| File name: | plugx |
| Full analysis: | https://app.any.run/tasks/e13474af-a4e8-4d94-9595-199e7f9e9ae3 |
| Verdict: | Malicious activity |
| Threats: | PlugX is a remote access trojan that is used extensively by Chinese APTs. The malware is primarily employed for spying on victims and can perform a variety of malicious activities, such as logging users’ keystrokes and exfiltrating information from browsers. |
| Analysis date: | March 31, 2020, 10:10:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 83CE36926FEEE5093D3DE26BAB01A582 |
| SHA1: | B858682AC8649B9D350B5FF968AD1A208D1B053A |
| SHA256: | 3D95D0AA878C13F197EF2BCCEF5DBD2633F8DE3CDF9691C46E264CCE2D241F9A |
| SSDEEP: | 3072:HyEqlSTXxTvOtvNbCGGezbcOl4gi939EdO0CYREqRuFFBOzDdnRBz:HyXS7xTvOtNbCN0bggi9teJkEzhz |
MALICIOUS
Application was dropped or rewritten from another process
- NvSmart.exe (PID: 2372)
- NvSmart.exe (PID: 572)
- NvSmart.exe (PID: 3424)
Loads dropped or rewritten executable
- NvSmart.exe (PID: 2372)
- sysprep.exe (PID: 820)
- NvSmart.exe (PID: 572)
- NvSmart.exe (PID: 3424)
Uses SVCHOST.EXE for hidden code execution
- NvSmart.exe (PID: 572)
Connects to CnC server
- svchost.exe (PID: 2560)
PLUGX was detected
- svchost.exe (PID: 2560)
SUSPICIOUS
Executable content was dropped or overwritten
- plugx.exe (PID: 3052)
- DllHost.exe (PID: 3380)
- NvSmart.exe (PID: 3424)
Executed as Windows Service
- NvSmart.exe (PID: 572)
Creates files in the program directory
- NvSmart.exe (PID: 2372)
- plugx.exe (PID: 3052)
- NvSmart.exe (PID: 3424)
Creates files in the Windows directory
- sysprep.exe (PID: 820)
- DllHost.exe (PID: 3380)
Executed via COM
- DllHost.exe (PID: 3380)
- DllHost.exe (PID: 1836)
Executed via WMI
- NvSmart.exe (PID: 3424)
Removes files from Windows directory
- DllHost.exe (PID: 1836)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:06:08 16:06:24+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 4096 |
| InitializedDataSize: | 212992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x10b0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Jun-2012 14:06:24 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 08-Jun-2012 14:06:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000000B8 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.452698 |
.rdata | 0x00002000 | 0x000000DE | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.345678 |
.data | 0x00003000 | 0x00026CF3 | 0x00027000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92024 |
.rsrc | 0x0002A000 | 0x0000BE30 | 0x0000C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.24883 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.89005 | 744 | UNKNOWN | Chinese - PRC | RT_ICON |
2 | 2.54353 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 4.35478 | 3752 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 5.17501 | 2216 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 3.47748 | 1384 | UNKNOWN | Chinese - PRC | RT_ICON |
6 | 2.83156 | 9640 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 1.58455 | 56 | UNKNOWN | Chinese - PRC | RT_STRING |
8 | 4.05874 | 1128 | UNKNOWN | Chinese - PRC | RT_ICON |
9 | 2.89005 | 744 | UNKNOWN | Chinese - PRC | RT_ICON |
10 | 2.54353 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
50
Monitored processes
10
Malicious processes
3
Suspicious processes
2
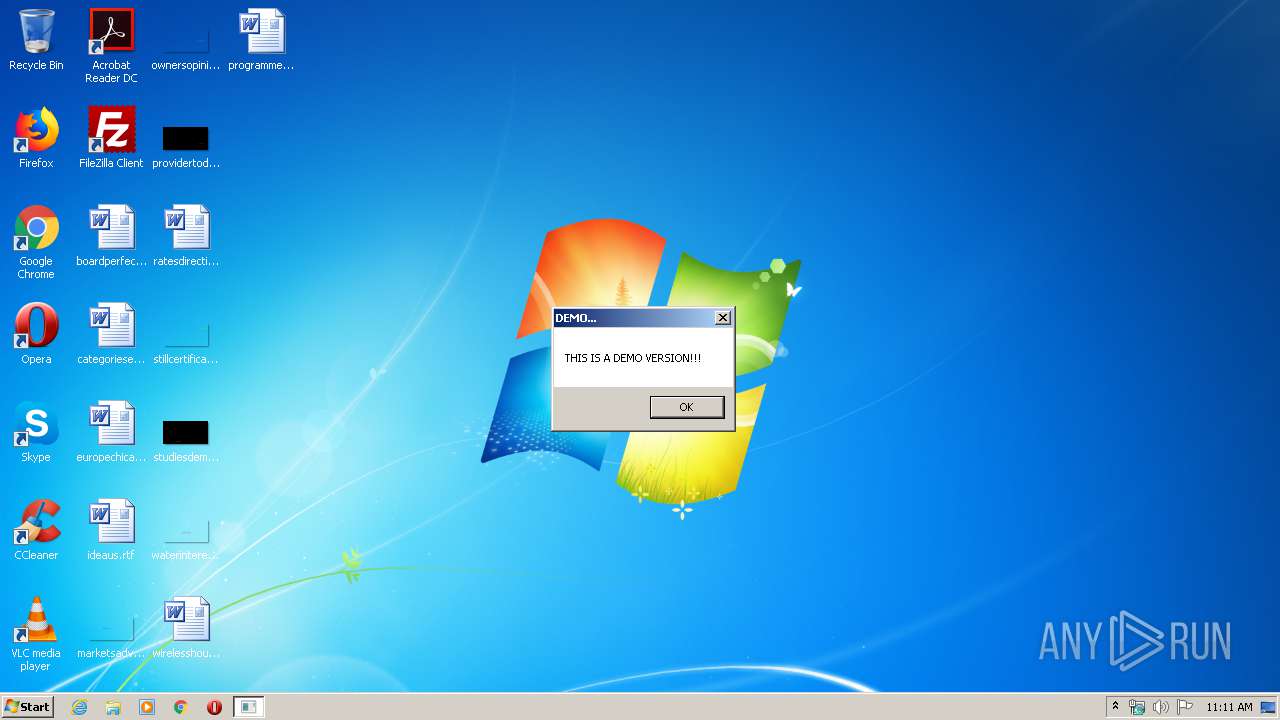
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\ProgramData\SxS\NvSmart.exe" 200 0 | C:\ProgramData\SxS\NvSmart.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: NVIDIA Smart Maximise Helper Host Exit code: 1223 Version: 6.14.10.100.01 Modules
| |||||||||||||||
| 820 | "C:\Windows\system32\sysprep\sysprep.exe" "C:\ProgramData\SxS\NvSmart.exe" 100 3052 | C:\Windows\system32\sysprep\sysprep.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: System Preparation Tool Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1836 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2372 | "C:\ProgramData\SxS\NvSmart.exe" 100 3052 | C:\ProgramData\SxS\NvSmart.exe | sysprep.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: NVIDIA Smart Maximise Helper Host Exit code: 1223 Version: 6.14.10.100.01 Modules
| |||||||||||||||
| 2560 | C:\Windows\system32\svchost.exe 201 0 | C:\Windows\system32\svchost.exe | NvSmart.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2720 | C:\Windows\system32\msiexec.exe 209 2560 | C:\Windows\system32\msiexec.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3052 | "C:\Users\admin\AppData\Local\Temp\plugx.exe" | C:\Users\admin\AppData\Local\Temp\plugx.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3380 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3424 | "C:\ProgramData\SxS\NvSmart.exe" 100 3052 | C:\ProgramData\SxS\NvSmart.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: NVIDIA Smart Maximise Helper Host Exit code: 1223 Version: 6.14.10.100.01 Modules
| |||||||||||||||
| 3756 | C:\Windows\system32\msiexec.exe UAC | C:\Windows\system32\msiexec.exe | — | NvSmart.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
144
Read events
137
Write events
7
Delete events
0
Modification events
| (PID) Process: | (3756) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3756) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2560) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\FAST |
| Operation: | write | Name: | CLSID |
Value: 38004100430045004500320034004200450035003900380037004600430042000000 | |||
| (PID) Process: | (2560) svchost.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2560) svchost.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
4
Suspicious files
6
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3424 | NvSmart.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\SxS\bug.log | binary | |
MD5:— | SHA256:— | |||
| 2372 | NvSmart.exe | C:\ProgramData\SxS\bug.log | binary | |
