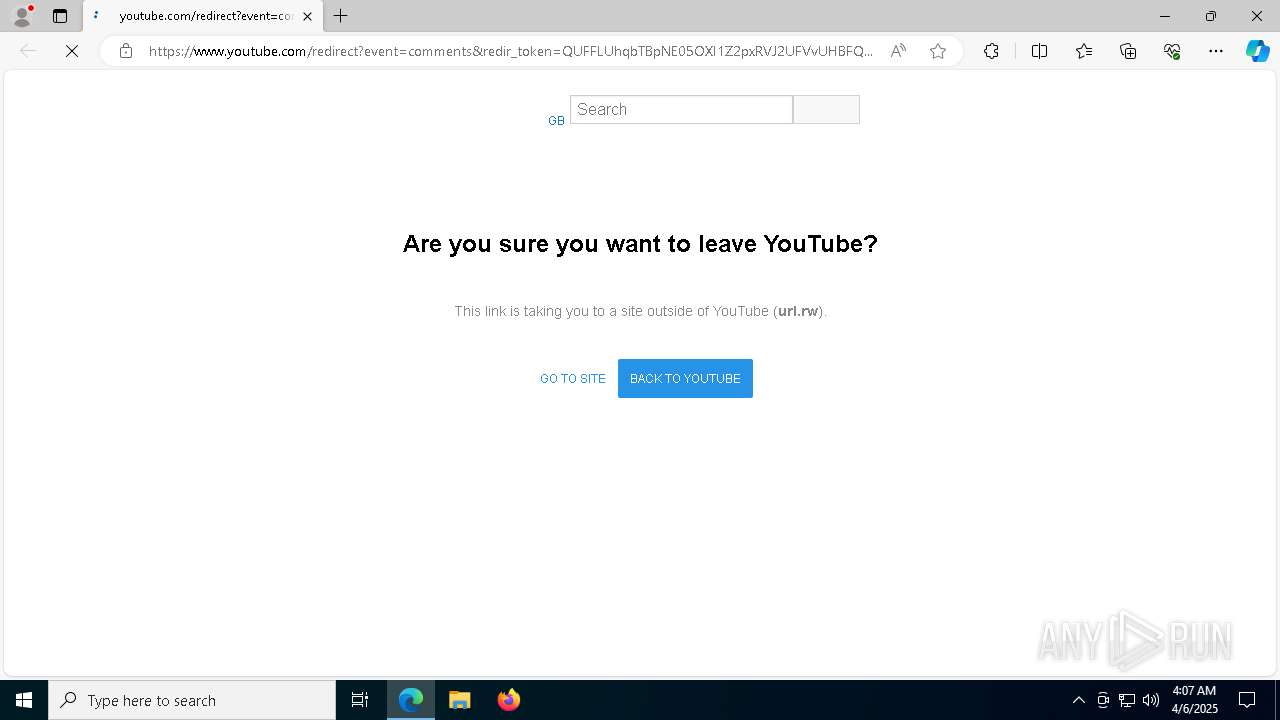
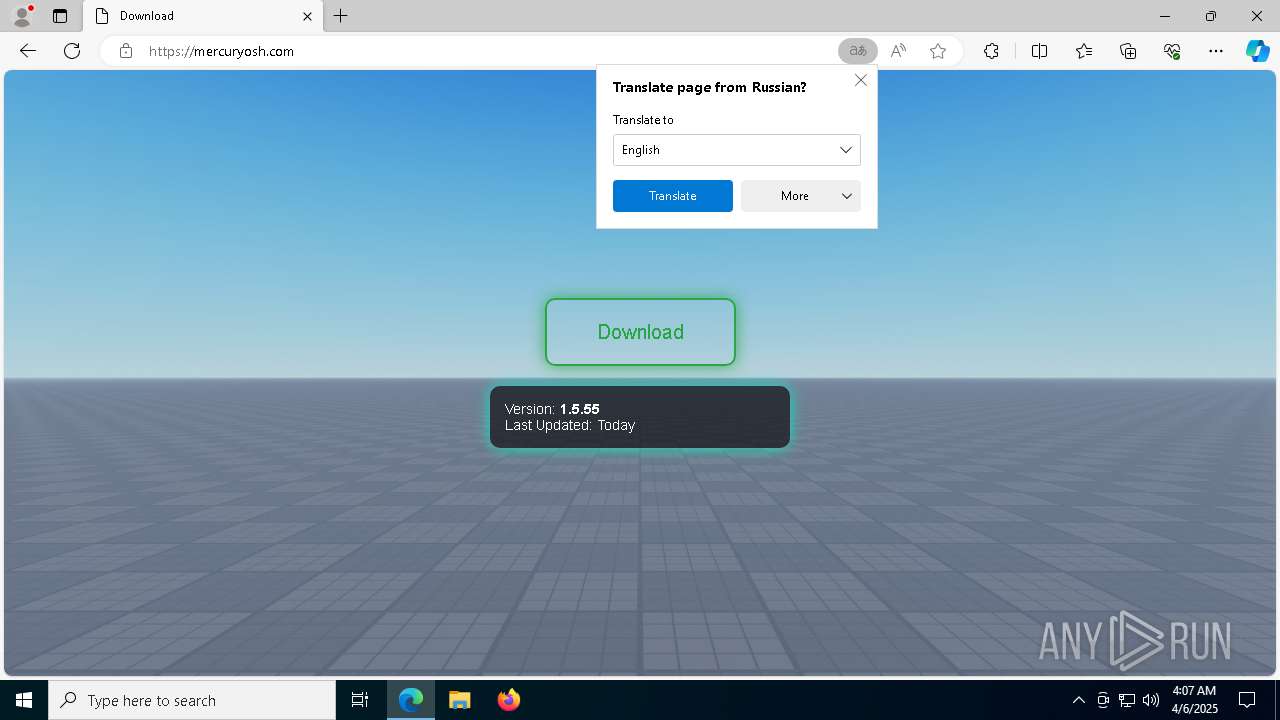
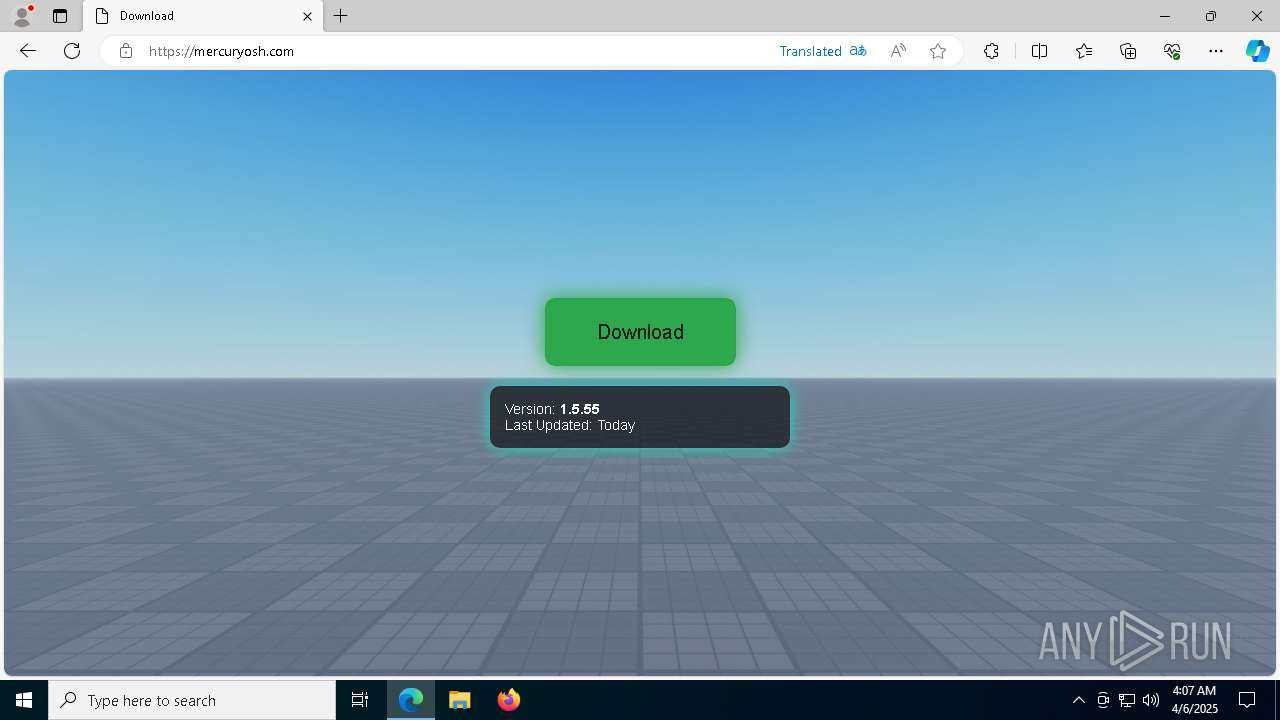
| URL: | https://www.youtube.com/redirect?event=comments&redir_token=QUFFLUhqbTBpNE05OXI1Z2pxRVJ2UFVvUHBFQ3ZwUnh5d3xBQ3Jtc0tuTk1aQVdjaXdoYWFXdGpEOWJ2NmVhcU9ONDVmdmlWd2VJcWI1bGNnZWt2bzhIbnJVNHEzRHZUM1Y4Q3NlcHA2U1B6VVpJTnZKc2pSSlNpejJtMzMyWnM4Zk5Ta0RHWUIxWkplNEtzZ1NRR0NFeWFPWQ&q=https%3A%2F%2Furl.rw%2Fryos%2F |
| Full analysis: | https://app.any.run/tasks/1055b663-c6c8-4d09-aed8-af5b00ef9935 |
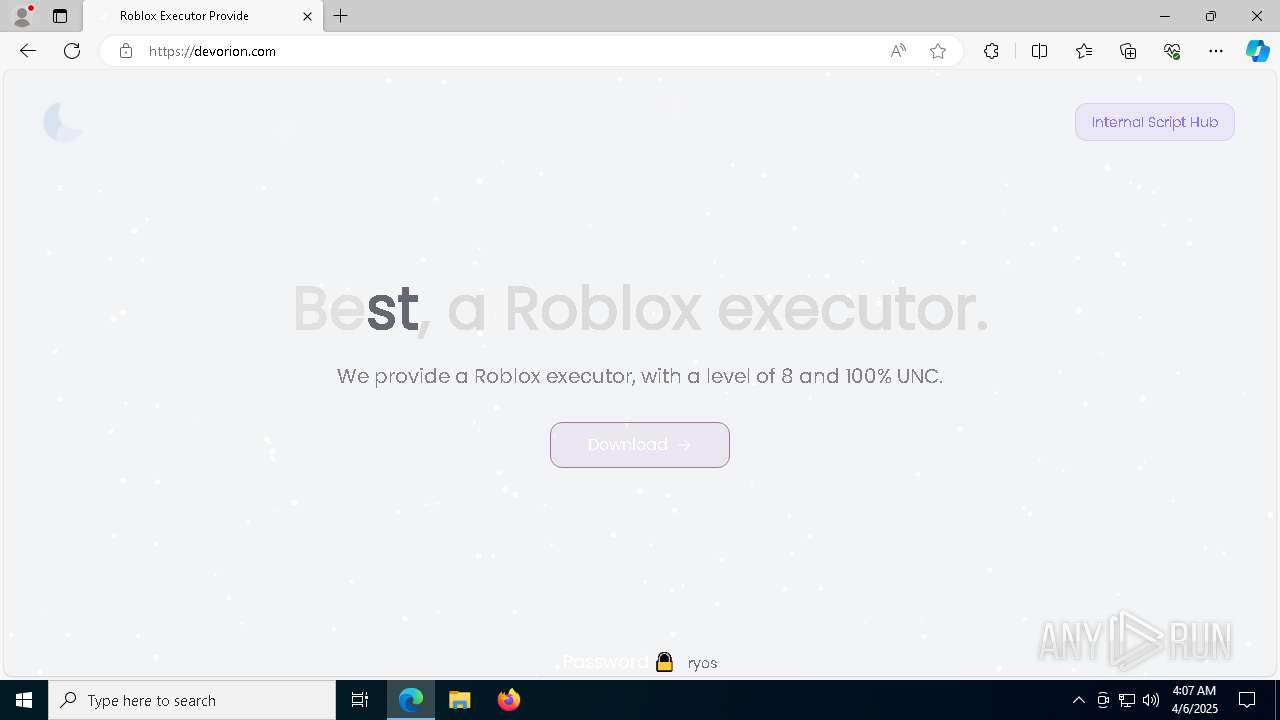
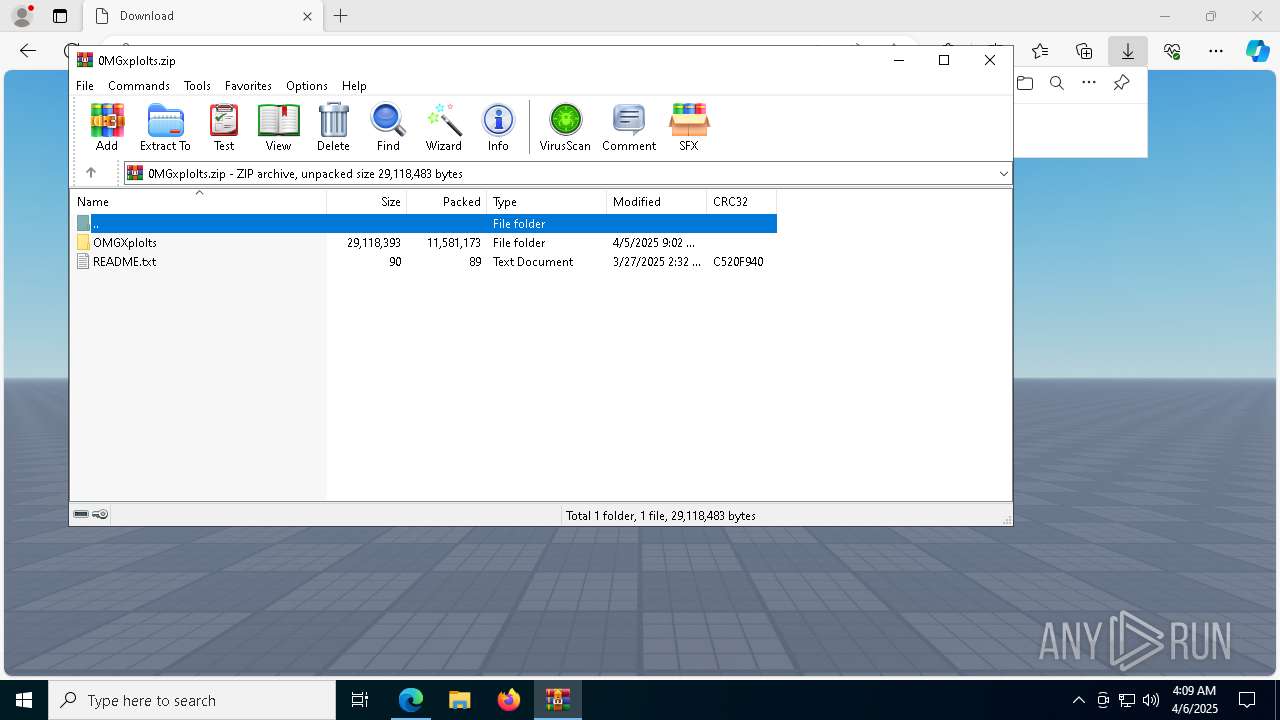
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | April 06, 2025, 04:07:22 |
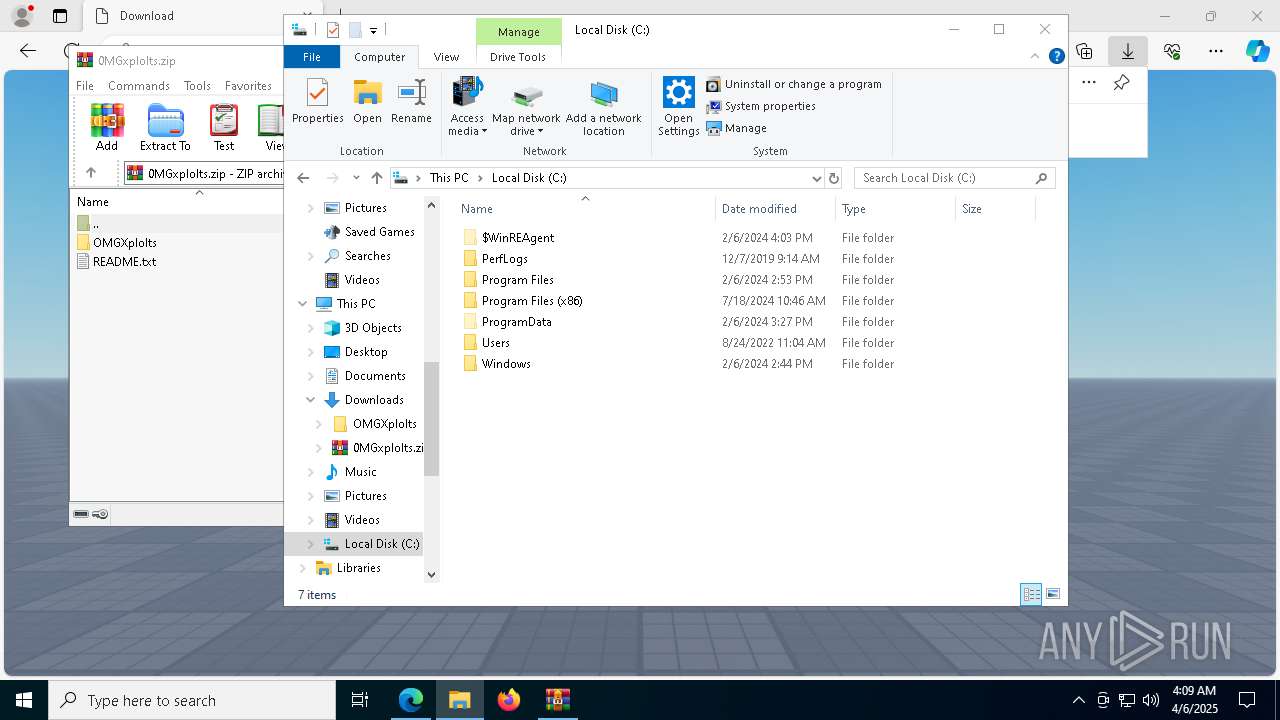
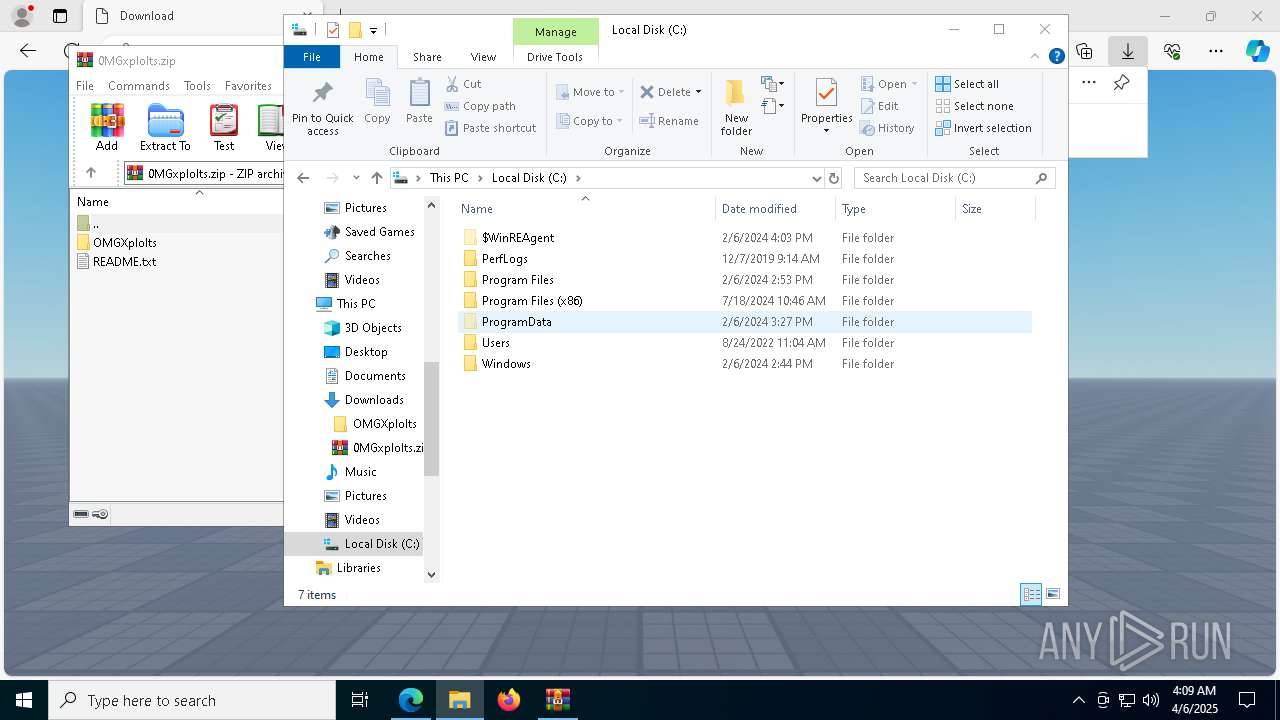
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9229D887FD8F5BA33142F68A67DA8C56 |
| SHA1: | 0D7DE68AF75B49F55B0512593B67C159939A056E |
| SHA256: | 39FAF6B271464E3A6A0BEBFF5E860B993A60E651668846A3DE4294F92D40F4DC |
| SSDEEP: | 6:2OLUxGKmquxZw67U94wJvJCQyrLW2spQo9HnJ5lN3zQLrn:2jGRPPV7VwJv+g99p53UHn |
MALICIOUS
Actions looks like stealing of personal data
- chrome.exe (PID: 4740)
- msedge.exe (PID: 5416)
RHADAMANTHYS mutex has been found
- RegSvcs.exe (PID: 6940)
- svchost.exe (PID: 7604)
RHADAMANTHYS has been detected (YARA)
- svchost.exe (PID: 5972)
Steals credentials from Web Browsers
- msedge.exe (PID: 5416)
RHADAMANTHYS has been detected (SURICATA)
- svchost.exe (PID: 5972)
SUSPICIOUS
Application launched itself
- chrome.exe (PID: 4740)
- msedge.exe (PID: 5416)
The process checks if it is being run in the virtual environment
- svchost.exe (PID: 7604)
Executes application which crashes
- RegSvcs.exe (PID: 6940)
Connects to unusual port
- svchost.exe (PID: 7604)
- svchost.exe (PID: 5972)
- dllhost.exe (PID: 8652)
Multiple wallet extension IDs have been found
- svchost.exe (PID: 5972)
Reads security settings of Internet Explorer
- msedge.exe (PID: 5416)
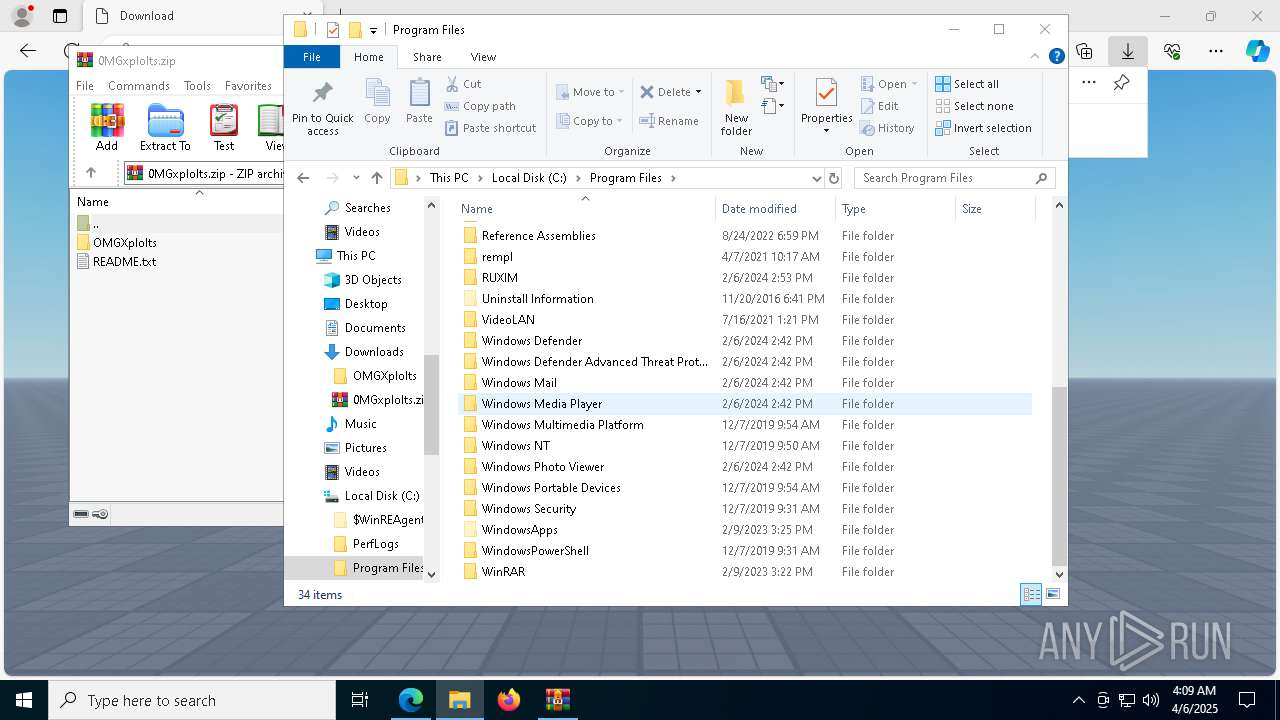
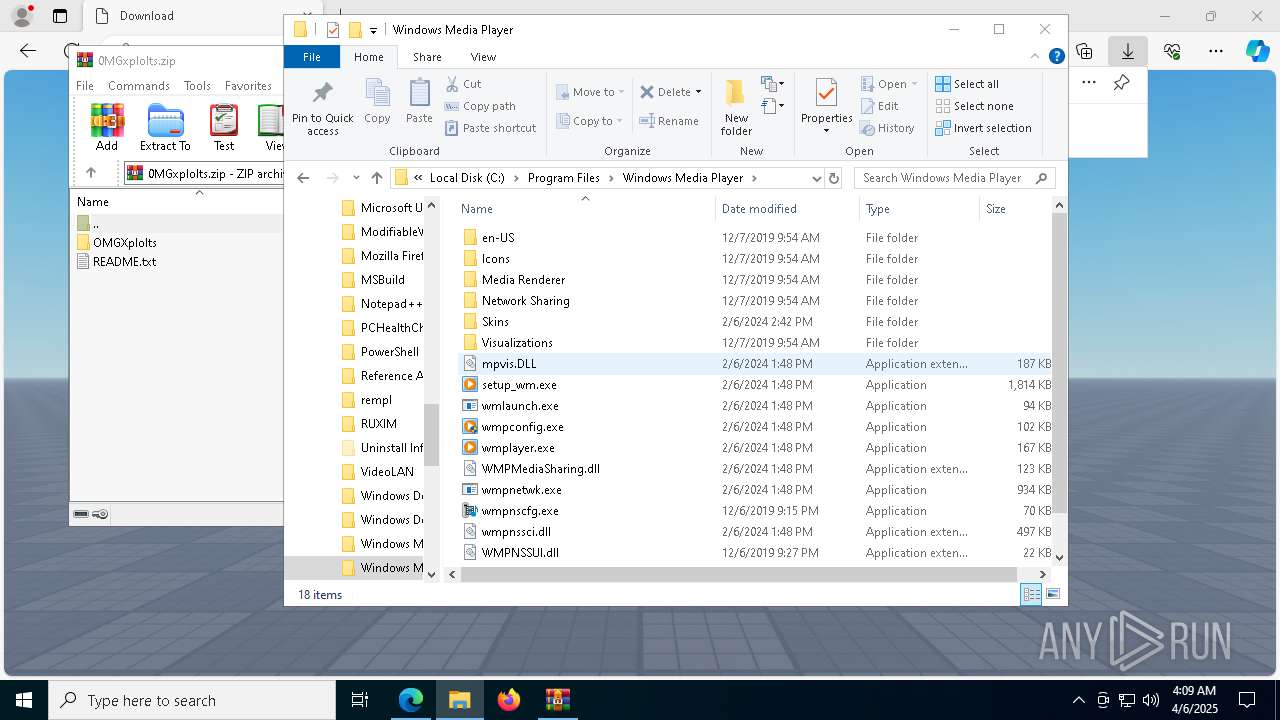
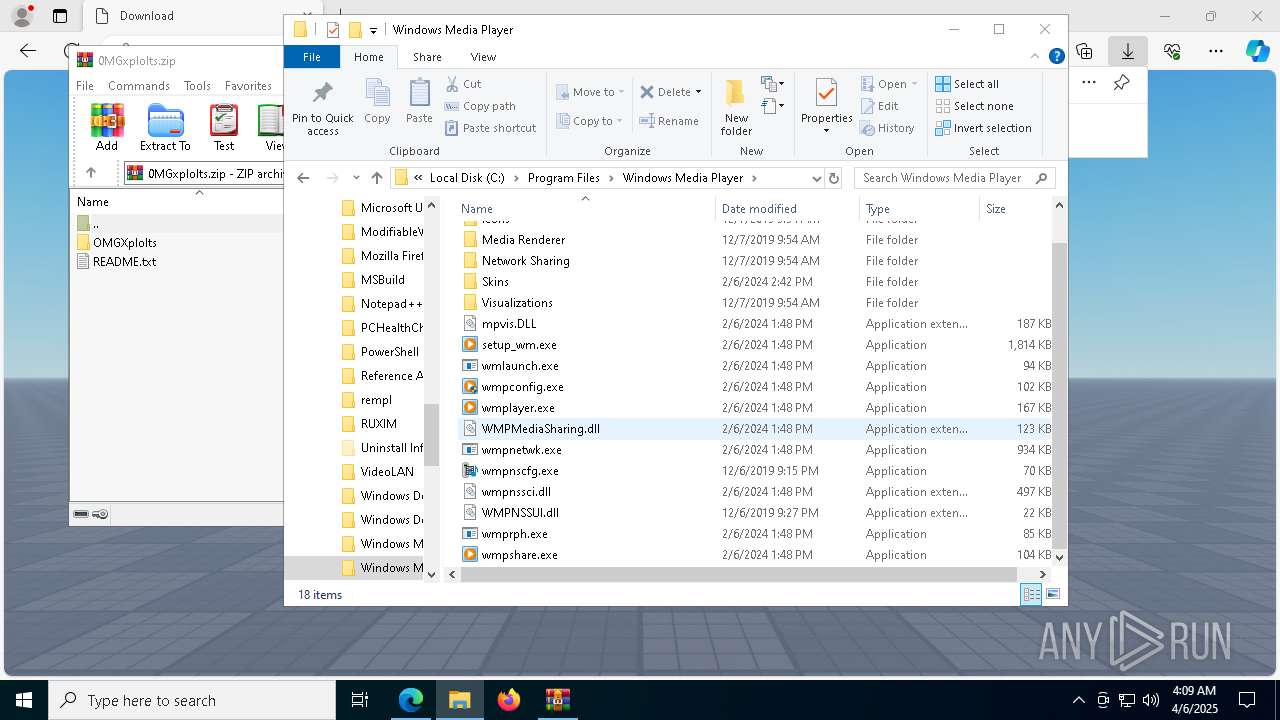
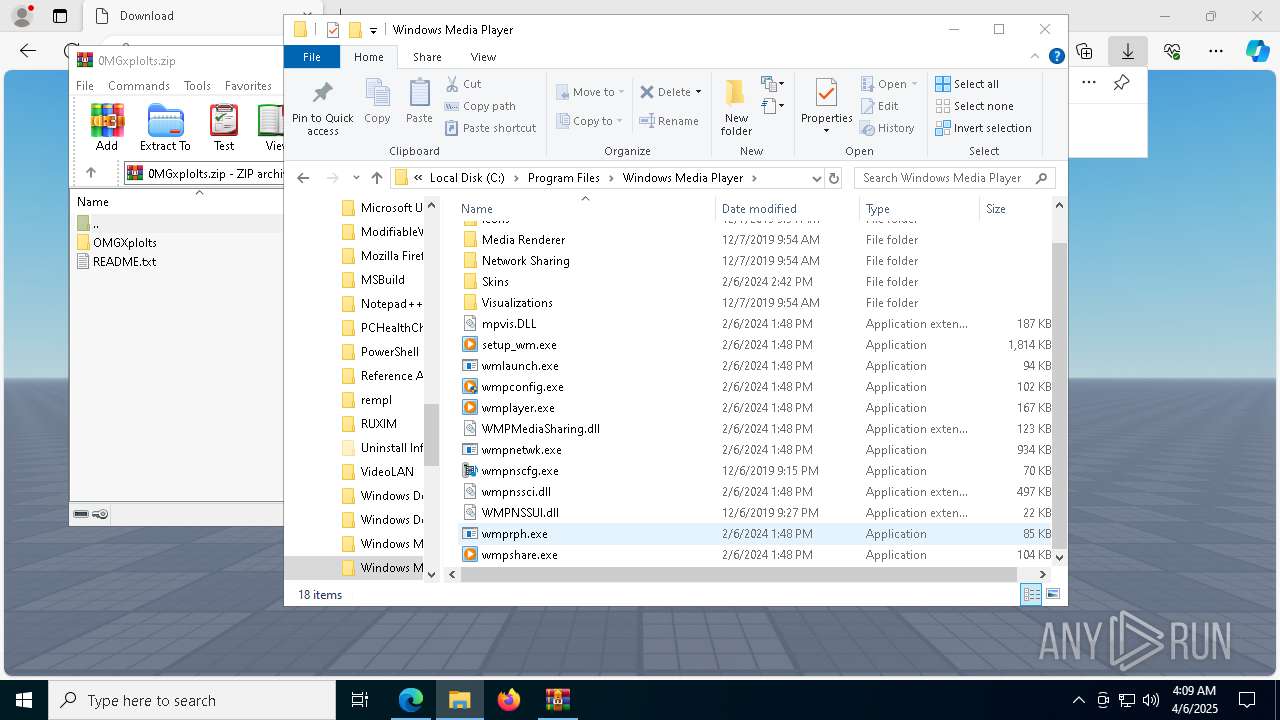
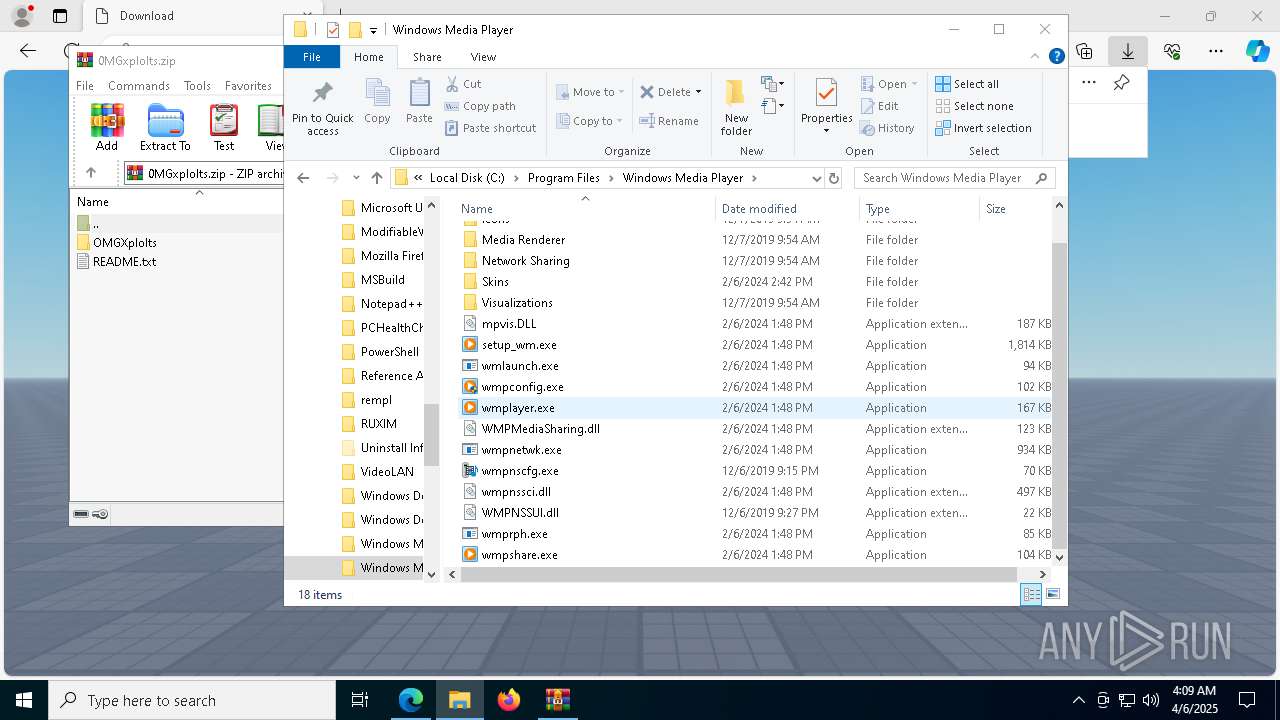
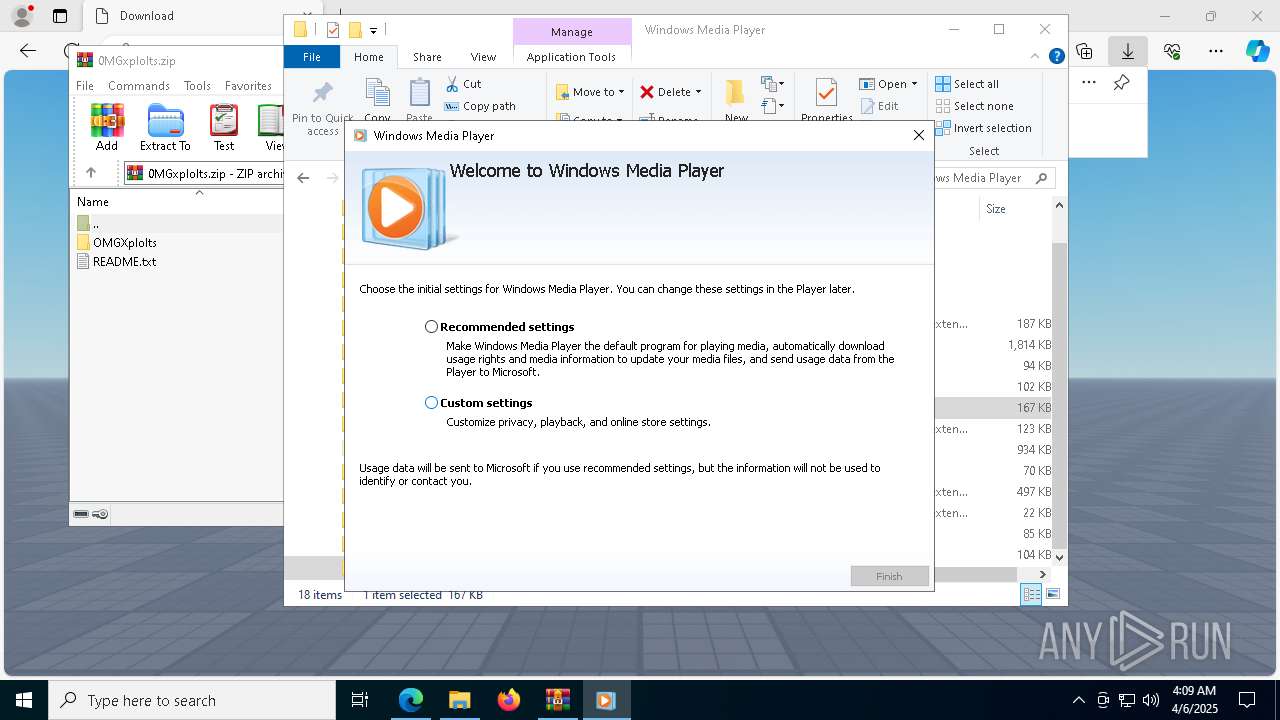
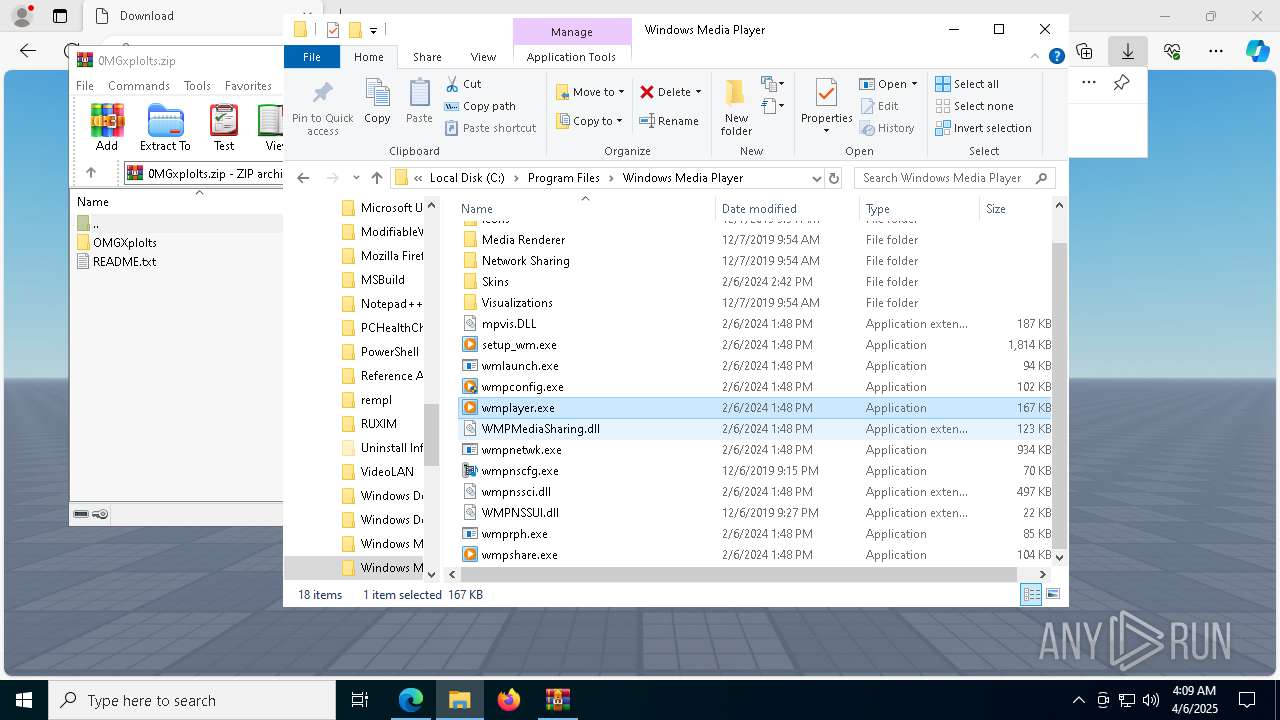
- wmplayer.exe (PID: 4724)
- setup_wm.exe (PID: 1912)
Reads Mozilla Firefox installation path
- msedge.exe (PID: 5416)
Loads DLL from Mozilla Firefox
- svchost.exe (PID: 5972)
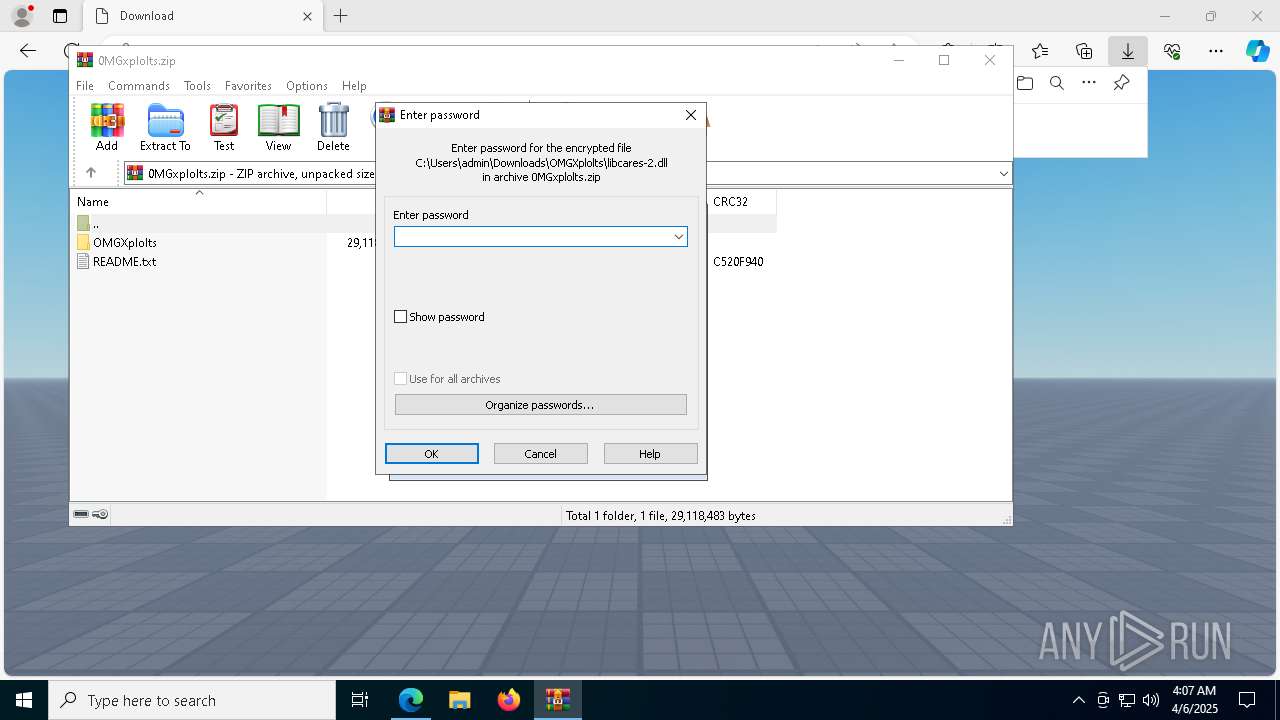
Executable content was dropped or overwritten
- wmplayer.exe (PID: 8600)
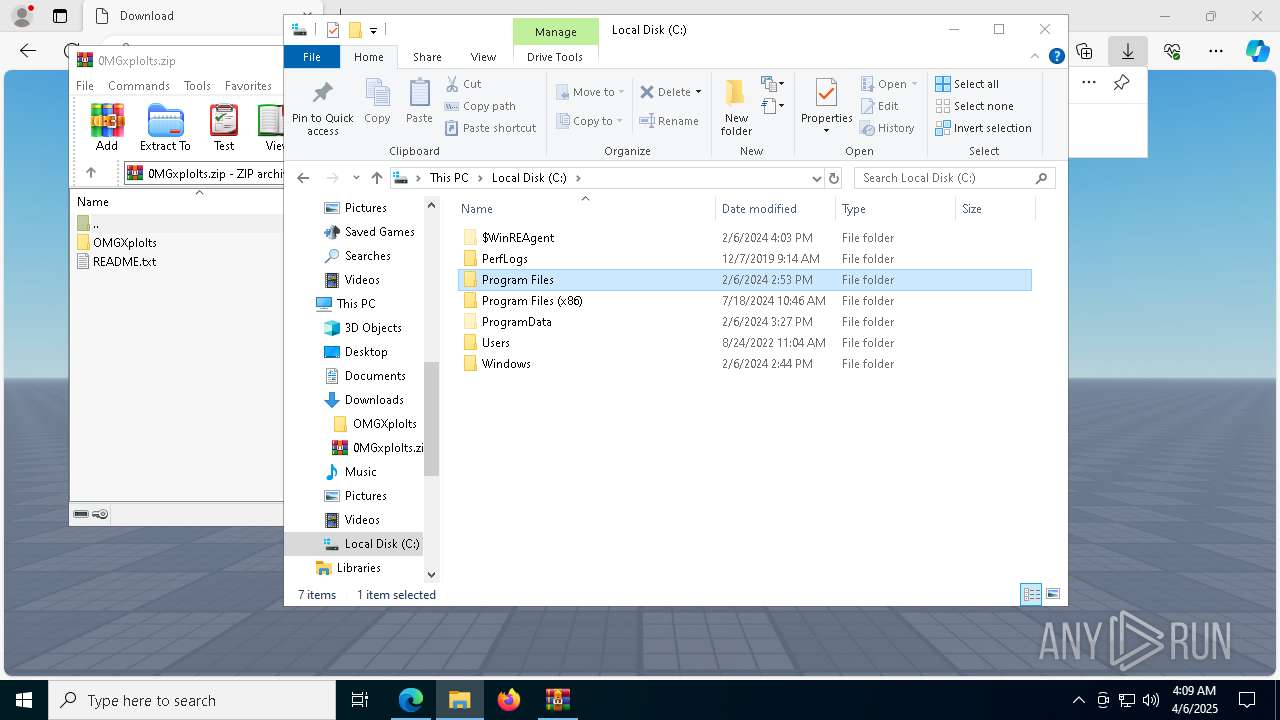
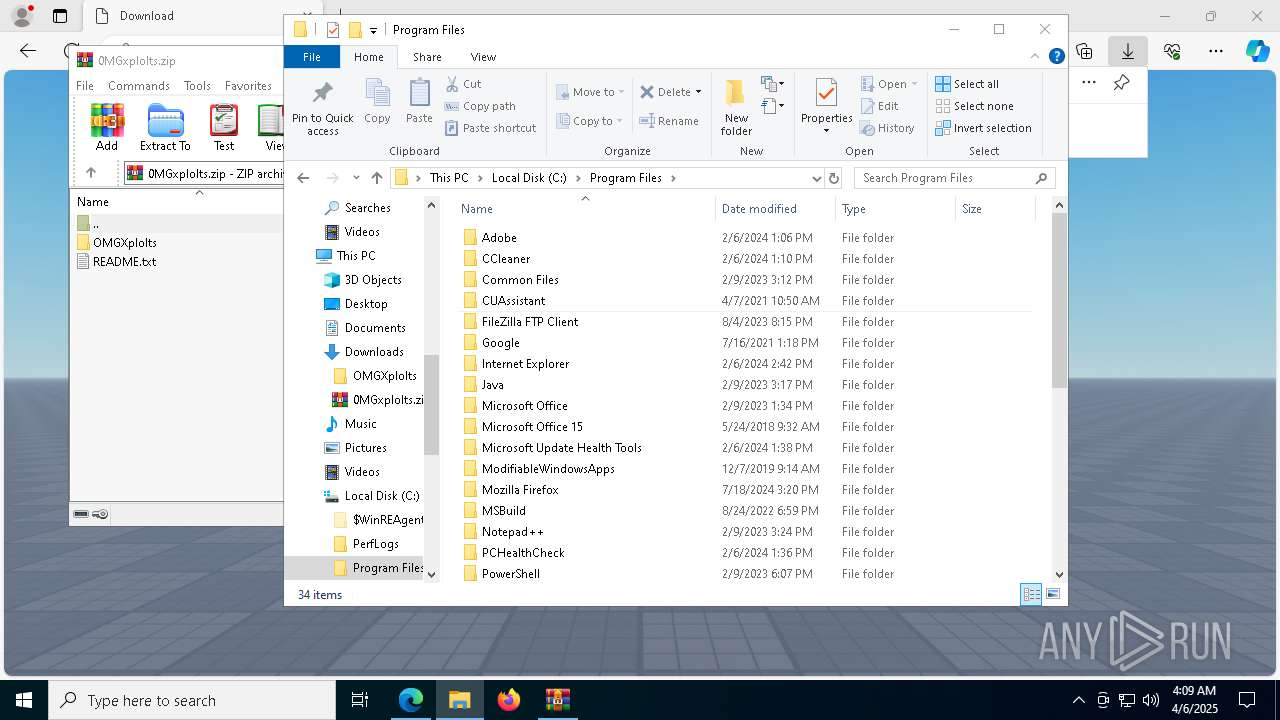
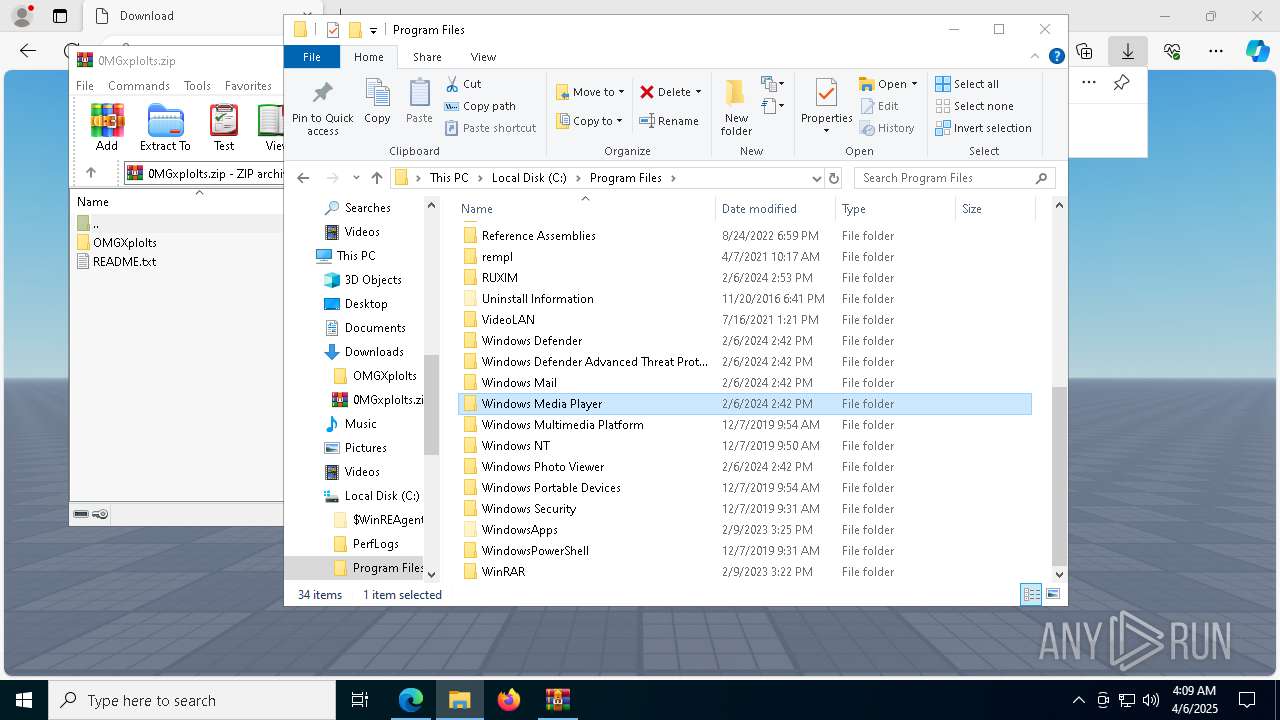
Searches for installed software
- svchost.exe (PID: 5972)
Reads the date of Windows installation
- wmplayer.exe (PID: 4724)
SQL CE related mutex has been found
- unregmp2.exe (PID: 7932)
INFO
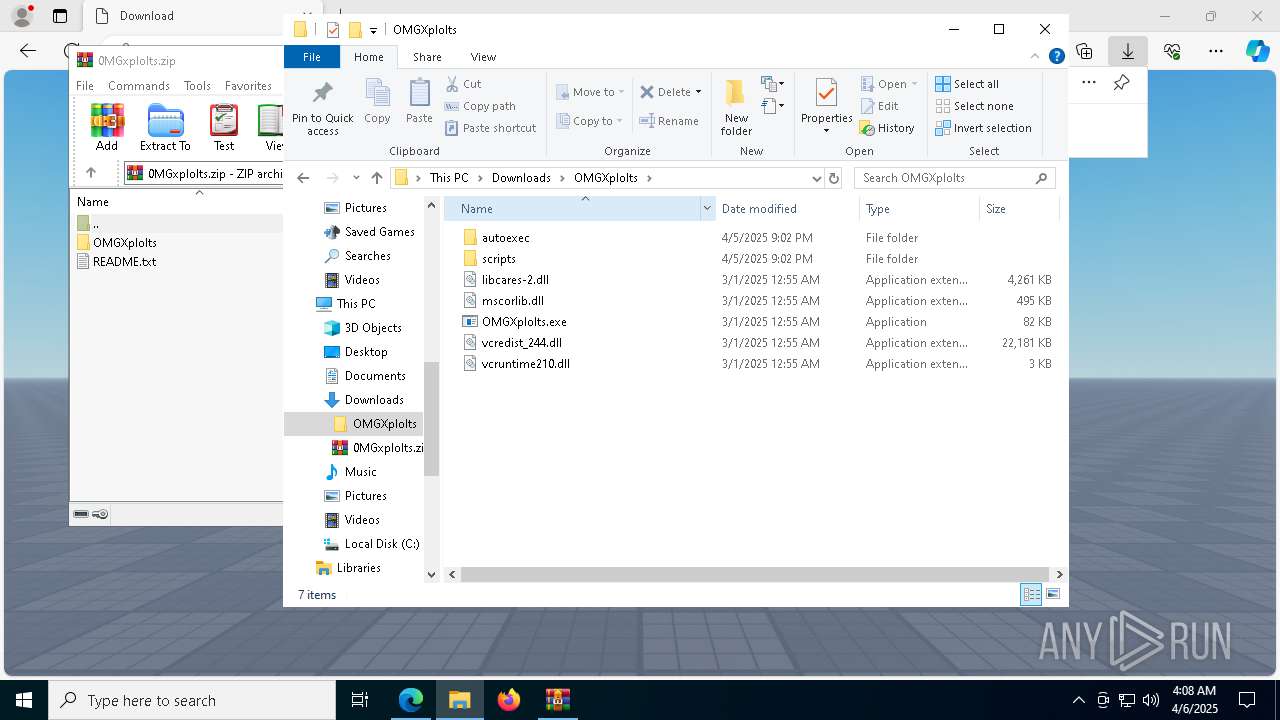
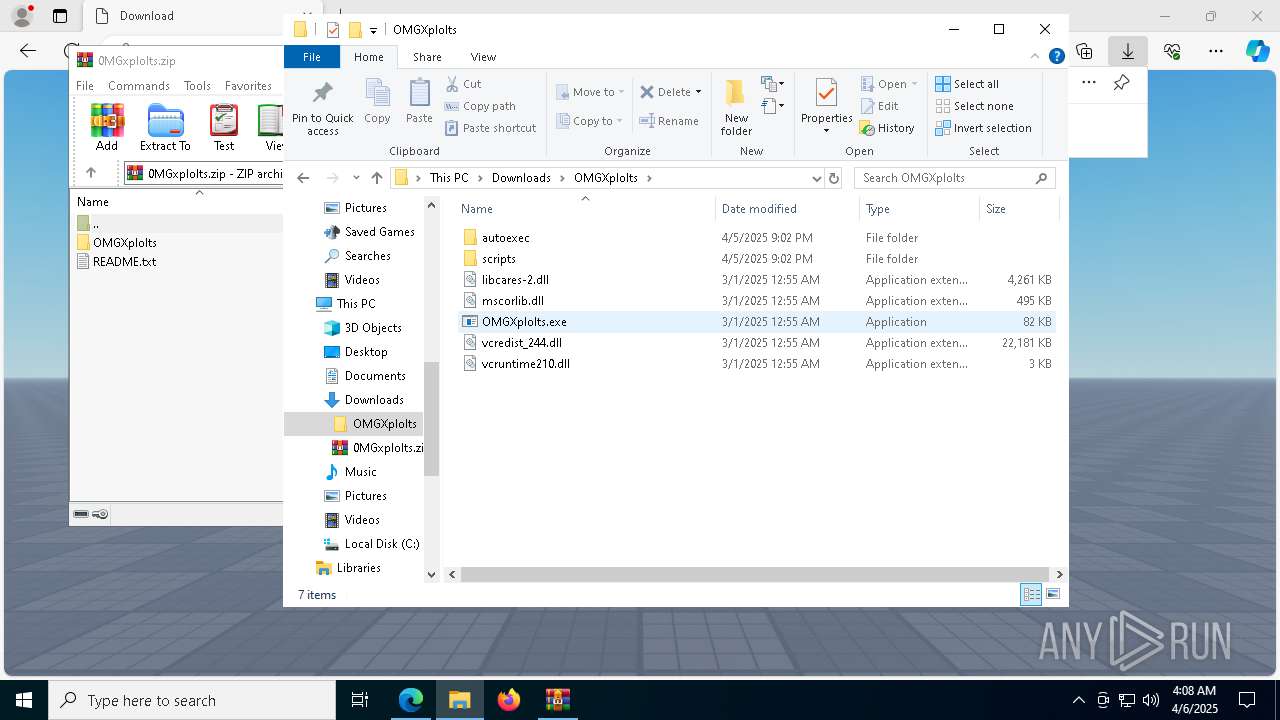
Checks supported languages
