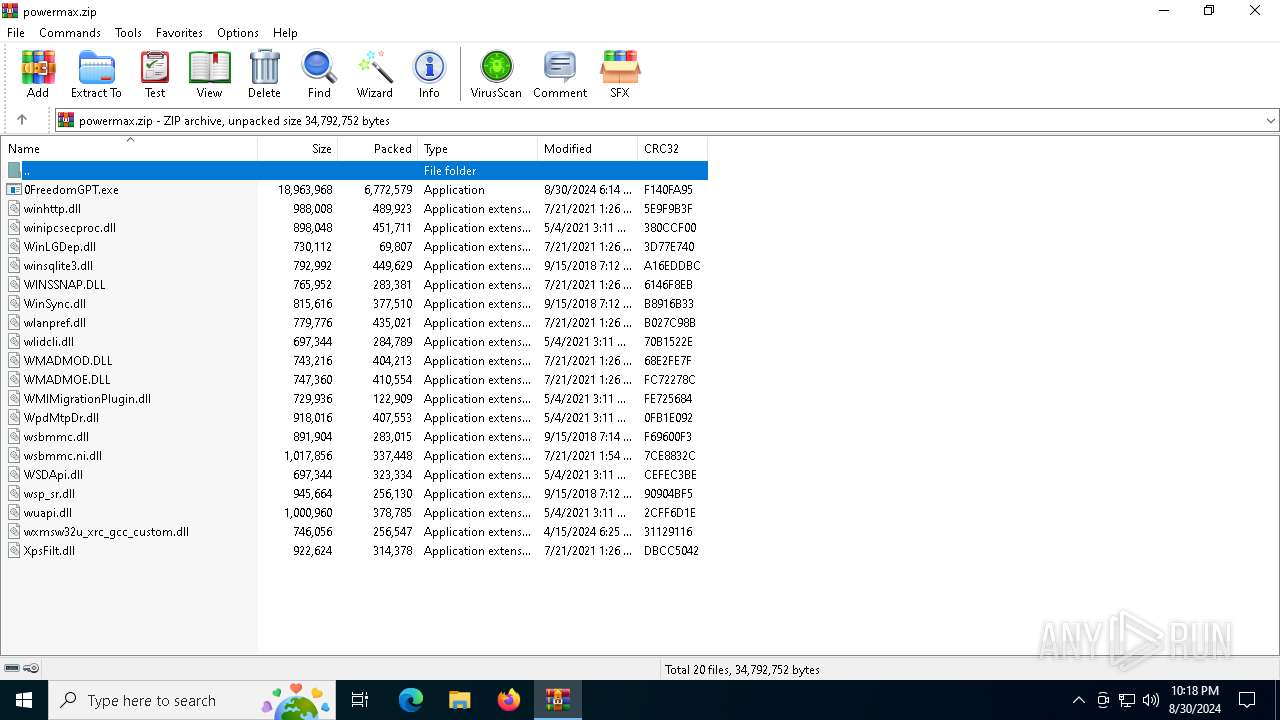
| File name: | powermax.zip |
| Full analysis: | https://app.any.run/tasks/25020c63-0a1f-4637-a62d-7f4255a0c914 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | August 30, 2024, 22:17:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 645F8ECC1AE014B912F66F9C8455708A |
| SHA1: | 65F58067C88FB33F7A2070F857496A22EEA1CE7A |
| SHA256: | 3C05BAE76B7283868C534461A22661949F360EB562D13E2792BEB73187D369E7 |
| SSDEEP: | 98304:GLHEqFqJxCZvEekE6PWasRVd2xJHesUoKLSR97+WrXw6NnrZgRM9KAgAHPC6vNGH:yu/yzLJX7fP/aq1q0wAZCHs5jRgu |
MALICIOUS
Actions looks like stealing of personal data
- BitLockerToGo.exe (PID: 1084)
Stealers network behavior
- BitLockerToGo.exe (PID: 1084)
LUMMA has been detected (SURICATA)
- BitLockerToGo.exe (PID: 1084)
SUSPICIOUS
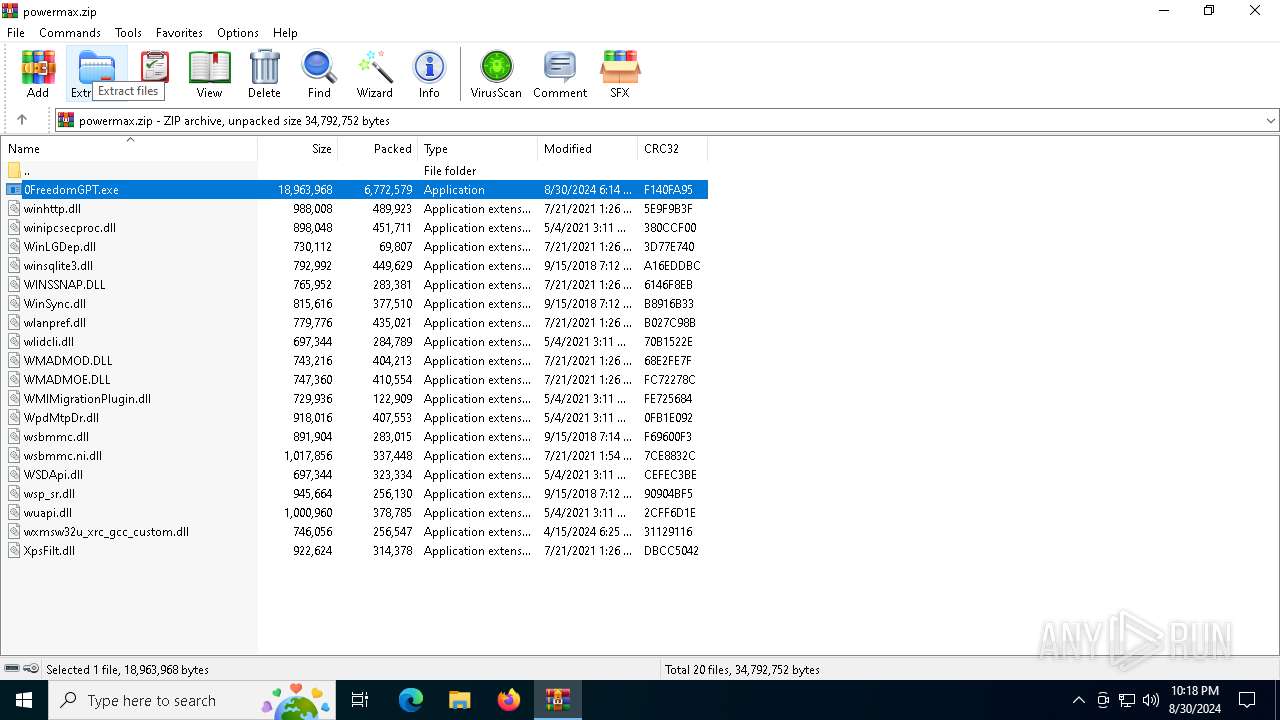
Process drops legitimate windows executable
- WinRAR.exe (PID: 6988)
Searches for installed software
- BitLockerToGo.exe (PID: 1084)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6988)
The process uses the downloaded file
- WinRAR.exe (PID: 6988)
Create files in a temporary directory
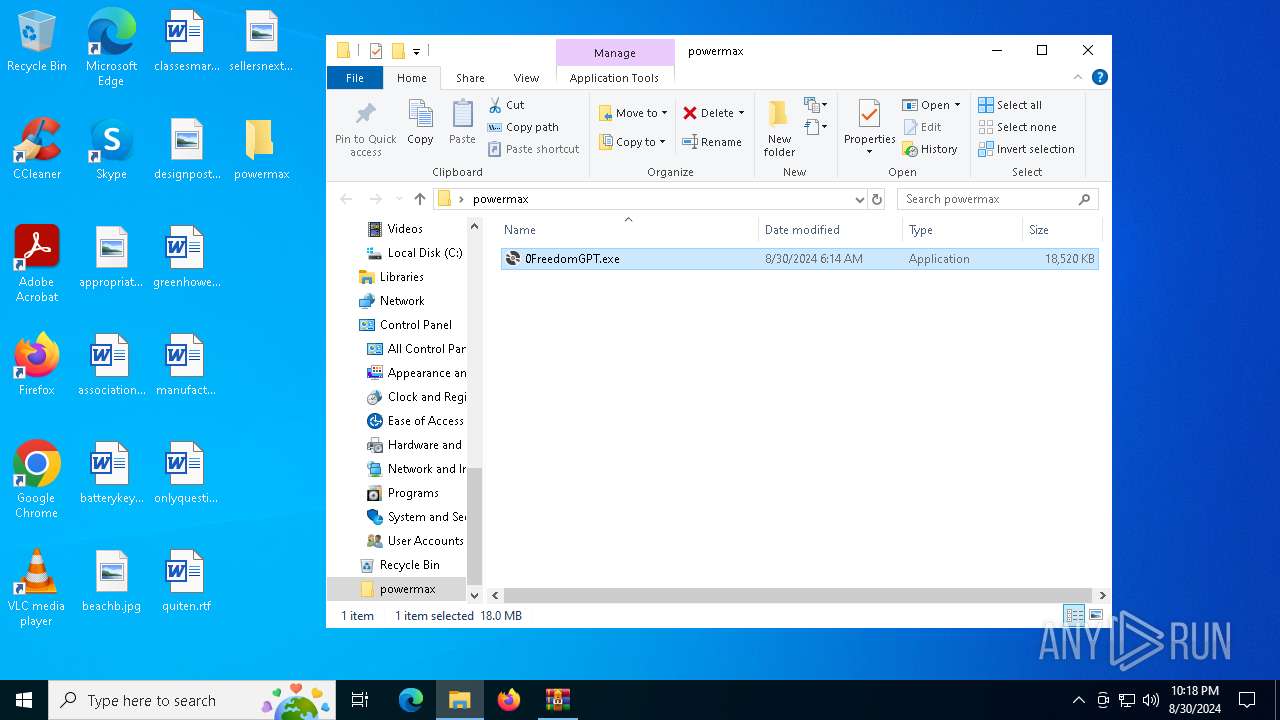
- 0FreedomGPT.exe (PID: 1436)
Checks supported languages
- 0FreedomGPT.exe (PID: 1436)
- BitLockerToGo.exe (PID: 1084)
Manual execution by a user
- 0FreedomGPT.exe (PID: 1436)
Reads the software policy settings
- BitLockerToGo.exe (PID: 1084)
Reads the computer name
- BitLockerToGo.exe (PID: 1084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:08:30 11:14:32 |
| ZipCRC: | 0xf140fa95 |
| ZipCompressedSize: | 6772579 |
| ZipUncompressedSize: | 18963968 |
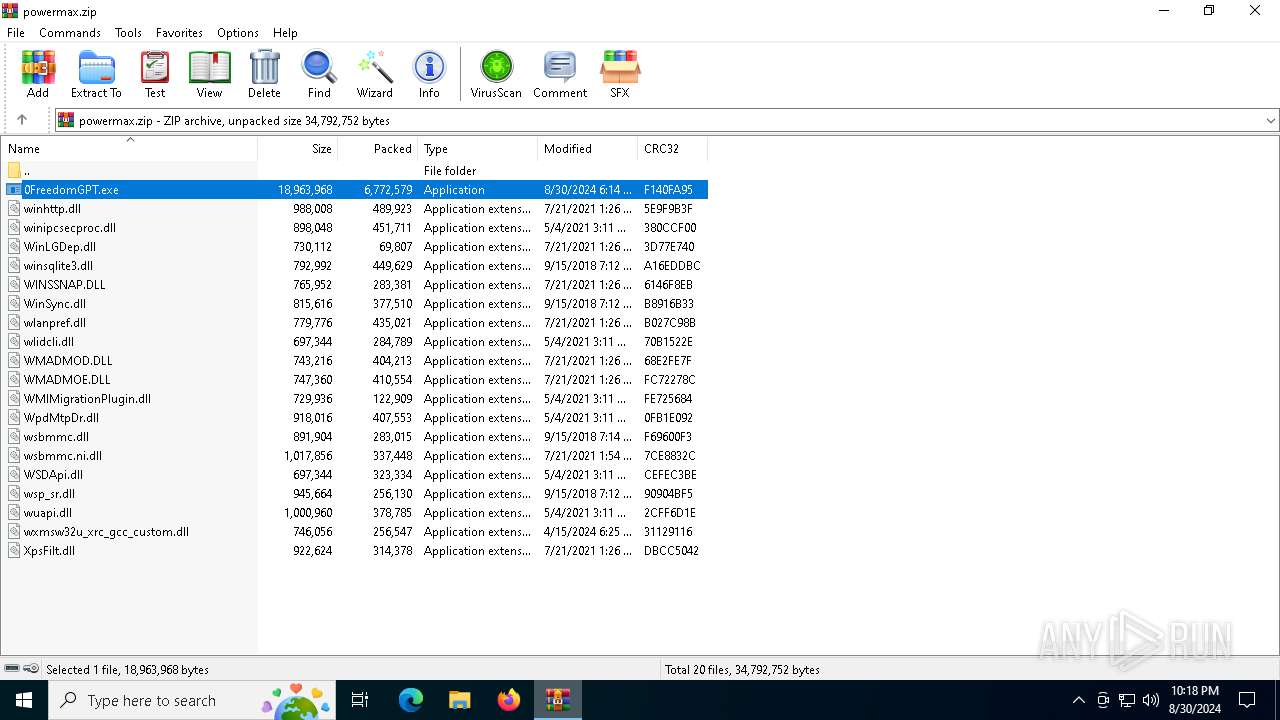
| ZipFileName: | 0FreedomGPT.exe |
Total processes
130
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1084 | "C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe" | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | 0FreedomGPT.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BitLocker To Go Reader Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
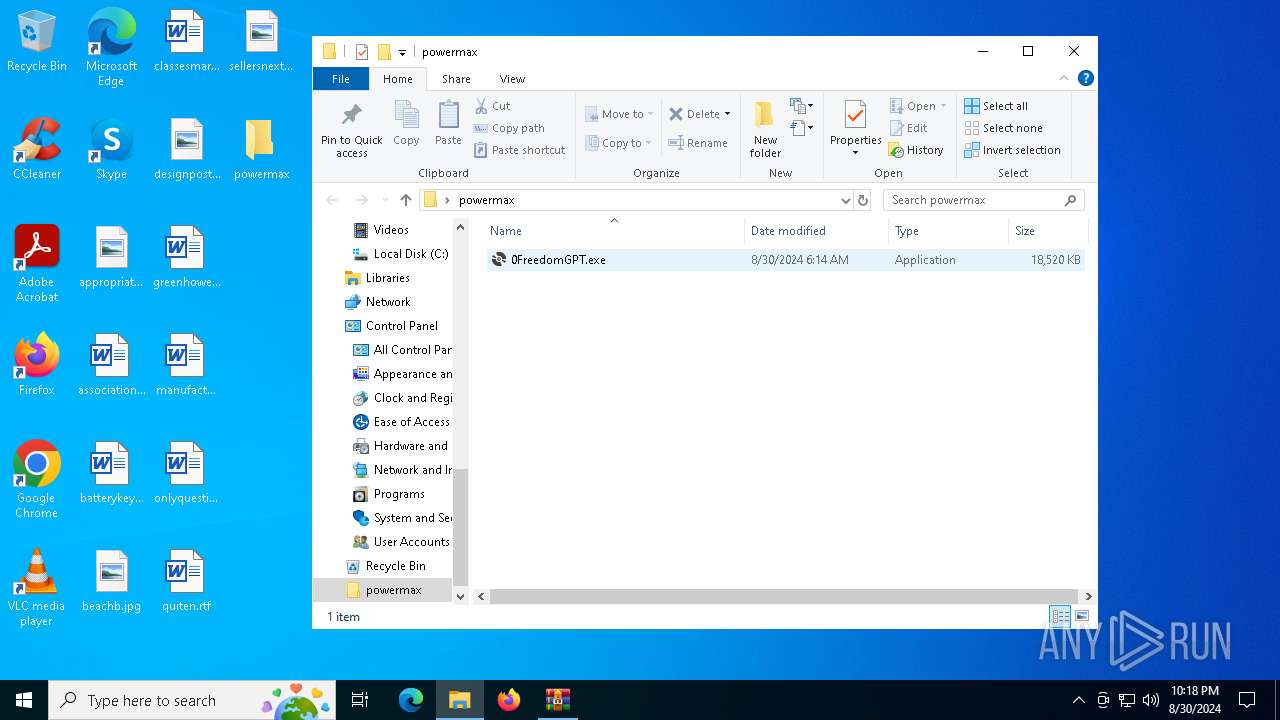
| 1436 | "C:\Users\admin\Desktop\powermax\0FreedomGPT.exe" | C:\Users\admin\Desktop\powermax\0FreedomGPT.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Exit code: 666 Version: 17.0.34511.75 built by: d17.9 Modules
| |||||||||||||||
| 2636 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6196 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
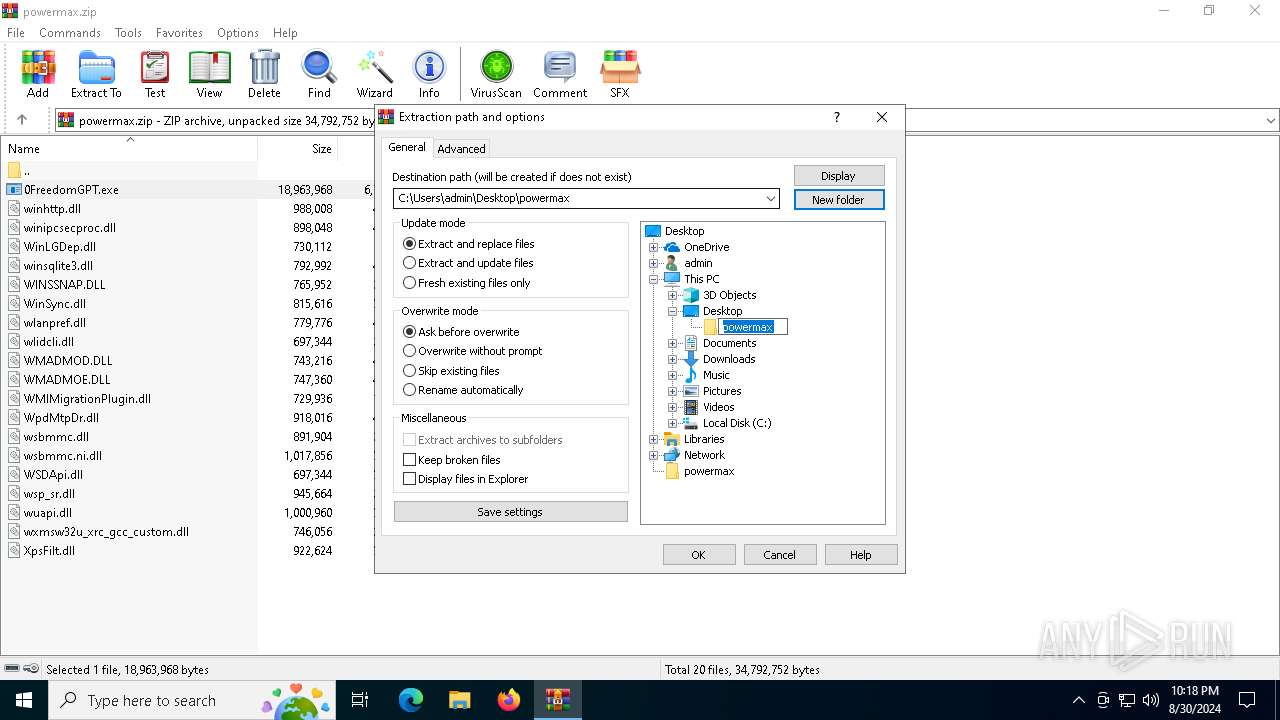
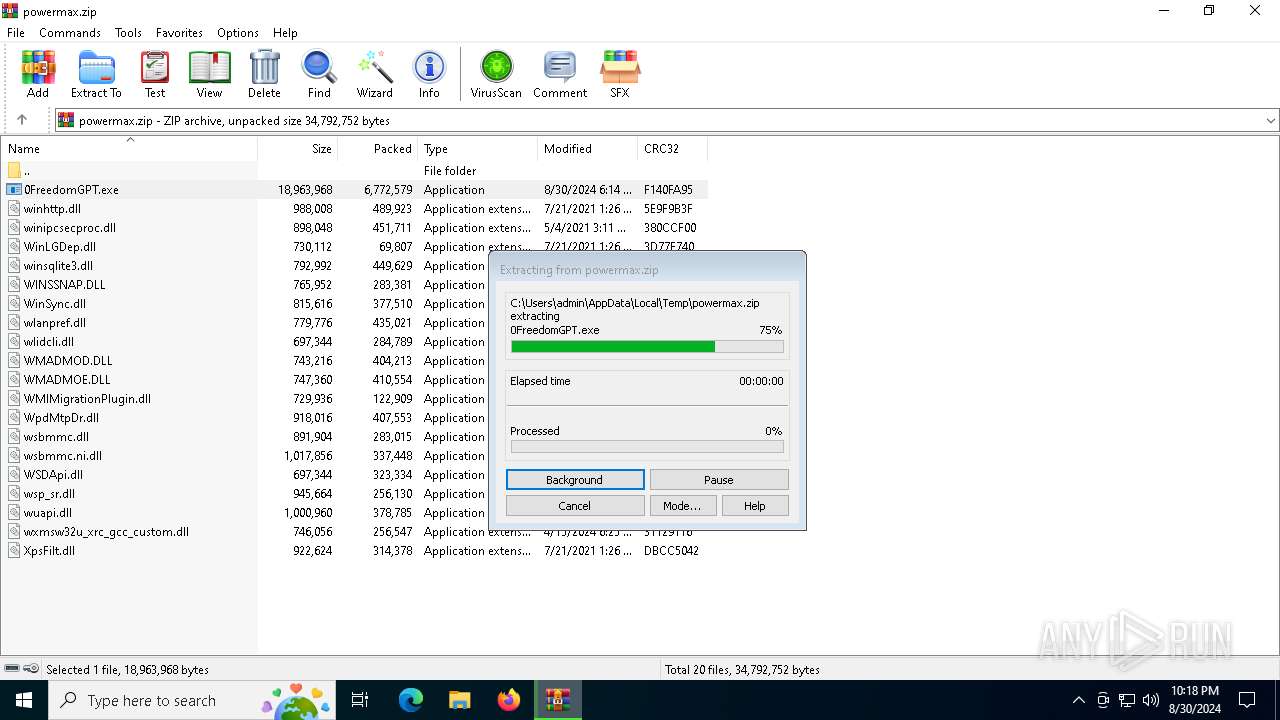
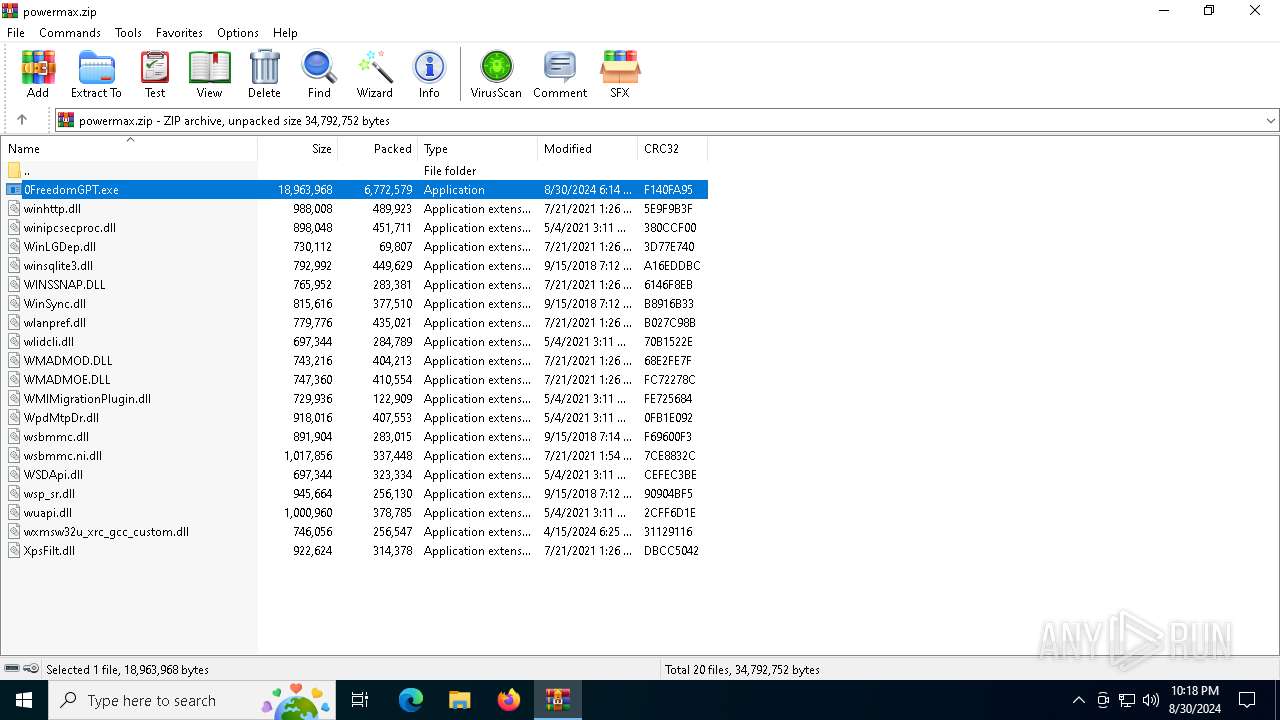
| 6988 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\powermax.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
7 807
Read events
7 552
Write events
255
Delete events
0
Modification events
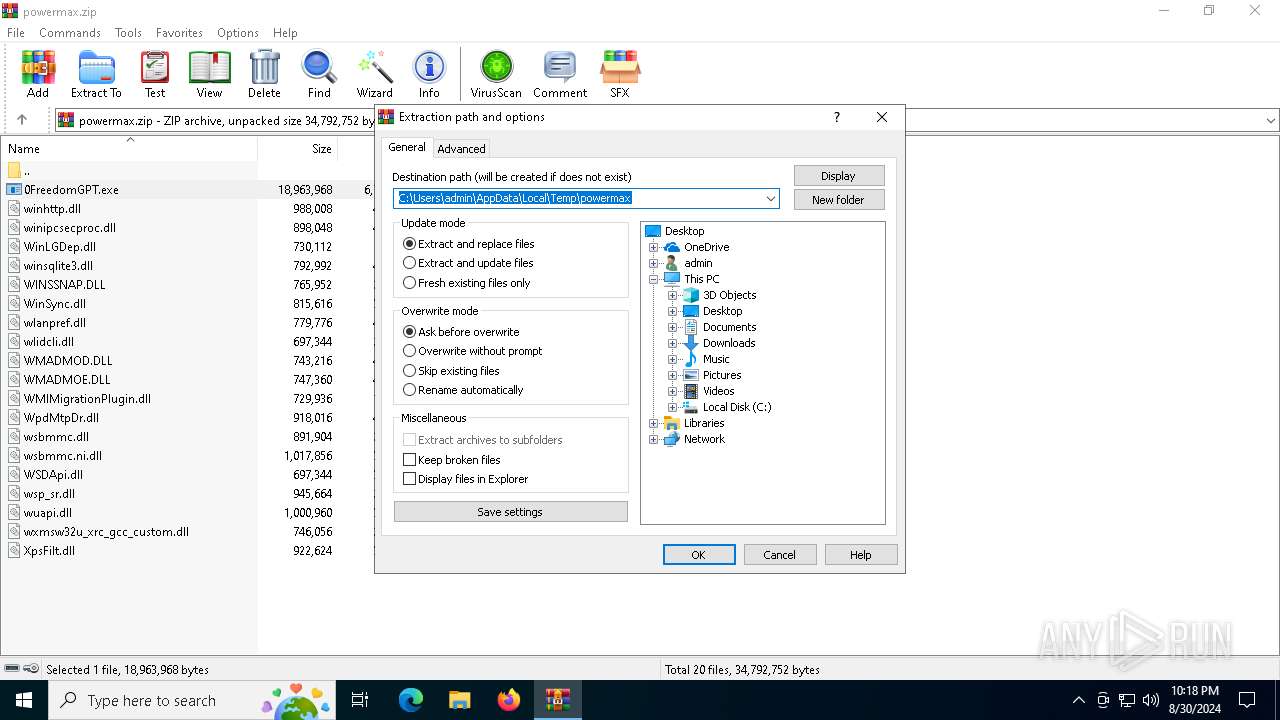
| (PID) Process: | (6988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\powermax.zip | |||
| (PID) Process: | (6988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6988) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\powermax | |||
| (PID) Process: | (1436) 0FreedomGPT.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | C:\WINDOWS\system32\,@tzres.dll,-462 |
Value: Afghanistan Standard Time | |||
Executable files
1
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6988 | WinRAR.exe | C:\Users\admin\Desktop\powermax\0FreedomGPT.exe | executable | |
MD5:E497B52BACB149C23EB2B37AADE56179 | SHA256:4913643B824A1C11630F88CB3B10D803B208B7A58463753156F1D07A7503AB6C | |||
| 1436 | 0FreedomGPT.exe | C:\Users\admin\AppData\Local\Temp\jsii-runtime.413025486\lib\program.js.map | har | |
MD5:CC6BC0F86592E7EB6202686AD266D896 | SHA256:6AE71D00EBFD9C8810B03D8A1E9939D4973FD846166A9F926BAF0E96624F1317 | |||
| 1436 | 0FreedomGPT.exe | C:\Users\admin\AppData\Local\Temp\jsii-runtime.413025486\bin\jsii-runtime.js | text | |
MD5:A7C8367F8B900617374F5D3FAC86DFD7 | SHA256:E4F82DB7579D84B2DDB49B16A8CBD8256D86751473D1A86B4B31D1E3963BA0FA | |||
| 1436 | 0FreedomGPT.exe | C:\Users\admin\AppData\Local\Temp\jsii-runtime.413025486\lib\program.js | text | |
MD5:9842A50D94DC0D72A507F11BF4ED8E04 | SHA256:C5BB8FAA8B90560BE019BB48B287CE05D3C89C747118609436D47794061B2607 | |||
| 1436 | 0FreedomGPT.exe | C:\Users\admin\AppData\Local\Temp\jsii-runtime.413025486\bin\jsii-runtime.js.map | har | |
MD5:0FEFBA04D8BBEDD2CFF7EB75C3834847 | SHA256:DBBDB23093B0732EE1504F79D3835B1C6B2E3F526AB42A6DA381E6CEC2648AE5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
31
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4164 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5400 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5400 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6552 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4164 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4164 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
circullateiosn.shop |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1084 | BitLockerToGo.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |