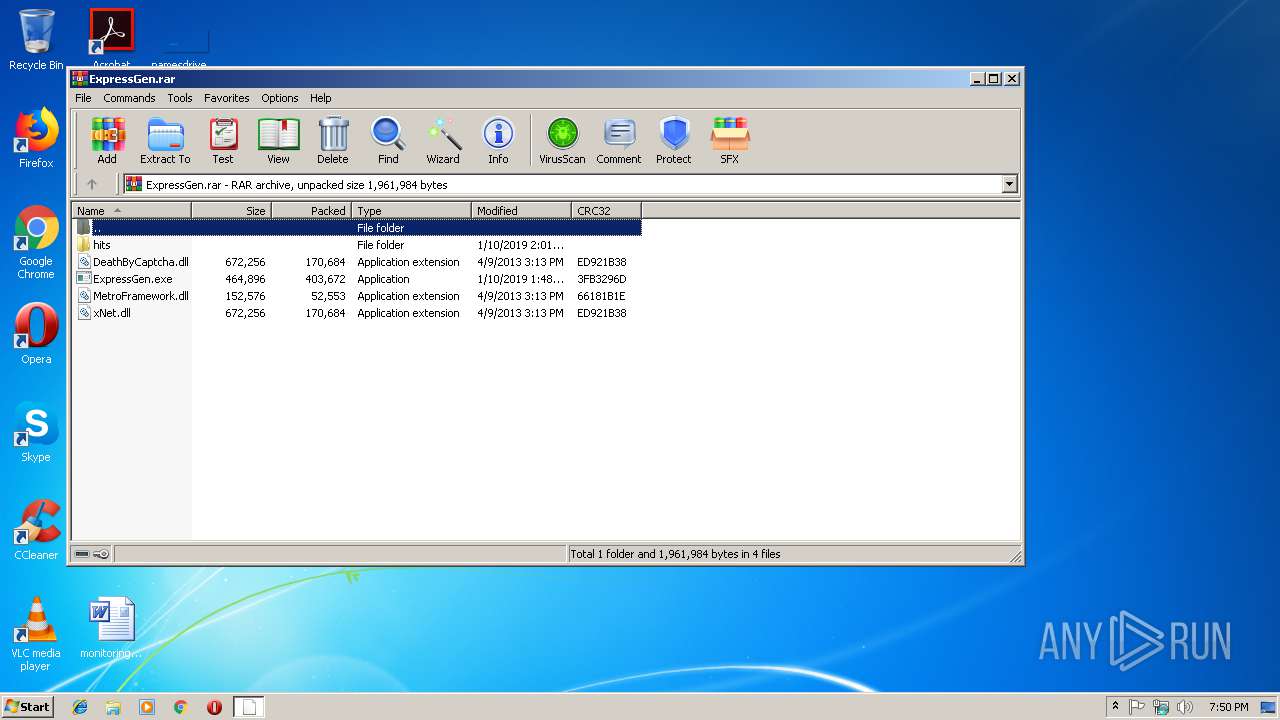
| download: | ExpressGen.rar |
| Full analysis: | https://app.any.run/tasks/eb283bcd-4055-486d-bd7f-878b84e1ae4d |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | January 10, 2019, 19:50:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 49D834E1F9F733C9F3F7256216BA2B1F |
| SHA1: | E453E7750A283DF64D1D9EDB73FDABAD3BF77B6F |
| SHA256: | 3CB2802B37C8060A433FAFF56BC1E92EB19DF44E514F94679A430FDBEB6844C6 |
| SSDEEP: | 12288:9e5XWBtzrbtQhLmjGbDIOGj8qrf5rp/irs09ijfPe5XWBtzrD:9KWnIsCIoqr2sHjHKWnD |
MALICIOUS
Application was dropped or rewritten from another process
- WindowsDefender.exe (PID: 3800)
- ExpressGen.exe (PID: 2840)
Changes the autorun value in the registry
- Regasm.exe (PID: 3824)
QUASAR was detected
- Regasm.exe (PID: 3824)
Actions looks like stealing of personal data
- Regasm.exe (PID: 3824)
SUSPICIOUS
Starts itself from another location
- ExpressGen.exe (PID: 2840)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3012)
- ExpressGen.exe (PID: 2840)
Checks for external IP
- Regasm.exe (PID: 3824)
Connects to unusual port
- Regasm.exe (PID: 3824)
Creates files in the user directory
- Regasm.exe (PID: 3824)
Reads Internet Cache Settings
- Regasm.exe (PID: 3824)
Loads DLL from Mozilla Firefox
- Regasm.exe (PID: 3824)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
35
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2840 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.34282\ExpressGen.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.34282\ExpressGen.exe | WinRAR.exe | ||||||||||||
User: admin Company: Update Integrity Level: MEDIUM Description: Update.exe Exit code: 0 Version: 1.1.1.0 Modules
| |||||||||||||||
| 3012 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ExpressGen.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3112 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | — | WindowsDefender.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 3800 | "C:\Users\admin\AppData\Local\Temp\WindowsDefender.exe" | C:\Users\admin\AppData\Local\Temp\WindowsDefender.exe | — | ExpressGen.exe | |||||||||||
User: admin Company: Update Integrity Level: MEDIUM Description: Update.exe Exit code: 0 Version: 1.1.1.0 Modules
| |||||||||||||||
| 3824 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | ExpressGen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
Total events
913
Read events
882
Write events
30
Delete events
1
Modification events
| (PID) Process: | (3012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3012) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ExpressGen.rar | |||
| (PID) Process: | (3012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
5
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.34282\ExpressGen.exe | executable | |
MD5:— | SHA256:— | |||
| 2840 | ExpressGen.exe | C:\Users\admin\AppData\Local\Temp\WindowsDefender.exe | executable | |
MD5:— | SHA256:— | |||
| 3824 | Regasm.exe | C:\Users\admin\AppData\Roaming\Logs\01-10-2019 | binary | |
MD5:— | SHA256:— | |||
| 3824 | Regasm.exe | C:\Users\admin\AppData\Local\Temp\68xoPlXDUDRe.bat | text | |
MD5:— | SHA256:— | |||
| 3012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.34282\DeathByCaptcha.dll | executable | |
MD5:612080028164B12939751DCCCBB68D4A | SHA256:E96030FDDAF7E78401567EE82480AD75EE48D3556199A3F85C0EC669EDAC2EF4 | |||
| 3012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.34282\MetroFramework.dll | executable | |
MD5:44538B311E9EC2BCF0A6452702628D99 | SHA256:BAF326F52D39155D722465947F4CC67E6E90CFD0F89954EAB959568E9BC342AA | |||
| 3012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.34282\xNet.dll | executable | |
MD5:612080028164B12939751DCCCBB68D4A | SHA256:E96030FDDAF7E78401567EE82480AD75EE48D3556199A3F85C0EC669EDAC2EF4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3824 | Regasm.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json/ | DE | text | 253 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3824 | Regasm.exe | 193.56.28.121:5431 | — | — | — | malicious |
3824 | Regasm.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3824 | Regasm.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3824 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar 1.3 RAT IP Lookup ip-api.com (HTTP headeer) |
3824 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar RAT |
1 ETPRO signatures available at the full report