MD5:— | SHA256:— | |||
| 2560 | svchost.exe | C:\ProgramData\SxS\bug.log | binary | |
MD5:— | SHA256:— | |||
| 820 | sysprep.exe | C:\Windows\System32\sysprep\Panther\setupact.log | text | |
MD5:— | SHA256:— | |||
| 820 | sysprep.exe | C:\Windows\System32\sysprep\Panther\diagerr.xml | text | |
MD5:67FC5B9D0957C4FBB37376DE49A2B170 | SHA256:8ADE5E7080E6D5337CA9B4BD31C9963DC556406189B53263DD5B37A9FBBBA523 | |||
| 3380 | DllHost.exe | C:\Windows\System32\sysprep\CRYPTBASE.DLL | executable | |
MD5:52DF5C2C07433E2A8F054C2347ACB3B4 | SHA256:DC09091E5D0CE03C6144748F17BD636F2F0B2CA56F88B550C1D48860596DBDB1 | |||
| 3424 | NvSmart.exe | C:\ProgramData\SxS\UAC.TMP | executable | |
MD5:52DF5C2C07433E2A8F054C2347ACB3B4 | SHA256:DC09091E5D0CE03C6144748F17BD636F2F0B2CA56F88B550C1D48860596DBDB1 | |||
| 3052 | plugx.exe | C:\ProgramData\SxS\NvSmart.exe | executable | |
MD5:09B8B54F78A10C435CD319070AA13C28 | SHA256:523D28DF917F9D265CD2C0D38DF26277BC56A535145100ED82E6F5FDEAAE7256 | |||
| 3052 | plugx.exe | C:\ProgramData\SxS\NvSmartMax.dll | executable | |
MD5:0674A0929AEC3DB11383523B40FA36D1 | SHA256:FB1C1DE76504A35B5C9CF4A60C4A7497064917E0AC96B5389B5EF56C4A02BC17 | |||
| 820 | sysprep.exe | C:\Windows\System32\sysprep\Panther\diagwrn.xml | text | |
MD5:67FC5B9D0957C4FBB37376DE49A2B170 | SHA256:8ADE5E7080E6D5337CA9B4BD31C9963DC556406189B53263DD5B37A9FBBBA523 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
15
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2560 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.PlugX Checkin |
2560 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.PlugX Checkin |
2560 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.PlugX Checkin |
2560 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.PlugX Checkin |
2560 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.PlugX Checkin |
2560 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.PlugX Checkin |
2560 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.PlugX Checkin |
8 ETPRO signatures available at the full report
Process | Message |
|---|---|
svchost.exe | Protocol:[ TCP], Host: [127.0.0.1:12345], Proxy: [0::0::]
|
NvSmart.exe | file: XInstall.cpp, line: 182, error: [1053]The service did not respond to the start or control request in a timely fashion.
|
svchost.exe | file: XSoTcpHttp.cpp, line: 381, error: [87]The parameter is incorrect.
|
svchost.exe | Protocol:[HTTP], Host: [127.0.0.1:12345], Proxy: [0::0::]
|
NvSmart.exe | file: XInstallUAC.cpp, line: 162, error: [5]Access is denied.
|
NvSmart.exe | file: XInstallUAC.cpp, line: 170, error: [5]Access is denied.
|
svchost.exe | Protocol:[ UDP], Host: [127.0.0.1:12345], Proxy: [0::0::]
|
svchost.exe | Protocol:[ICMP], Host: [127.0.0.1:12345], Proxy: [0::0::]
|
svchost.exe | Protocol:[ TCP], Host: [127.0.0.1:12345], Proxy: [0::0::]
|
svchost.exe | Protocol:[HTTP], Host: [127.0.0.1:12345], Proxy: [0::0::]
|