| File name: | PECL.exe |
| Full analysis: | https://app.any.run/tasks/54793357-baa3-4dfc-a537-6daaa020907d |
| Verdict: | Malicious activity |
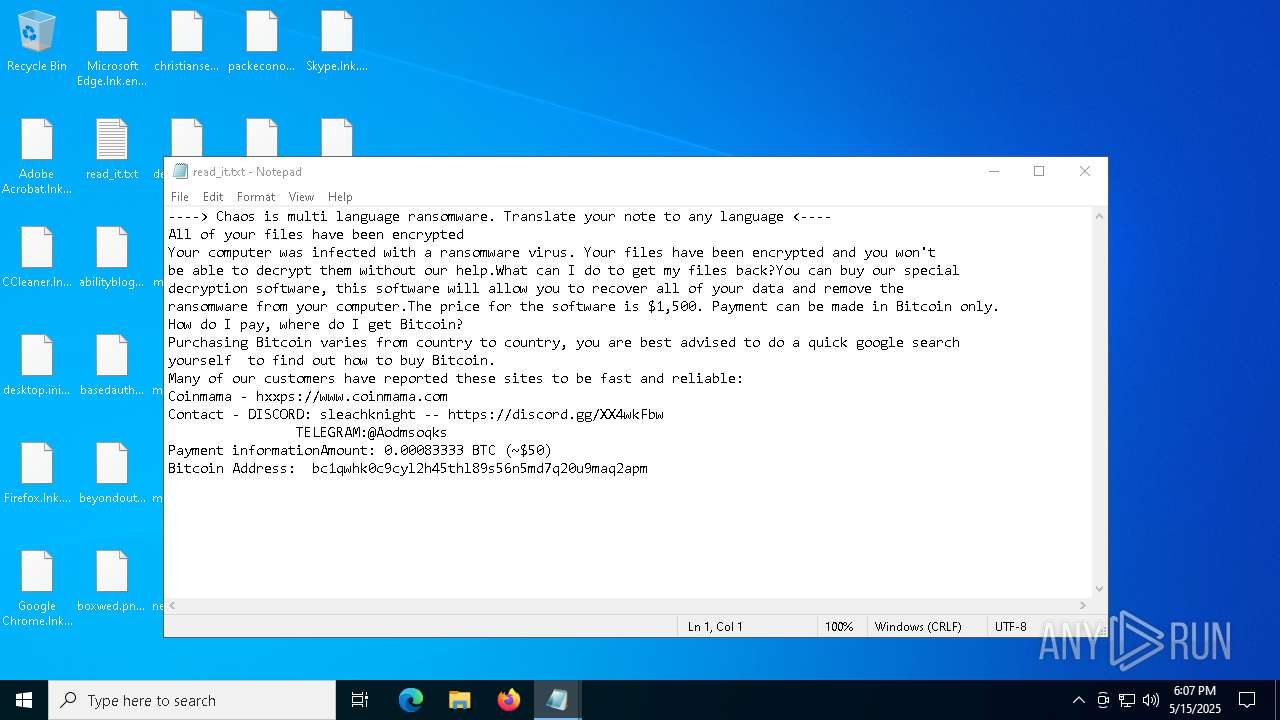
| Threats: | Chaos ransomware is a malware family known for its destructive capabilities and diverse variants. It first appeared in 2021 as a ransomware builder and later acted as a wiper. Unlike most ransomware strains that encrypt data to extort payment, early Chaos variants permanently corrupted files, while later versions adopted more conventional encryption techniques. |
| Analysis date: | May 15, 2025, 18:07:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | F4E779C431C946BFA31ED76CB545F628 |
| SHA1: | F918A3EBEDB99A3E380EBAA933AFD7EE8066C45E |
| SHA256: | 3A1F748B6B9E3F0F5E717A904C3E3FFCDCA9F973C286C522E46EF6696C0190D3 |
| SSDEEP: | 192:Qgh9JIWHWTatc3udGOqndxbnrBubOsT+TUnNXXudeoooopcPhHgSWes/91C1mSUu:Fh9DqdprBup+zvJWr91CvZlZHPrNYh |
MALICIOUS
Create files in the Startup directory
- INSTALL.exe (PID: 7780)
RANSOMWARE has been detected
- INSTALL.exe (PID: 7780)
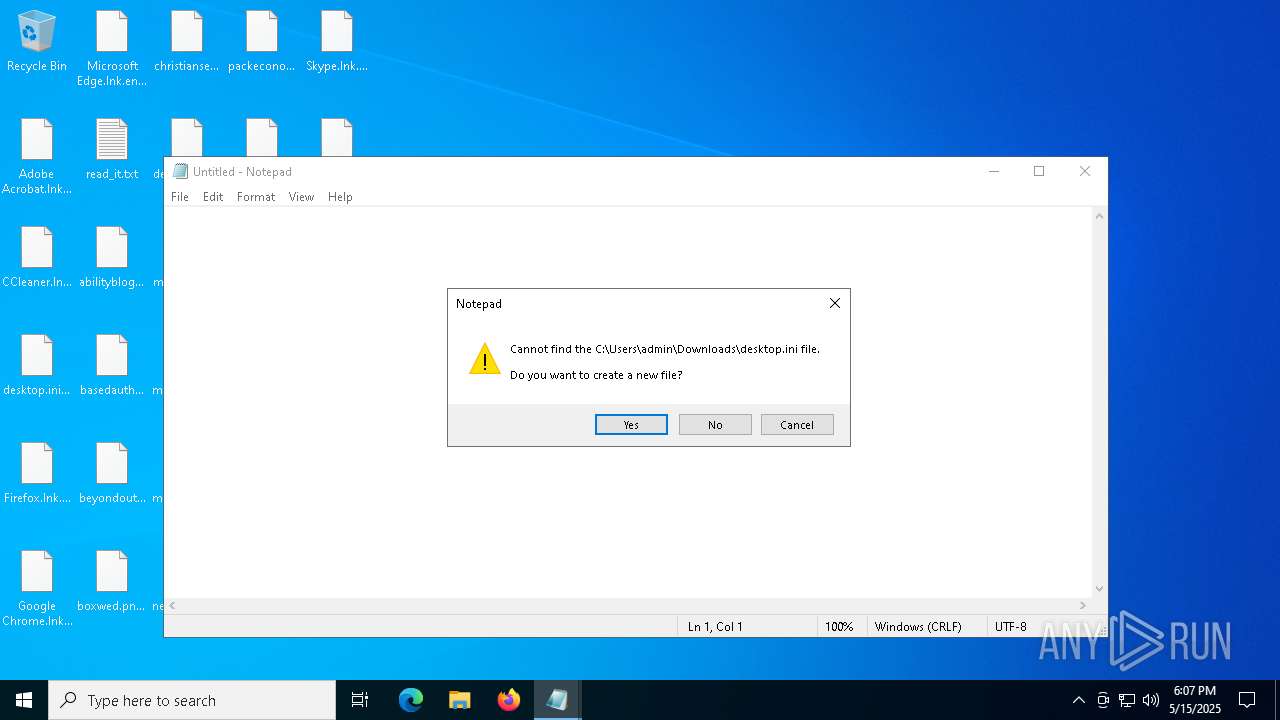
Renames files like ransomware
- INSTALL.exe (PID: 7780)
CHAOS has been detected (YARA)
- INSTALL.exe (PID: 7780)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 5324)
Deletes shadow copies
- cmd.exe (PID: 7720)
- cmd.exe (PID: 7268)
SUSPICIOUS
Starts itself from another location
- PECL.exe (PID: 7672)
Reads the date of Windows installation
- PECL.exe (PID: 7672)
- INSTALL.exe (PID: 7780)
Reads security settings of Internet Explorer
- PECL.exe (PID: 7672)
- INSTALL.exe (PID: 7780)
Executable content was dropped or overwritten
- PECL.exe (PID: 7672)
Found regular expressions for crypto-addresses (YARA)
- INSTALL.exe (PID: 7780)
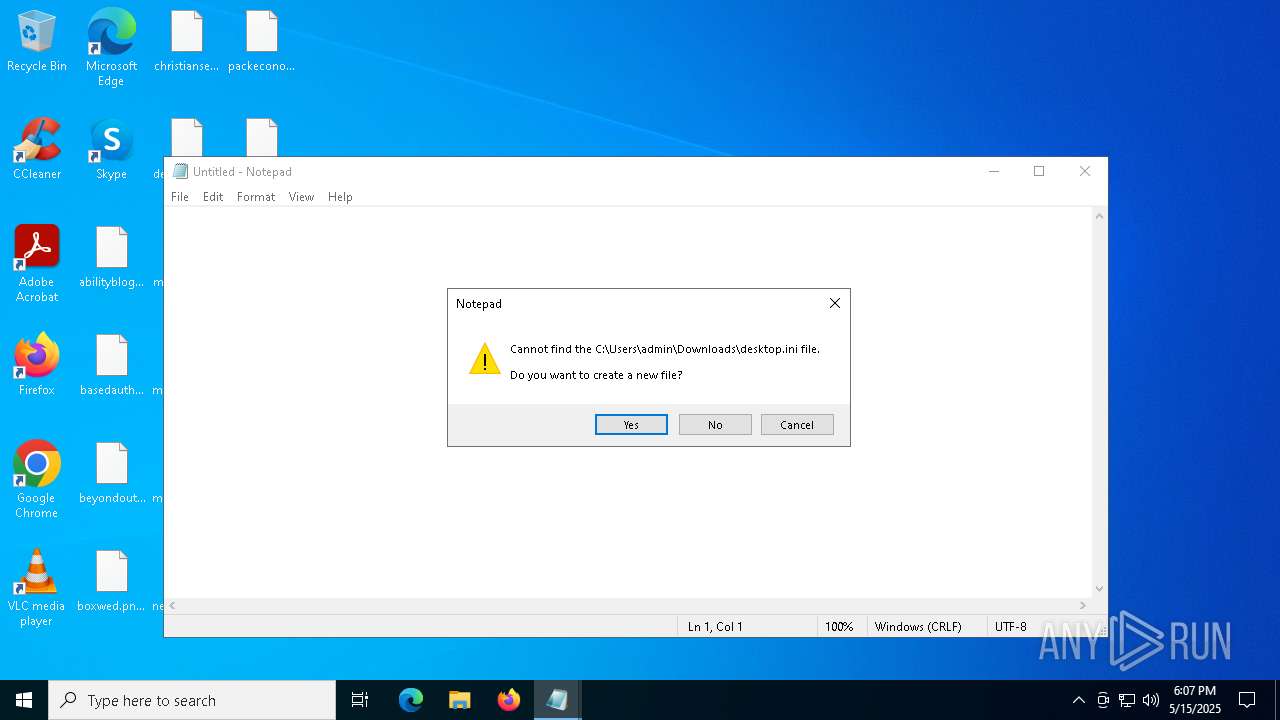
Write to the desktop.ini file (may be used to cloak folders)
- INSTALL.exe (PID: 7780)
Executes as Windows Service
- VSSVC.exe (PID: 7340)
- vds.exe (PID: 6592)
- wbengine.exe (PID: 2420)
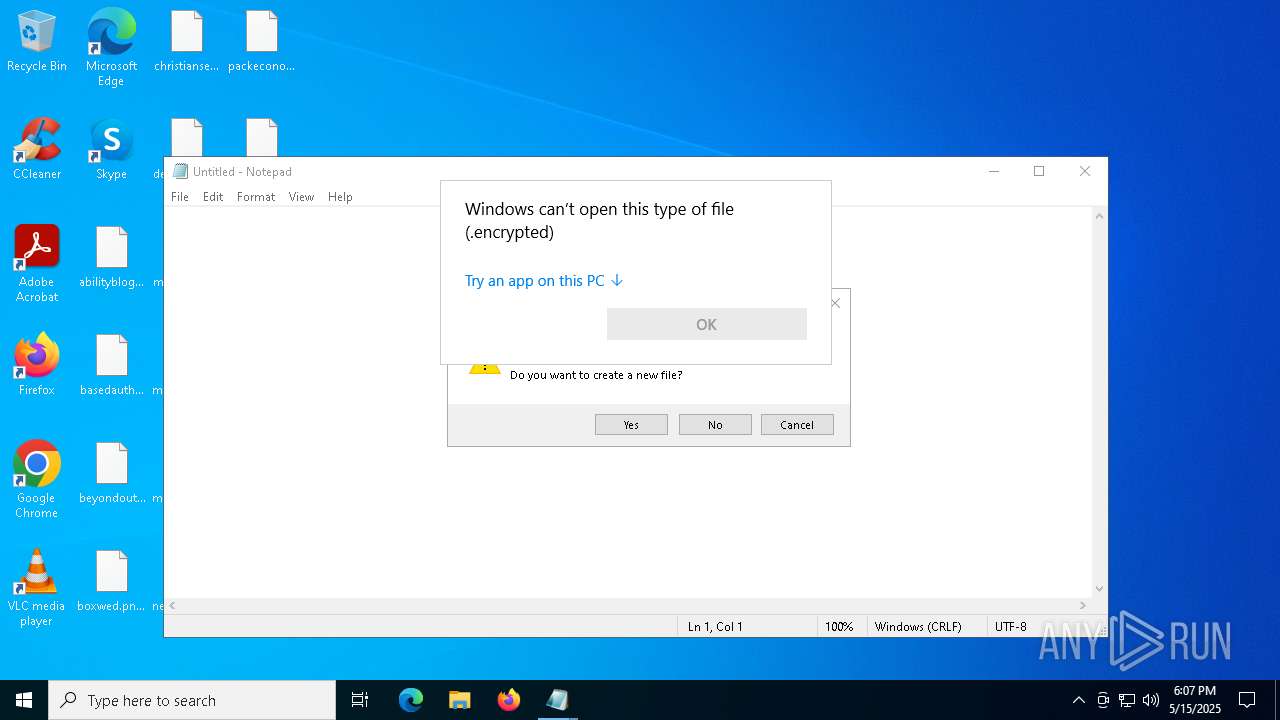
Start notepad (likely ransomware note)
- INSTALL.exe (PID: 7780)
Starts CMD.EXE for commands execution
- INSTALL.exe (PID: 7780)
INFO
Checks supported languages
- INSTALL.exe (PID: 7780)
- PECL.exe (PID: 7672)
Process checks computer location settings
- PECL.exe (PID: 7672)
- INSTALL.exe (PID: 7780)
Creates files or folders in the user directory
- PECL.exe (PID: 7672)
- INSTALL.exe (PID: 7780)
Reads the computer name
- PECL.exe (PID: 7672)
- INSTALL.exe (PID: 7780)
Reads the machine GUID from the registry
- INSTALL.exe (PID: 7780)
Auto-launch of the file from Startup directory
- INSTALL.exe (PID: 7780)
Manual execution by a user
- notepad.exe (PID: 7932)
- OpenWith.exe (PID: 8064)
- notepad.exe (PID: 8176)
- OpenWith.exe (PID: 7208)
- OpenWith.exe (PID: 2140)
- OpenWith.exe (PID: 1672)
- rundll32.exe (PID: 3020)
- OpenWith.exe (PID: 4980)
- rundll32.exe (PID: 5376)
- rundll32.exe (PID: 8008)
- rundll32.exe (PID: 5968)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 1672)
- OpenWith.exe (PID: 7208)
- OpenWith.exe (PID: 2140)
- OpenWith.exe (PID: 4980)
- OpenWith.exe (PID: 8064)
- INSTALL.exe (PID: 7780)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7932)
- WMIC.exe (PID: 7312)
- notepad.exe (PID: 1300)
Reads the software policy settings
- slui.exe (PID: 1272)
Checks proxy server information
- slui.exe (PID: 1272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:05:15 18:02:55+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 22016 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x73fe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | PECL.exe |
| LegalCopyright: | |
| OriginalFileName: | PECL.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
155
Monitored processes
30
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1272 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Roaming\read_it.txt | C:\Windows\System32\notepad.exe | — | INSTALL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1672 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Downloads\robertto.jpg.encrypted | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Downloads\desktop.ini.encrypted | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | "C:\WINDOWS\system32\wbengine.exe" | C:\Windows\System32\wbengine.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Block Level Backup Engine Service EXE Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3020 | "C:\WINDOWS\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\Downloads\propertiesjack.jpg | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4920 | bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4980 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Downloads\checkenough.png.encrypted | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5324 | "C:\Windows\System32\cmd.exe" /C bcdedit /set {default} bootstatuspolicy ignoreallfailures & bcdedit /set {default} recoveryenabled no | C:\Windows\System32\cmd.exe | — | INSTALL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5352 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 590
Read events
11 555
Write events
17
Delete events
18
Modification events
| (PID) Process: | (4920) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4920) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (4920) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4920) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Microsoft\Boot\bootmgfw.efi | |||
| (PID) Process: | (4920) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4920) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (4920) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4920) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Boot\Loader.efi | |||
| (PID) Process: | (4920) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{a5a30fa2-3d06-4e9f-b5f4-a01df9d1fcba}\Description |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4920) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{a5a30fa2-3d06-4e9f-b5f4-a01df9d1fcba}\Elements\24000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
1
Suspicious files
1
Text files
630
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7672 | PECL.exe | C:\Users\admin\AppData\Roaming\INSTALL.exe | executable | |
MD5:F4E779C431C946BFA31ED76CB545F628 | SHA256:3A1F748B6B9E3F0F5E717A904C3E3FFCDCA9F973C286C522E46EF6696C0190D3 | |||
| 7780 | INSTALL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\INSTALL.url | binary | |
MD5:090AC9B01FEB6A75AE2D936447248934 | SHA256:115822A1DA1F6E028B21888F6490ECF6126589E7E45DEB30D7D07519EC02201C | |||
| 7780 | INSTALL.exe | C:\Users\admin\Desktop\abilityblogs.rtf.encrypted | text | |
MD5:2A0B4761DFF851DA85F1BD0D868F3330 | SHA256:862B12FF4C91C35E22E6BA9FDB149B82966BAFC69D05A7B13637CF488CC80DA6 | |||
| 7780 | INSTALL.exe | C:\Users\admin\Desktop\christiansent.jpg.encrypted | text | |
MD5:62E50BD06BD82E1754264F2C43126816 | SHA256:647B0F3A7199EA7ABB95CC2EE810413EC32CF5E99A654FC196956A1696A1E2A6 | |||
| 7780 | INSTALL.exe | C:\Users\admin\Desktop\basedauthor.png.encrypted | text | |
MD5:9944A68BB0AC155DDC21AD1D1EE31B41 | SHA256:878223A43BCA6E64CCF51A428980393F0F9E63676FEFF0CE5FF2D87792BB56B8 | |||
| 7780 | INSTALL.exe | C:\Users\admin\Desktop\beyondoutside.rtf.encrypted | text | |
MD5:743069EA5973C94754184215B9E33AE6 | SHA256:1D9A87125B61AB80AA6152065A9A1B58013B26AFE296C81A946B361E3FD840C1 | |||
| 7780 | INSTALL.exe | C:\Users\admin\Desktop\desktop.ini | text | |
MD5:17F5C867EBF35EC81AC874227784E665 | SHA256:B9BAA2F4510A293BC98922E9AB2076507A56F66920BF6F566B493CE94532AC62 | |||
| 7780 | INSTALL.exe | C:\Users\admin\Desktop\basedauthor.png | text | |
MD5:9944A68BB0AC155DDC21AD1D1EE31B41 | SHA256:878223A43BCA6E64CCF51A428980393F0F9E63676FEFF0CE5FF2D87792BB56B8 | |||
| 7780 | INSTALL.exe | C:\Users\admin\Desktop\mediadeep.rtf | text | |
MD5:DFDAD89DD3237BDAAC17D8550C549299 | SHA256:4489DCE331316B37D764E98FDBC7F80F40A9BCF76F94FFCD75CA8FF748CC9051 | |||
| 7780 | INSTALL.exe | C:\Users\admin\Desktop\read_it.txt | text | |
MD5:517FBBA3D1863506E70C794F2971565C | SHA256:CE48BA8672A919715567AECF105503E9FA81D9F4FC4F9D322069D430F7F24CF2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
43
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3100 | SIHClient.exe | GET | 200 | 88.221.110.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3100 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
3100 | SIHClient.exe | GET | 200 | 88.221.110.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
3100 | SIHClient.exe | GET | 200 | 88.221.110.114:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
3100 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3100 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
3100 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
3100 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
3100 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3100 | SIHClient.exe | 88.221.110.114:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3100 | SIHClient.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3100 | SIHClient.exe | 20.242.39.171:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
8040 | backgroundTaskHost.exe | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |