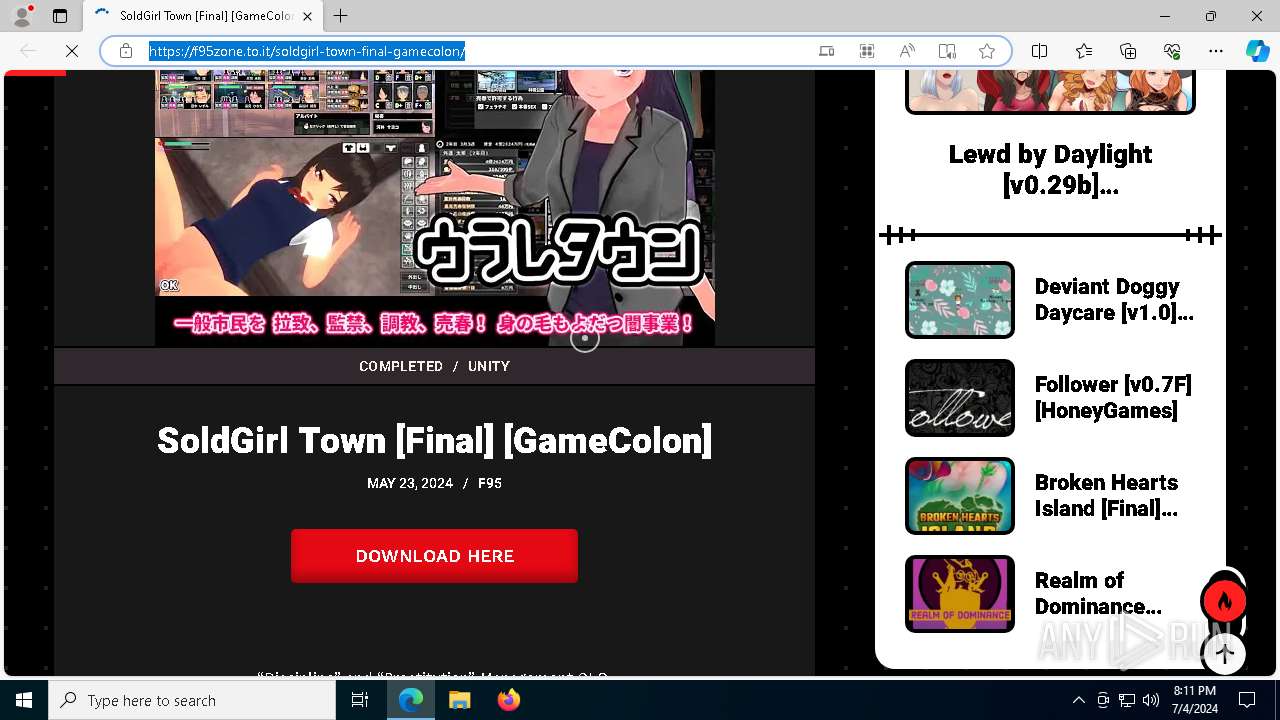
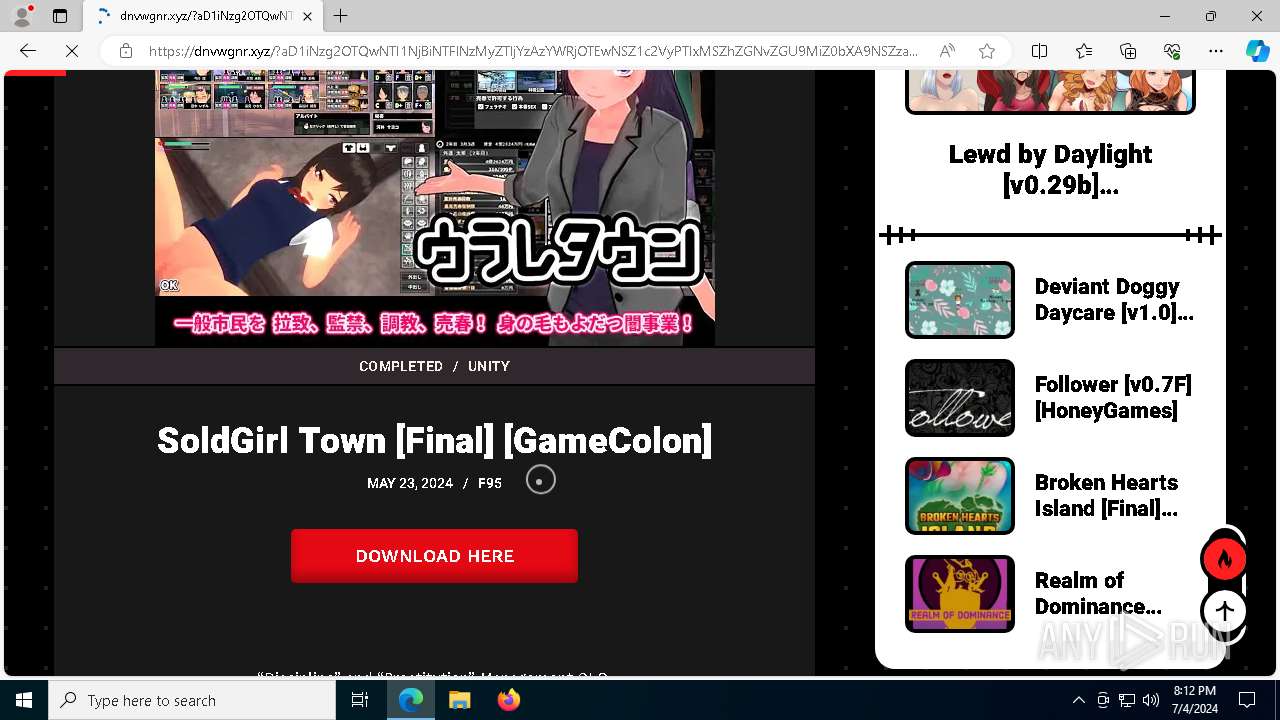
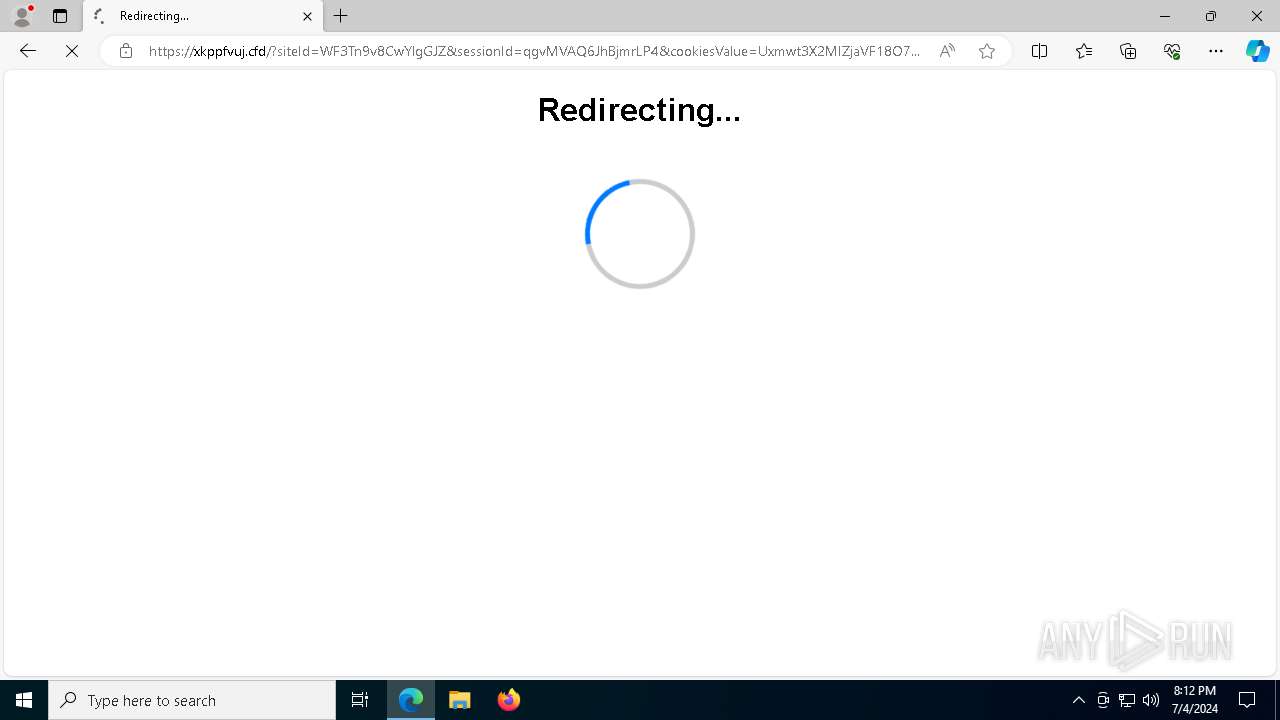
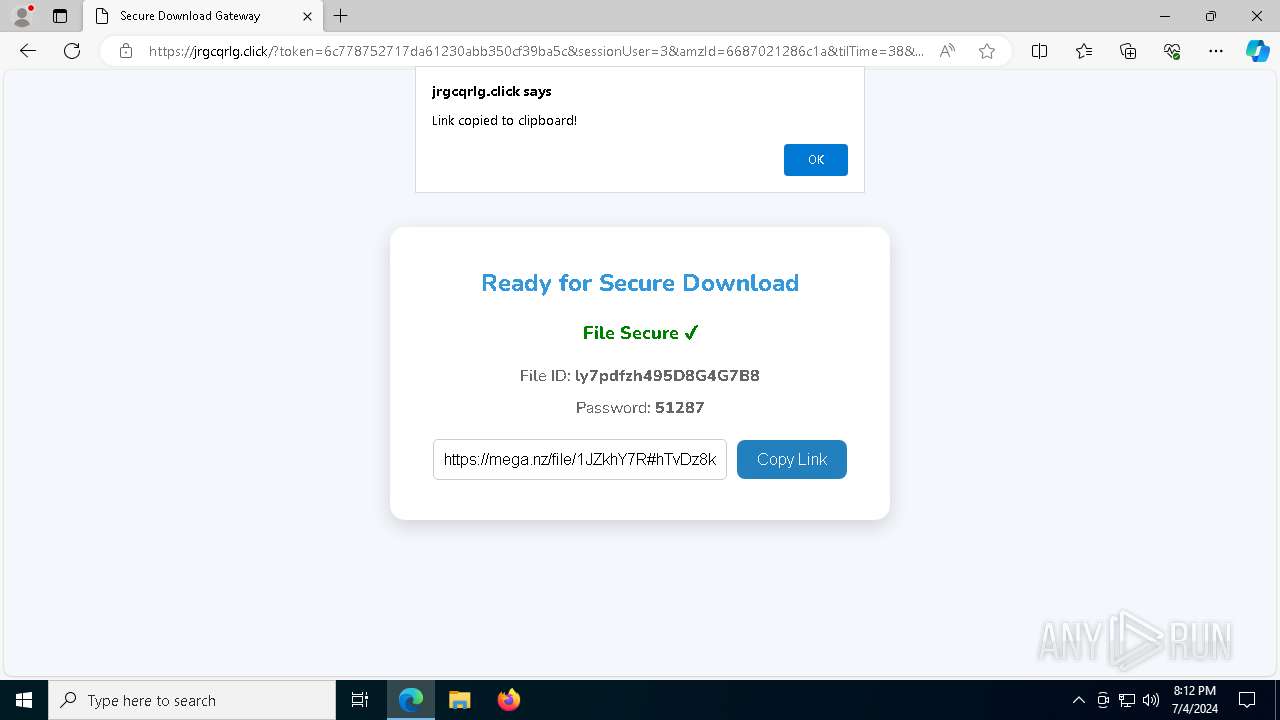
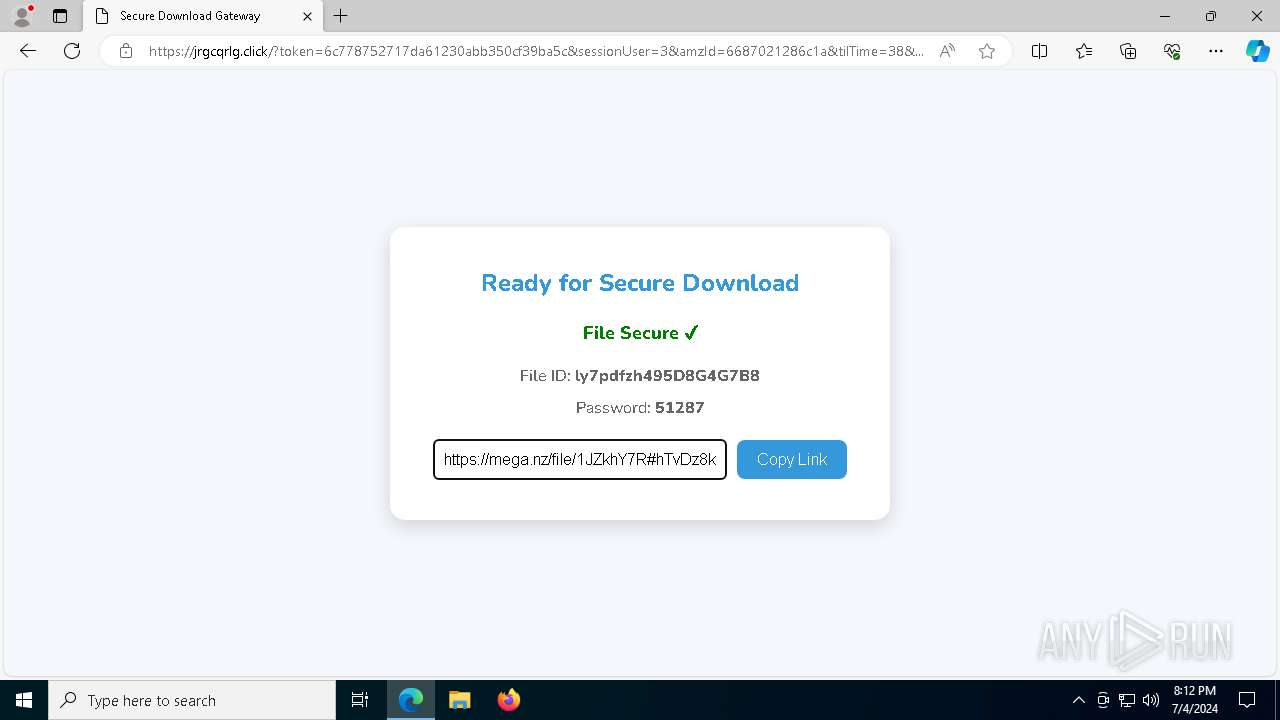
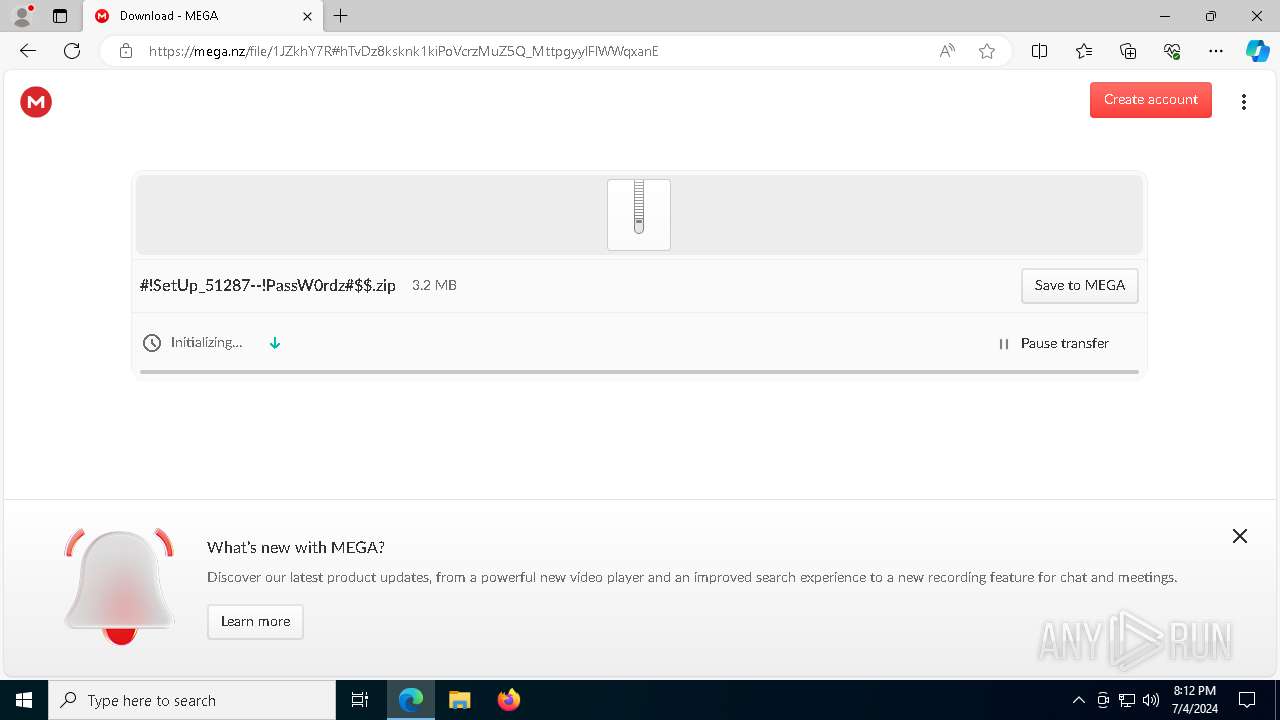
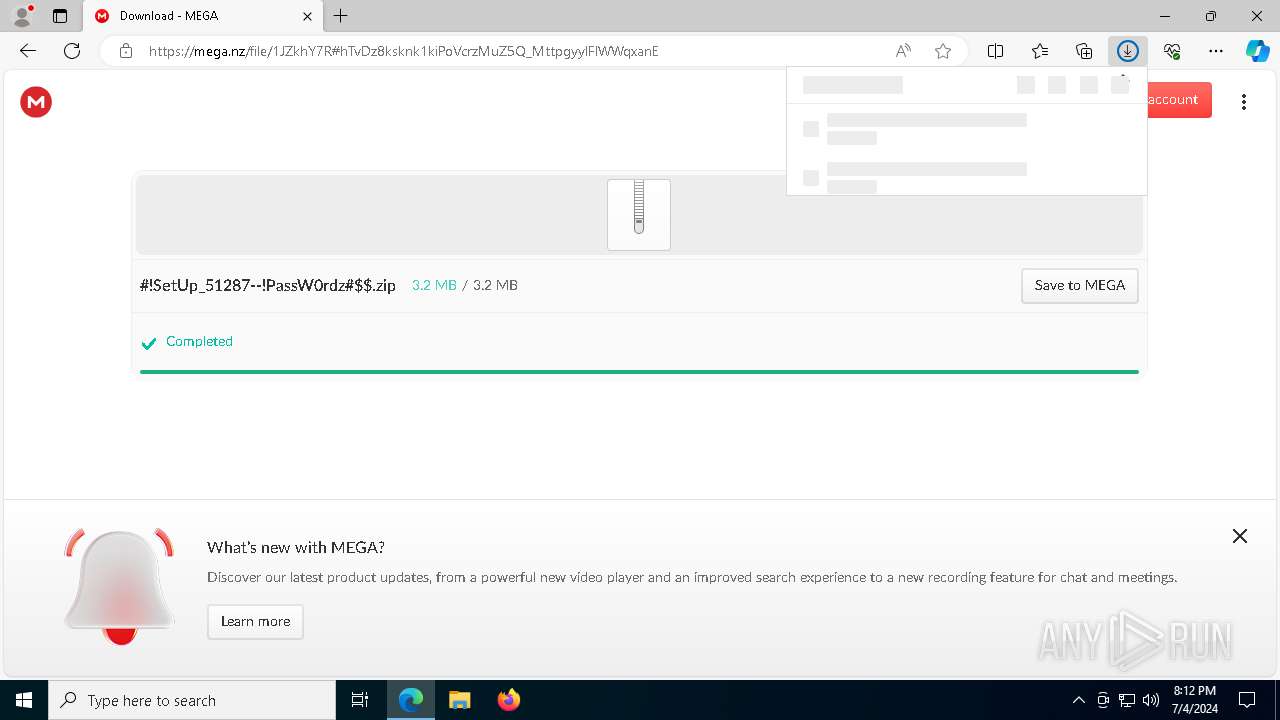
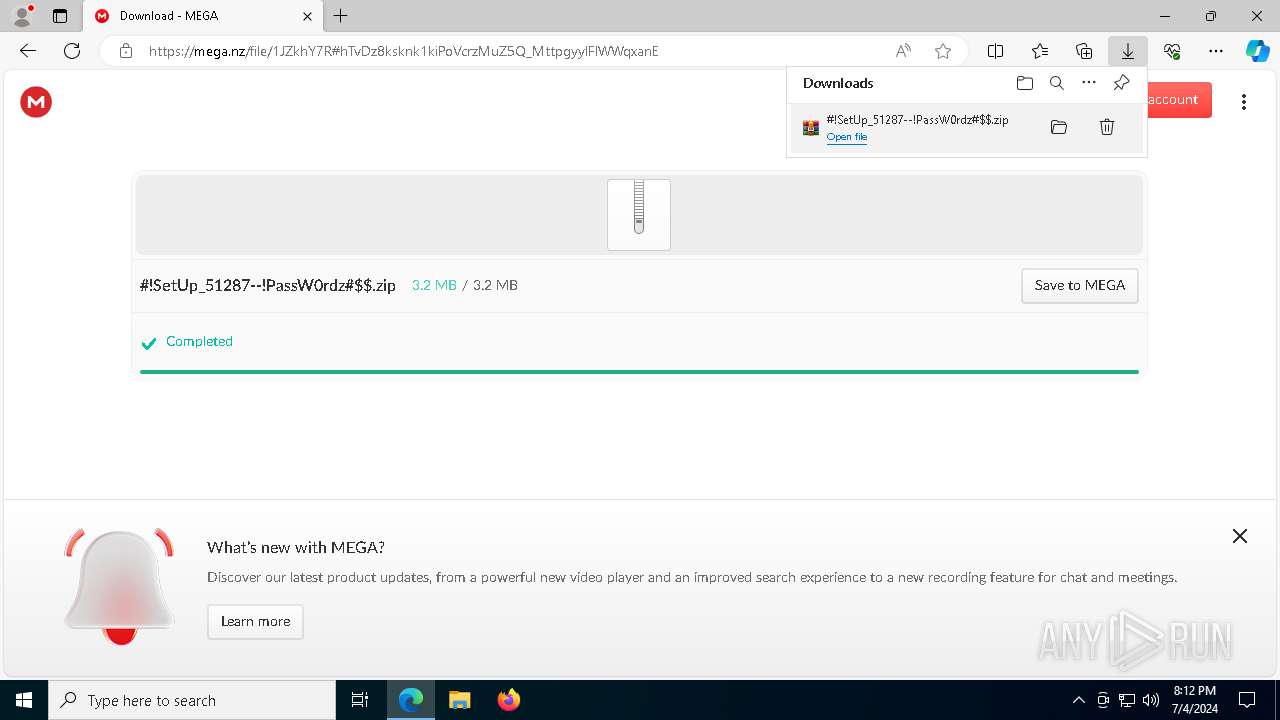
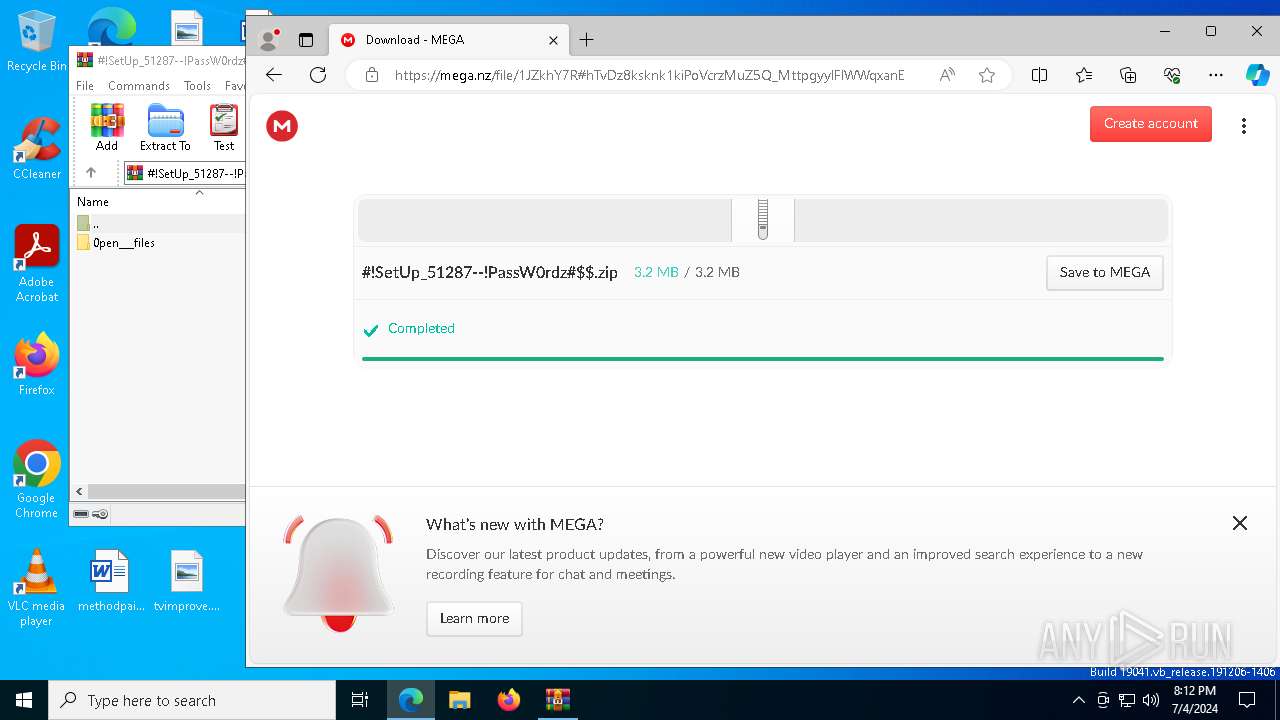
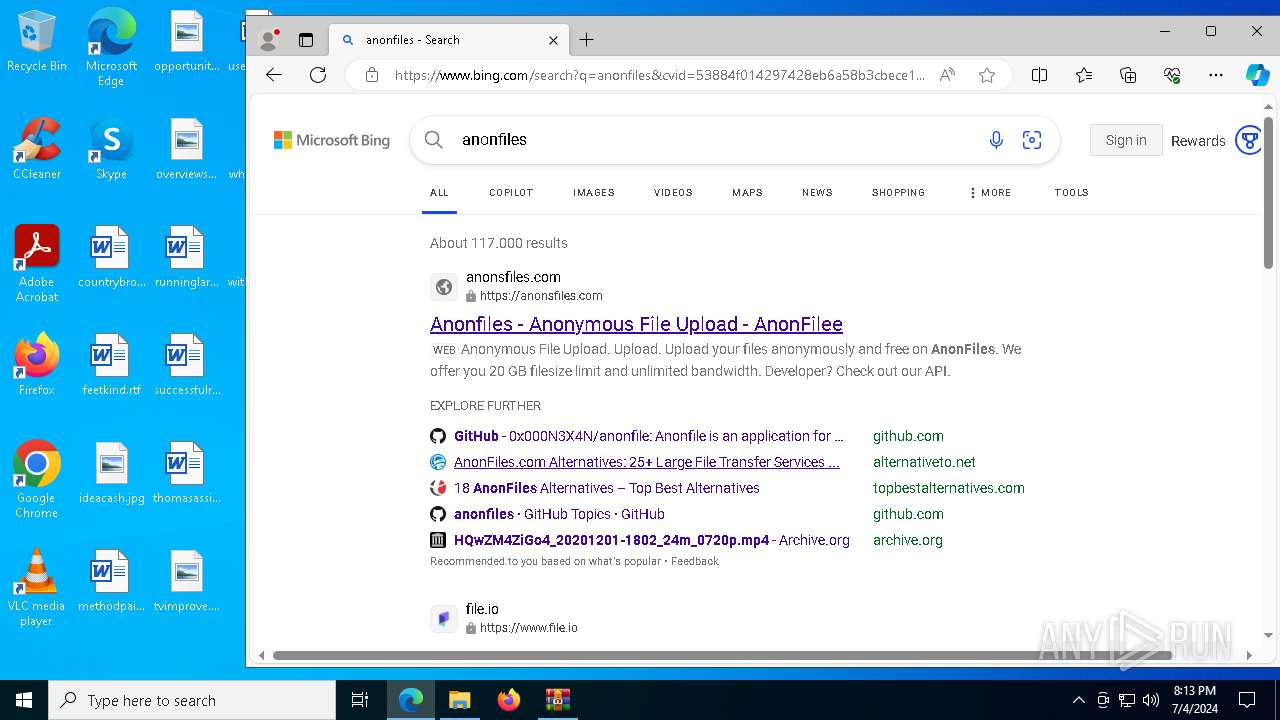
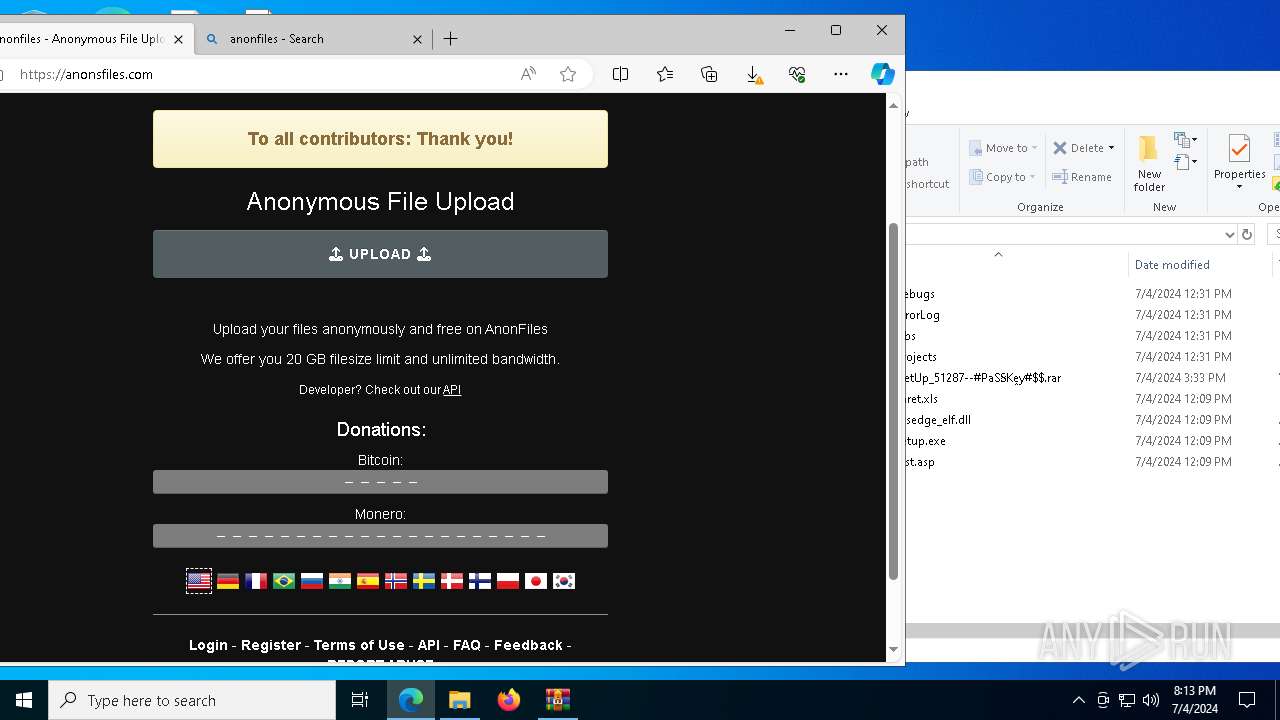
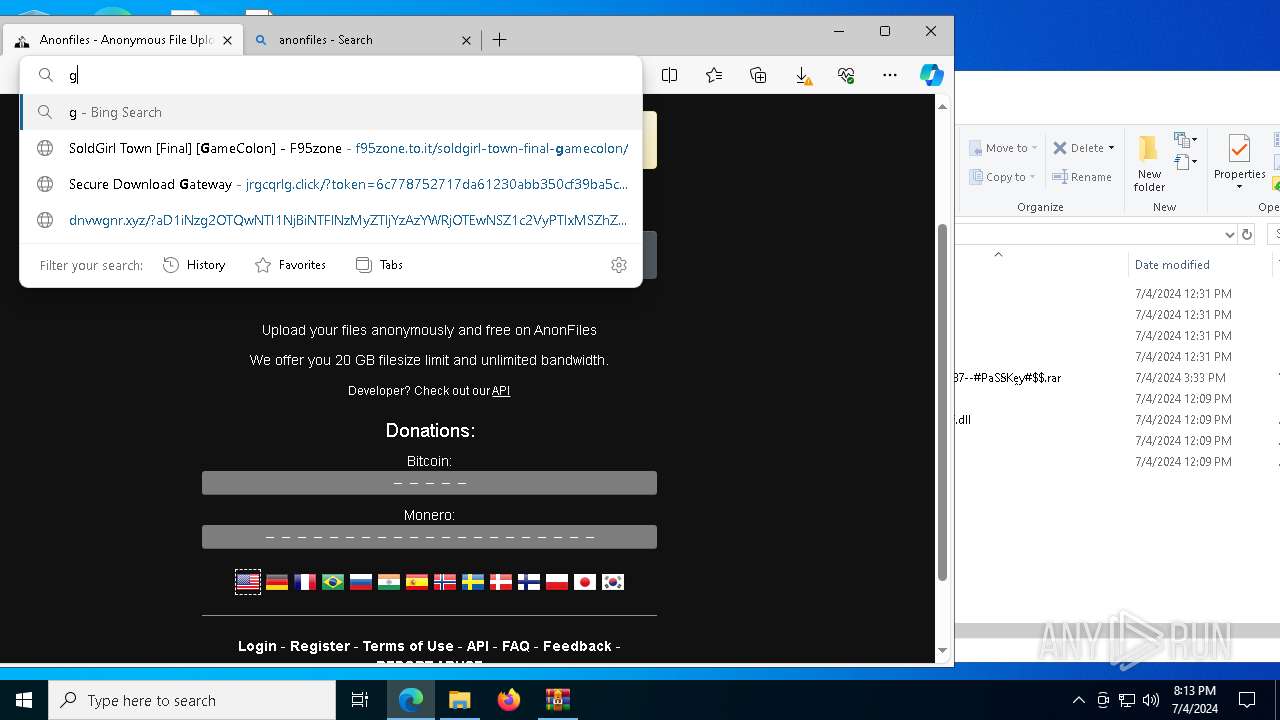
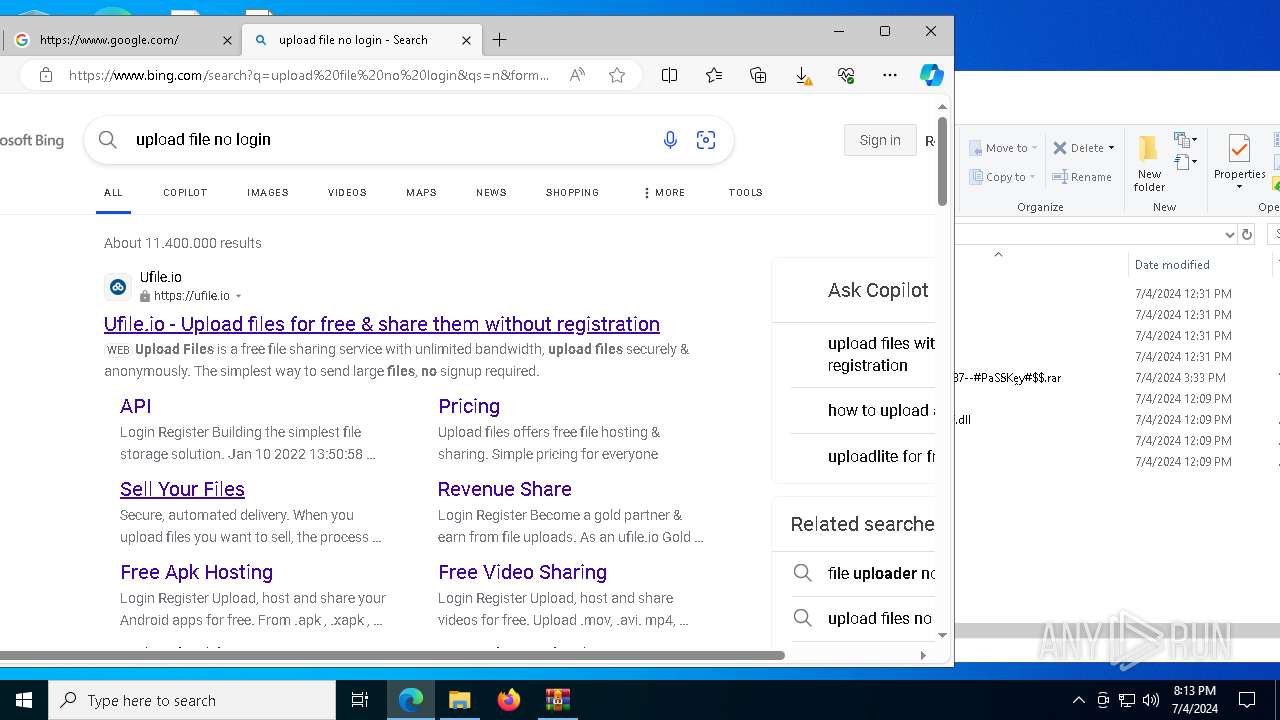
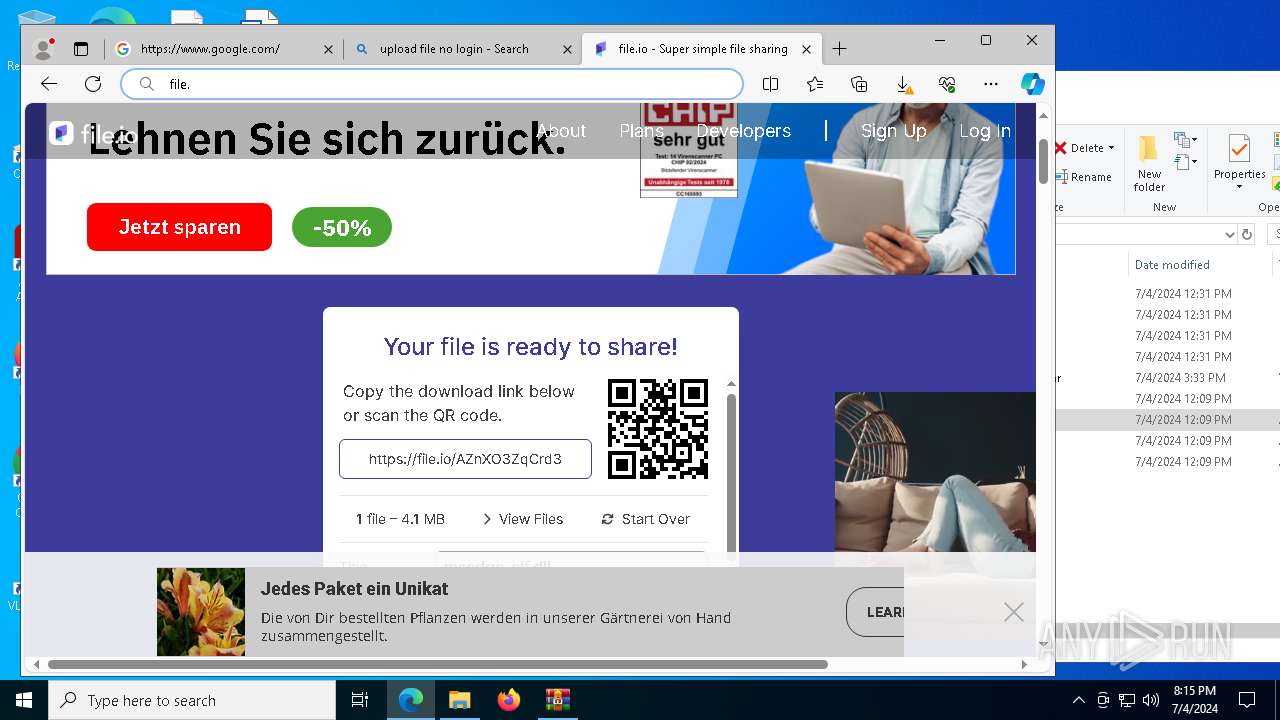
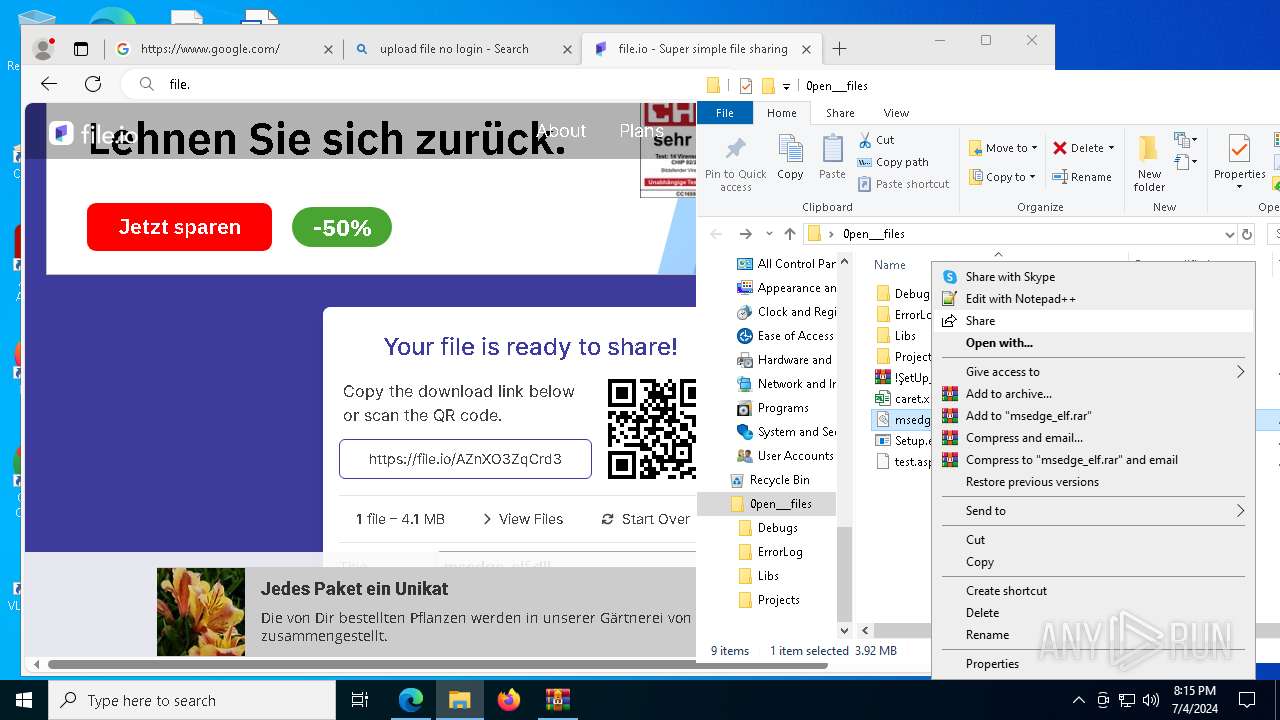
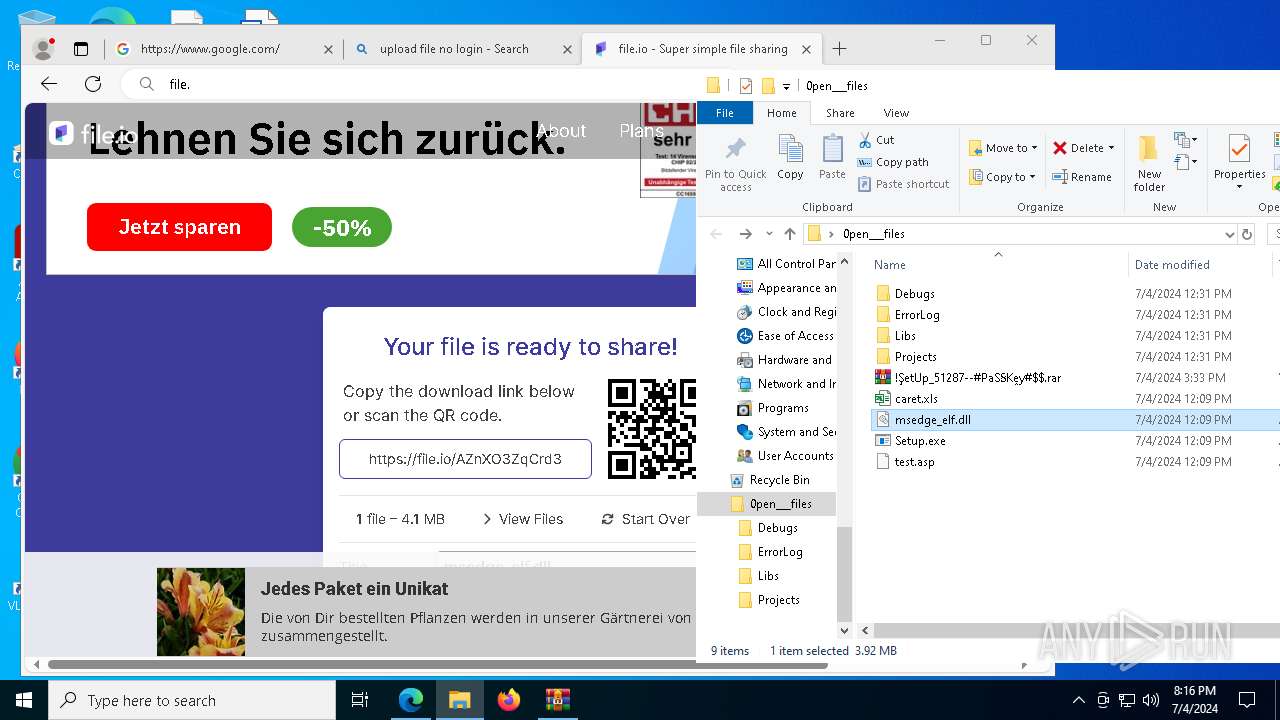
| URL: | https://f95zone.to.it/soldgirl-town-final-gamecolon/ |
| Full analysis: | https://app.any.run/tasks/eb7bf3d9-a876-42bd-a765-4dc1f20d5878 |
| Verdict: | Malicious activity |
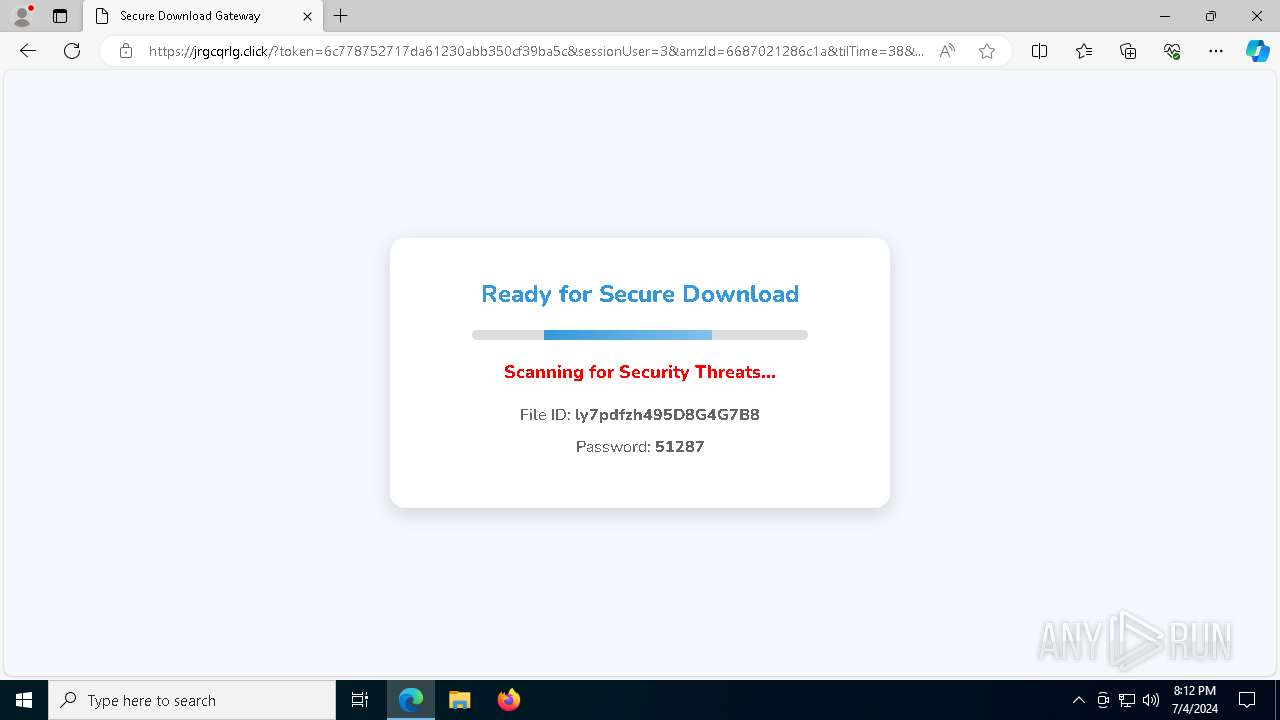
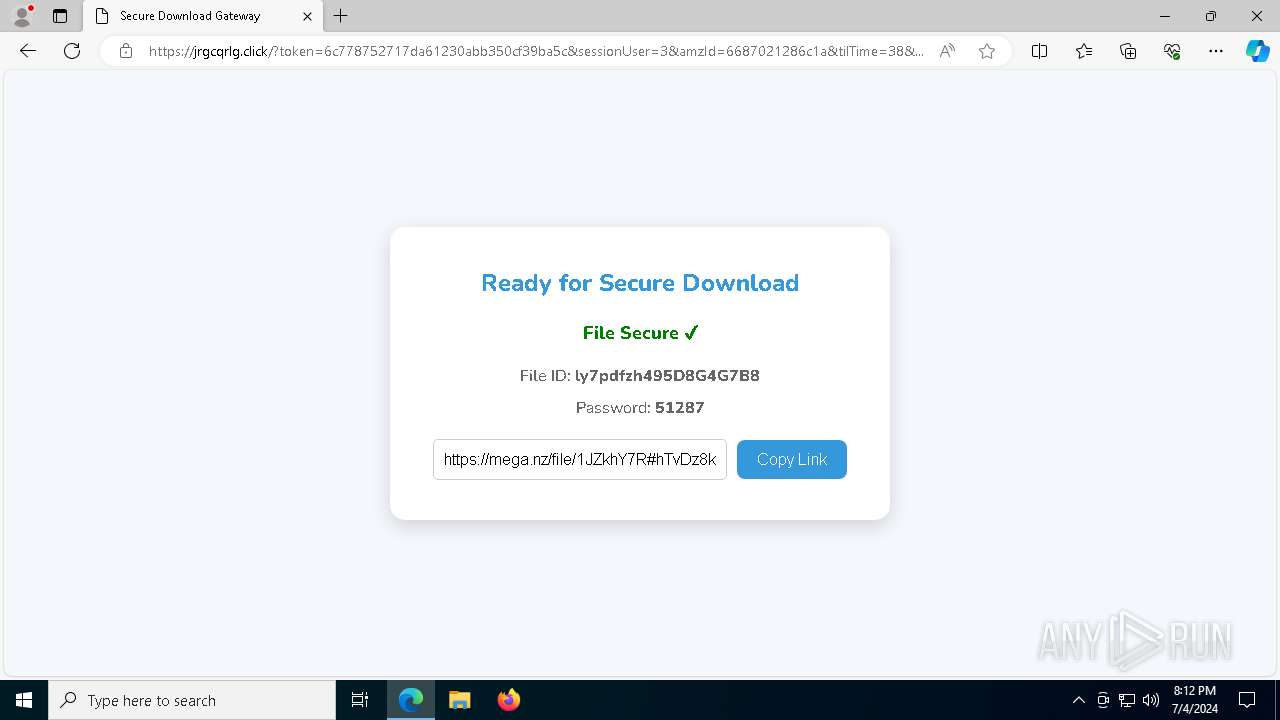
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | July 04, 2024, 20:11:50 |
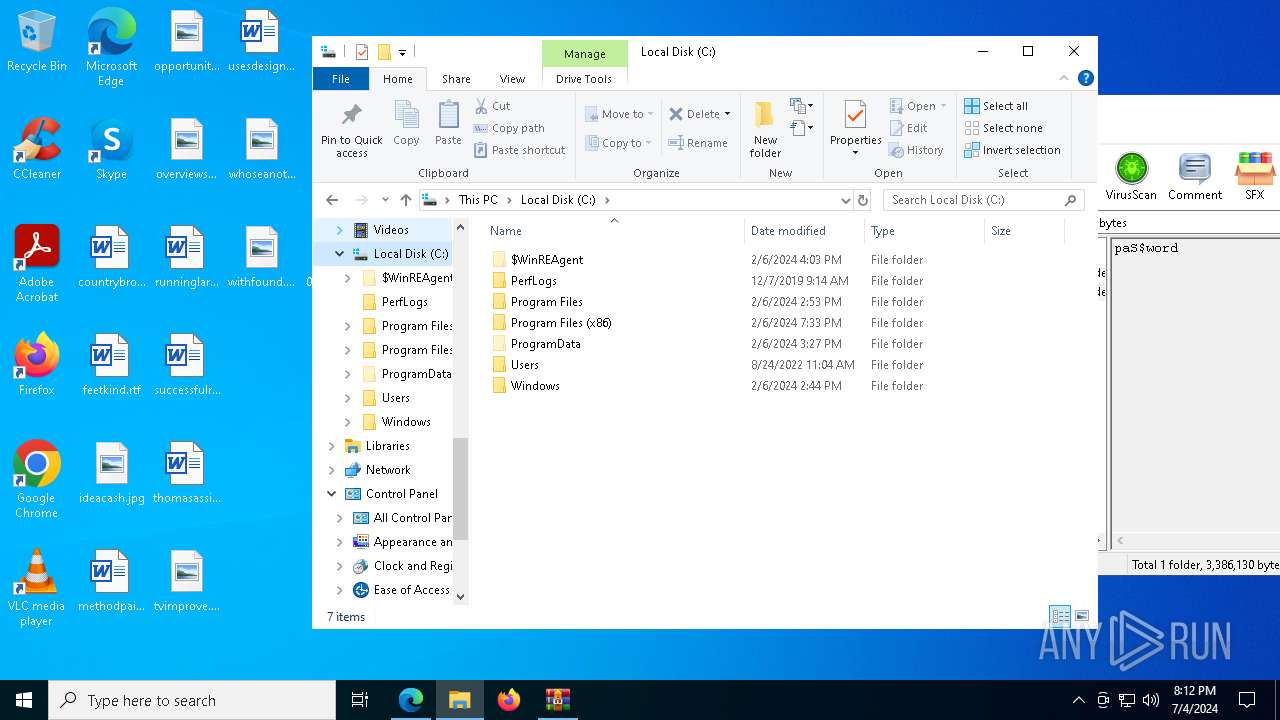
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2877AB6FDEAEE8C7A6960547605330D9 |
| SHA1: | D50AB818BB6132679F8A35B4123CB165A6B79465 |
| SHA256: | 3ACEB5E3B08EF5518B21FAEBB2205D2098A13C5C6B637ED9A2A2106FB20A2CBA |
| SSDEEP: | 3:N8uQfhhKWyRIRyeQEIjg:2uQJclR5eL |
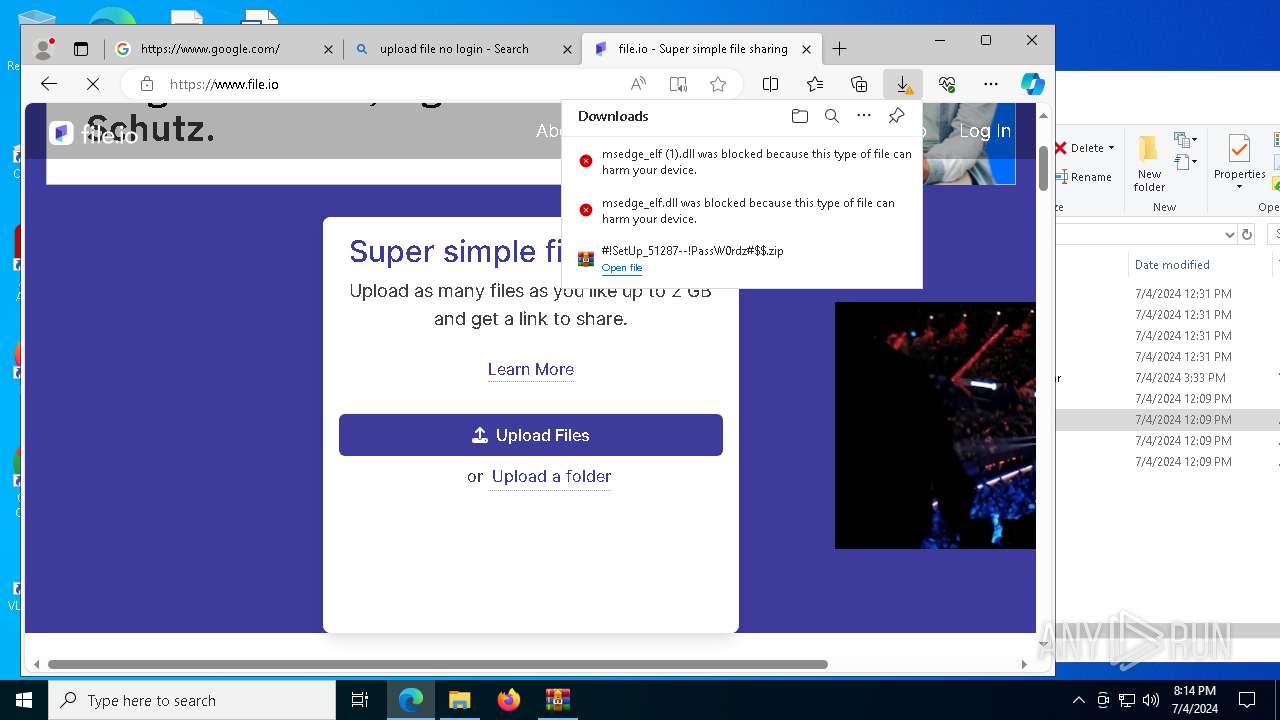
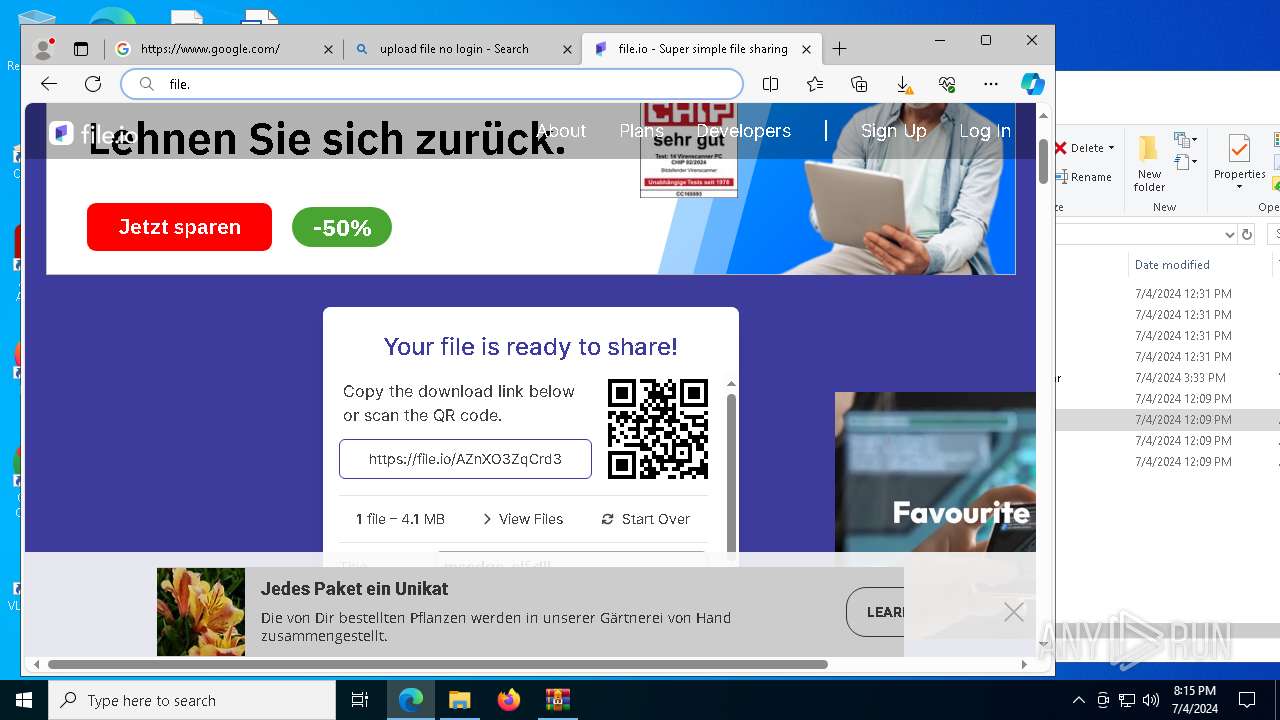
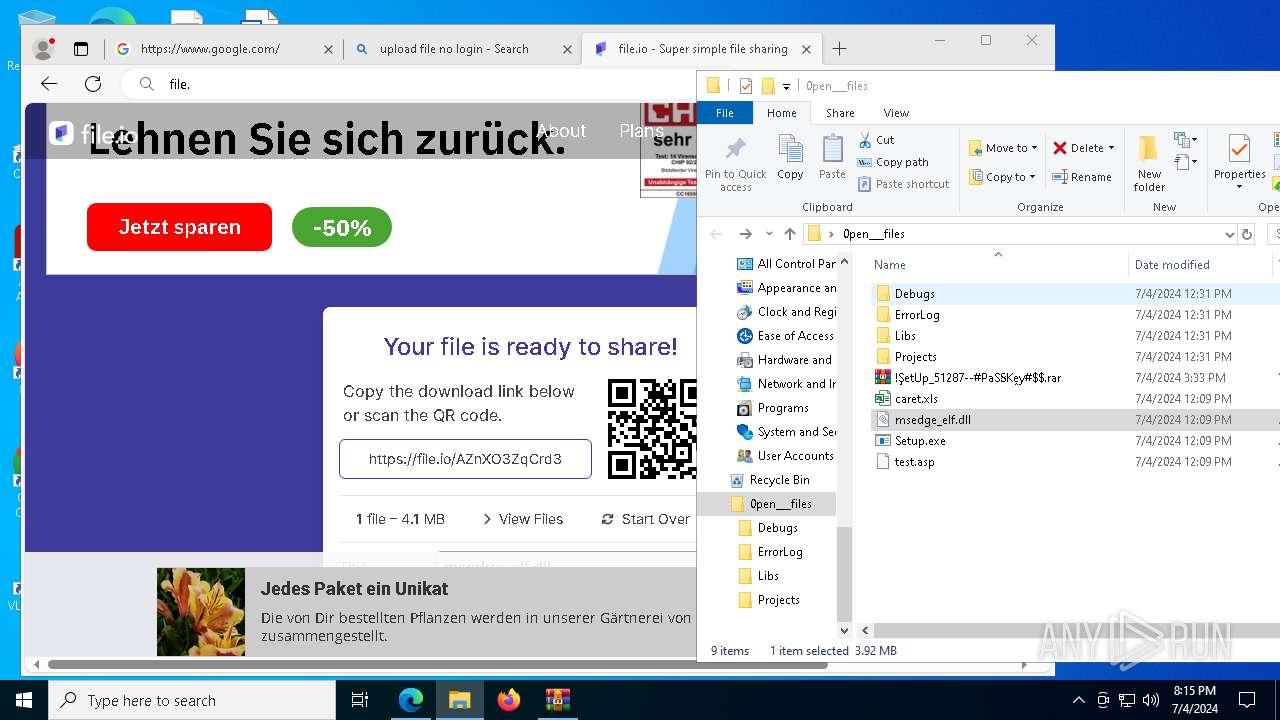
MALICIOUS
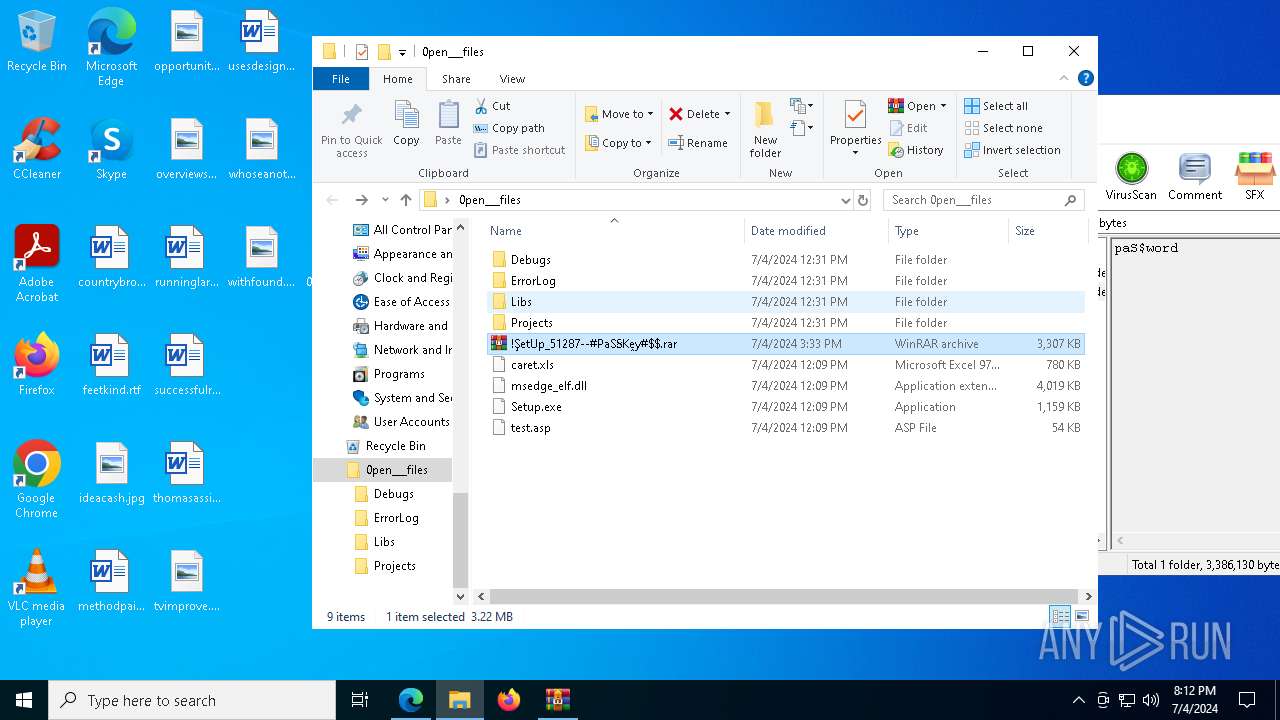
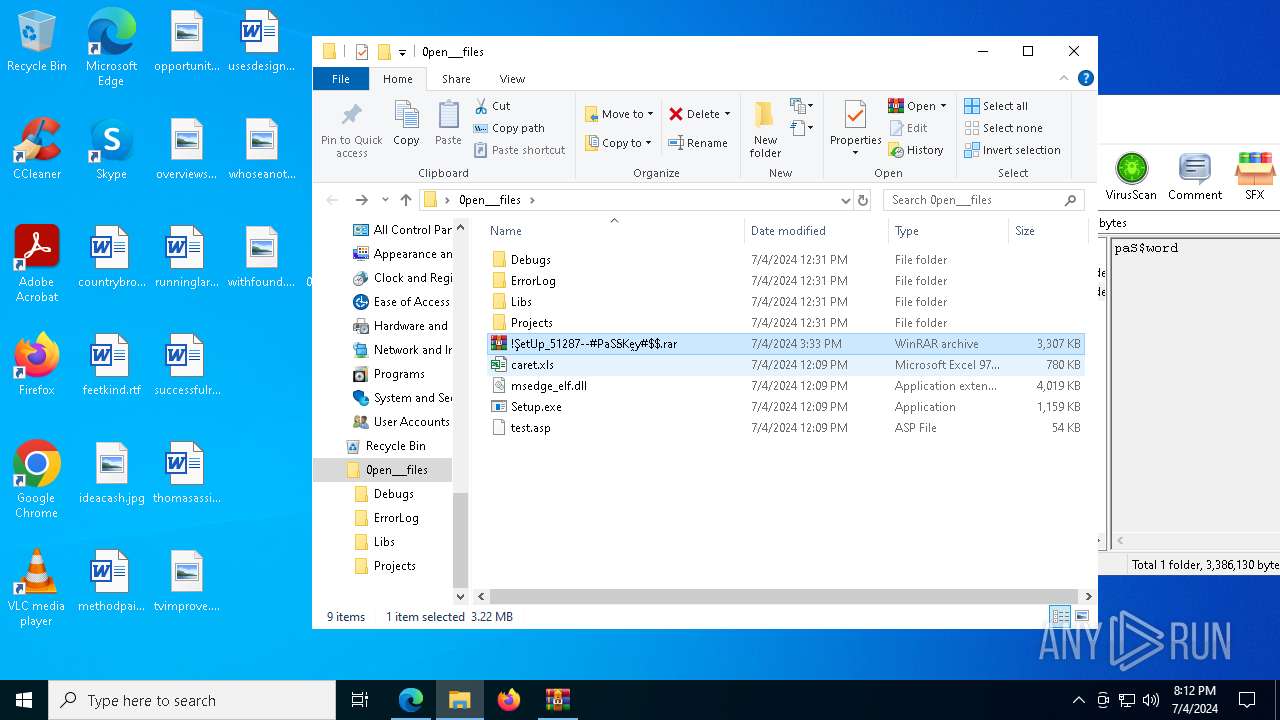
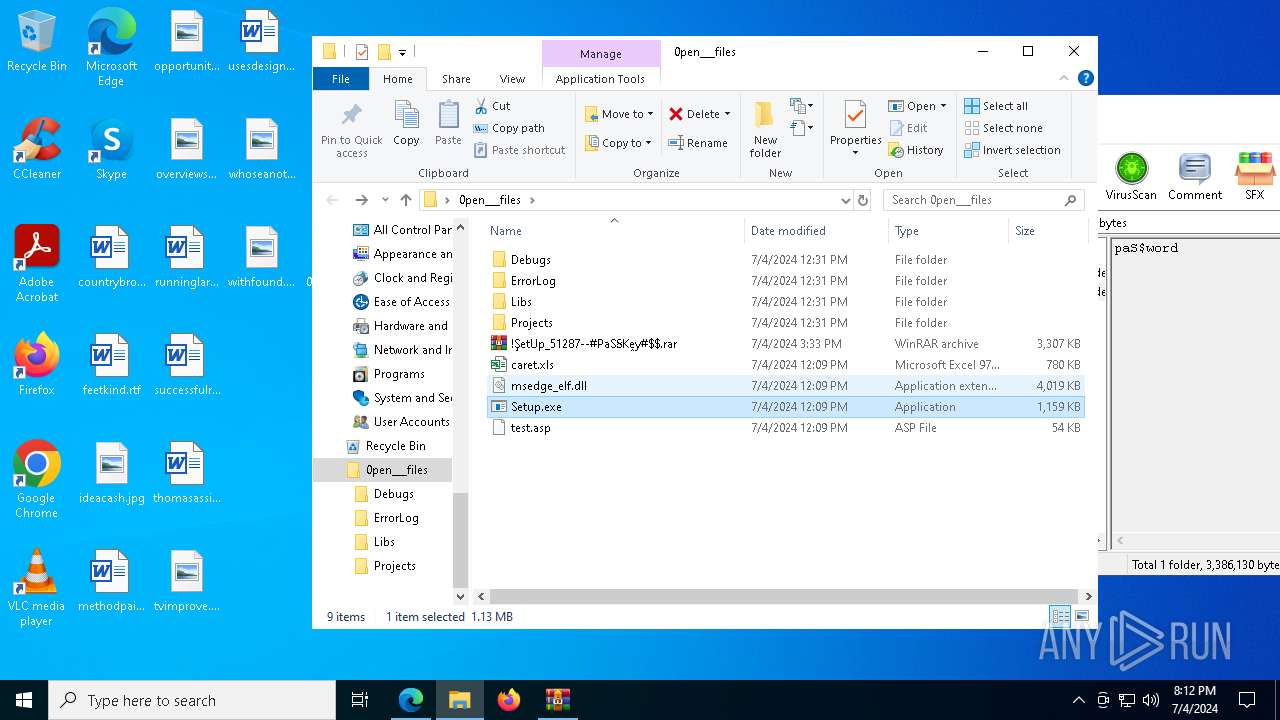
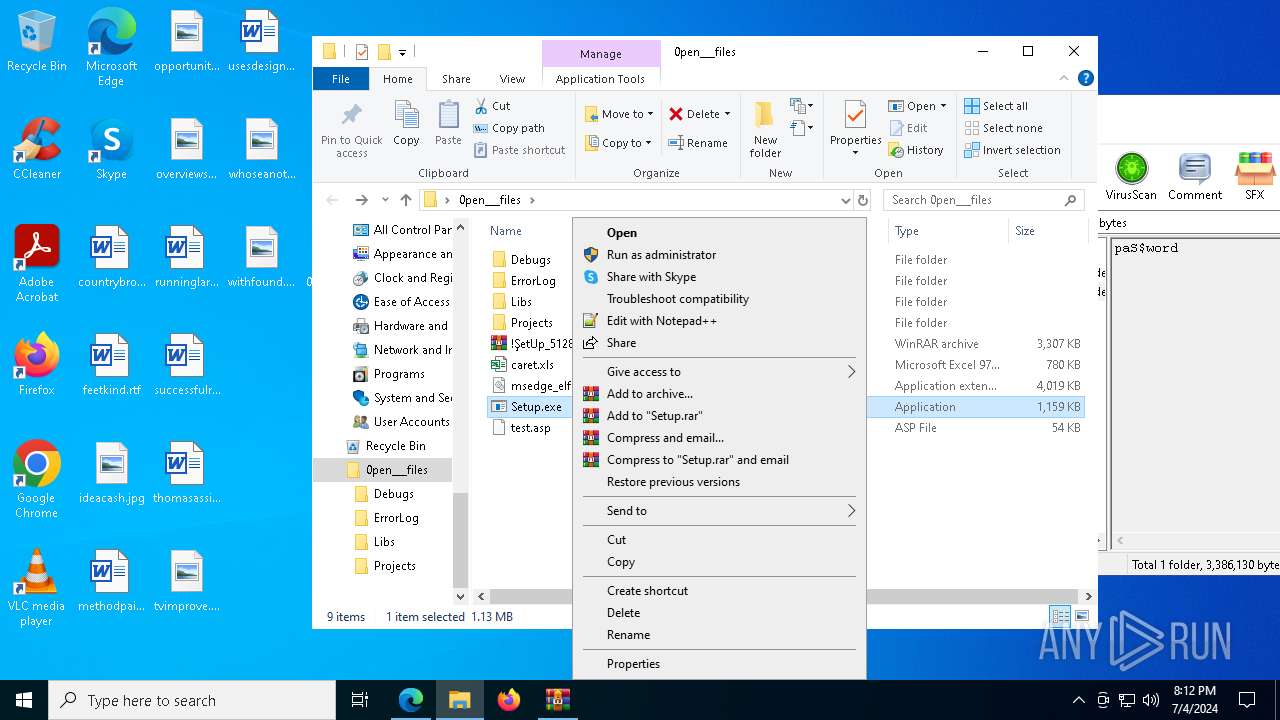
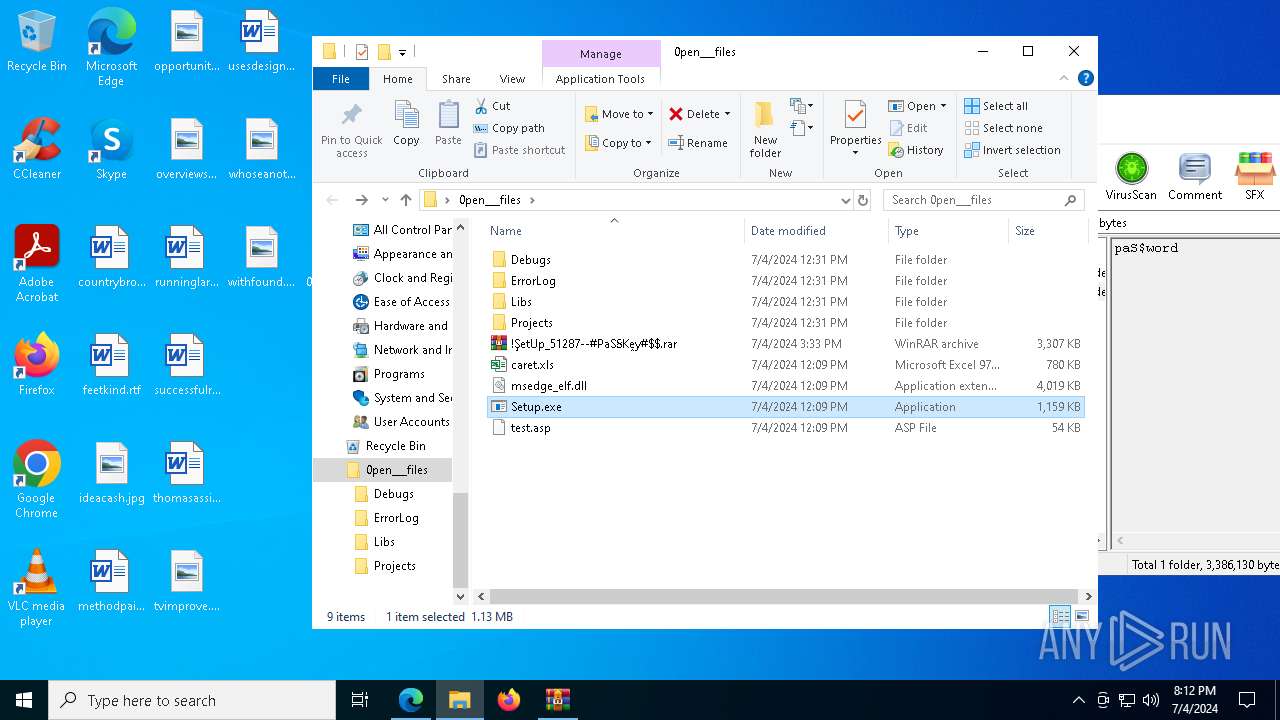
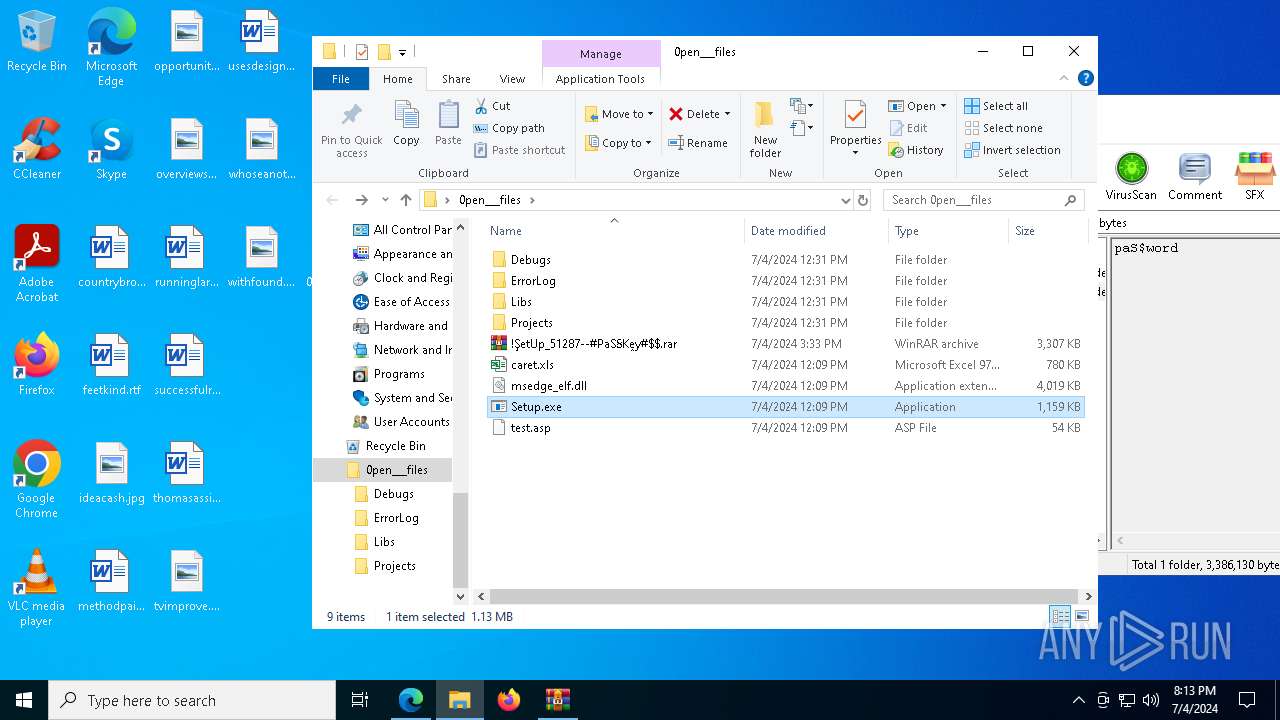
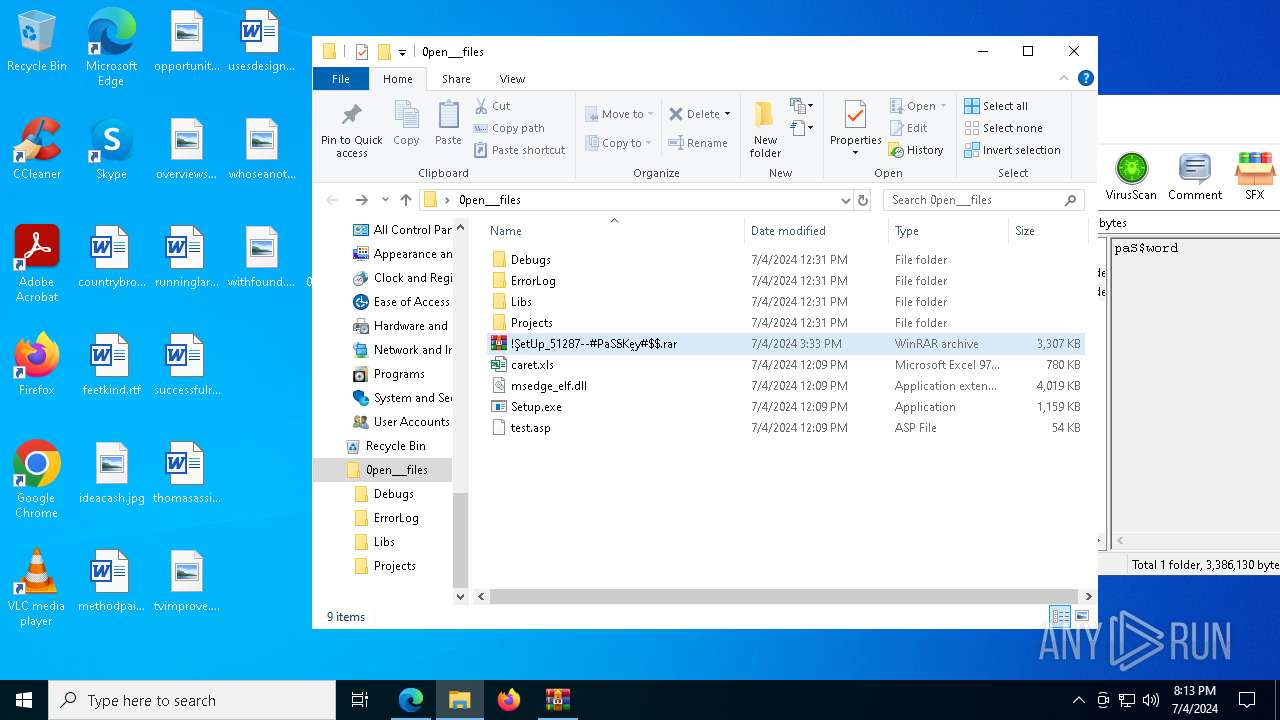
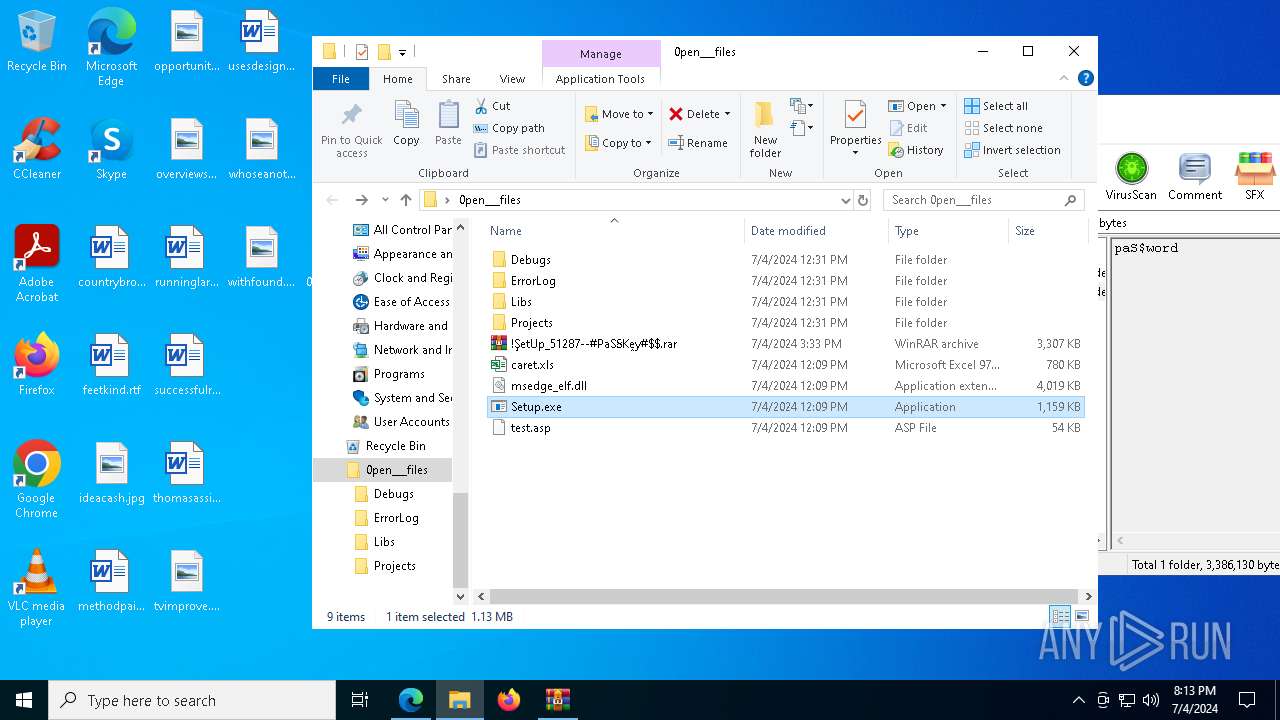
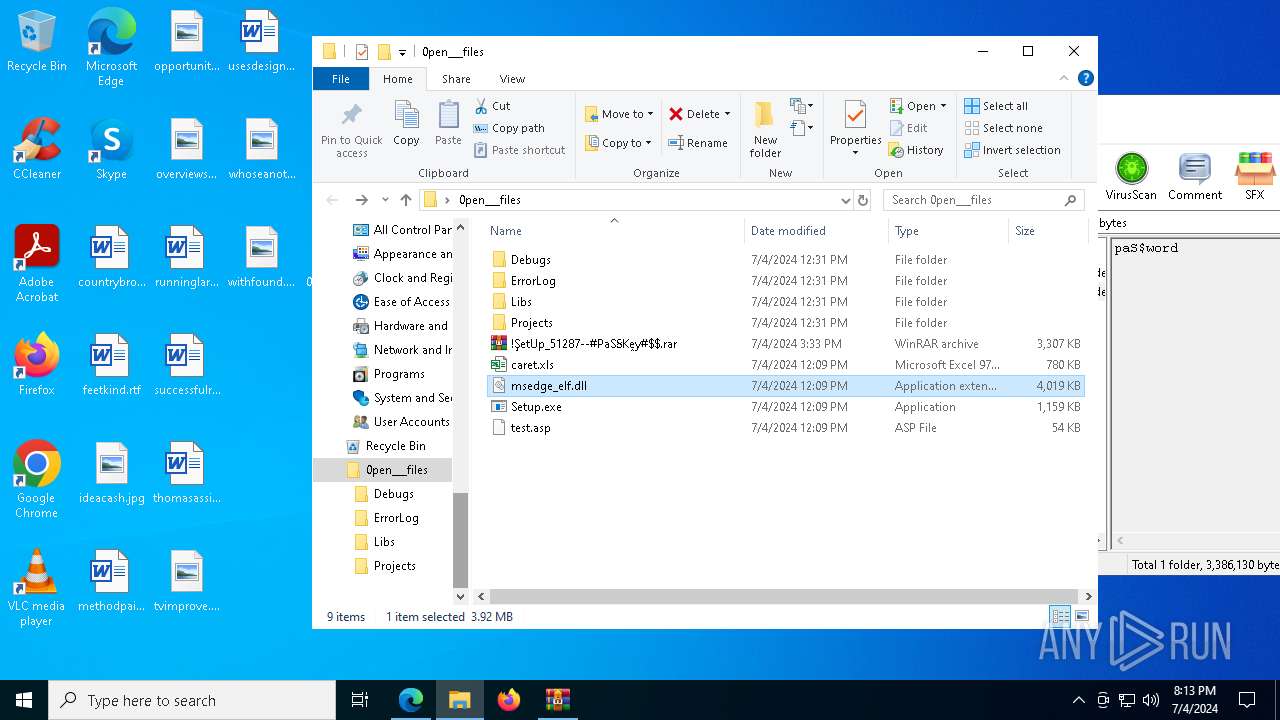
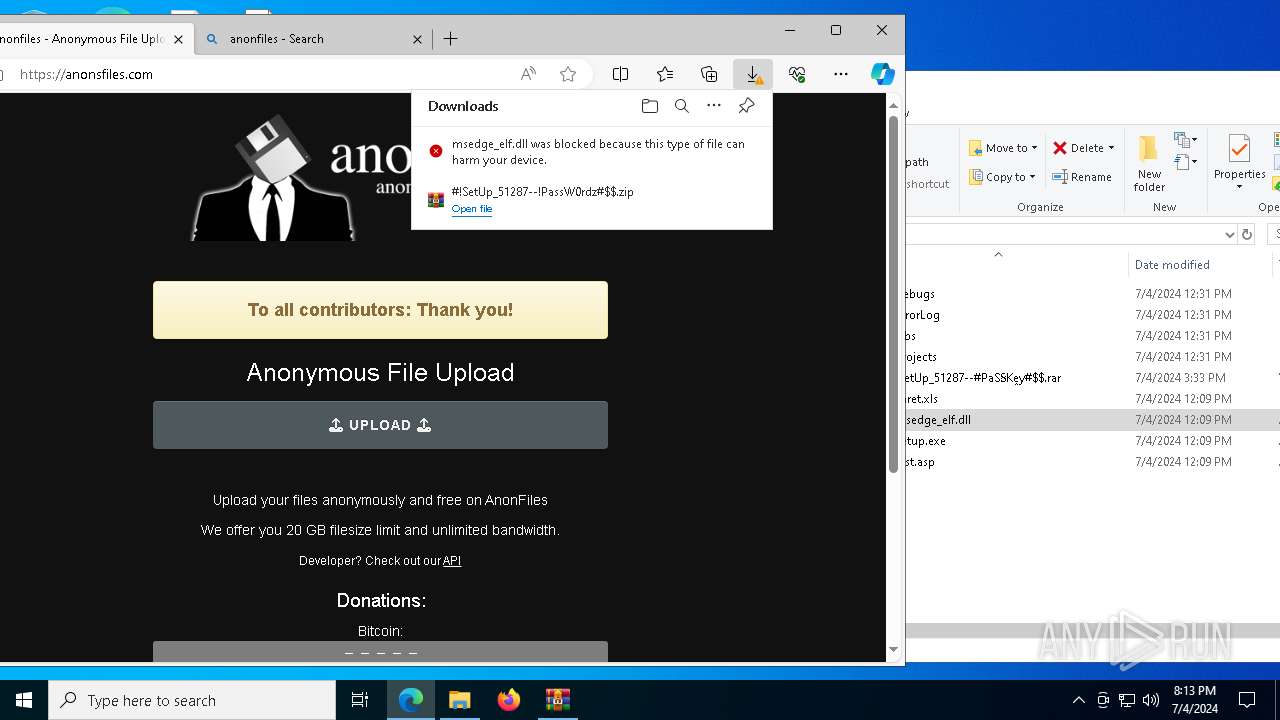
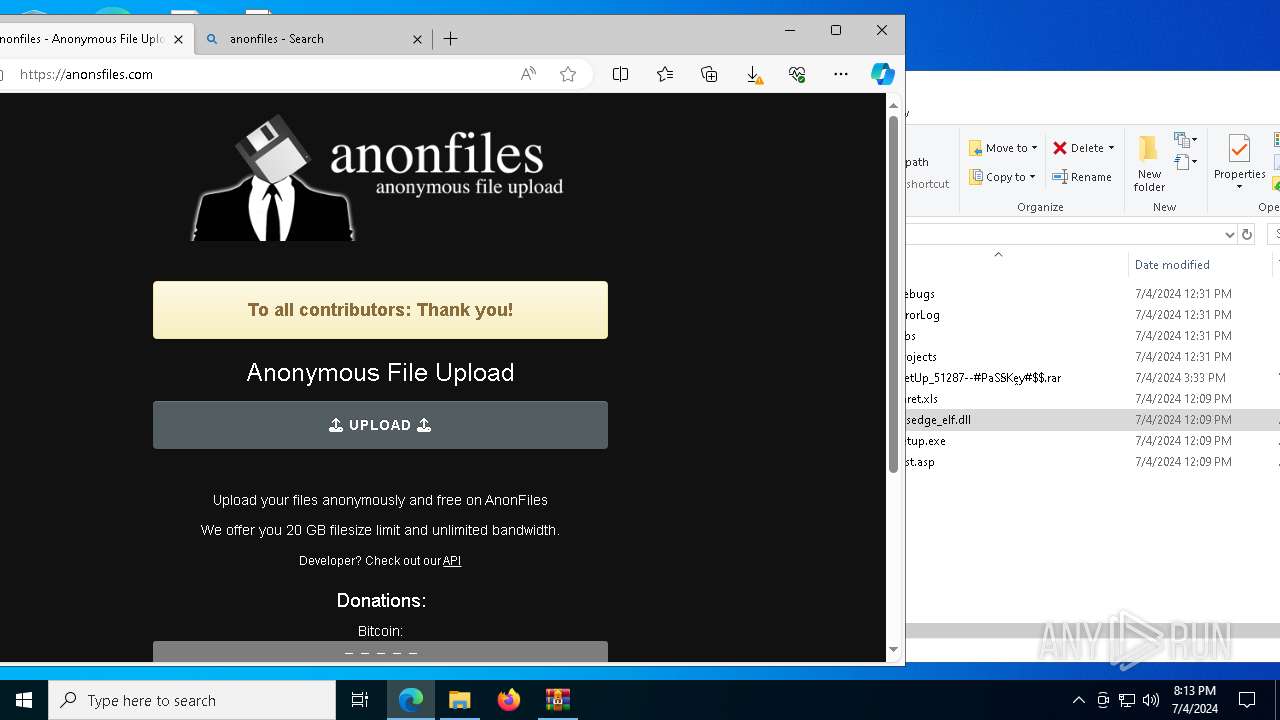
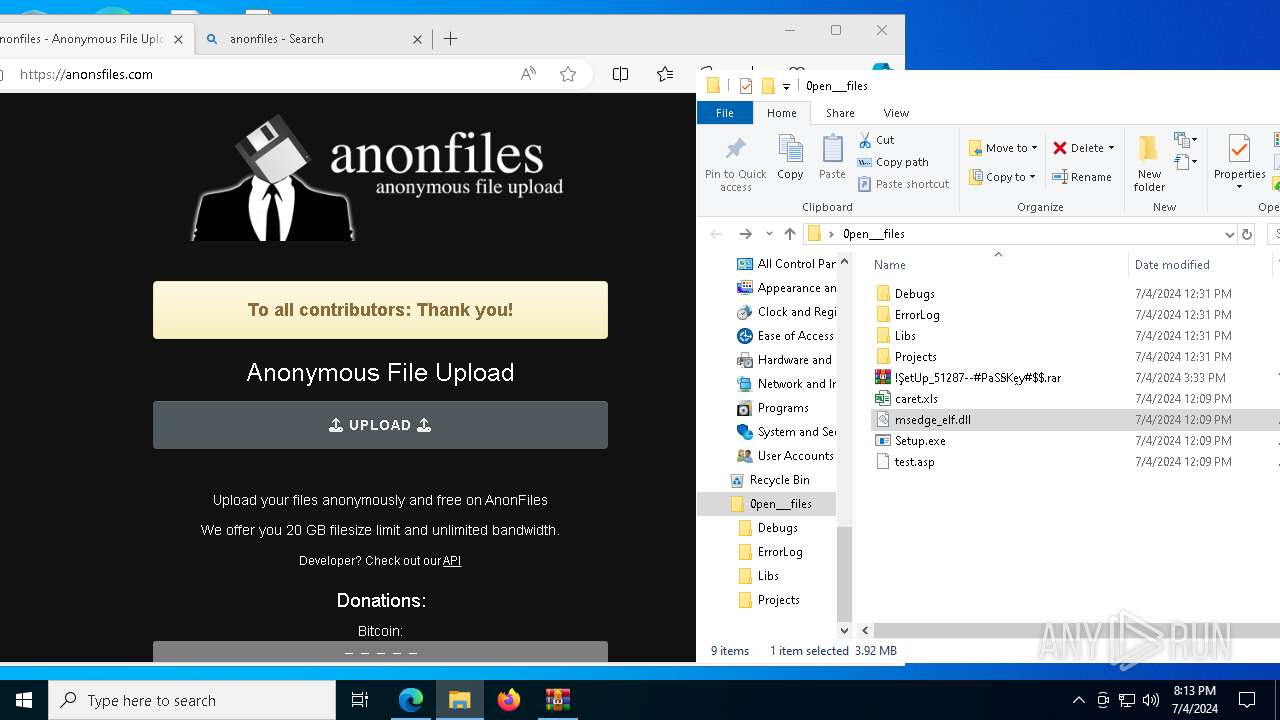
Drops the executable file immediately after the start
- Setup.exe (PID: 1328)
LUMMA has been detected (SURICATA)
- SearchIndexer.exe (PID: 1792)
Actions looks like stealing of personal data
- SearchIndexer.exe (PID: 1792)
HIJACKLOADER has been detected (YARA)
- explorer.exe (PID: 10224)
- explorer.exe (PID: 10020)
- comp.exe (PID: 1160)
AMADEY has been detected (SURICATA)
- explorer.exe (PID: 10224)
Connects to the CnC server
- explorer.exe (PID: 10224)
AMADEY has been detected (YARA)
- explorer.exe (PID: 10224)
SUSPICIOUS
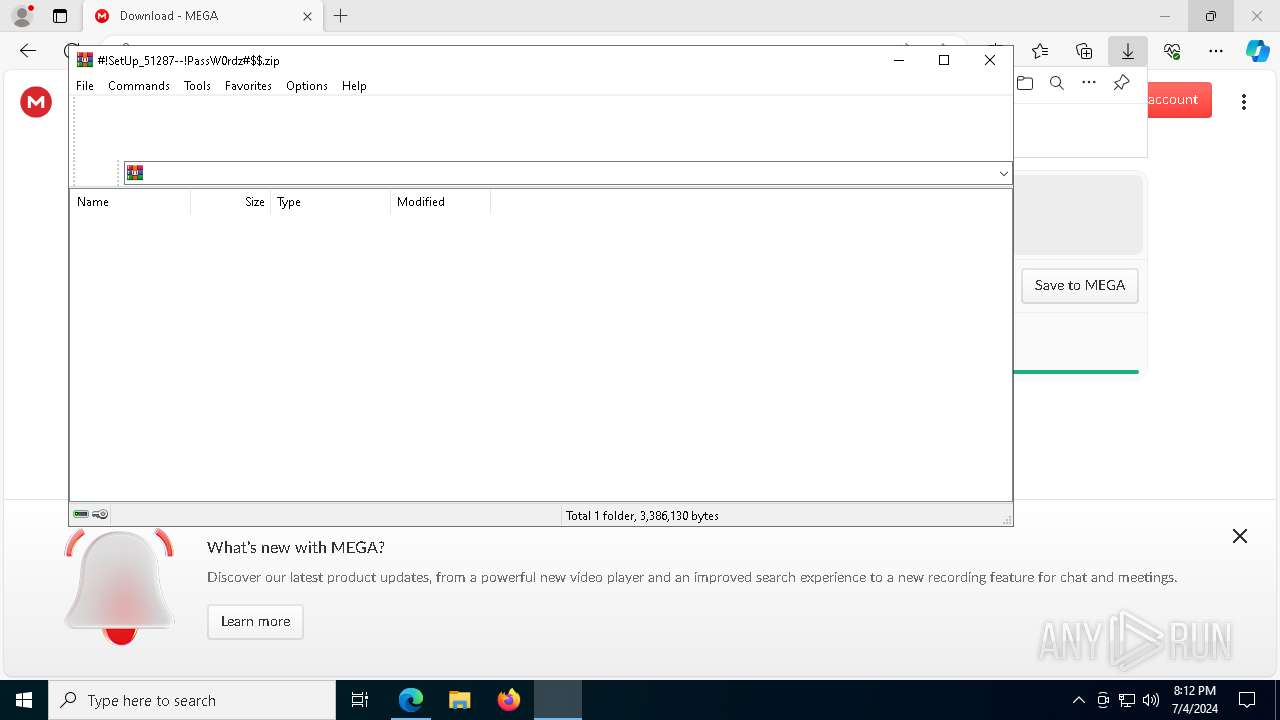
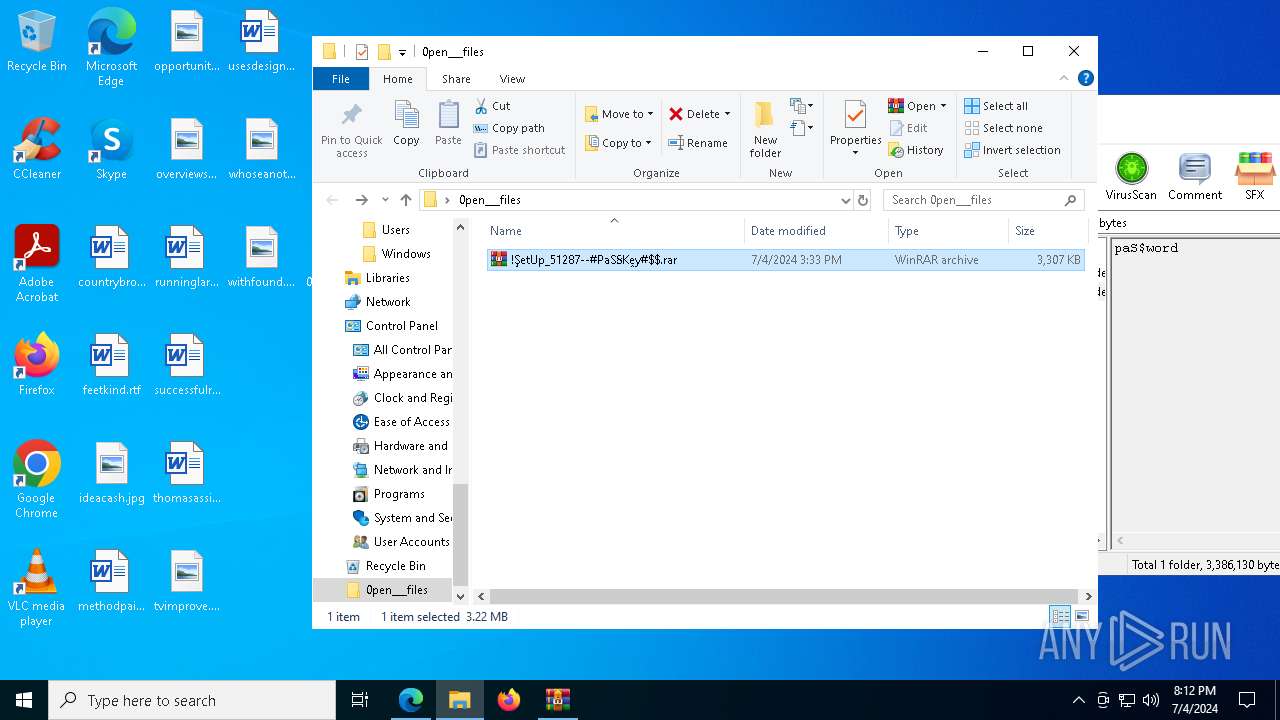
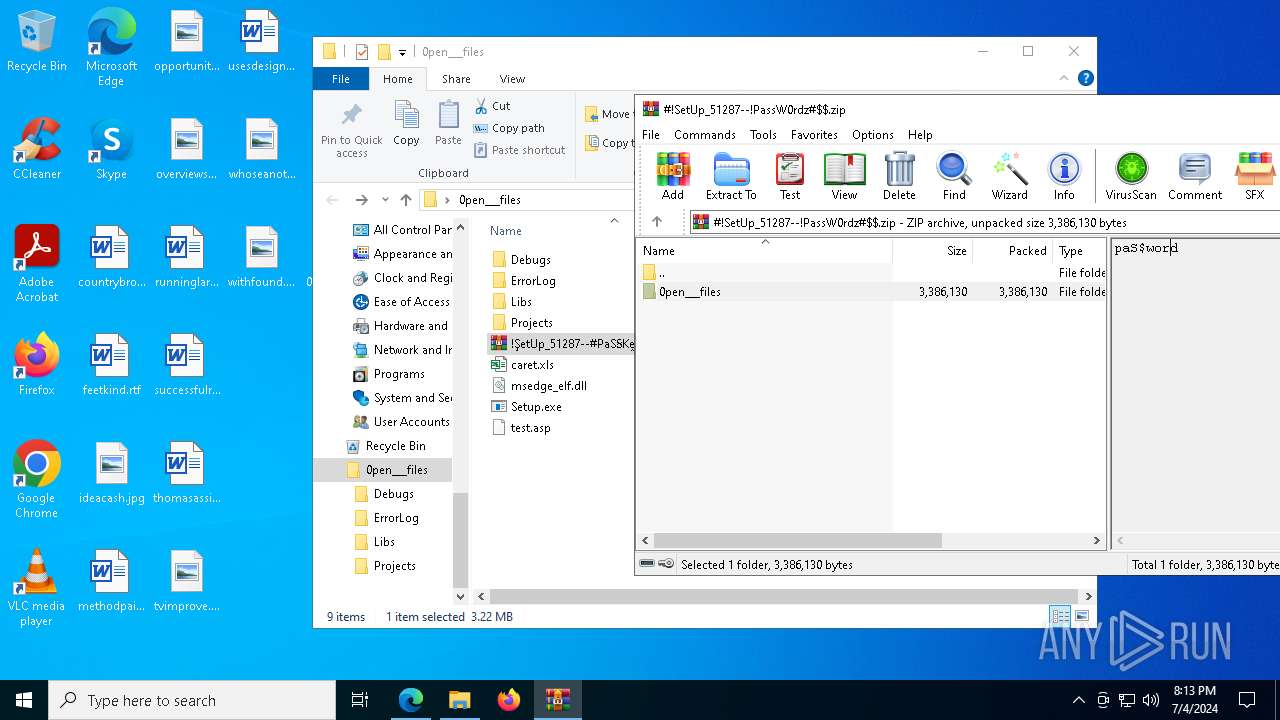
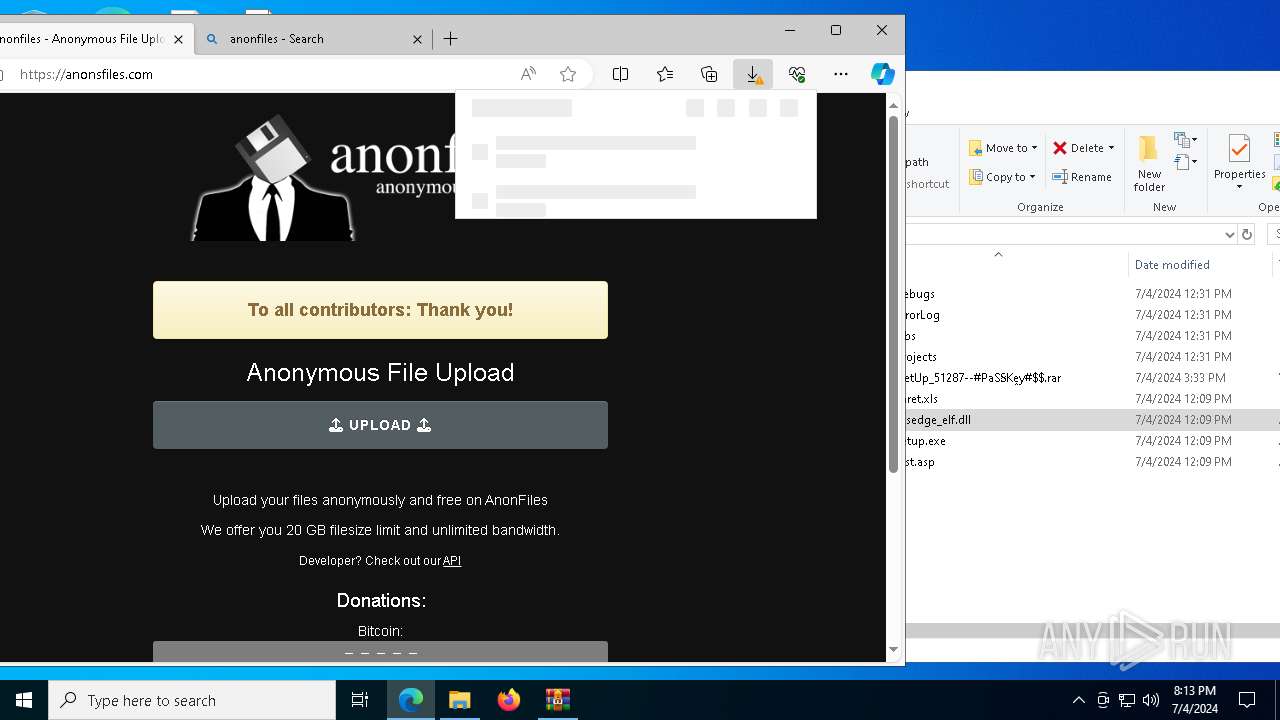
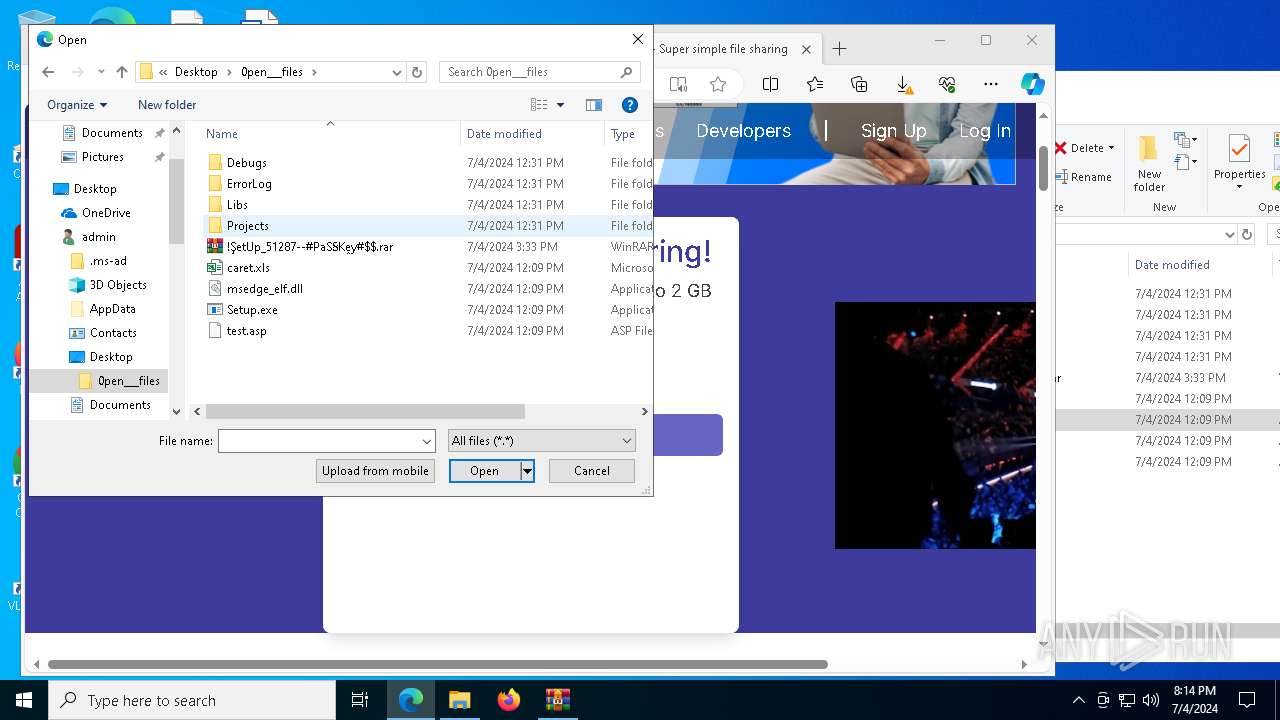
Process drops legitimate windows executable
- WinRAR.exe (PID: 528)
- Setup.exe (PID: 1328)
- msedge.exe (PID: 1928)
Starts a Microsoft application from unusual location
- Setup.exe (PID: 1328)
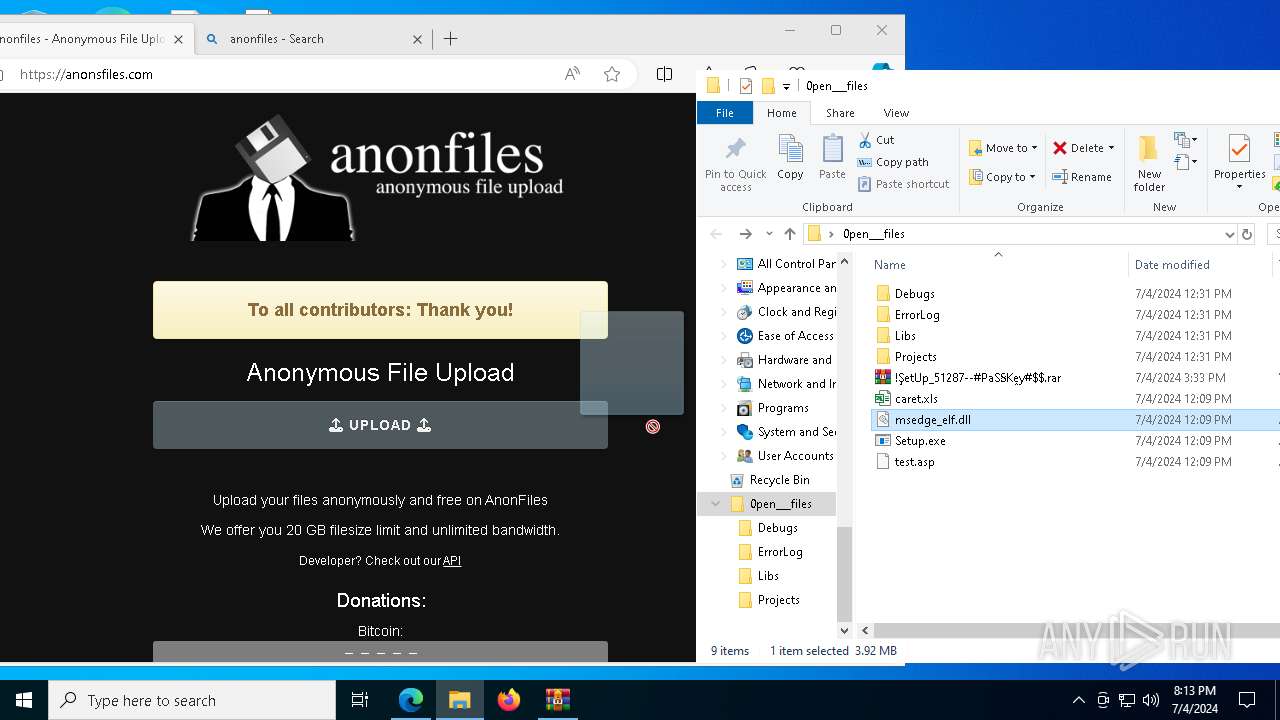
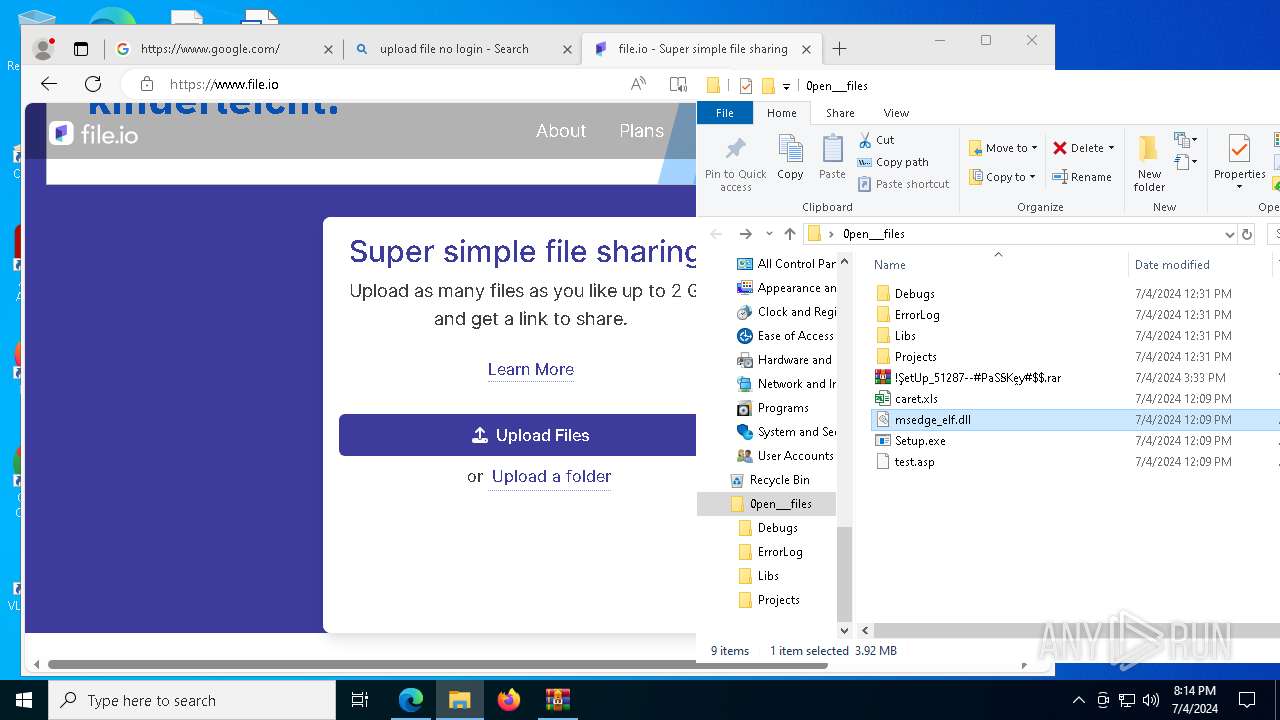
Executable content was dropped or overwritten
- Setup.exe (PID: 1328)
- SearchIndexer.exe (PID: 1792)
Starts application with an unusual extension
- Setup.exe (PID: 1328)
Searches for installed software
- SearchIndexer.exe (PID: 1792)
Found regular expressions for crypto-addresses (YARA)
- explorer.exe (PID: 10020)
Contacting a server suspected of hosting an CnC
- explorer.exe (PID: 10224)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 1928)
Checks supported languages
- identity_helper.exe (PID: 7528)
- Setup.exe (PID: 1328)
- more.com (PID: 8152)
- GXK7RM37JV8W5C9BZDKUMHY.exe (PID: 5988)
- HIDA9GYZNBRO1TDVEXMLI1P.exe (PID: 7688)
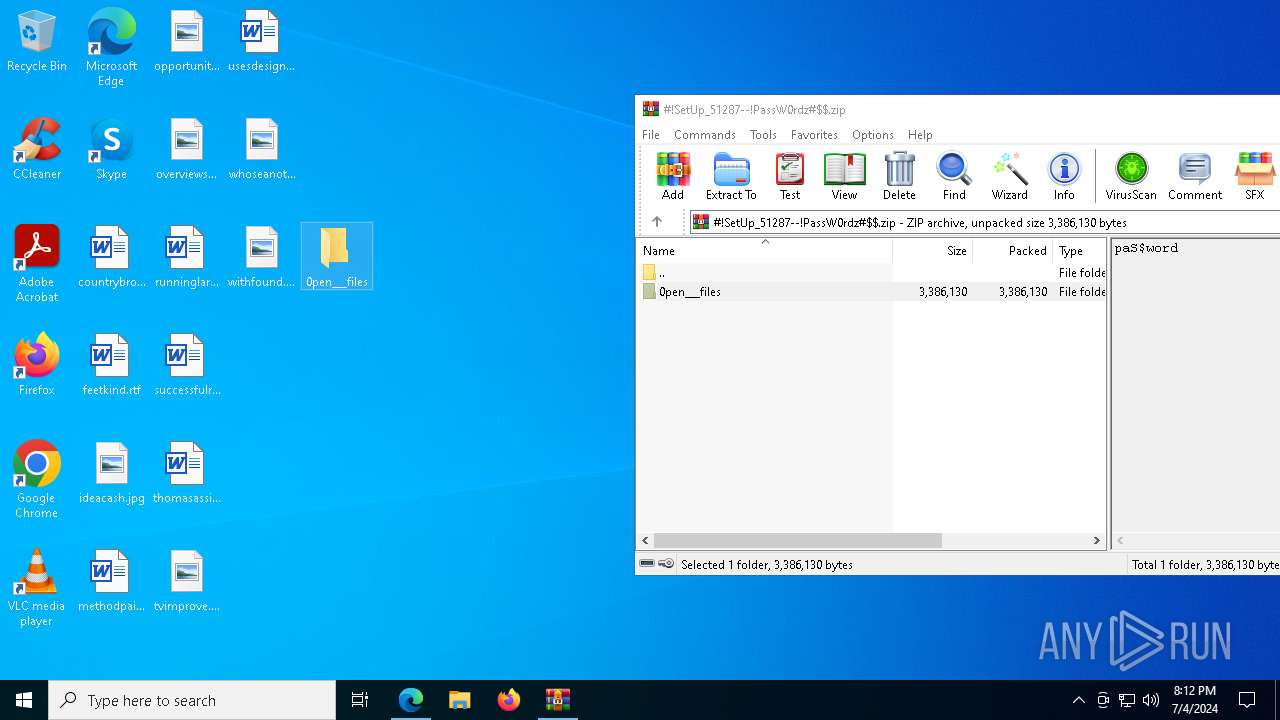
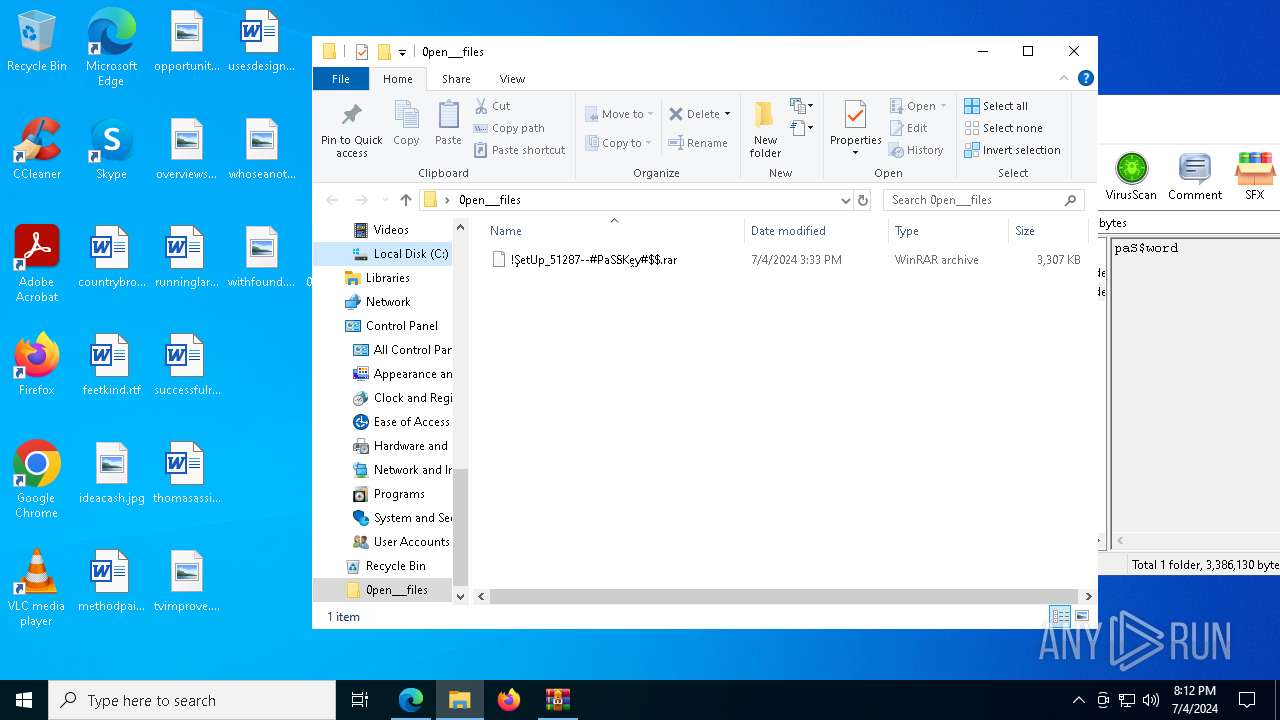
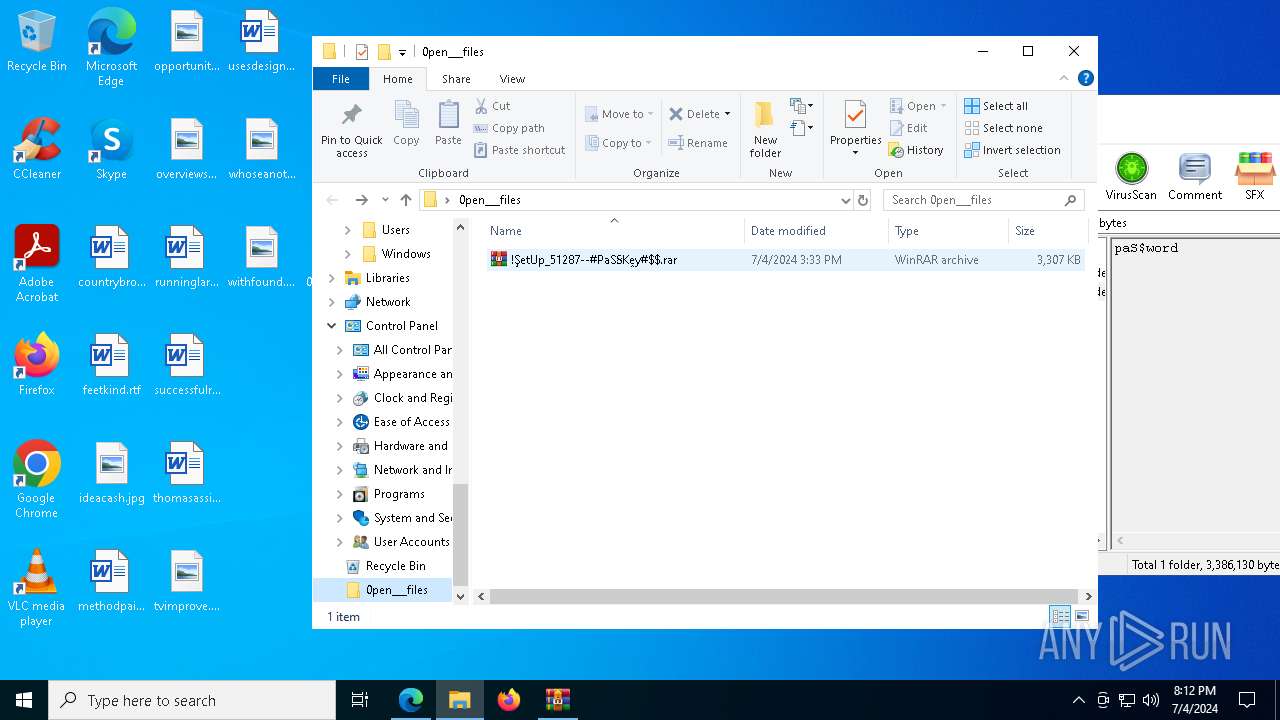
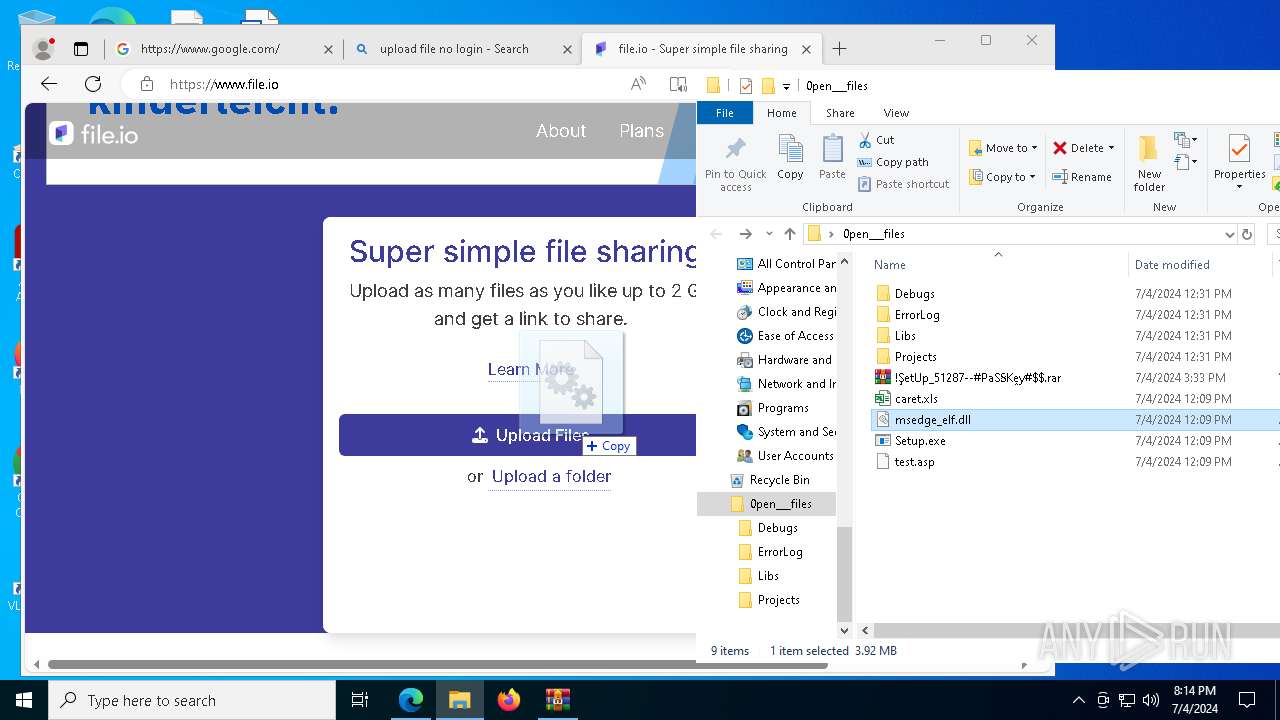
The process uses the downloaded file
- WinRAR.exe (PID: 7448)
- msedge.exe (PID: 1928)
- msedge.exe (PID: 7164)
Reads the computer name
- identity_helper.exe (PID: 7528)
- more.com (PID: 8152)
- Setup.exe (PID: 1328)
- GXK7RM37JV8W5C9BZDKUMHY.exe (PID: 5988)
- HIDA9GYZNBRO1TDVEXMLI1P.exe (PID: 7688)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 528)
- SearchIndexer.exe (PID: 1792)
- msedge.exe (PID: 5564)
- msedge.exe (PID: 1928)
- msedge.exe (PID: 6532)
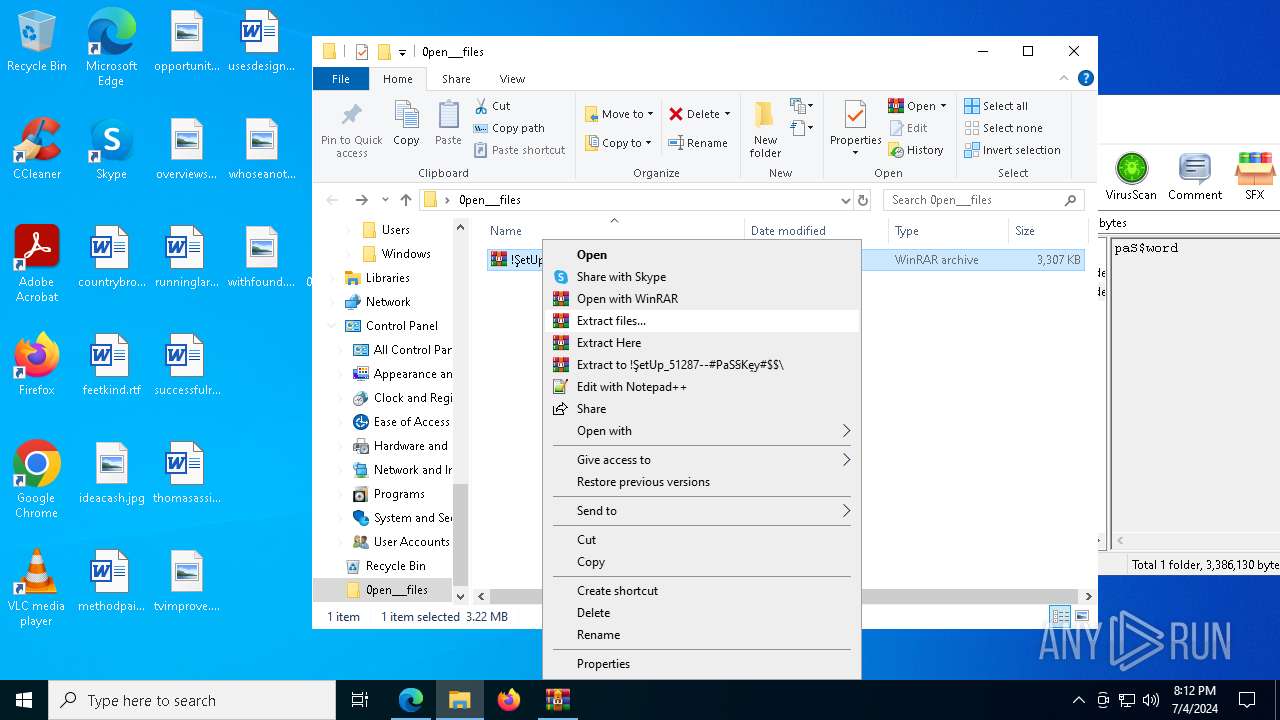
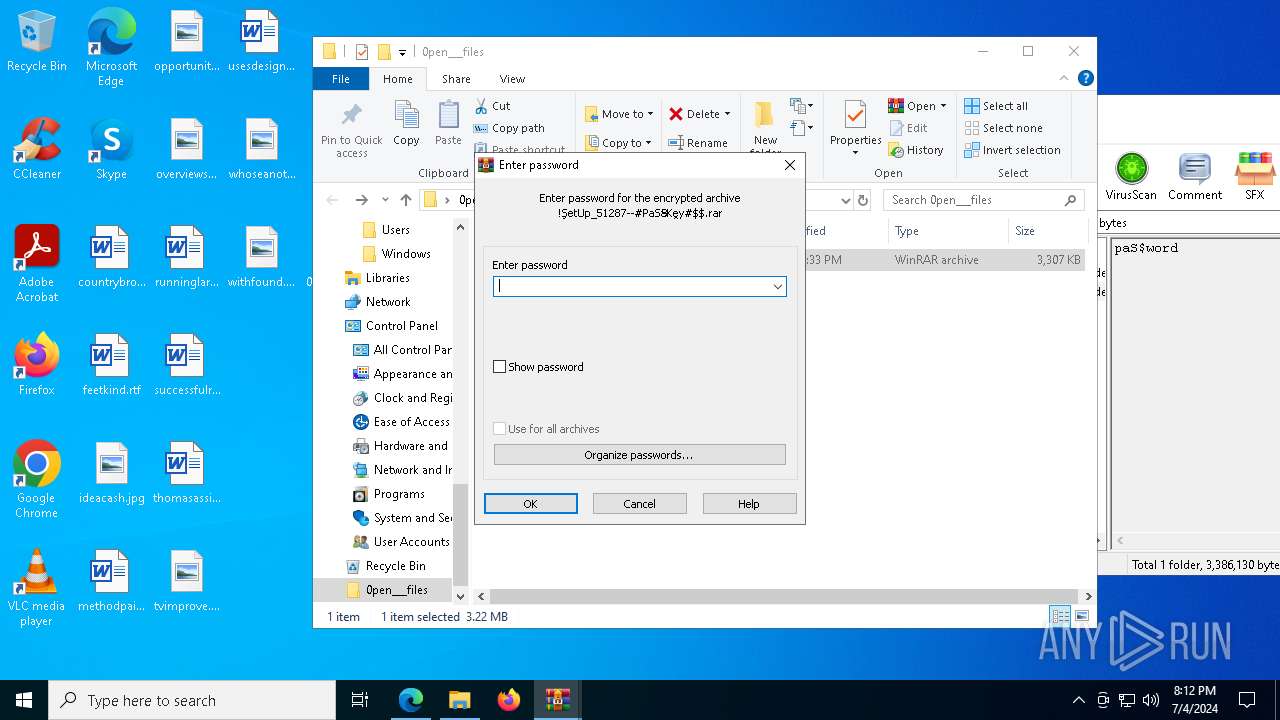
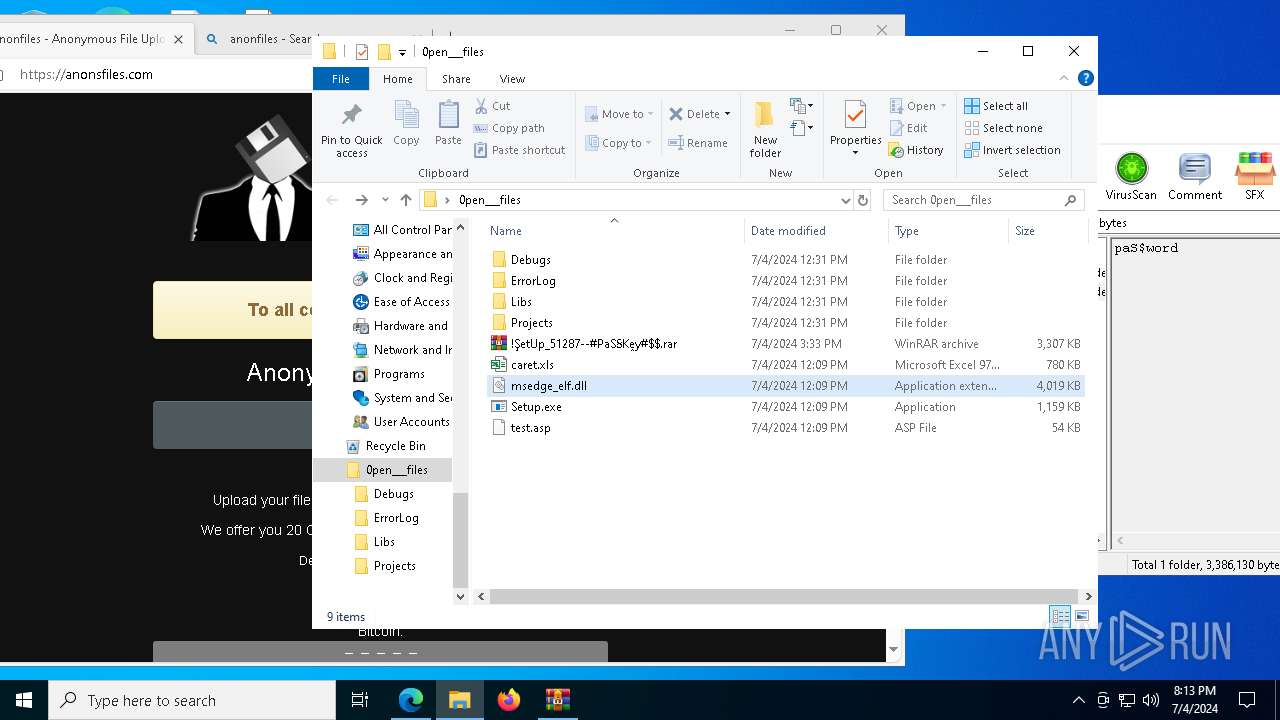
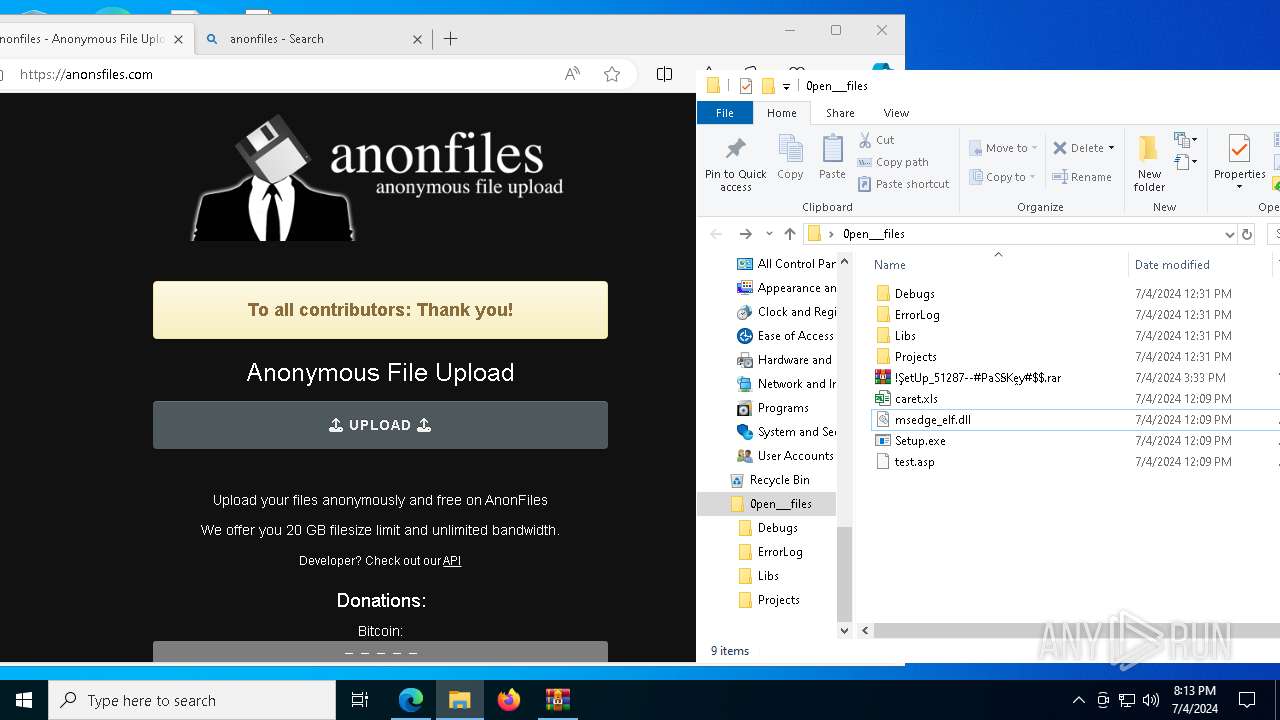
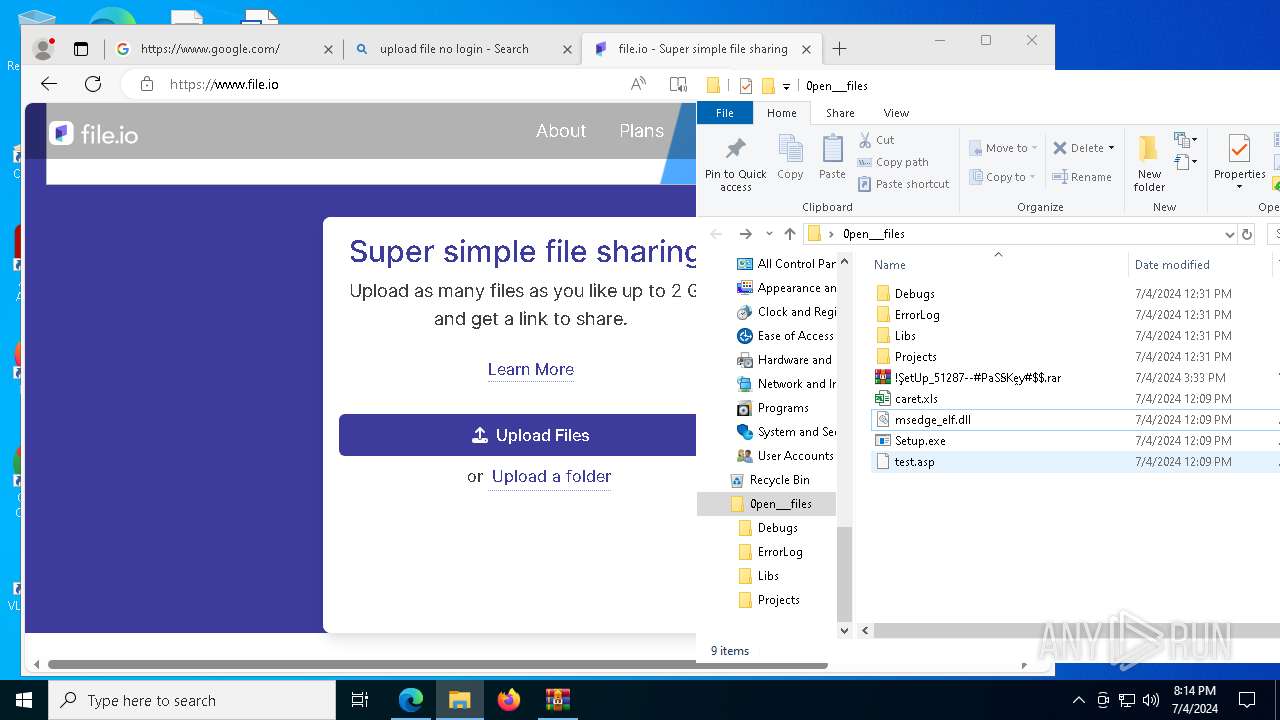
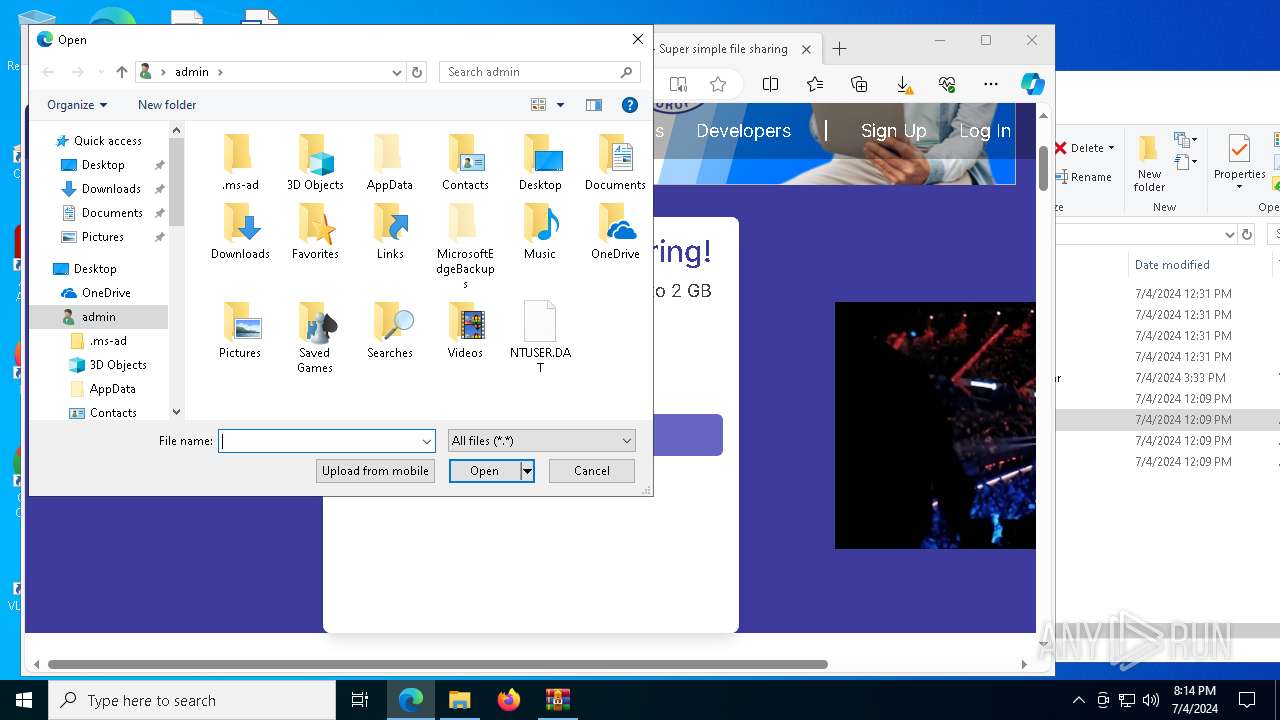
Manual execution by a user
- WinRAR.exe (PID: 528)
- Setup.exe (PID: 1328)
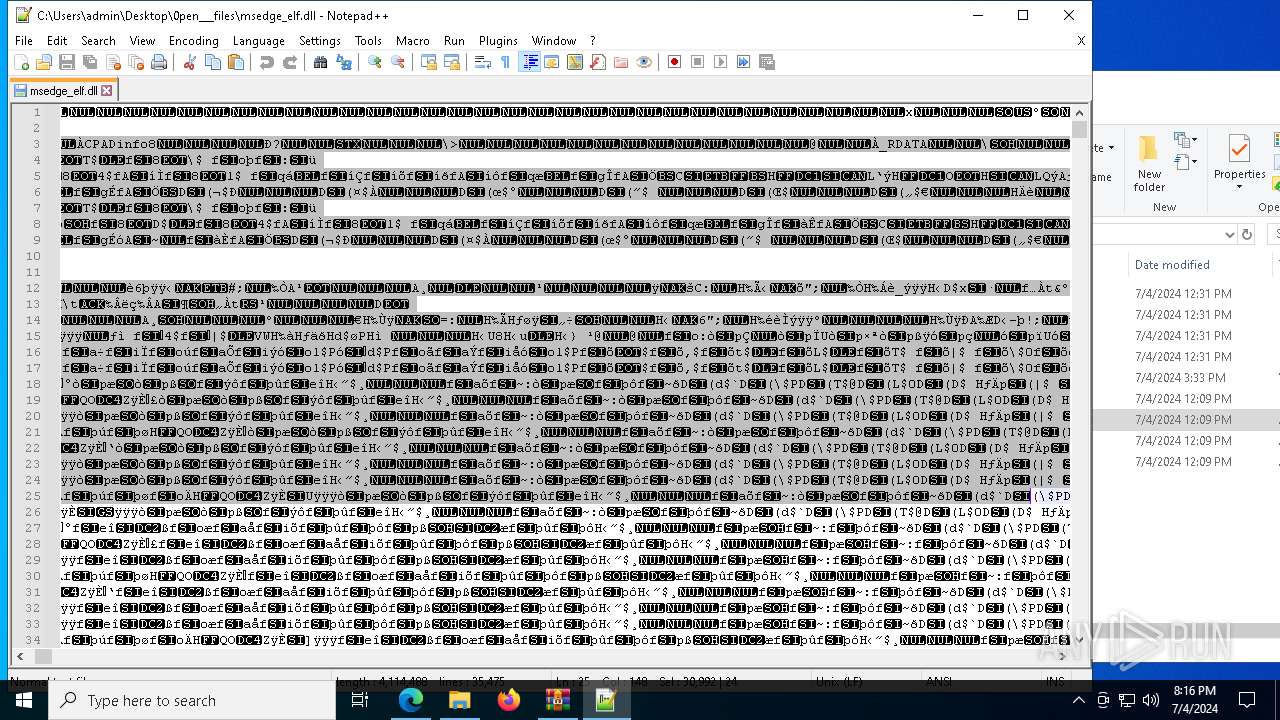
- notepad++.exe (PID: 8088)
Create files in a temporary directory
- Setup.exe (PID: 1328)
- more.com (PID: 8152)
- GXK7RM37JV8W5C9BZDKUMHY.exe (PID: 5988)
- SearchIndexer.exe (PID: 1792)
- HIDA9GYZNBRO1TDVEXMLI1P.exe (PID: 7688)
- comp.exe (PID: 1160)
- comp.exe (PID: 7740)
Reads the software policy settings
- slui.exe (PID: 2636)
- SearchIndexer.exe (PID: 1792)
- slui.exe (PID: 7956)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 528)
- msedge.exe (PID: 1928)
Creates files or folders in the user directory
- Setup.exe (PID: 1328)
Checks proxy server information
- explorer.exe (PID: 10224)
- slui.exe (PID: 7956)
Reads security settings of Internet Explorer
- explorer.exe (PID: 10224)
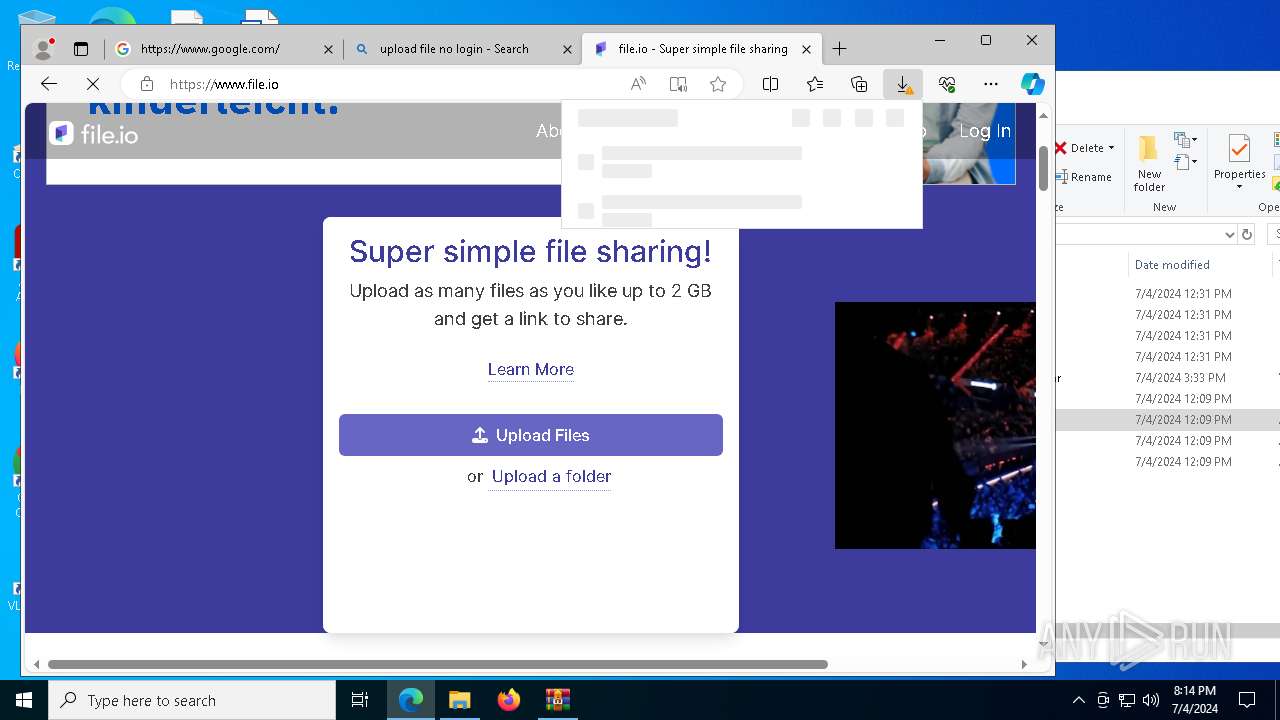
Application launched itself
- msedge.exe (PID: 1928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
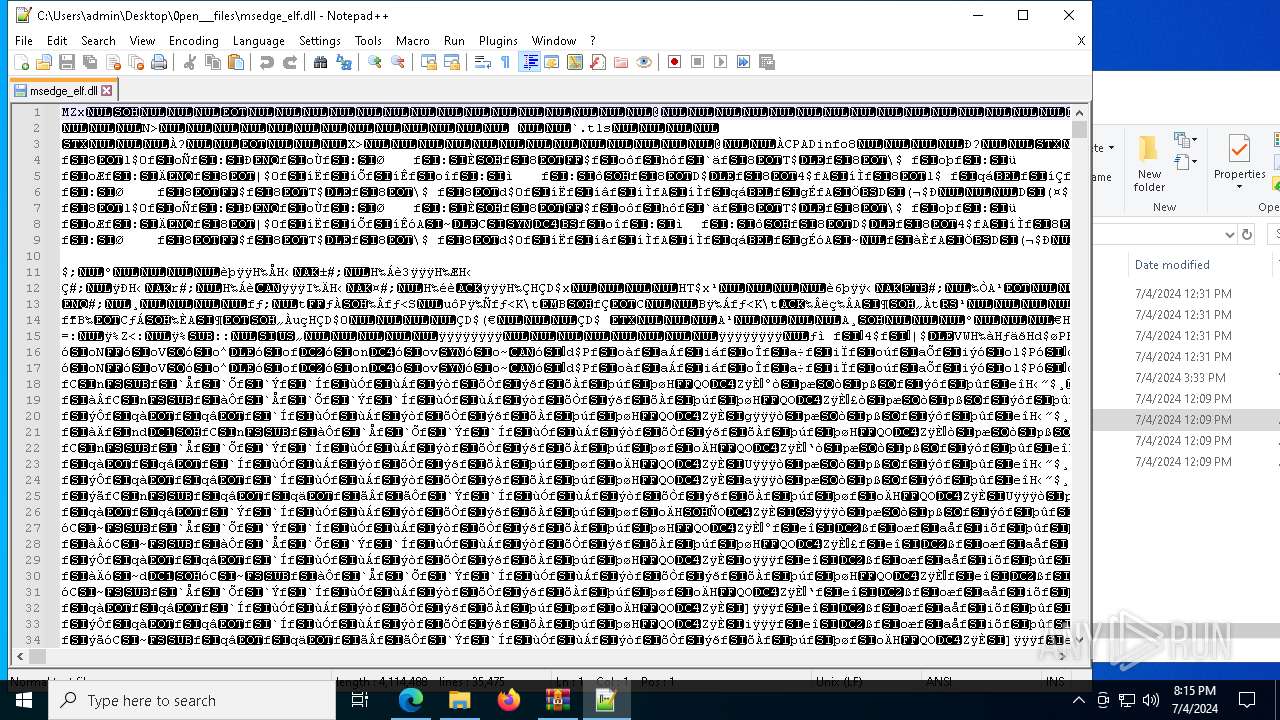
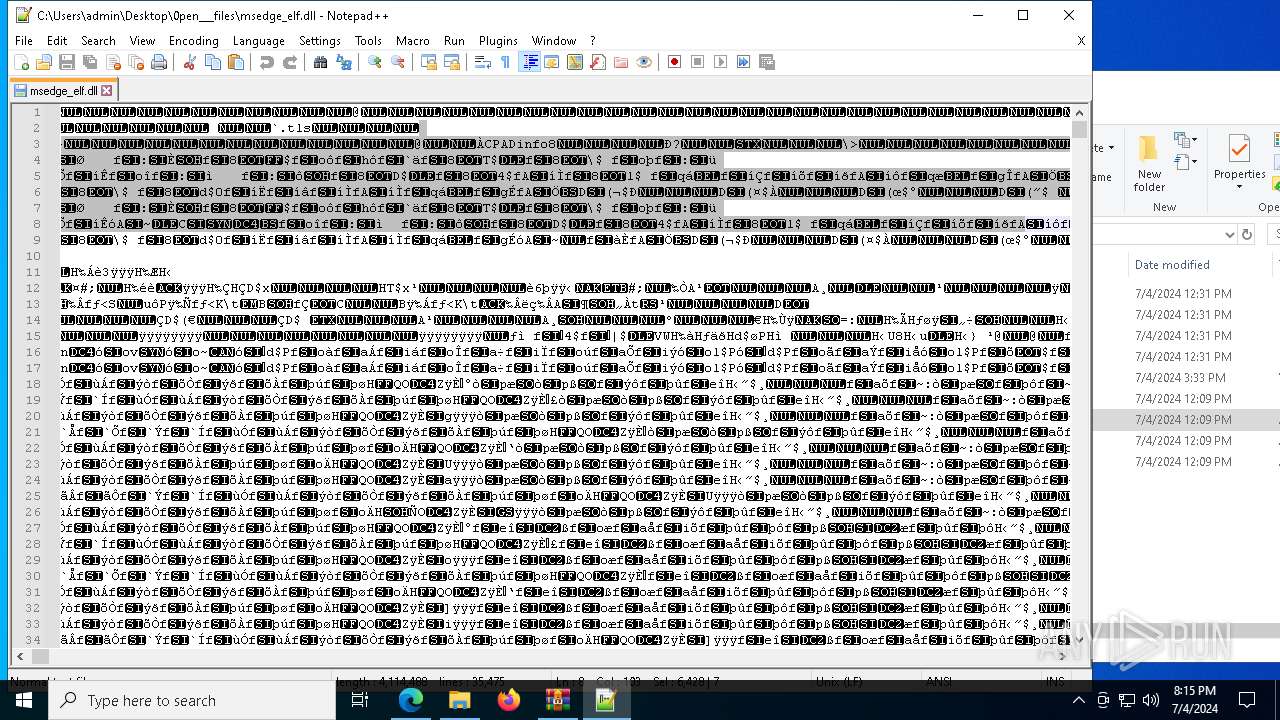
Amadey
(PID) Process(10224) explorer.exe
C2downloaddining.com
Strings (123)zip
2019
un:
.jpg
Content-Type: application/x-www-form-urlencoded
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
/quiet
exe
"
Content-Type: application/octet-stream
shutdown -s -t 0
vs:
Avira
&unit=
=
-executionpolicy remotesigned -File "
<c>
:::
Hkbsse.exe
rundll32
" && timeout 1 && del
POST
dm:
ESET
2022
Comodo
"taskkill /f /im "
st=s
-%lu
Bitdefender
f184b295cd
2016
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
&& Exit"
e2
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
d1
Powershell.exe
ComputerName
sd:
" && ren
<d>
r=
\App
downloaddining.com
ProgramData\
https://
WinDefender
#
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
id:
pc:
/k
Content-Type: multipart/form-data; boundary=----
VideoID
/h9fmdW6/index.php
wb
rb
lv:
Startup
downloaddining3.com
------
\0000
AVAST Software
GetNativeSystemInfo
rundll32.exe
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
cmd /C RMDIR /s/q
Main
ProductName
\
SOFTWARE\Microsoft\Windows NT\CurrentVersion
av:
+++
-unicode-
&&
e0
cmd
bi:
msi
DefaultSettings.XResolution
AVG
os:
--
Norton
S-%lu-
?scr=1
Content-Disposition: form-data; name="data"; filename="
"
/h9fmdW7/index.php
clip.dll
kernel32.dll
GET
DefaultSettings.YResolution
SYSTEM\ControlSet001\Services\BasicDisplay\Video
|
ps1
cred.dll
/Plugins/
dll
og:
/h9fmdW5/index.php
Sophos
%-lu
Programs
abcdefghijklmnopqrstuvwxyz0123456789-_
random
4.31
------
downloaddining2.com
Panda Security
0123456789
cred.dll|clip.dll|
Rem
CurrentBuild
http://
Kaspersky Lab
ar:
%USERPROFILE%
shell32.dll
360TotalSecurity
Doctor Web
e1
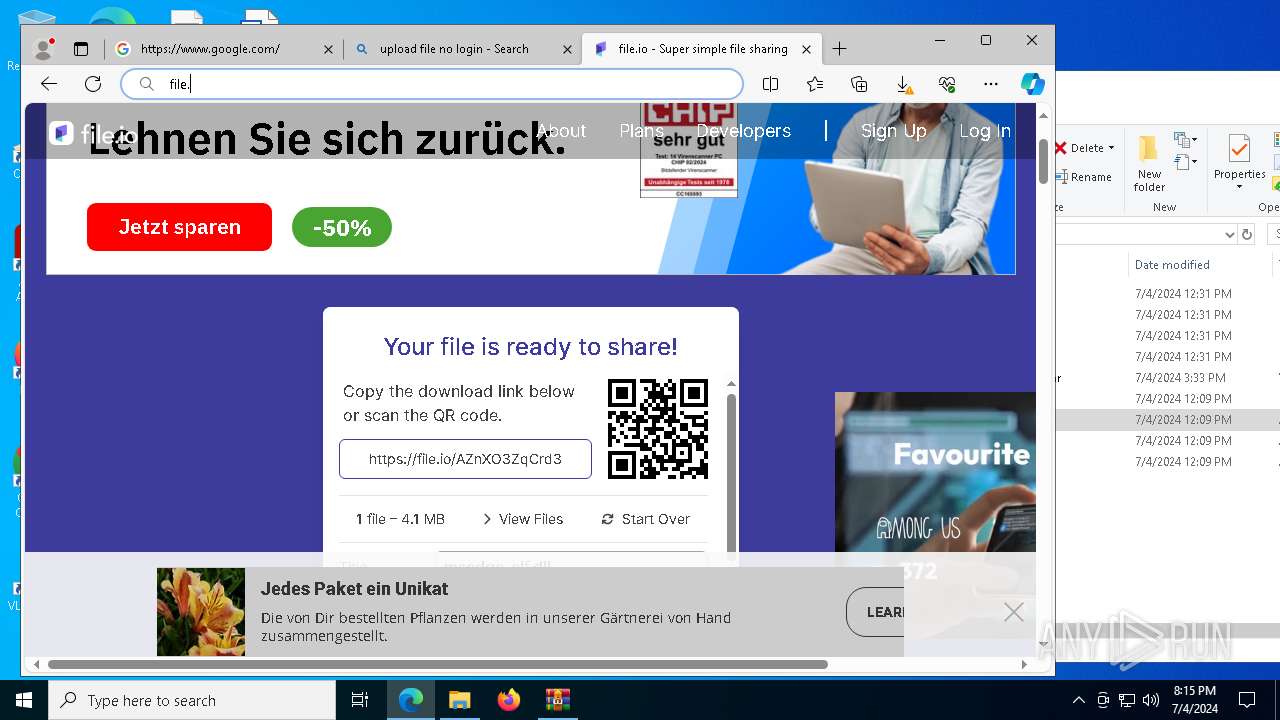
Total processes
313
Monitored processes
167
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
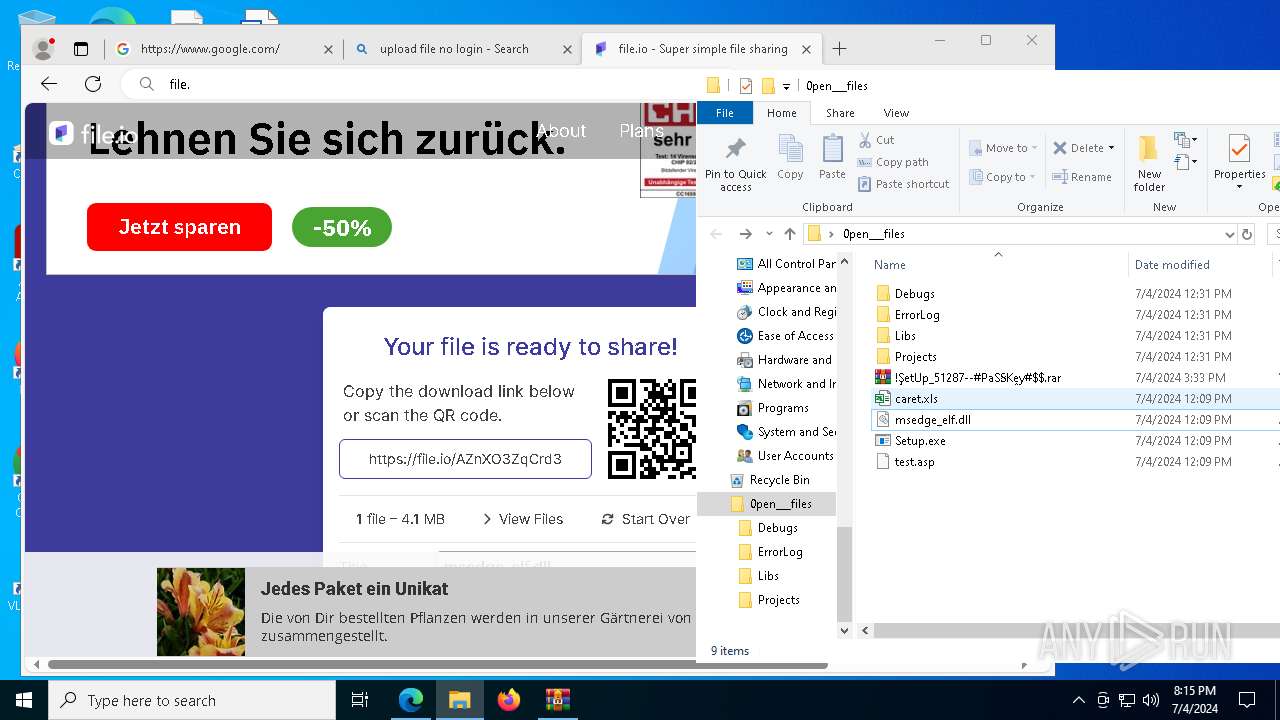
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=97 --mojo-platform-channel-handle=8712 --field-trial-handle=2284,i,4994901678013397528,6902240200503182224,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
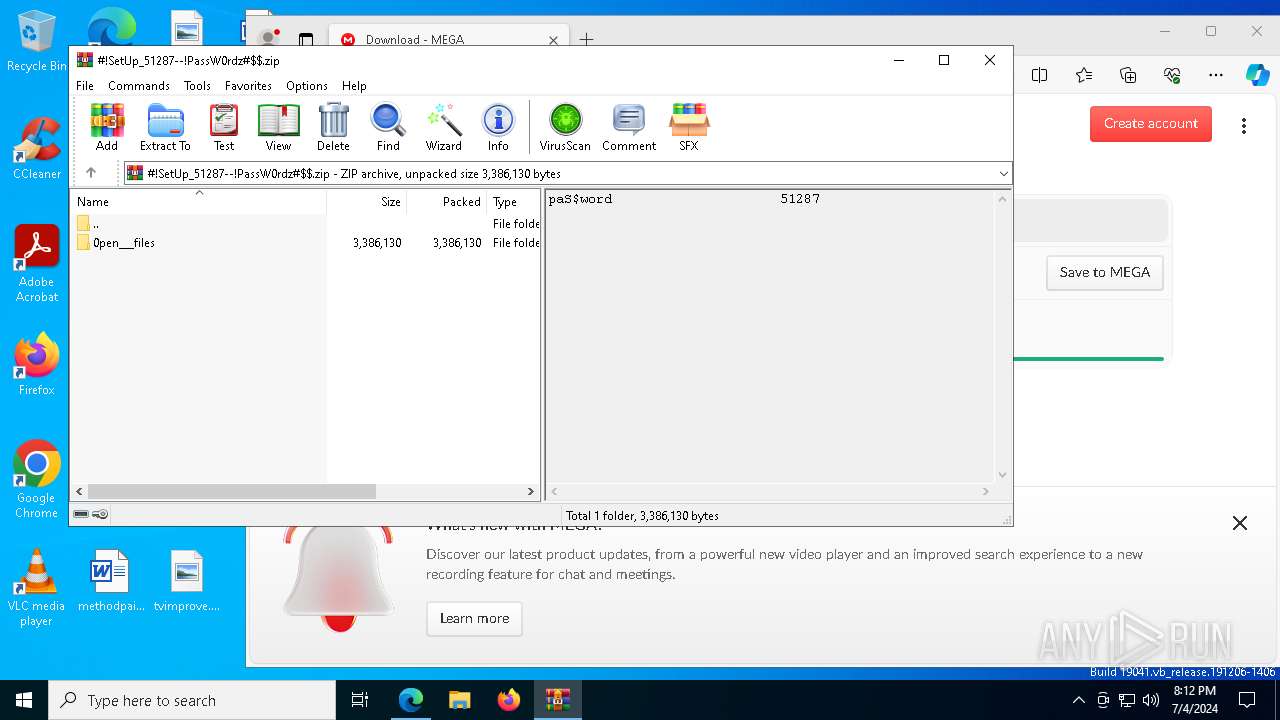
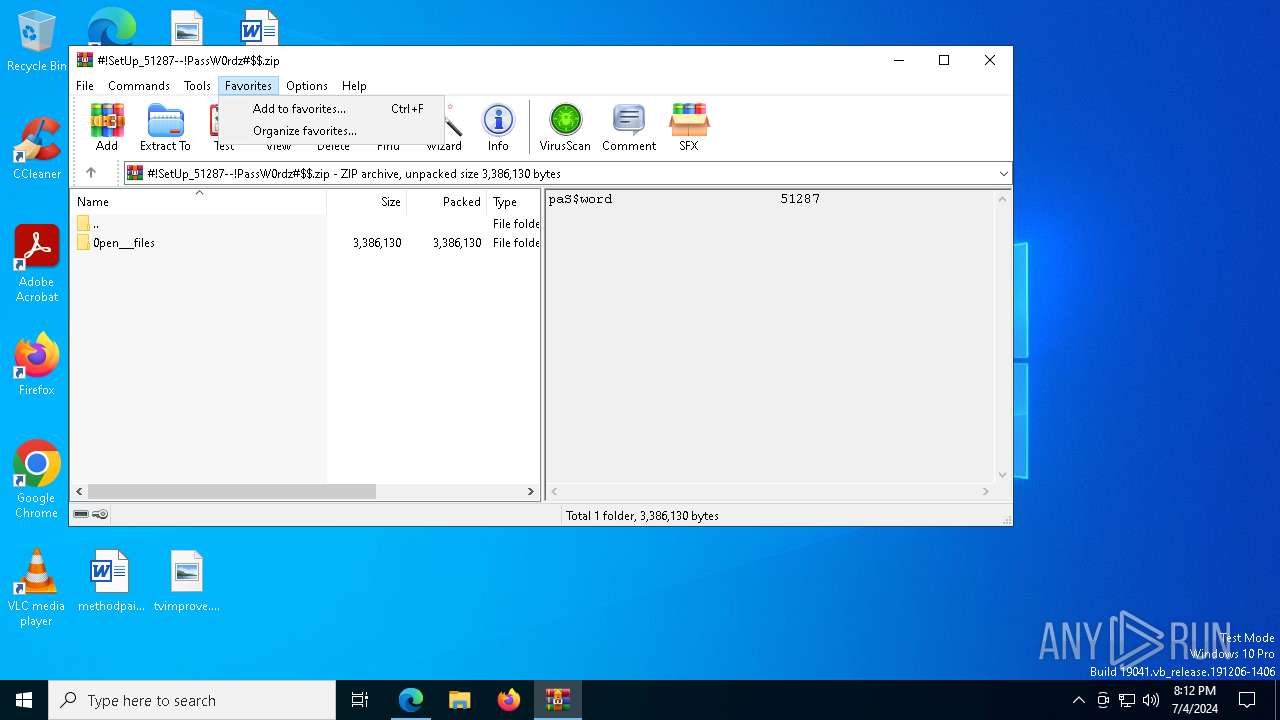
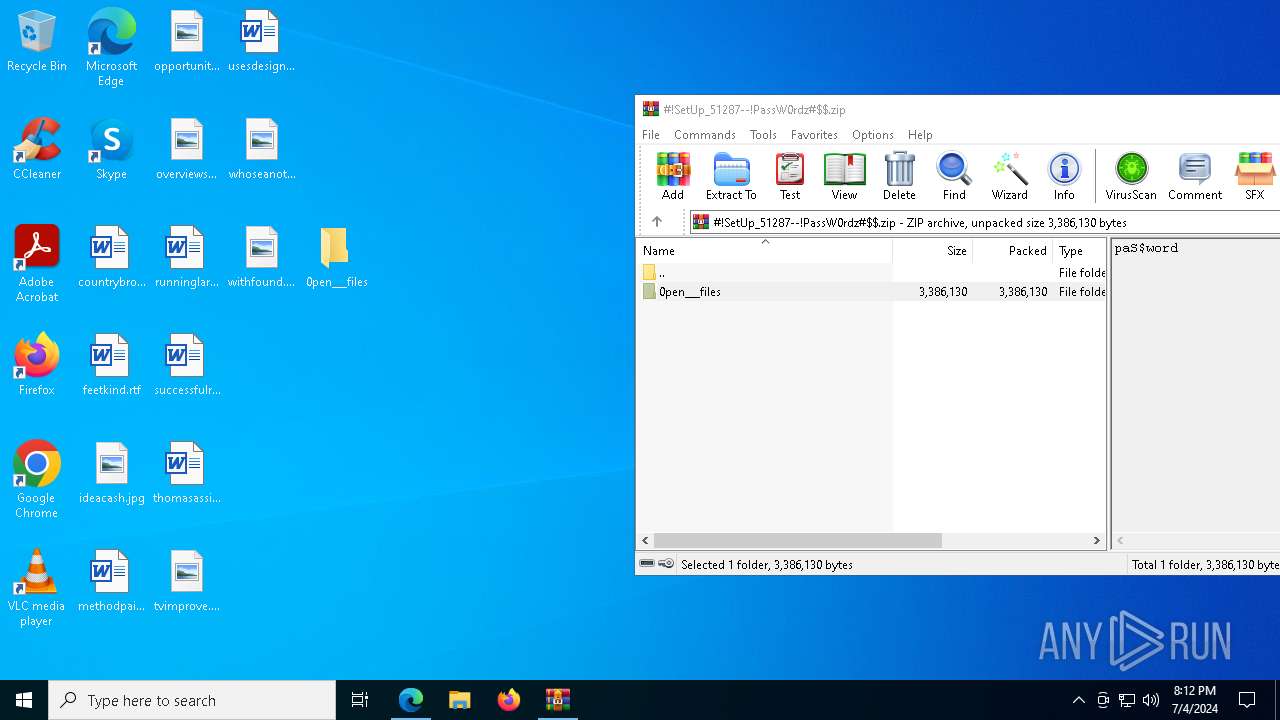
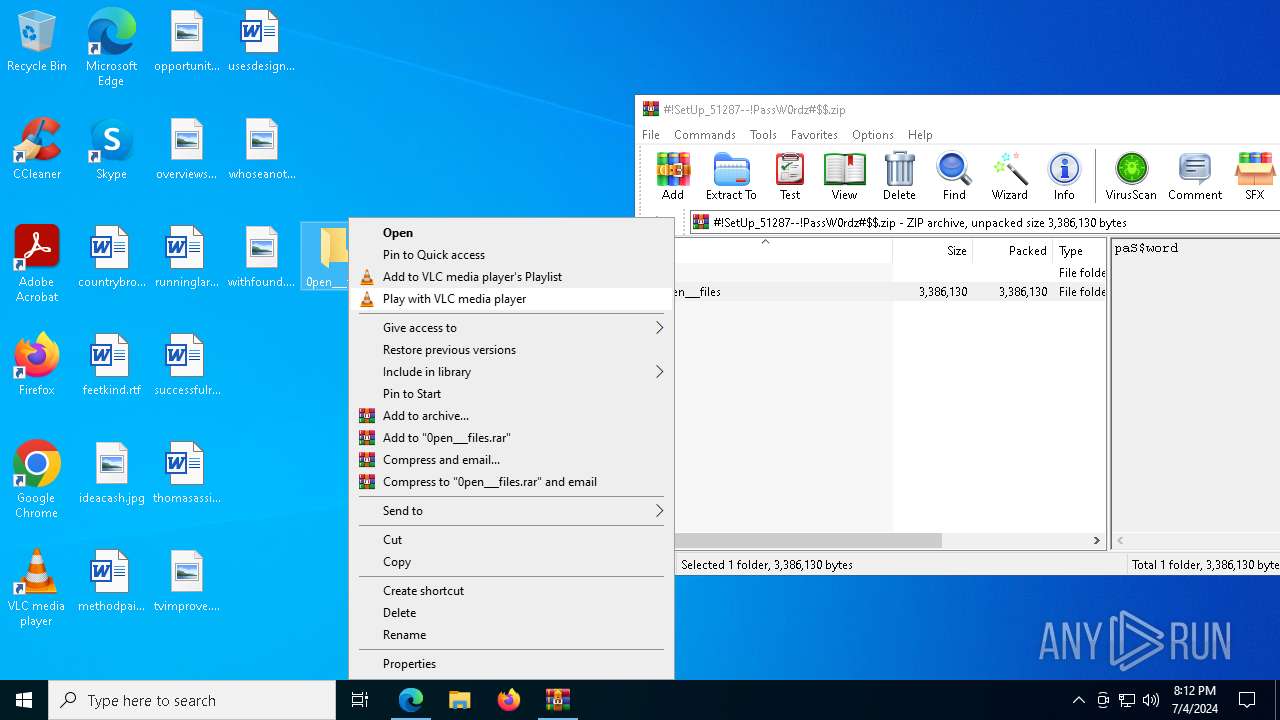
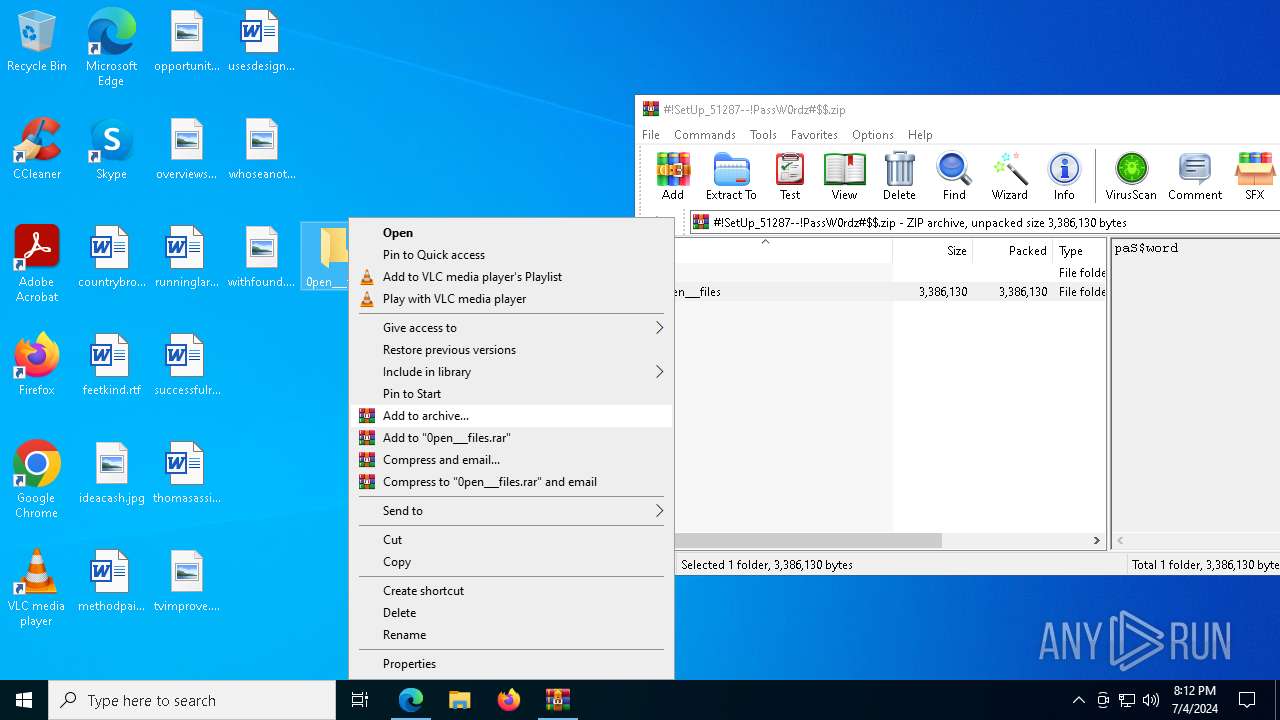
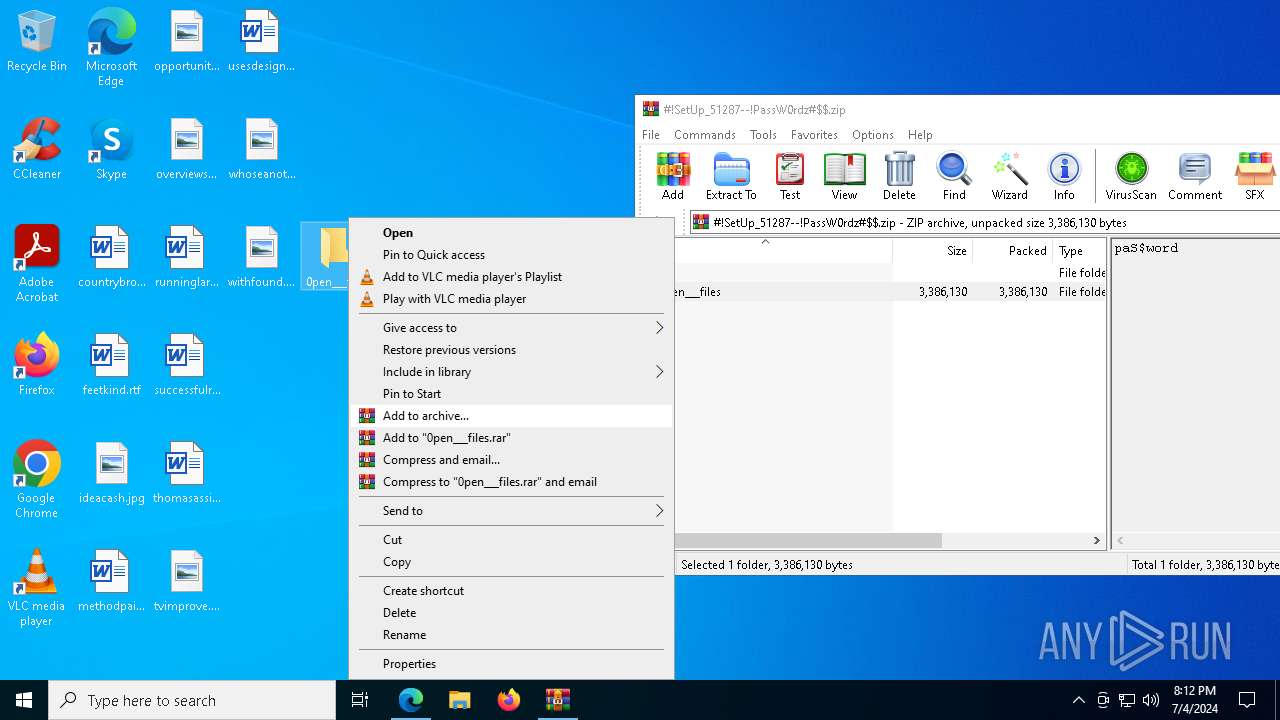
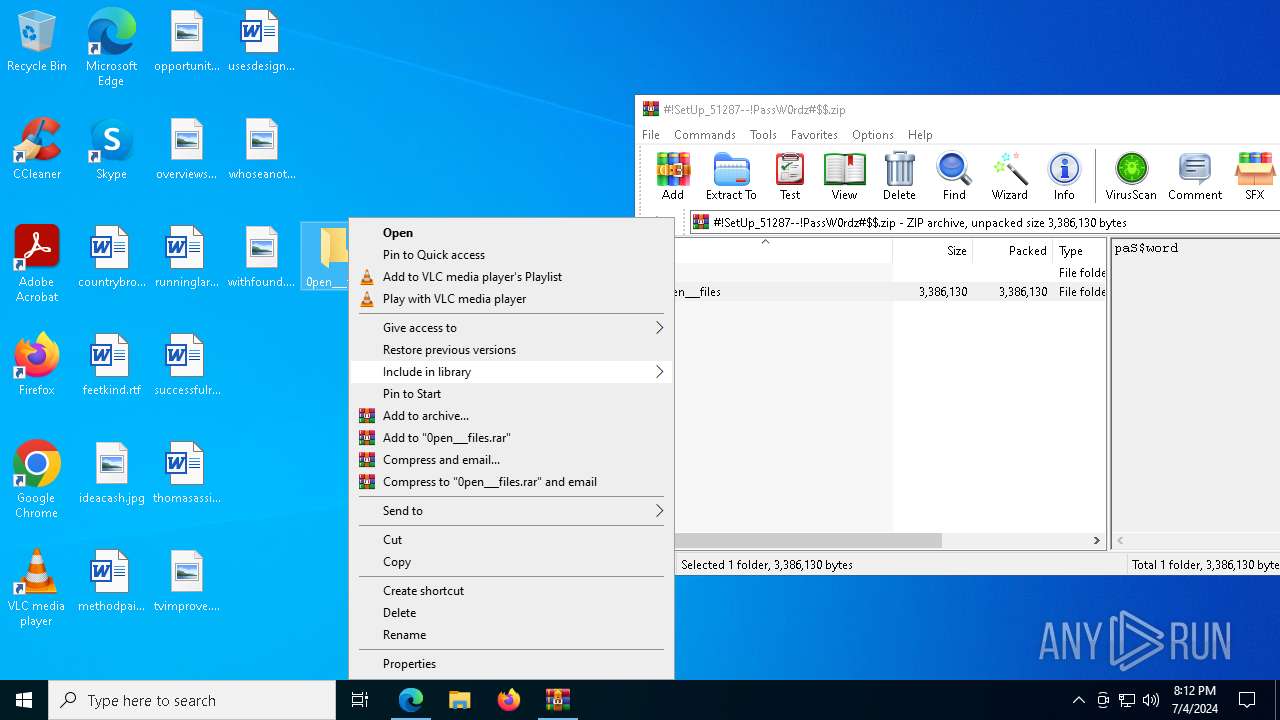
| 528 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\0pen___files\!ŞetUp_51287--#PaSꞨKḙy#$.rar" C:\Users\admin\Desktop\0pen___files\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 740 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6040 --field-trial-handle=2284,i,4994901678013397528,6902240200503182224,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=100 --mojo-platform-channel-handle=8724 --field-trial-handle=2284,i,4994901678013397528,6902240200503182224,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1160 | C:\WINDOWS\SysWOW64\comp.exe | C:\Windows\SysWOW64\comp.exe | GXK7RM37JV8W5C9BZDKUMHY.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: File Compare Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=57 --mojo-platform-channel-handle=6660 --field-trial-handle=2284,i,4994901678013397528,6902240200503182224,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=12000 --field-trial-handle=2284,i,4994901678013397528,6902240200503182224,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7276 --field-trial-handle=2284,i,4994901678013397528,6902240200503182224,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1328 | "C:\Users\admin\Desktop\0pen___files\Setup.exe" | C:\Users\admin\Desktop\0pen___files\Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: PWA Identity Proxy Host Exit code: 1 Version: 120.0.2210.61 Modules
| |||||||||||||||
| 1544 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x2ec,0x2f0,0x2f4,0x2e8,0x2fc,0x7ffd95195fd8,0x7ffd95195fe4,0x7ffd95195ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
33 571
Read events
33 123
Write events
420
Delete events
28
Modification events
| (PID) Process: | (1928) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1928) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1928) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1928) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1928) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1928) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1928) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1928) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (1928) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1928) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
25
Suspicious files
708
Text files
220
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1928 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1ceac5.TMP | — | |
MD5:— | SHA256:— | |||
| 1928 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1ceac5.TMP | — | |
MD5:— | SHA256:— | |||
| 1928 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1928 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1cead5.TMP | — | |
MD5:— | SHA256:— | |||
| 1928 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1928 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1cead5.TMP | — | |
MD5:— | SHA256:— | |||
| 1928 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1928 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1928 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1ceaf4.TMP | — | |
MD5:— | SHA256:— | |||
| 1928 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
63
TCP/UDP connections
614
DNS requests
718
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2248 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | unknown |
2248 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | unknown |
8024 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | unknown |
6756 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | unknown |
2276 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | unknown |
8024 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | unknown |
5052 | svchost.exe | HEAD | 200 | 23.53.40.65:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fdb8099d-2f6c-4383-8278-f7bc83f63cf3?P1=1720569935&P2=404&P3=2&P4=H8QonKqqez7oJo8zROgBJqm1YzKQdsv4lWaiIKSahqzIdr0mYqEliafcaYDt3Q%2bcuKxFx24RLJV5fspInCLU%2bA%3d%3d | DE | — | — | unknown |
5052 | svchost.exe | GET | 206 | 23.53.40.65:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fdb8099d-2f6c-4383-8278-f7bc83f63cf3?P1=1720569935&P2=404&P3=2&P4=H8QonKqqez7oJo8zROgBJqm1YzKQdsv4lWaiIKSahqzIdr0mYqEliafcaYDt3Q%2bcuKxFx24RLJV5fspInCLU%2bA%3d%3d | DE | binary | 1.09 Kb | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | unknown |
5052 | svchost.exe | GET | 206 | 23.53.40.65:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fdb8099d-2f6c-4383-8278-f7bc83f63cf3?P1=1720569935&P2=404&P3=2&P4=H8QonKqqez7oJo8zROgBJqm1YzKQdsv4lWaiIKSahqzIdr0mYqEliafcaYDt3Q%2bcuKxFx24RLJV5fspInCLU%2bA%3d%3d | DE | binary | 14 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1776 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2448 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2248 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6248 | msedge.exe | 172.67.159.49:443 | f95zone.to.it | — | — | unknown |
1928 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6248 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6248 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6248 | msedge.exe | 13.107.246.60:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
f95zone.to.it |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| unknown |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6248 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
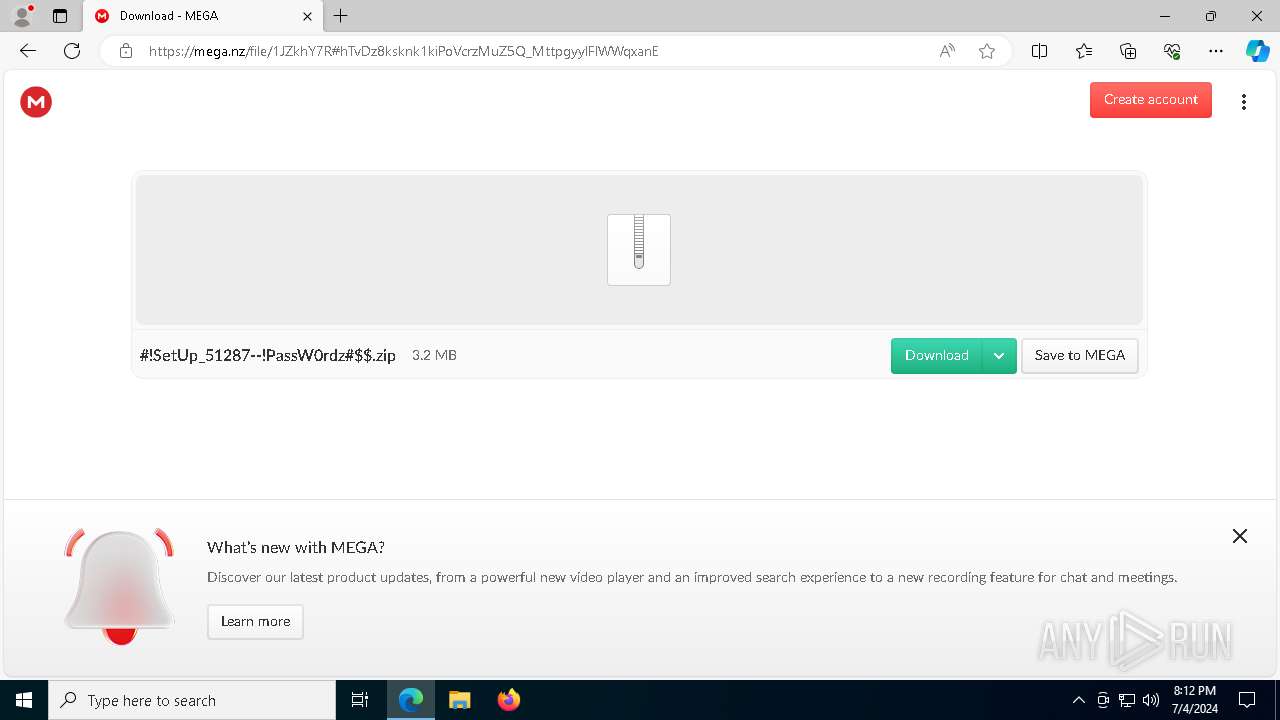
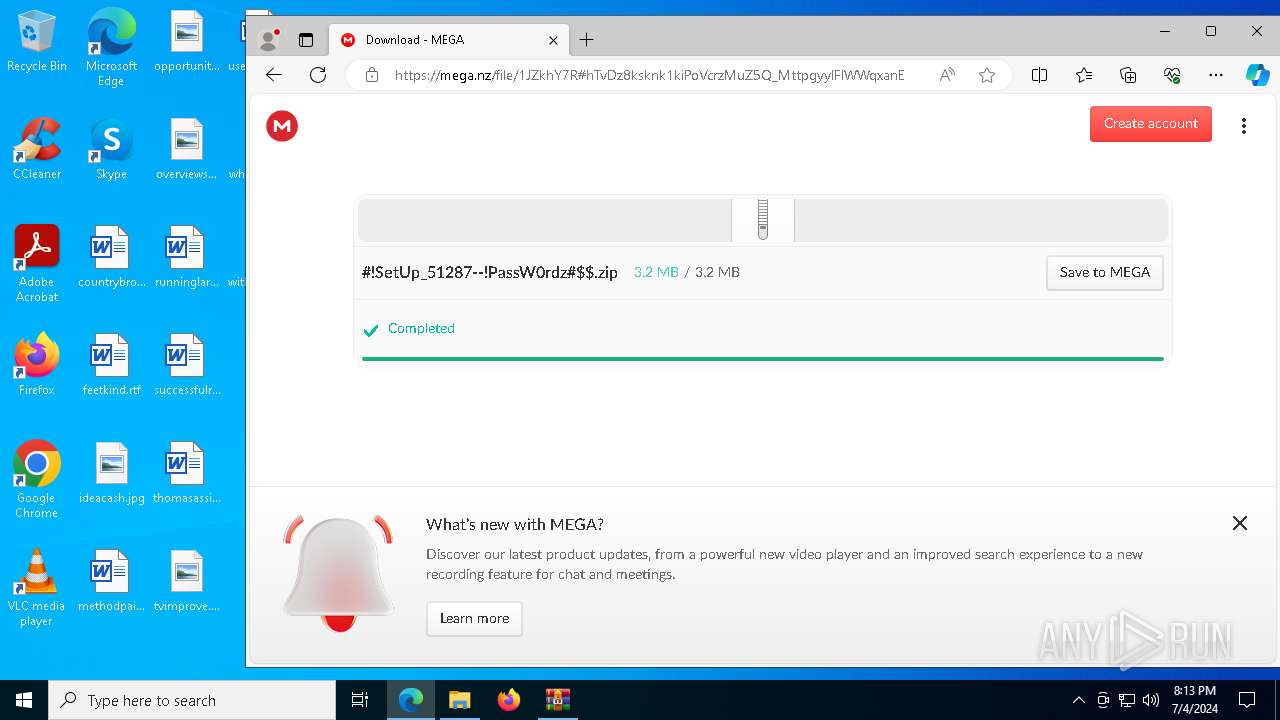
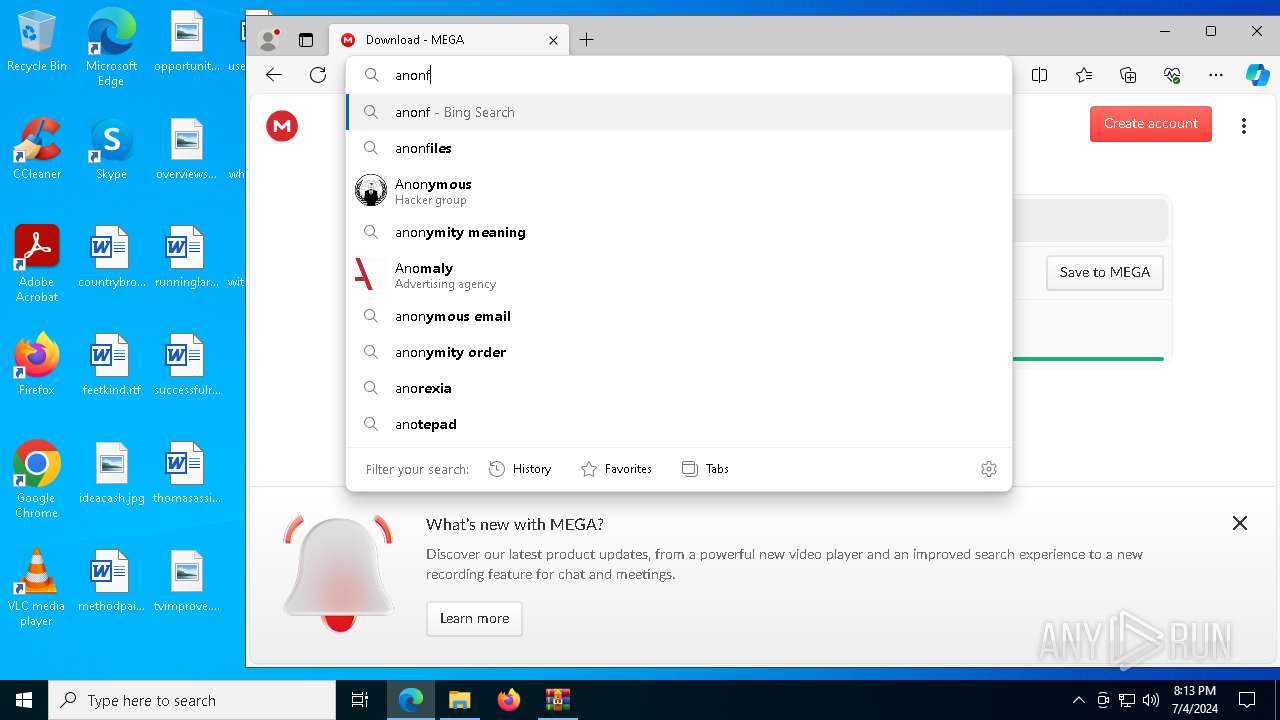
6248 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
6248 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
6248 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
6248 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
6248 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
6248 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
6248 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
6248 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
6248 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|