| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/67906a87-fe21-484d-ac06-bde7640a1675 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | December 20, 2024, 10:55:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 4FAAF8B146989402B01872F5F1FA5A88 |
| SHA1: | DC08532EB134AD2AEA2994705DDAEFF156C7DD6F |
| SHA256: | 3A10EC9DB282D82494DAE795ACF0DB44F8CF2E52BA69C06DBE87CAF759A9642F |
| SSDEEP: | 49152:ED3htlXhg0po3+8IzCmuUrHnRkWi/HvFz/dgs9H2iN4NuaLRfnRgRcr7dCz8+HVT:E5Xh5KuVxuUrxI1z/zWi+YapBMztVm50 |
MALICIOUS
Actions looks like stealing of personal data
- Oops.com (PID: 6720)
Steals credentials from Web Browsers
- Oops.com (PID: 6720)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
AutoIt loader has been detected (YARA)
- Oops.com (PID: 6720)
LUMMA mutex has been found
- Oops.com (PID: 6720)
SUSPICIOUS
Reads security settings of Internet Explorer
- setup.exe (PID: 6260)
Executing commands from ".cmd" file
- setup.exe (PID: 6260)
Get information on the list of running processes
- cmd.exe (PID: 6380)
Starts CMD.EXE for commands execution
- setup.exe (PID: 6260)
- cmd.exe (PID: 6380)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6380)
Application launched itself
- cmd.exe (PID: 6380)
The executable file from the user directory is run by the CMD process
- Oops.com (PID: 6720)
Starts application with an unusual extension
- cmd.exe (PID: 6380)
Starts the AutoIt3 executable file
- cmd.exe (PID: 6380)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2192)
INFO
Reads the computer name
- setup.exe (PID: 6260)
- Oops.com (PID: 6720)
Checks supported languages
- setup.exe (PID: 6260)
- Oops.com (PID: 6720)
Process checks computer location settings
- setup.exe (PID: 6260)
Creates a new folder
- cmd.exe (PID: 6636)
Reads mouse settings
- Oops.com (PID: 6720)
Reads the software policy settings
- Oops.com (PID: 6720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 19:20:04+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 29696 |
| InitializedDataSize: | 1132544 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x38af |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
146
Monitored processes
15
Malicious processes
4
Suspicious processes
0
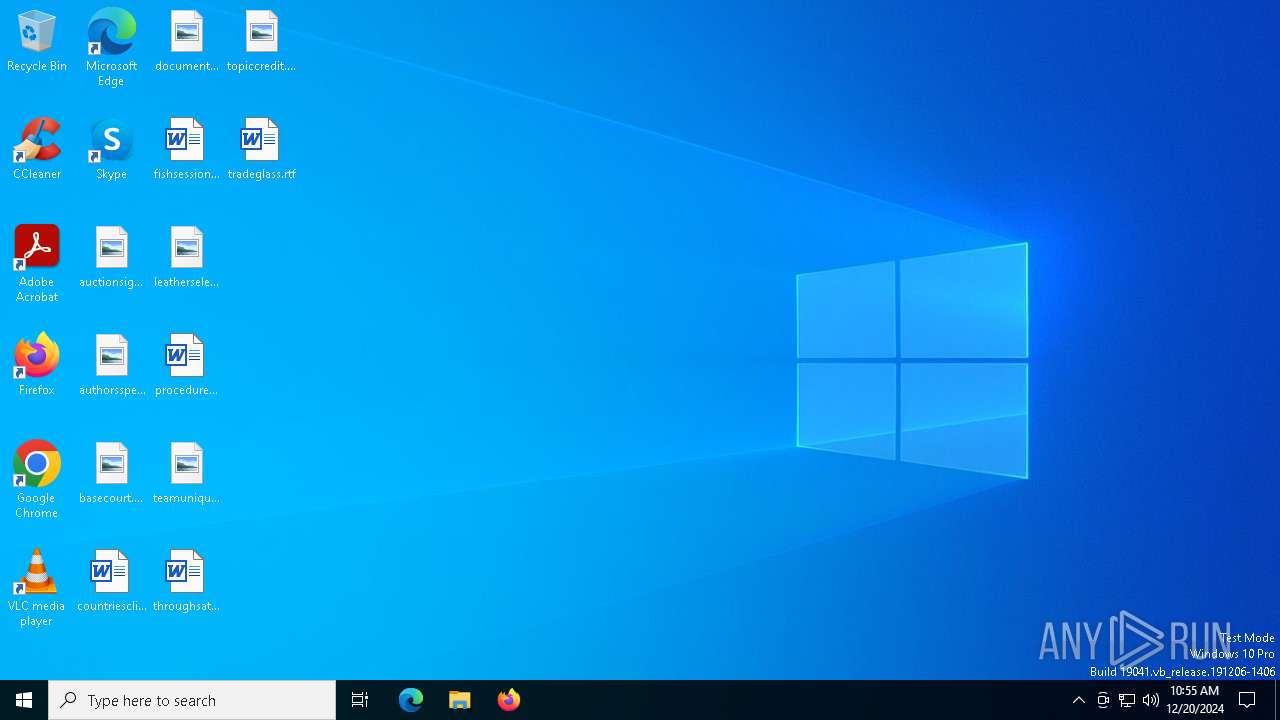
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6260 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6380 | "C:\Windows\System32\cmd.exe" /c copy Verse Verse.cmd & Verse.cmd | C:\Windows\SysWOW64\cmd.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6396 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6452 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 6460 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6480 | findstr /I "opssvc wrsa" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6576 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6584 | findstr "AvastUI AVGUI bdservicehost nsWscSvc ekrn SophosHealth" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6636 | cmd /c md 762009 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 194
Read events
1 194
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
19
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6260 | setup.exe | C:\Users\admin\AppData\Local\Temp\Carpet | binary | |
MD5:D6FDAC1A41F26CB2EACE7C04DD05695C | SHA256:890664F5520BF8376F7A6D7D8FEC0404AB6ABE0D80C7E3AB6413347E0016B49F | |||
| 6260 | setup.exe | C:\Users\admin\AppData\Local\Temp\Jury | binary | |
MD5:453792E93105051E32DCE2567A60DE07 | SHA256:90F397F2D62D90813AF0580D2B91F4786FF3B433831F5CEAF590A9CBC6AFA6DE | |||
| 6260 | setup.exe | C:\Users\admin\AppData\Local\Temp\Verse | text | |
MD5:BB50508188E4BFF4D6D771AC2F006CDF | SHA256:FF3C0C15F1EB1B7CE8610E062C849DC822ED0884FD56130BFD9070520E5F6568 | |||
| 6260 | setup.exe | C:\Users\admin\AppData\Local\Temp\Mhz | binary | |
MD5:D89012682B79133C829F5F262DB69C3B | SHA256:0E0371850D046D0555276D56F1ADBB8070E8731E7841EF41A401F72E8FAA0B75 | |||
| 6260 | setup.exe | C:\Users\admin\AppData\Local\Temp\Tax | binary | |
MD5:DBB2F626FAA591055BB550415E53F07D | SHA256:6D49DF4DB6E3188909456837737B2BDE7F69B1621CE8FCEA2336363313C2B484 | |||
| 6260 | setup.exe | C:\Users\admin\AppData\Local\Temp\Wellington | binary | |
MD5:B77C663AD6F288716EA743C0821AF230 | SHA256:FFAC95DB57A02329095E74CFB04FB0E2499617B67ECE41C8A76E08F9B86264CB | |||
| 6260 | setup.exe | C:\Users\admin\AppData\Local\Temp\Treasurer | binary | |
MD5:BDE0D0C513DA1DBD0E72EA64C16E205D | SHA256:37024DBFED21DD53908033255D4308B9882F42F6EC6F210C6A0B9510B1BF4676 | |||
| 6260 | setup.exe | C:\Users\admin\AppData\Local\Temp\Australian | binary | |
MD5:EC06B5288591E59A44F7897AD29C5F72 | SHA256:4DEE77D56A970AB86A2EB23CE1C03FC84B5B7BAEA06C7DDDC0BBABDA78EBA4B4 | |||
| 6260 | setup.exe | C:\Users\admin\AppData\Local\Temp\Recorders | binary | |
MD5:ADA95C38A1BFC3D6E7E71A7DD905E49E | SHA256:108DE0DF5BEC8E1FAE15268D610EAD26CB8D1B6E85B590A020DD6F625AE8036E | |||
| 6260 | setup.exe | C:\Users\admin\AppData\Local\Temp\Hazard | binary | |
MD5:AD8A02213E6C66B8C42AFC34307210BB | SHA256:D1C6FD90CF25AA97E6353BF66B89FCAC988464D8E6B75A39AB06F112FB3DB8E8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
54
DNS requests
24
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.125.143:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3172 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3172 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1356 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
5564 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.23.209.185:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.125.143:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
pPWHIINwGxxwQbgviFATVpP.pPWHIINwGxxwQbgviFATVpP |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Domain Observed Used for C2 Detected | STEALER [ANY.RUN] Suspected Lumma domain by CrossDomain (klipcatepiu0 .shop) |