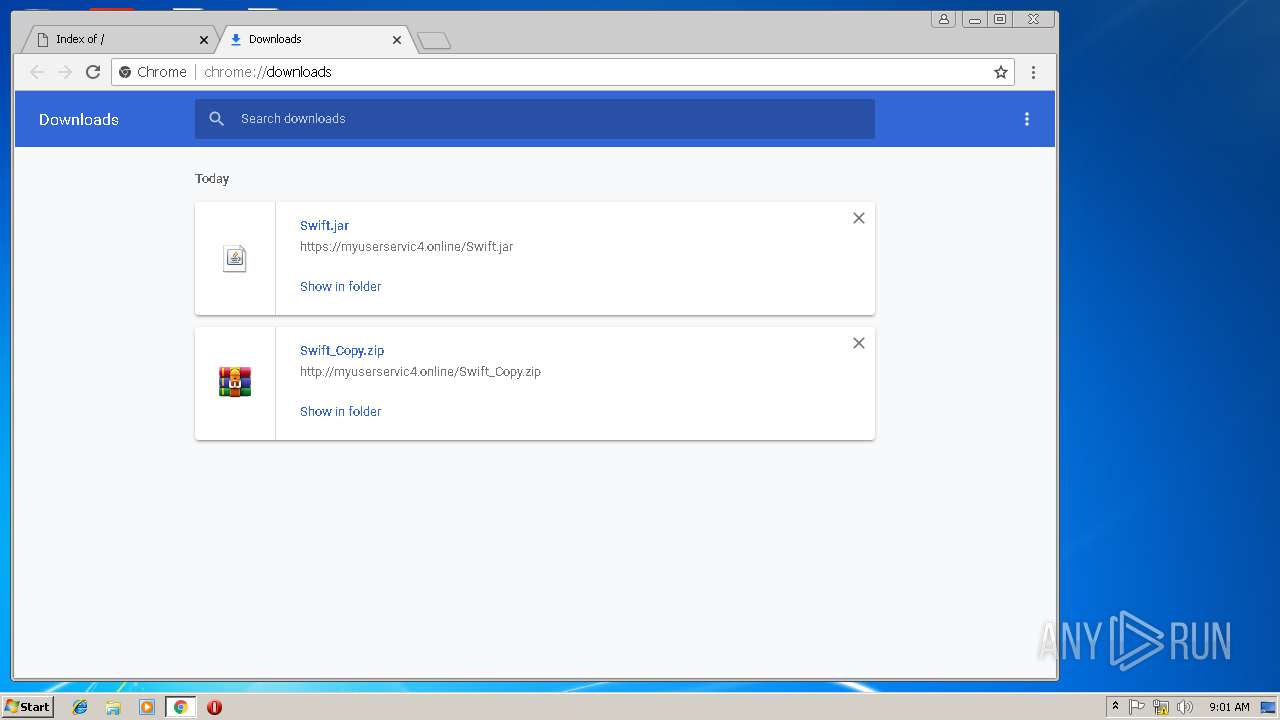
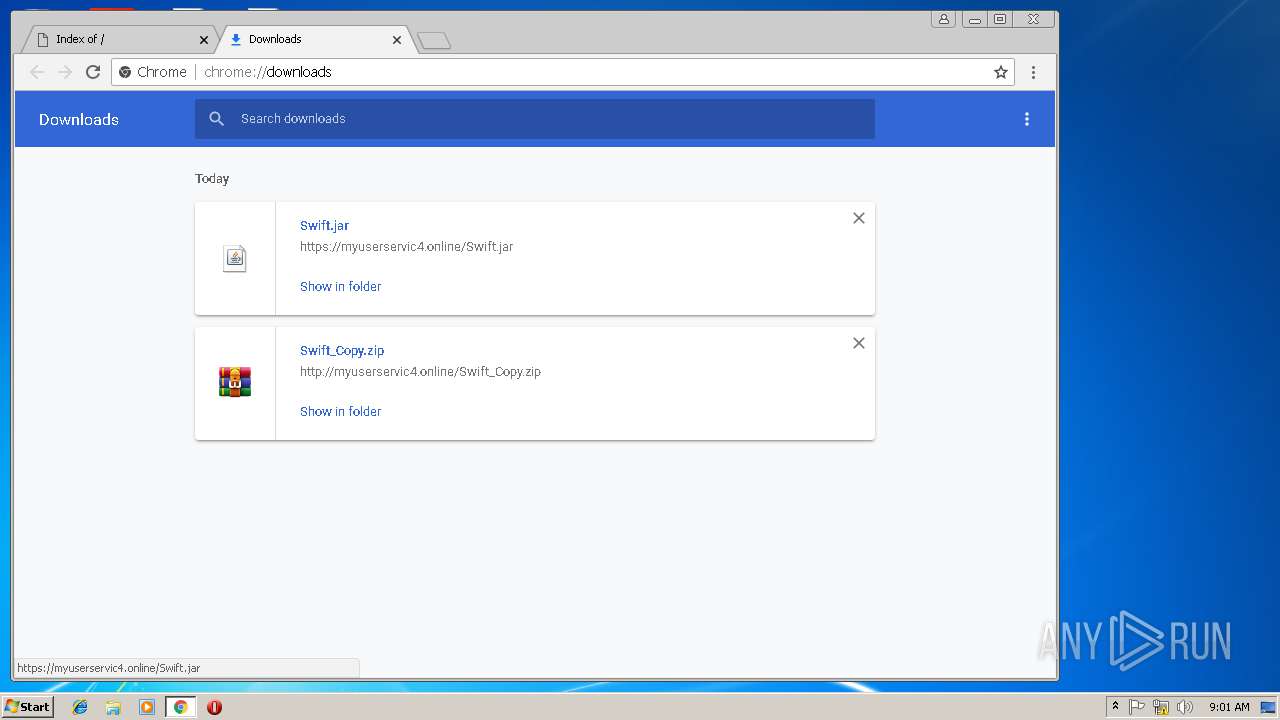
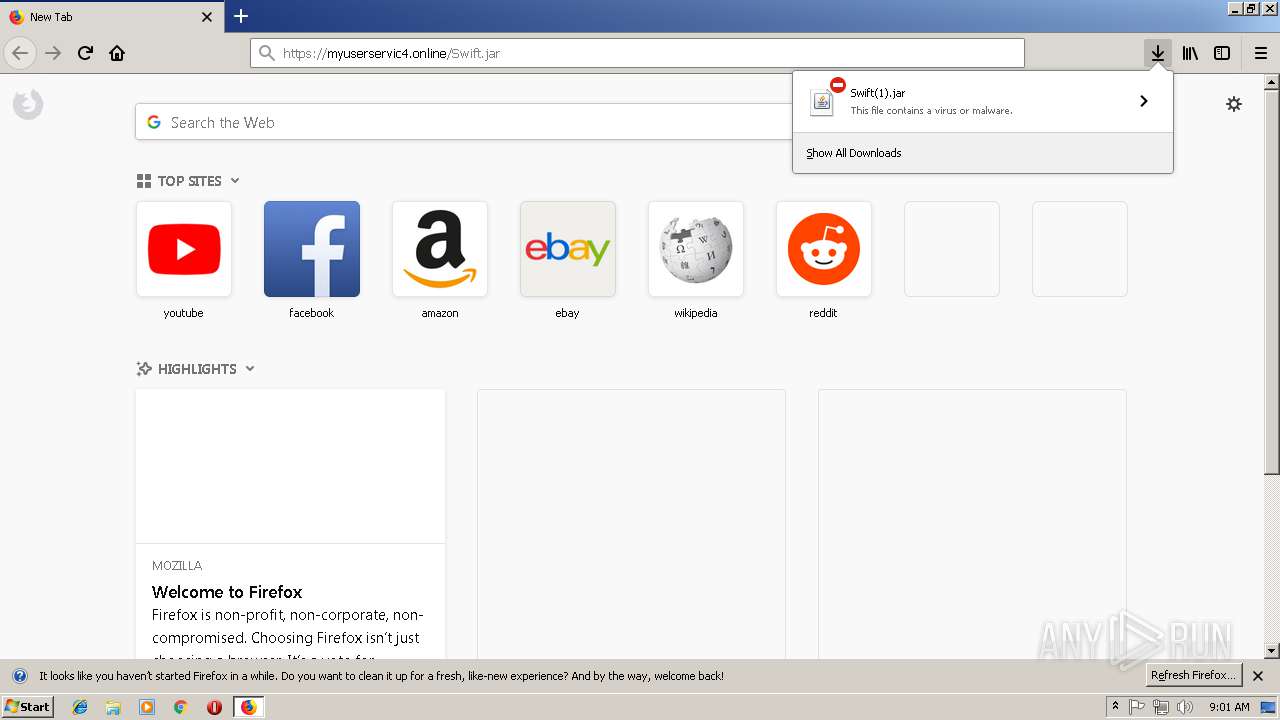
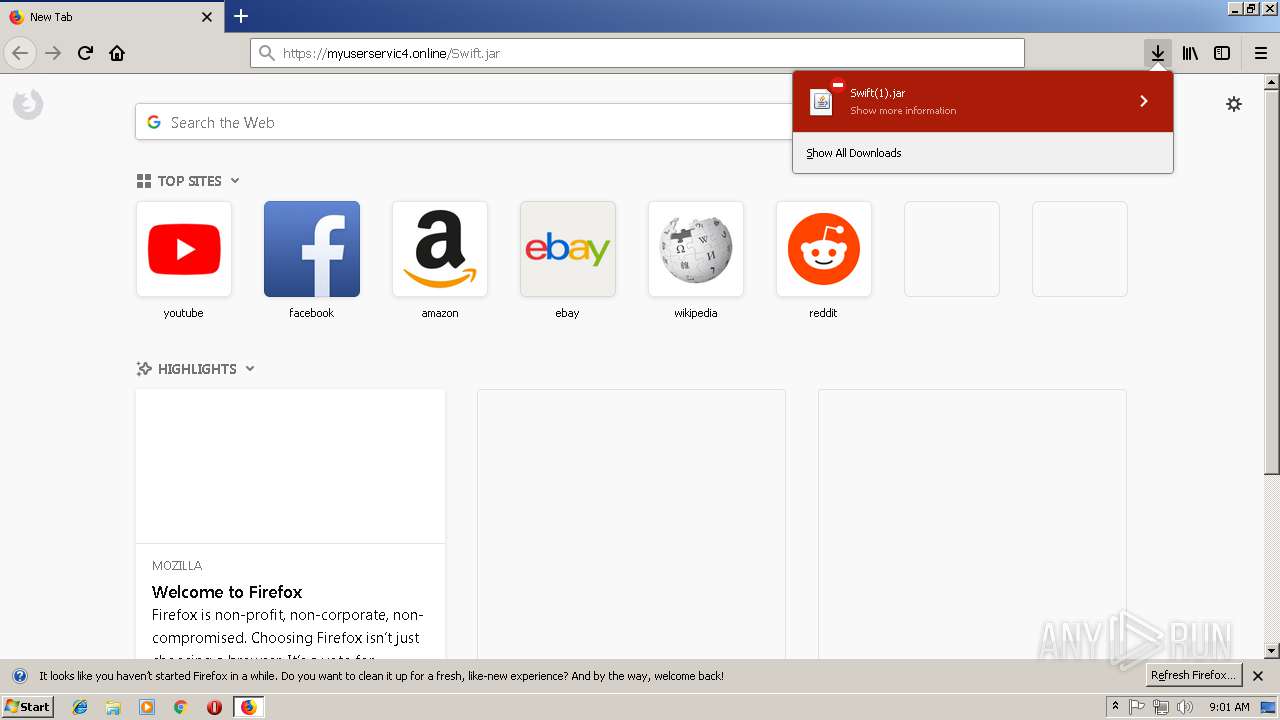
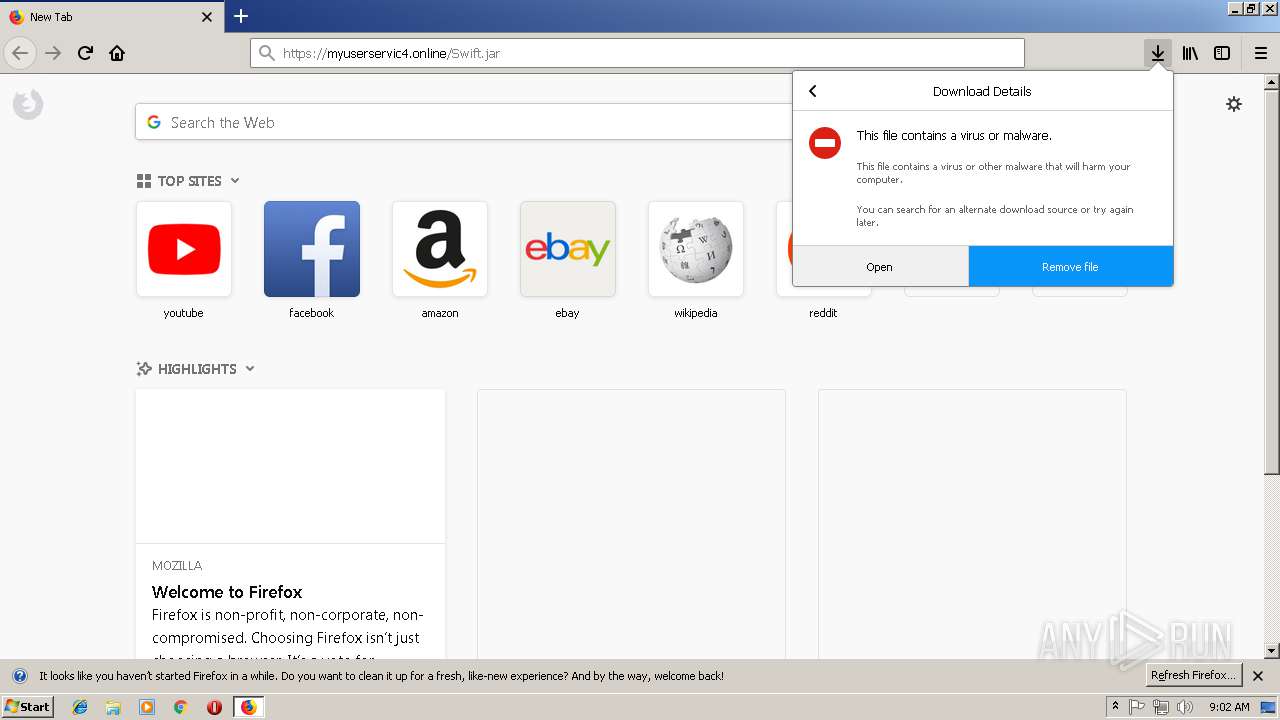
3860 | chrome.exe | GET | — | 167.160.179.181:80 | http://myuserservic4.online/Swift_Copy.zip | US | — | — | unknown |
3860 | chrome.exe | GET | — | 167.160.179.181:80 | http://myuserservic4.online/Swift_Copy.zip | US | — | — | unknown |
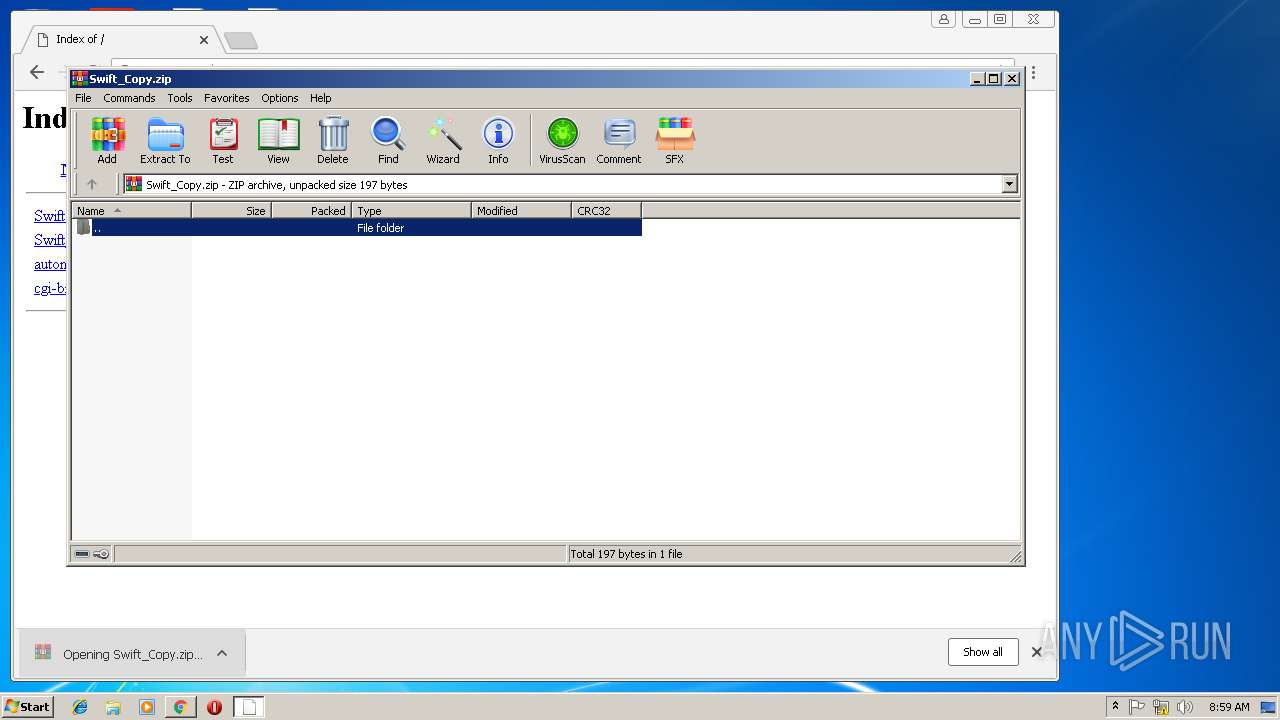
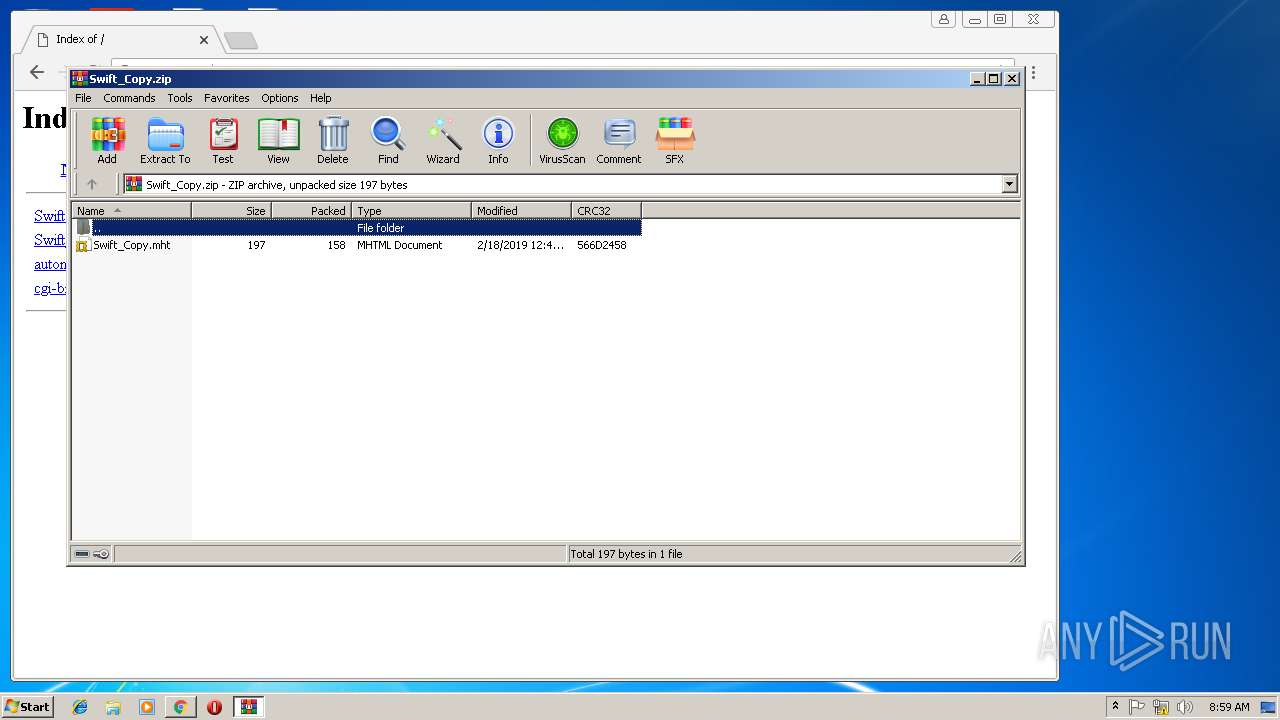
3860 | chrome.exe | GET | 200 | 167.160.179.181:80 | http://myuserservic4.online/Swift_Copy.zip | US | compressed | 284 b | unknown |
3172 | firefox.exe | POST | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3172 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3172 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
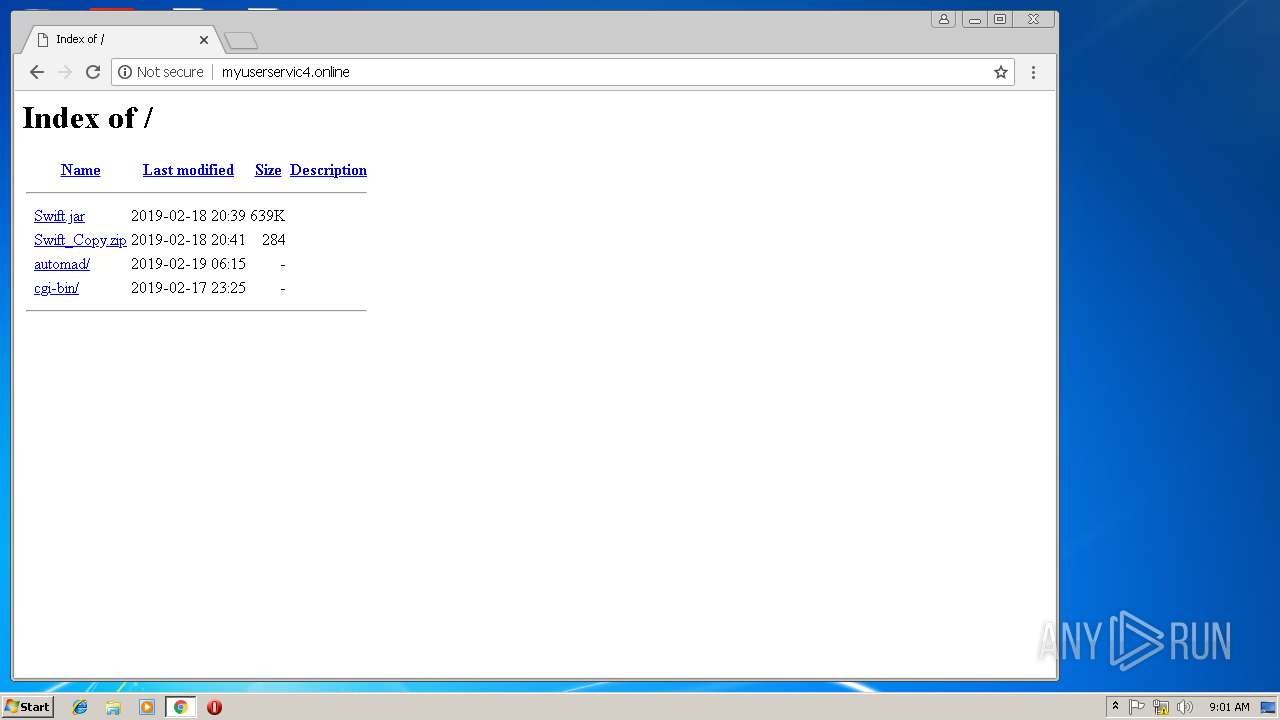
3860 | chrome.exe | GET | 200 | 167.160.179.181:80 | http://myuserservic4.online/ | US | html | 1.13 Kb | unknown |
3172 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2972 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3860 | chrome.exe | GET | 404 | 167.160.179.181:80 | http://myuserservic4.online/favicon.ico | US | html | 328 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2972 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3860 | chrome.exe | 172.217.18.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3860 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3860 | chrome.exe | 167.160.179.181:80 | myuserservic4.online | QuadraNet, Inc | US | unknown |
3860 | chrome.exe | 172.217.21.228:443 | www.google.com | Google Inc. | US | whitelisted |
3860 | chrome.exe | 172.217.22.99:443 | www.google.co.uk | Google Inc. | US | whitelisted |
3860 | chrome.exe | 172.217.16.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3860 | chrome.exe | 172.217.18.174:443 | ogs.google.com | Google Inc. | US | whitelisted |
2460 | iexplore.exe | 167.160.179.181:443 | myuserservic4.online | QuadraNet, Inc | US | unknown |
3612 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.co.uk |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
328 | javaw.exe | A Network Trojan was detected | ET TROJAN Possible Adwind SSL Cert (assylias.Inc) |
328 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.Java.Adwind.cu |
2644 | javaw.exe | A Network Trojan was detected | ET TROJAN Possible Adwind SSL Cert (assylias.Inc) |
2644 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.Java.Adwind.cu |
3808 | javaw.exe | A Network Trojan was detected | ET TROJAN Possible Adwind SSL Cert (assylias.Inc) |
3808 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.Java.Adwind.cu |