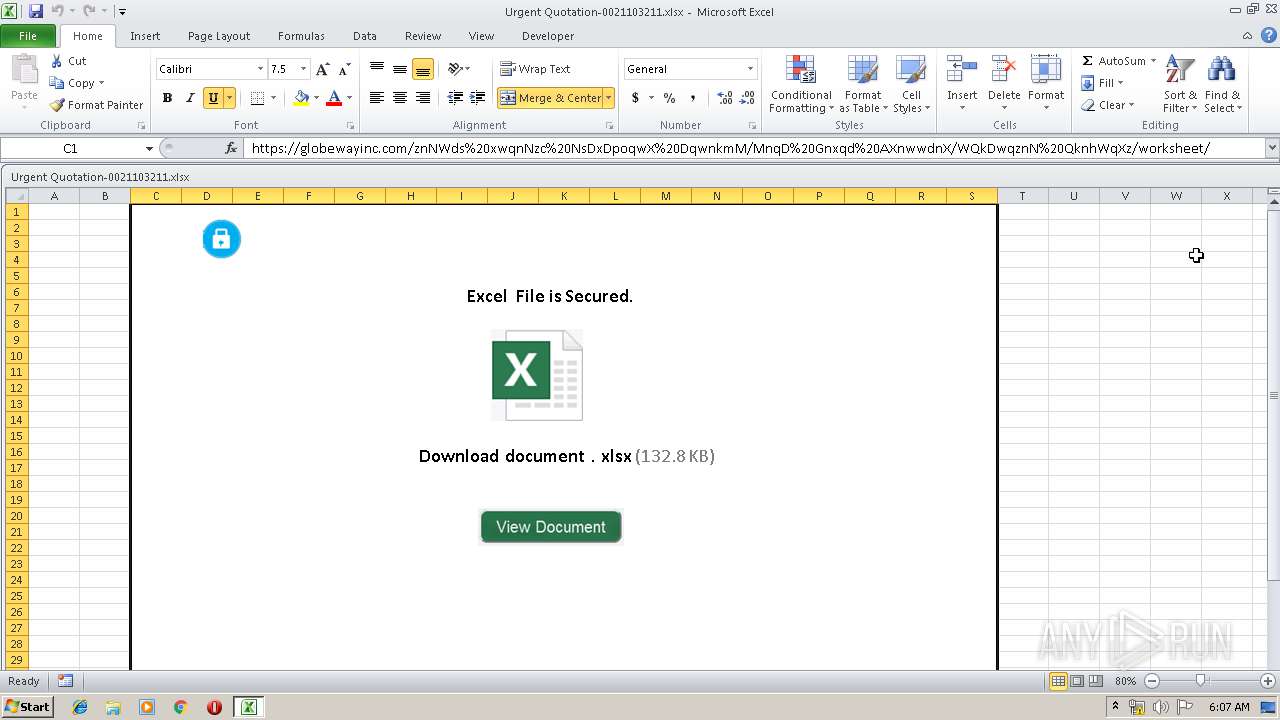
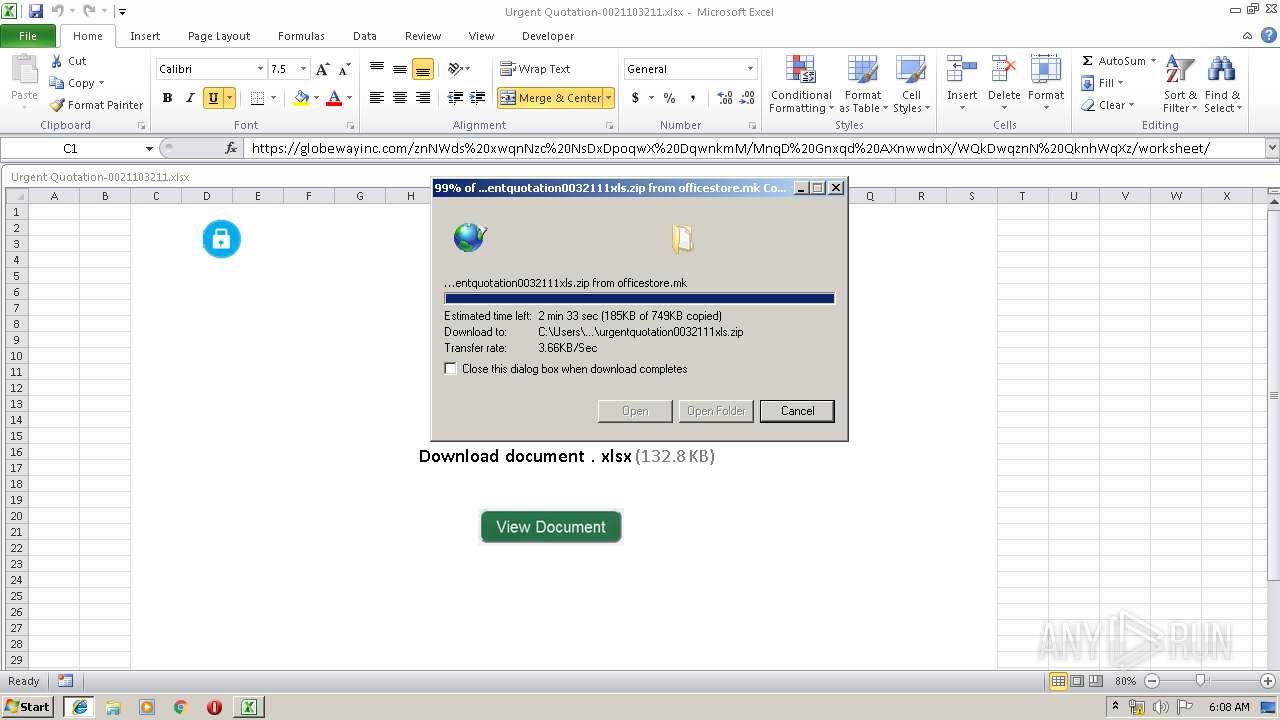
| File name: | Urgent Quotation-0021103211.xlsx |
| Full analysis: | https://app.any.run/tasks/0f0c7560-856b-4649-8773-9f6fffaffa3b |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | May 24, 2019, 05:07:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 1280C41C289F32A91783FF8BE5697BEF |
| SHA1: | 48A0850819EA78C26BC85907A2DD0E723210EB16 |
| SHA256: | 3C557F9F373F47F65B7CCB859C0996709E5C3142F48B30DF8A1C4DD1D37E5D7F |
| SSDEEP: | 384:I45lAxBP+FgylEmF91hDDWhAp0Q+gJkAY2C8c/aIawJ9PpOxx5E:h5l8BP+5lEu1hDDWhAp0ZgJk0C8cRasZ |
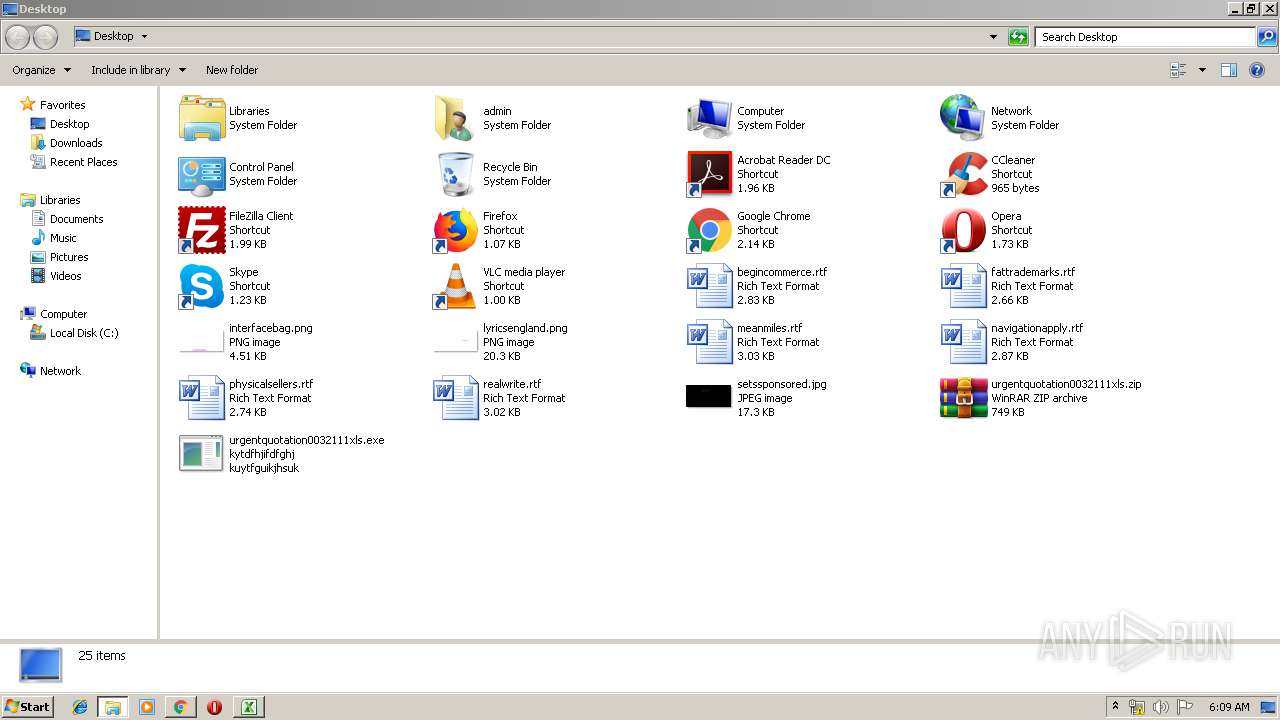
MALICIOUS
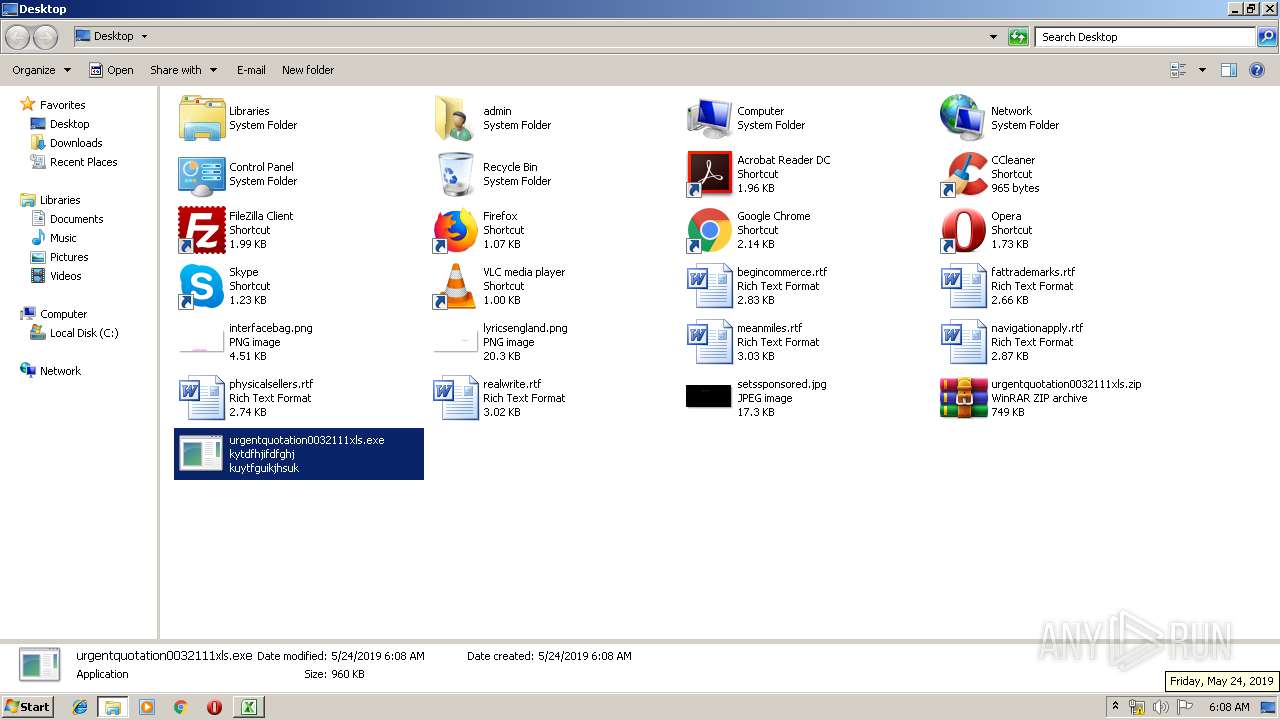
Application was dropped or rewritten from another process
- urgentquotation0032111xls.exe (PID: 3040)
- urgentquotation0032111xls.exe (PID: 1708)
Detected Hawkeye Keylogger
- urgentquotation0032111xls.exe (PID: 3040)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2140)
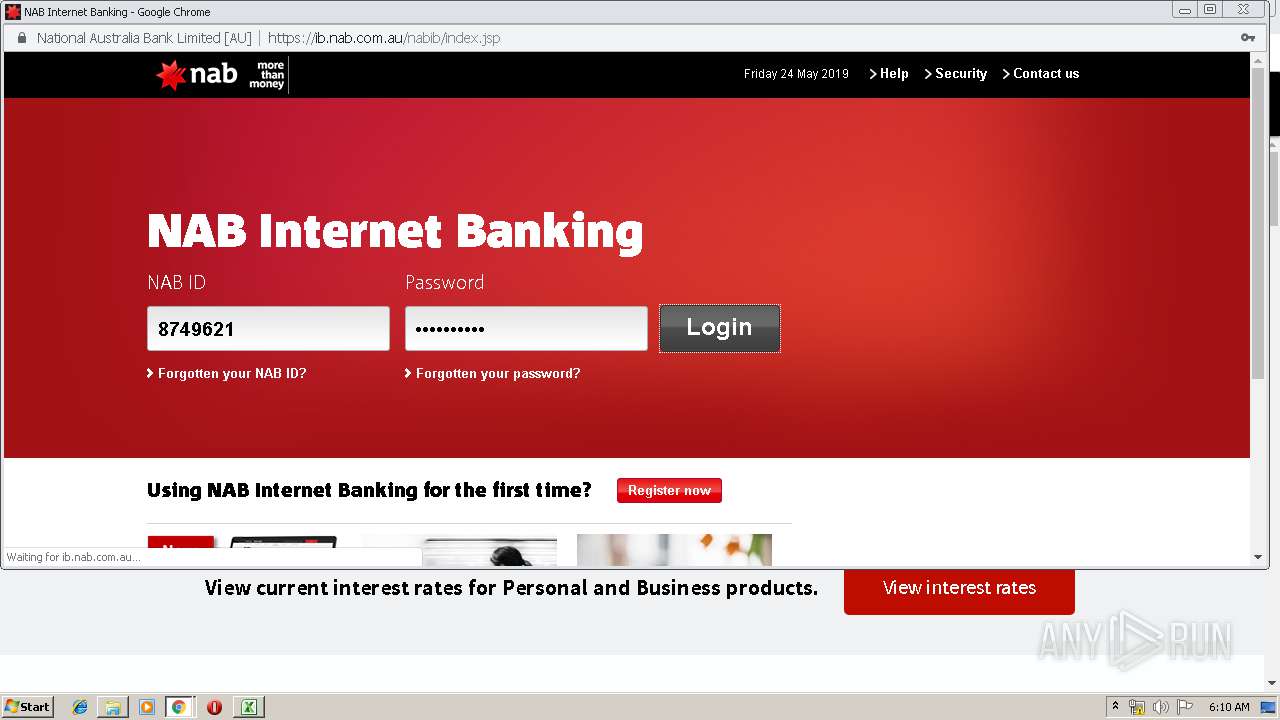
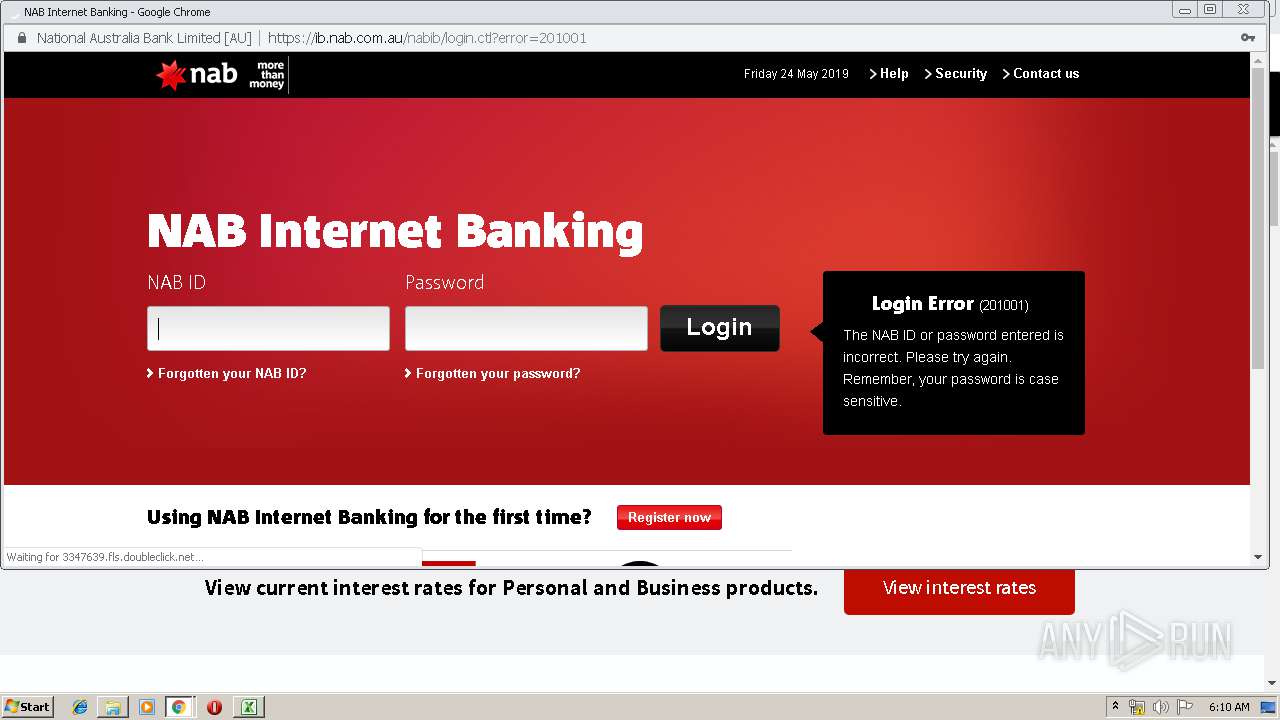
Stealing of credential data
- vbc.exe (PID: 2672)
- vbc.exe (PID: 2044)
Actions looks like stealing of personal data
- vbc.exe (PID: 2672)
- vbc.exe (PID: 2044)
SUSPICIOUS
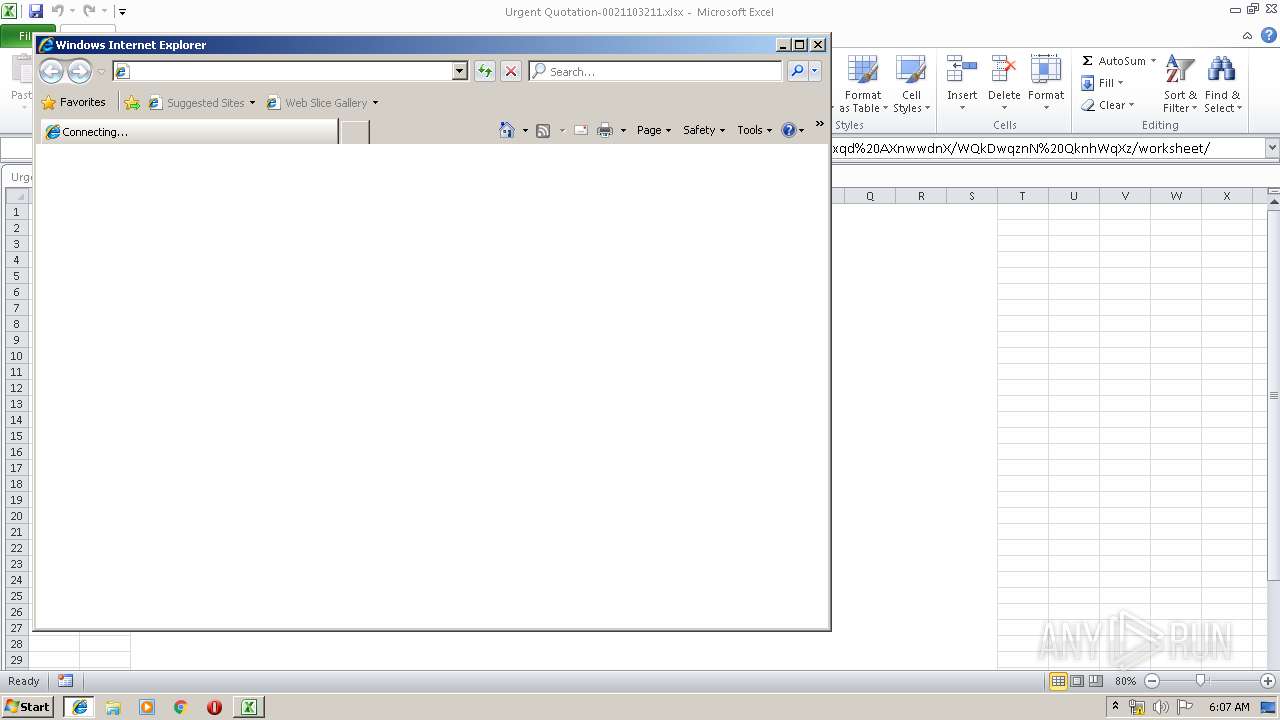
Starts Internet Explorer
- EXCEL.EXE (PID: 2140)
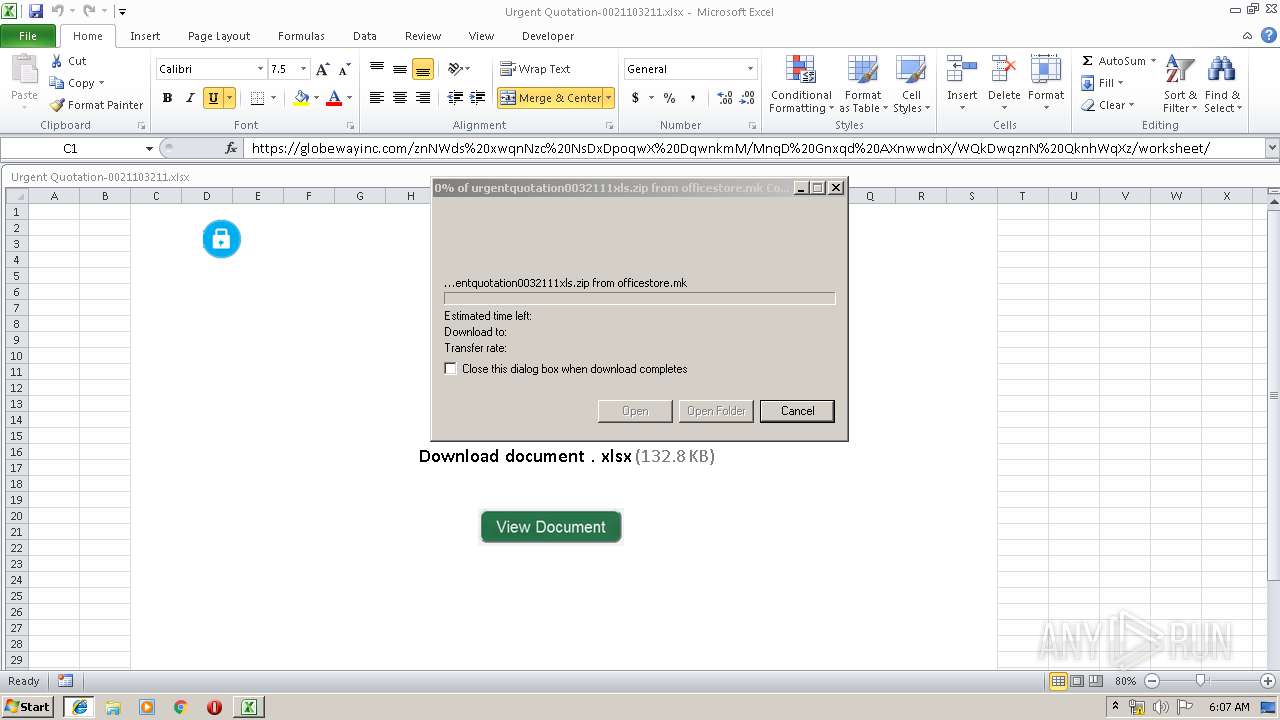
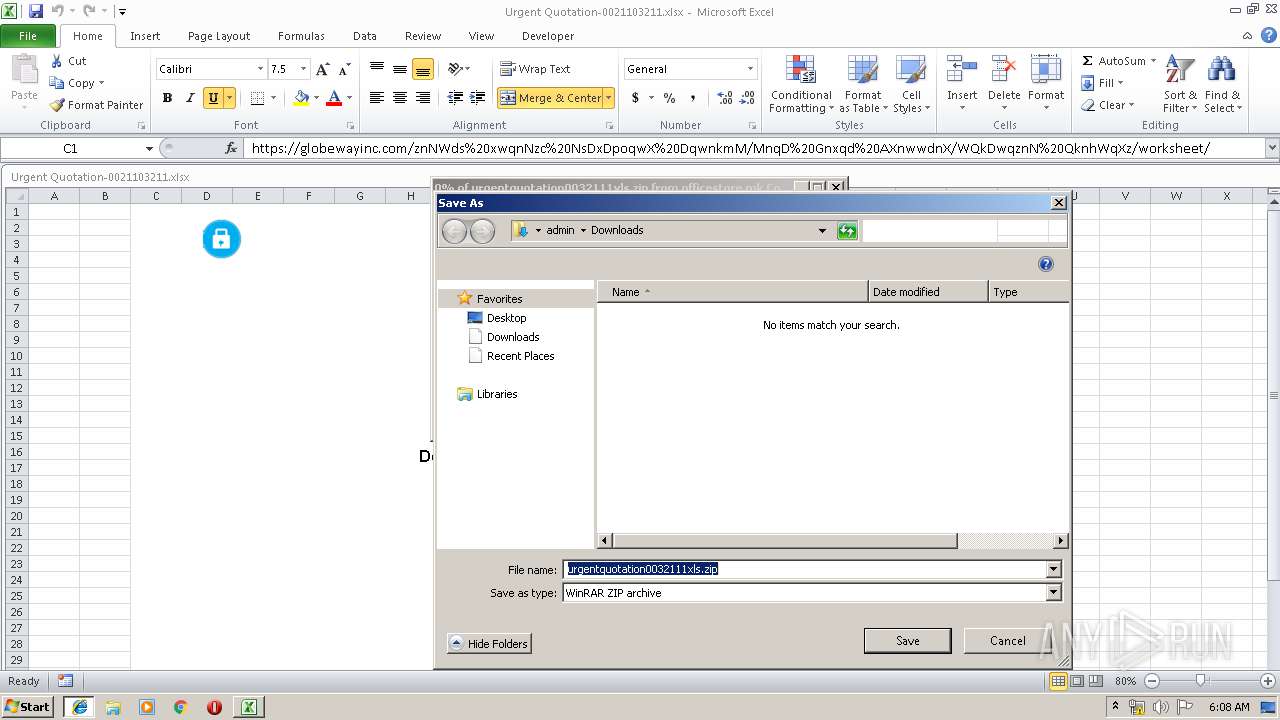
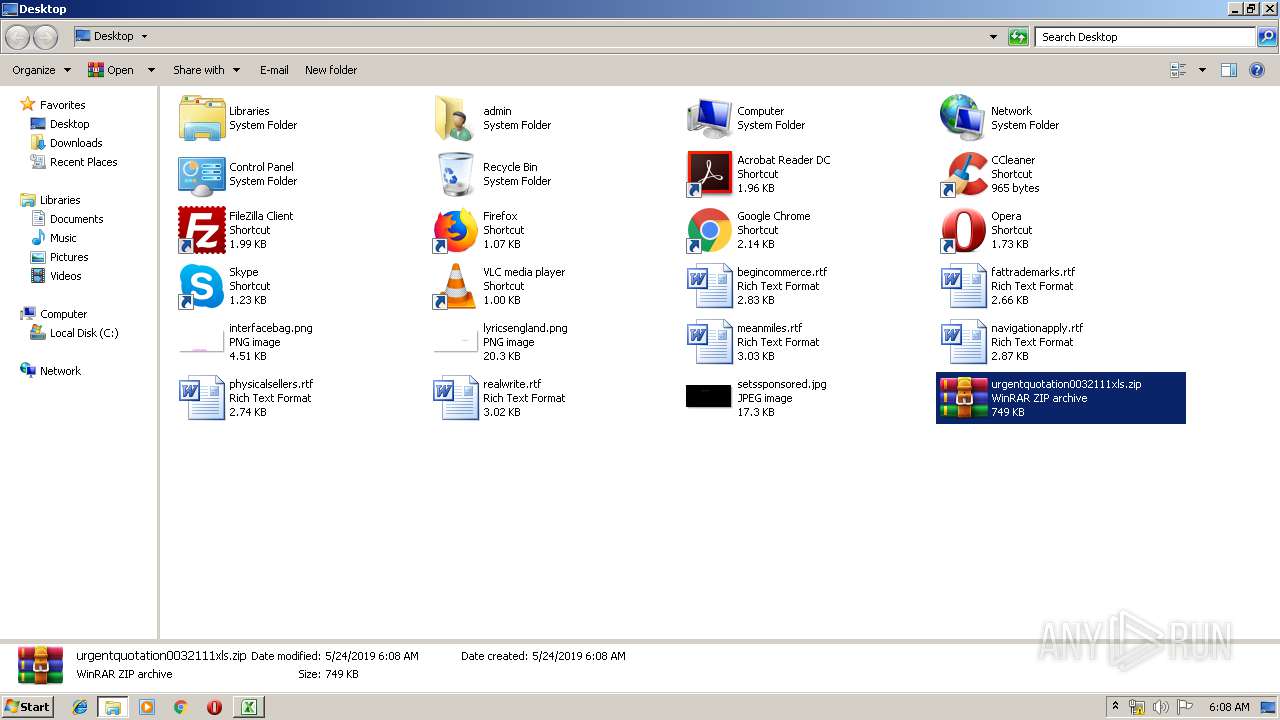
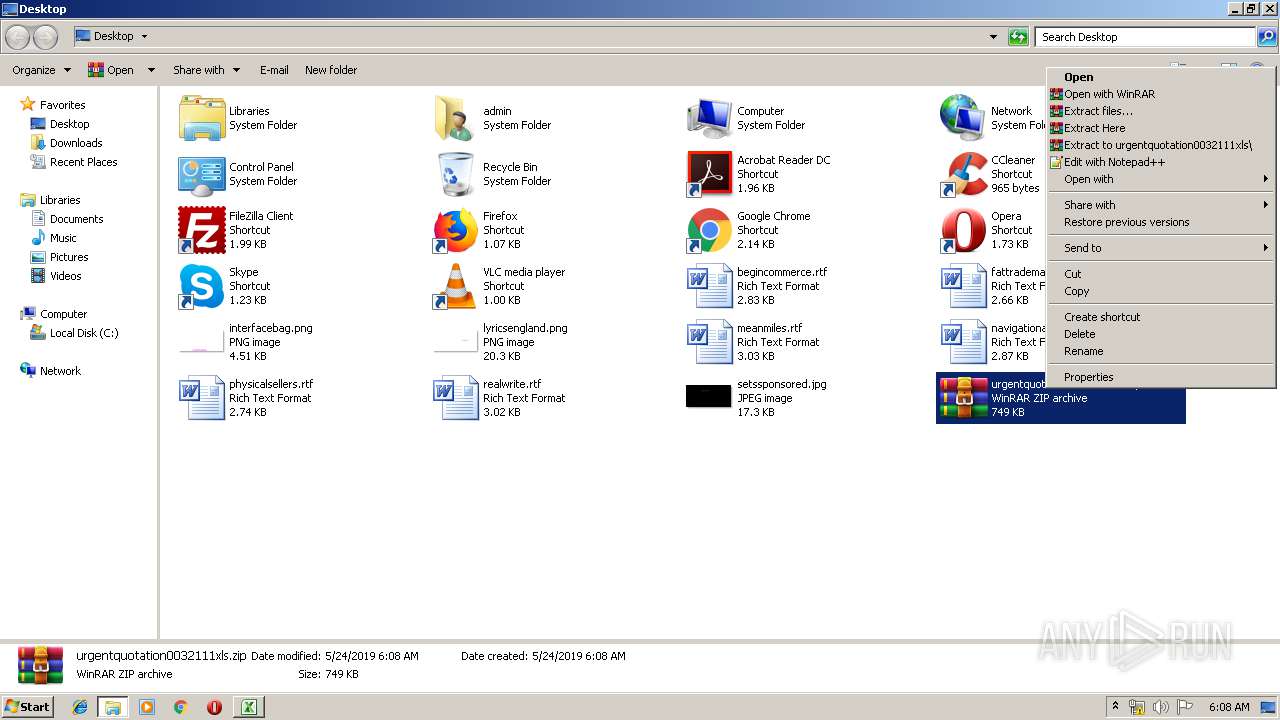
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2676)
Starts CMD.EXE for commands execution
- urgentquotation0032111xls.exe (PID: 1708)
Application launched itself
- urgentquotation0032111xls.exe (PID: 1708)
Executes scripts
- urgentquotation0032111xls.exe (PID: 3040)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 2044)
Reads Internet Cache Settings
- EXCEL.EXE (PID: 2140)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3640)
INFO
Creates files in the user directory
- iexplore.exe (PID: 2596)
- EXCEL.EXE (PID: 2140)
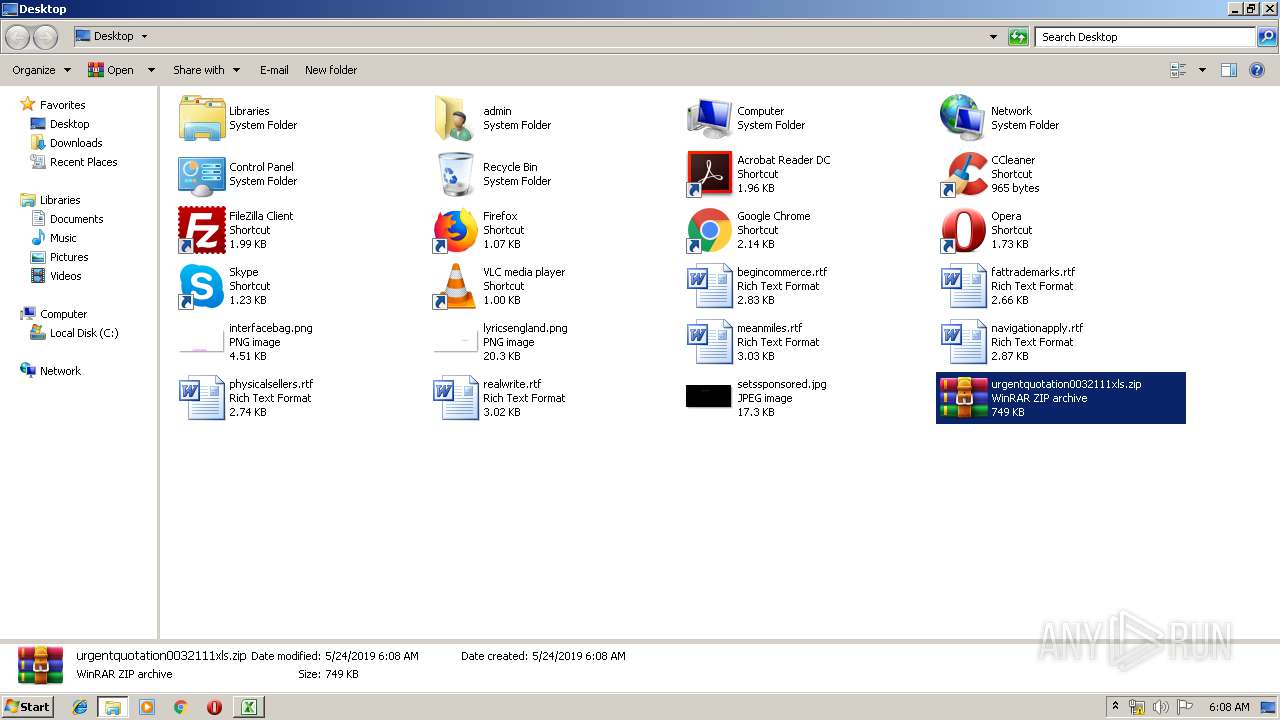
Manual execution by user
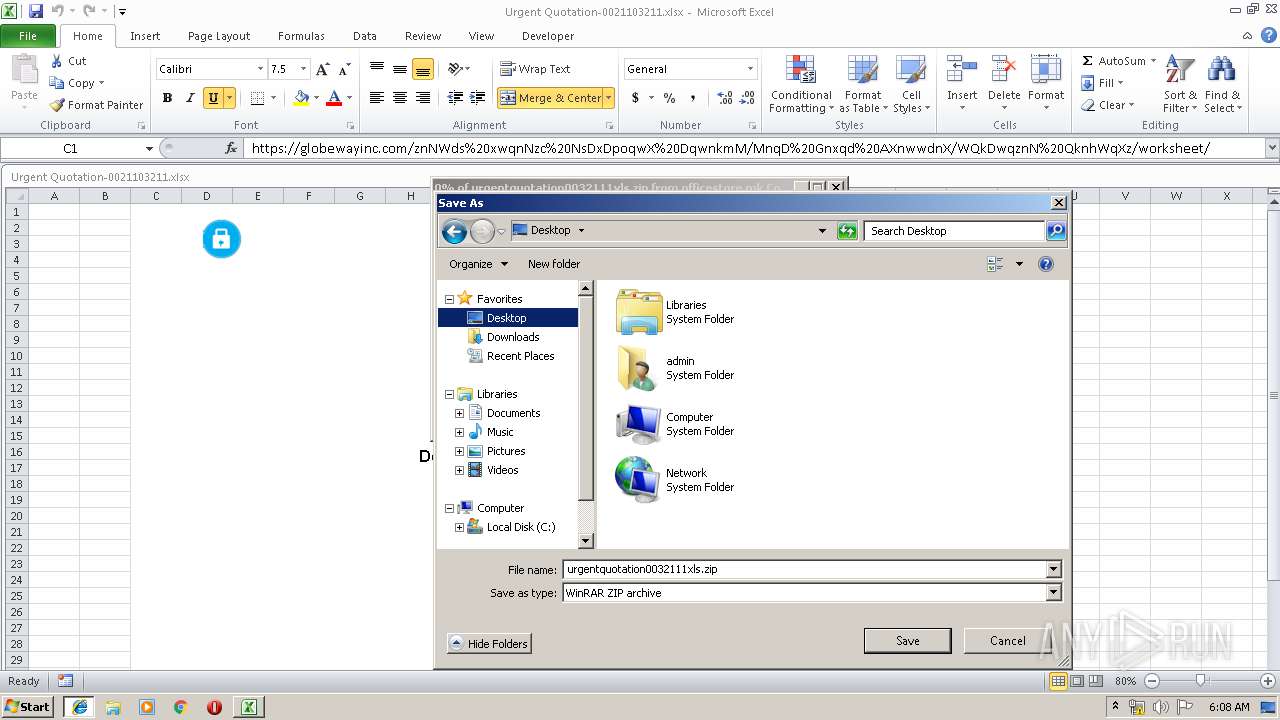
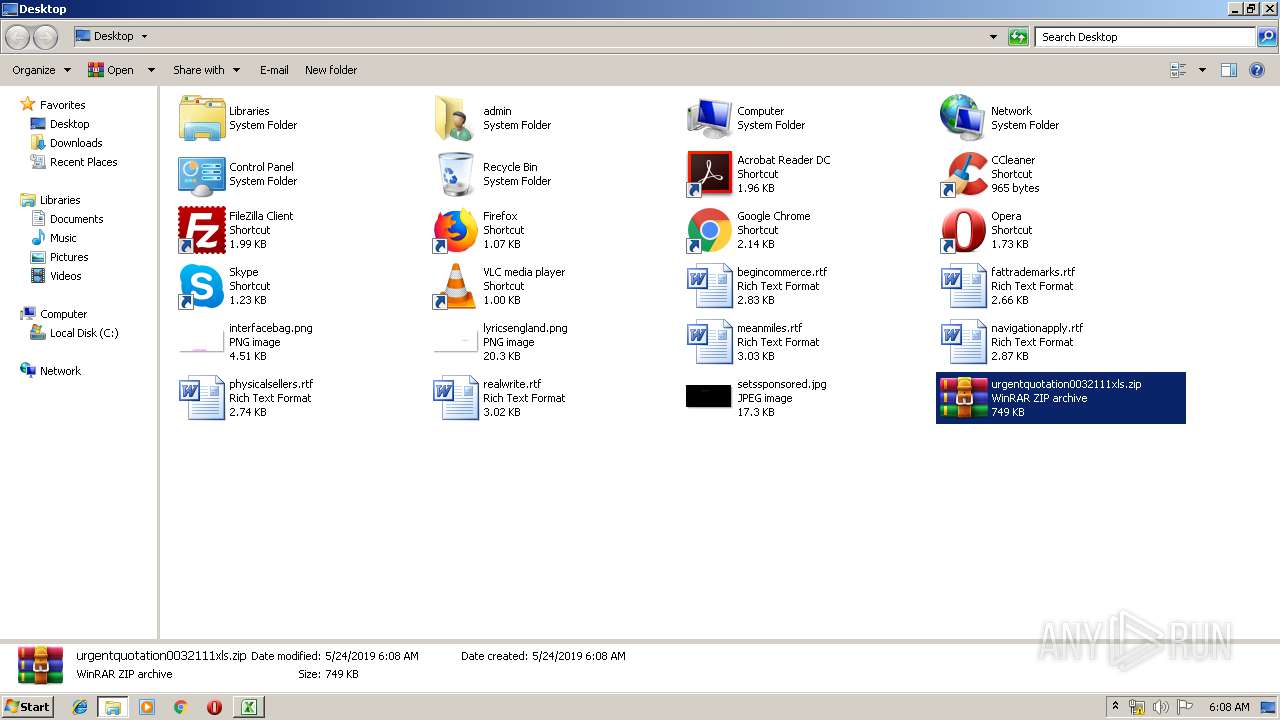
- urgentquotation0032111xls.exe (PID: 1708)
- WinRAR.exe (PID: 2676)
- chrome.exe (PID: 3640)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2140)
Reads Internet Cache Settings
- iexplore.exe (PID: 2596)
- iexplore.exe (PID: 1240)
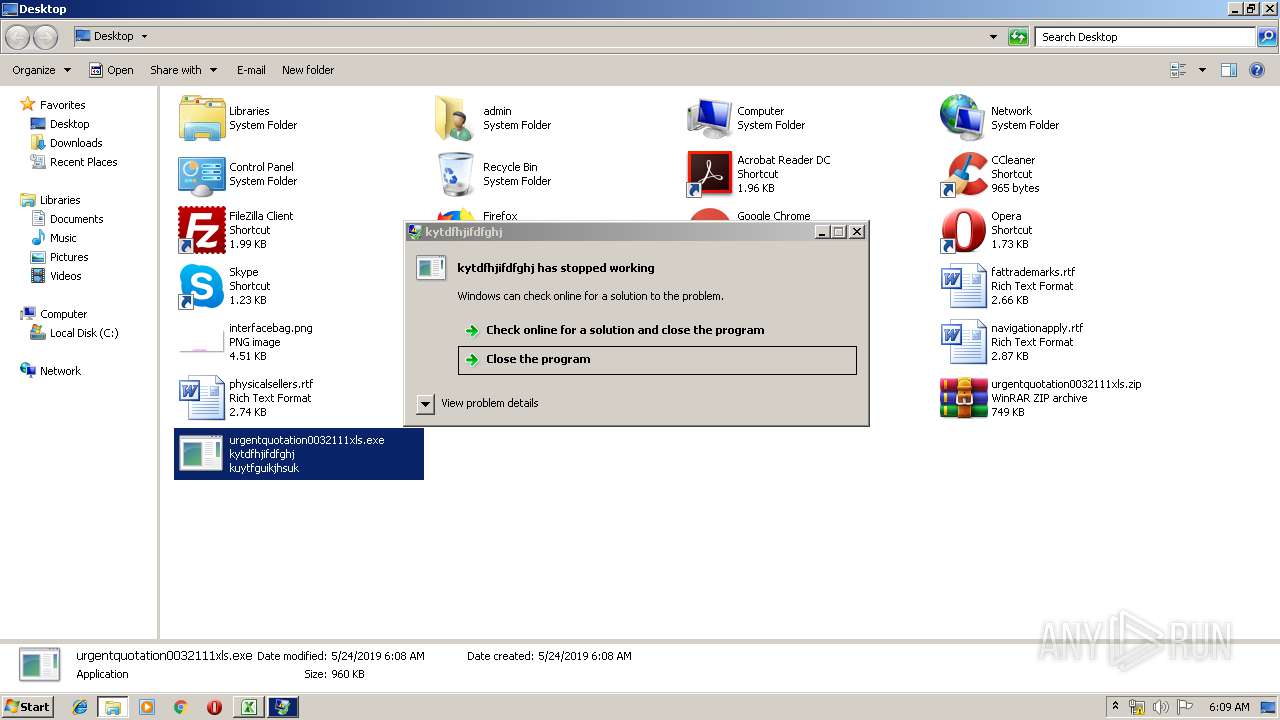
Application was crashed
- urgentquotation0032111xls.exe (PID: 1708)
Changes internet zones settings
- iexplore.exe (PID: 1240)
Application launched itself
- chrome.exe (PID: 3640)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x8546296f |
| ZipCompressedSize: | 408 |
| ZipUncompressedSize: | 1726 |
| ZipFileName: | [Content_Types].xml |
XML
| Application: | Microsoft Excel |
|---|---|
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 14.03 |
| LastModifiedBy: | USER |
| CreateDate: | 2016:08:23 21:52:25Z |
| ModifyDate: | 2019:05:23 22:58:30Z |
XMP
| Creator: | Double-Dee |
|---|
Total processes
76
Monitored processes
35
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,850118782366187018,5860031978058444425,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14586717873594512839 --mojo-platform-channel-handle=4080 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x61040f18,0x61040f28,0x61040f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,850118782366187018,5860031978058444425,131072 --enable-features=PasswordImport --service-pipe-token=12551034765615377809 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12551034765615377809 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2012 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,850118782366187018,5860031978058444425,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6571579192358105201 --mojo-platform-channel-handle=2472 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,850118782366187018,5860031978058444425,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6641509217308426420 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6641509217308426420 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,850118782366187018,5860031978058444425,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1167209805472983661 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1167209805472983661 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,850118782366187018,5860031978058444425,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3934038590217638864 --mojo-platform-channel-handle=3916 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1708 | "C:\Users\admin\Desktop\urgentquotation0032111xls.exe" | C:\Users\admin\Desktop\urgentquotation0032111xls.exe | explorer.exe | ||||||||||||
User: admin Company: kuytfguikjhsuk Integrity Level: MEDIUM Description: kytdfhjifdfghj Exit code: 3762504530 Version: 1.7.1.0 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,850118782366187018,5860031978058444425,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=12846886890738932278 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12846886890738932278 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2616 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
2 275
Read events
2 015
Write events
244
Delete events
16
Modification events
| (PID) Process: | (2140) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 28> |
Value: 32383E005C080000010000000000000000000000 | |||
| (PID) Process: | (2140) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2140) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2140) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 5C080000482028A2EE11D50100000000 | |||
| (PID) Process: | (2140) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | 28> |
Value: 32383E005C080000010000000000000000000000 | |||
| (PID) Process: | (2140) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2140) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2140) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2140) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2140) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\11F2BB |
| Operation: | write | Name: | 11F2BB |
Value: 040000005C0800004200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0055007200670065006E0074002000510075006F0074006100740069006F006E002D0030003000320031003100300033003200310031002E0078006C0073007800000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0001000000000000000085A5A3EE11D501BBF21100BBF2110000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
1
Suspicious files
186
Text files
270
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVREC32.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2140 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\urgentquotation0032111xls[1].zip | — | |
MD5:— | SHA256:— | |||
| 1240 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC2164B9FE1568039.TMP | — | |
MD5:— | SHA256:— | |||
| 1240 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1240 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1240 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFEA4E785434ED4A60.TMP | — | |
MD5:— | SHA256:— | |||
| 1240 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{E3AFB9B1-7DE1-11E9-A09E-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2596 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1240 | iexplore.exe | C:\Users\admin\Desktop\urgentquotation0032111xls.zip | compressed | |
MD5:— | SHA256:— | |||
| 1240 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{E3AFB9B2-7DE1-11E9-A09E-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
74
DNS requests
53
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
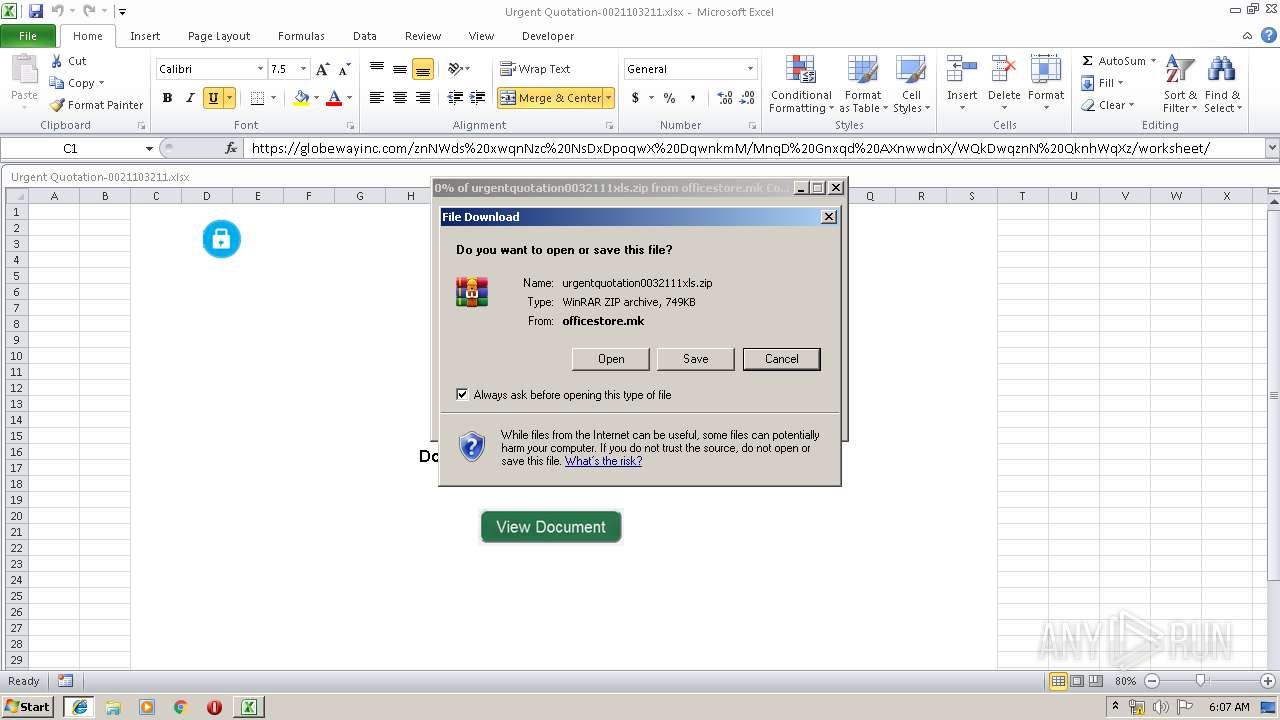
2140 | EXCEL.EXE | GET | — | 88.99.251.203:80 | http://officestore.mk/urgentquotation0032111xls.zip | DE | — | — | malicious |
2596 | iexplore.exe | GET | 200 | 88.99.251.203:80 | http://officestore.mk/urgentquotation0032111xls.zip | DE | compressed | 749 Kb | malicious |
3640 | chrome.exe | GET | 200 | 185.192.249.19:80 | http://r6---sn-quxapm-3c2e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=78.109.23.2&mm=28&mn=sn-quxapm-3c2e&ms=nvh&mt=1558674522&mv=m&pl=20&shardbypass=yes | UA | crx | 842 Kb | whitelisted |
3640 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 508 b | whitelisted |
3640 | chrome.exe | GET | 200 | 8.241.10.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
3640 | chrome.exe | GET | 200 | 8.241.10.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
3640 | chrome.exe | GET | 200 | 8.241.10.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/8CF427FD790C3AD166068DE81E57EFBB932272D4.crt | US | der | 1.06 Kb | whitelisted |
3640 | chrome.exe | GET | 200 | 13.32.24.195:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
1240 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3640 | chrome.exe | GET | 200 | 104.81.127.62:80 | http://ocsp.entrust.net/MEUwQzBBMD8wPTAJBgUrDgMCGgUABBQsSqZpWQuWOxHU9pAda%2B7Lf6V20AQUaJDkZ6SmU4DHhmak8fdLQ%2FuEvW0CBFHTQEQ%3D | NL | der | 1.98 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2140 | EXCEL.EXE | 88.99.251.203:80 | officestore.mk | Hetzner Online GmbH | DE | malicious |
2596 | iexplore.exe | 88.99.251.203:80 | officestore.mk | Hetzner Online GmbH | DE | malicious |
3640 | chrome.exe | 172.217.16.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3640 | chrome.exe | 216.58.209.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3040 | urgentquotation0032111xls.exe | 77.88.21.38:587 | smtp.yandex.com | YANDEX LLC | RU | whitelisted |
3640 | chrome.exe | 172.217.21.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
3640 | chrome.exe | 172.217.16.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3640 | chrome.exe | 216.58.215.78:443 | apis.google.com | Google Inc. | US | whitelisted |
3640 | chrome.exe | 172.217.16.36:443 | www.google.com | Google Inc. | US | whitelisted |
3640 | chrome.exe | 216.58.215.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officestore.mk |
| malicious |
www.bing.com |
| whitelisted |
smtp.yandex.com |
| malicious |
www.google.com.ua |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |