| File name: | sample11.exe |
| Full analysis: | https://app.any.run/tasks/65cd3cf1-d457-4481-b8c7-3c2f75a7830f |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
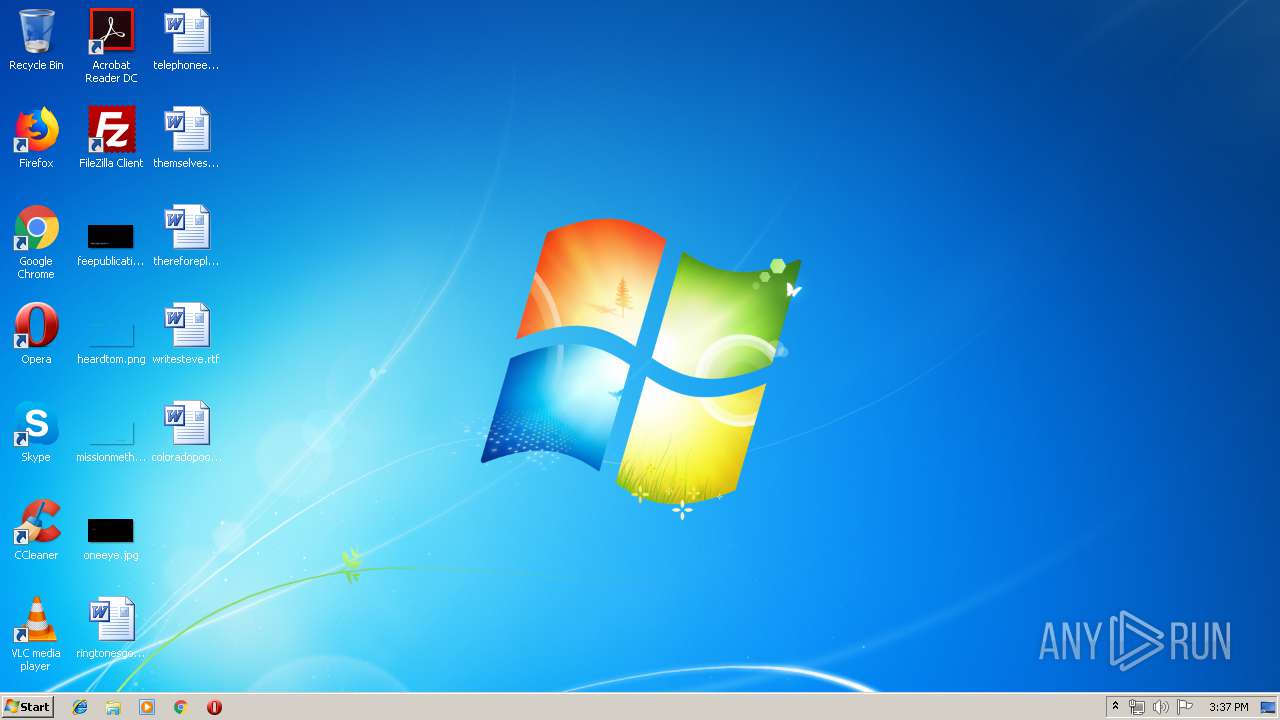
| Analysis date: | April 25, 2019, 14:34:05 |
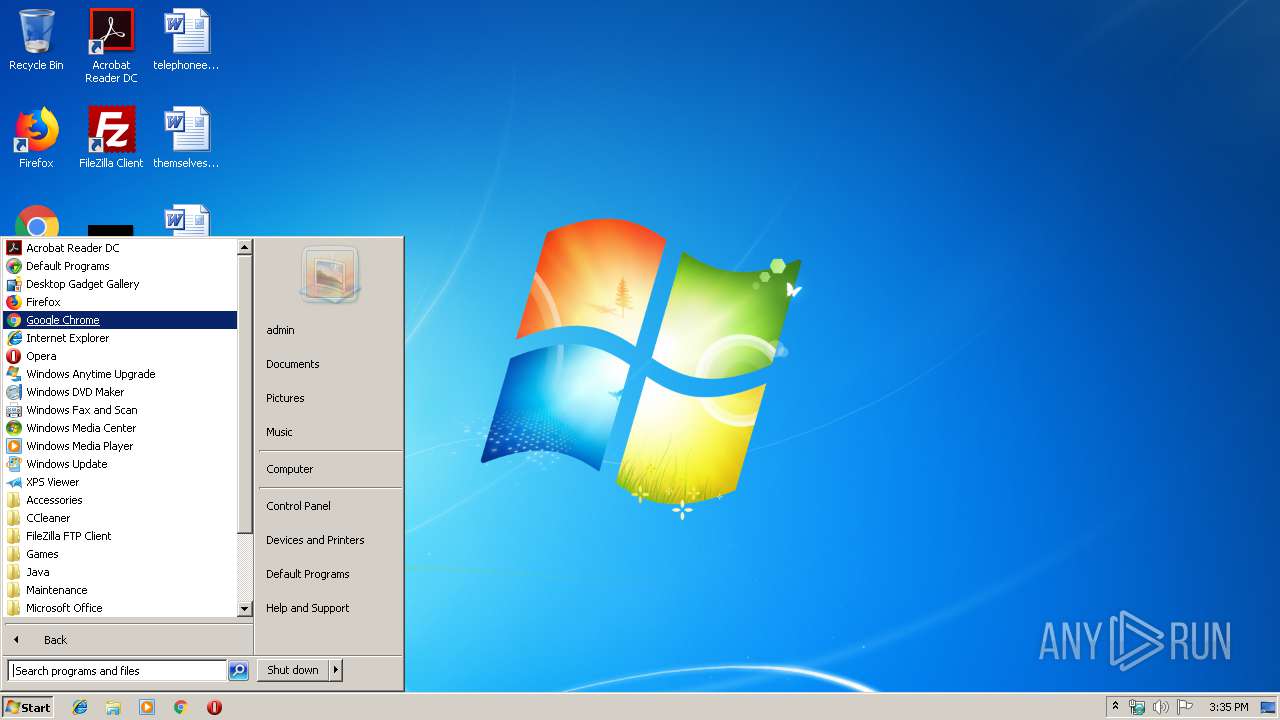
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7407A12A61C10667FBBCA160B21D13D2 |
| SHA1: | A94B955DAB53A0E2B66CD6F62E654D9D1C881A43 |
| SHA256: | 3CB84A06D0EACDC565575E487D081FC4B3C88984F035B2C23F0EDE520F065DA7 |
| SSDEEP: | 6144:JVlcL8QDcOGtWkiwaIv8jV4qVKiEgq6Cj0vt9SlE8y:TCYQoOGtWuv8jV4qpEt6CSt9SNy |
MALICIOUS
Changes the autorun value in the registry
- sample11.exe (PID: 3060)
Runs app for hidden code execution
- sysimages.exe (PID: 2800)
- sample11.exe (PID: 3060)
- sample11.exe (PID: 2552)
- sysimages.exe (PID: 3596)
- sysimages.exe (PID: 3800)
- sample11.exe (PID: 3116)
- sysimages.exe (PID: 3376)
- sample11.exe (PID: 2196)
- sysimages.exe (PID: 3044)
- sample11.exe (PID: 3832)
- sample11.exe (PID: 2956)
- sample11.exe (PID: 1276)
- sample11.exe (PID: 4036)
- sample11.exe (PID: 3024)
- sample11.exe (PID: 2360)
Application was injected by another process
- explorer.exe (PID: 252)
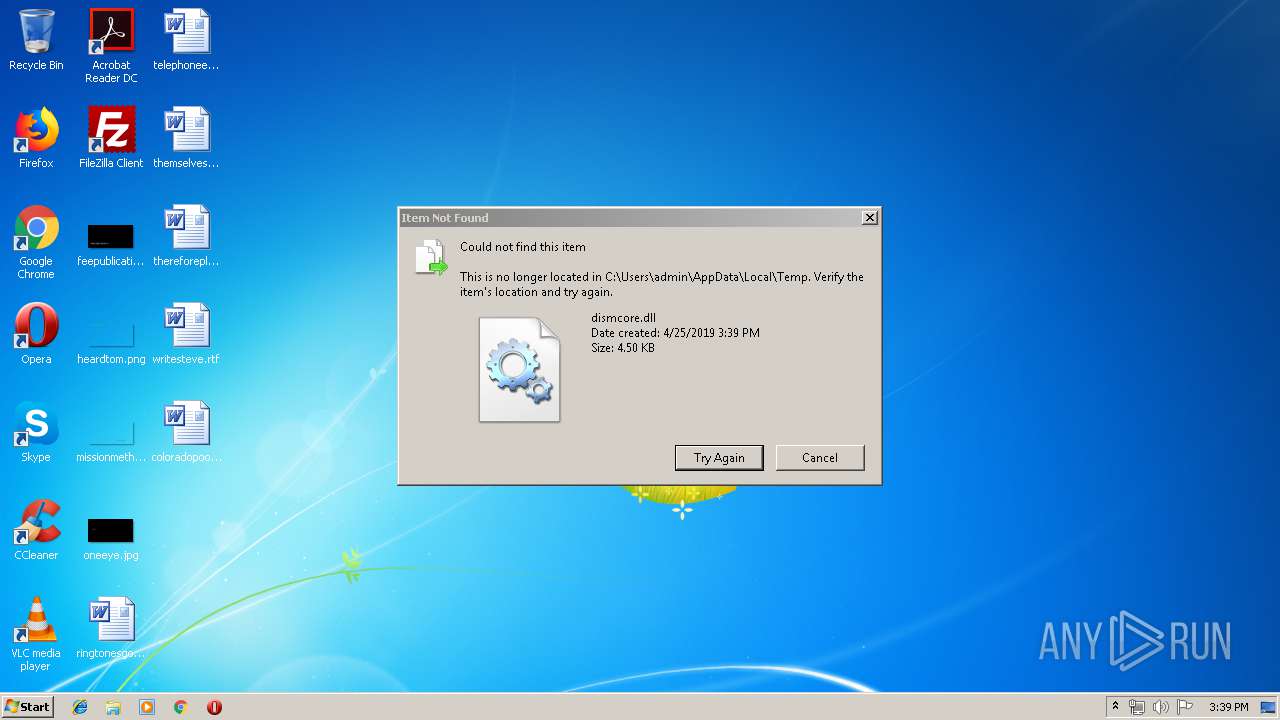
Loads dropped or rewritten executable
- dism.exe (PID: 3524)
- dism.exe (PID: 3112)
- dism.exe (PID: 3492)
- dism.exe (PID: 1520)
- dism.exe (PID: 3440)
- dism.exe (PID: 3432)
- dism.exe (PID: 2108)
- dism.exe (PID: 2952)
- dism.exe (PID: 3868)
- dism.exe (PID: 3692)
- dism.exe (PID: 3972)
- dism.exe (PID: 3916)
- dism.exe (PID: 2344)
- dism.exe (PID: 2652)
Changes settings of System certificates
- sample11.exe (PID: 3436)
Runs injected code in another process
- sysimages.exe (PID: 2800)
Connects to CnC server
- sysimages.exe (PID: 2436)
- sysimages.exe (PID: 3800)
- sample11.exe (PID: 3116)
- sample11.exe (PID: 3616)
- sysimages.exe (PID: 3376)
- sample11.exe (PID: 1236)
- sample11.exe (PID: 3832)
- sample11.exe (PID: 3676)
- sample11.exe (PID: 1276)
- sample11.exe (PID: 3612)
- sample11.exe (PID: 4036)
- sample11.exe (PID: 2788)
- sample11.exe (PID: 3024)
- sample11.exe (PID: 2360)
AVEMARIA was detected
- sysimages.exe (PID: 2436)
- sysimages.exe (PID: 3800)
SUSPICIOUS
Starts CMD.EXE for commands execution
- sample11.exe (PID: 3060)
- sysimages.exe (PID: 2800)
- sysimages.exe (PID: 3044)
- sample11.exe (PID: 2552)
- sysimages.exe (PID: 3596)
- sysimages.exe (PID: 3800)
- sample11.exe (PID: 3116)
- sysimages.exe (PID: 3376)
- sample11.exe (PID: 2196)
- sample11.exe (PID: 3832)
- sample11.exe (PID: 2956)
- sample11.exe (PID: 1276)
- sample11.exe (PID: 4036)
- sample11.exe (PID: 3024)
- sample11.exe (PID: 2360)
Executable content was dropped or overwritten
- sample11.exe (PID: 3060)
- DllHost.exe (PID: 3352)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 1132)
- DllHost.exe (PID: 2088)
- cmd.exe (PID: 1084)
- DllHost.exe (PID: 3476)
- cmd.exe (PID: 2848)
- cmd.exe (PID: 2688)
- DllHost.exe (PID: 2560)
- cmd.exe (PID: 1496)
- DllHost.exe (PID: 3672)
- cmd.exe (PID: 3404)
- cmd.exe (PID: 3464)
- DllHost.exe (PID: 3188)
- cmd.exe (PID: 328)
- cmd.exe (PID: 3928)
- DllHost.exe (PID: 3328)
- cmd.exe (PID: 2340)
- DllHost.exe (PID: 2776)
- cmd.exe (PID: 3696)
- cmd.exe (PID: 1632)
- DllHost.exe (PID: 2404)
- cmd.exe (PID: 1712)
- cmd.exe (PID: 3916)
- DllHost.exe (PID: 3768)
Starts itself from another location
- sample11.exe (PID: 3060)
Creates files in the user directory
- sysimages.exe (PID: 2800)
- sample11.exe (PID: 3436)
- sample11.exe (PID: 3060)
- sysimages.exe (PID: 3796)
- sysimages.exe (PID: 3044)
- sample11.exe (PID: 2552)
- powershell.exe (PID: 1744)
- sample11.exe (PID: 3116)
- sample11.exe (PID: 1928)
- powershell.exe (PID: 3456)
- sysimages.exe (PID: 2436)
- sysimages.exe (PID: 3376)
- sample11.exe (PID: 3616)
- sample11.exe (PID: 2196)
- powershell.exe (PID: 2156)
- sysimages.exe (PID: 3800)
- sample11.exe (PID: 1548)
- sysimages.exe (PID: 3596)
- powershell.exe (PID: 2212)
- sample11.exe (PID: 3832)
- powershell.exe (PID: 3684)
- sample11.exe (PID: 3676)
- sample11.exe (PID: 2956)
- sample11.exe (PID: 1276)
- powershell.exe (PID: 3664)
- sample11.exe (PID: 4036)
- sample11.exe (PID: 3612)
- sample11.exe (PID: 3192)
- sample11.exe (PID: 3008)
- powershell.exe (PID: 3968)
- sample11.exe (PID: 2788)
- sample11.exe (PID: 2360)
- powershell.exe (PID: 3624)
- sample11.exe (PID: 3024)
- sample11.exe (PID: 2232)
- sample11.exe (PID: 3932)
- sample11.exe (PID: 2444)
- sample11.exe (PID: 1236)
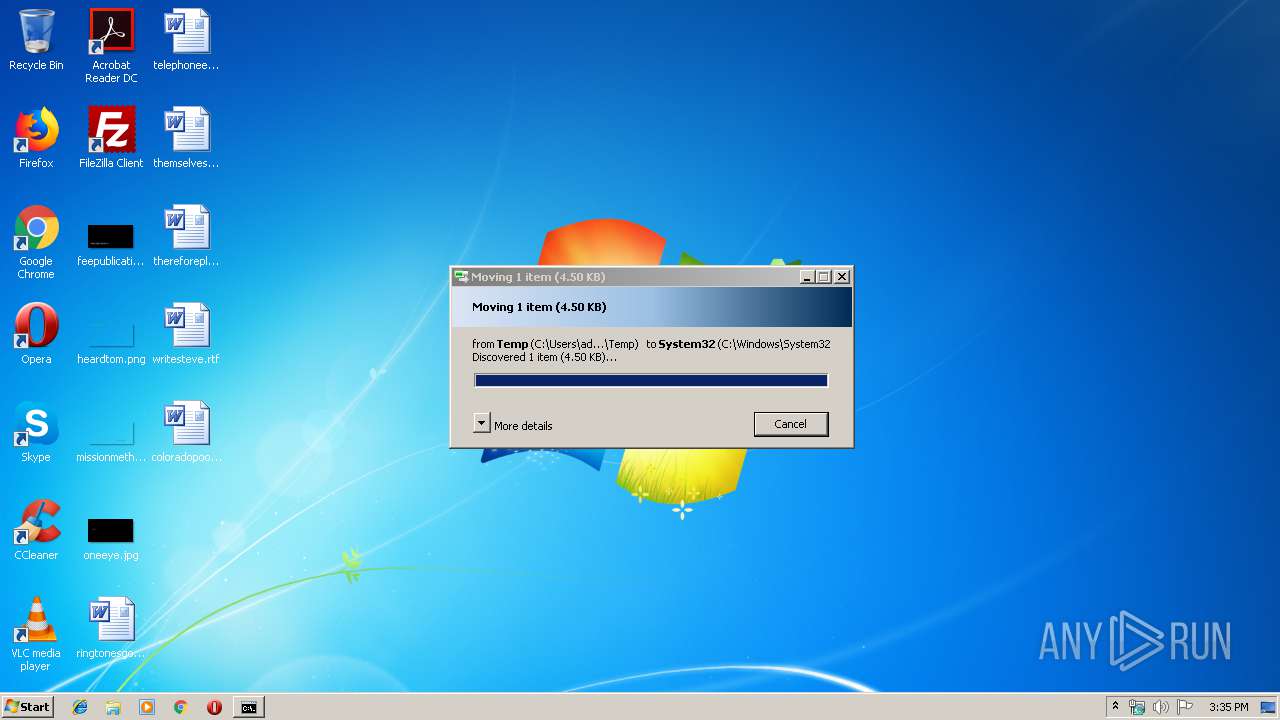
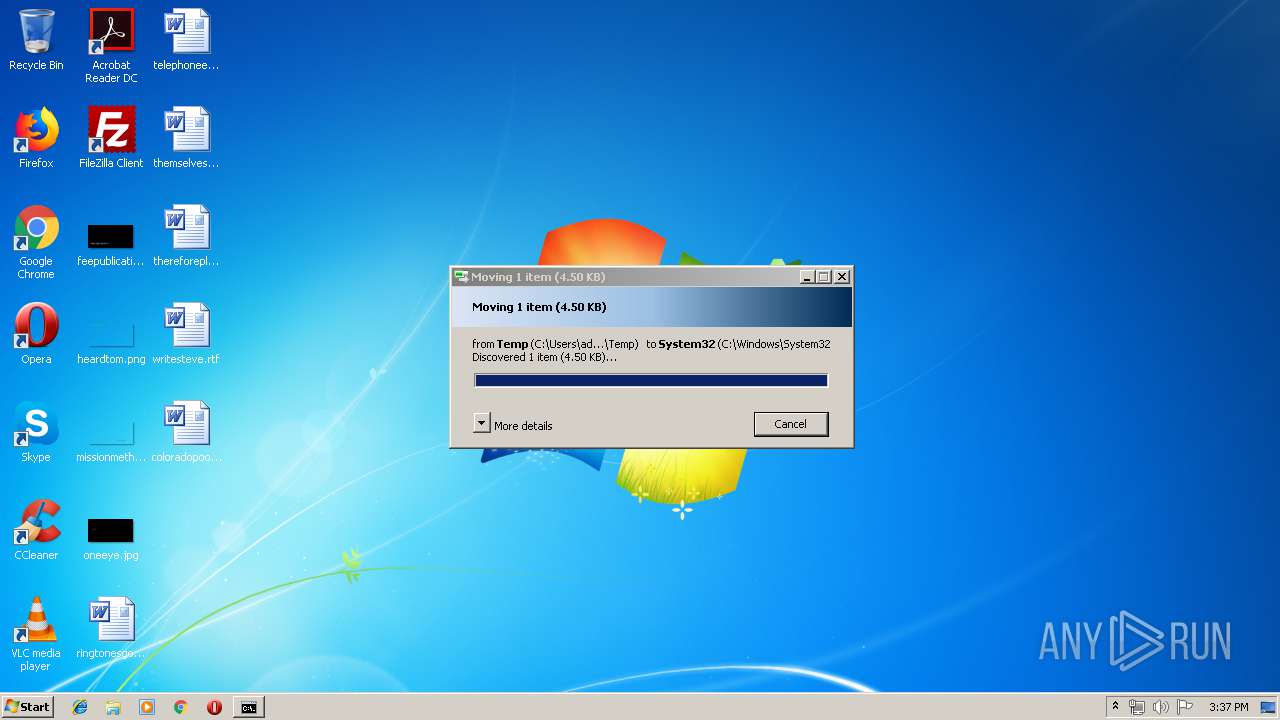
Creates files in the Windows directory
- pkgmgr.exe (PID: 2404)
Adds / modifies Windows certificates
- sample11.exe (PID: 3436)
Executes PowerShell scripts
- sample11.exe (PID: 3436)
- sysimages.exe (PID: 3796)
- sysimages.exe (PID: 2436)
- sample11.exe (PID: 3616)
- sample11.exe (PID: 1236)
- sample11.exe (PID: 3676)
- sample11.exe (PID: 3612)
- sample11.exe (PID: 2788)
Reads the machine GUID from the registry
- sysimages.exe (PID: 3800)
- sysimages.exe (PID: 2436)
- sample11.exe (PID: 3116)
- sample11.exe (PID: 3616)
- sysimages.exe (PID: 3376)
- sample11.exe (PID: 1236)
- sample11.exe (PID: 3832)
- sample11.exe (PID: 3676)
- sample11.exe (PID: 1276)
- sample11.exe (PID: 3612)
- sample11.exe (PID: 4036)
- sample11.exe (PID: 2788)
- sample11.exe (PID: 3024)
- sample11.exe (PID: 2360)
Loads DLL from Mozilla Firefox
- sysimages.exe (PID: 2436)
- sysimages.exe (PID: 3800)
- sysimages.exe (PID: 3376)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:22 21:33:57+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 119808 |
| InitializedDataSize: | 385536 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xe34e |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 44.12.3.5 |
| ProductVersionNumber: | 8.9.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | More vases pro |
| FileDescription: | used to make vases pro |
| CompanyName: | Vases InTERNATIONAL GROUP |
| LegalCopyright: | 2019 Copyright |
| ProductVersion: | 8.9.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Apr-2019 19:33:57 |
| Detected languages: |
|
| ProductName: | More vases pro |
| FileDescription: | used to make vases pro |
| CompanyName: | Vases InTERNATIONAL GROUP |
| LegalCopyright: | 2019 Copyright |
| ProductVersion: | 8.9.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 22-Apr-2019 19:33:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001D317 | 0x0001D400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53043 |
.rdata | 0x0001F000 | 0x00006D0C | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.19422 |
.data | 0x00026000 | 0x00011CE4 | 0x00010C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.15242 |
.rsrc | 0x00038000 | 0x0002A944 | 0x0002AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.71649 |
.reloc | 0x00063000 | 0x00002944 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.63617 |
.bss | 0x00066000 | 0x00019343 | 0x00019400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.02362 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.59632 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.44792 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.35389 | 21640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.91016 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.70476 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 4.43992 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.00548 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 4.87039 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
KERNEL32.dll |
USER32.dll |
WININET.dll |
Total processes
209
Monitored processes
110
Malicious processes
8
Suspicious processes
25
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 328 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | sample11.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 676 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Package Manager Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 700 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Package Manager Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 720 | "C:\Users\admin\AppData\Local\Temp\sample11.exe" | C:\Users\admin\AppData\Local\Temp\sample11.exe | — | dism.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1084 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | sysimages.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1132 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | sysimages.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1236 | "C:\Users\admin\AppData\Local\Temp\sample11.exe" | C:\Users\admin\AppData\Local\Temp\sample11.exe | dism.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1276 | "C:\Users\admin\AppData\Local\Temp\sample11.exe" | C:\Users\admin\AppData\Local\Temp\sample11.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1412 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Package Manager Exit code: 3221226540 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
9 956
Read events
8 780
Write events
1 176
Delete events
0
Modification events
| (PID) Process: | (3060) sample11.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sample11_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3060) sample11.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sample11_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3060) sample11.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sample11_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3060) sample11.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sample11_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3060) sample11.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sample11_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3060) sample11.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sample11_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3060) sample11.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sample11_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3060) sample11.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sample11_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3060) sample11.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sample11_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3060) sample11.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sample11_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
26
Suspicious files
17
Text files
62
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3060 | sample11.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[1].txt | — | |
MD5:— | SHA256:— | |||
| 2800 | sysimages.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[1].txt | — | |
MD5:— | SHA256:— | |||
| 2212 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0DFG9SSSBGKY20IOJU0Q.temp | — | |
MD5:— | SHA256:— | |||
| 3060 | sample11.exe | C:\Users\admin\AppData\Roaming\sysimages.exe | executable | |
MD5:— | SHA256:— | |||
| 3060 | sample11.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[2].txt | text | |
MD5:— | SHA256:— | |||
| 2404 | pkgmgr.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:— | SHA256:— | |||
| 2800 | sysimages.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[2].txt | text | |
MD5:— | SHA256:— | |||
| 3436 | sample11.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[1].txt | text | |
MD5:— | SHA256:— | |||
| 3796 | sysimages.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[2].txt | text | |
MD5:— | SHA256:— | |||
| 2816 | pkgmgr.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
95
DNS requests
6
Threats
34
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3060 | sample11.exe | 172.217.18.110:443 | google.com | Google Inc. | US | whitelisted |
3796 | sysimages.exe | 172.217.18.110:443 | google.com | Google Inc. | US | whitelisted |
3436 | sample11.exe | 23.105.131.236:18744 | fastcharge.warzonedns.com | Nobis Technology Group, LLC | US | malicious |
3796 | sysimages.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
3044 | sysimages.exe | 172.217.18.110:443 | google.com | Google Inc. | US | whitelisted |
3060 | sample11.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
3436 | sample11.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
2552 | sample11.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
3044 | sysimages.exe | 23.105.131.236:18744 | fastcharge.warzonedns.com | Nobis Technology Group, LLC | US | malicious |
3120 | sysimages.exe | 172.217.18.110:443 | google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
google.com |
| malicious |
fastcharge.warzonedns.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2436 | sysimages.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
3800 | sysimages.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
2436 | sysimages.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Connection |
3800 | sysimages.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Connection |
3116 | sample11.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
3116 | sample11.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Connection |
3616 | sample11.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
3616 | sample11.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Connection |
3376 | sysimages.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
3376 | sysimages.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Connection |
5 ETPRO signatures available at the full report