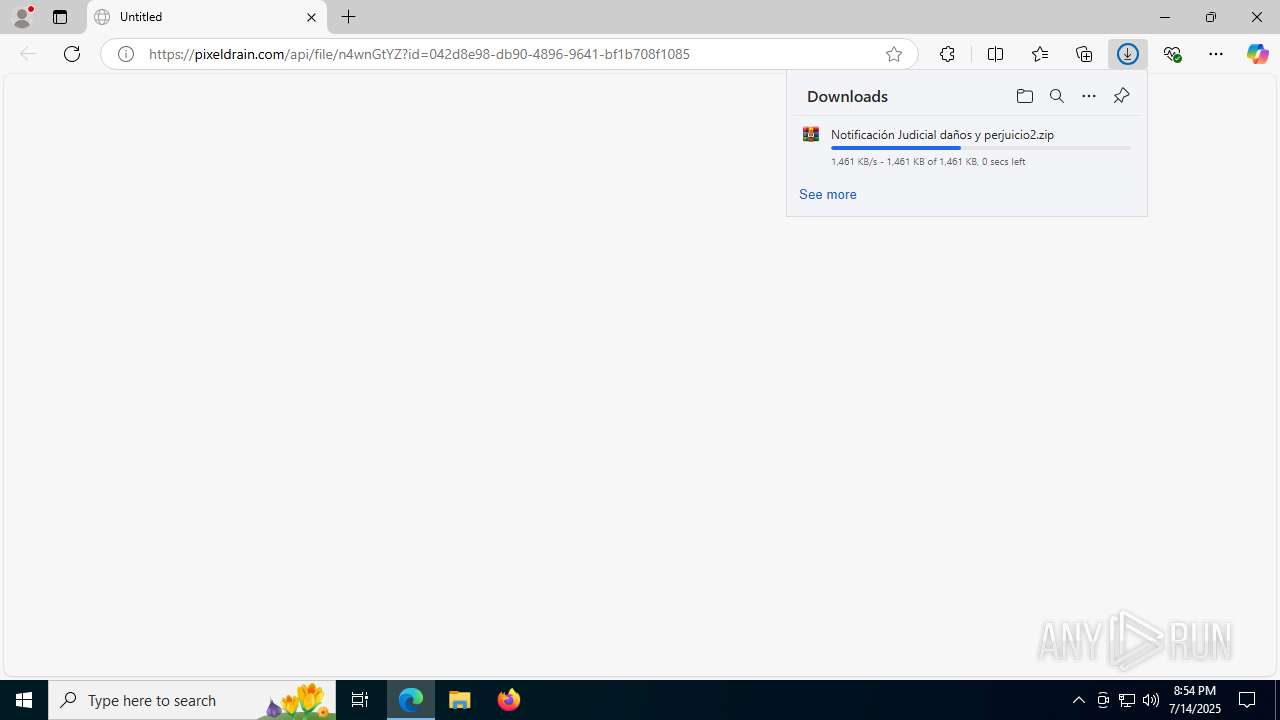
| URL: | https://pixeldrain.com/api/file/n4wnGtYZ?id=042d8e98-db90-4896-9641-bf1b708f1085 |
| Full analysis: | https://app.any.run/tasks/1402362a-b2b6-4ca9-ac12-49a235bb66c9 |
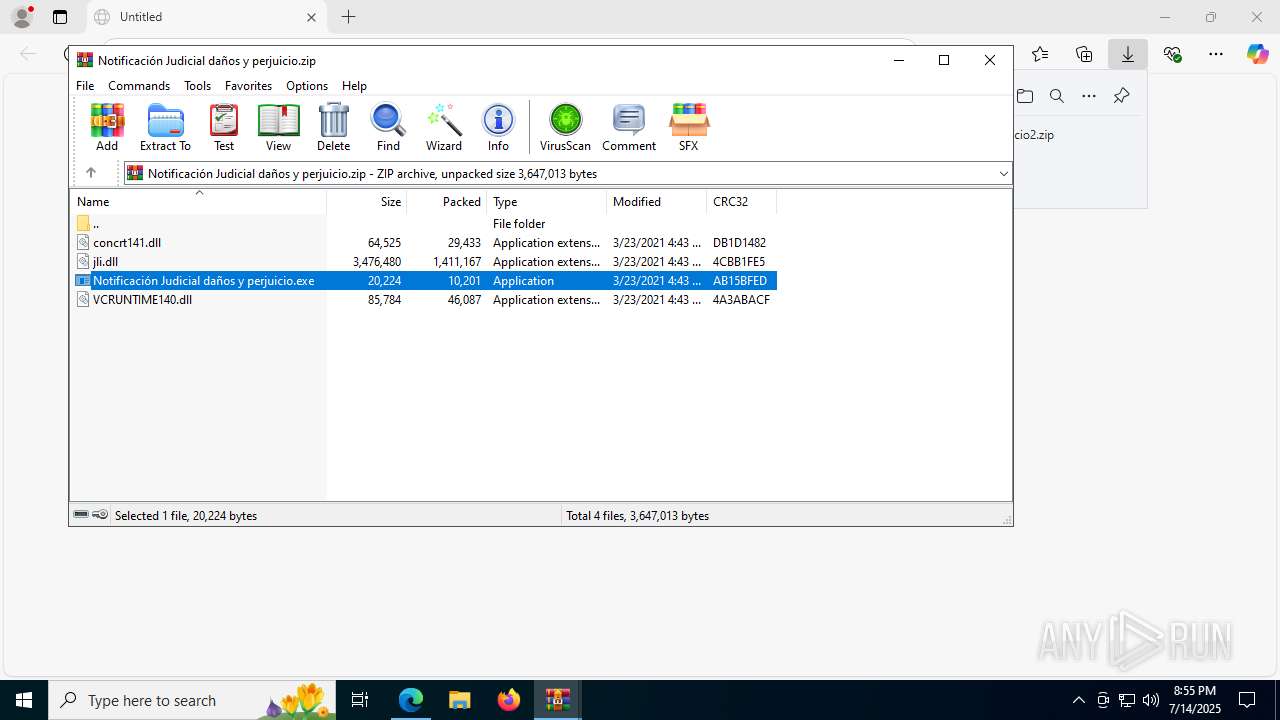
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | July 14, 2025, 20:53:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 59353E2E937678A7AA970C39AC7FBE3A |
| SHA1: | 42ED4D12D6C005C23C1E843D0BD52C2BAA55DD62 |
| SHA256: | 3B10B67E503AB831C748AB191BAF096261BC13048AACFF9D790649A529E2E16B |
| SSDEEP: | 3:N8Icl/GK09J7SA6YHB7cTAIZV2S:2IG/d0bSA6qeTtP |
MALICIOUS
Changes the autorun value in the registry
- Notificación Judicial daños y perjuicio.exe (PID: 8108)
ASYNCRAT has been detected (MUTEX)
- InstallUtil.exe (PID: 1496)
Steals credentials from Web Browsers
- InstallUtil.exe (PID: 1496)
Actions looks like stealing of personal data
- InstallUtil.exe (PID: 1496)
ASYNCRAT has been detected (SURICATA)
- InstallUtil.exe (PID: 1496)
ASYNCRAT has been detected (YARA)
- InstallUtil.exe (PID: 1496)
SUSPICIOUS
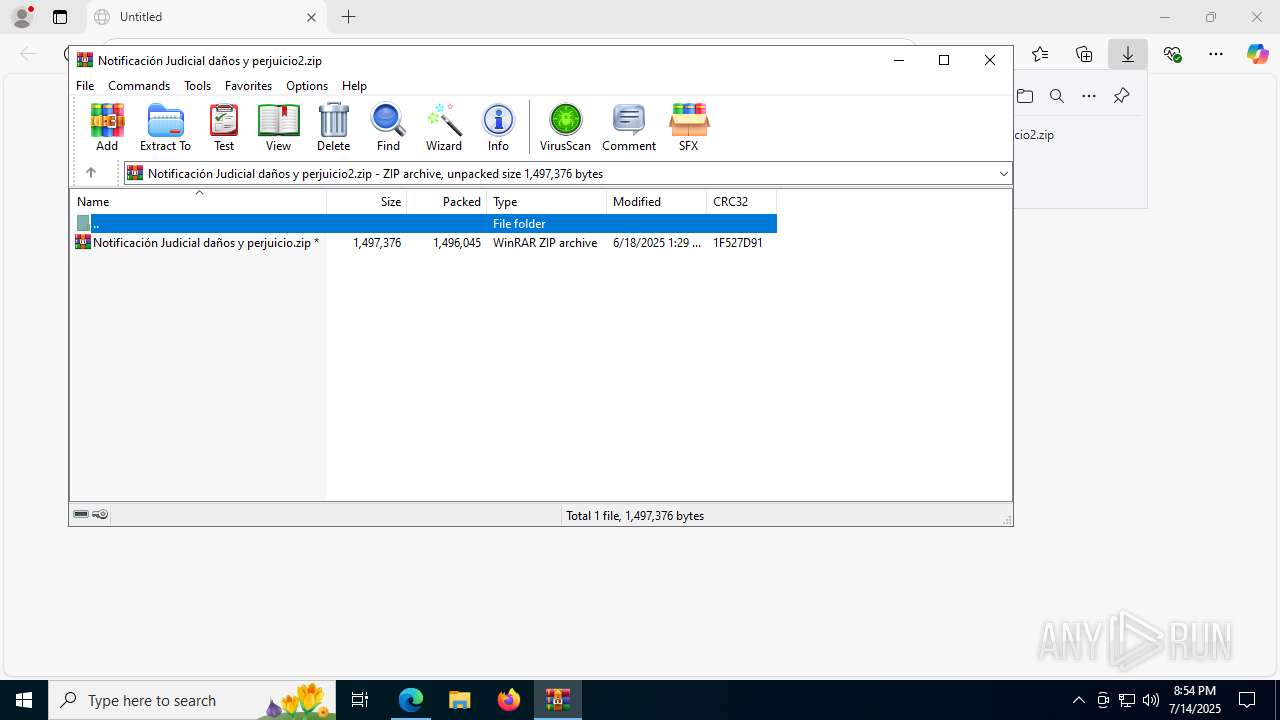
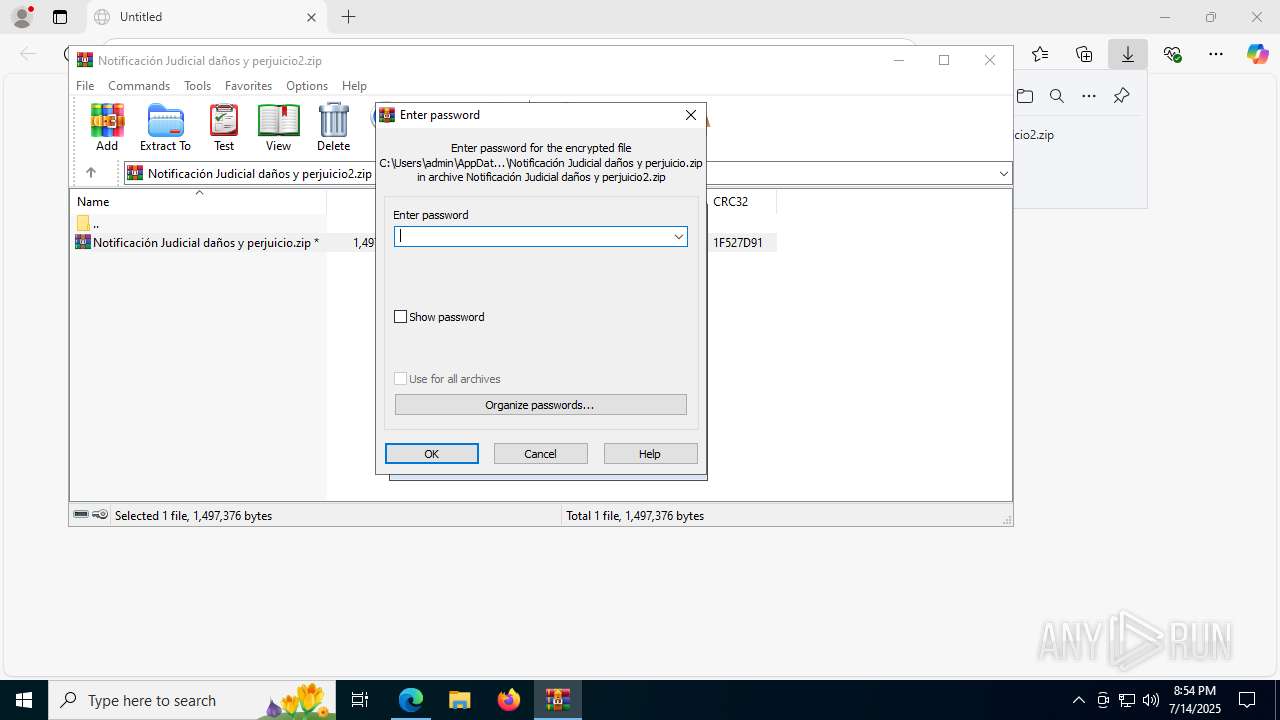
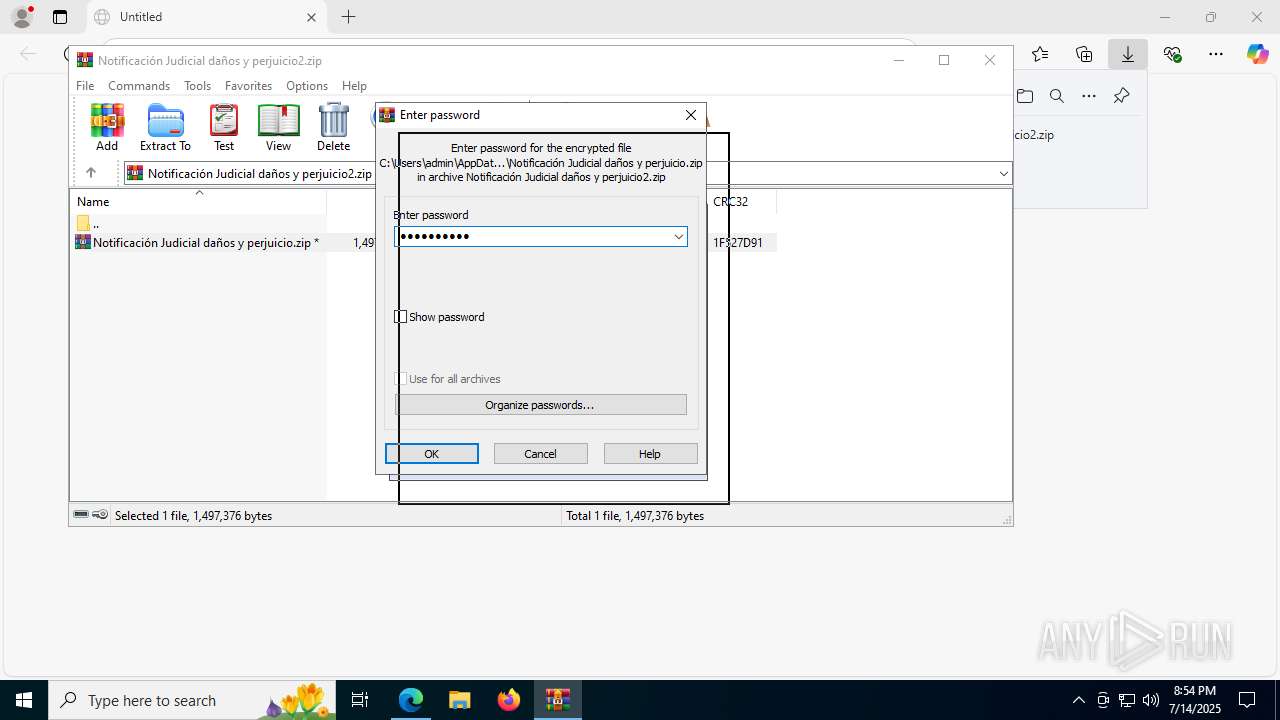
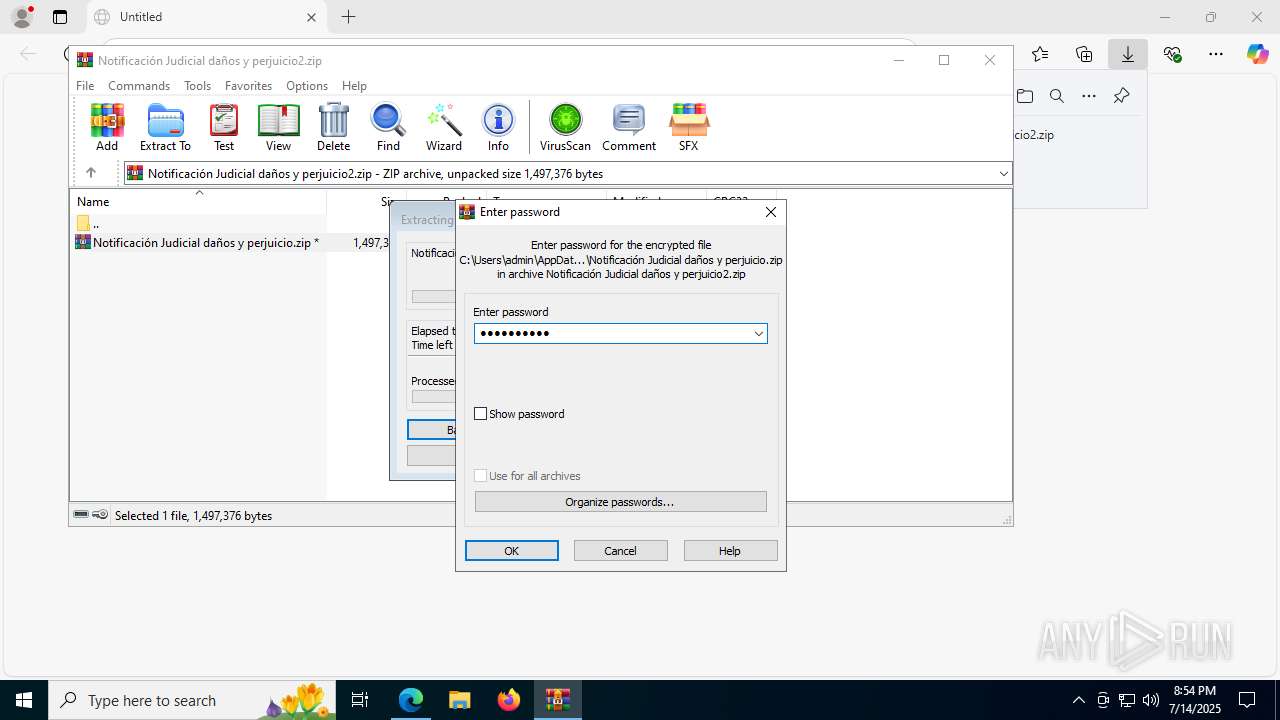
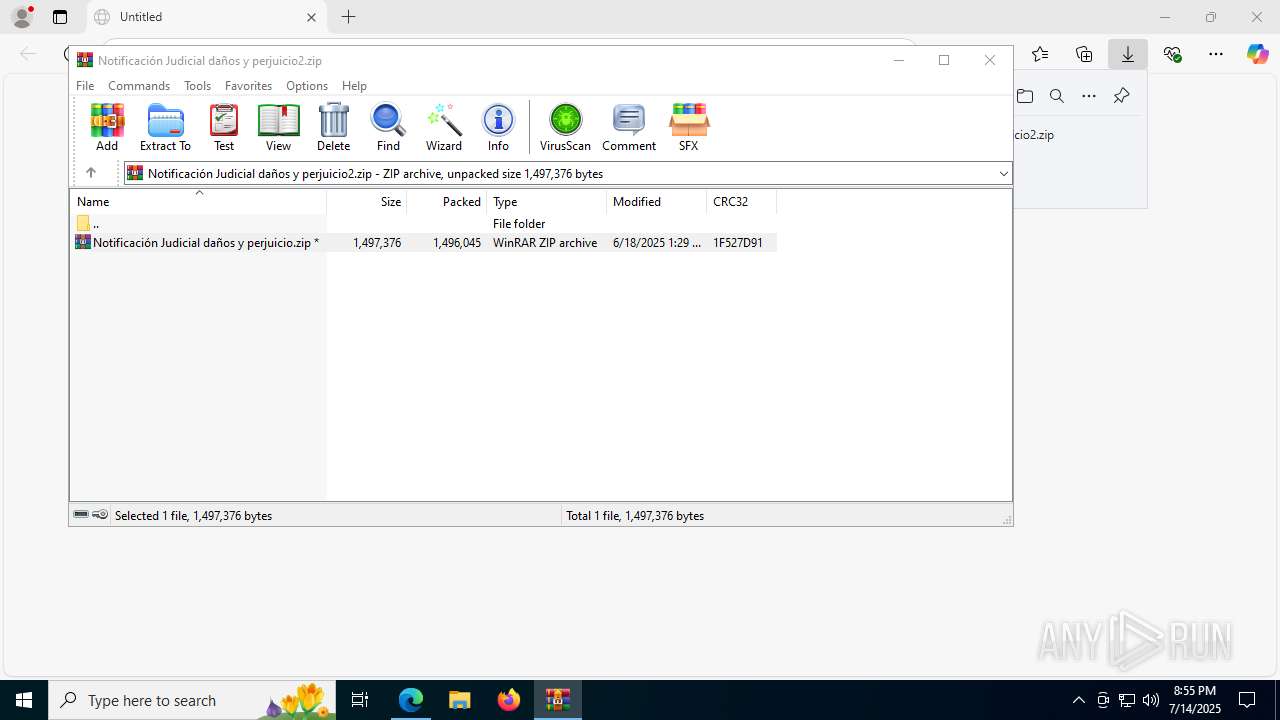
Process drops legitimate windows executable
- WinRAR.exe (PID: 7860)
- WinRAR.exe (PID: 7632)
- Notificación Judicial daños y perjuicio.exe (PID: 8108)
Application launched itself
- WinRAR.exe (PID: 7860)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7860)
- WinRAR.exe (PID: 7632)
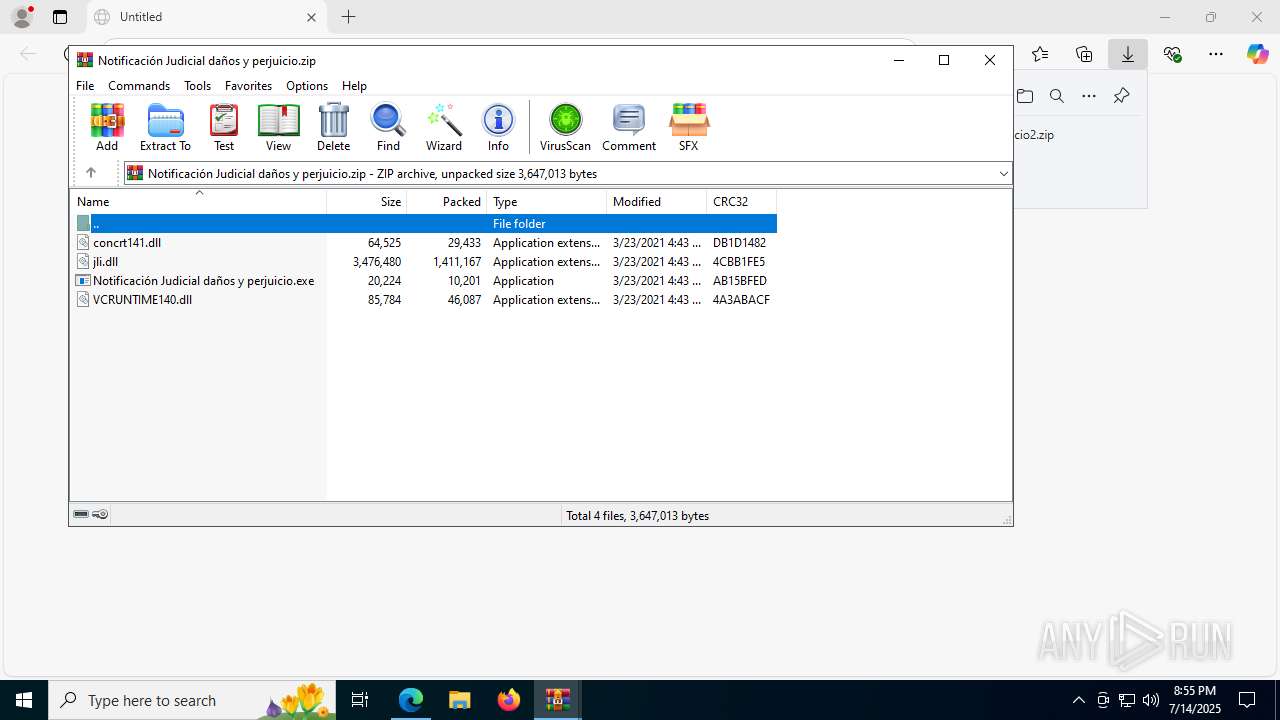
The process drops C-runtime libraries
- Notificación Judicial daños y perjuicio.exe (PID: 8108)
Contacting a server suspected of hosting an CnC
- InstallUtil.exe (PID: 1496)
Connects to unusual port
- InstallUtil.exe (PID: 1496)
Executable content was dropped or overwritten
- Notificación Judicial daños y perjuicio.exe (PID: 8108)
INFO
Launching a file from a Registry key
- Notificación Judicial daños y perjuicio.exe (PID: 8108)
Reads Environment values
- identity_helper.exe (PID: 7448)
Application launched itself
- msedge.exe (PID: 6648)
The sample compiled with english language support
- WinRAR.exe (PID: 7860)
- WinRAR.exe (PID: 7632)
- Notificación Judicial daños y perjuicio.exe (PID: 8108)
Checks supported languages
- Notificación Judicial daños y perjuicio.exe (PID: 8108)
- InstallUtil.exe (PID: 1496)
- identity_helper.exe (PID: 7448)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7632)
Reads the computer name
- InstallUtil.exe (PID: 1496)
- Notificación Judicial daños y perjuicio.exe (PID: 8108)
- identity_helper.exe (PID: 7448)
Reads the machine GUID from the registry
- InstallUtil.exe (PID: 1496)
Reads the software policy settings
- InstallUtil.exe (PID: 1496)
- slui.exe (PID: 7136)
Checks proxy server information
- slui.exe (PID: 7136)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(1496) InstallUtil.exe
C2 (1)enviojs2025.kozow.com
Ports (1)8000
Version| CRACKED BY https://t.me/xworm_v2
Options
AutoRunfalse
MutexAsyncMutex_6SI8OkPnk
InstallFolder%AppData%
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAOQb7nA/hP/L1XXxqdDJNzANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjMwNTI1MDUyMTIyWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAIykAVxs0s6rZ/dwP6ujJtpnj6RSsCsZN6Cfj1InZxSIswX+zNiKJys8xyLlyexoya3ebLp5gOSz...
Server_SignatureXBEQknkdRJdCU8tSSoQePYR8tR77JiZC3ekd7ltgMsyr1lnwFfemdG5htutVTi+x1DEr3jCOLkKOABN8cwn9ohDmzt6EYCNCyD6MUulkf2Fm9ARNgbunSbZoa3tGcyZoXJHwbGlSbB+rczlc9do9UU8Z5XhmvsVlZEb3Uy5Ki6dTjuSuwTZbeoz2xSCTt1ucouXDUfcSz38LGmSv+0aehVTC9uuLSe8rk1KFGqMgW47aPebn9bn4NVIQEkvwGvvFnj5eqz+dq77OaRHhxWDz2OFotHlvnS1jB08elYUwbE29...
Keys
AES621c325006b09e078df69a02ebc405375b0bffee121e81a4c18220292c187042
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
Total processes
175
Monitored processes
37
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3360,i,3857003353417714505,4485407334728269206,262144 --variations-seed-version --mojo-platform-channel-handle=3644 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1332 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3240,i,3857003353417714505,4485407334728269206,262144 --variations-seed-version --mojo-platform-channel-handle=7208 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1380 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | — | Notificación Judicial daños y perjuicio.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Version: 4.8.9037.0 built by: NET481REL1 | |||||||||||||||
| 1496 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\installutil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | Notificación Judicial daños y perjuicio.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Version: 4.8.9037.0 built by: NET481REL1 Modules
AsyncRat(PID) Process(1496) InstallUtil.exe C2 (1)enviojs2025.kozow.com Ports (1)8000 Version| CRACKED BY https://t.me/xworm_v2 Options AutoRunfalse MutexAsyncMutex_6SI8OkPnk InstallFolder%AppData% Certificates Cert1MIIE8jCCAtqgAwIBAgIQAOQb7nA/hP/L1XXxqdDJNzANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjMwNTI1MDUyMTIyWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAIykAVxs0s6rZ/dwP6ujJtpnj6RSsCsZN6Cfj1InZxSIswX+zNiKJys8xyLlyexoya3ebLp5gOSz... Server_SignatureXBEQknkdRJdCU8tSSoQePYR8tR77JiZC3ekd7ltgMsyr1lnwFfemdG5htutVTi+x1DEr3jCOLkKOABN8cwn9ohDmzt6EYCNCyD6MUulkf2Fm9ARNgbunSbZoa3tGcyZoXJHwbGlSbB+rczlc9do9UU8Z5XhmvsVlZEb3Uy5Ki6dTjuSuwTZbeoz2xSCTt1ucouXDUfcSz38LGmSv+0aehVTC9uuLSe8rk1KFGqMgW47aPebn9bn4NVIQEkvwGvvFnj5eqz+dq77OaRHhxWDz2OFotHlvnS1jB08elYUwbE29... Keys AES621c325006b09e078df69a02ebc405375b0bffee121e81a4c18220292c187042 Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 | |||||||||||||||
| 1976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5524,i,3857003353417714505,4485407334728269206,262144 --variations-seed-version --mojo-platform-channel-handle=5044 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2604 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc43a1f208,0x7ffc43a1f214,0x7ffc43a1f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3648 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2768,i,3857003353417714505,4485407334728269206,262144 --variations-seed-version --mojo-platform-channel-handle=2600 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4788 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=944,i,3857003353417714505,4485407334728269206,262144 --variations-seed-version --mojo-platform-channel-handle=2436 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4828 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5920,i,3857003353417714505,4485407334728269206,262144 --variations-seed-version --mojo-platform-channel-handle=1340 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
13 513
Read events
13 482
Write events
31
Delete events
0
Modification events
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7520B72480982F00 | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328406 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1E7D422E-1261-41C6-8182-A3FA793D6653} | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328406 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {665BB4AC-45FF-456B-B1EF-7225E338340F} | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D9CFC82480982F00 | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
6
Suspicious files
99
Text files
67
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF17542b.TMP | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF17542b.TMP | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17544a.TMP | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF175469.TMP | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF175479.TMP | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
54
DNS requests
59
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6128 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:j8Qo4CiJll5CLh7XZJcKVNcJrioKy3XjYuvhLkQ6IS8&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2668 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8164 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8164 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7808 | svchost.exe | HEAD | 200 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1752582423&P2=404&P3=2&P4=Rks1QaIG2hNczuipbjaGqCr39qEDR6NxkS8prqercxCPriZ%2bc%2fjs5F1t22dAa8fvm%2fFvDKy7uCZxVp5%2bhPw98Q%3d%3d | unknown | — | — | whitelisted |
7808 | svchost.exe | HEAD | 200 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752586019&P2=404&P3=2&P4=DBCjdp1s8zgMEG8l4oUTOPcFsgxxzRVc5LHKzissVGrGweJhN6fW5rkVpdCliW2tCgaCIk4bmLjPseWbDCHrBA%3d%3d | unknown | — | — | whitelisted |
7808 | svchost.exe | GET | 206 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1752582423&P2=404&P3=2&P4=Rks1QaIG2hNczuipbjaGqCr39qEDR6NxkS8prqercxCPriZ%2bc%2fjs5F1t22dAa8fvm%2fFvDKy7uCZxVp5%2bhPw98Q%3d%3d | unknown | — | — | whitelisted |
7808 | svchost.exe | GET | 206 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752586019&P2=404&P3=2&P4=DBCjdp1s8zgMEG8l4oUTOPcFsgxxzRVc5LHKzissVGrGweJhN6fW5rkVpdCliW2tCgaCIk4bmLjPseWbDCHrBA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3588 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6128 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6128 | msedge.exe | 203.23.179.11:443 | pixeldrain.com | GSL Networks Pty LTD | DE | whitelisted |
6128 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6128 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6128 | msedge.exe | 92.123.104.63:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
pixeldrain.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
www.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6128 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
6128 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
6128 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
2200 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.kozow .com Domain |
1496 | InstallUtil.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
1496 | InstallUtil.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
1496 | InstallUtil.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
1496 | InstallUtil.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |