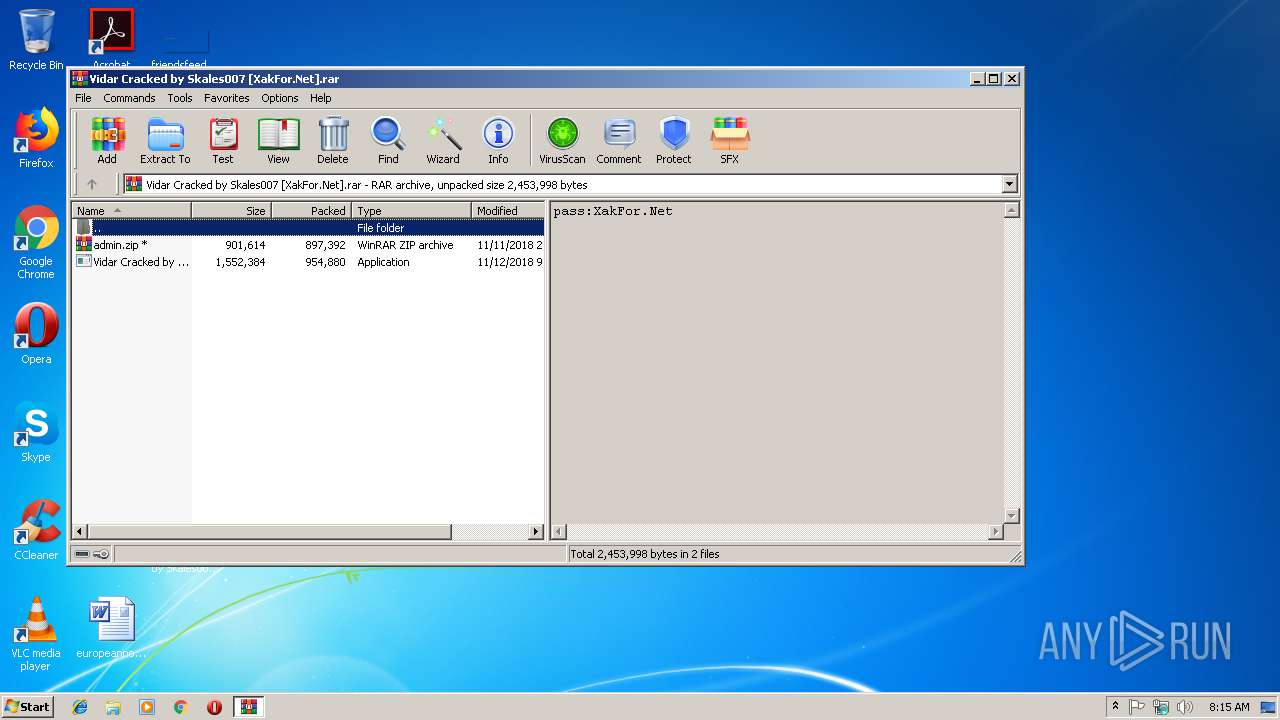
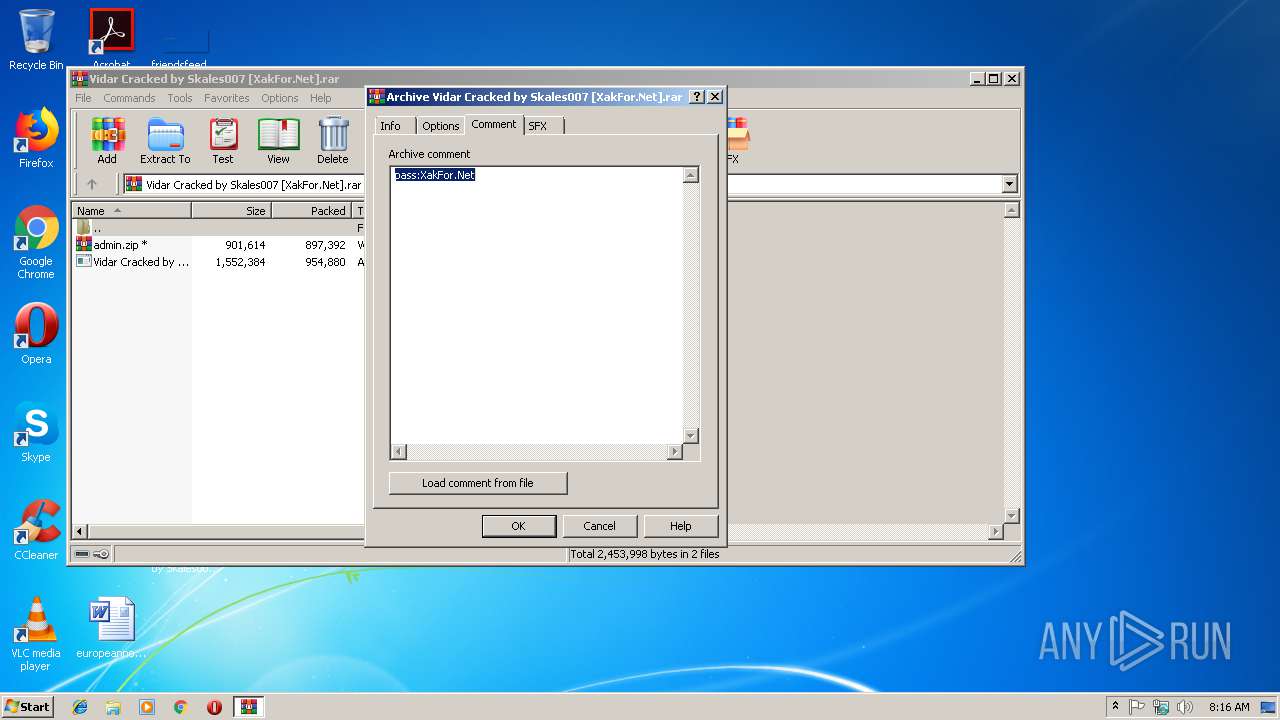
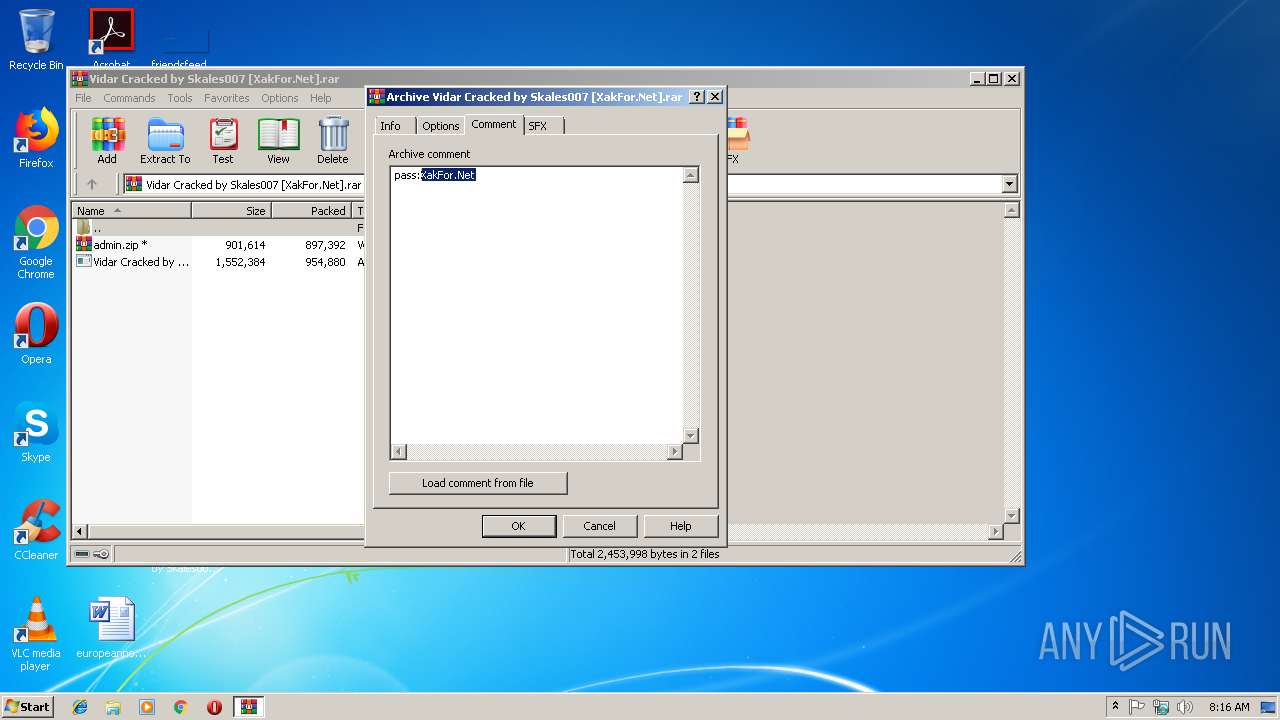
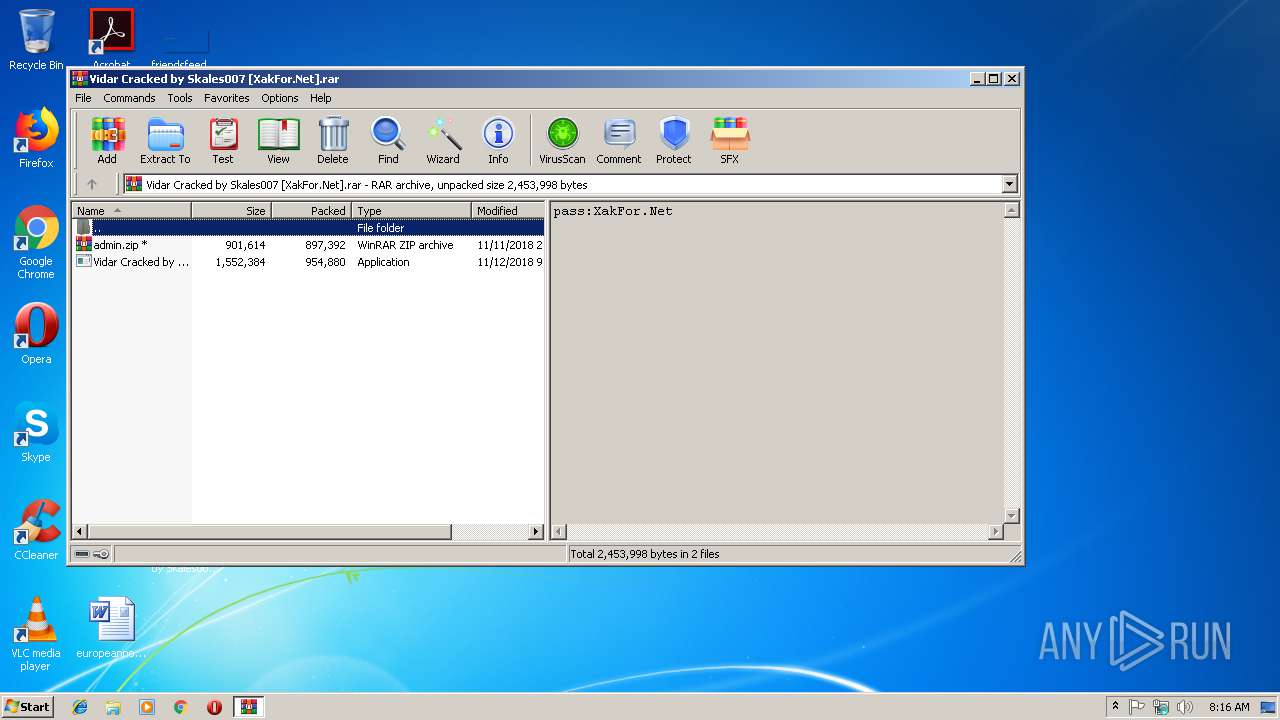
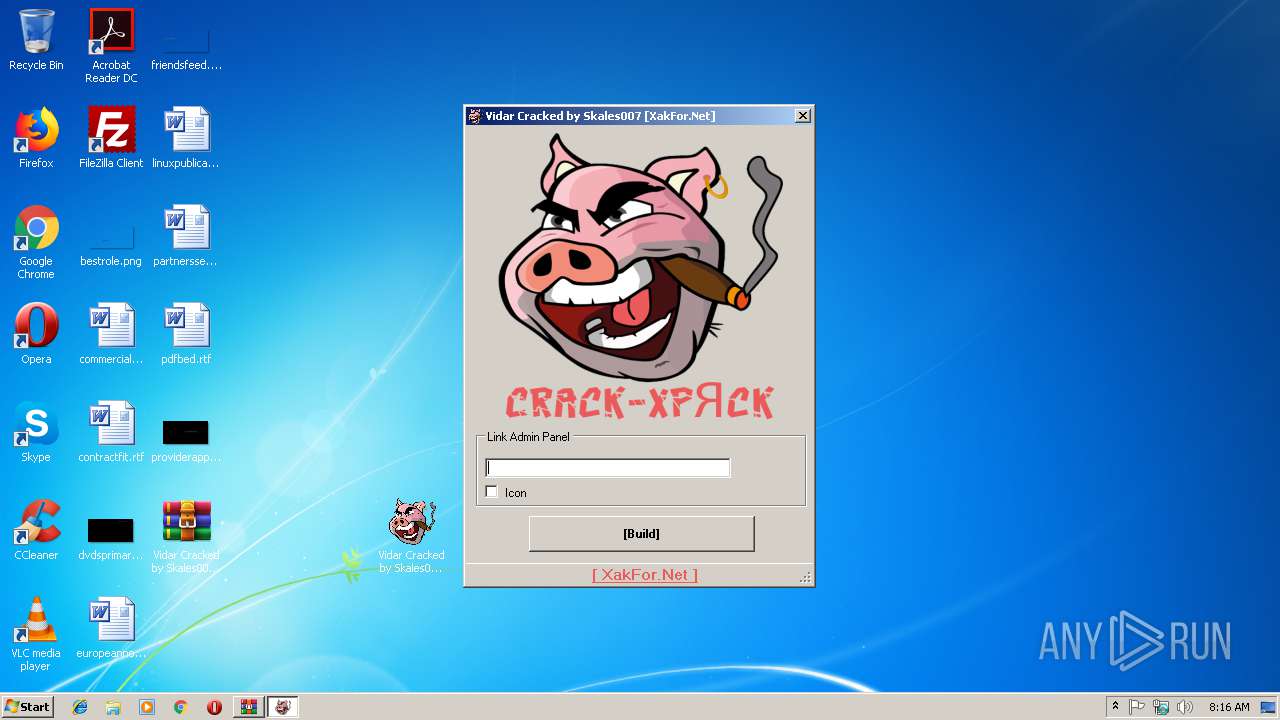
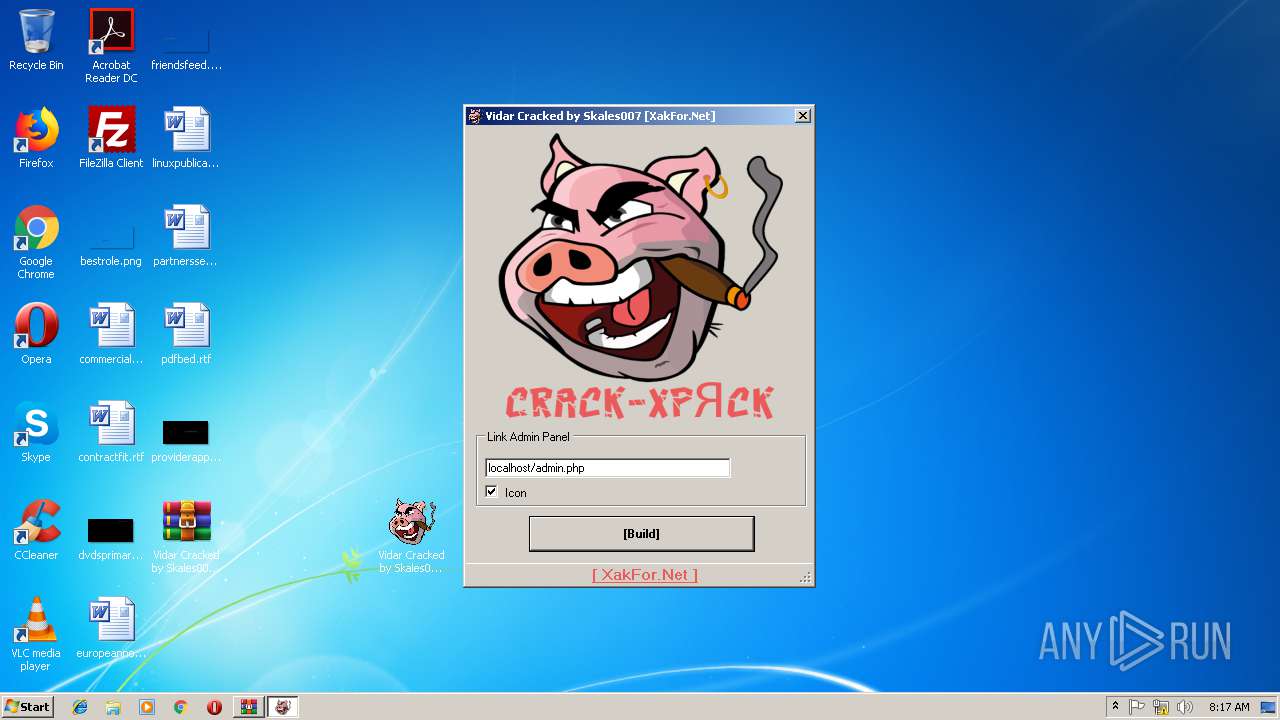
| File name: | Vidar Cracked by Skales007 [XakFor.Net].rar |
| Full analysis: | https://app.any.run/tasks/95e920b3-7f54-46cf-b1d5-689c2ecbad4e |
| Verdict: | Malicious activity |
| Threats: | Arkei is a stealer type malware capable of collecting passwords, autosaved forms, cryptocurrency wallet credentials, and files. |
| Analysis date: | December 06, 2018, 08:15:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 44BFA00E965CD475467AA2FE20CCD15E |
| SHA1: | F6D2B251202F23C967E513DF928C5AB084B34CBC |
| SHA256: | 3A3765DC248D9B07B8090EDD5B6A67159B1D277B42BEBC58E1699FEAACE39A22 |
| SSDEEP: | 49152:zloY/Lx1TVScf/f5hMYqADqqIIkyRY8xQtOoqGgOqC:Px1Jbf/f5hvqOzadqGgOR |
MALICIOUS
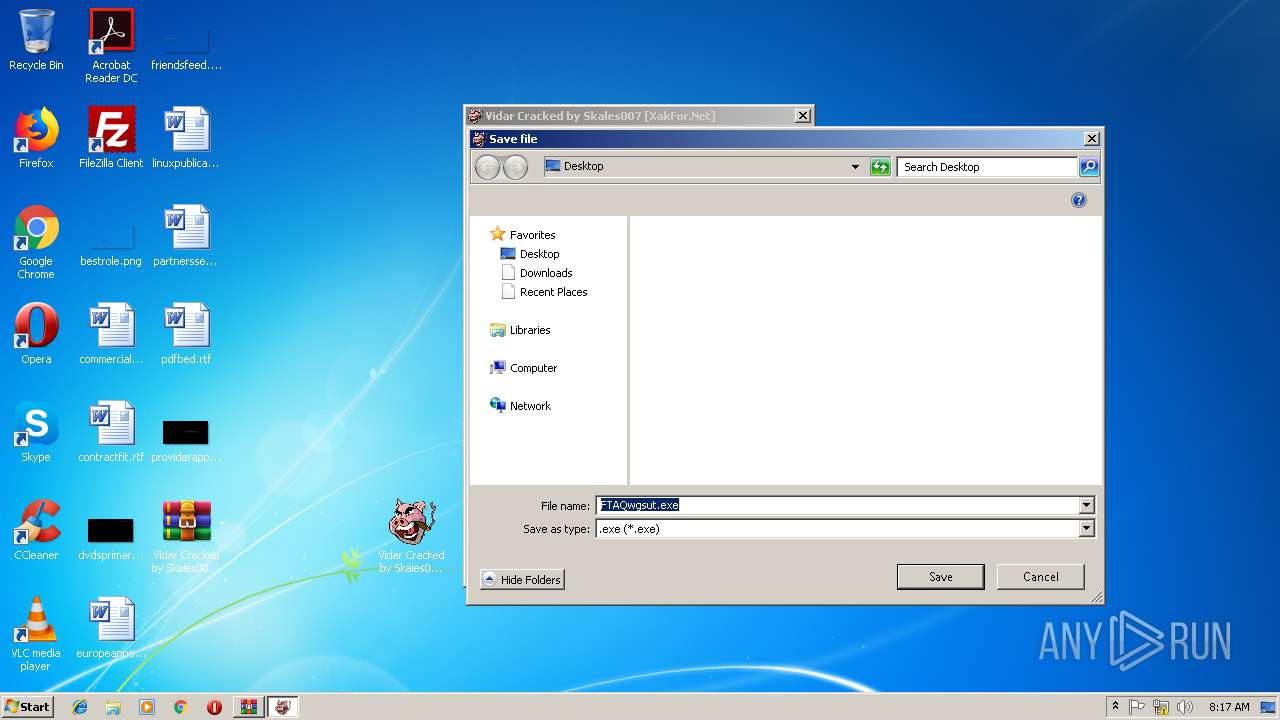
Application was dropped or rewritten from another process
- Vidar Cracked by Skales007 [XakFor.Net].exe (PID: 3388)
- FTAQwgsut.exe (PID: 3484)
ARKEI was detected
- FTAQwgsut.exe (PID: 3484)
Stealing of credential data
- FTAQwgsut.exe (PID: 3484)
Actions looks like stealing of personal data
- FTAQwgsut.exe (PID: 3484)
SUSPICIOUS
Executable content was dropped or overwritten
- Vidar Cracked by Skales007 [XakFor.Net].exe (PID: 3388)
Loads DLL from Mozilla Firefox
- FTAQwgsut.exe (PID: 3484)
Checks for external IP
- FTAQwgsut.exe (PID: 3484)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3712)
Creates files in the program directory
- FTAQwgsut.exe (PID: 3484)
Starts CMD.EXE for commands execution
- FTAQwgsut.exe (PID: 3484)
Creates files in the user directory
- FTAQwgsut.exe (PID: 3484)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
38
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2780 | taskkill /im FTAQwgsut.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
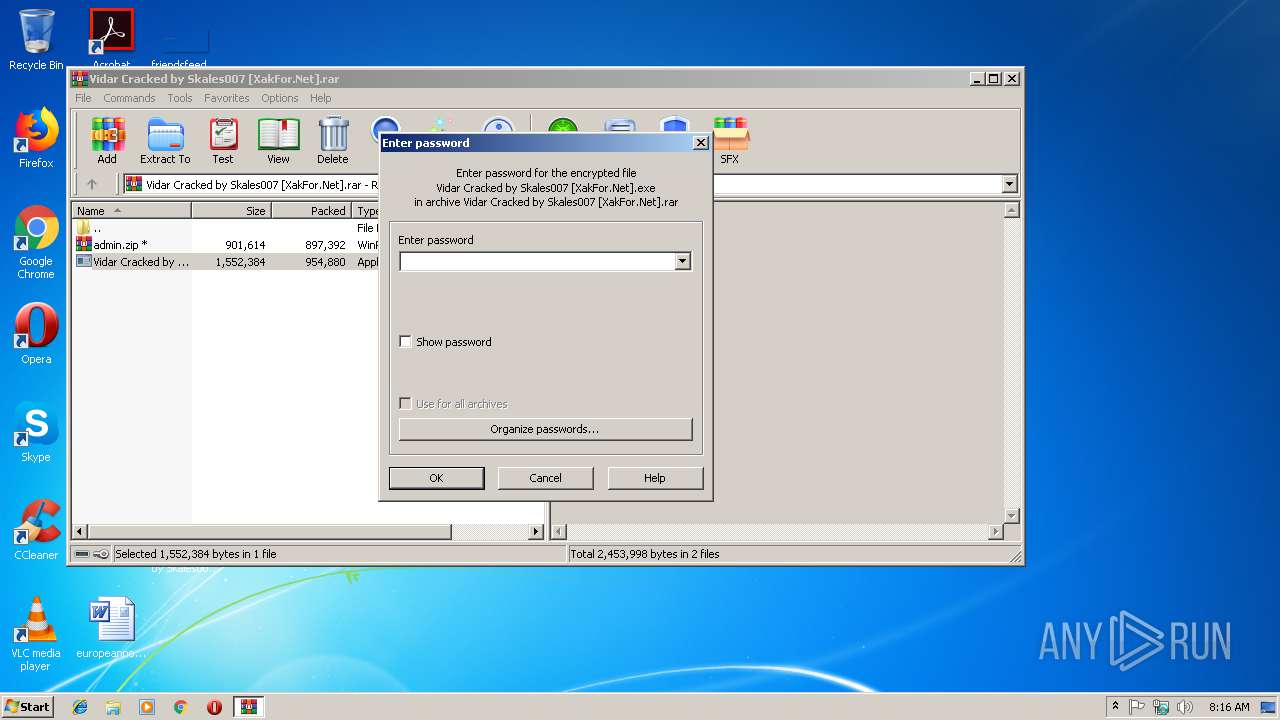
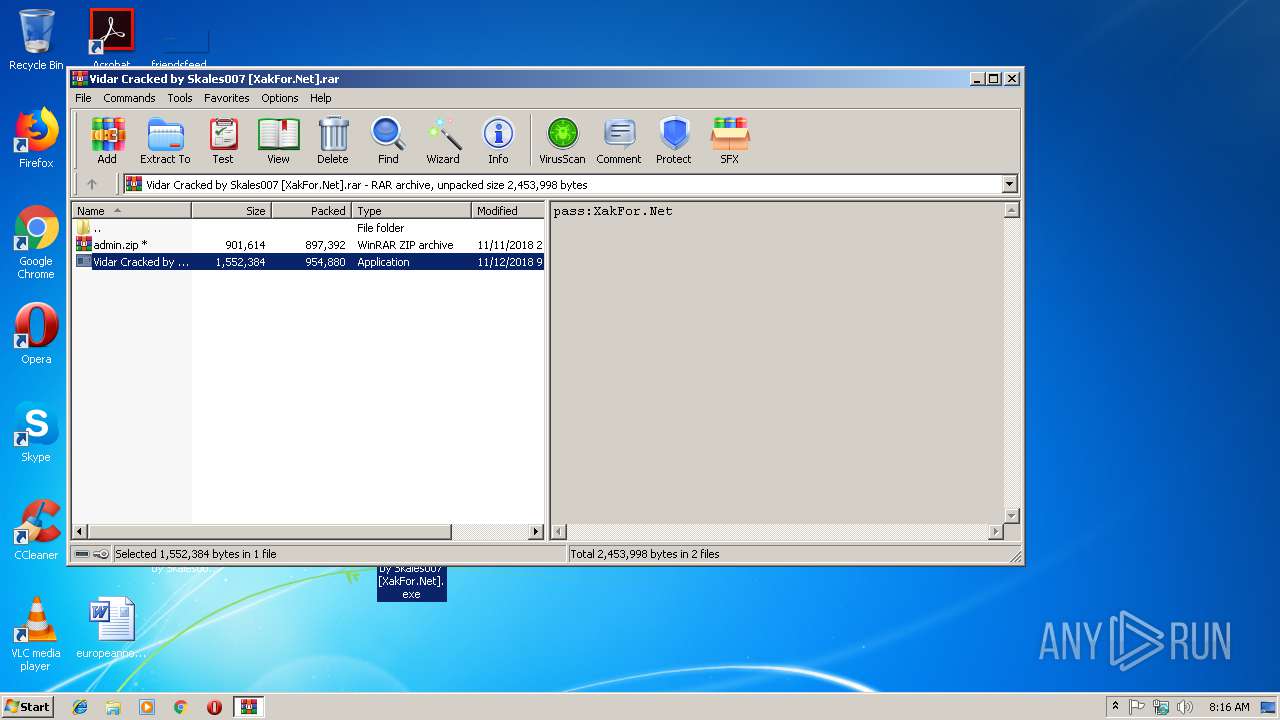
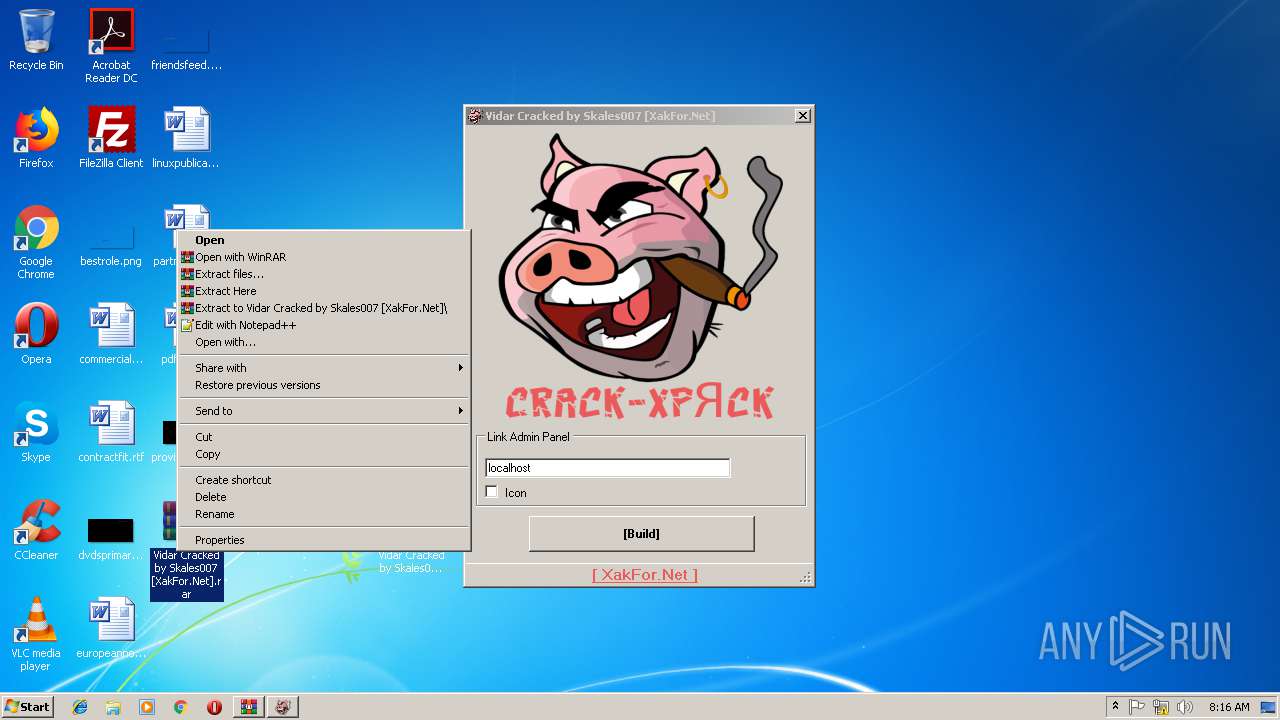
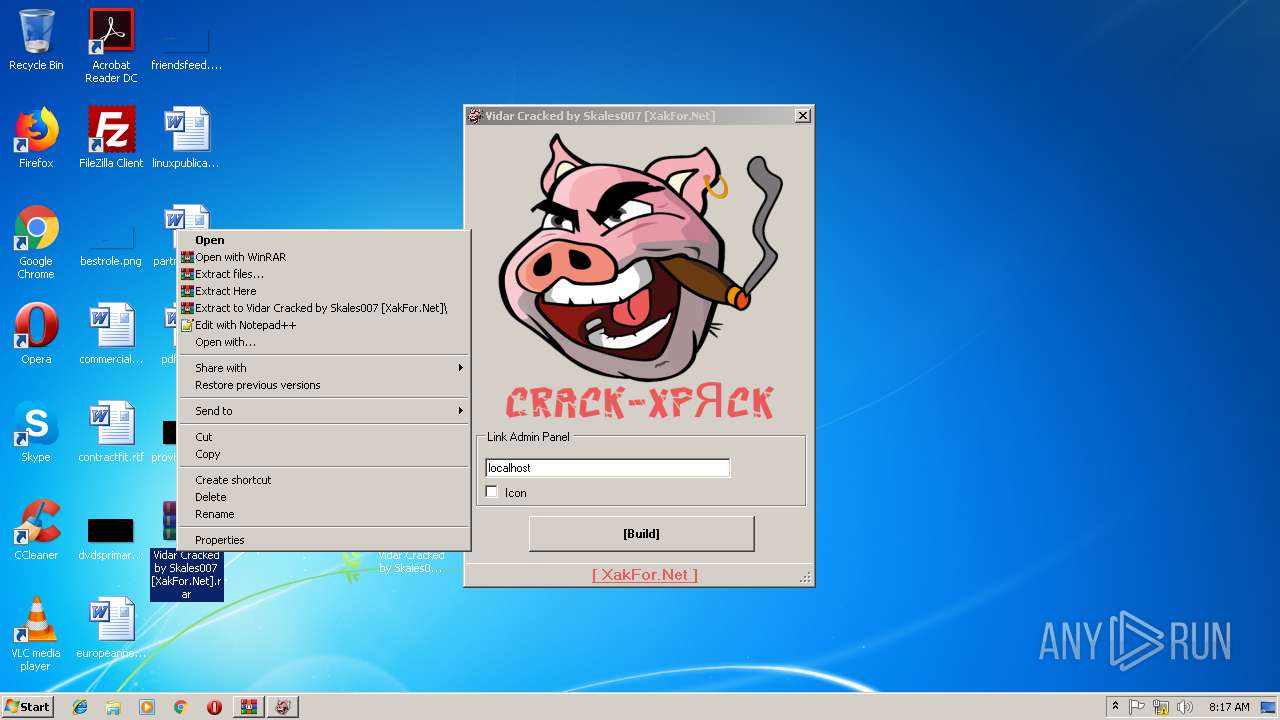
| 2960 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Vidar Cracked by Skales007 [XakFor.Net].rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
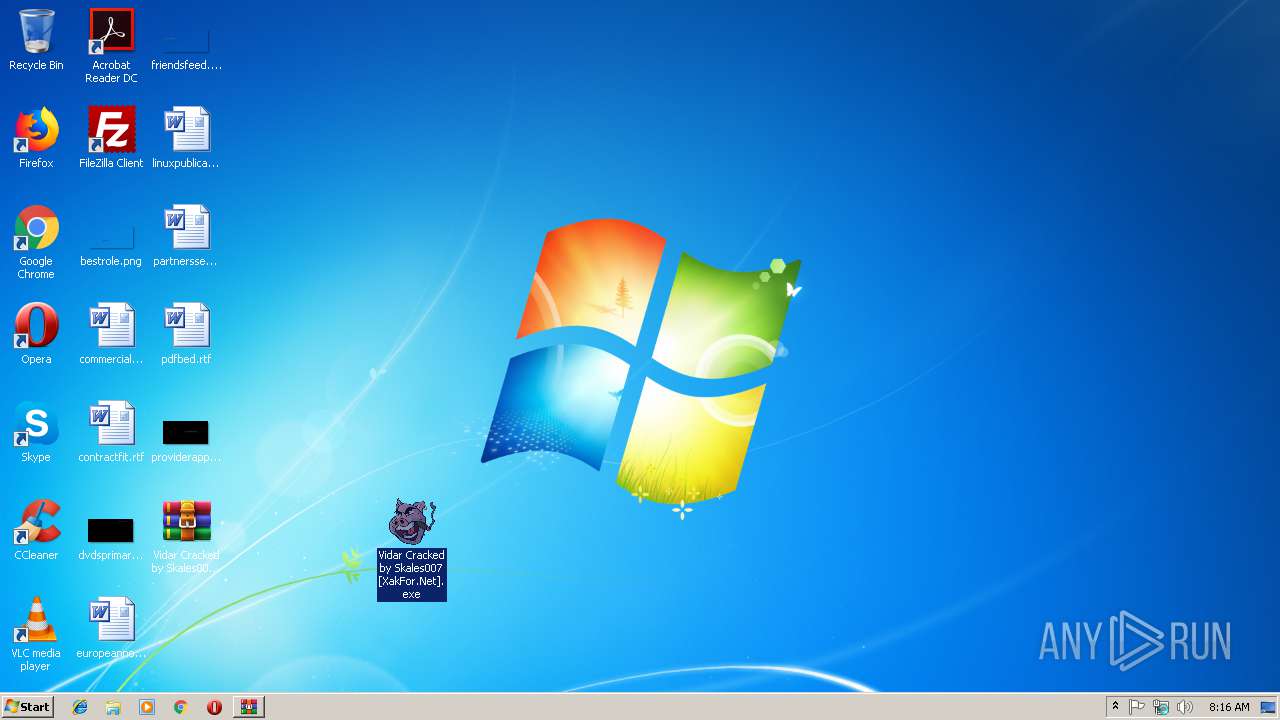
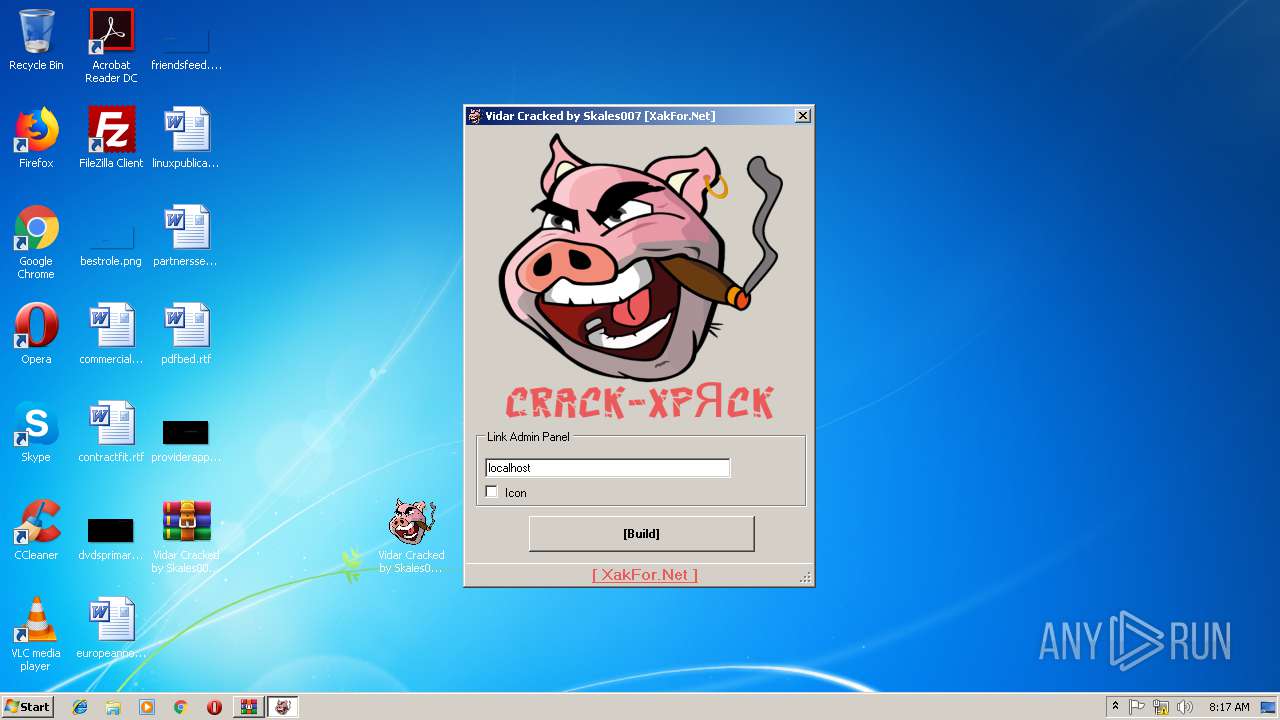
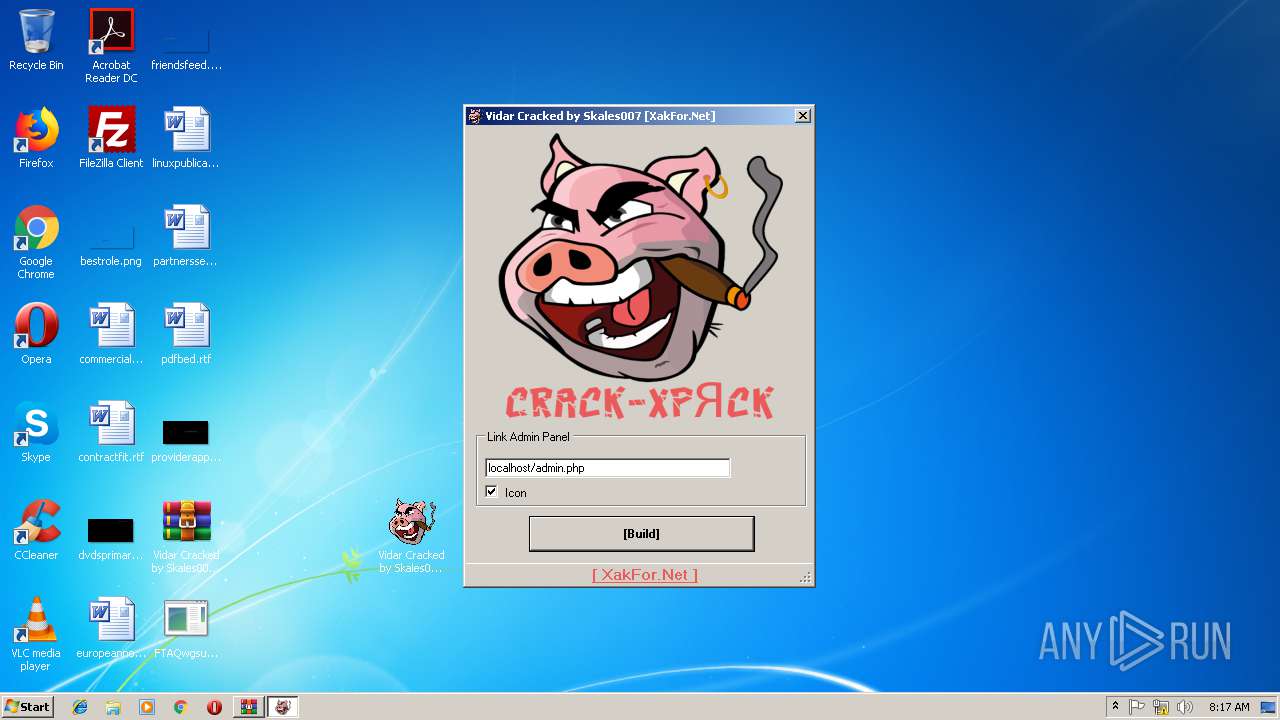
| 3388 | "C:\Users\admin\Desktop\Vidar Cracked by Skales007 [XakFor.Net].exe" | C:\Users\admin\Desktop\Vidar Cracked by Skales007 [XakFor.Net].exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Vidar Cracked by Skales007 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3484 | "C:\Users\admin\Desktop\FTAQwgsut.exe" | C:\Users\admin\Desktop\FTAQwgsut.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3712 | "C:\Windows\System32\cmd.exe" /c taskkill /im FTAQwgsut.exe /f & erase C:\Users\admin\Desktop\FTAQwgsut.exe & exit | C:\Windows\System32\cmd.exe | — | FTAQwgsut.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
935
Read events
867
Write events
65
Delete events
3
Modification events
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Vidar Cracked by Skales007 [XakFor.Net].rar | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3388) Vidar Cracked by Skales007 [XakFor.Net].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 2 |
Value: 56006900640061007200200043007200610063006B0065006400200062007900200053006B0061006C006500730030003000370020005B00580061006B0046006F0072002E004E00650074005D002E006500780065000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000000000000 | |||
Executable files
2
Suspicious files
1
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2960.18137\Vidar Cracked by Skales007 [XakFor.Net].exe | — | |
MD5:— | SHA256:— | |||
| 3388 | Vidar Cracked by Skales007 [XakFor.Net].exe | C:\Users\admin\Desktop\stub.bin | — | |
MD5:— | SHA256:— | |||
| 3388 | Vidar Cracked by Skales007 [XakFor.Net].exe | C:\Users\admin\Desktop\RCX2767.tmp | — | |
MD5:— | SHA256:— | |||
| 3484 | FTAQwgsut.exe | C:\ProgramData\U64W5IL6NPV57HPY07YB\files\information.txt | — | |
MD5:— | SHA256:— | |||
| 3388 | Vidar Cracked by Skales007 [XakFor.Net].exe | C:\Users\admin\Desktop\FTAQwgsut.exe | executable | |
MD5:— | SHA256:— | |||
| 3484 | FTAQwgsut.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\line[1].txt | text | |
MD5:— | SHA256:— | |||
| 3484 | FTAQwgsut.exe | C:\ProgramData\U64W5IL6NPV57HPY07YB\ld | sqlite | |
MD5:— | SHA256:— | |||
| 3484 | FTAQwgsut.exe | C:\ProgramData\U64W5IL6NPV57HPY07YB\SE_90059c37-1320-41a4-b58d-2b75a9850d2f5118933904.zip | compressed | |
MD5:— | SHA256:— | |||
| 3484 | FTAQwgsut.exe | C:\ProgramData\U64W5IL6NPV57HPY07YB\files\passwords.txt | text | |
MD5:0ED84EDA88A19802AF9C9D6670349475 | SHA256:1F367E81EF2666C51E1BA310CEC9015187150DF1BAAD543E252DA9717DD7FB0A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3484 | FTAQwgsut.exe | POST | 200 | 185.194.141.58:80 | http://ip-api.com/line/ | DE | text | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3484 | FTAQwgsut.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3484 | FTAQwgsut.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3484 | FTAQwgsut.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.PWS.Stealer.23869 (Arkei) |
1 ETPRO signatures available at the full report