- identity_helper.exe (PID: 1676)
- OMGXplolts.exe (PID: 4724)
- RegSvcs.exe (PID: 6940)
- chrome.exe (PID: 4740)
- msedge.exe (PID: 5416)
- wmplayer.exe (PID: 8600)
- wmplayer.exe (PID: 4724)
- setup_wm.exe (PID: 1912)
Reads Environment values
- identity_helper.exe (PID: 1676)
- chrome.exe (PID: 4740)
- msedge.exe (PID: 5416)
Autorun file from Downloads
- msedge.exe (PID: 680)
- msedge.exe (PID: 5972)
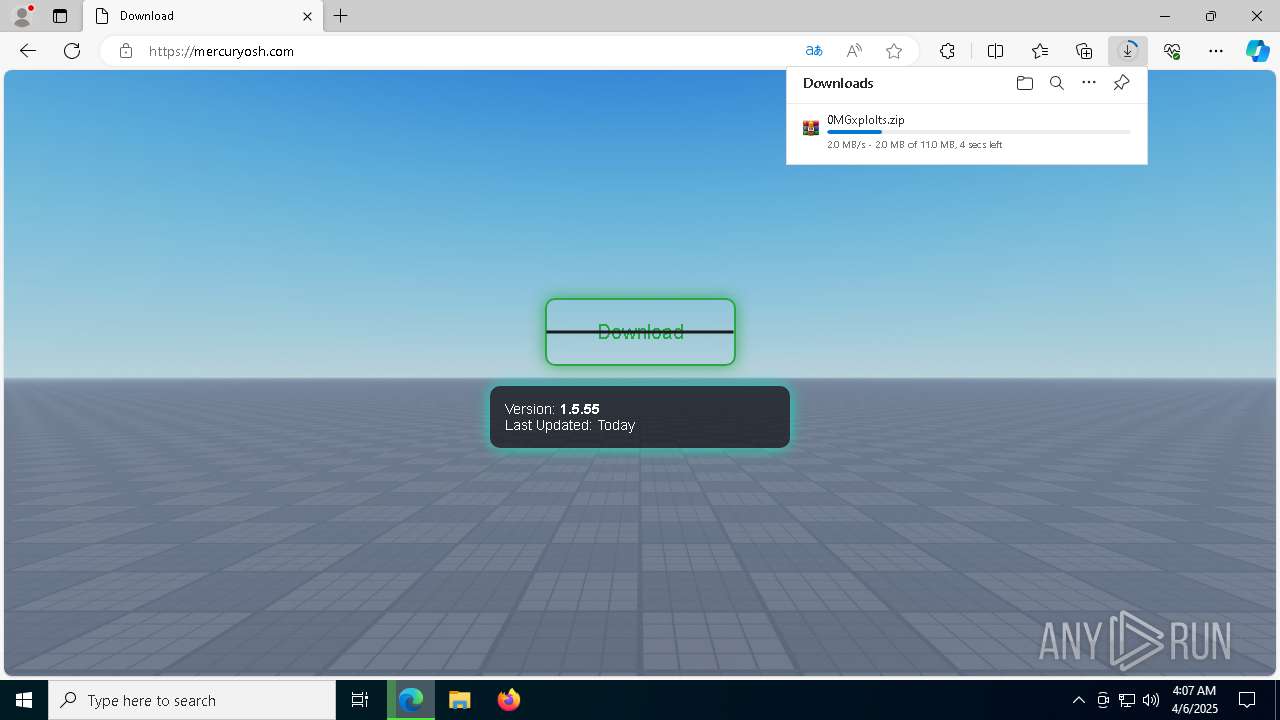
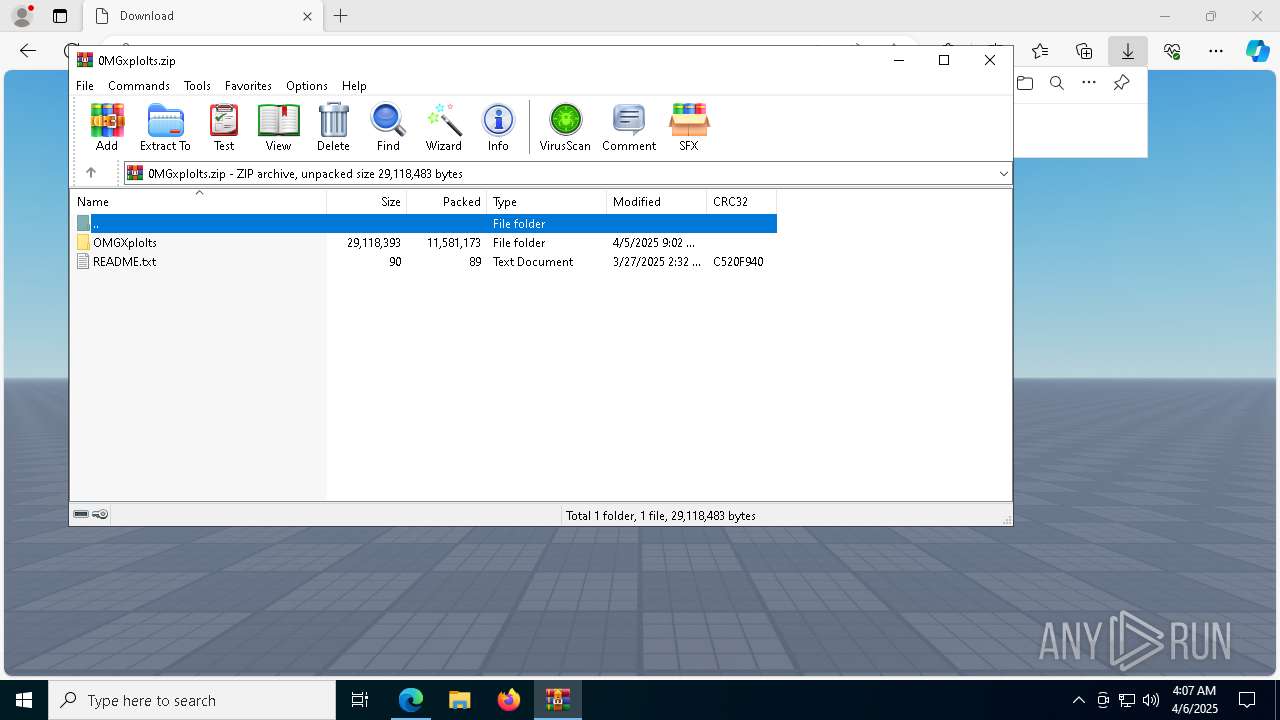
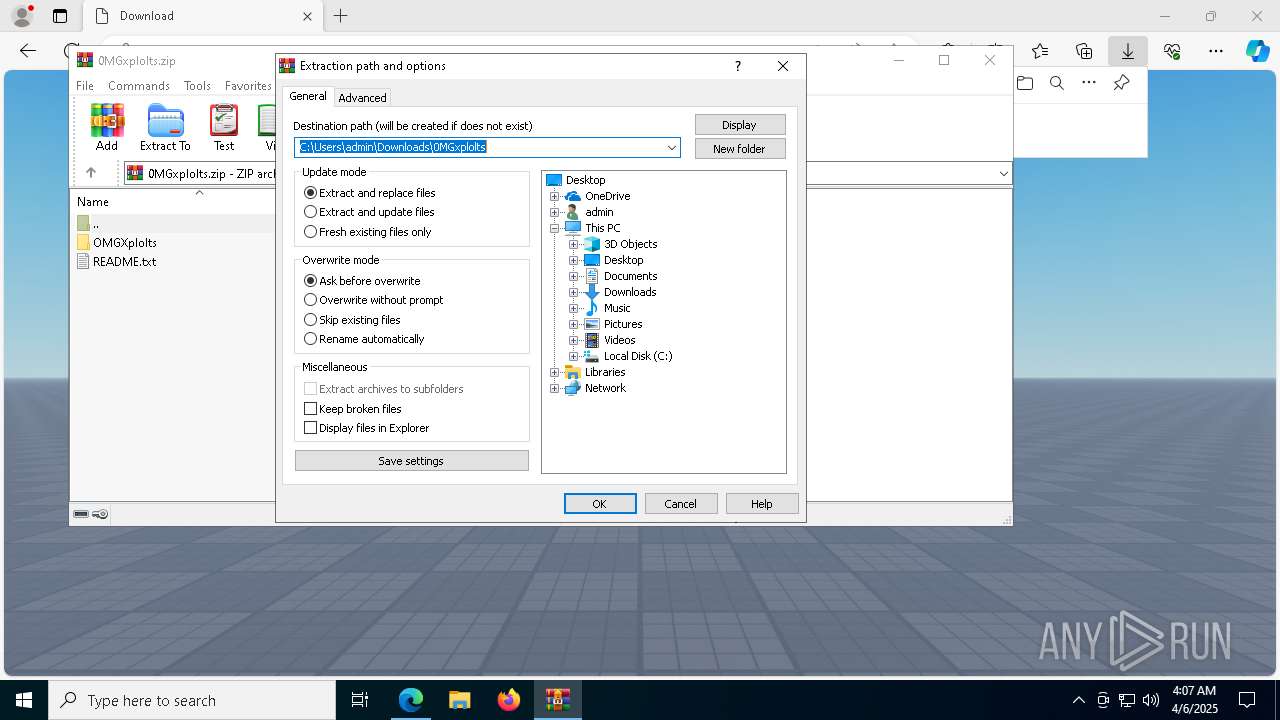
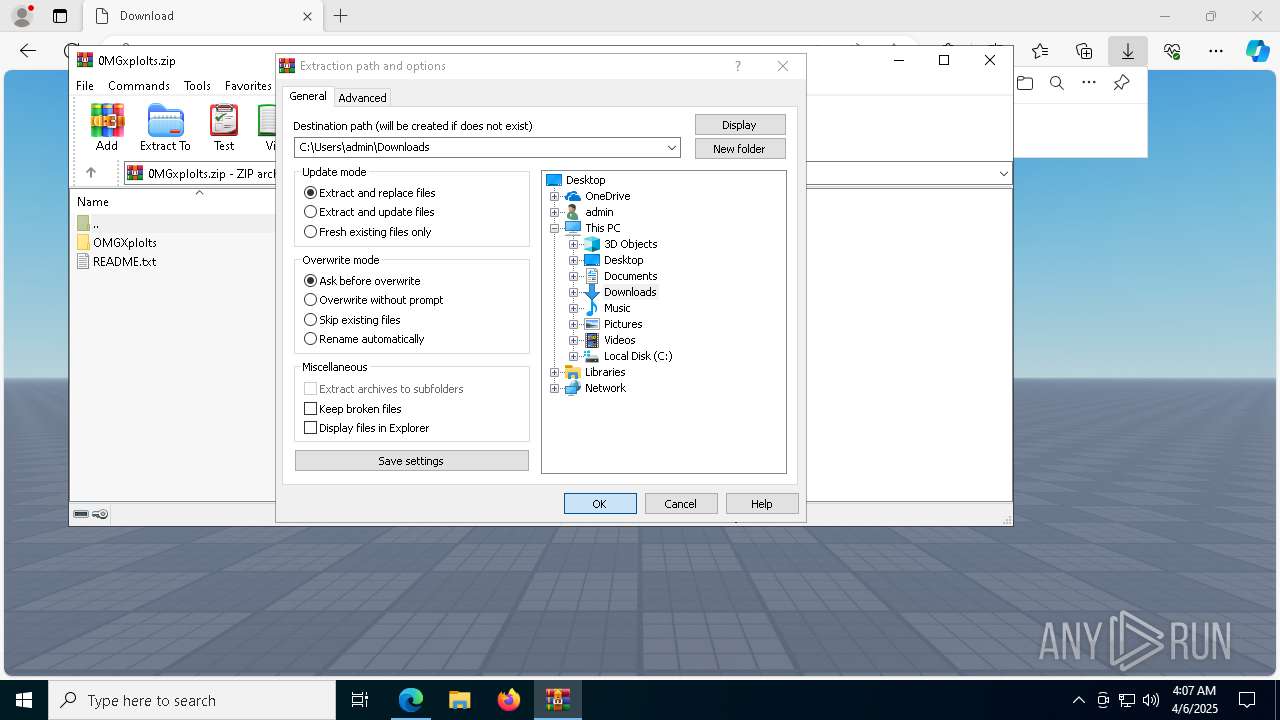
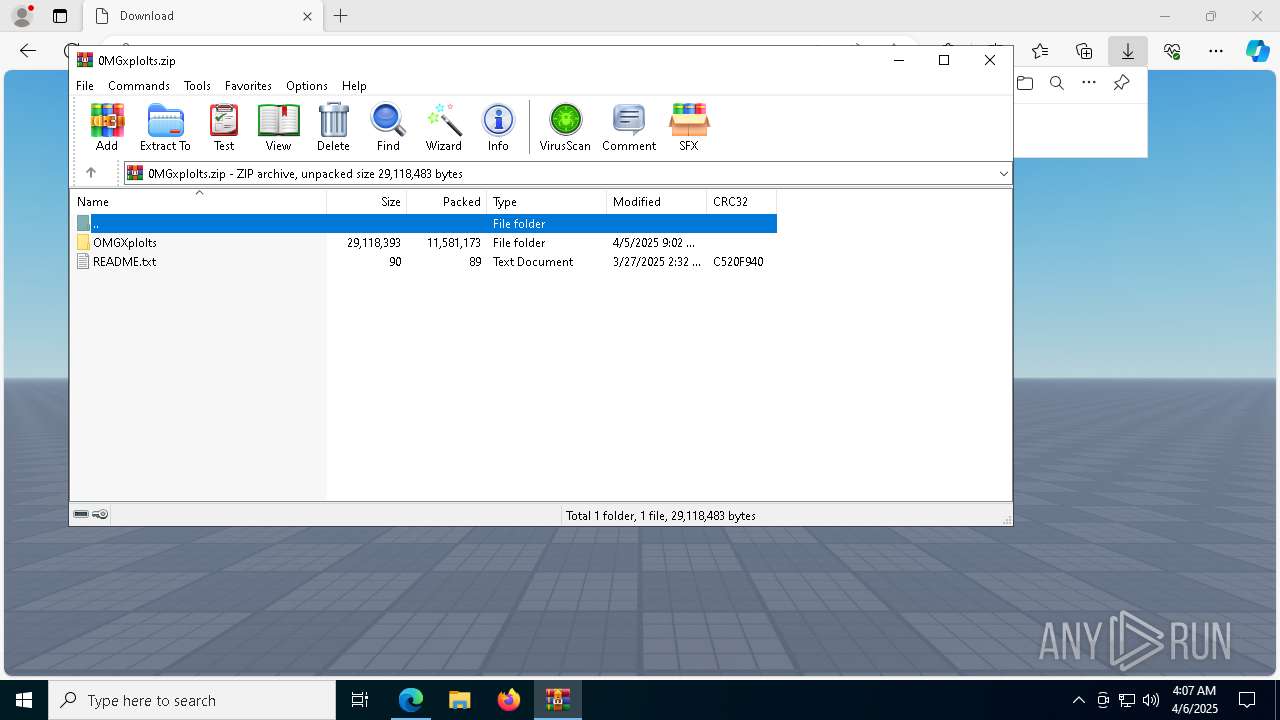
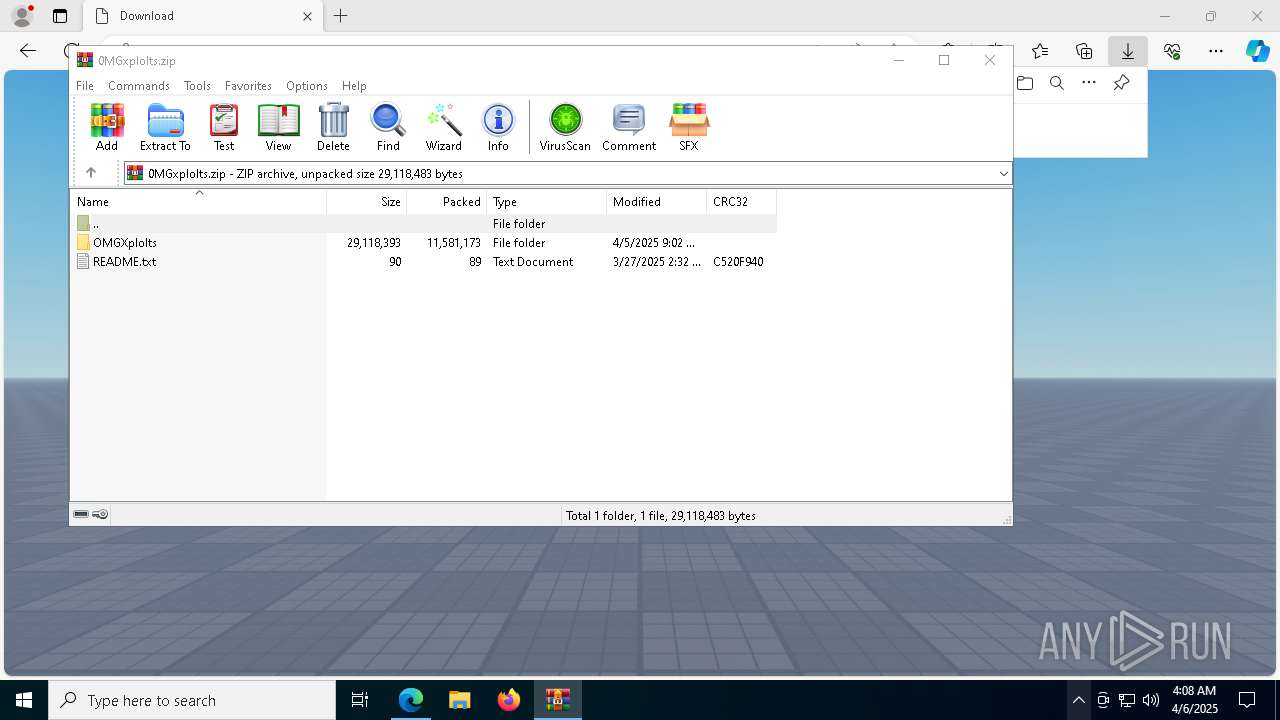
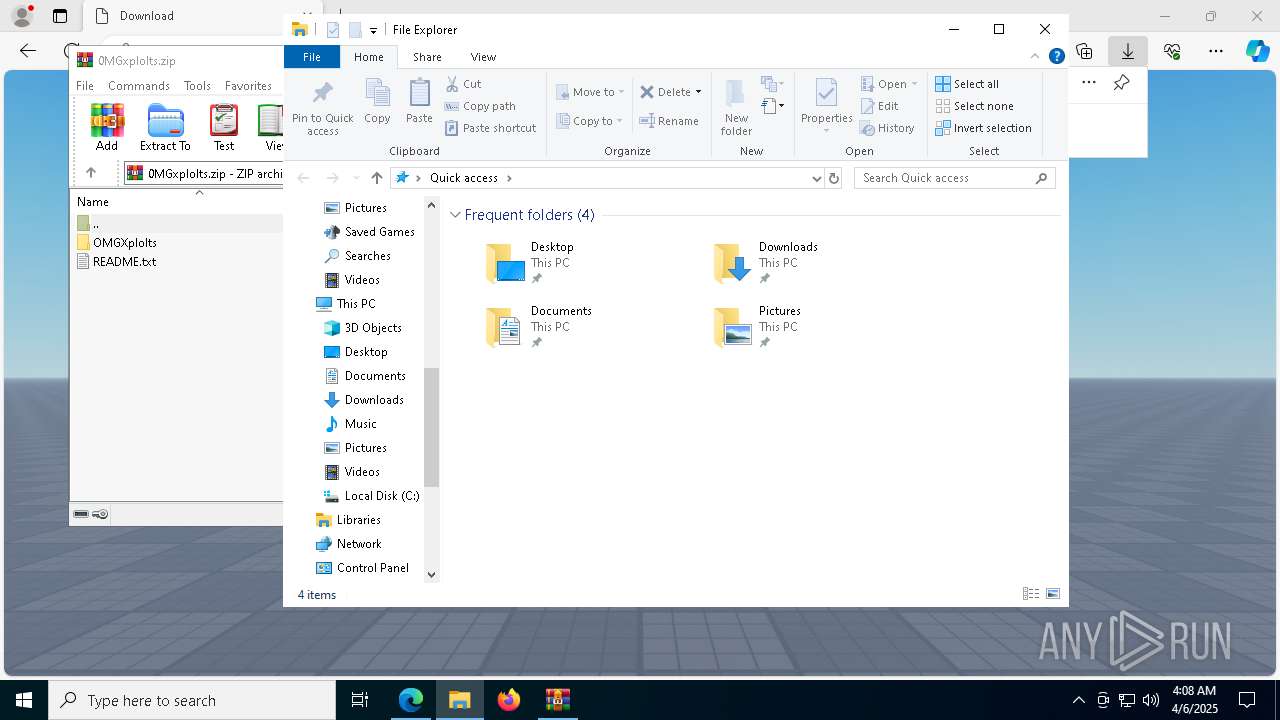
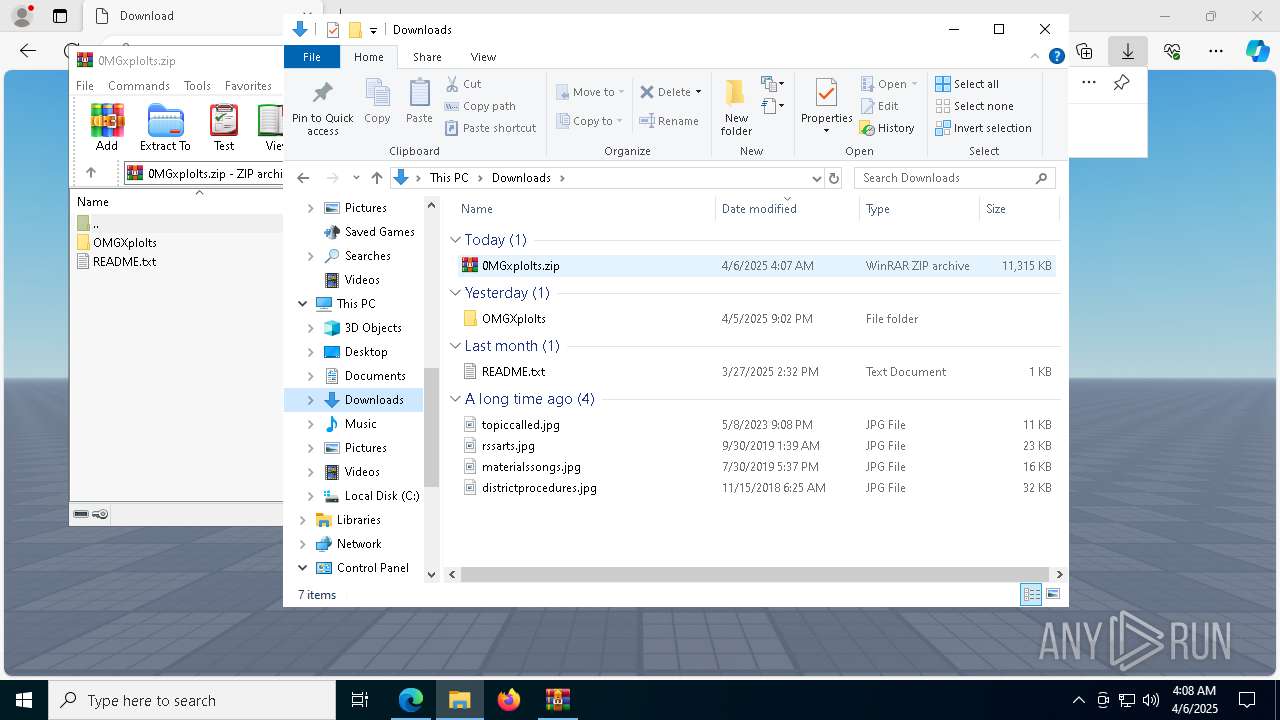
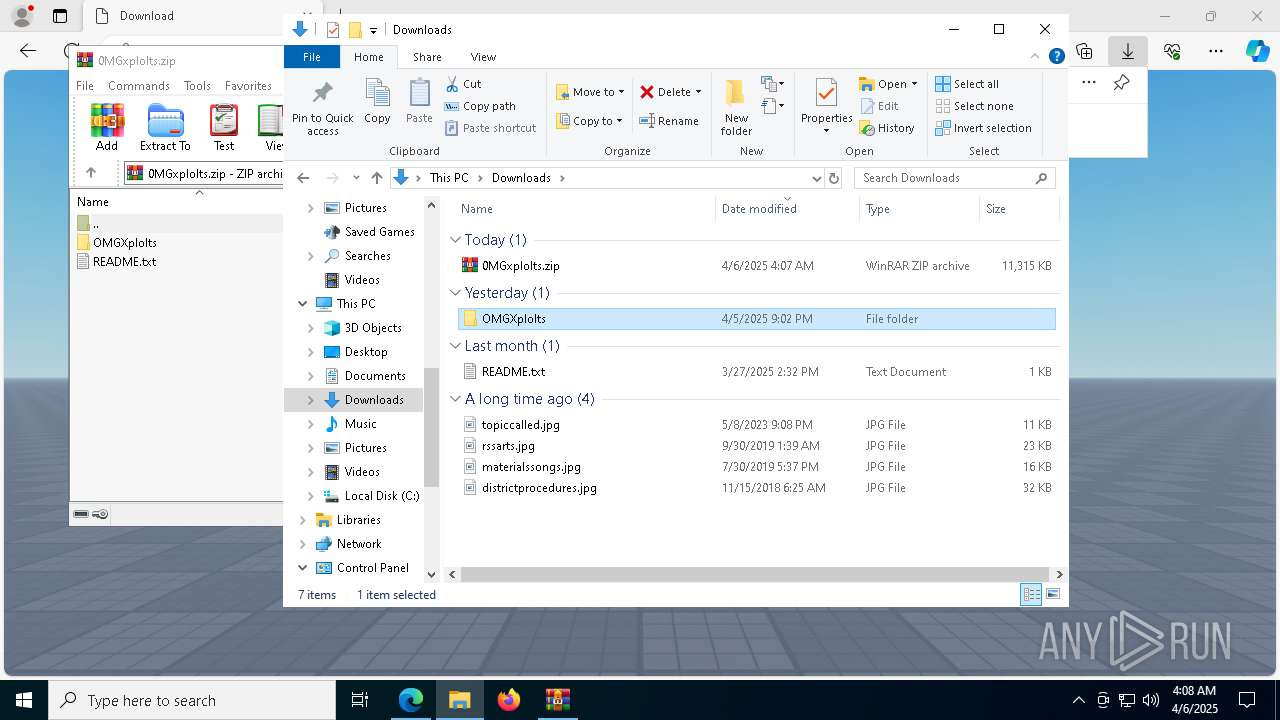
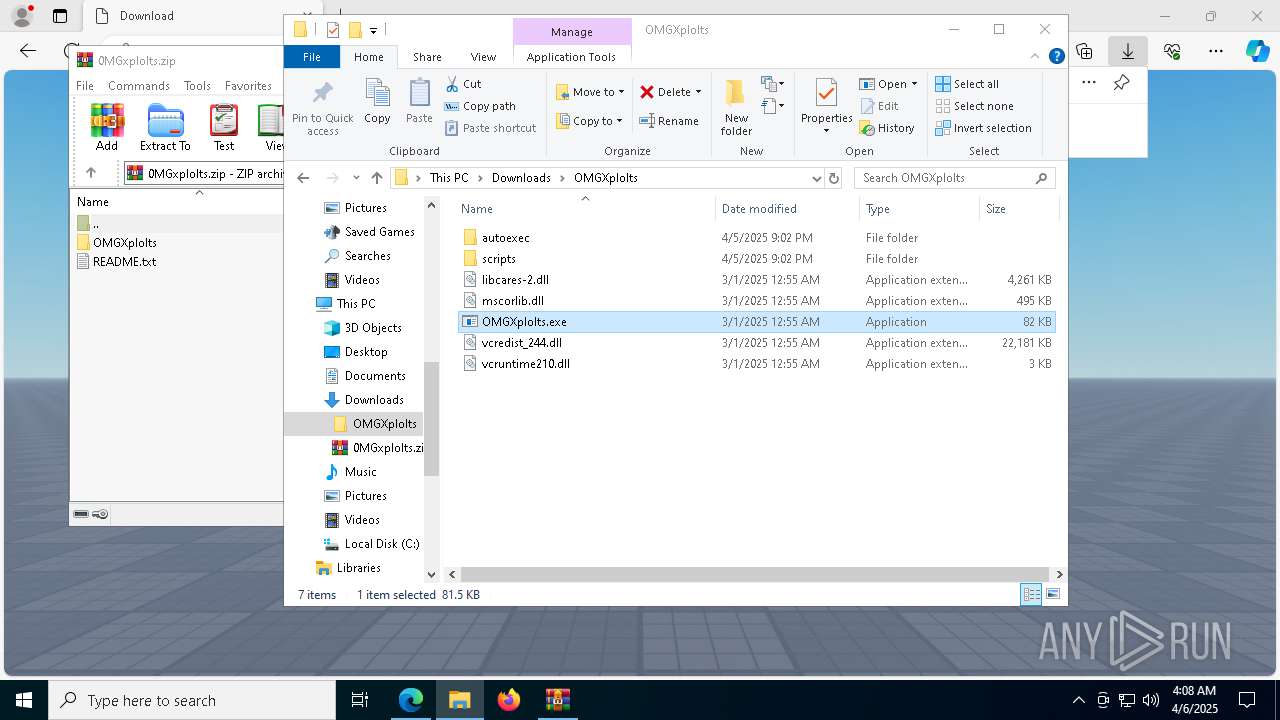
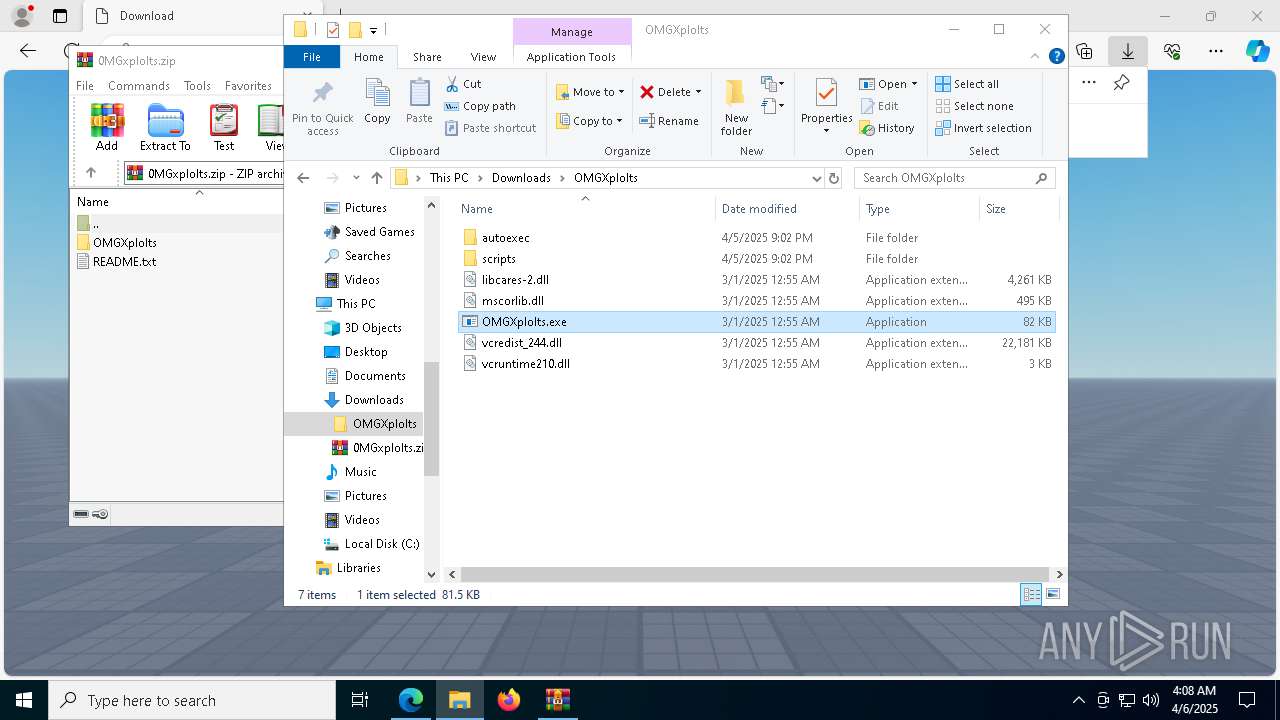
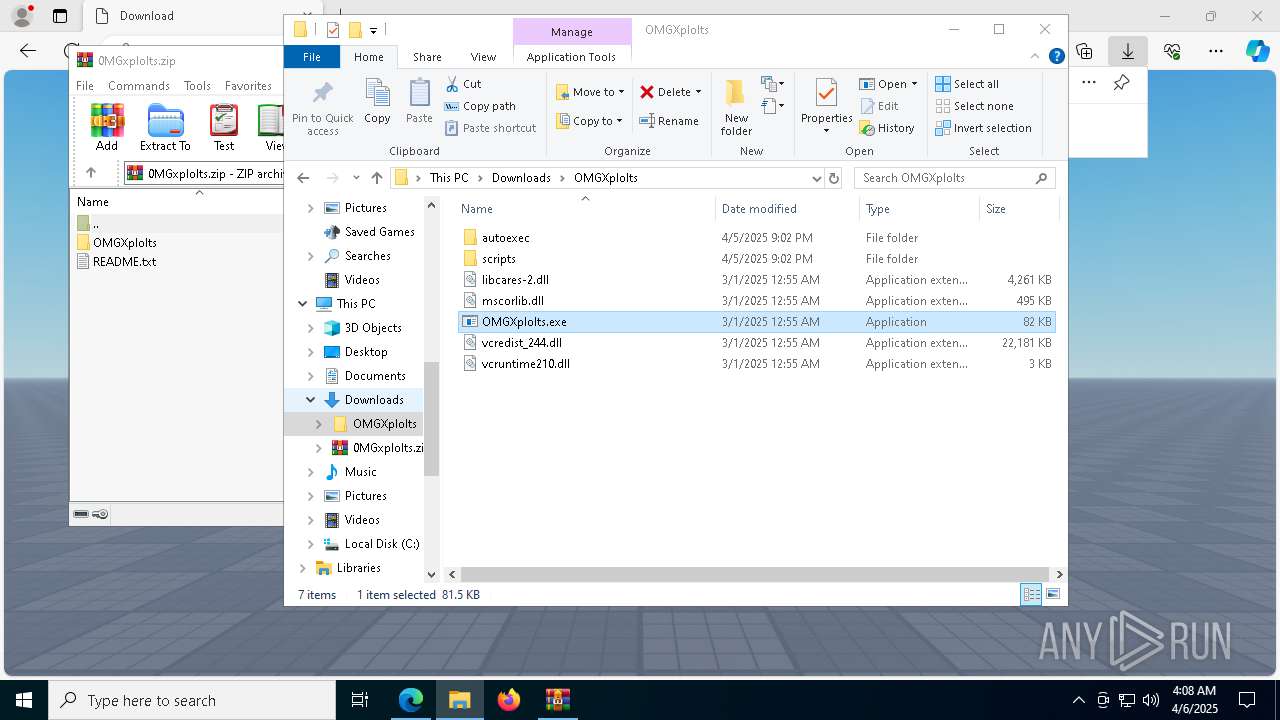
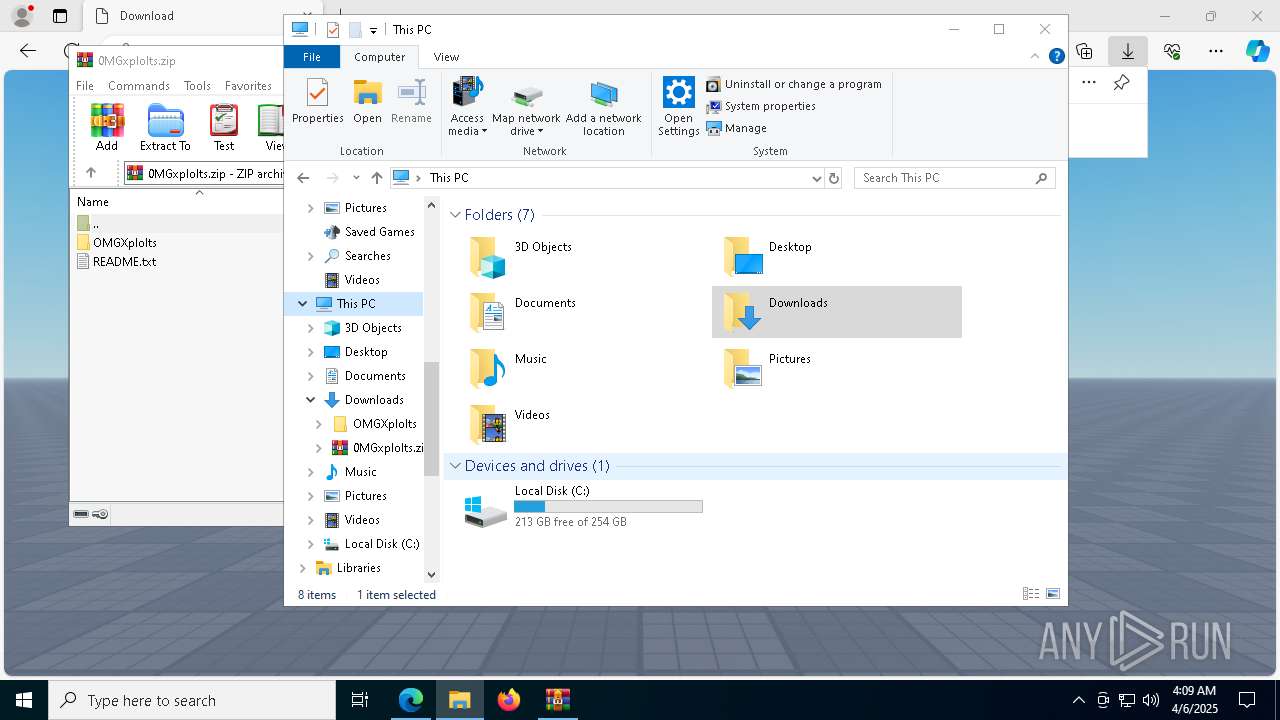
Manual execution by a user
- OMGXplolts.exe (PID: 4724)
- svchost.exe (PID: 7604)
- svchost.exe (PID: 5972)
- wmplayer.exe (PID: 4724)
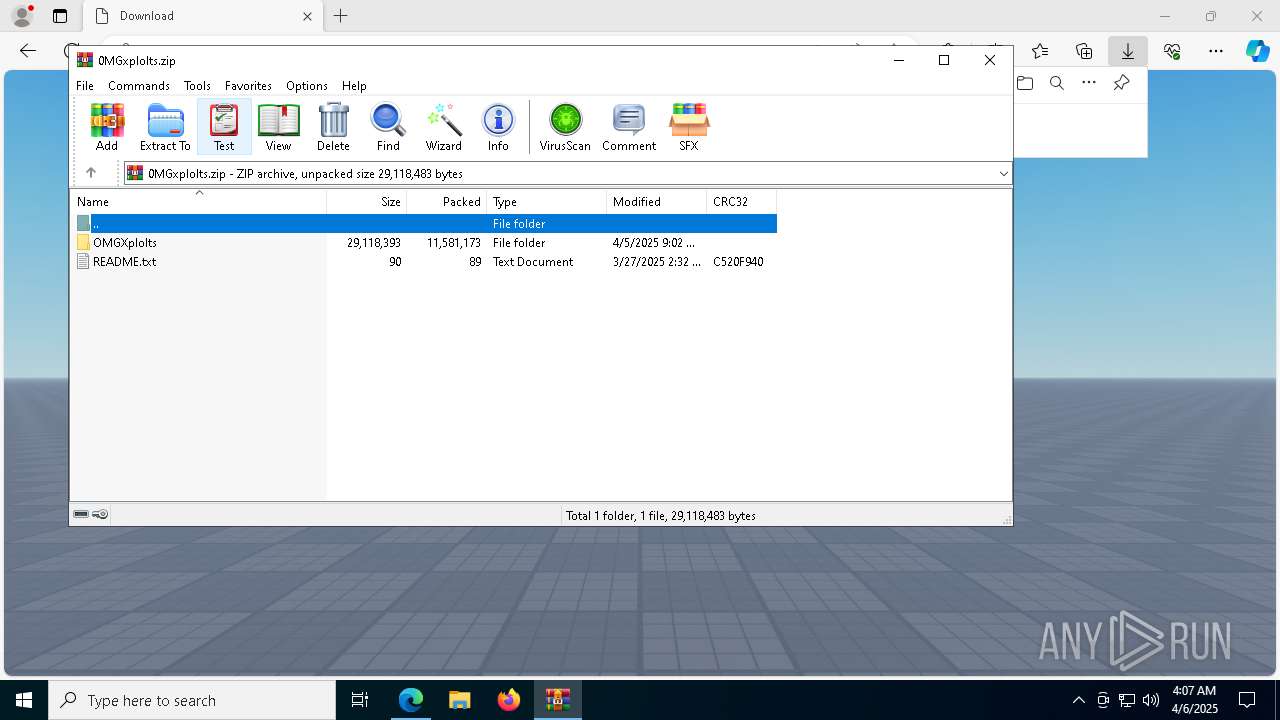
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5384)
Reads the computer name
- OMGXplolts.exe (PID: 4724)
- chrome.exe (PID: 4740)
- identity_helper.exe (PID: 1676)
- msedge.exe (PID: 5416)
- wmplayer.exe (PID: 8600)
- wmplayer.exe (PID: 4724)
- setup_wm.exe (PID: 1912)
Create files in a temporary directory
- svchost.exe (PID: 5972)
- chrome.exe (PID: 4740)
- msedge.exe (PID: 5416)
- setup_wm.exe (PID: 1912)
Reads Microsoft Office registry keys
- msedge.exe (PID: 680)
Application launched itself
- msedge.exe (PID: 680)
Checks proxy server information
- chrome.exe (PID: 4740)
- msedge.exe (PID: 5416)
- slui.exe (PID: 9152)
- setup_wm.exe (PID: 1912)
Process checks computer location settings
- chrome.exe (PID: 4740)
- msedge.exe (PID: 5416)
- wmplayer.exe (PID: 4724)
- setup_wm.exe (PID: 1912)
Reads the machine GUID from the registry
- chrome.exe (PID: 4740)
- msedge.exe (PID: 5416)
- wmplayer.exe (PID: 8600)
Process checks whether UAC notifications are on
- msedge.exe (PID: 5416)
Reads the software policy settings
- slui.exe (PID: 1116)
- slui.exe (PID: 9152)
The sample compiled with english language support
- wmplayer.exe (PID: 8600)
Creates files or folders in the user directory
- unregmp2.exe (PID: 7932)
- wmplayer.exe (PID: 8600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
229
Monitored processes
95
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://www.youtube.com/redirect?event=comments&redir_token=QUFFLUhqbTBpNE05OXI1Z2pxRVJ2UFVvUHBFQ3ZwUnh5d3xBQ3Jtc0tuTk1aQVdjaXdoYWFXdGpEOWJ2NmVhcU9ONDVmdmlWd2VJcWI1bGNnZWt2bzhIbnJVNHEzRHZUM1Y4Q3NlcHA2U1B6VVpJTnZKc2pSSlNpejJtMzMyWnM4Zk5Ta0RHWUIxWkplNEtzZ1NRR0NFeWFPWQ&q=https%3A%2F%2Furl.rw%2Fryos%2F" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2288 --field-trial-handle=1892,i,3532261073915963025,10602567007761598952,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --mojo-platform-channel-handle=3744 --field-trial-handle=2504,i,13031007800453456842,10737471342166299357,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3568 --field-trial-handle=1892,i,3532261073915963025,10602567007761598952,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 960 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4596 --field-trial-handle=2504,i,13031007800453456842,10737471342166299357,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=4352 --field-trial-handle=2504,i,13031007800453456842,10737471342166299357,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1528 --field-trial-handle=2504,i,13031007800453456842,10737471342166299357,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1676 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6128 --field-trial-handle=2504,i,13031007800453456842,10737471342166299357,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1912 | "C:\Program Files (x86)\Windows Media Player\setup_wm.exe" /RunOnce:"C:\Program Files\Windows Media Player\wmplayer.exe" | C:\Program Files (x86)\Windows Media Player\setup_wm.exe | — | wmplayer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Media Configuration Utility Exit code: 0 Version: 12.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 697
Read events
16 541
Write events
136
Delete events
20
Modification events
| (PID) Process: | (680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (680) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F3A6A98AAA902F00 | |||
| (PID) Process: | (680) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9976B28AAA902F00 | |||
| (PID) Process: | (680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B257F5B0-4C78-44E2-A10F-DA4330FB54A9} | |||
| (PID) Process: | (680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7DEAC4B3-37D9-4A30-94BB-E50A4DAB5236} | |||
| (PID) Process: | (680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FA3BA420-45DB-4A53-96B6-D68797A4A6C7} | |||
| (PID) Process: | (680) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1B6ED98AAA902F00 | |||
Executable files
20
Suspicious files
534
Text files
135
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c093.TMP | — | |
MD5:— | SHA256:— | |||
| 680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c0a2.TMP | — | |
MD5:— | SHA256:— | |||
| 680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c0a2.TMP | — | |
MD5:— | SHA256:— | |||
| 680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c0a2.TMP | — | |
MD5:— | SHA256:— | |||
| 680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c0a2.TMP | — | |
MD5:— | SHA256:— | |||
| 680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
94
DNS requests
116
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8856 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1743953629&P2=404&P3=2&P4=Z9BJF7n7miX%2fd8f2%2bRU4gJs8JmsrbEMIdMH7PsZXL0QGfIV3a89v2Iwzxy6Vg3Qwm%2bneKxab6GVE9S38%2bSfEqA%3d%3d | unknown | — | — | whitelisted |
8856 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1743953629&P2=404&P3=2&P4=Z9BJF7n7miX%2fd8f2%2bRU4gJs8JmsrbEMIdMH7PsZXL0QGfIV3a89v2Iwzxy6Vg3Qwm%2bneKxab6GVE9S38%2bSfEqA%3d%3d | unknown | — | — | whitelisted |
8856 | svchost.exe | HEAD | 200 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1743953629&P2=404&P3=2&P4=RFB3Y4ScdPJor8ap1w203l%2fnoKPX5FSZ80%2fCwLnilKUddsizwNqbCHmFQCaVxE6j0tBHhZcmy8nhc2K4PREAqw%3d%3d | unknown | — | — | whitelisted |
8856 | svchost.exe | GET | 200 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1743953630&P2=404&P3=2&P4=kZYxoxI1oCWJxA0VZQtMx5IC%2feD4spHT12YKa7Daddfywm0577v577Fqtkxez5m97FIgkP%2ftp7apXM86WJwtqg%3d%3d | unknown | — | — | whitelisted |
8856 | svchost.exe | GET | 200 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1743953629&P2=404&P3=2&P4=RFB3Y4ScdPJor8ap1w203l%2fnoKPX5FSZ80%2fCwLnilKUddsizwNqbCHmFQCaVxE6j0tBHhZcmy8nhc2K4PREAqw%3d%3d | unknown | — | — | whitelisted |
8856 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743953629&P2=404&P3=2&P4=D7wm29OOZ9z%2fJle1qizk1JYA7sKTDVefNntfvvatjBTPmkke9oAKK%2f%2bYMx8v5J5LC4L4W%2fZ%2bZt6hDrf1Na4iBg%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8856 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1743953629&P2=404&P3=2&P4=Z9BJF7n7miX%2fd8f2%2bRU4gJs8JmsrbEMIdMH7PsZXL0QGfIV3a89v2Iwzxy6Vg3Qwm%2bneKxab6GVE9S38%2bSfEqA%3d%3d | unknown | — | — | whitelisted |
8856 | svchost.exe | HEAD | 200 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1743953630&P2=404&P3=2&P4=kZYxoxI1oCWJxA0VZQtMx5IC%2feD4spHT12YKa7Daddfywm0577v577Fqtkxez5m97FIgkP%2ftp7apXM86WJwtqg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
680 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7308 | msedge.exe | 216.58.206.46:443 | www.youtube.com | — | — | whitelisted |
7308 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7308 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7308 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7308 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.youtube.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7308 | msedge.exe | Misc activity | ET INFO URL Shortener Domain in DNS Lookup (url .rw) |
7308 | msedge.exe | Misc activity | ET INFO URL Shortener Domain in DNS Lookup (url .rw) |
7308 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Domain (url .rw in TLS SNI) |
7308 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Domain (url .rw in TLS SNI) |
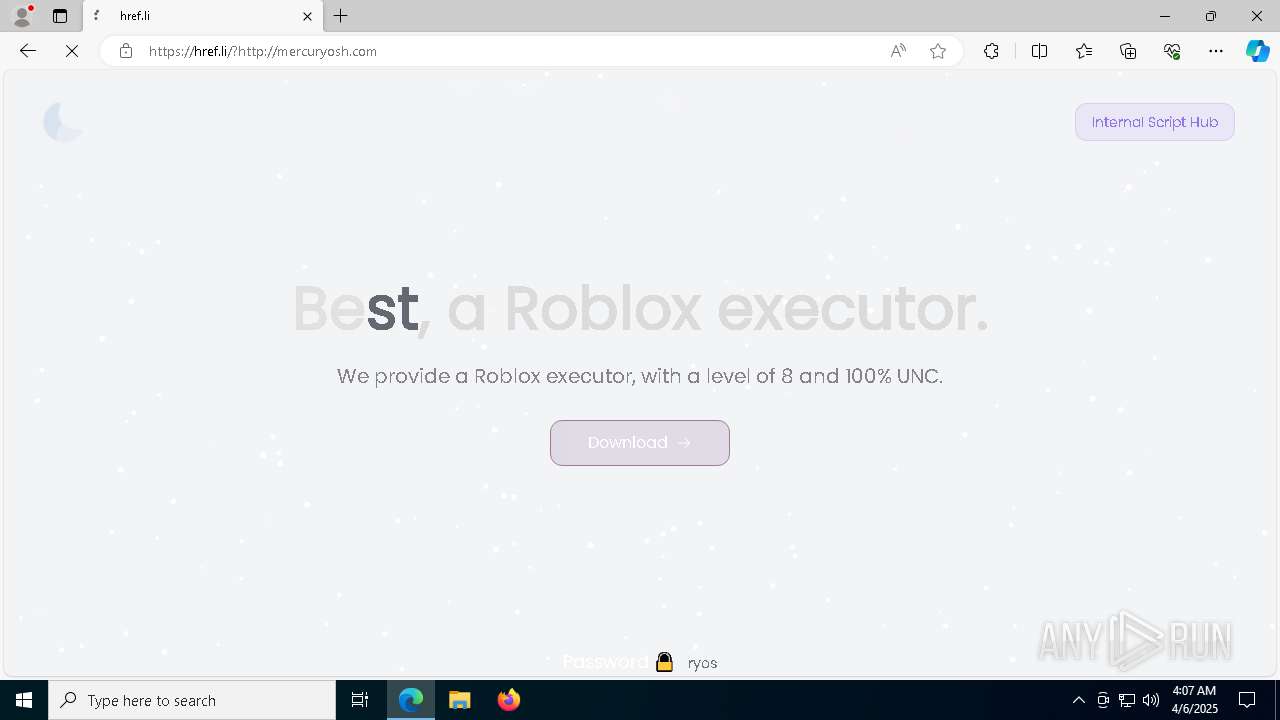
7308 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7308 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
5972 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
5972 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
8652 | dllhost.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 29 |
2 ETPRO signatures available at the full report